1. Introduction
Despite the fact that today almost all ships are to some extent digitalized, the shipping industry addresses the digital transformation challenge, including the emergence of crew-less vessels [
1]. Such vessels come in two broad categories, namely the remotely operated vessel and the autonomous vessel; both kinds are referred to as
cyber-enabled ships (C-ES) [
2]. The C-ES is a cyber physical ecosystem which consists of the vessel itself, a Shore Control Center (SCC) that controls and handles the C-ES, the communication links between the vessel and the SCC, and other ships in the vicinity.
The integration of Information Technology (IT) and Operation Technology (OT) to form
Cyber Physical Systems (CPS), which constitute a central element of the digital transformation process in many application domains is unavoidably accompanied by an increase and a diversification of the cyber risks that the domain is facing. This is mainly due to the fact that whereas traditional operations were designed with no need for cyber security in mind, modern IT-enabled operations are allowed to be accessed and controlled by outward-facing information systems, through interfaces that are rarely adequately secure [
3].
The C-ES is no exception. Although most of the C-ES CPSs are parts of today’s conventional ships, their exposure to contemporary technologies, aiming to be controlled and monitored remotely, increases the attack surface and makes them more vulnerable to cyber-attacks. Indeed, research on the cyber security risks of autonomous and unmanned vessels [
2,
4] has revealed an increased attack surface and several vulnerable systems. Thus, ship-side cyber security incidents, such as, for example, the ones reported in Reference [
5,
6,
7], have already occurred; in fact, such incidents have been increasing at an alarming rate over the last three years [
8]. Such incidents may also impact the safety of humans, operations, and cargo.
In the light of these findings, of the increased financial value of the sector [
9], and of the multitude of potential attackers, including such with advanced capabilities, the promotion of cyber security and safety of the C-ES ecosystem becomes very important [
10]. The first step towards strengthening the cyber security posture of an ecosystem is to understand, analyze, and manage the cyber risks that it faces; this will eventually drive the design of a security architecture that includes appropriate cyber security controls that will mitigate the risks.
Risk is defined as “the effect of uncertainty on objectives” [
11]. Cyber Security risk is associated with the potential that threats will exploit vulnerabilities of an asset or group of assets and thereby cause harm to an organization. Cyber risk is assessed in terms of the likelihood of a
threat1 occurring, the extent of the
vulnerabilities2 to the threat, and the magnitude of the
impact3; these constitute the
elements of cyber risk.
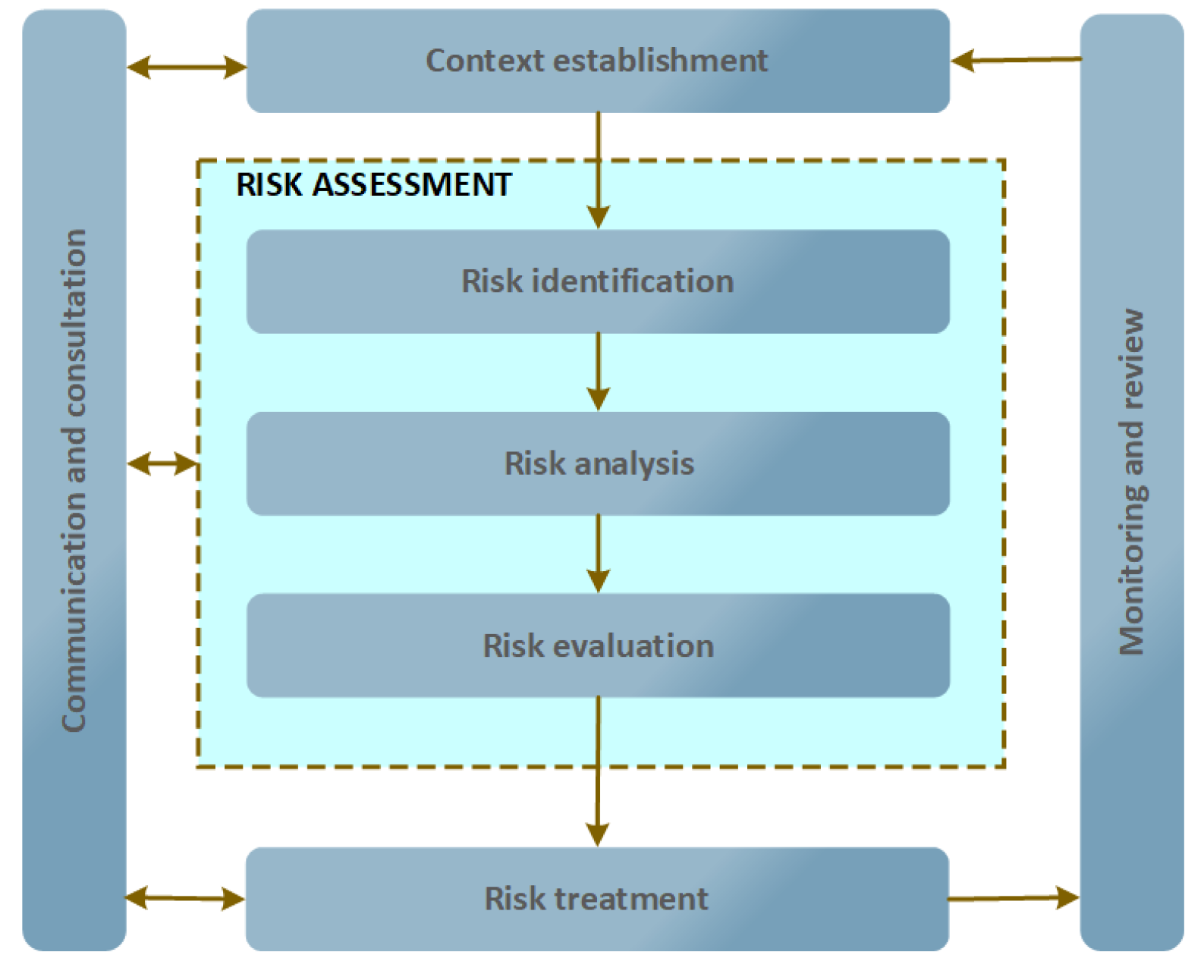
The risk management process as specified in ISO 31000 [
13] comprises five sub-processes [
11], as shown in
Figure 1:
The external and internal context for cyber security risk management should be established, which involves setting the basic criteria necessary for cyber security risk management, defining the scope and boundaries, and establishing an appropriate organization operating the cyber security risk management.
Risks should be assessed, i.e., identified, quantified or qualitatively described, and prioritized against risk evaluation criteria and objectives relevant to the organization.
Controls to reduce, retain, avoid, or share the risks should be selected and a risk treatment plan defined.
Information about risk should be exchanged and/or shared between the decision-makers and other stakeholders.
Risks and their elements should be monitored and reviewed to identify any changes at an early stage and to maintain an overview of the complete risk picture. This is why, as
Figure 1 illustrates, the cyber security risk management process can be iterative for risk assessment and/or risk treatment activities.
In this paper, we focus on the risk assessment and the risk treatment sub-processes. Risk assessment methods are quantitative, qualitative, or semi-quantitative. Quantitative risk assessment is based on using mathematical methods and rules and assigns a numerical value, often in the [1-x] range to each risk. The results are less subjective than those of the other two types, and therefore drive the process of control selection more effectively, but they cannot be easily communicated to non-technically oriented decision-makers. In contrast, qualitative risk assessment is based on applying non-numerical methods and assigns a level value to each risk, such as low, medium, and high. This type of assessment has a limited number of results, but these are more comprehensible to decision-makers. Finally, semi-quantitative risk assessment combines rules and methods for evaluating the risk by combining numeric values and levels; for example, the [1-x] range can easily be converted into qualitative expressions that help risk communication to decision-makers.
STRIDE and DREAD have been selected for the work described herein. These methods can effectively analyze highly interconnected CPSs comprising heterogeneous components [
14], and they are most appropriate for analyzing systems under development. In such systems, the operational and functional requirements are not established yet. Alternative approaches need such requirements to produce valid results. In contrast, STRIDE and DREAD facilitate the analysis of conceptual systems by answering questions regarding the security objectives of the targeted ecosystem. Moreover, the combination of qualitative and quantitative methods to analyze the cyber risk provides a holistic view, not captured by other methods. Further, this hybrid approach facilitates the communication of the results to relevant stakeholders while allowing the representation of cyber risk in numeric form, thus facilitating the assessment of the effectiveness of controls at later stages of the risk treatment process. Finally, both STRIDE and DREAD are being widely used in both academia and industry [
15].
Risk treatment is the process followed to modify risk [
11]. A risk can be treated by:
modifying its level, by introducing controls;
retaining it, with no further action taken;
avoiding it, by avoiding the activity or condition that gives rise to the particular risk;
sharing it with other party or parties, for example, by means of insurance and/or risk financing.
The four options for risk treatment are not mutually exclusive. Sometimes a combination of options, such as modifying risks and sharing or retaining any residual risks, can be beneficial.
Individual elements of the cyber risk of, as well as
attacks4 against individual CPSs in the C-ES, have been studied, and proposals for risk assessment approaches have appeared in the literature. However, to the best of our knowledge, a holistic assessment of the cyber risks of the whole CPS part of the C-ES ecosystem, comprising all of the aforementioned types of risk assessment methods, which leads to concrete proposals for cyber security controls and can also be used by non-technical decision-makers, has not been made available.
In this paper:
we extend our previous work in Reference [
2] on qualitative risk assessment of CPSs on board the C-ES to all CPSs identified in Reference [
16];
we provide a quantitative risk assessment for all C-ES CPSs identified in Reference [
16];
we propose an approach for systematically selecting appropriate cyber security controls to mitigate the cyber risks; and
we demonstrate the workings of the approach by applying it to select cyber security controls for the most vulnerable CPSs on board the C-ES.
The remainder of the paper is structured as follows: In
Section 2, we review the relevant literature. In
Section 3, we use the STRIDE method [
17] as modified in Reference [
2] to analyze the threats and the attack scenarios for the CPSs of the C-ES that have been identified in Reference [
16] and to qualitatively assess the related risks. In
Section 4, we turn our attention to quantitatively assessing the risks, by leveraging a variant of the DREAD method [
18] adapted for use in CPSs. Our proposed approach for systematically selecting cyber security controls is presented in
Section 5, where also its workings are demonstrated by means of applying it to select controls for the three most vulnerable on-board CPSs of the C-ES. Finally,
Section 6 summarizes our conclusions and indicates directions for future research.
2. Related Work
A wealth of cyber risk assessment methods applicable to general purpose IT systems exists. Whilst these can be and have been applied to IT systems in the maritime domain, they cannot accurately assess cyber risks related to CPSs [
19]. Cyber risk assessment methods for CPSs more often than not are domain specific, as they need to take into account safety as an impact factor additional to the “traditional” impact factors of confidentiality, integrity, and availability [
3]. In the maritime domain, a review of cyber security risk assessment methods appeared in Reference [
20]. Rødseth et al. in Reference [
21] proposed a risk assessment method for the unmanned merchant ship. Although the method aims to identify both safety and security risks, particular focus is given on hazard identification and to the accordant risks, with cyber security left largely unaddressed. Tam et al. in Reference [
4] proposed the MaCRA model-based framework for maritime cyber-risk assessment and applied it to a number of example scenarios [
22]. However, the aim of MaCRA is not to assess the risks or flaws of specific systems, but rather to facilitate the understanding of cyber risks in the maritime domain. B. Svilicic et al. in Reference [
23] proposed a framework for assessing cyber risks in ships and applied it to the case of the Electronic Chart Display and Information System (ECDIS).
Several works in the literature have analyzed security threats and risks for specific systems used in specific types of autonomous and remotely controlled vessels. Among these, Bolbot et al. in Reference [
24] identified and analyzed safety related cyber-attacks in an autonomous inland ferry; their analysis covers safety aspects regarding the navigational and propulsion system of the ferry. Silverajan et al. in Reference [
25] explored security issues and cyber attacks targeting systems of smart ships. Awan et al. in Reference [
26] have analyzed 59 documented accidents to better understand the vulnerabilities of Integrated Bridge System (IBS) components. Svilicic et al. in Reference [
27] present a study on the cyber security resilience of a shipboard Integrated Navigational System (INS) installed on a RoPax ship engaged in international trade. Wang et al. in Reference [
28] propose a secure relative integrated navigation method to counteract injected fault measurement attacks. Balduzzi et al. in Reference [
29] presented a security evaluation of the Automatic Identification System (AIS), by introducing threats affecting both the implementation in online providers and the protocol specification. Lund et al. in Reference [
30] described a proof-of-concept attack on an INS and its integrated ECDIS, and demonstrated the attack on a vessel. Kavallieratos et al. in Reference [
2] identified potential cyber attack scenarios and qualitatively evaluated the accordant risks for a number of CPSs of the C-ES ecosystem, both on-board and in the SCC.
Systematic methods for selecting security controls for IT systems either view the problem of control selection as an investment problem and apply management tools and financial analysis to optimize the selection [
31], or in the context of responding to an intrusion, i.e., when a specific attack has been already detected as taking place [
32]. A combinatorial optimization model to efficiently select security controls was proposed in Reference [
31]. However, security control selection is still largely performed empirically, particularly for CPSs. In the maritime domain, potential cyber security controls for systems on board autonomous and remote controlled vessels have also been proposed. Bothur et al. in Reference [
33] discussed the security vulnerabilities that smart ships face, and described security countermeasures, particularly procedural and technical solutions, by following a defense in depth approach. Silverajan et al. in Reference [
25] analyzed the main systems of an unmanned smart ship and proposed defense strategies against previously discussed cyber attacks and threats. Bolbot et al. in Reference [
24] analyzed safety-related cyber attacks for the navigational and propulsion systems, evaluated the accordant risks and proposed general security recommendations. Sahay et al. in Reference [
34] proposed an SDN framework to mitigate cyber attacks and improve the resilience in the smart ship’s communication network. None of the above works followed a systematic, risk-based process for selecting the controls. Further, the aforementioned analyses focused on defense strategies and controls that are not system-specific.
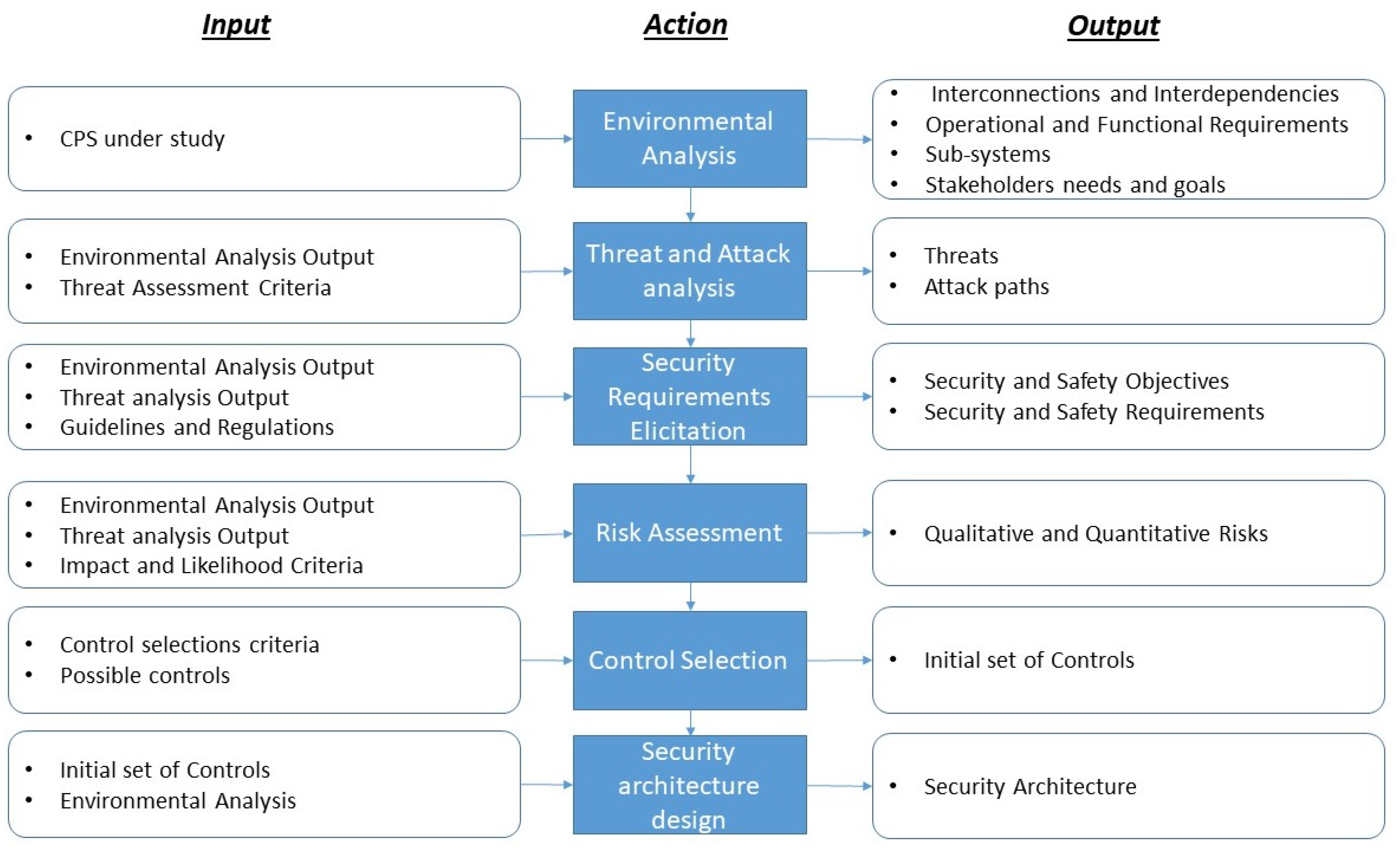
5. Cyber Risk Treatment
The ISO27005 risk management approach aims at identifying risk treatment strategies rather than designing the security architecture of the system under study. A necessary prerequisite for designing such an architecture for the C-ES is to select appropriate controls for each individual component, and to consolidate these into a coherent and consistent whole that will take into account not only the risks, but also the requirements stemming from the C-ES’s environment. Accordingly, we propose an approach for managing the risks of the C-ES, as depicted in
Figure 2, where six sub-processes are specified, along with their inputs and outputs. The Environmental Analysis sub-process for the C-ES has been carried out in Reference [
16]; the Threat Analysis sub-process has been carried out in Reference [
2]; and the Security Requirements Elicitation sub-process has been carried out in Reference [
39]. In this work we focus on the Cyber Risk Assessment sub-process (
Section 3 and
Section 4) and on the Control Selection sub-process (
Section 5.1). The Security Architecture Design sub-process is the subject of future work.
5.1. Control Selection
This activity includes the initial selection of a set of minimum security controls to protect the system based on a set of criteria that take into account the security requirements; the cyber risks; the possible attacks; and the possibly already existing controls. This set will ensure baseline protection of the system; the baseline controls are the starting point for the design of the overall security architecture, which will derive from the application of tailoring to the set of security control baselines to account for peculiarities of the system and of the organization that owns or operates the system. In the sequel our approach for selecting the set of baseline controls is described.
A number of sources (e.g., Reference [
40,
41,
42]) provide sets of security controls from which a selection can be made. All of these sources pertain to information systems rather than cyber-physical systems; hence their applicability in the case under study is limited. However, Appendix G of the NISTGuide to Industrial Control Systems (ICS) Security [
43] provides the
ICS overlay, which is a partial tailoring of the controls and control baselines in Reference [
41,
42], which adds supplementary guidance specific to ICS. We will be using this source to select controls from, according to the following set of criteria, adapted from Reference [
44]:
- C1:
Kind of CPS that needs to be protected;
- C2:
Security aspects that need to be protected.
- C3:
Threats that need to be eliminated.
- C4:
Potential control alternatives.
- C5:
The value of the CPS to protect, according to its importance. This has been assessed within the process of attack path analysis, performed in Reference [
38].
- C6:
The likelihood of threat occurrence. This derives from the threat analysis performed within the risk assessment process of
Section 3 and
Section 4.
- C7:
Risk coverage provided by alternative controls.
As an example, the values of the control selection criteria for the spoofing threat against AIS are as follows:
- C1:
Navigational CPS;
- C2:
Integrity and availability. These are derived from the security requirements that have been established in Reference [
39].
- C3:
Spoofing/Tampering/DoS. These derive from the threat analysis results performed in Reference [
2] and in
Section 3 and
Section 4.
- C4:
Encryption/Tamperproof hardware.
- C5:
High. This has been assessed within the process of attack path analysis, performed in Reference [
38].
- C6:
Very likely. This derives from the threat analysis performed within the risk assessment process of
Section 3 and
Section 4.
- C7:
Low. No alternative controls are already in place.
and lead to selecting the IA-3 control category of Reference [
43]. An example of a control that belongs to this category is the establishment and use of an authentication infrastructure for such devices, such as, e.g., the one proposed in Reference [
45,
46].
5.2. Application to the Case of the AIS, the ECDIS, and the GMDSS
The results of the application of the process described above to the three most vulnerable on-board systems of the C-ES are shown in
Table 6,
Table 7 and
Table 8.
Table 9 depicts the consolidated controls per studied CPS.
Some of these controls are recommended for all systems (Device Identification and Authentication (IA-3), Cryptographic Protection (SC-13), Denial of Service Protection (SC-5), Physical Access Control (PE-3), Internal System Connections (CA-9)), whilst others are recommended for two or for only one of the studied systems. During the security architecture design phase, the controls identified for all systems will need to be re-considered, consolidated, checked for applicability in the specific environment, conformance to guidelines, compliance to standards etc.
As is typical with risk treatment strategies, the application of security controls does modify (reduce) the risk but does not eradicate it. To complete the risk treatment process one needs to assess the effectiveness of the applied controls, to consider the residual risk within the specific environmental and organizational context and to possibly repeat the process until the residual risk falls below the accepted risk level. This process can be effectively performed when the whole security architecture of the C-ES has been determined; accordingly, this is an item for future work.
One of the distinctive characteristics of CPSs is their ability to interconnect dynamically, sometimes to address scope beyond the originally intended one. This often results in emergent, hence unpredictable, behavior. In order to effectively secure CPSs in such situations, dynamic assessment of cyber risk is recommended. The proposed methodology, as it now stands, cannot capture such behavior. However, it can be extended, along the lines followed in Reference [
36].