Re-Keying Scheme Revisited: Security Model and Instantiations
Abstract
:1. Introduction
1.1. Background on Re-Keying Schemes
1.2. Our Contribution
1.3. Related Work
2. Preliminaries
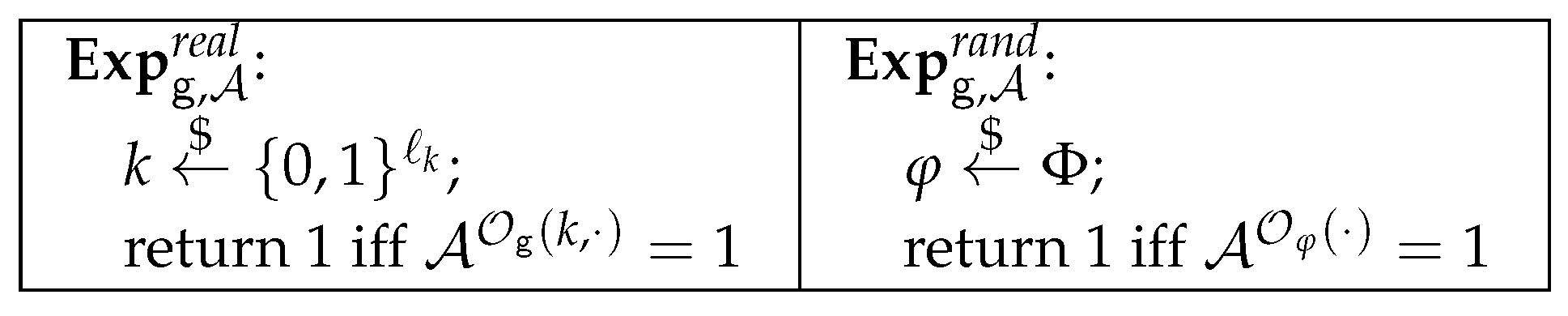
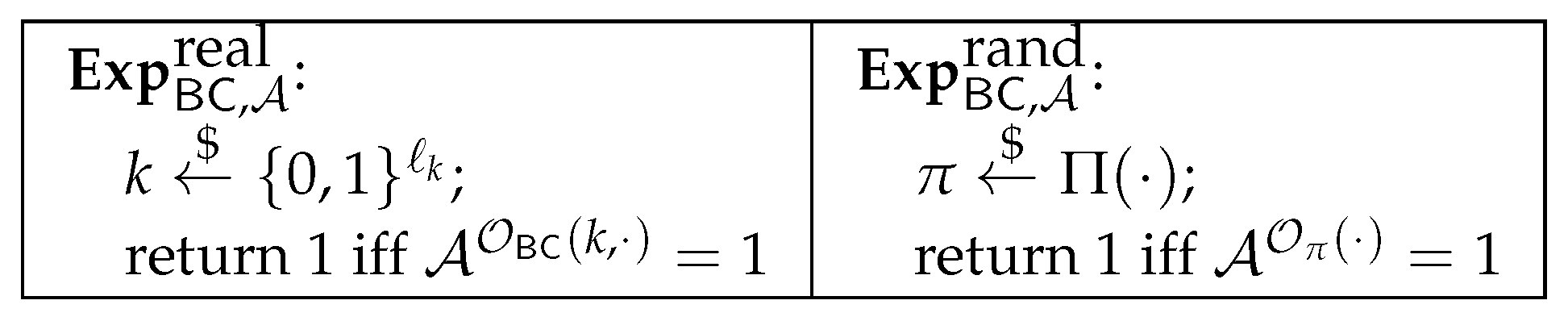
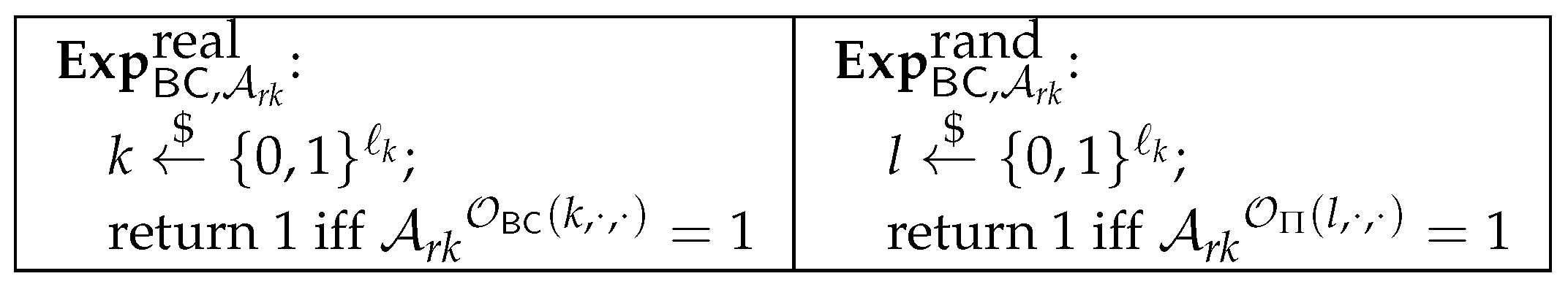
2.1. Block Cipher
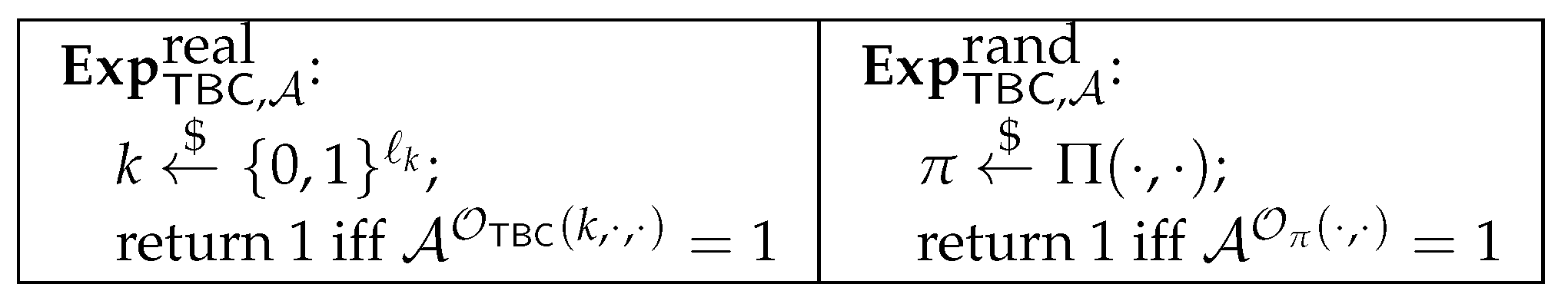
2.2. Tweakable Block Cipher
3. SCA on the Previous Re-Keying Schemes
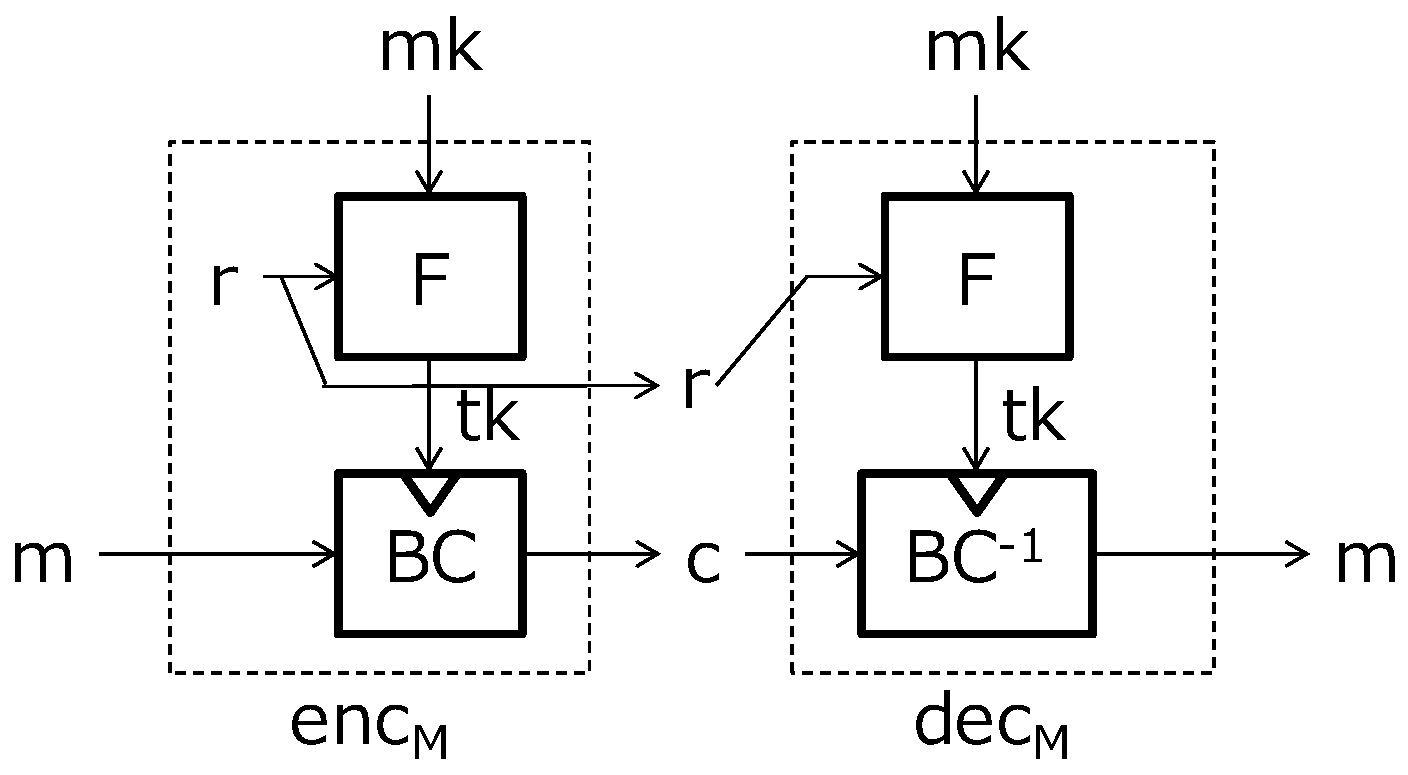
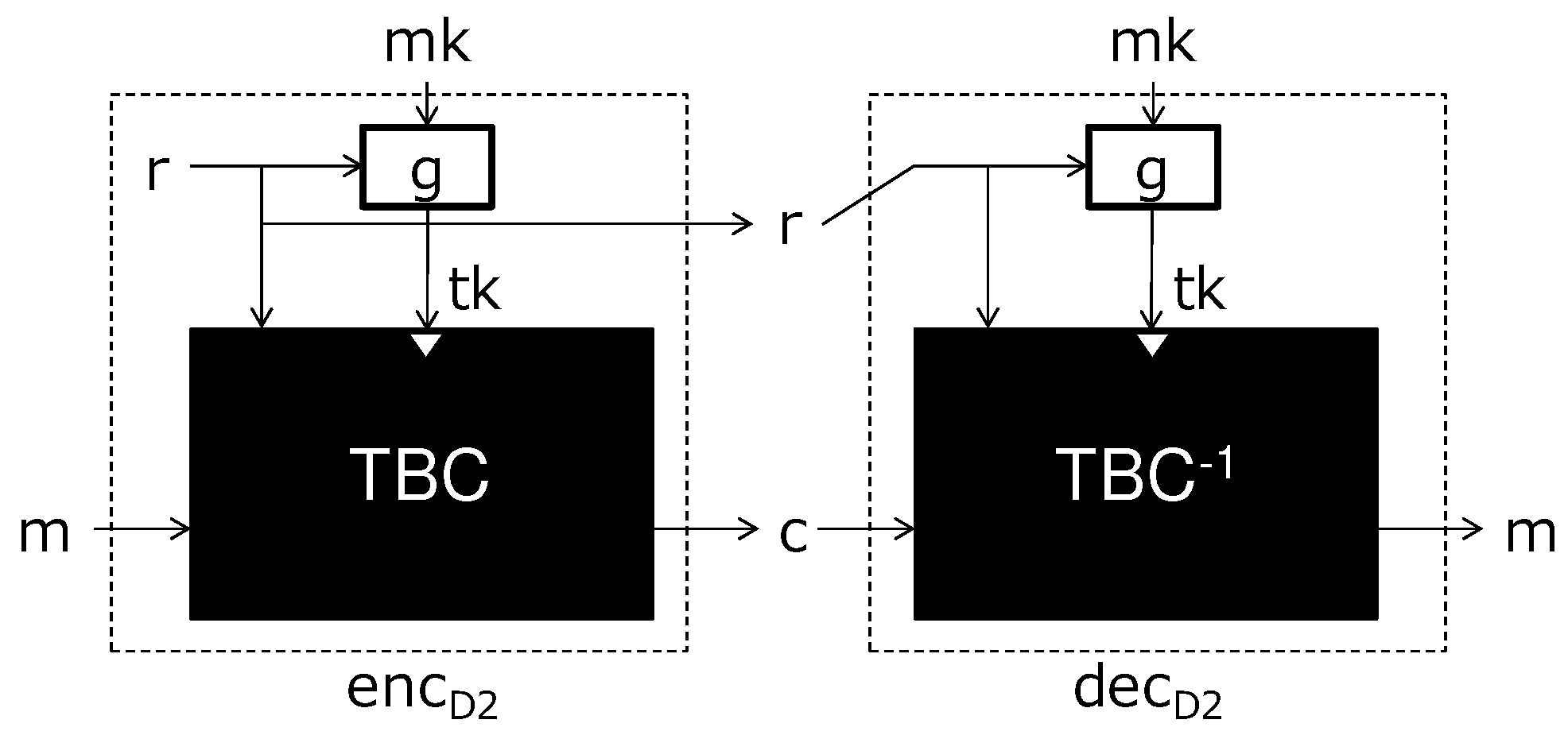
3.1. Previous Works
3.2. The Attacks
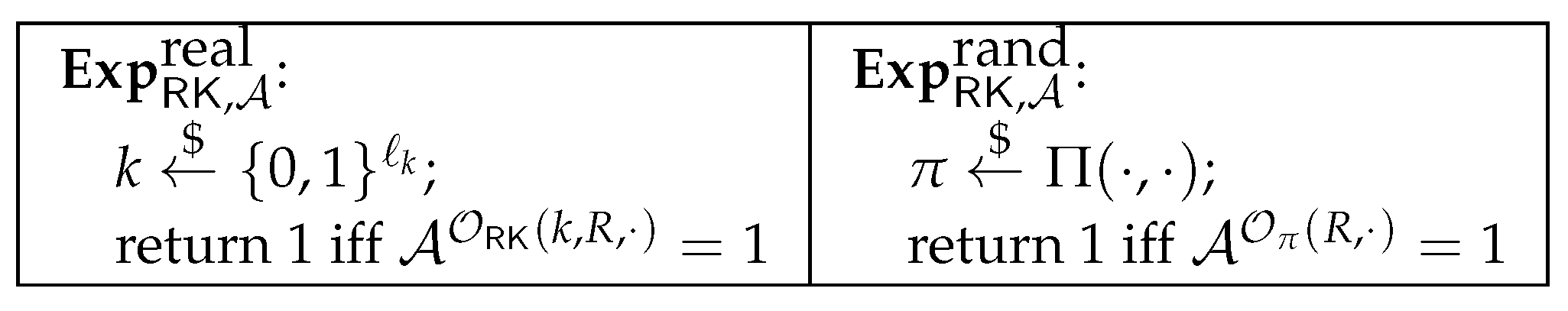
4. Security Model of the Re-Keying Scheme in Considering the SCA
5. New Concrete Re-Keying Schemes
5.1. Building Blocks
5.2. Our Concrete Schemes
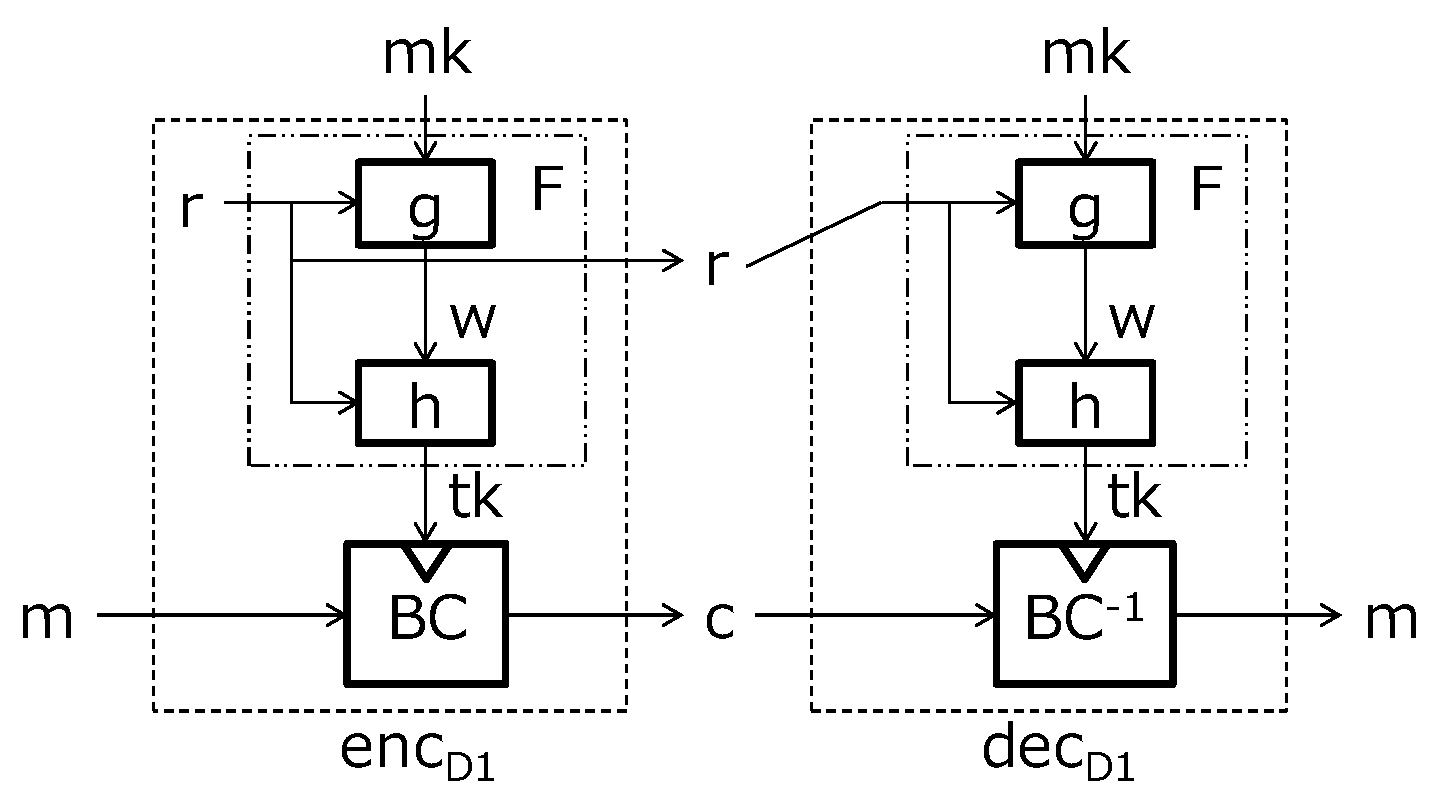
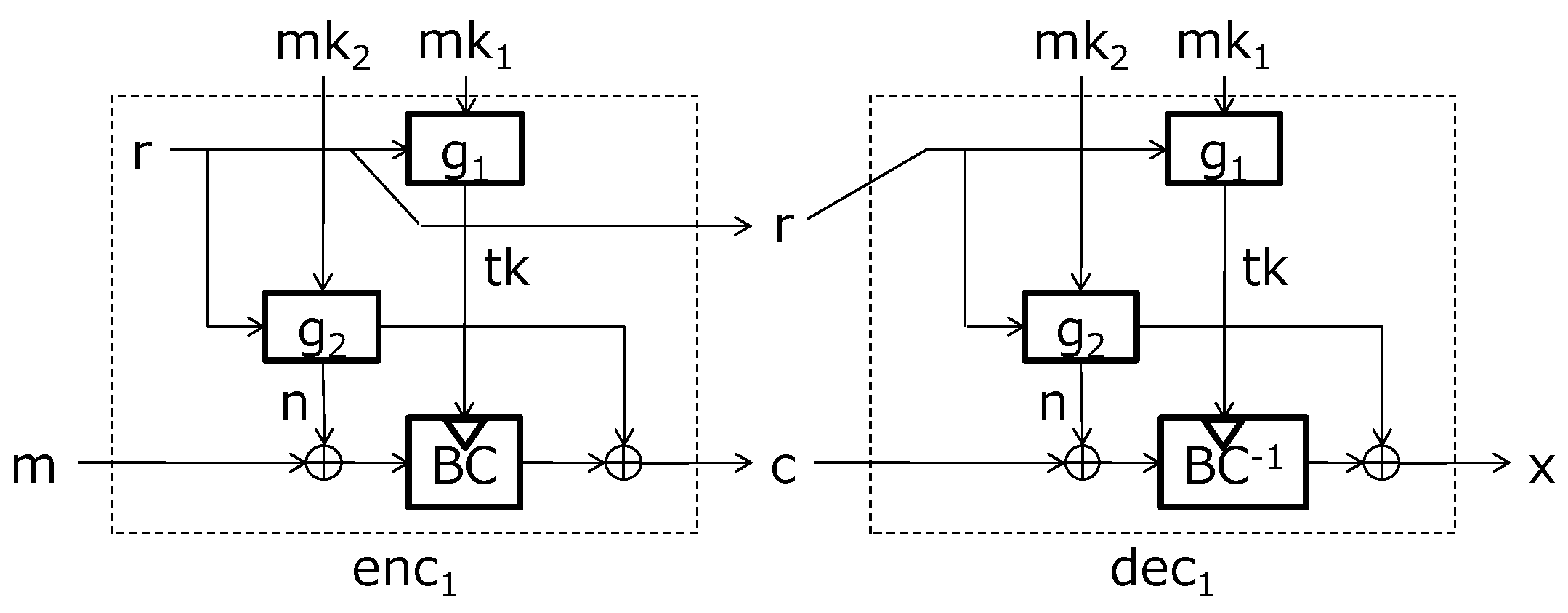
5.2.1. First-Order SCA-Resistant Re-Keying Scheme
| Algorithm 1 First-order SCA-resistant re-keying scheme: |
| Input: master secret key and plaintext m |
| Output: ciphertext |
| 1. Choose a randomness r |
| 2. Compute |
| 3. Compute |
| 4. Compute |
| 5. Return |
| Algorithm 2 First-order SCA-resistant re-keying scheme: |
| Input: master secret key and ciphertext |
| Output: plaintext m |
| 1. Compute |
| 2. Compute |
| 3. Compute |
| 4. return m |
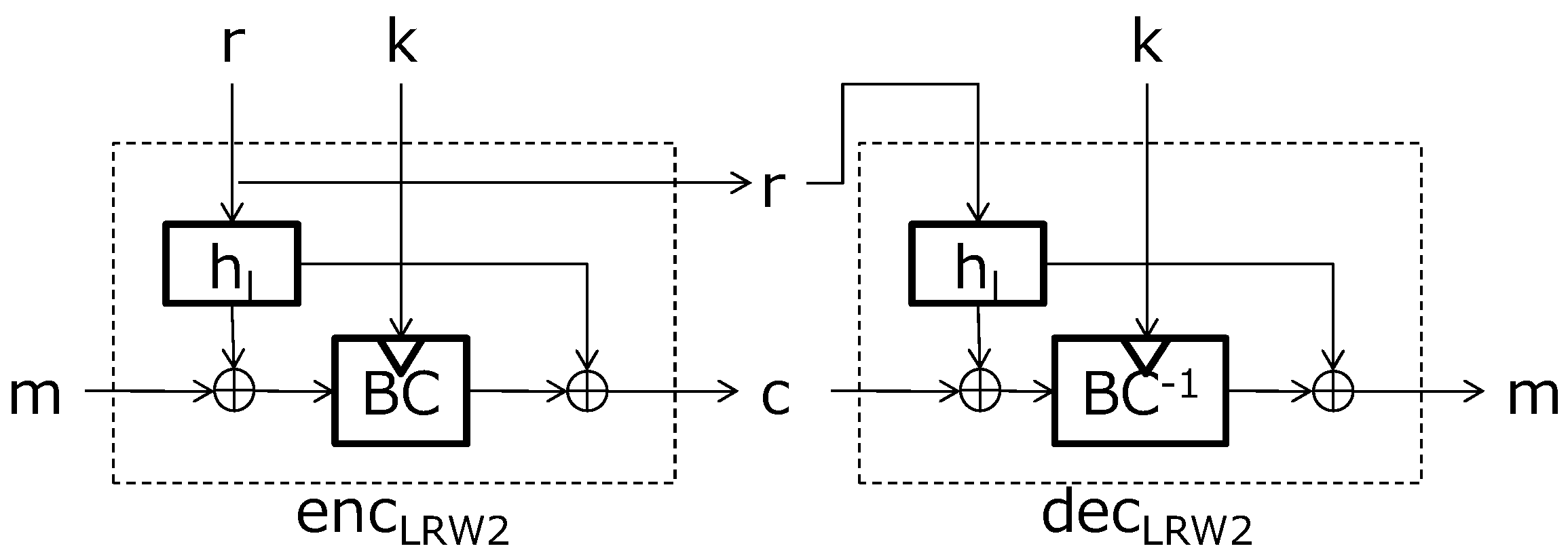
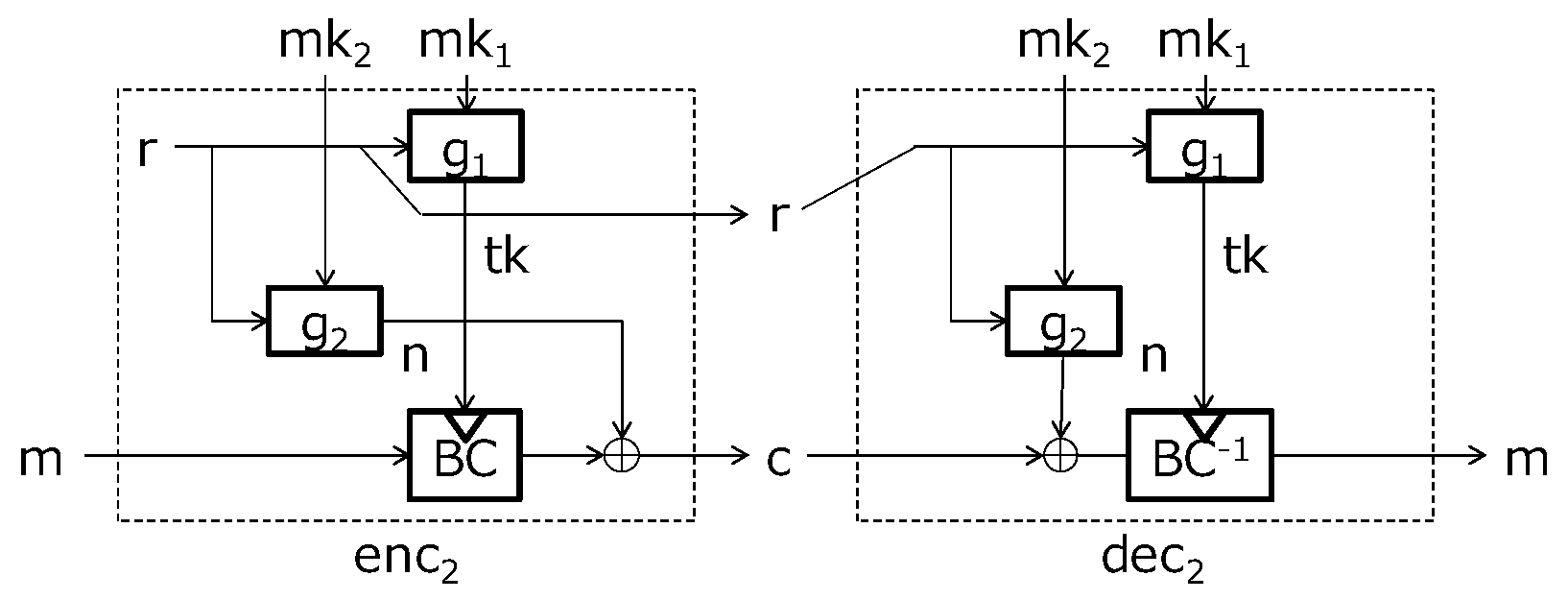
5.2.2. SCA-Resistant Re-Keying Encryption Scheme
| Algorithm 3 First-order SCA-resistant re-keying encryption scheme: |
| Input: master secret key and plaintext m |
| Output: ciphertext |
| 1. Choose a randomness r |
| 2. Compute |
| 3. Compute |
| 4. Compute |
| 5. Return |
| Algorithm 4 First-order SCA-resistant re-keying encryption scheme: |
| Input: master secret key and ciphertext |
| Output: plaintext m |
| 1. Compute |
| 2. Compute |
| 3. Compute |
| 4. Return m |
6. Security Considerations
6.1. Security of the SCA-Resistant Re-Keying Scheme
6.2. Security of the SCA-Resistant Re-Keying Encryption Scheme
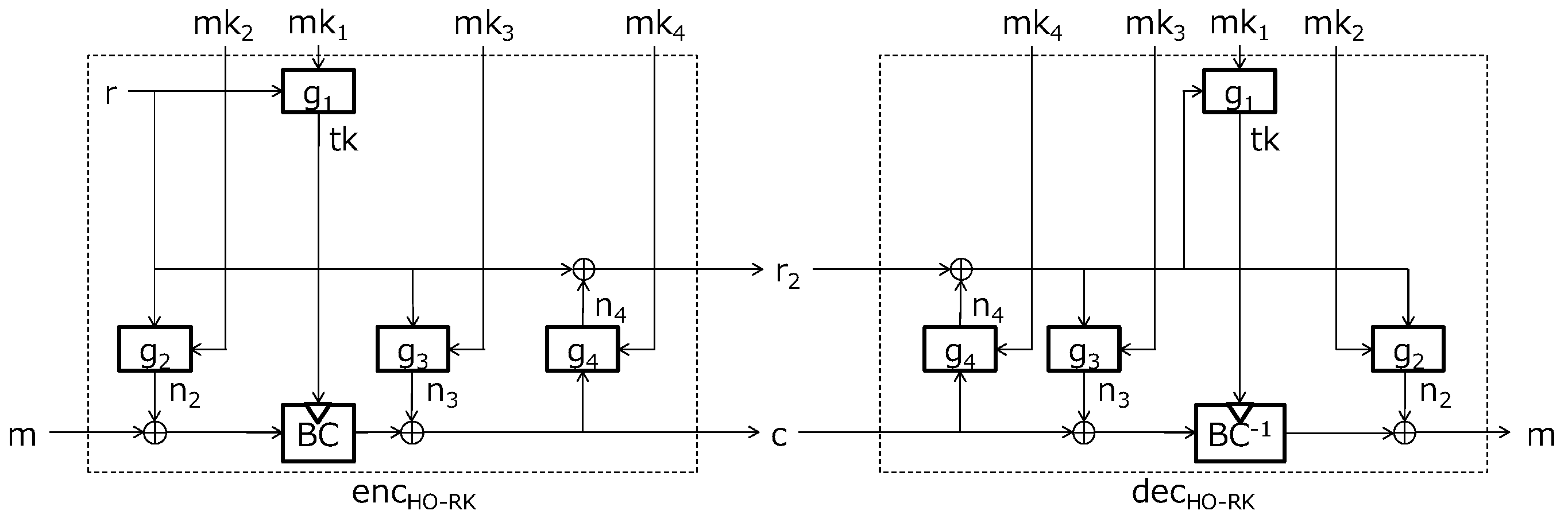
6.3. Toward the Higher Oder SCA-Resistant Schemes
| Algorithm 5 Higher order SCA-resistant re-keying encryption scheme: |
| Input: master secret key and plaintext m |
| Output: ciphertext |
| 1. Choose a randomness r |
| 2. Compute |
| 3. Compute |
| 4. Compute |
| 5. Compute |
| 6. Return |
| Algorithm 6 Higher-order SCA-resistant re-keying encryption scheme: |
| Input: master secret key and ciphertext |
| Output: plaintext m |
| 1. Compute |
| 2. Compute |
| 3. Compute |
| 4. Compute |
| 5. Return m |
7. Discussion
7.1. Application to Sensor Network Devices
7.2. Construction of g
8. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Kocher, P.C.; Jaffe, J.; Jun, B. Differential Power Analysis. In Advances in Cryptology, 19th Annual International Cryptology Conference, Santa Barbara, CA, USA, 15–19 August 1999; Wiener, M.J., Ed.; Lecture Notes in Computer Science; Springer: Cham, Switzerland, 1999; Volume 1666, pp. 388–397. [Google Scholar]
- Mangard, S.; Oswald, E.; Popp, T. Power Analysis Attacks: Revealing the Secrets of Smart Cards; Springer: Cham, Switzerland, 2007. [Google Scholar]
- Kocher, P.C. Leak-Resistant Cryptographic Indexed Key Update. U.S. Patent 6,539,092, 25 March 2003. [Google Scholar]
- Medwed, M.; Standaert, F.; Großschädl, J.; Regazzoni, F. Fresh Re-keying: Security against Side-Channel and Fault Attacks for Low-Cost Devices. In Progress in Cryptology, Proceedings of the Third International Conference on Cryptology in Africa, Stellenbosch, South Africa, 3–6 May 2010; Bernstein, D.J., Lange, T., Eds.; Lecture Notes in Computer Science; Springer: Cham, Switzerland, 2010; Volume 6055, pp. 233–244. [Google Scholar]
- Dobraunig, C.; Eichlseder, M.; Mangard, S.; Mendel, F. On the Security of Fresh Re-keying to Counteract Side-Channel and Fault Attacks. In Smart Card Research and Advanced Applications, Proceedings of the 13th International Conference, Paris, France, 5–7 November 2014; Joye, M., Moradi, A., Eds.; Lecture Notes in Computer Science; Springer: Cham, Switzerland, 2015; Volume 8968, pp. 233–244. [Google Scholar]
- Dobraunig, C.; Koeune, F.; Mangard, S.; Mendel, F.; Standaert, F. Towards Fresh and Hybrid Re-Keying Schemes with Beyond Birthday Security. In Smart Card Research and Advanced Applications, Proceedings of the 14th International Conference, CARDIS 2015, Bochum, Germany, 4–6 November 2015; Homma, N., Medwed, M., Eds.; Lecture Notes in Computer Science; Springer: Cham, Switzerland, 2016; Volume 9514, pp. 225–241. [Google Scholar]
- Coron, J.S.; Patarin, J.; Seurin, Y. The Random Oracle Model and the Ideal Cipher Model are Equivalent. In Proceedings of the Annual International Cryptology Conference, Santa Barbara, CA, USA, 17–21 August 2008. [Google Scholar]
- Liskov, M.; Rivest, R.L.; Wagner, D. Tweakable Block Ciphers. J. Cryptol. 2011, 24, 588–613. [Google Scholar] [CrossRef]
- Dziembowski, S.; Faust, S.; Herold, G.; Journault, A.; Masny, D.; Standaert, F. Towards Sound Fresh Re-keying with Hard (Physical) Learning Problems. In Advances in Cryptology-CRYPTO 2016, Proceedings of the 36th Annual International Cryptology Conference, Santa Barbara, CA, USA, 14–18 August 2016; Robshaw, M., Katz, J., Eds.; Lecture Notes in Computer Science; Springer: Cham, Switzerland, 2016; Volume 9815, pp. 272–301. [Google Scholar]
- Chittamuru, S.V.R.; Thakkar, I.G.; Bhat, V.; Pasricha, S. SOTERIA: Exploiting process variations to enhance hardware security with photonic NoC architectures. In Proceedings of the 55th Annual Design Automation Conference, DAC 2018, San Francisco, CA, USA, 24–29 June 2018; p. 81. [Google Scholar]
- National Institute of Standards and Technology (NIST). NIST Special Publication 800-38A: Recommendation for Block Cipher Modes of Operation: Methods and Techniques. 2001. Available online: https://csrc.nist.gov/publications/detail/sp/800-38a/final (accessed on 11 March 2019).
- Jean, J.; Nikolic, I.; Peyrin, T. Tweaks and Keys for Block Ciphers: The TWEAKEY Framework. In Advances in Cryptology-ASIACRYPT 2014, Proceedings of the 20th International Conference on the Theory and Application of Cryptology and Information Security, Kaoshiung, Taiwan, 7–11 December 2014; Sarkar, P., Iwata, T., Eds.; Lecture Notes in Computer Science; Springer: Cham, Switzerland, 2014; Volume 8874, pp. 274–288. [Google Scholar]
- National Institute of Standards and Technology (NIST). Federal Information Processing Standards Publication (FIPS) 197, Specification for the ADVANCED ENCRYPTION STANDARD (AES). 2001. Available online: https://csrc.nist.gov/publications/detail/fips/197/final (accessed on 11 March 2019).
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Komano, Y.; Hirose, S. Re-Keying Scheme Revisited: Security Model and Instantiations. Appl. Sci. 2019, 9, 1002. https://doi.org/10.3390/app9051002
Komano Y, Hirose S. Re-Keying Scheme Revisited: Security Model and Instantiations. Applied Sciences. 2019; 9(5):1002. https://doi.org/10.3390/app9051002
Chicago/Turabian StyleKomano, Yuichi, and Shoichi Hirose. 2019. "Re-Keying Scheme Revisited: Security Model and Instantiations" Applied Sciences 9, no. 5: 1002. https://doi.org/10.3390/app9051002
APA StyleKomano, Y., & Hirose, S. (2019). Re-Keying Scheme Revisited: Security Model and Instantiations. Applied Sciences, 9(5), 1002. https://doi.org/10.3390/app9051002




