A Static-loop-current Attack Against the Kirchhoff-Law-Johnson-Noise (KLJN) Secure Key Exchange System
Abstract
1. Introduction
1.1. On Secure Communications
1.1.1. Secure Key Exchange
1.1.2. Conditional Security
1.1.3. Unconditional (Information-Theoretic) Security
1.2. On the KLJN Secure Key Distribution
On Former Attacks Against the KLJN Secure Key Distribution
2. The New Attack Scheme Utilizing Deterministic Loop Currents
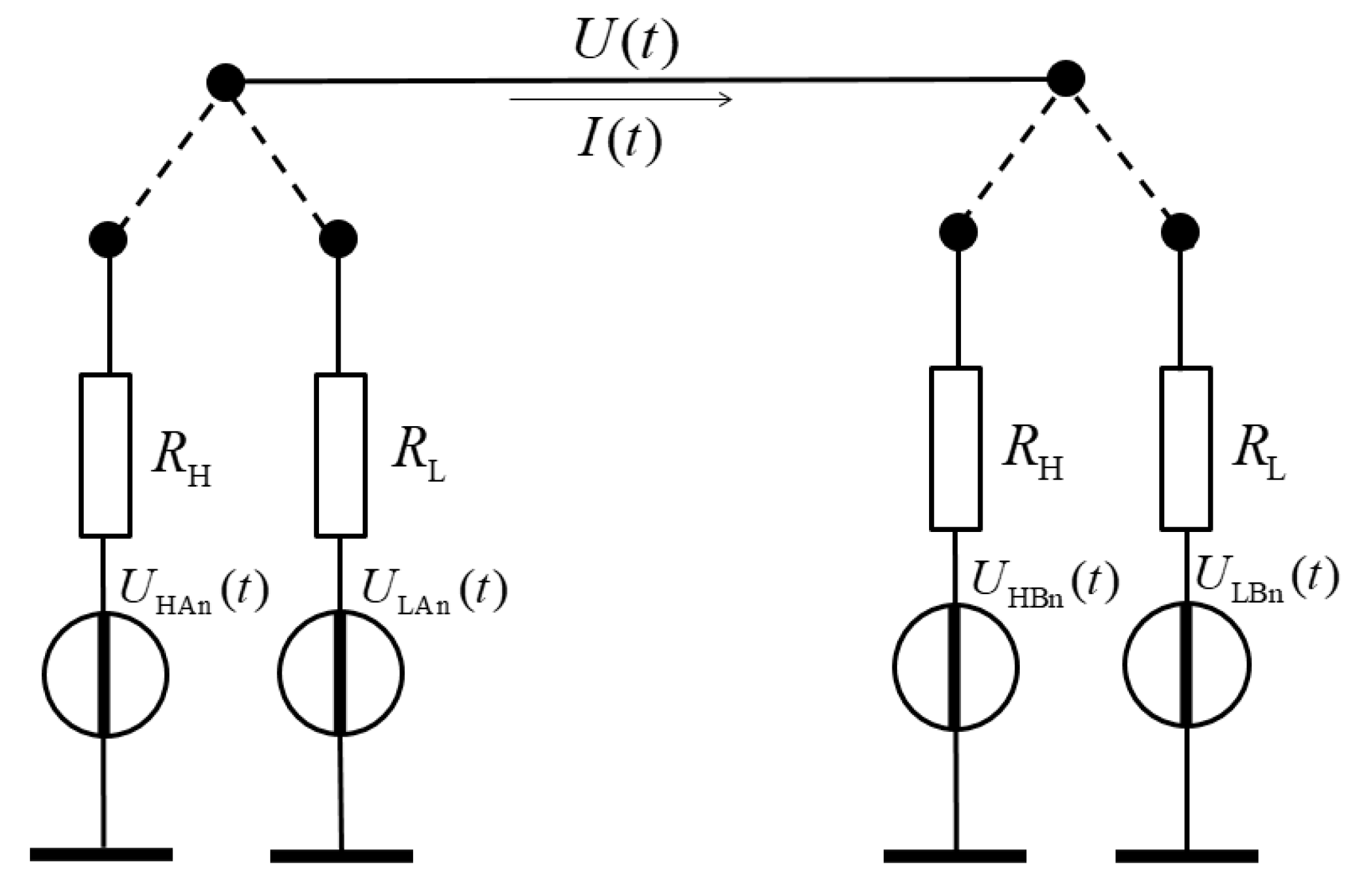
2.1. The Situation that Eve Utilizes for the Attack
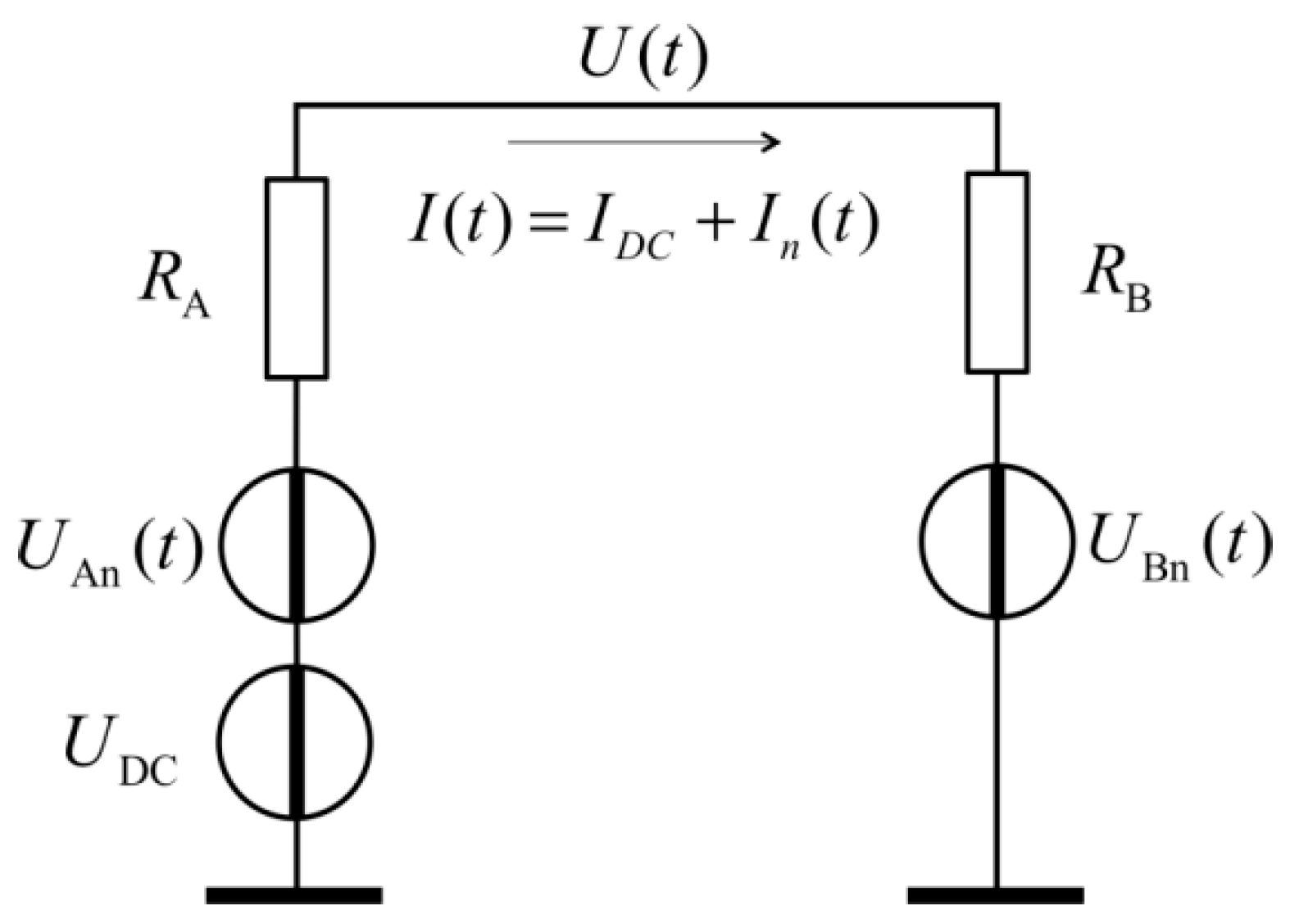
2.2. The Attack Scheme
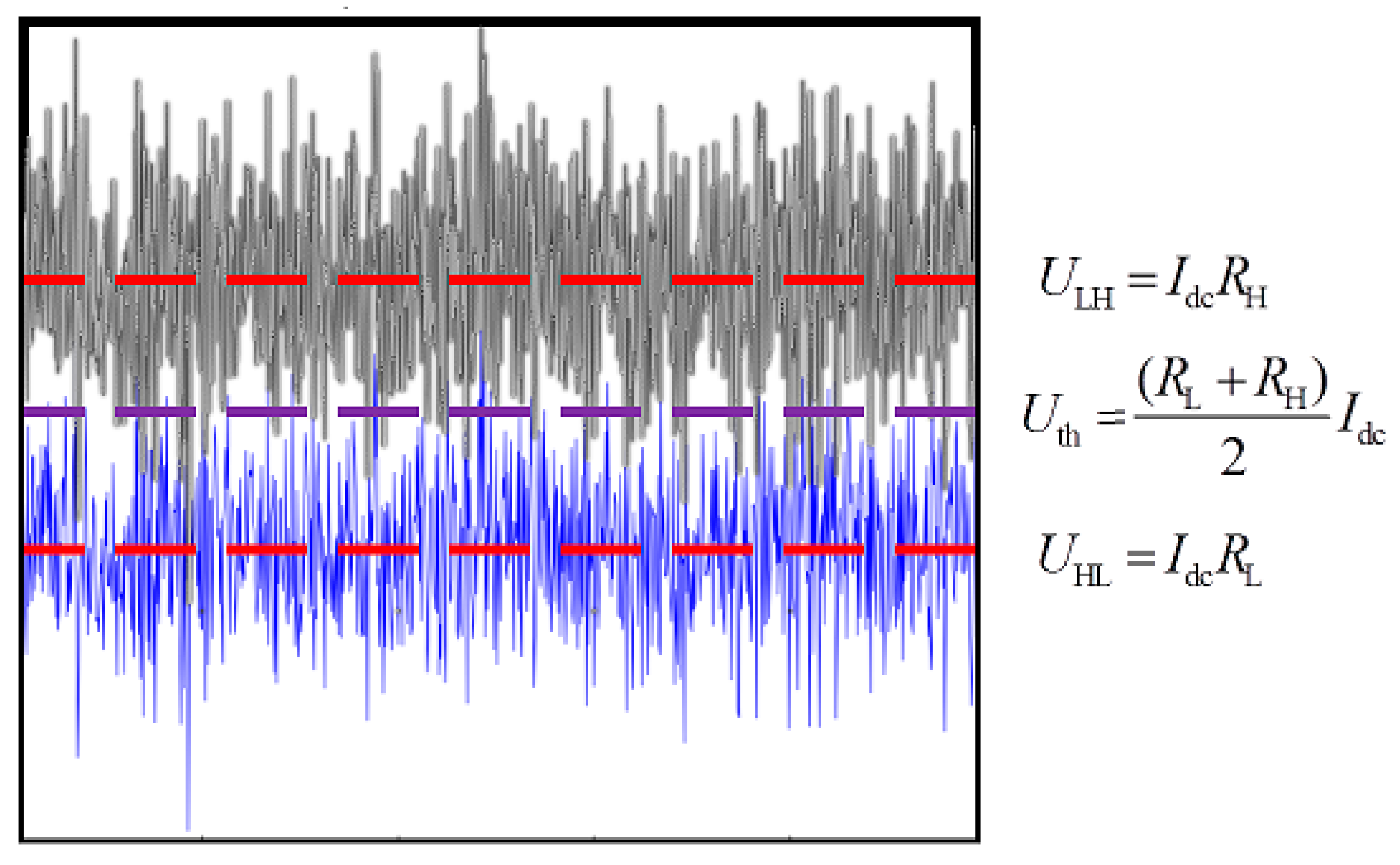
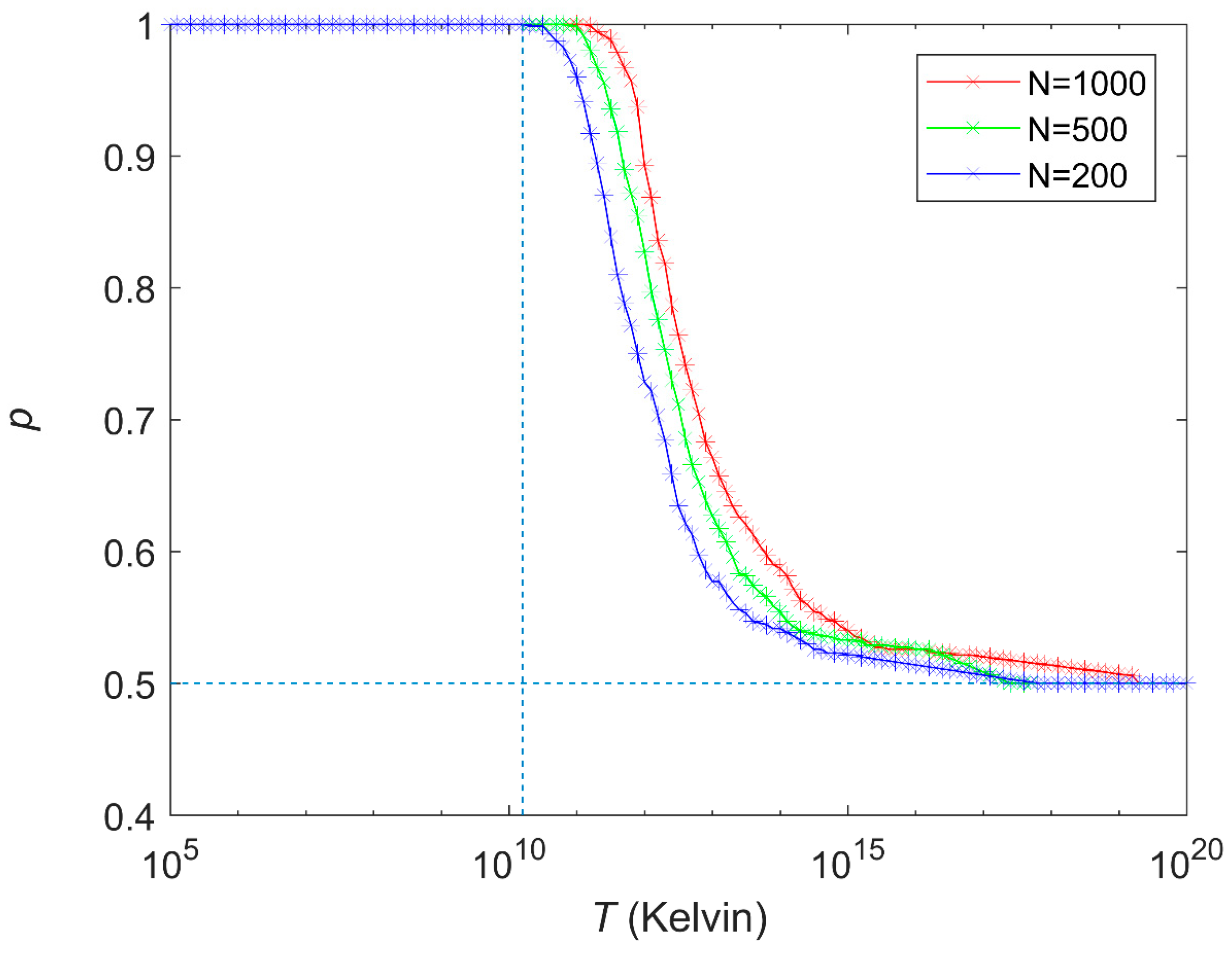
3. Simulation Results
4. Some of the Possible Defense Techniques Against the Attack
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Diffie, W.; Hellman, M. New Directions in Cryptography. IEEE Trans. Inf. Theory 1976, 22, 644–654. [Google Scholar] [CrossRef]
- Delfs, H.; Knebl, H. Introduction to Cryptography; Springer: Berlin/Heidelberg, Germany, 2002; Volume 2. [Google Scholar]
- Wiesner, S.J. Conjugate Coding. Sigact News 1983, 1, 78–88. [Google Scholar] [CrossRef]
- Bennett, C.H.; Brassard, G. Quantum cryptography: Public key distribution and coin tossing. Proc. IEEE Int. Conf. Comput. Syst. Signal Process. 1984, 175, 8. [Google Scholar] [CrossRef]
- Wootters, W.; Zurek, W. A Single Quantum Cannot be Cloned. Nature 1982, 299, 802–803. [Google Scholar] [CrossRef]
- Yuen, H. Security of quantum key distribution. IEEE Access 2016, 4, 724–749. [Google Scholar] [CrossRef]
- Makarov, V.; Bourgoin, J.P.; Chaiwongkhot, P.; Gagné, M.; Jennewein, T.; Kaiser, S.; Kashyap, R.; Legré, M.; Minshull, C.; Sajeed, S. Laser Damage Creates Backdoors in Quantum Communications. Technology 2015, 16, 22. [Google Scholar]
- Renner, R. Security of Quantum Key Distribution. Int. J. Quantum Inf. 2008, 6, 1–127. [Google Scholar] [CrossRef]
- Yuen, H.P. On the foundations of quantum key distribution—Reply to Renner and beyond. arXiv, 2012; arXiv:1210.2804. [Google Scholar]
- Hirota, O. Incompleteness and limit of quantum key distribution theory. arXiv, 2012; arXiv:1208.2106v2. [Google Scholar]
- Renner, R. Reply to recent scepticism about the foundations of quantum cryptography. arXiv, 2012; arXiv:1209.2423v.1. [Google Scholar]
- Yuen, H.P. Security significance of the trace distance criterion in quantum key distribution. arXiv, 2012; arXiv:1109.2675v3. [Google Scholar]
- Yuen, H.P. Unconditional security in quantum key distribution. arXiv, 2012; arXiv:1205.5065v2. [Google Scholar]
- Yuen, H.P. Key generation: Foundation and a new quantum approach. IEEE J. Sel. Top. Quantum Electron. 2009, 15, 1630–1645. [Google Scholar] [CrossRef]
- Merali, Z. Hackers blind quantum cryptographers. Nat. News 2009. [Google Scholar] [CrossRef]
- Gerhardt, I.; Liu, Q.; Lamas-Linares, A.; Skaar, J.; Kurtsiefer, C.; Makarov, V. Full-field implementation of a perfect eavesdropper on a quantum cryptography system. Nat. Commun. 2011, 2, 349. [Google Scholar] [CrossRef] [PubMed]
- Lydersen, L.; Wiechers, C.; Wittmann, C.; Elser, D.; Skaar, J.; Makarov, V. Hacking commercial quantum cryptography systems by tailored bright illumination. Nat. Photonics 2010, 4, 686–689. [Google Scholar] [CrossRef]
- Gerhardt, I.; Liu, Q.; Lamas-Linares, A.; Skaar, J.; Scarani, V.; Makarov, V.; Kurtsiefer, C. Experimentally faking the violation of Bell’s inequalities. Phys. Rev. Lett. 2011, 107, 170404. [Google Scholar] [CrossRef]
- Makarov, V.; Skaar, J. Faked states attack using detector efficiency mismatch on SARG04, phase-time, DPSK, and Ekert protocols. Quantum Inf. Comp. 2008, 8, 622–635. [Google Scholar]
- Wiechers, C.; Lydersen, L.; Wittmann, C.; Elser, D.; Skaar, J.; Marquardt, C.; Makarov, V.; Leuchs, G. After-gate attack on a quantum cryptosystem. New J. Phys. 2011, 13, 013043. [Google Scholar] [CrossRef]
- Lydersen, L.; Wiechers, C.; Wittmann, C.; Elser, D.; Skaar, J.; Makarov, V. Thermal blinding of gated detectors in quantum cryptography. Opt. Express 2010, 18, 27938–27954. [Google Scholar] [CrossRef]
- Jain, N.; Wittmann, C.; Lydersen, L.; Wiechers, C.; Elser, D.; Marquardt, C.; Makarov, V.; Leuchs, G. Device calibration impacts security of quantum key distribution. Phys. Rev. Lett. 2011, 107, 110501. [Google Scholar] [CrossRef] [PubMed]
- Lydersen, L.; Skaar, J.; Makarov, V. Tailored bright illumination attack on distributed-phase-reference protocols. J. Mod. Opt. 2011, 58, 680–685. [Google Scholar] [CrossRef]
- Lydersen, L.; Akhlaghi, M.K.; Majedi, A.H.; Skaar, J.; Makarov, V. Controlling a superconducting nanowire single-photon detector using tailored bright illumination. New J. Phys. 2011, 13, 113042. [Google Scholar] [CrossRef]
- Lydersen, L.; Makarov, V.; Skaar, J. Comment on Resilience of gated avalanche photodiodes against bright illumination attacks in quantum cryptography. Appl. Phys. Lett. 2011, 99, 196101. [Google Scholar] [CrossRef]
- Sauge, S.; Lydersen, L.; Anisimov, A.; Skaar, J.; Makarov, V. Controlling an actively-quenched single photon detector with bright light. Opt. Express 2011, 19, 23590–23600. [Google Scholar] [CrossRef] [PubMed]
- Lydersen, L.; Jain, N.; Wittmann, C.; Maroy, O.; Skaar, J.; Marquardt, C.; Makarov, V.; Leuchs, G. Superlinear threshold detectors in quantum cryptography. Phys. Rev. Lett. 2011, 84, 032320. [Google Scholar] [CrossRef]
- Lydersen, L.; Wiechers, C.; Wittmann, C.; Elser, D.; Skaar, J.; Makarov, V. Avoiding the blinding attack in QKD; Reply (Comment). Nat. Photonics 2010, 4, 801. [Google Scholar] [CrossRef]
- Makarov, V. Controlling passively quenched single photon detectors by bright light. New J. Phys. 2009, 11, 065003. [Google Scholar] [CrossRef]
- Kish Laszlo, B. Totally Secure Classical Communication Utilizing Johnson (-Like) Noise and Kirchhoff’s Law. Phys. Lett. A 2006, 352, 178–182. [Google Scholar] [CrossRef]
- Kish, L.B. Methods of Using Existing Wire Lines (power lines, phone lines, internet lines) for Totally Secure Classical Communication Utilizing Kirchhoff’s Law and Johnson-like Noise. arXiv, 2006; arXiv:physics/0610014. [Google Scholar]
- Gonzalez, E.; Kish, L.B.; Balog, R.; Enjeti, P. Information theoretically secure, enhanced Johnson noise based key distribution over the smart grid with switched filters. PLoS ONE 2013, 8, e70206. [Google Scholar] [CrossRef]
- Kish, L.B.; Entesari, K.; Granqvist, C.G.; Kwan, C. Unconditionally secure credit/debit card chip scheme and physical unclonable function. Fluct. Noise. Lett. 2017, 16, 1750002. [Google Scholar] [CrossRef]
- Kish, L.B.; Kwan, C. Physical Uncloneable Function Hardware Keys Utilizing Kirchhoff-Law-Johnson-Noise Secure Key Exchange and Noise-Based Logic. Fluct. Noise Lett. 2013, 12, 1350018. [Google Scholar] [CrossRef]
- Saez, Y.; Cao, X.; Kish, L.B.; Pesti, G. Securing Vehicle Communication Systems by the KLJN Key Exchange Protocol. Fluct. Noise Lett. 2014, 13, 1450020. [Google Scholar] [CrossRef]
- Cao, X.; Saez, Y.; Pesti, G.; Kish, L.B. On KLJN-based secure key distribution in vehicular communication networks. Fluct. Noise Lett. 2015, 14, 1550008. [Google Scholar] [CrossRef]
- Cho, A. Simple noise may stymie spies without quantum weirdness. Science 2005, 309, 2148. [Google Scholar] [CrossRef] [PubMed]
- Kish, L.B.; Scheuer, J. Noise in the Wire: The Real Impact of Wire Resistance for the Johnson (-Like) Noise Based Secure Communicator. Phys. Lett. A 2010, 374, 2140–2142. [Google Scholar] [CrossRef]
- Kish, L.B.; Granqvist, C.G. Elimination of a Second-Law-attack, and all cable-resistance-based attacks, in the Kirchhoff-law–Johnson-noise (KLJN) secure key exchange system. Entropy 2014, 16, 5223–5231. [Google Scholar] [CrossRef]
- Vadai, G.; Gingl, Z.; Mingesz, R. Generalized attack protection in the Kirchhoff-law–Johnson-noise secure key exchanger. IEEE Access 2016, 4, 1141–1147. [Google Scholar] [CrossRef]
- Hao, F. Kish’s key exchange scheme is insecure. IEEE Proc. Inf. Soc. 2006, 153, 141–142. [Google Scholar] [CrossRef]
- Kish, L.B. Response to Feng Hao’s paper Kish’s key exchange scheme is insecure. Fluct. Noise Lett. 2006, 6, C37–C41. [Google Scholar] [CrossRef]
- Vadai, G.; Gingl, Z.; Mingesz, R. Generalized Kirchhoff-law–Johnson-noise (KLJN) secure key exchange system using arbitrary resistors. Sci. Rep. 2015, 2015, 13653. [Google Scholar] [CrossRef] [PubMed]
- Chen, H.P.; Gonzalez, E.; Saez, Y.; Kish, L.B. Cable Capacitance Attack against the KLJN Secure Key Exchange. Information 2015, 6, 719–732. [Google Scholar] [CrossRef]
- Gunn, L.J.; Allison, A.; Abbott, D. A new transient attack on the Kish key distribution system. IEEE Access 2015, 3, 1640–1648. [Google Scholar] [CrossRef]
- Kish, L.B.; Granqvist, C.G. Comments on A New Transient Attack on the Kish Key Distribution System. Metrol. Meas. Syst. 2016, 23, 321–331. [Google Scholar] [CrossRef]
- Kish, L.B. Enhanced secure key exchange systems based on the Johnson-noise scheme. Metrol. Meas. Syst. 2013, 20, 191–204. [Google Scholar] [CrossRef]
- Kish, L.B.; Granqvist, C.G. Random-resistor–random-temperature Kirchhoff-law-Johnson-noise (RRRT-KLJN) key exchange. Metrol. Meas. Syst. 2016, 23, 3–11. [Google Scholar] [CrossRef]
- Chen, H.P.; Mohammad, M.; Kish, L.B. Current Injection Attack against the KLJN Secure Key Exchange. Metrol. Meas. Syst. 2016, 23, 173–181. [Google Scholar] [CrossRef]
- Kish, L.B. Protection against the Man-in-the-Middle-Attack for the Kirchhoff-Loop-Johnson (-Like)-Noise Cipher and Expansion by Voltage-Based Security. Fluct. Noise Lett. 2006, 6, L57–L63. [Google Scholar] [CrossRef]
- Kish, L.B.; Horvath, T. Notes on Recent Approaches Concerning the Kirchhoff-Law-Johnson-Noise-based Secure Key Exchange. Phys. Lett. A 2009, 373, 2858–2868. [Google Scholar] [CrossRef]
- Kish, L.B.; Abbott, D.; Granqvist, C.G. Critical analysis of the Bennett-Riedel attack on secure cryptographic key distributions via the Kirchhoff-law-Johnson-noise scheme. PLoS ONE 2013, 8, e81810. [Google Scholar] [CrossRef]
- Chen, H.P.; Kish, L.B.; Granqvist, C.G. On the Cracking Scheme in the Paper a Directional Coupler Attack against the Kish Key Distribution System by Gunn, Allison and Abbott. Metrol. Meas. Syst. 2014, 21, 389–400. [Google Scholar] [CrossRef]
- Chen, H.P.; Kish, L.B.; Granqvist, C.G.; Schmera, G. Do Electromagnetic Waves Exist in a Short Cable at Low Frequencies? What Does Physics Say? Fluct. Noise Lett. 2014, 13, 1450016. [Google Scholar] [CrossRef]
- Kish, L.B.; Gingl, Z.; Mingesz, R.; Vadai, G.; Smulko, J.; Granqvist, C.G. Analysis of an attenuator artifact in an experimental attack by Gunn-Allison-Abbott against the Kirchhoff-law-Johnson-noise (KLJN) secure key exchange system. Fluct. Noise Lett. 2015, 14, 1550011. [Google Scholar] [CrossRef]
- Kish, L.B. The Kish Cypher. The Story of KLJN for Unconditional Security. World Sci. 2017. [Google Scholar] [CrossRef]
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Melhem, M.Y.; Kish, L.B. A Static-loop-current Attack Against the Kirchhoff-Law-Johnson-Noise (KLJN) Secure Key Exchange System. Appl. Sci. 2019, 9, 666. https://doi.org/10.3390/app9040666
Melhem MY, Kish LB. A Static-loop-current Attack Against the Kirchhoff-Law-Johnson-Noise (KLJN) Secure Key Exchange System. Applied Sciences. 2019; 9(4):666. https://doi.org/10.3390/app9040666
Chicago/Turabian StyleMelhem, Mutaz Y., and Laszlo B. Kish. 2019. "A Static-loop-current Attack Against the Kirchhoff-Law-Johnson-Noise (KLJN) Secure Key Exchange System" Applied Sciences 9, no. 4: 666. https://doi.org/10.3390/app9040666
APA StyleMelhem, M. Y., & Kish, L. B. (2019). A Static-loop-current Attack Against the Kirchhoff-Law-Johnson-Noise (KLJN) Secure Key Exchange System. Applied Sciences, 9(4), 666. https://doi.org/10.3390/app9040666




