1. Introduction
With the growing threat of SCA (Side-Channel Attack, [
1,
2,
3,
4]), many countermeasures have been proposed accordingly, and the masking method has been one of the most promising power attack countermeasures for securely implementing block ciphers [
5,
6].
The basic principle of the masking methods is that if the sensitive variable (which depends on key material and some known information by definition) is split into some random shares and then is manipulated in a secure manner, the relationship between the behavior of internal variables and the corresponding side-channel information may look independent from the outside world. However, after the introduction of the glitch attack, there has been a lot of concern about the security of the masking method itself [
7,
8,
9].
The glitch attack primarily utilizes a specific hardware (HW) criterion, say, the glitch. More precisely, most of the HW-based masking schemes prior to the glitch attack were mainly based on the assumption that all gates’ input signals arrive at the gate simultaneously. However, that is not true in practice. That is, the gate delay and the variable path lengths are very common in semiconductor technologies, so each input signal arrives at a gate at different times. And, with this phenomenon in hand, the state of the gate’s output signal fluctuates within a clock cycle until it is finally stabilized at a certain value, which is called a glitch. In particular, the glitch phenomenon highly affects the amount of electrical power consumed by the circuit, and, moreover, the consumed power is highly related to the circuit’s input. The glitch attack analyzes this relationship to retrieve some secret information in cryptographic devices. Unfortunately, most masking schemes prior to the glitch attack have been shown to possess some inherent vulnerabilities to the attack.
To mitigate the devastating effect of the glitch attack, the authors in [
10,
11,
12,
13] introduced the concept of TI (Threshold Implementation), which is based on the techniques of secret-sharing and multi-party computation and is believed to be provably secure against a first-order differential power attack (DPA). Basically, TI is a Boolean masking scheme which satisfies three specific properties, say, correctness, non-completeness, and uniformness. The correctness implies that the (Boolean) sum of the output shares is equal to the original output. And, the (
-th order) non-completeness means that processing any combination of up to
output masks altogether does not require at least one input share. The uniformness requires that the output distribution is preserved when a function is implemented in a shared form. The exact definition of these three properties is given in the next section. The most important characteristic of TI is that (first-order) TI is provably secure against the 1st-order differential power attack even in the presence of glitches [
11].
As another glitch attack countermeasure, the authors in [
14] proposed a new kind of gates, say, G-equivariant gates. Simply speaking, the G-equivariant gate is the gate, the toggling count of whose output is independent with the arrival order of the gate’s input signals. After all, the independency is believed to successfully prevent the 1st-order side-channel DPA regardless of the arrival order of the input signals. However, it was also shown in [
14] that there are no G-equivariant gates which have two input shares and the XOR sum in which two output shares is equal to the logical AND evaluation of its original inputs.
Contribution of this paper. As noted before, the most notable characteristic of TI is that it is provably secure against the 1st-order DPA even in the presence of glitches. And, the main concern of this paper lies at the security proof itself. That is, we re-investigate the proof that TI is secure against the 1st-order DPA even in the presence of glitches, and conclude that the proof has some missing points. To remedy it, we then propose to utilize the concept of G-equivariance. More precisely, while the original concept of G-equivariance is defined for 2-share masking setting, we use the extended notion of G-equivariance to an arbitrary number of shares and prove that the non-complete masked circuit is actually G-equivariant, which, in turn, implies that any non-complete TI can successfully prevent the glitch attack. Finally, we show that there are some G-equivariant gates that are not non-complete; thus, the notion of G-equivariance is broader than that of non-completeness. Consequently, the contribution of this paper is three-fold. First, we review the proof in [
14] that any non-complete TI with uniform input sharing is secure against the 1st order DPA even in the presence of glitches and claim that the proof is not satisfactory by introducing a contradictory example. Next, extending the definition of G-equivariance, this paper proves that non-completeness implies G-equivariance, which fills the gap in the security proof in [
14]. Finally, we give some exemplary gates which are not non-complete but are G-equivariant.
The paper is organized as follows. In
Section 2, we review some prerequisite knowledge for our subsequent discussions. In
Section 3, we show why the proof that non-completeness guarantees the 1st-order DPA-resistance is not satisfactory. Then, in the next section, we will prove that non-completeness implies G-equivariance and give some examples that are G-equivariant without being non-complete. The conclusion is given in
Section 5.
2. Prerequisite
2.1. Notation
In this paper, small letters (possibly with superscripts) stand for elements of finite fields or functions over finite fields and small letters (possibly with superscripts) with subscripts are used for denoting a component element of a finite field element (when the finite field is considered as a vector space over a base field), a component function of a vectorial function, or an input parameter of a multivariate function. For example, can be written as for . The -th order mask of (which will more precisely be defined later) is denoted as for .
2.2. Masking Method
Power attack, which was first introduced by P. Kocher et al. can retrieve sensitive information in cryptographic devices using devices’ power consumption patterns ([
2]). Various techniques were introduced as power attack countermeasures, among which the masking method is representative for securely implementing, for example, block ciphers against DPA(differential power attack).
To apply the (Boolean) masking method to a function one should first determine the input masking order and the output masking order and then should take the following procedure: for given ,
- (1)
Randomly choose
- (2)
Compute , where denotes the bitwise eXclusive-OR operation.
- (3)
From , compute with in the manner that any information about the original input is not leaked during the computation.
The procedure above is usually called the -order masking scheme for and, if , it is also called the -th order masking scheme. The vector is called the -th order mask (or, sharing) of or the -th order input mask of and each is called a share of . Similarly, is called the -th order mask of or the -th order output mask of , and each is called a share of . Importantly, the quantities and are closely related to the effort an attacker has to pay to break the masking scheme. For example, to successfully recover a key from the masking scheme with -th input order, it is believed that an attacker needs to observe at least individual shares or statistical moments.
The function computing the output mask given the input mask is denoted as and is called a shared implementation of thus for each .
Devising a masking scheme for linear or affine functions is known to be an easy task. For example, if
is linear (with respect to
) and
, then
thus letting
gives a well-established masking scheme for
. However, designing a masking scheme for non-linear functions, such as block ciphers’ S-box, is non-trivial, and the gate-level masking method was introduced to address this issue, especially in the hardware masking scheme design [
15].
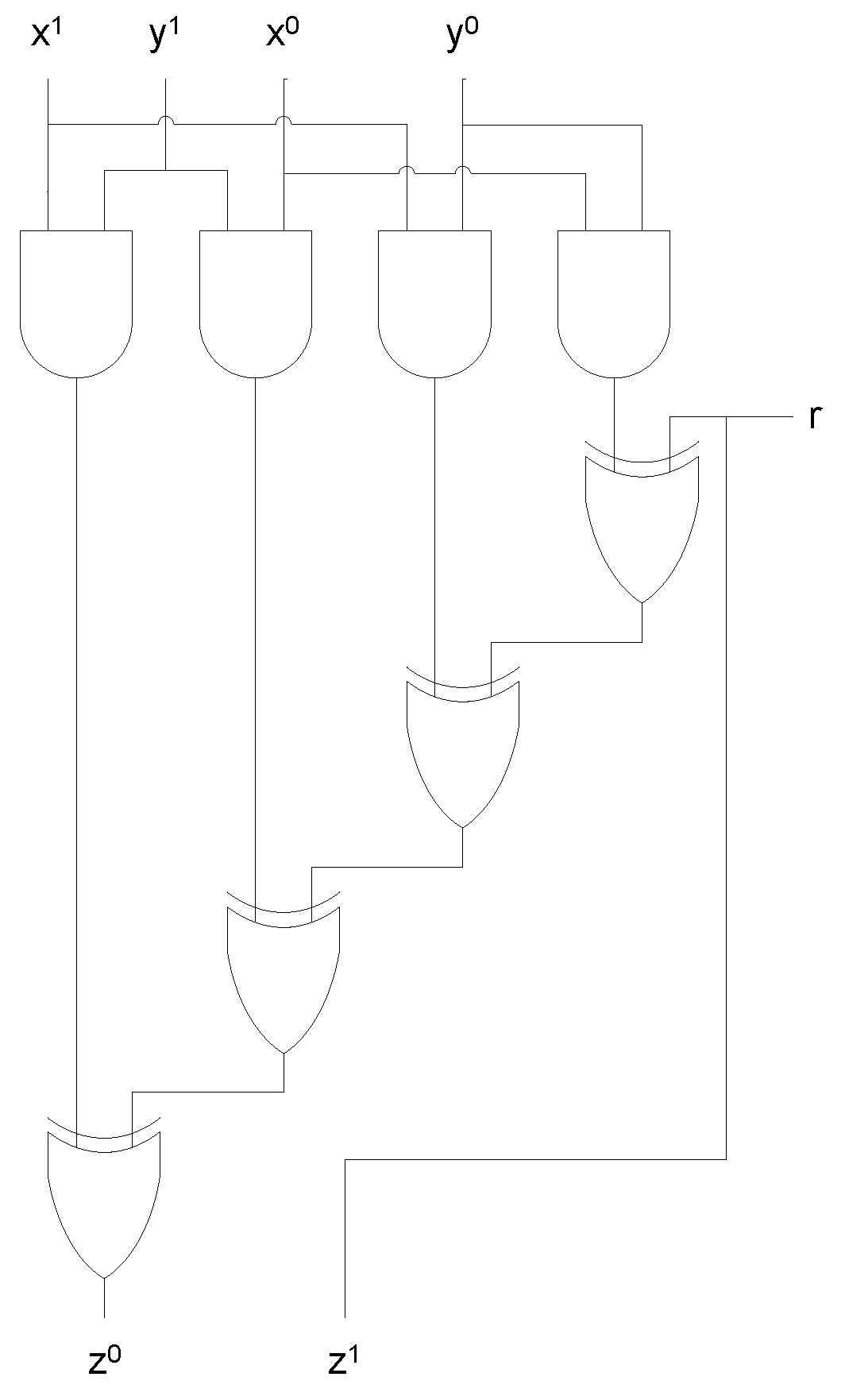
The idea of the gate-level masking method is very simple: after decomposing any function (or circuit) into basic gates, like AND, XOR and so on, and individually applying an appropriate masking scheme to the corresponding basic gates, the resulting circuit will serve as the masking scheme for the original function. Especially, since AND, OR, NAND, and NOR gates are the only non-linear basic gates, and OR, NAND, and NOR gates can be constructed with the composition of AND, XOR, and NOT gates; the main research of the gate-level masking method focuses on how to apply the masking method to the AND gate. For example,
Figure 1 shows the masking scheme for the 2-input AND gate proposed by E. Trichina [
15], which can be mathematically described as: for a random bit
,
2.3. Glitch Attack and Countermeasures
Most of the previous gate level masking methods prior to the glitch attack implicitly or explicitly assumed that all input signals of any gate arrive at the gate simultaneously. However, the idealized assumption is shown not to hold in practice. That is, due to the gate delay and the variable path lengths, which are very common in the semiconductor technology, each input signal arrives at the gate at different times. Moreover, eliminating such the arrival time variation is known to be a hard task, especially for CMOS, the most widely used semiconductor technology. And, when input signals get to a gate at a different time, the state of the gate’s output signal fluctuates within a clock cycle until it is finally stabilized at a certain value. This phenomenon is called the glitch or the hazard.
The glitch phenomenon highly affects the amount of electrical power consumed by circuits. Moreover, the amount of consumed power is highly related to the circuit’s input. And, the power analysis attack which analyzes the relationship between the glitch phenomenon and the power consumption pattern is called the glitch attack [
7,
8,
9]. Unfortunately, many gate-level masking schemes are known to be vulnerable to the glitch attack. Various countermeasures have been proposed since the glitch attack was introduced, and this paper focuses on the G-equivariant gates [
14] and the threshold implementation [
10,
11,
12,
13].
The notion of G-equivariant gates relies on the belief that if a (averaged) toggling count of the gate’s output is constant regardless of the arrival order of the gate input signals [
14], the gate’s power consumption pattern will not be influenced by the glitch phenomenon so that the glitch attack can be prevented. Unfortunately, as noted in [
14], there are no 2-share G-equivariant gates in which the XOR sum gives rise to the AND-gate evaluation of the original input values. More precisely, there are no G-equivariant gates
satisfying
To remedy this undesirable situation, the authors introduced the concept of semi-G-equivariance with the weakened condition that, in the Equation (2), arrives at the gate at the same time and arrives at the gate simultaneously. However, even though there are some semi-G-equivariant gates that are available for glitch-attack-resistantly constructing the AND gate, there have been some doubts about the appropriateness of such weakened conditions.
TI (Threshold Implementation, [
10,
11,
12,
13]) was proposed as another glitch attack countermeasure and is said to be provably secure even in the presence of glitches. TI is defined to be a masking scheme satisfying three specific properties: correctness, non-completeness, and uniformness. Given a function
, the shared implementation
of
is said to be correct if
for any mask
of
. And
is defined to be
-th order non-complete if any processing of up to
component functions
does not require at least one input share. Thus, for example, the following
is the first-order non-complete shared implementation of the AND gate: for
,
That is, for and the computation of does not involve nor for each .
Finally, the shared implementation
of
is said to be uniform if, for any output mask
, the probability that
for all
is constant if
is fixed. For example, the following shared implementation of the AND gate is uniform as
Table 1 shows: for random bits
and
,
3. Non-Completeness Implies 1st-Order DPA Security?
As stated in
Section 2, Threshold Implementation is known to be provably secure against the 1st-order differential power attack even in the presence of glitches, and it is usually referenced that the corresponding security proof is given in Theorem 2 and Corollary 1 of [
11]. Unfortunately, as indicated below, the proof is not satisfactory in the sense that there is a counter-example of not being secure against the glitch attack while satisfying the condition presented in [
11]. For easy reference, here, we re-state the theorem.
Theorem 1 (same with Theorem 2 in [
11])
. For a shared implementation of , if the input shares are uniform and is correct and non-complete, then each output share is statistically independent of the original input and the original output . And, the same holds for any intermediate result that is appearing during the computation of and for any physical quantities like power consumption, electro-magnetic radiation, etc., which are a function of these intermediate results. Note that the original theorem in [
11] was stated for the multi-input and multi-output function, while Theorem 1 above assumes that
has a single input and single output. However, the difference does not affect the validity of the argument below.
In [
11], for proving the theorem above, the authors showed that, for any variable
appearing in the computation of
and any input
of
,
Clearly, the Equation (5) implies that
and
are statistically independent. And then, [
11] presented the following corollary:
Corollary 1 ([
11])
. For a shared implementation of , if the input shares are uniform and is correct and non-complete, then the expected value of the power consumption of a circuit implementing is independent of and , even in the presence of glitches or the delayed arrival of some inputs. Now, in proving the corollary above, the authors of [
11] stated that “Since the proof of Theorem 2 makes no assumption on the behavior of the circuit and/or the presence of glitches, the theorem holds for each sub-circuit computing one of the
, also in the case of delayed inputs or glitches. Furthermore, the mean power consumption of the whole circuit is the sum of the mean power consumptions of the sub-circuits and expectation is a linear operation” [
11]. After all, [
11] used the argument that, if all the intermediate variables of the shared circuit are statistically independent of the input and the output, the shared implementation is secure against the 1st-order DPA even in the presence of a glitch. However, this argument is not true, in general. That is, there are some shared circuits whose intermediate variables are statistically independent of the input and the output, but that are not secure against the glitch attack. For example, consider the masking scheme by Trichina described in
Figure 1. First, it can be proved that all the intermediate results of the scheme, say,
,
are statistically independent of the original input and output. More precisely, for any
if
,
, then
, while if
, then
.
Similarly, we can prove that
for any
and
,
}. Thus, the presupposition of Corollary 1 is satisfied for the Trichina’s scheme; however, the scheme is also known to be susceptible to the glitch attack [
7,
8,
9], which contradicts the conclusion of Corollary 1.
Remark 1. We note that the security guarantee of TI given in [11] is against the 1st-order univariate DPA. Thus, the attackers are assumed to be able to utilize only the mean value of power traces gathered at a specific time moment. And, the attackers who rely on the variance value of gathered power traces or power traces gathered at several time moments are called the higher-order DPA attackers, and [11] and this paper do not consider such attackers. At this point, it is emphasized that we do not claim that the non-complete TI with uniform inputs has some power attack weaknesses. Actually, the non-complete TI is shown to be very secure in various leakage detection tests [
10,
11,
12,
13]. Thus, it is plausible that TI gives a lot of resistance to DPA, even in the presence of glitches. However, as the previous argument shows, it is not clear why it gives such security from a theoretical viewpoint. After all, the problem is that [
11] does not contain any theoretical explanation of how we can mitigate the glitch effect. And, as will be explained in the next section, the G-equivariance [
14] gives a useful instrument for how to mitigate such an effect. However, G-equivariance also has its own drawbacks. Most notably, there are no (1st-order) G-equivariant gates, the XOR sum in which the output gives rise to the ordinary 2-input AND gate evaluation, and that is why we should use the extended concept of G-equivariance to the higher-order setting in [
16]. More details can be found in
Section 4.
4. Non-Completeness Implies G-Equivariance
To solve the problem discussed in the previous section, we use the extended concept of the G-equivariance in [
16].
Originally, the G-equivariance was introduced as a glitch attack countermeasure, and a gate (or a function) is defined to be G-equivariant if the energy consumption of the gate is independent of the arrival order of input signals [
14]. However, as paper [
14] indicated, there are no G-equivariant gates in which the Boolean sum is equal to the 2-input AND gate evaluation, and the authors loosened the condition imposed on the G-equivariance to get the semi-G-equivariance. The semi-G-equivariance (the exact definition of which can be found in [
14]) requires the energy consumption of a gate to be independent of the order of input signals with the constraint that some signals should arrive at the gate simultaneously, and [
14] proved that there are some semi-G-equivariant gates that summed up to give the 2-input AND gate. For example, the gates
with
have the property that they are semi-G-equivariant, that is, their energy consumption is independent of the arrival order of input signals if
and
arrive at
or
at the same time and
and
arrive at
or
simultaneously, and
. However, there is a critical problem with semi-G-equivariant gates. It is not easy to satisfy the condition imposed on the gates. That is, for example, it is very hard to make
(and
and
as well) in (6) arrive at
or
at the same time. The custom design process may solve the issue; however, with a high cost.
The G-equivariance and semi-G-equivariance in [
14] were basically defined in the 1st-order setting. More precisely, any input signal
of a gate is assumed to be decomposed as
with
. However, there is no justification for why the input signals for the G-equivariant gate should have such form. And, using the extended notion of G-equivariance to the higher-order setting in [
16], this paper assumes that every signal
is represented as
with
for a given positive integer
.
In the subsequent, a gate with inputs and 1 output is considered as a Boolean function , where stands for the binary finite field with addition operation , and is an extension field of degree over , which can be considered as an -dimensional vector space over For a positive integer , we denote as the set of all mappings from the set into itself.
Definition 1 ([
14,
16])
. Given a positive integer , a gate and , the partial energy function is defined aswherestands for the 4-dimensional real vector space with the basisand, for, and in (7) is defined by: and In Definition 1, the basis vectors of can actually be interpreted as the amount of power consumed while changes or holds its output. That is, when the output of changes from 0 to 1, it is assumed that consumes the energy , while is assumed to consume the energy , if changes its output from 1 to 0. And, when the output bit of is fixed at 0 or 1, is assumed to consume the energy or , respectively. Also, in the definition, was introduced to describe the arrival order of the gate’s input signal. Thus, for example, in (8) implies that the -th input signal arrives at the -th order.
Since we are primarily interested in masking a 2-input AND gate, all the gates in the subsequent are assumed to have 2 inputs.
Definition 2 ([
14,
16])
. For a positive integer and any input of a gate , the tuple is called a -th order masked signal of if- (1)
and
- (2)
for any
- (3)
For any,andare statistically independent, considered as random variables.
Definition 3 ([
14,
16])
. A -th order masked gate of a gate is the tuple satisfying the following:- (1)
- (2)
For any inputofand any-th order masked signalof, we havefor.
In this case, each of the -th order masked gate is called a -th order component masked gate of .
Definition 4 ([
14,
16])
. Given a -th order masked gate of a gate , a -th order component masked gate, say is-th order G-equivariant if for any and the expectation value is independent of any choice of -th order masked signals of and of In the sequel, a -th order G-equivariant component masked gate is briefly called as a G-equivariant gate, if there is no confusion.
Lemma 1 ([
14,
16])
. Given a -th order masked gate of a gate , a -th order component masked gate, say is -th order G-equivariant if and only if, for any and the following 16 values are equal for any choice :where and . Finally, we are at the moment when we can prove that non-completeness implies G-equivariance. However, since the provable security is believed to hold for TI satisfying the first-order non-completeness (in fact, the higher-order non-completeness does not guarantee the higher-order security, as shown in [
17]), and the first-order non-completeness is generally realized in the 2nd-order masking scheme ([
10,
11,
12,
13]), we will focus on the 2nd-order masked gate in the sequel.
Theorem 2. Given a 2nd order masked gate of a gate , if a 2nd order component masked gate, say is first-order non-complete, then it is 2nd-order G-equivariant.
Proof. Without loss of generality, assume that
is independent of
and
so that
can be denoted as
By Lemma 1, proving that
is 2nd-order G-equivariant is equivalent to showing that, for any
and
,
for any
, where
is defined by
where
and
. Note that (10) is equal to the Equation (9) for
. Now, rewriting the summation in (10), we have
And the Equation (11) is equal to
for
and
since
is independent of
and
, thus changing
and
to
and
in
and changing
and
to
and
in
does not impact on evaluating
and
. Finally, substituting
with
,
with
,
with
and
with
, the Equation (12) is equal to
which is again equal to
And, this completes the proof. □
Corollary 2. The following 2nd-order component masked gatesgive the shared implementationof the 2-input AND gate whose energy consumption is independent of the arrival order of input signals:
In other words, the energy consumption ofin (15) is independent of the arrival order of input signals and . Proof. The claim is a direct consequence of Theorem 2 since are first-order non-complete. □
By Corollary 2, the set of first-order non-complete gates is a subset of the set of 2nd-order G-equivariant gates. And, at this point, it may be questionable if there are any 2nd-order G-equivariant but first-order complete gates that can be used for implementing the AND gate in a shared form. Interestingly, the answer is yes. For example, it can be shown that the following gates
are G-equivariant:
Also, the XOR sum of in (16) gives the AND gate evaluation for the original inputs, that is, is equal to . However, since involves all shares of for its computation, it is not non-complete.
Remark 2. The G-equivariant gate is for ensuring the security only for the single gate; thus, it does not guarantee the security of the composition of several gates. And, to get the security of composited gates, the cryptosystem’s implementers must consider inserting some registers, for example, to eliminate the glitch’s effect to not propagate through the several gates. However, we emphasize that the same undesirable increase of circuit’s size from inserting registers is very common in most hardware masking schemes, including the threshold implementation [10,11,12,13], mainly due to the glitch’s effect.