A New Resource Allocation Protocol for the Backhaul of Underwater Cellular Wireless Networks
Abstract
:Featured Application
Abstract
1. Introduction
- Traffic volume. The amount of the uplink traffic (i.e., from a base station to a base station controller) is much larger than that of the downlink traffic (i.e., from a base station controller to a base station) in a UCWN, which is completely contrary to a TCWN.
- Performance. The transmission rate of a backhaul link of a UCWN is much lower than that of a TCWN. Besides, the latency of a backhaul link of a UCWN is much higher than that of a TCWN.
- The ability to manage drastic change of uplink traffic. As the protocol in [16] was designed under the assumption that the UBSC capacity is enough to manage the input traffic from all the UBSs, it can be partially efficient when the uplink traffic of all the UBSs does not change quickly or does not show any bursty nature (which can be caused by mobile UTs such as autonomous underwater vehicles (AUVs)). However, in practice, it is possible that the uplink traffic of a UBS may abruptly increase due to burst traffic caused by mobile UTs or the rise of traffic gathered from (fixed) UTs in its cell. This can make a UBSC experience a shortage of backhaul capacity, and consequently it suffers from long latency and packet drops by queue-overflow. Thus, a more responsive resource reallocation reflecting traffic condition, that the uplink traffic of each UBS changes fast or the outbreak of burst uplink traffic occurs frequently, is strongly required.
- The way to readjust the backhaul capacity of a UBS. In [16], a UBSC collects traffic information from all the UBSs, calculates their backhaul capacity, and periodically reassigns their backhaul capacity by informing them of their new backhaul capacity. In other words, all the UBSs must communicate with a UBSC for the readjustment of their backhaul capacity at the same time. This is quite inefficient to the backhaul link of a UCWN suffering from both low transmission rate and high latency because the message overhead for reallocation of the backhaul capacity is quite large. Thus, considering low transmission rate and high latency of the backhaul links, a more efficient method to reassign the backhaul capacity of UBSs is necessary.
- Interoperability. As there are diverse modulation and coding schemes (MCSs) and multiple access schemes such as FDMA (Frequency Division Multiple Access), TDMA, CDMA (Code Division Multiple Access), and OFDMA (Orthogonal Frequency Division Multiple Access) for different underwater communication links and ranges, a resource allocation protocol, which is interoperable with diverse MCSs and multiple access schemes, is required.
- Scenario 1: varying the upper limit (or maximum) of the backhaul capacity of a UBS,
- Scenario 2: varying the lower limit of the resource utilization threshold where a UBS returns unused backhaul capacity when its current resource-utilization becomes less than this lower limit.
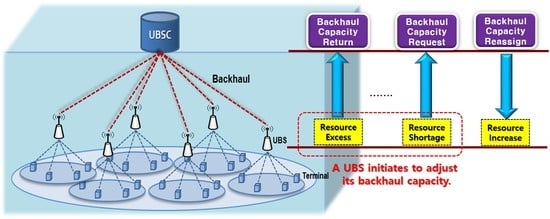
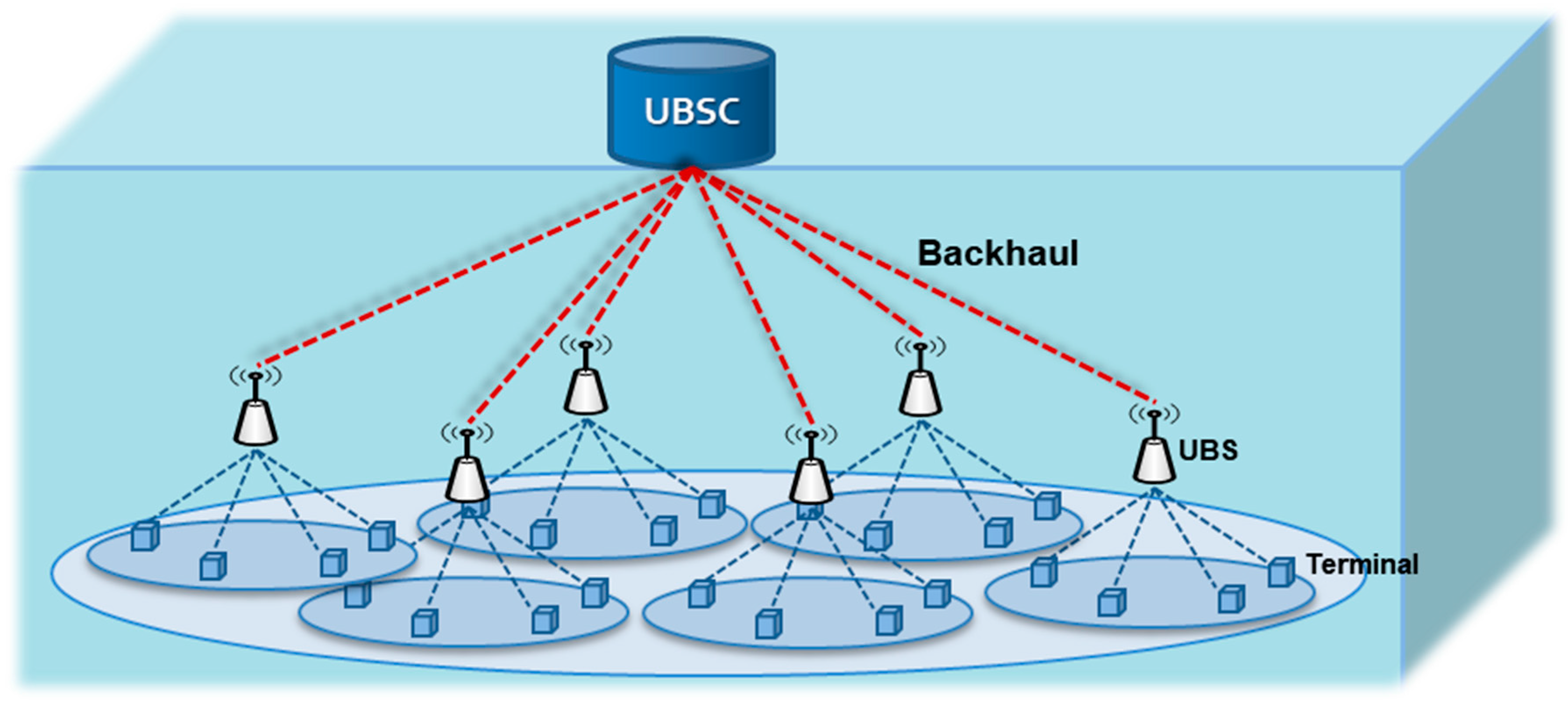
2. System Description
3. Description of UBSI Resource Allocation Protocol
- The UBSI resource allocation protocol is basically designed to efficiently manage the non-guaranteed UBSC capacity which implies that the capacity of the UBSC is insufficient to deal with the uplink traffic induced by UBSs.
- A UBS triggers to adjust its backhaul capacity for itself according to its queue status which does not affect the actions of other UBSs. To do this, a UBS requests additional backhaul capacity in case of occurring packet drops due to the shortage of current backhaul capacity. This can improve the performances of a UCWN in terms of energy efficiency, message overhead, throughput, and latency. A UBS also returns a portion of its backhaul capacity to the UBSC when it detects that its resource is under-utilized in order to manage the limited backhaul capacity of the UBSC.
- A ratio-based backhaul capacity is employed in order to be interoperable with any multiple access protocols (e.g., TDMA, CDMA, FDMA, or OFDMA) which have different resources, respectively.
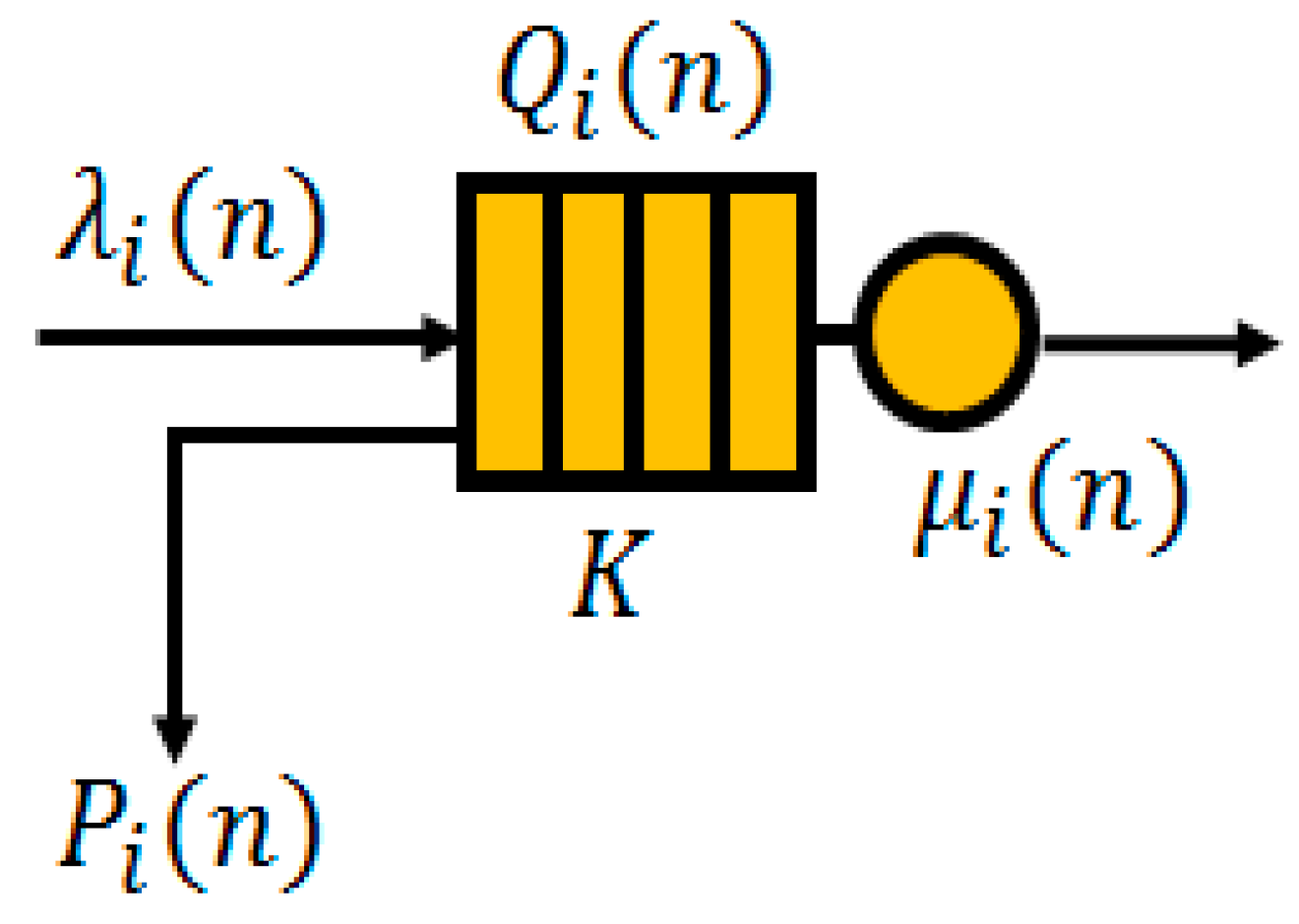
3.1. Queue Model and Backhaul Capacity of UBSs
3.1.1. Queue Model
- is the arrival rate of a UBS during the -th time interval. In other words, this is the number of packets of a UBS received from all the UTs residing in its cell during the -th time interval.
- is the service rate a UBS during the -th time interval. That is, this implies the number of packets served by UBS during the -th time interval. Once the backhaul capacity of a UBS is determined, it holds until the next reallocation. And a UBS transmits its uplink traffic with the data rate up to its backhaul capacity. is the queue length of a UBS at the end of the -th time interval. Specifically, this is the number of packets remaining at the queue of UBS at the end of the -th time interval. The queue length of a UBS is expressed as a function of its previous queue length at time interval − 1, the current input traffic (i.e., packet arrival) rate and the backhaul capacity during time interval . Besides, the queue length has its maximum value denoted by . Thus, it is expressed as the following equation.
- is the number of packet drops of a UBS during the -th time interval. In other words, this is the number of packets dropped from the queue of a UBS during the -th time interval. Similar to the is a function of its previous queue length at time − 1, the current input traffic (i.e., packet arrival) rate and backhaul capacity during time interval , and represented as
3.1.2. Backhaul Capacity of UBSs
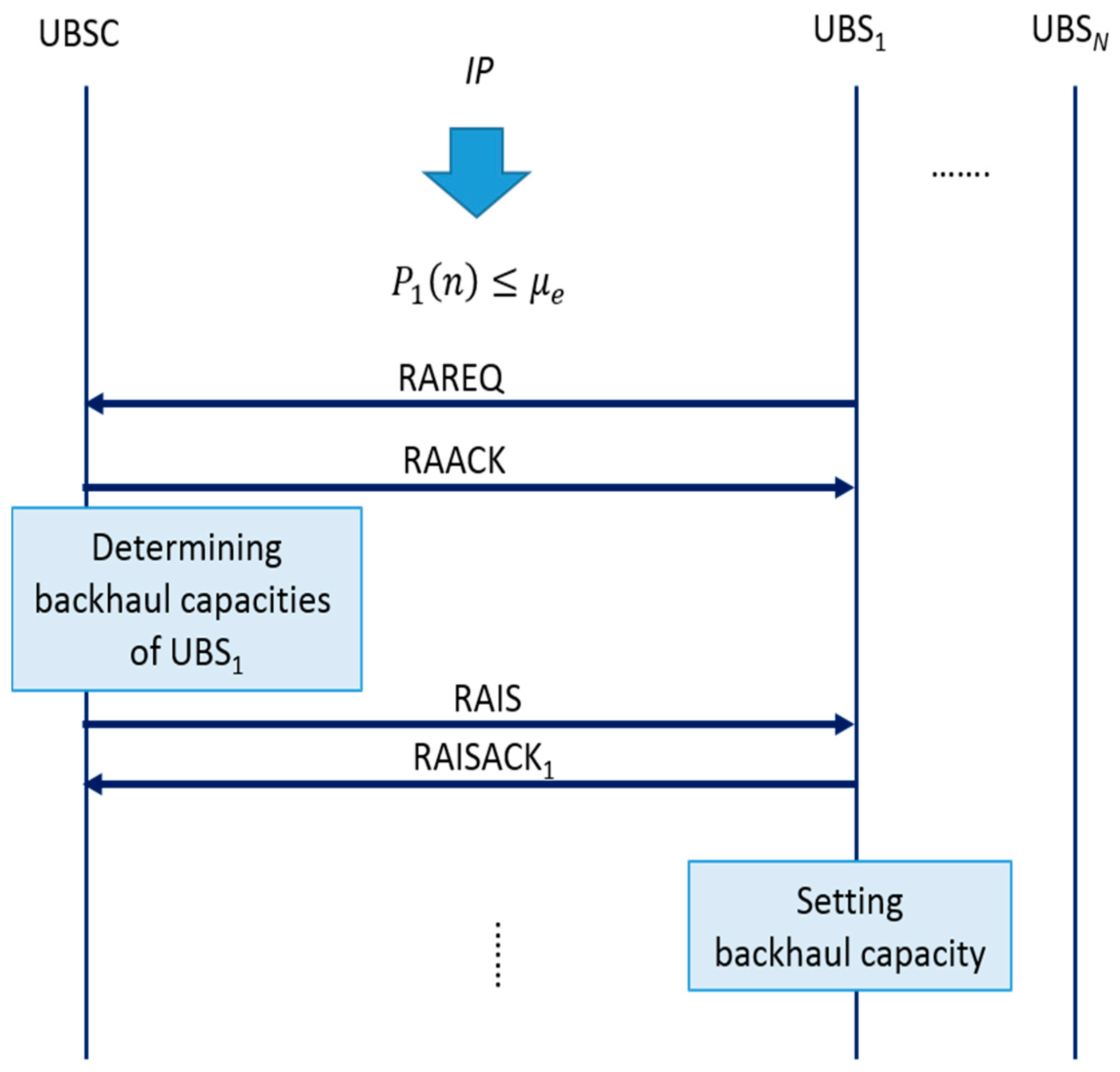
3.2. Protocol Messages and Procedures
3.2.1. Protocol Messages
- A Resource Information Request (RIREQ) is a message that a UBSC asks all UBSs to send their traffic information as specified in Section 3.1.1.
- A Resource Information Response (RIREP) is a response message to RIREQ sent by a UBS which includes its traffic information.
- A Resource Allocation Information Send (RAIS) is a message sent by a UBSC to inform a UBS sending a RIREQ of new backhaul capacity. During the IP, this message contains allocated backhaul capacity of each UBS and is broadcasted to all the UBSs. However, during the NP, this message contains reallocated backhaul capacity of a UBS which requested reallocation of its backhaul capacity. Thus, in this case, this message is sent to only one UBS.
- A Resource Allocation Information Send Acknowledgement (RAISACK) sent by a UBS is an acknowledgement message of RAIS.
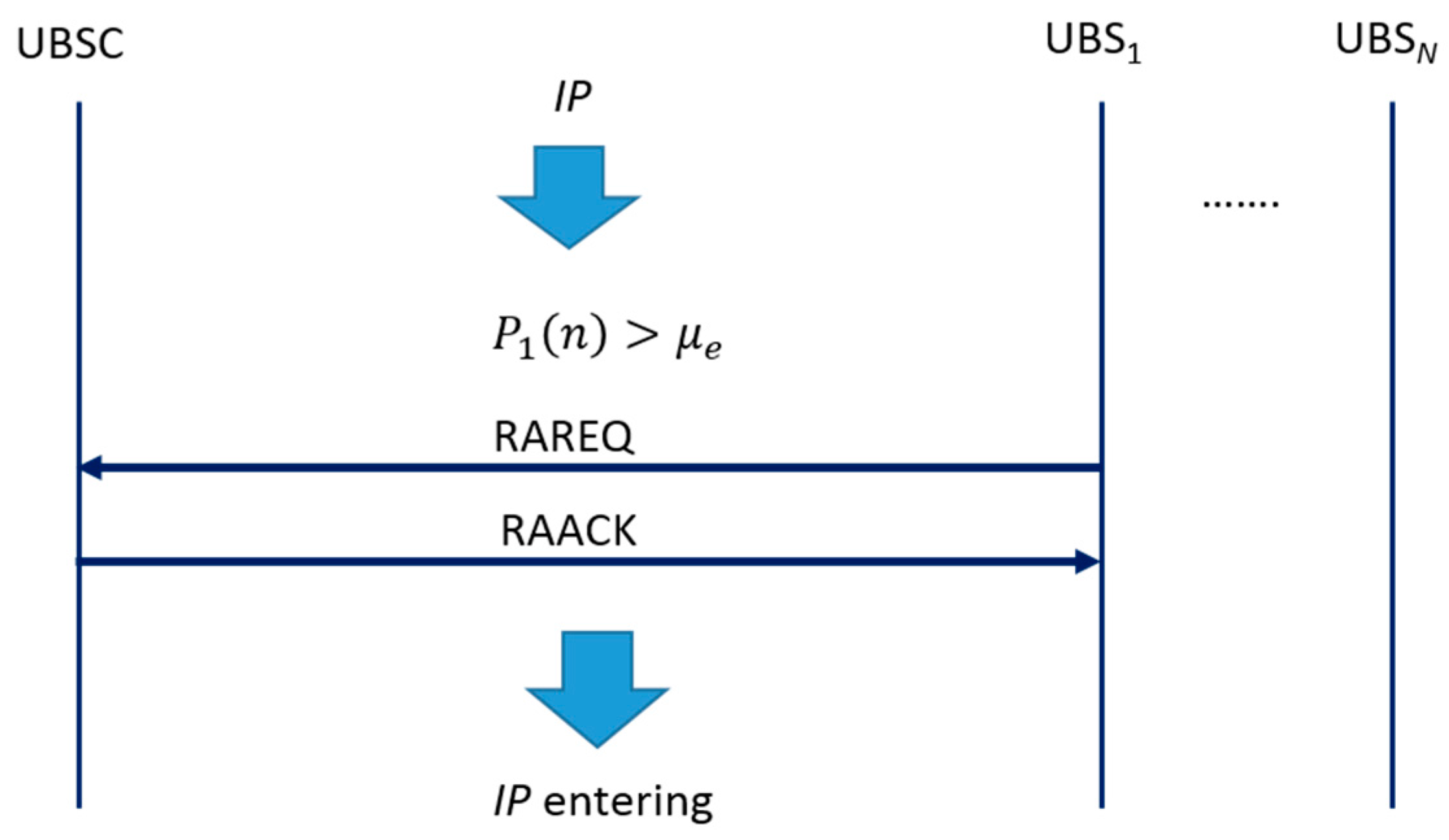
- A Resource Reallocation Request (RAREQ) is a message that a UBS asks a UBSC to adjust its backhaul capacity.
- A Resource Reallocation Acknowledgement (RAACK) sent by a UBSC is an acknowledgement message of the RAREQ.
3.2.2. Initialization Phase
3.2.3. Normal Operation Phase
- As decreases, the frequency of backhaul capacity adjustment decreases since a UBS will have less probability of the event . Thus, it is expected to improve energy efficiency and to have less message overhead, but to deteriorate overall resource utilization, throughput, and packet drop rate.
- As increases, the frequency of backhaul capacity adjustment increases since a UBS will have higher probability of the event . The performance pattern is expected to be opposite to when decreases. This implies that a performance trade-off exists between these two situations.
4. Simulation and Performance Analysis Results
4.1. System Level Simulation Description and Performance Measures
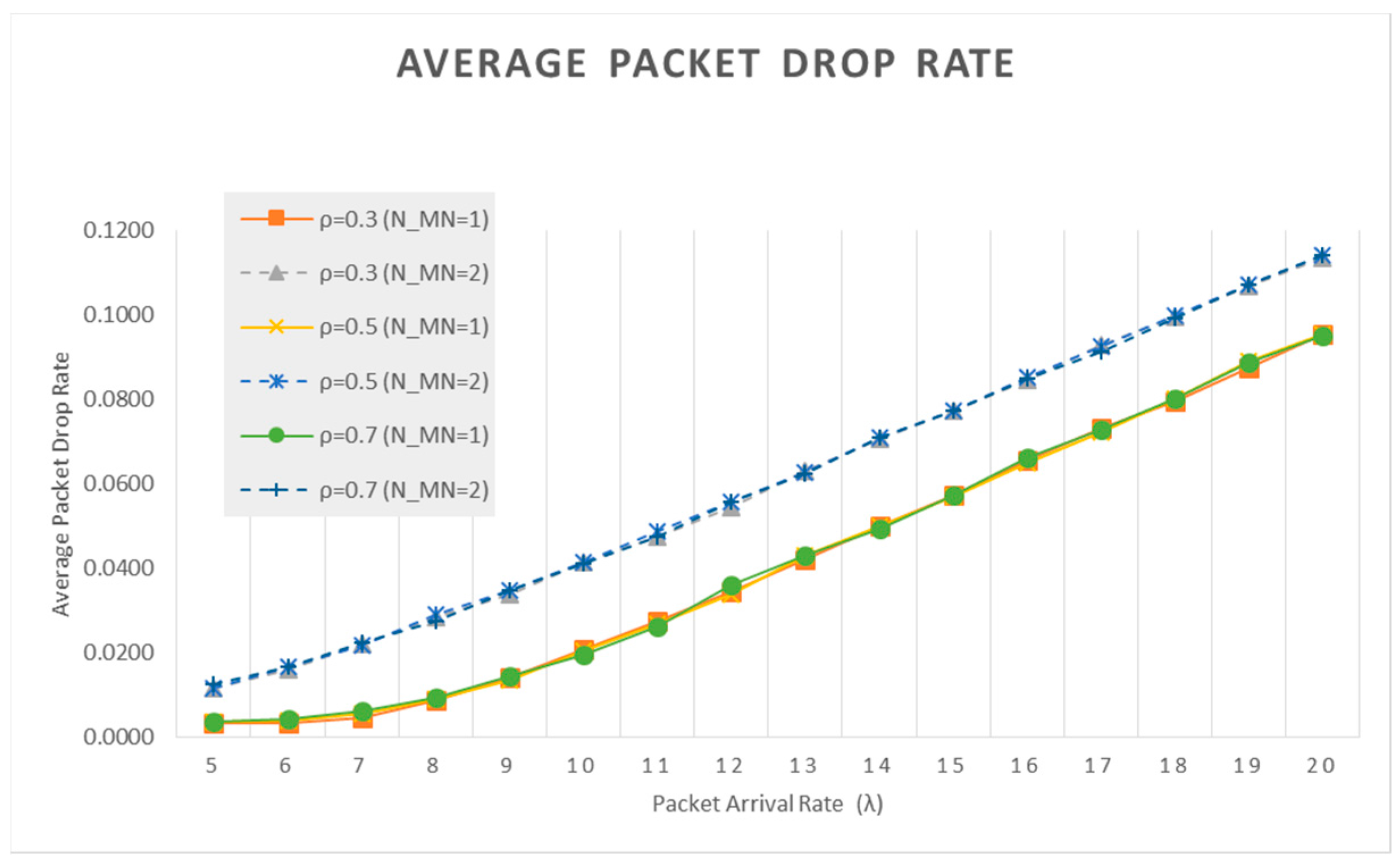
- Average packet drop rate: a ratio of dropped packets over ingress packets in a queues of a UBS.
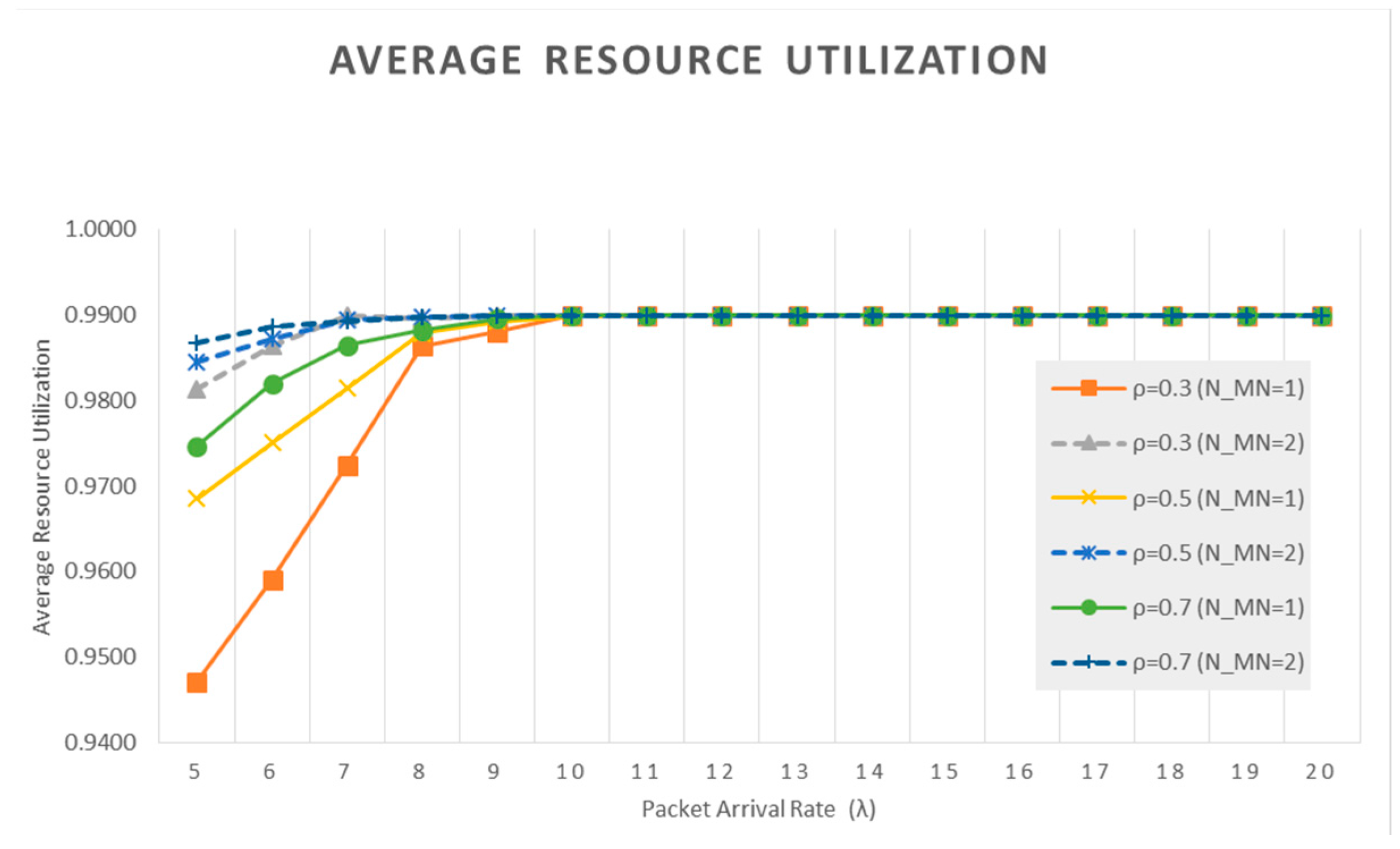
- Average resource utilization: a ratio of used backhaul capacity over assigned backhaul capacity of a UBS.
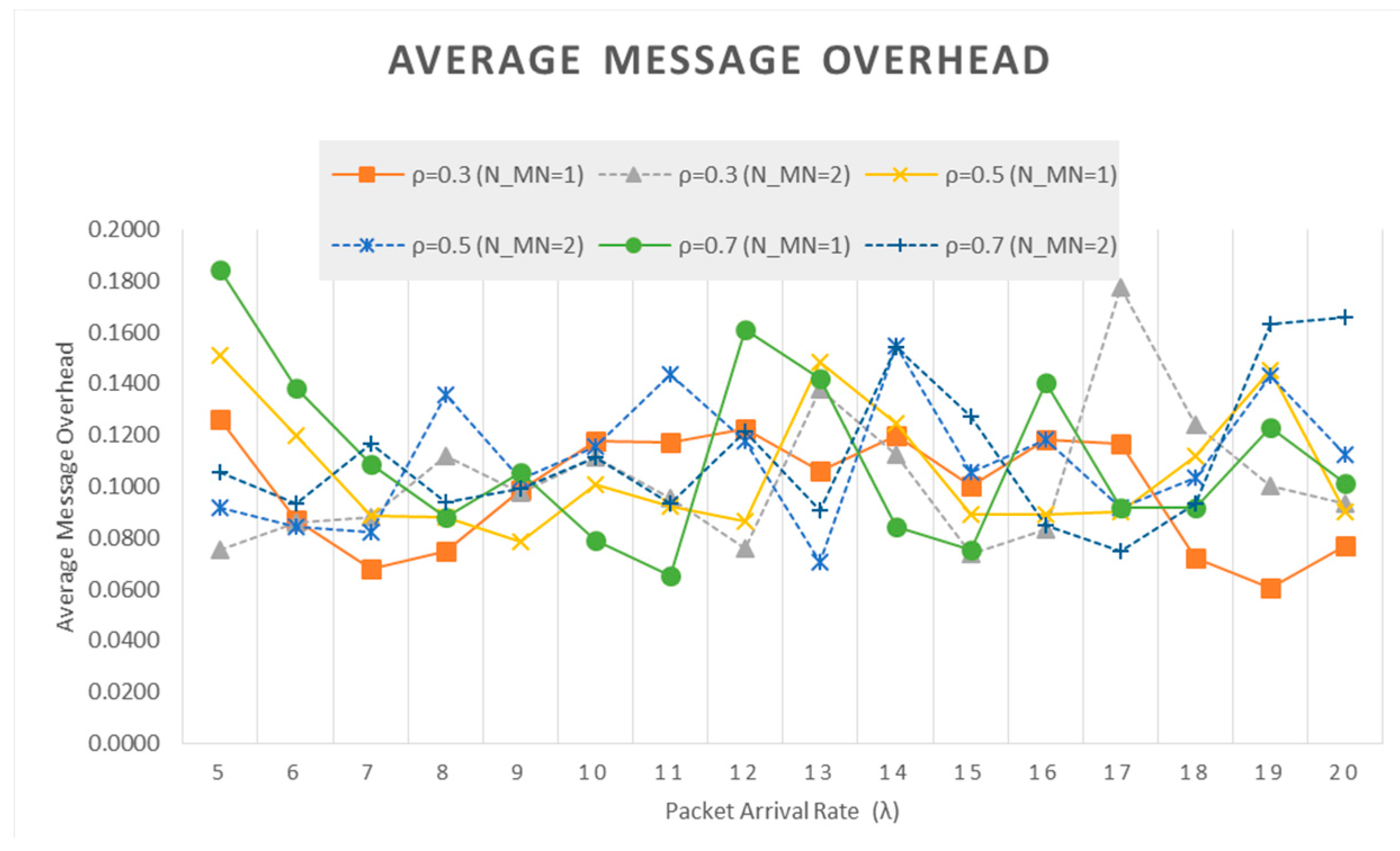
- Average message overhead: the number of messages induced by resource reallocation.
- Average reserved UBSC capacity of the UBSC.
4.2. Simulation Results and Performance Analysis
- Scenario 1: varying the upper limit (or maximum) of the backhaul capacity of a UBS.
- Scenario 2: varying the lower limit of the resource utilization threshold where a UBS returns unused backhaul capacity when its current resource-utilization becomes less than this lower limit.
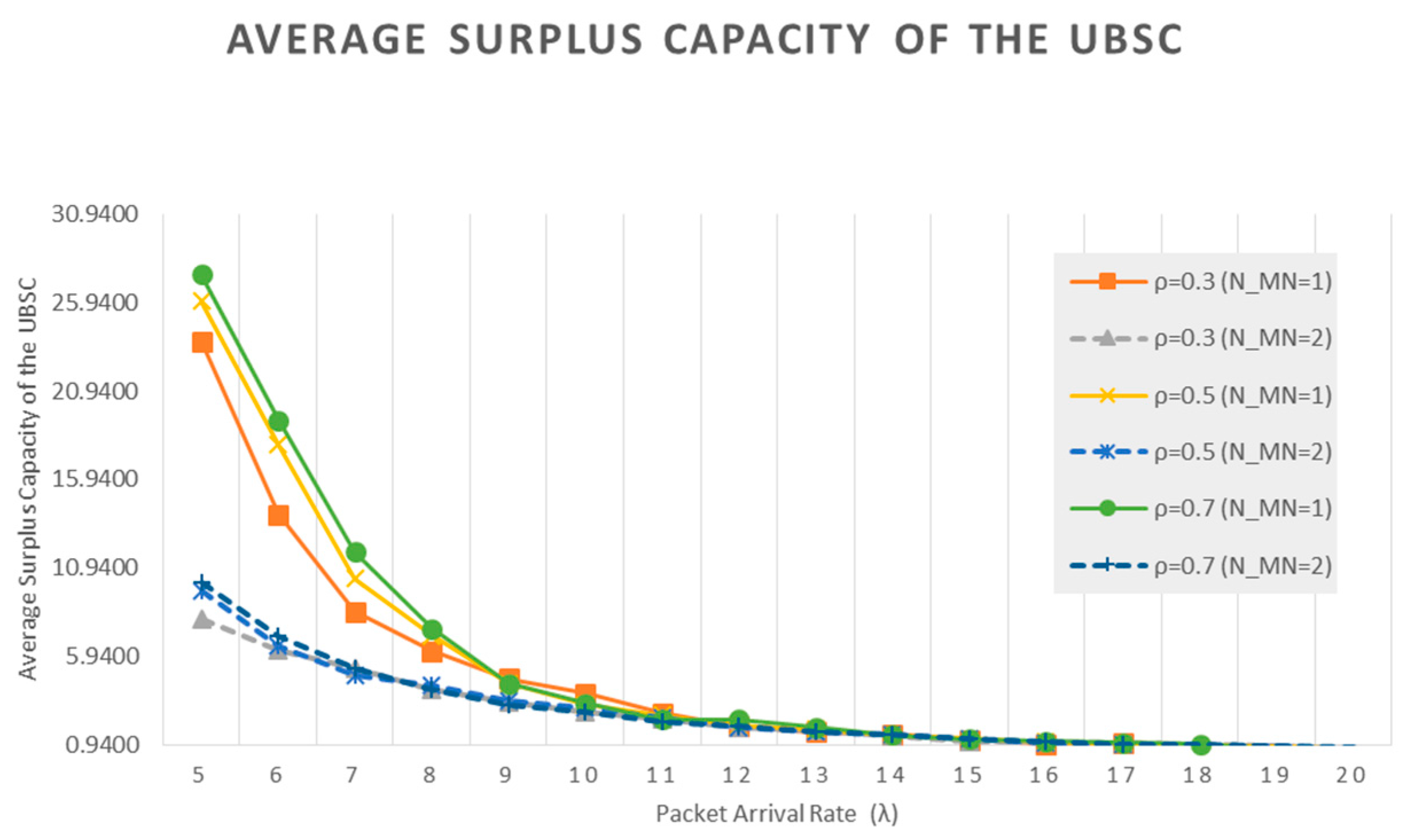
4.2.1. Scenario 1
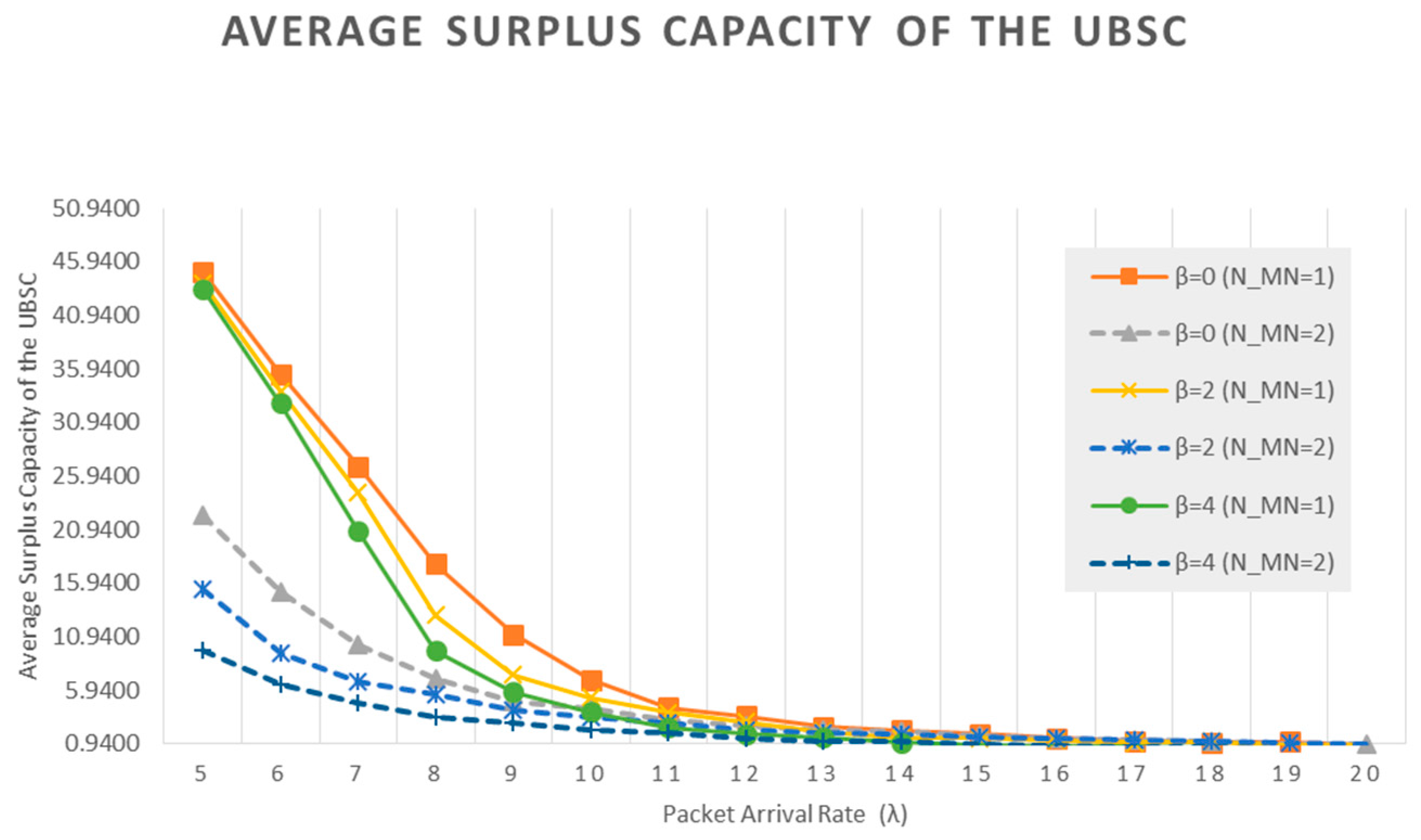
4.2.2. Scenario 2
4.2.3. Simulation Summary
- Average packet drop rate is not dependent upon under-utilization limit (, but more dependent upon the number of mobile UTs ( generating burst traffic and upon the average packet arrival rate .
- There is a close relationship (or a tradeoff) among the average resource utilization, the average message overhead, and the average reserved capacity of the UBSC for . Specifically, as becomes higher, the average resource utilization becomes higher, the average message overhead also gets higher, and the reserved capacity of the UBSC also becomes higher.
- This means that as becomes higher, each UBS uses only required backhaul capacity and returns unused backhaul capacity to the UBSC. Accordingly, the reserved capacity of the UBSC becomes higher. However, to maintain only required backhaul capacity in each UBS, each UBS needs to send and receive the control signaling messages, which results in high average message overhead.
- Note that high reserved backhaul capacity in the UBSC can be helpful to cope with burst traffic with high packet arrival rate in some UBSs (mainly caused by the mobile terminals such as AUVs).
- Average packet drop rate increases as the adjustment parameter ( increases. Average packet drop rate becomes higher as the average packet arrival rate and the number of mobile UTs ( increases.
- For and the number of mobile UTs ( is equal to one, the average packet drop rate is almost the same as and increase. This is because UBSs have sufficient backhaul capacities to support low packet arrival rate.
- For , there is a close relationship (or a tradeoff) among the average resource utilization, the average message overhead, and the average reserved capacity of the UBSC. Specifically, as becomes higher, the average resource utilization becomes lower, the average message overhead also gets higher, and the reserved capacity of the UBSC also becomes lower.
- This means that as becomes higher, a UBS can have higher the maximum backhaul capacity given by + . So, in this case, some UBSs can have larger backhaul capacity than (equal to 10 in the SLS) and the capacity may not be fully utilized due to small , resulting in low resource utilization. Besides, when some UBSs have larger backhaul capacity than due to > 0, the other UBSs will have lower capacity than since the total backhaul capacity is limited. Consequently, the reserved capacity of the UBSC becomes lower for larger . In this case, if the traffic pattern of the UBSs is changed, the probability that backhaul capacity for each UBS is adjusted to reflect the updated traffic condition becomes high. Thus, the average message overhead mainly due to this adjustment can be large when is large.
- For , there is a close relationship (or a tradeoff) among the average resource utilization, the average message overhead, and the average reserved capacity of the UBSC, which is different from the relationship for .
- Specifically, as becomes higher, the average resource utilization becomes higher, the average message overhead also gets higher, and the reserved capacity of the UBSC also becomes lower.
- Note that for this case as becomes higher, the average resource utilization becomes higher. This is because, for , some UBSs can have higher backhaul capacity (given by + ), and this capacity (greater than ) can handle burst traffic as well as instantaneous high traffic due to large . Consequently, the backhaul resource can be almost fully utilized, producing high average resource utilization.
- Therefore, when we determine the operational value of in the real UCWN, we first need to consider the average packet arrival rate of UBSs.
5. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Underwater Wireless Communication Market—Global Drivers, Opportunities, Trends, and Forecasts to 2022; Infoholic Research: Bengaluru, India, 2017; pp. 35–42. Available online: https://www.infoholicresearch.com/report/underwater-wireless-communication-market-trends-and-forecast-2016-2022/ (accessed on 25 January 2018).
- Murad, M.; Sheikh, A.; Manzoor, M.; Felemban, E.; Qaisar, S. A Survey on current underwater acoustic sensor network application. Int. J. Comput. Theory Eng. 2015, 7, 51–56. [Google Scholar] [CrossRef]
- Heidemann, J.; Ye, W.; Wills, J.; Syed, A.; Li, Y. Research challenges and applications for underwater sensor networking. In Proceedings of the IEEE Wireless Communications and Networking Conference (WCNC 2006), Las Vegas, NV, USA, 3–6 April 2006; pp. 228–235. [Google Scholar] [CrossRef]
- Yun, C.; Lim, Y. GSR-TDMA: A geometric spatial reuse-time division multiple access MAC protocol for multihop underwater acoustic sensor networks. J. Sens. 2016, 2016, 6024610. [Google Scholar] [CrossRef]
- Chitre, M.; Shahabudeen, S.; Stojanovic, M. Underwater acoustic communications and networking: Recent advances and future challenge. Mar. Technol. Soc. J. 2008, 42, 103–116. [Google Scholar] [CrossRef]
- Urick, R.J. Principle of Underwater Sound, 3rd ed.; McGraw-Hill: New York, NY, USA, 1983; ISBN 10: 0932146627. [Google Scholar]
- Akyildiz, I.F.; Pompili, D.; Melodia, T. Underwater acoustic sensor networks: Research and challenges. J. Ad-Hoc Netw. 2005, 3, 257–279. [Google Scholar] [CrossRef]
- Kim, J.H.; Im, T.H.; Kim, K.Y.; Ko, H.L. A study on the underwater base station based underwater acoustic communication systems. Proc. KICS Int. Conf. Commun. 2015, 353–354. Available online: https://www.kics.or.kr/home/kor/morgue/searchArticle.aspx?Mode=search (accessed on 24 January 2018).
- Jiang, Z. Underwater acoustic networks-Issues and solutions. Int. J. Intell. Control Syst. 2008, 13, 152–161. [Google Scholar]
- Stojanovic, M.; Freitag, L. Recent trends in underwater acoustic communications. Mar. Technol. Soc. J. 2013, 47, 45–50. [Google Scholar] [CrossRef]
- Stojanovic, M. Design and capacity analysis of cellular-type underwater acoustic communications. IEEE J. Ocean. Eng. 2008, 33, 171–181. [Google Scholar] [CrossRef]
- Labrador, Y.; Karimi, M.; Pan, D.; Miller, J. Modulation and error correction in the underwater acoustic communication channel. J. Comput. Sci. Netw. Secur. 2009, 9, 123–130. [Google Scholar]
- Stojanovic, M. Frequency reuse underwater: Capacity of an acoustic cellular network. In Proceedings of the Second Workshop on Underwater Networks (WuWNet ′07), Montreal, QC, Canada, 14 September 2007; pp. 19–24. [Google Scholar] [CrossRef]
- Nabavinejad, A.; Ghahfarokhi, S. Improving coverage and capacity in underwater acoustic cellular networks. In Proceedings of the 2013 15th International Conference on Advanced Communication Technology (ICACT), Pyeong-Chang, Korea, 27–30 January 2013; pp. 1249–1256. [Google Scholar]
- Peleato, B.; Stojanovic, M. A Channel sharing scheme for underwater cellular networks. In Proceedings of the IEEE OCEANS, Aberdeen, UK, 18–21 June 2007. [Google Scholar] [CrossRef]
- Yun, C.; Park, J.; Choi, S. Backhaul resource allocation protocol for underwater cellular communication networks. J. Korean Inst. Commun. Inf. Sci. 2017, 42, 393–402. [Google Scholar] [CrossRef]
- Biswas, S.K.; Izmailov, R. Design of a Fair Bandwidth Allocation Policy for VBR Traffic in ATM Networks. IEEE/ACM Trans. Netw. 2000, 8, 2425–2431. [Google Scholar] [CrossRef]
- Son, K.; Ryu, H.; Chong, S.; Yoo, T. Dynamic bandwidth allocation schemes to improve utilization under non-uniform traffic in Ethernet passive optical networks. In Proceedings of the 2004 IEEE International Conference on Communications (IEEE Cat. No.04CH37577), Paris, France, 20–24 June 2004; pp. 1766–1770. [Google Scholar] [CrossRef]
- Subhashini, N.; Therese, A.B. User prioritized User prioritized constraint free dynamic bandwidth allocation algorithm for EPON networks. Indian J. Sci. Technol. 2015, 8, 1–7. [Google Scholar] [CrossRef]





| Parameters | Description |
|---|---|
| The index of a UBS | |
| The number of UBSs | |
| The index of discrete time | |
| The maximum queue length | |
| The UBSC capacity | |
| The maximum backhaul capacity of a UBS | |
| The backhaul capacity of UBS at time | |
| The input traffic rate of UBS at time | |
| The reserved capacity of a UBSC at time | |
| The queue length of UBS at time | |
| The number of packet drops of UBS at time | |
| The resource utilization of UBS at time | |
| The message overhead of UBS at time |
| Type | Direction | Phase | Transmission Type | Note |
|---|---|---|---|---|
| RIREQ | UBSC→UBS | IP, NP | Broadcast | Request traffic information (commonly used in IP and NP) |
| RIREP | UBS→UBSC | IP, NP | Unicast | Send traffic information (commonly used in IP and NP) |
| RAIS | UBSC→UBS | IP, NP | Unicast/Broadcast | Send the backhaul capacity to UBSs (commonly used in IP and NP) |
| RAISACK | UBS→UBSC | IP, NP | Unicast | An acknowledgement of RAIS (commonly used in IP and NP) |
| RAREQ | UBS→UBSC | NP | Unicast | Request of resource readjustment of a UBS (used in only NP) |
| RAACK | UBSC→UBS | NP | Unicast | An acknowledgement of RAACK (used in only NP) |
| Parameters | Description | Values in SLS |
|---|---|---|
| M | The number of SLSs with the same parameters | 10 |
| The index of discrete time per one SLS | 0~10,000 | |
| The number of UBSs | 10 | |
| The maximum queue length | 100 | |
| The capacity of a UBSC | 100 | |
| The maximum backhaul capacity of a UBS | + | |
| Adjustment parameter | 0~5 (default: 0) | |
| The backhaul capacity of UBS at time | 0 < < | |
| Average packet arrival rate of a UBS generated from normal UTs | 3~20 | |
| Under-utilization limit | 0.3~0.8 (default: 0.5) | |
| The number of mobile UTs (or nodes) generating burst traffic | 1~4 (default: 1) | |
| Average packet arrival rate of a UBS generated from mobile UTs | 10~60 (default: 30) | |
| Window size for average traffic calculation | 1~10 (default: 1) |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Yun, C.; Choi, S. A New Resource Allocation Protocol for the Backhaul of Underwater Cellular Wireless Networks. Appl. Sci. 2018, 8, 178. https://doi.org/10.3390/app8020178
Yun C, Choi S. A New Resource Allocation Protocol for the Backhaul of Underwater Cellular Wireless Networks. Applied Sciences. 2018; 8(2):178. https://doi.org/10.3390/app8020178
Chicago/Turabian StyleYun, Changho, and Suhan Choi. 2018. "A New Resource Allocation Protocol for the Backhaul of Underwater Cellular Wireless Networks" Applied Sciences 8, no. 2: 178. https://doi.org/10.3390/app8020178
APA StyleYun, C., & Choi, S. (2018). A New Resource Allocation Protocol for the Backhaul of Underwater Cellular Wireless Networks. Applied Sciences, 8(2), 178. https://doi.org/10.3390/app8020178