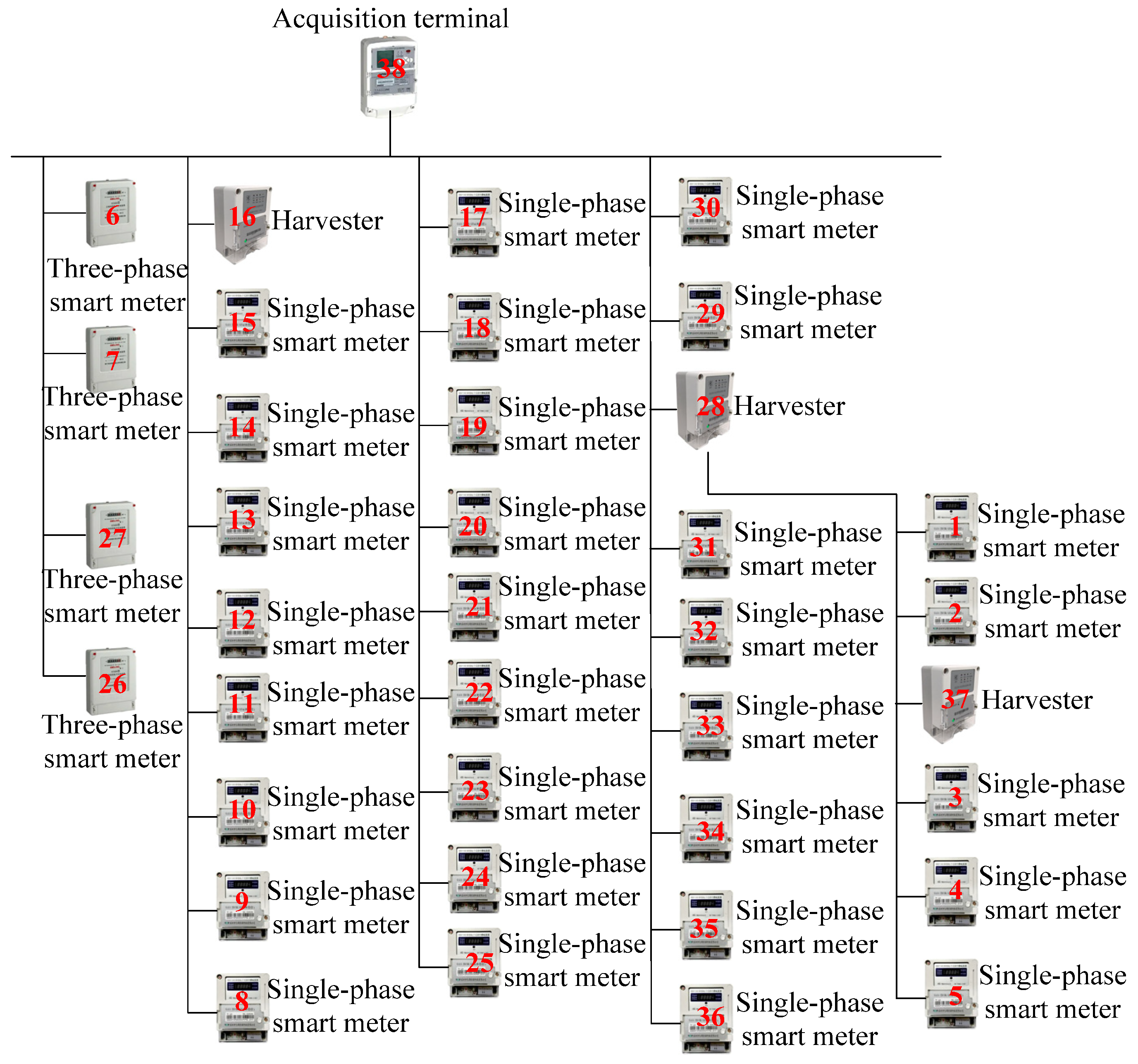
3.1. High-Speed Power Line Carrier Communication Network Formation
In high-speed power line carrier communication, establishing a stable link requires careful selection of appropriate power lines and nodes, forming the essential foundation for subsequent data transmission. A stable and reliable network guarantees that chaotic sequences generated by chaotic mapping maintain their complexity and unpredictability without causing transmission interference, thereby improving communication confidentiality and security. The minimal connected dominating set method enables the identification and construction of key node sets that preserve full network connectivity while minimizing node count, effectively reducing data transmission redundancy and delays [
13]. This approach is implemented through a power line carrier routing algorithm to construct the high-speed power line carrier communication network.
The concept of vertex domination in graph theory can be defined as a vertex dominating other vertices. In an undirected graph , for a vertex subset , if for , there exist such that , then is said to dominate , and is considered a dominating set of . If any two vertices in an undirected graph are connected by a path, then is considered a connected graph. Let be a dominating set of . If there exists an edge set that makes a connected graph, then is considered a connected dominating set of graph . If for , is not a connected dominating set, then is considered a minimal connected dominating set of graph .
The primary objective of the high-speed power line carrier routing and networking algorithm is to construct an optimal network structure among the carrier nodes. A high-speed power line carrier communication network with bidirectional communication can be modeled as an undirected connected graph , where denotes the set of all carrier nodes, and is the set of edges, with each edge of indicating the existence of a communication path between two carrier nodes.
The research on high-speed power line carrier communication networking strategies primarily centers on dividing the network into logically interconnected subnetworks and ensuring reliable communication between devices [
14]. Within a given area containing
carrier devices, maximizing network utilization efficiency requires selecting a minimal set of
devices with superior communication capabilities to serve as routing nodes, thereby guaranteeing reliable network-wide communication. This challenge is mathematically formulated as a minimal connected dominating set problem in graph theory.
From a graph theory perspective, this work establishes a weighted network analysis model employing the minimal connected dominating set concept. Building upon this model, we propose a novel high-speed power line carrier routing algorithm that executes the following procedure: First, the algorithm selects initial routing nodes via maximum weight priority determination. Specifically, for each carrier node, it verifies whether the node exhibits the largest weight among its neighbors, thus ensuring the selection of the highest signal-to-noise ratio node as a dominating node. Second, the method performs network connectivity re-optimization on preliminary routing nodes to derive the minimal connected dominating set solution. During optimization, when any neighbor remains unconnected through existing dominating nodes, the algorithm designates it a new dominating node.
Therefore, in the algorithm implementation, each carrier device is classified into one of three states: undetermined, a dominating node, or a dominated node. The undetermined state occurs during initial network formation when a device’s role remains undefined. The dominating node and dominated node states represent operational roles adopted during or after network formation, where dominating nodes function as routing nodes within the network.
The specific steps for the formation of a high-speed power line carrier communication network are as follows:
Step 1: Each carrier device in the network acquires a unique node identifier () and is assigned a communication performance weight based on its signal-to-noise ratio. During initialization, all carrier devices set their state to “undetermined” (), where represents the three states of carrier equipment in the process of networking. When the value is 0, it means that the carrier equipment is undetermined; when the values are 1 and 2, it corresponds to the state of the dominant node and dominated node of the carrier equipment, respectively.
Step 2: A carrier device initiates a networking request by broadcasting at maximum power [
15], collecting the
and weight information of other devices within its communication range. If device
has the highest weight among all one-hop neighbors in set
, proceed to Step 3; otherwise, proceed to Step 4.
Step 3: Update the device’s state to “dominant node” () and broadcast its node number and state value to all one-hop neighbors.
Step 4: The device updates its state based on received broadcast messages [
16], categorized as follows:
- (1)
If any carrier device in the network receives broadcast information from the carrier device , and its current state is “undetermined”, it updates its status to “dominated node” () and broadcasts its status information to devices within its communication range.
- (2)
If any carrier device receives broadcast information from the carrier device , and its current state is “undetermined”, it evaluates the weights of other devices in the received broadcast set . Specifically, it checks whether there exists a dominant node in subset , (where represents devices with weights greater than ). If such a node exists, updates its status to “dominating node” () and broadcasts its node number and status to devices within its communication range; otherwise, it continues waiting.
Step 5: If all carrier devices in the network have determined their states (i.e., , where denotes the set of undetermined nodes), the system enters a waiting time before proceeding to the connectivity optimization phase.
Step 6: To ensure network reliability and minimize the number of routing nodes, the following optimization rules are applied:
- (1)
For any dominated node , if two devices and within its communication range cannot connect via existing dominating nodes, updates its status to “dominating node” ().
- (2)
For any dominant node , if two carrier devices and within its communication range can be connected through other dominant nodes (excluding itself), the state of is updated to a dominated node (). Simultaneously, identifies the highest-weight dominating node within its neighbor set as its own dominating node.
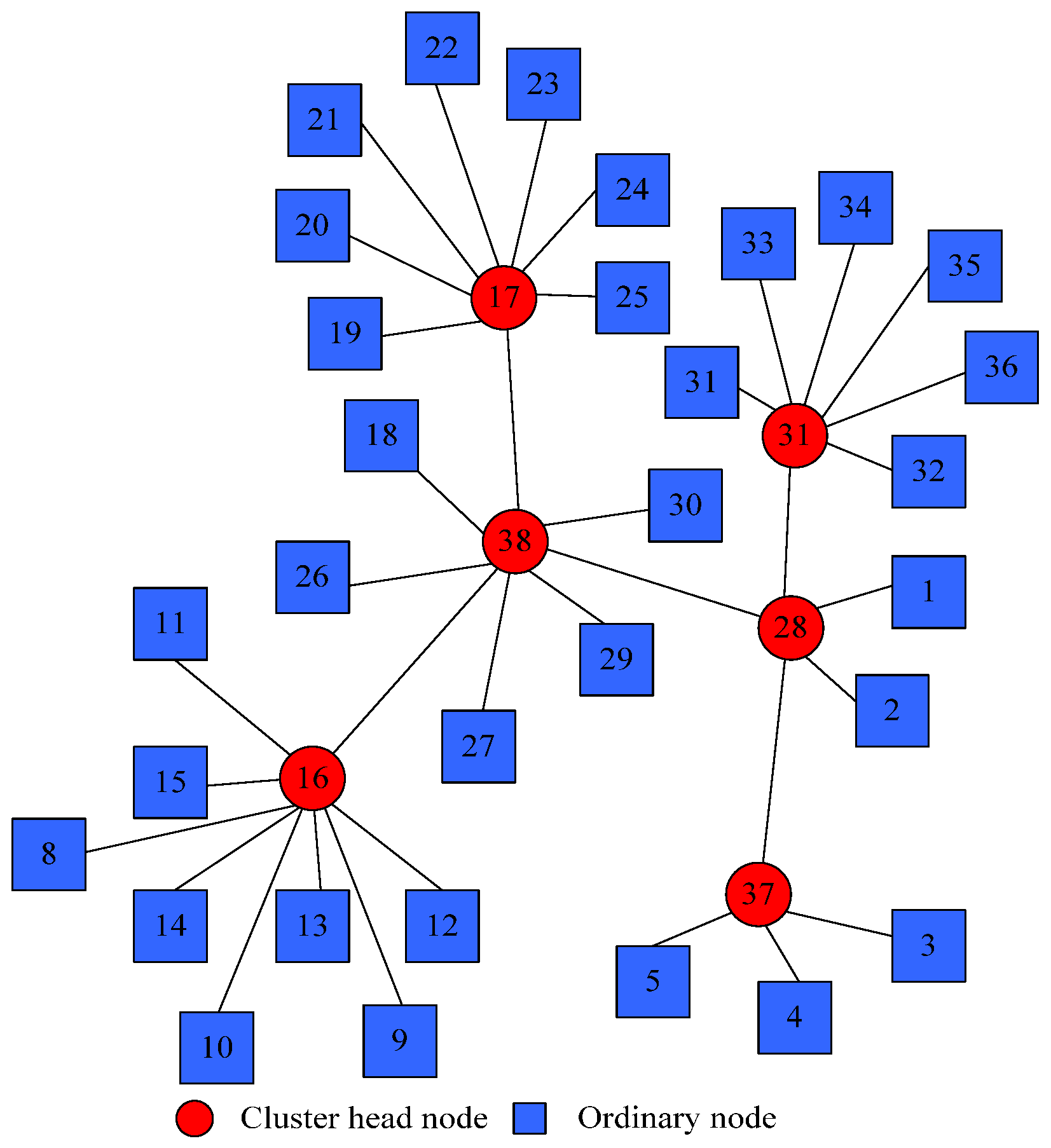
This algorithm determines the state of each carrier node in the high-speed power line carrier network. Each dominating node establishes connections with its corresponding dominated nodes to form subnetworks. Furthermore, any two dominated nodes are directly connected, creating a complete network where the carrier nodes act as cluster heads. Ultimately, the dominating nodes interconnect to form the high-speed power line carrier communication network.
3.2. Cryptographic Security Analysis
In the secure transmission method for high-speed power line carrier communication, cryptographic security represents one of the core performance evaluation metrics. This paper conducts a detailed security analysis focusing on three key aspects: key space size, resistance against known attacks, and entropy measurement, thereby demonstrating the method’s high security characteristics.
The key space represents the set of all possible keys, and its size directly influences the encryption system’s resistance to brute-force attacks.
In the generalized two-dimensional polynomial chaotic mapping system, the cryptographic key is determined by three components: the chaotic system’s initial conditions, the control parameters, and the polynomial’s highest degree. This configuration ensures that even with supercomputing capabilities, an attacker would require a computationally impractical time frame (exceeding the universe’s age) to exhaust all possible key combinations, thereby guaranteeing the encryption system’s theoretical security.
The system’s resistance to known attacks manifests in four key aspects:
- (1)
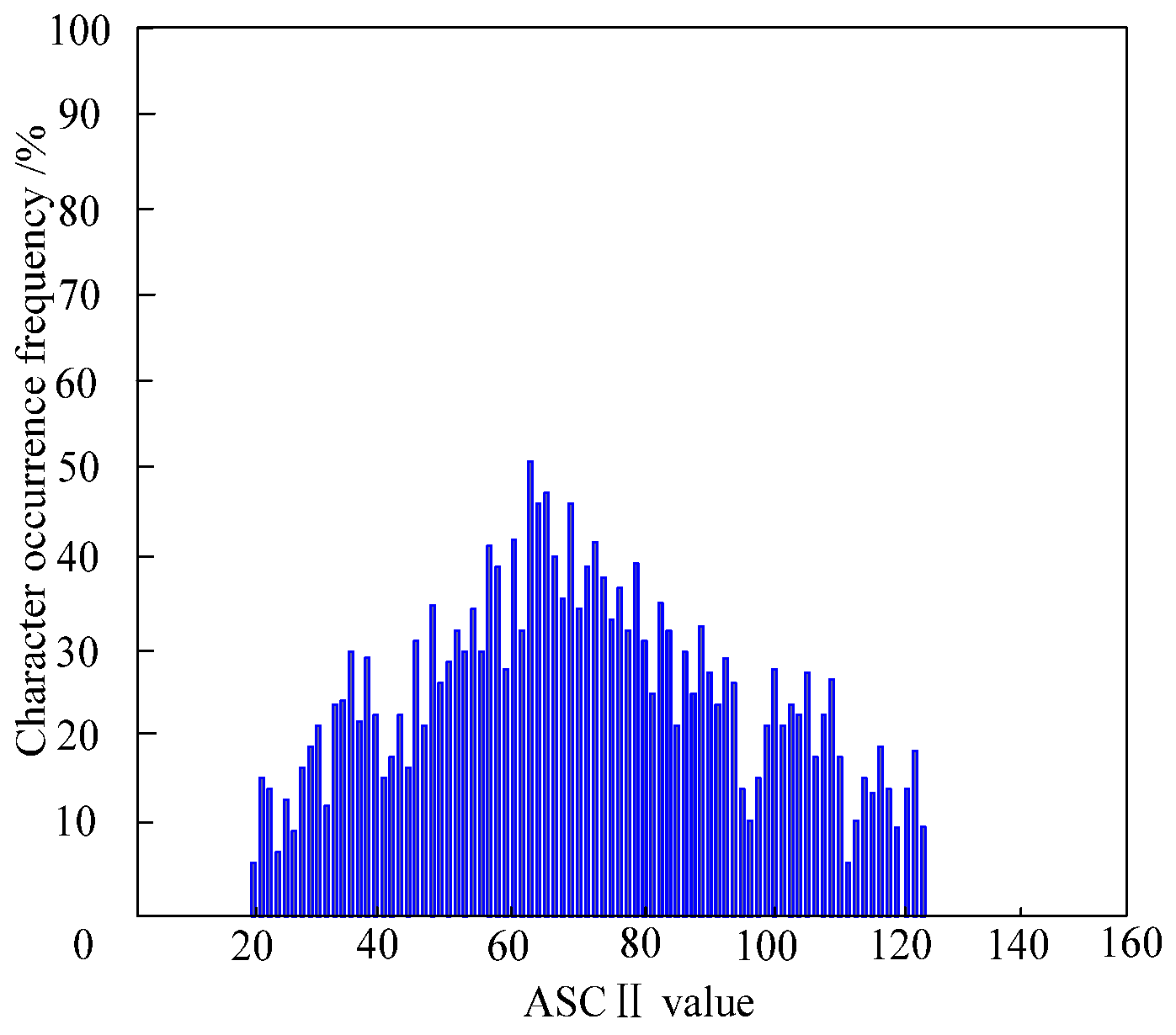
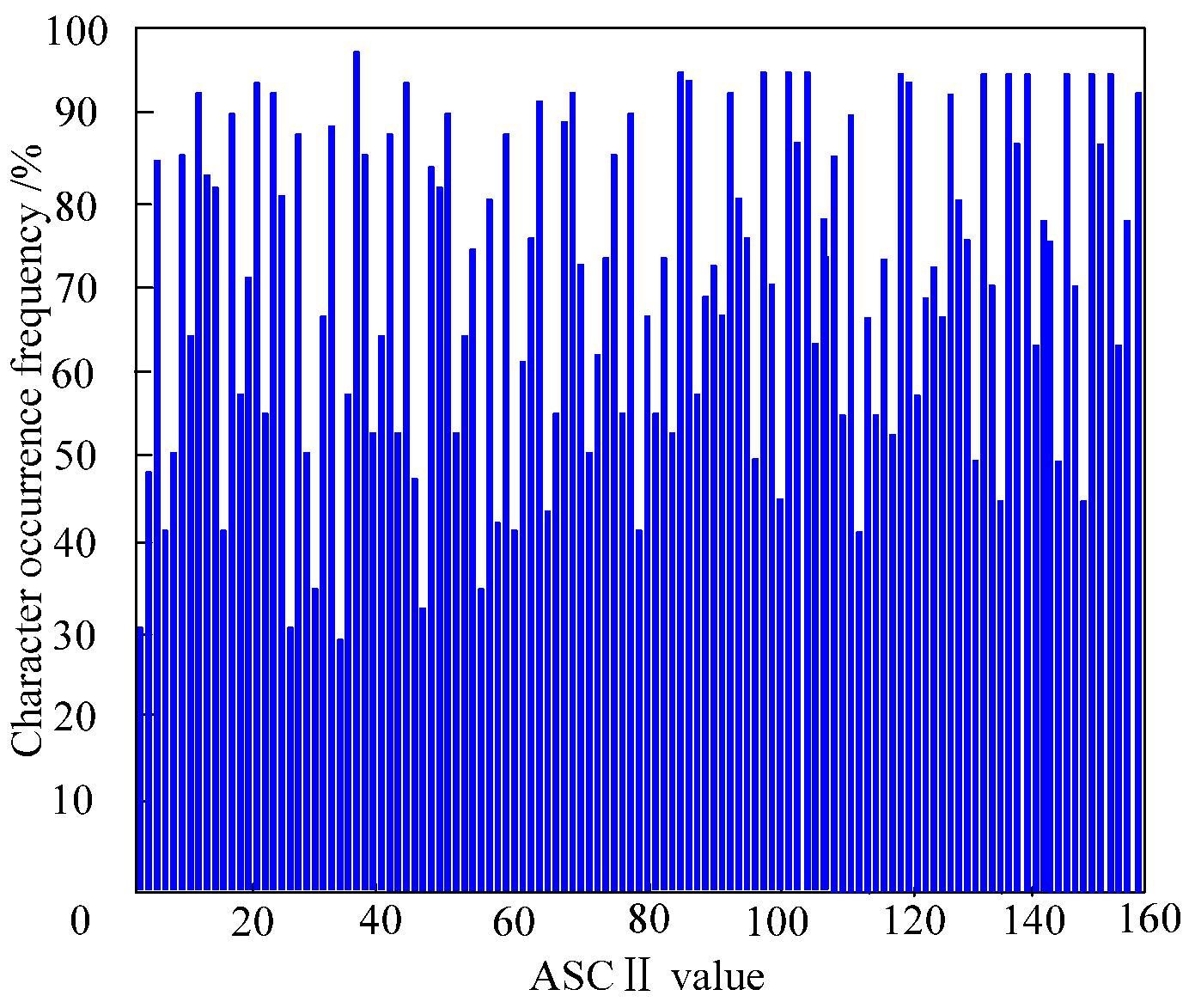
Statistical attacks: The quasi-random sequences generated by chaotic mapping exhibit white-noise-like statistical properties (e.g., autocorrelation and cross-correlation). The generalized two-dimensional polynomial chaotic mapping ensures uniform and unpredictable sequence distributions, preventing attackers from extracting meaningful information through statistical analysis techniques like differential or linear cryptanalysis.
- (2)
Chosen-plaintext/ciphertext attacks: Extreme sensitivity to initial conditions and parameters makes deducing the chaotic system’s internal state impossible even with known plaintext–ciphertext pairs. Dynamic parameter adjustment (e.g., transmission fluctuation-based key updates) further strengthens this resistance.
- (3)
Side-channel attacks: Hardware-based implementation inherently decouples side-channel information (power consumption, electromagnetic radiation) from cryptographic keys. Combined with dynamic parameter adaptation, this effectively mitigates power analysis and timing attacks.
- (4)
Known-key attacks: The chaotic mapping’s complexity and parameter diversity ensure security even with partial key exposure. Regular key updates through the system’s built-in mechanism provide additional protection against such compromises.
Entropy serves as a quantitative measure of information uncertainty, where higher entropy values correspond to greater system security. For chaotic sequences, entropy can be quantified as the number of bits per symbol. Considering a chaotic sequence with a uniformly distributed output range of [0, 1], the per-sample entropy is given by
Leveraging the long-periodicity and aperiodicity characteristics of chaotic sequences, the total entropy value exhibits linear growth with increasing sequence length, surpassing traditional encryption algorithms significantly. This high-entropy property ensures that attackers cannot predict the complete sequence from partial information, thereby maintaining data confidentiality and integrity.
3.3. Confidential Transmission Method Based on Generalized Two-Dimensional Polynomial Chaotic Mapping
3.3.1. Analysis of Transmission Fluctuation Deviations in High-Speed Power Line Carrier Communication Networks
The autoregressive moving average (ARMA) model analyzes transmission fluctuation deviations within the high-speed power line carrier communication network established in
Section 3.1. When abnormal fluctuations occur during data transmission, the ARMA model’s transmission characteristics undergo modifications. Consequently, deviation analysis of the ARMA model’s transmission time series is required to identify network abnormalities.
In this network, the residual quantifies the transmission deviation and serves as the deviation measure. The residual sequence of network transmission characteristics is analyzed, which is based on the deviation between the current high-speed power line carrier communication transmission and normal data. At the same time, the network transmission residual is updated periodically. Since the residual series exhibits non-stationary behavior, differencing (first-order or higher) is applied to achieve stationarity before modeling. Following smoothing, the ARMA model simulates and captures the series fluctuations, enabling predictive analysis. The implementation process comprises the following steps:
First, the autocorrelation coefficient (ACF) and partial autocorrelation coefficient (PACF) are computed.
Second, by analyzing the autocorrelation and partial autocorrelation properties of the samples, an appropriate series is selected to fit the ARMA model, and its unknown parameters are estimated.
Subsequently, the model validity is verified; if validation fails, the model is re-selected for fitting. Upon successful validation, the model is optimized, and the best-performing model is selected from the validated candidates through comprehensive evaluation.
Finally, the optimal model is employed to forecast future time series.
After completing the fitting process, let the residual sequence of the high-speed power line carrier communication network transmission at time
be
. The anomalous deviation of the actual network transmission time series is calculated as
where
indicates the degree of deviation at the moment
;
indicates the mean value of the residuals at the moment
; and
denotes standard deviation. Among them, the deviation degree quantifies the abnormality between the actual network transmission time series and the expected or fitted values. A larger deviation indicates greater discrepancy between the transmission time series at time t and the expected/fitted value. The residual mean, calculated as the average of all residuals (differences between actual and fitted values) over a specified period, reflects the overall deviation level between actual transmission performance and expected/fitted values. The standard deviation measures data dispersion, where a higher value indicates greater fluctuations in the residual sequence, corresponding to increased divergence between actual and expected transmission time series. Conversely, a smaller standard deviation signifies reduced fluctuations and minimal differences.
3.3.2. Encryption and Decryption for High-Speed Power Line Carrier Communication Based on Generalized Two-Dimensional Polynomial Chaotic Mapping
Using a generalized two-dimensional polynomial chaotic mapping, the deviation
of the acquired high-speed power line carrier communication network is computed in conjunction with
Section 3.3.1. The key challenge to high-speed power line carrier communication [
17] is to resist the interference of power line noise and signal attenuation while improving the confidentiality and stability of communication.
Two-dimensional (2D) logistic mapping models:
where
and
represent the chaotic mapping state variables at time
;
and
denote the state variables at time
;
,
, and
denote the control parameters of the two-dimensional logistic mapping.
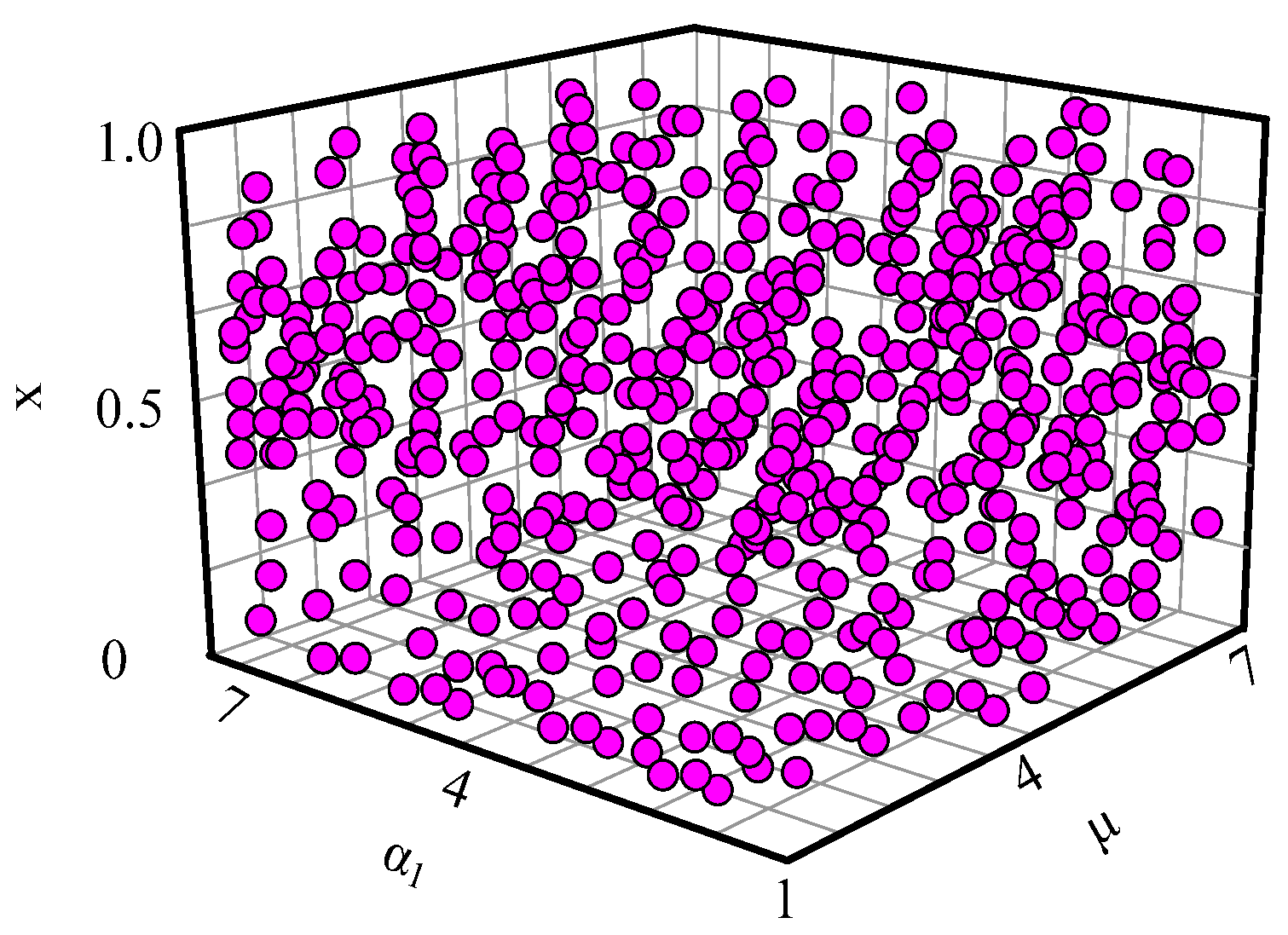
In standard two-dimensional logistic mapping, these parameters adjust the system’s nonlinear characteristics and dynamic behavior. For generalized two-dimensional polynomial chaotic mapping, they serve as key parameters governing the system’s complexity and unpredictability. The parameter selection criteria ensure system stability while enabling the generation of diverse chaotic sequences through appropriate choices of , , and , thereby significantly expanding the key space.
To enhance chaotic mapping dynamics, we propose a generalized two-dimensional polynomial chaotic mapping based on Formula (3), incorporating different control parameters and the maximum polynomial degree. The mathematical expression is
where
denotes the control parameters of the two-dimensional polynomial chaotic mapping;
denotes the highest polynomial degree; and
denotes the modal extraction factor. Specifically,
determines the mapping’s structural complexity, analogous to the highest polynomial degree, which governs the chaotic mapping’s complexity and topological characteristics. The parameter selection follows these criteria: increasing
enhances the mapping complexity, generating more intricate and unpredictable chaotic sequences, thereby strengthening encryption robustness. Similarly,
functions as a polynomial coefficient or supplementary adjustment parameter to fine-tune the chaotic mapping’s properties. The selection criterion requires choosing
values that maximize sensitivity to initial conditions and parameter variations, thus improving the encryption system’s resistance to minor perturbations. Through the dynamic adjustment of
and
, the encryption system adapts to evolving communication environments and requirements, significantly enhancing its robustness and reliability.
The generalized two-dimensional polynomial chaotic mapping model defined in Formula (4) generates a chaotic sequence for information transmission in the high-speed power line carrier communication network. The encryption and decryption keys are produced by integrating this chaotic sequence with the communication network’s deviation degree from
Section 3.3.1, implemented through the following procedure:
Step 1: Select an appropriate generalized two-dimensional polynomial chaotic system equation as the chaotic sequence generation algorithm for high-speed power line carrier communication networks [
18].
Step 2: Initialize the iteration with values to generate the initial chaotic sequence for the high-speed power line carrier communication network.
Step 3: Perform iterative computations from the current trajectory position to produce the chaotic sequence for transmitted information [
19].
Step 4: Generate encryption and decryption keys
and
by applying the communication network deviation
(from
Section 3.3.1) through
mapping and iteration cycles.
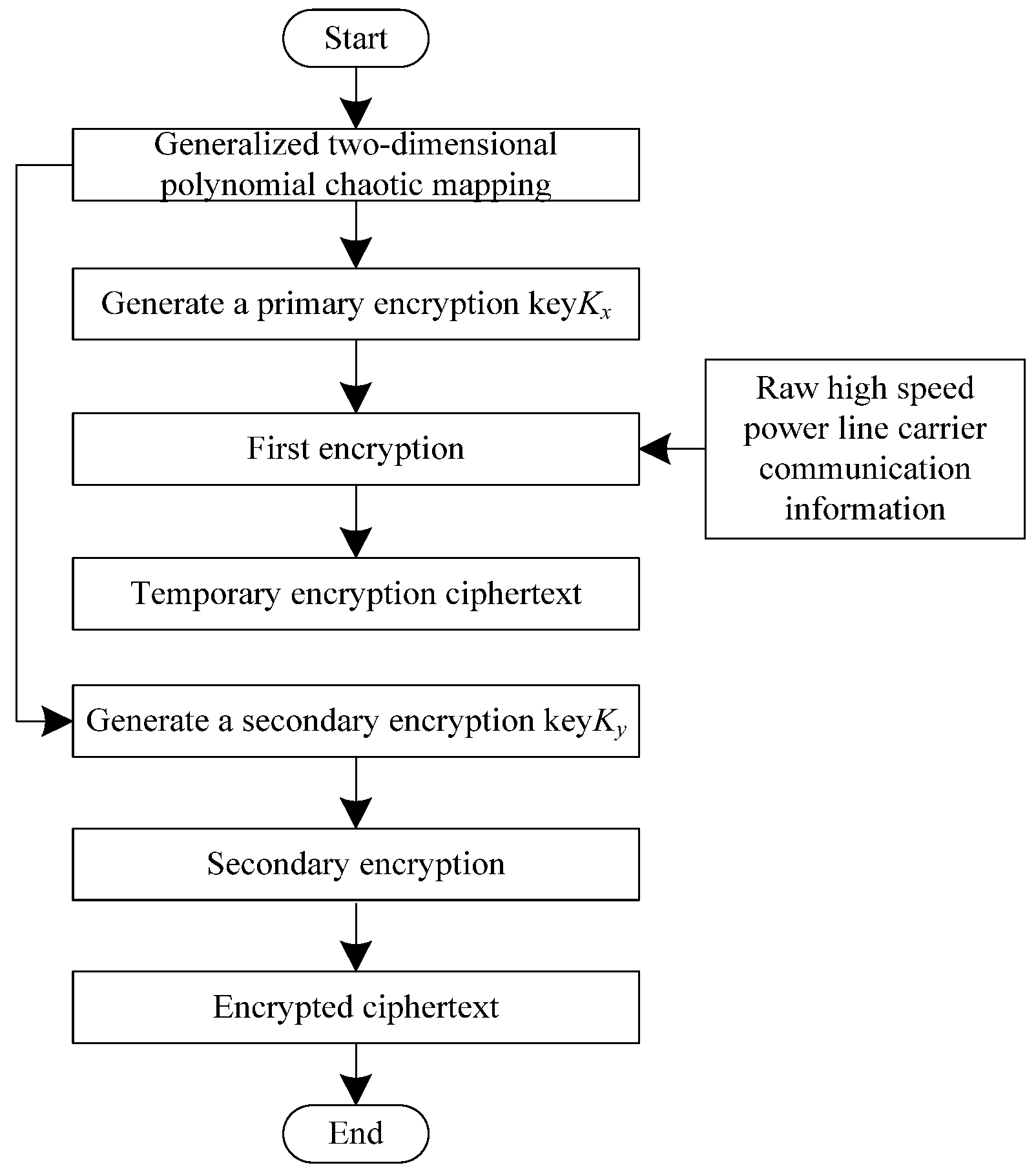
The system architecture of the encrypted high-speed power line carrier communication network, implementing generalized two-dimensional polynomial chaotic mapping for information transmission, is shown in
Figure 1.
The operational process of the encrypted high-speed power line carrier communication network implementing generalized two-dimensional polynomial chaotic mapping is as follows:
Step 1: Load the key generated by the generalized two-dimensional polynomial chaotic mapping equations.
Step 2: Encrypt the transmission information
of the high-speed power line carrier communication network using the following encryption formula:
Step 3: Generate the temporary ciphertext .
Step 4: Load the key generated by the generalized two-dimensional polynomial chaotic mapping equations.
Step 5: Perform secondary encryption on the temporary ciphertext
using the following formula:
Step 6: Generate the final ciphertext .
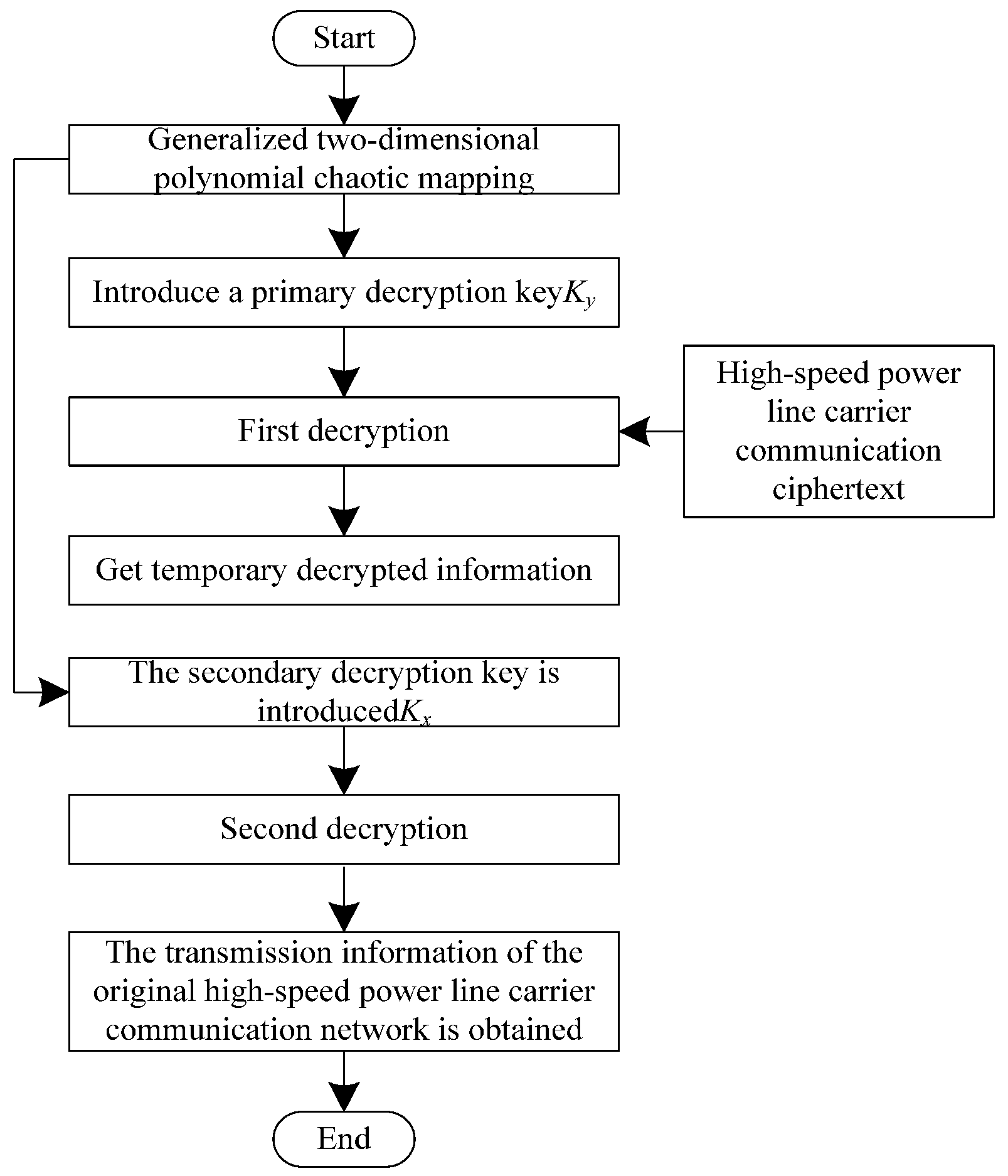
The decryption flow of the information transmitted by a high-speed power line carrier communication network using generalized two-dimensional polynomial chaotic mapping is shown in
Figure 2.
The decryption process using two-dimensional polynomial chaotic mapping for high-speed power line carrier communication networks is as follows:
Step 1: Extract the encrypted ciphertext
through sequential reading [
20].
Step 2: Load the decryption key generated by the generalized two-dimensional polynomial chaotic mapping equations.
Step 3: Decrypt the ciphertext
transmitted by the high-speed power line carrier communication network, using the following formula:
Step 4: Generate the decrypted temporary ciphertext .
Step 5: Load the decryption key generated by the generalized two-dimensional polynomial chaotic mapping equations.
Step 6: Perform secondary decryption on the intermediate ciphertext
using the following formula:
Step 7: The high-speed power line carrier communication network transmits information .
3.3.3. Confidential Transmission Scheme for High-Speed Power Line Carrier Communications Based on Generalized Two-Dimensional Polynomial Chaotic Mapping
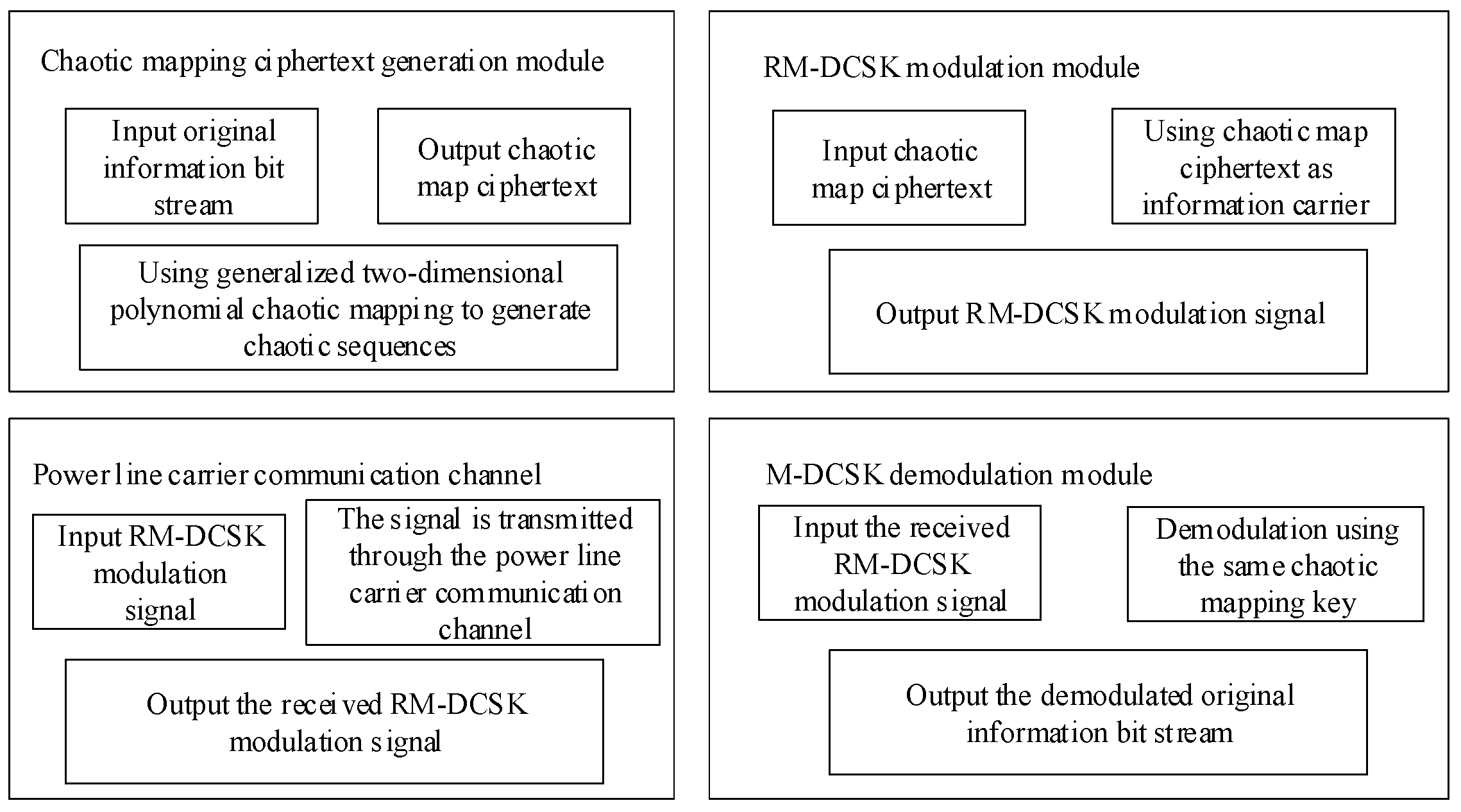
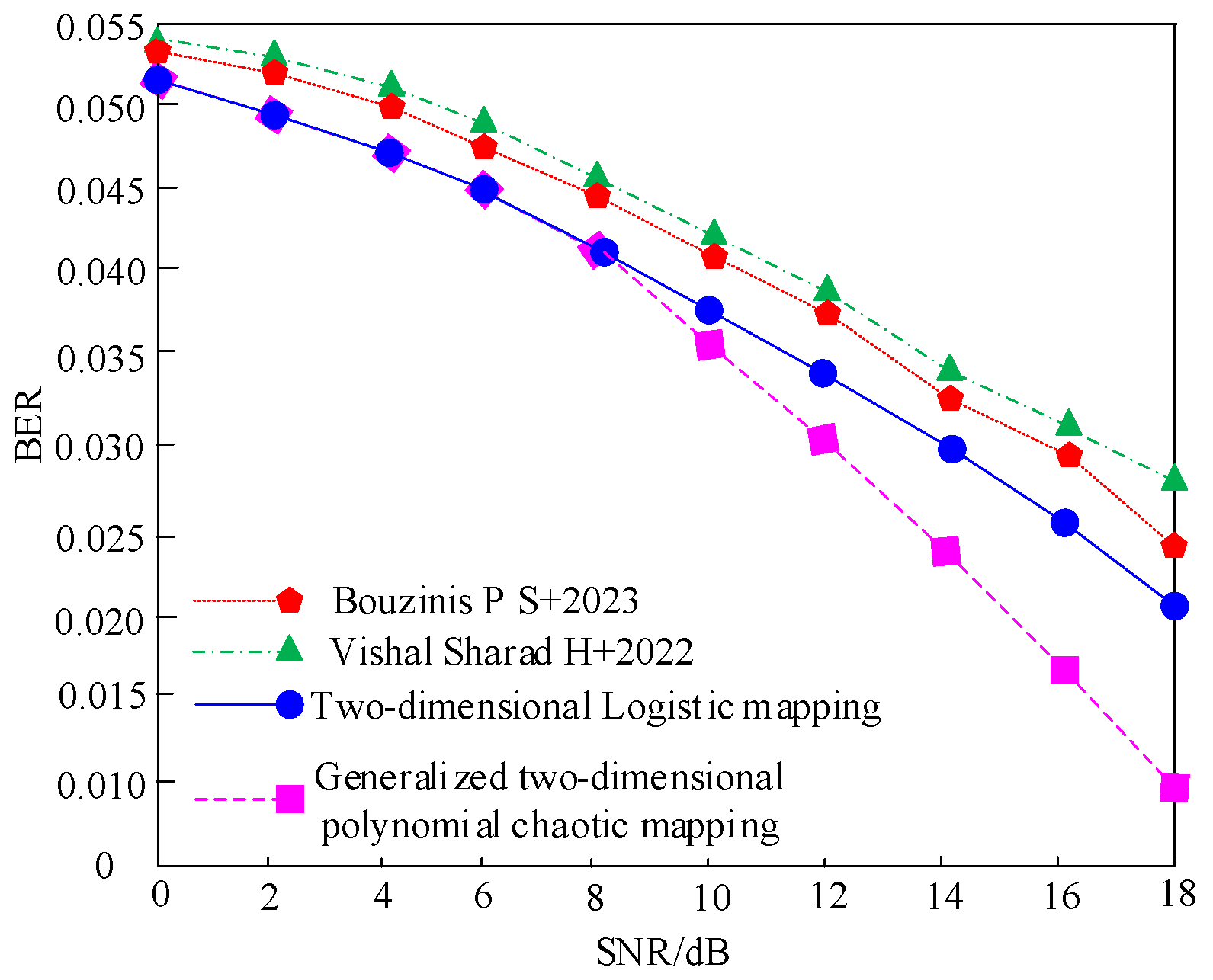
The inherent unpredictability and ergodicity of chaotic mapping make it particularly suitable for secure data transmission in networks. When ciphertext encrypted via the generalized two-dimensional polynomial chaotic mapping (
Section 3.3.2) is employed for data transmission, its output distribution critically impacts the bit error rate (BER) performance. The generalized 2D polynomial chaotic mapping proposed in this work achieves a near-uniform output distribution across the entire value space, thereby enhancing secure communication performance. By integrating the reference-modulated differential chaotic shift keying (RM-DCSK) with the ciphertext encrypted via the generalized 2D polynomial chaotic mapping (
Section 3.3.2), the RM-DCSK secure transmission scheme ensures robust and secure high-speed power line carrier communication.
The schematic diagram of the ciphertext interface of chaotic map and RM-DCSK modulation is shown in
Figure 3.
The advantages of a high-speed power line carrier communication secure transmission scheme based on generalized two-dimensional polynomial chaotic mapping over traditional secure transmission methods are as follows:
- (1)
Confidentiality enhancement
The scheme leverages the complex dynamic behavior of generalized two-dimensional polynomial chaotic mapping to generate cryptographically strong key sequences with high randomness and unpredictability. This significantly elevates the confidentiality level of transmitted data and substantially increases the computational complexity for potential attackers. The expanded key space in two-dimensional space provides superior anti-deciphering capability compared to traditional methods, effectively mitigating the risks of information leakage and malicious attacks.
- (2)
Anti-Interference performance
The proposed encryption scheme demonstrates exceptional resistance to power line channel impairments including electromagnetic interference, equipment noise, and signal attenuation. The inherent randomness and complexity of the chaotic mapping ensure consistent communication stability and reliability, while preserving data integrity and accuracy during transmission. This enhanced robustness enables reliable operation in highly dynamic communication environments.
- (3)
Transmission efficiency
The scheme fully exploits the high-bandwidth characteristics of power line carrier communication to support high-throughput, low-latency data transmission. Through optimized modulation/demodulation algorithms, the system achieves superior spectral efficiency and overall performance. This meets and exceeds the stringent requirements of smart grid applications, while providing scalable infrastructure for future power system advancements.
The RM-DCSK secure transmission scheme consists of transmitter and receiver components. The transmitter first encrypts the message bits with a key generated by the generalized 2D polynomial chaotic mapping in
Section 3.3.2, produces a high-speed power line carrier communication ciphertext, and then transmits the transmitter and receiver components. The receiver decodes the received ciphertext using the key generated by the generalized 2D polynomial chaotic mapping in
Section 3.3.2 to recover the message bits.
- (1)
Transmitting end:
serves as the information bits for
, and
represents the high-speed power line carrier communication ciphertext encrypted using the generalized 2D polynomial chaotic mapping described in
Section 3.3.2, with a line length of
. This is expressed as
, where
denotes the spreading index. The first time slot within the high-speed power line carrier communication network, established in
Section 3.1, is designated as the reference time slot. The ciphertext
acts as an information carrier, transmitting the bits
in the first time slot. The second time slot consists of two parts: the first part is the information transmitted in the previous time slot,
, serving as the message carrier, followed by the transmission of the bits
in the second time slot. The latter part is the high-speed power line carrier communication ciphertext of the current time slot,
, which satisfies
- (2)
Receiving end: When the receiver obtains the high-speed power line carrier communication ciphertext, it decrypts and recovers the original information bits using the key derived from the generalized two-dimensional polynomial chaotic mapping in
Section 3.3.2. The RM-DCSK confidential transmission scheme primarily relies on chaotic delay characteristics and non-coherent demodulation techniques. The received ciphertext deviates from the original due to noise interference during transmission across different high-speed power line carrier communication networks. In this paper, the additive white Gaussian noise (AWGN) channel model is adopted as the primary communication medium, and the channel interference is modeled as additive white Gaussian noise
. Therefore, the received ciphertext
is expressed as
Decryption is carried out using the key pairs generated by the generalized 2D polynomial chaotic mapping of
Section 3.3.2 to decode
, thereby recovering the original information bits and completing the confidential transmission of high-speed power line carrier communication.