With the rapid development of mobile application services using mobile computing, a variety of mobile applications (e.g., e-mail, social networks, online shopping, playing videos, and mobile games) are becoming more and more practical, which not only enhances people’s ways of life but also brings them more convenience [
1]. It is worth mentioning that data security and privacy in these services are vulnerable to various threats. The Check Point researchers declared in an analysis report that about 100 million users’ private data were leaked due to illegal intrusion from multiple Android applications, which included real-time databases, push notifications, and cloud key storage, and these leaked data may become “fat meat” in the eyes of malicious actors [
2,
3]. Attention must be given to security and privacy issues as soon as possible.
The two-factor authentication mechanism (i.e., password + smart card) can achieve user identity verification and session key agreement through protocol interaction. Legal users can access data securely via the session key, thus effectively protecting data security and privacy. However, existing two-factor authentication (2FA) protocols have a fly in the ointment. Given that mobile devices may have constrained resources, many 2FA protocols sacrifice security for higher efficiency and availability.
From the perspective of efficiency, to enhance computational efficiency and diminish the communication overhead, earlier researchers tried to design a practical authentication and key agreement (AKA) protocol by using the hash function and symmetric cryptography (e.g., [
9,
10,
11]). Gope et al. [
9] put forward a lightweight privacy-preserving authentication protocol in which the server does not need to carry out any time-consuming search operations to identify the tag. In addition, it does not need to store a secret key in the tag device. Yang et al. [
10] proposed an efficient, perfect forward secrecy-enabled AKA protocol on the basis of a lightweight hash function and XOR operation. Das et al. [
11] developed a remote user authentication protocol based on dynamic ID that allows the user to select and update their passwords randomly and does not maintain a verifier table. Nevertheless, it was found that the scheme in [
12] could not provide forward secrecy to secure the session key.
Public-key cryptography technology can be used to enhance the security of the AKA protocol [
12]. These public-key cryptography technologies (such as ECC [
13], RSA [
14], and bilinear pairings [
15]) are becoming widely used in the design of AKA protocols [
7,
16,
17], making it possible to enhance the safety of the session key and preserve user’s anonymity, etc. However, given the authentication performance, using a large number of public-key cryptography techniques throughout the process often leads to greater communication/storage consumption costs and lacks practicality. Accordingly, designing a 2FA protocol that balances security and availability is a challenge.
1.1. Related Work
Since the first 2FA protocol [
18] was presented in 1981, hundreds of research studies on 2FA protocols for mobile computing have been undertaken, such as on client–server (C/S) architecture [
16,
17,
19,
20] and multi-server environments [
21].
On the one hand, for the design of the technical protocol, Durlanik et al. [
16] proposed a 2FA protocol implementing a public key exchange mechanism with ECC for the session initiation protocol (SIP). They stated that the memory requirements and total execution times of the proposed protocol were greatly improved compared to non-elliptic approaches. For multi-server environments, Chatterjee et al. [
21] introduced a modified authentication protocol employing symmetric key encryption–decryption, the hash function, and a Chebyshev chaotic map and proved that the user can only use a single identity and password to manage authentication for different servers.
On the other hand, to enhance the security of the 2FA protocol, Wang [
22] provided a design philosophy, a corresponding solution, and a stronger attack model for 2FA protocols. Later, Wang et al. [
19] investigated the difficulty of designing identity-based privacy protection 2FA protocols. To enable trusted users (such as doctors or clinicians) to access sensor data from patients using wireless body area networks in the healthcare IoT, Fotouhi et al. [
20] designed a lightweight 2FA protocol. Additionally, security proof results showed that the presented protocol offered forward secrecy and could resist common attacks, including privileged insider attacks.
Furthermore, on the basis of cloud services, Vivekanandan et al. [
23] proposed a three-factor mobile user authentication protocol for distributed multimedia in 2020. They stated that their protocol provides extra characteristics, such as user choice-based service provider registration, initial user identity registration, and user revocation. Although the protocol [
23] can resist various known attacks, it has low authentication efficiency due to the high computational overhead.
To effectively achieve remote communication between users of specific medical services and service providers, Hsu et al. [
24] designed a three-factor, user-controlled, single-sign-on scheme with privacy protection and fast authentication. The results of the performance comparison indicated that their scheme had more security attributes and the lowest cost. However, unlike other schemes that store credentials on the server side, this scheme stores large quantities of user credentials on the client side, which results in low communication efficiency.
For end-to-end communication in 5G-enabled narrow-band IoT networks, Hsu et al. [
25] proposed a privacy-preserving authenticated key exchange protocol for a multi-server architecture that allows mobile users to log on to multiple servers with an easy-to-remember password and then compute a session key. Although they used elliptic curve cryptography with a small key size to improve communication efficiency, the protocol bears the risk of the session key being easily obtained by adversaries.
In 2021, in order to resist offline dictionary guessing attacks and continuous leakage of secrets from identity servers, Zhang et al. [
26] put forward a password-based threshold single-sign-on authentication protocol for mobile users. In addition, they designed a hybrid mechanism and mixed it with the proposed protocol to effectively thwart online dictionary guessing attacks. However, their solutions are not satisfactory in terms of performance and are not suitable for large-scale applications.
For distributed mobile cloud environments, Vivekanandan et al. [
27] put forward a privacy protection user authentication protocol using blockchain technology. By means of security analysis methods (e.g., BAN logic, informal analysis, the scyther tool, and the Automated Validation of Internet Security Protocols and Applications (AVISPA) tool), they examined the proposed protocol in relation to various common attacks and found that the proposed protocol could resist all known attacks. Similarly to [
26], Sastry and Reddy’s scheme also has the problem that its low performance is not conducive to enhancing the authentication phase efficiently.
To preserve user privacy in the IoT healthcare system, Lin et al. [
28] designed a smart card-based authentication protocol with a multi-server architecture. However, we found that no timestamp was used, and so the proposed protocol could not resist denial of service (DoS) attacks. On the basis of extended chaotic maps, Meshram et al. [
29] presented a 2FA protocol where a new value
is stored in the server during the authentication procedure. However, this protocol cannot resist desynchronization attacks. Despite the fact that user anonymity can be ensured with the protocols from [
28,
29], they cannot offer user un-traceability, since the messages in the proposed protocol contain various continual values with which attackers can guess the identities of users easily. Additionally, as the users’ private credentials are stored directly in the card without being shielded, Lin et al.’s scheme [
28] is vulnerable to stolen smart card attacks.
In 2022, in order to lessen the operation costs and hardware overhead caused by card readers, Meher and Amin [
30] designed a multi-factor authentication protocol that does not use smart cards and which is user-friendly and robust. Moreover, the proposed protocol addressed the problem of smart card loss/theft. The authors analyzed their authentication protocol in its response to several security threats, and the results showed that their scheme was safe.
For the multiple service providers in a 6G-assisted intelligent medical environment, Le et al. [
31] proposed a three-factor (i.e., smart card, password, and biometrics) authentication protocol with time-limited characteristics. In their scheme, service providers and patients can establish healthcare communications effectively and securely. However, user credentials are stored on the server side, which has potential risks. Moreover, the protocol is vulnerable to password-guessing attacks.
Considering the security threats from physical attacks, physically unclonable functions (PUFs) that can resist physical attacks are widely used to design robust authentication protocols [
32,
33]. These two research works both claimed that the proposed schemes could resist physical attacks, such as cloning attacks and physical tampering attacks.
1.2. Motivations and Contribution
In practical terms, a 2FA protocol (password + smart card as the two authentication factors) is supposed to offer comprehensive security and various desired characteristics.
Table 1 shows the four essential security goals [
34] that a 2FA protocol must meet.
However, current state-of-the-art 2FA protocols do not meet at least one of the four presented security goals. For instance, according to the acknowledged criteria and heuristic analysis of this paper, the protocol in [
35] cannot offer user un-traceability, the protocols in [
36,
37] cannot resist password-guessing attacks or provide session-key security, and the protocol in [
38] is vulnerable to counterfeiting attacks. Similarly, using a heuristic analysis with detailed attack steps, Shin et al. [
39] found that the static key and the client’s password in the protocols in [
40,
41] can be obtained by any attacker. To enhance security and maintain high efficiency, we developed a robust 2FA protocol for mobile computing. The key contributions of this paper are as follows:
- 1.
Design of a 2FA protocol for mobile computing
The “Fuzzy-Verifiers” [
42] and “Honeywords” [
42] techniques, which can be used to construct a fuzzy password verifier and effectively resist password-guessing attacks, were applied in our protocol. Further, based on the hash function and ECC, we designed a 2FA protocol that supports user registration, mutual authentication, and user password updating.
- 2.
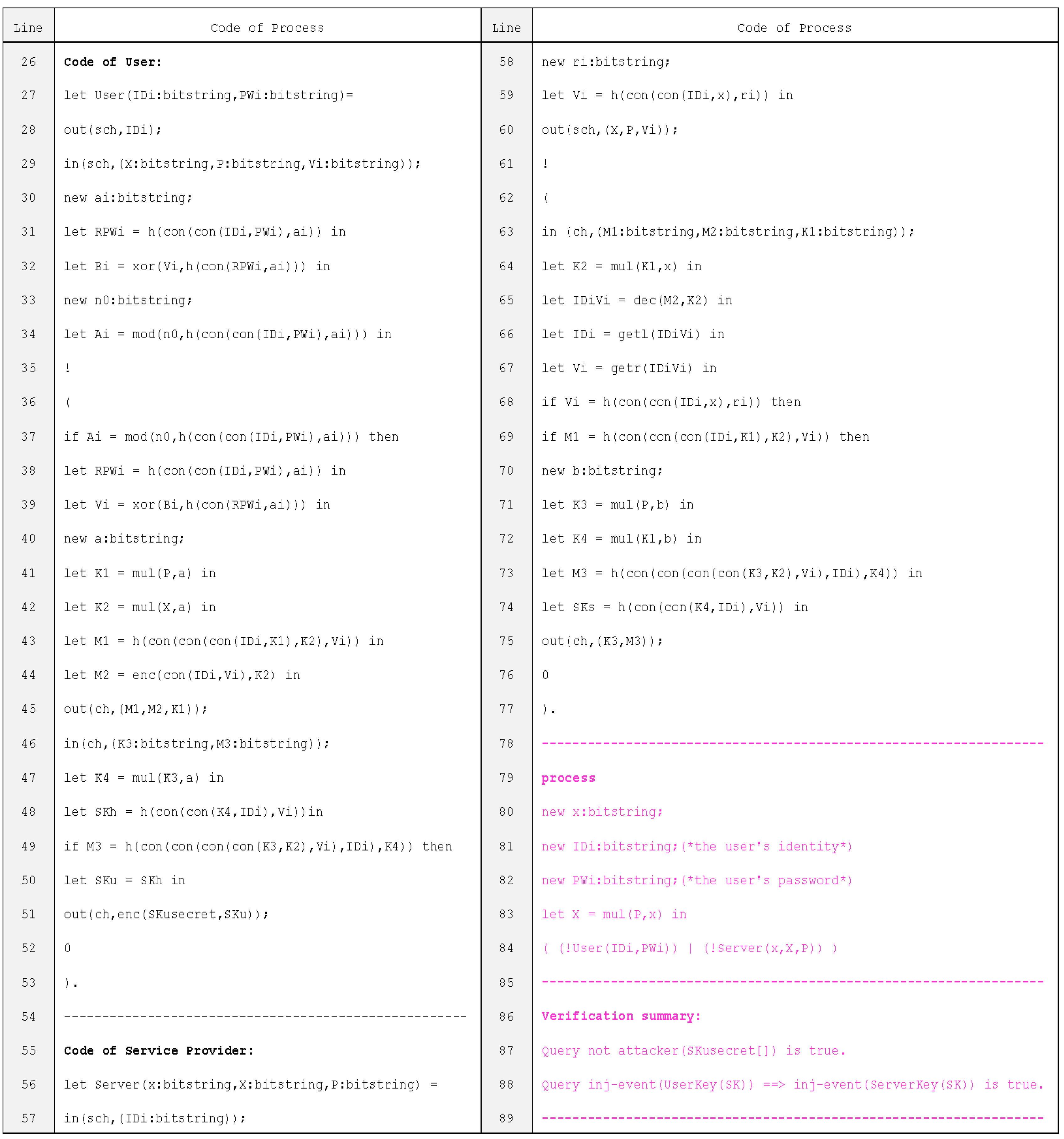
The semantic security of the 2FA protocol
The semantic security of the session key was proved with a security proof in our protocol. Additionally, through heuristic analysis, we demonstrated that the proposed protocol meets the ten security evaluation criteria. Furthermore, our protocol’s entity authentication, message confidentiality, and session key security were confirmed using the ProVerif [
43] tool.
- 3.
Performance analysis of the 2FA protocol
A comparative analysis of the functionality, communication, and computation cost of the proposed protocol was conducted with six common related protocols; i.e., those of Roy et al. [
37] (IEEE IoTJ’18), Islam et al. [
5] (IEEE IoTJ’18), and so on. A better balance between security and availability was achieved in the proposed protocol according to the comparison results.