Decentralized Inner-Product Encryption with Constant-Size Ciphertext
Abstract
:1. Introduction
1.1. Contribution
1.2. Organization
2. Preliminaries
2.1. Notation
2.2. Bilinear Maps and Complexity Assumption
- Bilinearity: For , and , the equation holds.
- Non-Degeneracy: Assume g is the generator of , then, .
- Computability: For , there exists an efficient algorithm to compute .
2.3. Definition of Decentralized Inner Product Encryption
2.3.1. System Model
2.3.2. Definition of DIPE
- . An authority in the system or a third party will run the algorithm. Taking as input a security parameter , the algorithm outputs a public parameter .
- . All authorities will run the algorithm. Taking as inputs a public parameter , and a number i, the algorithm outputs a master secret key and a public key of each authority, where i is the index of authority.
- . All authorities will run the algorithm. Taking as inputs a public parameter , a master secret key , a global identity and a predicate vector , the algorithm outputs a partial key of the private key associated with generated by authority. Note that the description of will be included in the partial keys.
- . A sender will run the algorithm. Taking as inputs a public parameter , all the public keys of each authority , a message M and an attribute vector , the algorithm outputs a ciphertext C associated with . Note that the description of will be included in the ciphertext.
- . A receiver will run the algorithm. Taking as inputs all the partial key of private keys of each authority , a ciphertext C and an attribute vector , the algorithm outputs a message M or ⊥.
- Correctness. For , ,, , where , we have that:
- -
- If , then.
- -
- If , then.
2.3.3. Security Model
- .chooses an attribute vector and sends to .
- .runs the Setup algorithm to generate and , where , is the index of authority. sends and to .
- .can make polynomially times queries of the following oracle.
- -
- KeyExtract oracle: sends a predicate vector and a global identity to , and returns the private key of . There is a restriction, that is, .
- .submits two distinct messages of the same length to . then randomly chooses and generates ciphertexts . Then, sends to .
- .Same as Phase1.
- .will output a bit and win the game if .The advantage of winning the game is defined as:
3. The Proposed Scheme
- Randomly choose bilinear groups of prime order p with a generator ;
- Choose an one-way hash function, ;
- Output the public parameter .
- Choose ;
- Choose ;
- Choose ;
- Output a public key of authority i, ;
- Output a master secret key of authority , .
- Return failure symbol ⊥ if ;
- Output the private key , where.
- Choose ;
- Output the ciphertexts as , where.
- If , perform the following computation; otherwise, return ⊥;
- Compute.
- Compute .
4. Security Proof
- Set . Define ;
- Choose ;
- Compute and ;
- For , , compute and following the AuthSetup shown in Section 3;
- Send to the public keys , and the master secret key s .
- Hash oracle:This oracle takes and (global identity) as input and outputs an element of . If there exists a record in the H-list, return . Otherwise, the oracle performs the following steps:
- If , then randomly choose and return to ;
- Choose ;
- Implicitly setby computingThis can be efficiently computed with the instance of q-DBDHE problem;
- Return to and store into the H-list.
- KeyExtract oracle:Upon receiving a vector and a global identity from , where (As shown in Definition 3, is not allowed to make a KeyExtract query with , otherwise can break the security trivially.) performs as follows. For , can be easily computed using the algorithm shown in Section 3 since knows . As for , it can be computed from the instance of the ℓ-DBDHE problem by the following steps:
- Query and set . Let , whereNote that can be found in the H-list;
- For , computeOne can note that, in the exponent of ,the only unknown term is . However, the coefficient of isThus, can be easily computed using the knowledge of and the instance of the ℓ-DBDHE problem;
- ComputeOne can note that the exponent of isAgain, the coefficient of the unknown term isTherefore, can be also computed using the knowledge of and the instance of the ℓ-DBDHE problem.
- Choose ;
- Set ;
- Compute
- Compute
- Output to .
5. Comparison
5.1. Asymptotic Comparisons
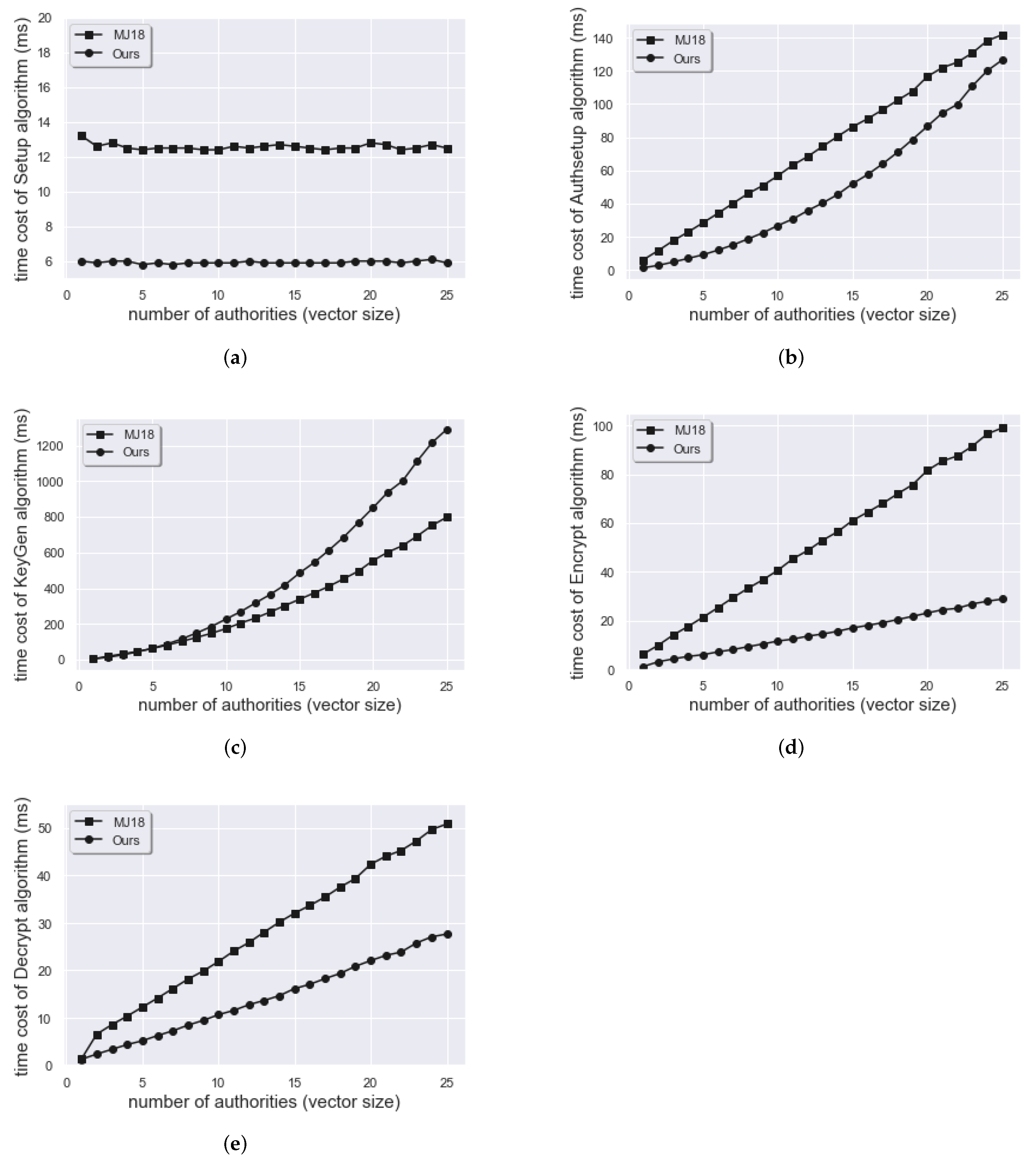
5.2. Experimental Result
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Shamir, A. Identity-Based Cryptosystems and Signature Schemes. In Advances in Cryptology; Blakley, G.R., Chaum, D., Eds.; Springer: Berlin/Heidelberg, Germany, 1985; pp. 47–53. [Google Scholar]
- Boneh, D.; Franklin, M. Identity-Based Encryption from the Weil Pairing. In Advances in Cryptology—CRYPTO 2001; Kilian, J., Ed.; Springer: Berlin/Heidelberg, Germany, 2001; pp. 213–229. [Google Scholar]
- Katz, J.; Sahai, A.; Waters, B. Predicate Encryption Supporting Disjunctions, Polynomial Equations, and Inner Products. In Advances in Cryptology—EUROCRYPT 2008; Smart, N., Ed.; Springer: Berlin/Heidelberg, Germany, 2008; pp. 146–162. [Google Scholar]
- Lewko, A.; Okamoto, T.; Sahai, A.; Takashima, K.; Waters, B. Fully Secure Functional Encryption: Attribute-Based Encryption and (Hierarchical) Inner Product Encryption. In Advances in Cryptology—EUROCRYPT 2010; Gilbert, H., Ed.; Springer: Berlin/Heidelberg, Germany, 2010; pp. 62–91. [Google Scholar]
- Attrapadung, N.; Libert, B. Functional Encryption for Inner Product: Achieving Constant-Size Ciphertexts with Adaptive Security or Support for Negation. In Public Key Cryptography—PKC 2010; Nguyen, P.Q., Pointcheval, D., Eds.; Springer: Berlin/Heidelberg, Germany, 2010; pp. 384–402. [Google Scholar]
- Park, J.H. Inner-product encryption under standard assumptions. Des. Codes Cryptogr. 2011, 58, 235–257. [Google Scholar] [CrossRef]
- Tan, Z.; Zhang, W. A Predicate Encryption Scheme Supporting Multiparty Cloud Computation. In Proceedings of the 2015 International Conference on Intelligent Networking and Collaborative Systems, Taipei, Taiwan, 2–4 September 2015; pp. 252–256. [Google Scholar]
- Kim, I.; Hwang, S.O.; Park, J.H.; Park, C. An Efficient Predicate Encryption with Constant Pairing Computations and Minimum Costs. IEEE Trans. Comput. 2016, 65, 2947–2958. [Google Scholar] [CrossRef]
- Zhang, Y.; Li, Y.; Wang, Y. Efficient inner product encryption for mobile clients with constrained computation capacity. Int. J. Innov. Comput. Inf. Control 2019, 15, 209–226. [Google Scholar]
- Soroush, N.; Iovino, V.; Rial, A.; Roenne, P.B.; Ryan, P.Y.A. Verifiable Inner Product Encryption Scheme. In Public-Key Cryptography—PKC 2020; Kiayias, A., Kohlweiss, M., Wallden, P., Zikas, V., Eds.; Springer International Publishing: Cham, Switzerland, 2020; pp. 65–94. [Google Scholar]
- Tseng, Y.F.; Liu, Z.Y.; Tso, R. Practical Inner Product Encryption with Constant Private Key. Appl. Sci. 2020, 10, 8669. [Google Scholar] [CrossRef]
- Fiat, A.; Naor, M. Broadcast Encryption. In Advances in Cryptology—CRYPTO’ 93; Stinson, D.R., Ed.; Springer: Berlin/Heidelberg, Germany, 1994; pp. 480–491. [Google Scholar]
- Acharya, K. Secure and efficient public key multi-channel broadcast encryption schemes. J. Inf. Secur. Appl. 2020, 51, 102436. [Google Scholar] [CrossRef]
- Chen, L.; Li, J.; Zhang, Y. Anonymous Certificate-Based Broadcast Encryption With Personalized Messages. IEEE Trans. Broadcast. 2020, 66, 867–881. [Google Scholar] [CrossRef]
- Li, J.; Wang, S.; Li, Y.; Wang, H.; Wang, H.; Wang, H.; Chen, J.; You, Z. An Efficient Attribute-Based Encryption Scheme With Policy Update and File Update in Cloud Computing. IEEE Trans. Ind. Inform. 2019, 15, 6500–6509. [Google Scholar] [CrossRef]
- Xue, L.; Yu, Y.; Li, Y.; Au, M.H.; Du, X.; Yang, B. Efficient attribute-based encryption with attribute revocation for assured data deletion. Inf. Sci. 2019, 479, 640–650. [Google Scholar] [CrossRef]
- Li, J.; Zhang, Y.; Ning, J.; Huang, X.; Poh, G.S.; Wang, D. Attribute Based Encryption with Privacy Protection and Accountability for CloudIoT. IEEE Trans. Cloud Comput. 2020, 1. [Google Scholar] [CrossRef]
- Katz, J.; Maffei, M.; Malavolta, G.; Schröder, D. Subset Predicate Encryption and Its Applications. In Cryptology and Network Security; Capkun, S., Chow, S.S.M., Eds.; Springer International Publishing: Cham, Switzerland, 2018; pp. 115–134. [Google Scholar]
- Chatterjee, S.; Mukherjee, S. Large Universe Subset Predicate Encryption Based on Static Assumption (Without Random Oracle). In Topics in Cryptology—CT-RSA 2019; Matsui, M., Ed.; Springer International Publishing: Cham, Switzerland, 2019; pp. 62–82. [Google Scholar]
- Tseng, Y.F.; Gao, S.J. Efficient Subset Predicate Encryption for Internet of Things. In Proceedings of the 2021 IEEE Conference on Dependable and Secure Computing (DSC), Edinburgh, UK, 22–24 June 2021; pp. 1–2. [Google Scholar] [CrossRef]
- Rajan, M.; Varghese, A.; Narendra, N.; Singh, M.; Shivraj, V.; Chandra, G.; Balamuralidhar, P. Security and Privacy for Real Time Video Streaming Using Hierarchical Inner Product Encryption Based Publish-Subscribe Architecture. In Proceedings of the 2016 30th International Conference on Advanced Information Networking and Applications Workshops (WAINA), Crans-Montana, Switzerland, 23–25 March 2016; pp. 373–380. [Google Scholar] [CrossRef]
- Xiong, H.; Yang, M.; Yao, T.; Chen, J.; Kumari, S. Efficient Unbounded Fully Attribute Hiding Inner Product Encryption in Cloud-Aided WBANs. IEEE Syst. J. 2021, 1–9. [Google Scholar] [CrossRef]
- Zhang, L.; Wang, Z.; Mu, Y.; Hu, Y. Fully Secure Hierarchical Inner Product Encryption for Privacy Preserving Keyword Searching in Cloud. In Proceedings of the 2015 10th International Conference on P2P, Parallel, Grid, Cloud and Internet Computing (3PGCIC), Krakow, Poland, 4–6 November 2015; pp. 449–453. [Google Scholar] [CrossRef]
- Huang, K.C.; Chen, Y.C. Privacy Preserving Outsourced Data Integration from Inner Product Encryption. In Proceedings of the 2021 International Symposium on Intelligent Signal Processing and Communication Systems (ISPACS), Hualien City, Taiwan, 16–19 November 2021; pp. 1–2. [Google Scholar] [CrossRef]
- Michalevsky, Y.; Joye, M. Decentralized Policy-Hiding ABE with Receiver Privacy. In Proceedings of the 23rd European Symposium on Research in Computer Security, ESORICS 2018, Barcelona, Spain, 3–7 September 2018; pp. 548–567. [Google Scholar]
- Chase, M. Multi-authority Attribute Based Encryption. In Theory of Cryptography; Vadhan, S.P., Ed.; Springer: Berlin/Heidelberg, Germany, 2007; pp. 515–534. [Google Scholar]
- Lewko, A.; Waters, B. Decentralizing Attribute-Based Encryption. In Advances in Cryptology—EUROCRYPT 2011; Paterson, K.G., Ed.; Springer: Berlin/Heidelberg, Germany, 2011; pp. 568–588. [Google Scholar]
- Zhang, L.; Gao, X.; Kang, L.; Liang, P.; Mu, Y. Distributed Ciphertext-Policy Attribute-Based Encryption With Enhanced Collusion Resilience and Privacy Preservation. IEEE Syst. J. 2021, 1–12. [Google Scholar] [CrossRef]
- Boneh, D.; Gentry, C.; Waters, B. Collusion Resistant Broadcast Encryption with Short Ciphertexts and Private Keys. In Advances in Cryptology—CRYPTO 2005; Shoup, V., Ed.; Springer: Berlin/Heidelberg, Germany, 2005; pp. 258–275. [Google Scholar]
- Boneh, D.; Hamburg, M. Generalized Identity Based and Broadcast Encryption Schemes. In Proceedings of the International Conference on the Theory and Application of Cryptology and Information Security, Melbourne, Australia, 7–11 December 2008. [Google Scholar]
- Canetti, R.; Halevi, S.; Katz, J. Chosen-Ciphertext Security from Identity-Based Encryption. In Advances in Cryptology—EUROCRYPT 2004; Cachin, C., Camenisch, J.L., Eds.; Springer: Berlin/Heidelberg, Germany, 2004; pp. 207–222. [Google Scholar]
- Fujisaki, E.; Okamoto, T. Secure Integration of Asymmetric and Symmetric Encryption Schemes. In Advances in Cryptology—CRYPTO’ 99; Wiener, M., Ed.; Springer: Berlin/Heidelberg, Germany, 1999; pp. 537–554. [Google Scholar]
- Fujisaki, E.; Okamoto, T. Secure Integration of Asymmetric and Symmetric Encryption Schemes. J. Cryptol. 2011, 26, 80–101. [Google Scholar] [CrossRef]
- Koppula, V.; Waters, B. Realizing Chosen Ciphertext Security Generically in Attribute-Based Encryption and Predicate Encryption. In Advances in Cryptology—CRYPTO 2019; Boldyreva, A., Micciancio, D., Eds.; Springer International Publishing: Cham, Switzerland, 2019; pp. 671–700. [Google Scholar]
- Yamada, S.; Attrapadung, N.; Hanaoka, G.; Kunihiro, N. Generic Constructions for Chosen-Ciphertext Secure Attribute Based Encryption. In Public Key Cryptography—PKC 2011; Catalano, D., Fazio, N., Gennaro, R., Nicolosi, A., Eds.; Springer: Berlin/Heidelberg, Germany, 2011; pp. 71–89. [Google Scholar]

| Notation | Description |
|---|---|
| a bilinear group with prime order p | |
| a bilinear group by pairing of the element of | |
| e | a bilinear mapping; |
| g | a generator of |
| n | total number of authorities |
| ℓ | the length of predicate/attribute vector |
| ith authority | |
| public parameter | |
| public key of authority i | |
| master secret key of authority i | |
| a predicate vector | |
| an attribute vector | |
| an identity of a receiver | |
| M | a message |
| Encryption Cost | Decryption Cost | |
|---|---|---|
| [3] | ||
| [8] | ||
| [5] | ||
| [11] | ||
| [25] | ||
| Ours |
| Ciphertext Length | Private Key Length | |
|---|---|---|
| [3] | ||
| [8] | ||
| [5] | ||
| [11] | ||
| [25] | ||
| Ours |
| Decentralization | Confidentiality | Security | Group | Complexity | |
|---|---|---|---|---|---|
| Model | Order | Assumption | |||
| [3] | No | CPA | STD | Composite | SD |
| [8] | No | CPA | STD | Prime | -DBDH |
| [5] | No | CPA | STD | Prime | ℓ-DBDHE |
| [11] | No | CPA* | STD | Prime | M-DDH |
| [25] | Yes | CPA | ROM | Prime | k-Lin |
| Ours | Yes | CPA | ROM | Prime | ℓ-DBDHE |
| CPU | Intel(R) Core(TM) i7-10875H CPU @ 2.30 GHz |
|---|---|
| Memory | 4 GB |
| OS | Ubuntu-16.04 (64-bit) |
| Package | Python Charm-Crypto (v0.43) library |
| Pairing group | SS512 |
| CPU | Intel(R) Core(TM) i5-8257U CPU @ 1.40 GHz |
|---|---|
| Memory | 2 GB |
| OS | Docker:Debian10 |
| Package | pbc-0.5.14 |
| Pairing group | Type a1 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Tseng, Y.-F.; Gao, S.-J. Decentralized Inner-Product Encryption with Constant-Size Ciphertext. Appl. Sci. 2022, 12, 636. https://doi.org/10.3390/app12020636
Tseng Y-F, Gao S-J. Decentralized Inner-Product Encryption with Constant-Size Ciphertext. Applied Sciences. 2022; 12(2):636. https://doi.org/10.3390/app12020636
Chicago/Turabian StyleTseng, Yi-Fan, and Shih-Jie Gao. 2022. "Decentralized Inner-Product Encryption with Constant-Size Ciphertext" Applied Sciences 12, no. 2: 636. https://doi.org/10.3390/app12020636
APA StyleTseng, Y.-F., & Gao, S.-J. (2022). Decentralized Inner-Product Encryption with Constant-Size Ciphertext. Applied Sciences, 12(2), 636. https://doi.org/10.3390/app12020636






