1. Introduction
Over the past seven decades, there has been an improvement in gender equality laws worldwide. This has brought about developments in the management and prevention of sexual harassment and harassment on the grounds of sex. Sexual harassment and harassment on the grounds of sex have been defined by the European Directive 2006/54/CE (Article 2). The first concept is defined as any form of unwanted verbal, non-verbal or physical conduct of a sexual nature that occurs with the purpose or effect of violating the dignity of a person, in particular when creating an intimidating, hostile, degrading, humiliating, or offensive environment. The second term is defined as when unwanted conduct related to the sex of a person occurs with the purpose or effect of violating the dignity of that person, and of creating an intimidating, hostile, degrading, humiliating, or offensive environment.
In the same vein, the Council of Europe Convention on preventing and combating violence against women and domestic violence (presented in 2011 and in effect since 1 August 2014), known as the Istanbul Convention, defines sexual harassment and harassment on the grounds of sex in the same terms as in the European Directive.
The prevention and management of sexual harassment have been widely addressed in organizations, corporations, companies, but also in other types of structures, such as higher education institutions. In this sense, we are going to study the different measures that can be adopted by universities to manage these situations.
In Spain, the scenario has been defined thanks to the passing of the Organic Law on Measures regarding Comprehensive Protection against Gender-Based Violence (LO 1/2004, 28 December), and some years later, the Organic Law for Effective Equality between Women and Men (LO 3/2004, 22 March). The Organic Law of Universities (LO 6/2001, 21 December) completes this Spanish scenario, introducing the principle of equality by indicating the mandatory introduction of equal opportunity management units. Many of these units have developed protocols to properly handle situations of harassment. They will be the subject of analysis later in this paper.
There has gradually been greater awareness in all universities about the severity of sexual harassment and gender-based harassment, and the necessity of having a way to prevent and manage these situations. As a result, many of the public universities (and as a case of study, in Spain) have developed specific protocols for this issue within the last years (
Biglia et al. 2017). These protocols are focused on addressing complaints, however, have a marked punitive character, and in many cases include awareness-raising measures, with the prevention of harassment situations as something secondary. As a result, these situations are still taking place, and some women do not feel protected by this management tool.
Unfortunately situations of sexual harassment are still taking place. Rates between 0.0003 and 0.0015 assaults per enrollment have been achieved in the last years at U.S. universities (
Streng and Kamimura 2015), so this shows the need to continue the study of the sexual harassment protocols and suggest measures for improvement. As an example, in Spain, the protocols for sexual harassment are of very recent implementation, and although the reception to these types of initiatives has been very good, the situations of harassment have continued to occur (
Jara 2018).
There is sexual harassment in universities which takes diverse forms. One of the manners in which that perpetrators harass includes utilizing Trojan or backdoor programs. This software permits remote access to a victim’s PC or cell phone so as to assume control of it. Along these lines, perpetrators can take private photos, access the incorporated camera and other data that they could use for coercion or blackmail.
A diagnosis of the current situation related to the actual protocols will be made in this work, and some measures to improve the performance of universities will be proposed.
The paper is structured as follows. After defining the aims of the study, previous works on the subject are reviewed. After this, some proposals are explained, and the usual actions developed in university environments in response to sexual harassment and harassment on the grounds on sex are described. The methodology includes a poll applied in Spanish public universities and data analysis. We finish with an analysis of the results, and then broadly discuss the results of the survey and the implemented measures. Finally we draw conclusions, including suggestions for future works.
2. Subject of Study and Aims
The subject of study is the set of measures taken to manage sexual harassment and harassment on the grounds of sex in public universities, often structured as a protocol. A protocol is defined as a detailed sequence of procedure. This definition, although brief, gives us an idea of what we can expect; an ordinance with different phases and stages, which forms a sequence, and directs the actions of those who consult it. A protocol should consider, firstly, all circumstances which could arise, and offer solutions to problems, taking advantage of the resources that are available in a particular environment.
We are going to review the situation with regard to protocols for managing sexual harassment, as has been done in previous works. For this, an exhaustive bibliographic review has been carried out, and with this, a series of proposals have been synthesized to be integrated as good practices which are advisable to be put into practice in the different institutions of higher level.
We will describe the existing protocols in Spanish public universities, their characteristics, and the way they are implemented. To this end, an in-depth reading of all the protocols that have been carried out in Spanish universities has been done, and it has been completed with a survey to check the degree of implementation of these measures.
The final aim of this paper is to consider the question of whether the existing protocols in public universities fulfil these episodes of sexual harassment, and to indicate a series of good practices which could complement those in place.
3. State of the Question
Situations of sexual harassment and harassment on the grounds of sex in the university domain have been studied before, at a national and international level.
There are some previous works that have elaborated on the specific handling of sexual harassment and harassment on the grounds of sex, but only consider them in the workplace (
Monfort 2013). Even though this can be very useful for university personnel, it fails to consider the institution as a whole, and students in particular. For this reason, we are more interested in work that encompasses the specific characteristics of the academic environment. Papers that date back more than 20 years (
Roark 1994) tend to be more focused on framing definitions and explaining the characteristics of the university community.
There are a number of intervention projects focusing on sexual violence in Spain. Safo is a group of women from the Universidad de Barcelona, who belong to the Community of Researchers on Excellence for All. This group, created in 1999, undertakes substantive practical action as regards the handling of sexual harassment in universities. Of the 6995 projects subsidized by the Instituto de la Mujer y para la Igualdad de Oportunidades (Women’s Institute for Equal Opportunity) between 1983 and 2005, only Safo received funding to research recognition of the problem in 2005 (
Puigvert et al. 2017).
Aguilar Ródenas et al. (
2009) suggested actions to consider, listing measures to prevent violence against women in universities, although they did not distinguish between sexual harassment and harassment on the grounds of sex.
More recently, USVreact (JUST/2014/RDAP/AG/VICT/7401), co-financed by the European Commission (Directorate-General for Justice, Rights, Equality and Citizenship Program, DAPHNE), and coordinated by Brunel University in London, includes seven partners and many collaborating partners from seven European countries. Its objective is to design training models intended to help university personnel recognize situations of sexual harassment, and provide a first response (
Biglia et al. 2017).
USVreact analyzes university policies in answer to situations of gender violence at an international level, and offers ideas for designing courses adapted to the specific institutional culture of each participating university. The universities that are partners in the project direct and evaluate training of up to 80 professionals for each session from their institutions, and share their results with the other participating groups. The project began in March 2016, and terminated with the presentation of its results at an international conference in London, in November 2017. Although this is the closest project to being at an international level, there were limitations. The participating Spanish universities represented only one autonomous region (Catalonia), and the project focused entirely on training and did not explore specific measures to deal with harassment.
On 10 April 2018, ‘Pikara Magazine’ (
Jara 2018), published research about the efforts taken against harassment in Spanish public universities. After three months of research, during which all fifty public universities in Spain were contacted, a report entitled ‘Mapa sobre acoso en las universidades’ (Map of Harassment in Universities) was published. It included information on a national level, and a general overview of how, and to what extent, male violence is being confronted in each university. A framework of studies on this subject has thus been previously established.
Disregarding these examples, we need to add that the reasonable use of managing harassment as far as information and communication technologies (ICT) is constrained (
Rodríguez-Rodríguez et al. 2020). This is in any event, considering that these advances have changed the manner by which numerous individuals, specifically youngsters, impart and communicate (
Flores and Browne 2017).
By and by, past researchers have offered promising prospects in this area, surrounded by the activity of associations, organizations, or the government.
STATT (
2014), a Hong-Kong-based system of specialists working with respect to worldwide turn of events and security issues, remembered some fascinating activities for their report. In this work, STATT proposed different explicit activities to cultivate satisfactory administration of inappropriate behavior, for example, the starting of HarassMap in Egypt in 2010. This is a volunteer-based activity where individuals from the general population can report an occurrence of sexual harassment by sending an SMS, email, Facebook, or Twitter post, or by rounding out an online report structure. These reports are then mapped on the HarassMap. STATT is additionally associated with creating data and concentrating better approaches for imparting.
With their crusade Stop Online Abuse, the UK government has attempted comparable activities. This campaign is trying to help survivors of online maltreatment, specifically women and lesbian, gay, bisexual, transgender and intersex (LGBTI) individuals. In any case, this campaign doesn’t expand farther than this, for example, to interconnect other potential, circumstances, or conditions of harassment.
Among other progressively transversal activities, we can feature some projects, for example, that of the World Bank, which has moved toward the issue of harassment from the zones of public transport to those of health, justice, and education. As for ICT, the World Bank supported and composed—in conjunction with a number of local in-nation associations (some of them universities)—a weekend-long hackathon occasion in January 2013, that spread over Central America and Washington DC, with the aim to elevate ICT applied to overseeing and maintaining a strategic distance from brutality against women (
William and Corman 2013). They brought together gender equality specialists and several volunteer innovation engineers who gave their time and gifts to making innovation based answers for tackling abusive behavior at home. Toward the end of the two days, the volunteers had created model applications running from SMS-based alarm administrations, online projects, and applications for use on Facebook, directed to youngsters in danger.
We need also to bear in mind that there are related issues to the harassment. People’s perception of sexual harassment contributes to its continuation (
Ferrer-Pérez and Bosch-Fiol 2014). A survey of 1693 people at the Universidad de Illes Balears found that sexual harassment is classified differently depending on a person’s sex and their position in the university community. In addition, harassment is often not reported, as reflected in the
Macroencuesta de Violencia contra la Mujer (Macro Survey on Violence Against Women) in 2015 (
Miguel Luken 2015).
Schubert (
2015) noted that patriarchal power structures are firmly established in Spanish universities.
So, there are numerous barriers when evaluating universities on this subject, as the lack of reports or complaints about these situations, sometimes due to a failure to identify a situation as harassment (
Valls et al. 2016). The aim of this paper is to identify the existing strategies and complete the view of the management of sexual harassment.
4. Discussion of Response Mechanisms
This section describes proposals and specifics. Universities can implement the suggestions in the area of their competences, in order to avoid and manage harassment incidents. Some of these proposals are outlined by previous works, and some others are shaped by the authors after identifying gaps in the strategies adopted by the universities.
4.1. General Considerations about the Content and Focus of Sexual Harassment and Harassment on the Grounds of Sex Protocols in Public Universities
The objective of a response protocol for the victims of sexual harassment or harassment on the grounds of sex is to establish an itinerary which avoids distancing victims from public institutions and placing them in private ones (
Sagot 2002). The development of a path which considers all possible variations is very important, as is its evaluation and the monitoring of its phases and procedures.
It is recognized that the phases that comprise a protocol should not be structured as a linear process, but should plan ahead and describe the possible sequence of multiple pathways that a victim could follow in the process of reporting the event and looking for help (
Ranney 2000). The processes given in protocols for the management of situations of harassment are varied. This variance goes beyond the logical differences that could exist in institutions in terms of student body make up and the number or type of degrees offered. The different phases of management process and their details should be compared between different universities. In this way, they would be able to broaden their perspectives and come to a consensus which could favor inter-institutional cooperation. A general procedure has been abstracted in the analysis phase of this work, which can serve as a model or guide.
In addition to the above, protocols are principally conceived as a group of actions with the aim of responding to the victim when an act of aggression has occurred. It has an assistive character, and in some instances, punitive, but it is also possible to design sequences of procedures to prevent aggression.
There can be danger (and advantage) when using the so-called “fast-track procedure” as a resolution phase in some universities. Although it has been designed as a rapid process to avoid greater suffering for the victim, it is worrying that the result of the process could be agreements that the victim does not want, and discouragement with regard to reporting the incident, or making it known to others. This type of procedure should not be carried out in an environment of power, rather than assistance. This could inhibit people and foster revictimization. It is necessary to avoid questioning the victim in a way that could lead to them feeling that they are partly to blame (
Heras González and Padilla Richart 2014).
Although the protocols are directed specifically towards serious incidents such as sexual harassment and harassment on the grounds of sex, there are also cases of harassment due to sexual orientation, identity, ethnic background, origin, functional diversity, religion, and so on, in universities. A cross-sectional view is necessary, and must include some of these perspectives, as at the Universidad Miguel Hernández, which recognizes sexual orientation as a cause of harassment.
To conclude, designing a protocol should take into account the scope of the procedures and the level of coordination and communication. It is necessary to avoid duplicating resources and effort, and provide specific training for the professionals who intervene.
4.2. Area of Assistance
4.2.1. Increase Actions with the Victim
Integral assistance to the victim should be assured. This should be transversal and cover various aspects. These are summarized below, along with their relationship to the services universities normally provide.
Support throughout the entire process, including after the application of the protocol.
Psychological and medical assistance if the situation requires.
Protection and safety, at least on the campus grounds.
Legal assistance.
Assistance in the use/protection of information and communication technologies.
Other assistance the victim may require.
4.2.2. Actions with the Aggressor
Surveillance mechanisms should be designed for the aggressor so that while respecting their freedom and privacy, new events can be avoided. The aggressor’s environment should be approached with caution in order to anticipate possible future incidents. If the aggressor is willing, psychological assistance could help to manage and diagnose the reasons that led to committing an act of harassment. Consciousness-raising courses and therapy in terms of gender, which are designed to modify undesirable behavior, could be positive.
4.3. General and Organizational Scope
4.3.1. Minimum Budget Requirements
A minimum amount of money is needed to allow the development of the procedures outlined in the protocols. It is necessary to be included on a budgetary allocation in the annual budget of every university, which could ensure the development and implementation of long-term policies.
4.3.2. Revision and Evaluation of Protocols
Many of the universities do not evaluate or revise their protocols. This is something to be concerned about. It is necessary for mechanisms to be put into place to revise and evaluate university protocols; planning audits should have the following as guidelines:
The evaluations should be carried out compulsorily and with a fixed time period which does not exceed one year.
Internal control mechanisms should be insured and introduced in the description of the protocol.
External controls are necessary, which involve a global audit. This should be performed by people who are not involved in carrying out the protocol. If possible, they should be from outside the university to guarantee their independence.
Feedback from people who have made use of the activated protocol should be included in the evaluation process, with the objective of identifying its strengths and weaknesses.
4.3.3. The Creation of Task Groups
As well as people who have used the protocol procedures, the evaluation should include groups who could be especially vulnerable to harassment or aggression in the university community.
Creating task groups with all the implicated parties could lead to debate, which enriches the handling of the problem by considering ideas provided by groups who could be vulnerable to sexual harassment or harassment on the grounds of sex. At the same time, worker and student representatives, who are responsible for safeguarding these groups’ rights, could give valuable input. Dynamic work should be carried out in these groups through periodic meetings and presentations of proposals. They should have access, with due diligence, to information about events which have been reported, insuring the anonymity of the people involved. Periodic surveys of the university community should be considered. In this way, people’s perception of the way harassment situations are managed can be evaluated.
The participation of these groups will also help to avoid any sense of disconnection between managers’ experiences and feelings of helplessness felt by victims.
4.3.4. Safety and Surveillance
Creation of Safe Spaces (Purple Points)
These are areas that are managed by women, where victims of aggression are helped (
Dame and Grant 2001). It must be kept in mind that the space is not neutral, and the sex of the person who is giving help, and gender relations should be considered.
These initiatives have been implemented at events where there are large crowds of people, and in which alcohol consumption leads to numerous situations of sexual harassment. In this context, it is necessary that victims are able to count on an area of support. Universities organize a number of celebrations which have these characteristics, such as concerts, festivals, and the beginning of the term. The creation of safe spaces has been developed in different contexts, such as in sporting events. In this case, it is envisioned as an exclusively feminine space, in which the absence of male aggressors is insured. Designing specific sporting events for women could be put into practice at universities.
It is necessary to consider whether safe spaces should be mixed gender, and where men who may have suffered harassment, including for their sexual orientation, can also seek help.
Consciousness-Raising and Surveillance Groups during Events
Groups which safeguard women’s safety could be organized, and other groups could report on and attempt to impede harassment during specific events. At the same time, these people could staff safe spaces to provide information or assistance to possible victims. They would gather detailed information on the aggression, with the aim of informing the security services and drawing up a report at the end of the event.
Increase Surveillance and Safety. Presence and Video Surveillance
In the daily life of the university, or more importantly, during multitudinous events such as festivals, concerts or sporting events, it is advisable to plan for surveillance in order to prevent harassment, and if it occurs, to stop it as quickly as possible. A professional security service, made up of men and women with training in gender issues should therefore be present. This is essential, since incidents of sexual harassment have sometimes been given less importance by security staff. They may consider these incidents to be examples of “boys being boys”, and therefore, nothing serious.
There should be sufficient video surveillance during events and in daily life. This would make it possible to control non-authorized, or after-hours access to centers, and to intervene when harassment is reported, or, where sexual aggression did take place, to identify the aggressor. The measures contained in Organic Law 15/1999, 13 December on Personal Data Protection, and the European Regulation on Data Protection must be taken into account. It should also be noted that, at times, video surveillance has the opposite effect than that desired; making the people who are the object of protection uncomfortable (
Koskela 2002).
Design of University Spaces and Contexts from a Gender Perspective
The development of spaces, and later surveillance, with a gender perspective should be mentioned. This is included in general urban planning (
Muxí Martínez et al. 2011), with the same objective considered here: To increase safety and decrease harassment. Isolated spaces are reduced, adequate lighting is insured, and measures should be implemented to guarantee that cleaning closets and other types of spaces (such as classrooms, offices) remain locked when they are not in use.
4.3.5. Actions in Areas of Training and Participation
Creation of Studies and Official Courses. Complementary Training for Victims
Universities can offer courses that allow more specialized training for professionals from diverse areas, centering it on their fields. There are a wide range of possibilities, and these can and should be encouraged by the education entity at various levels. From introductory courses of a few dozen hours, to specific master’s degrees, and specialized diplomas or university expert degrees, they should incorporate coeducation as a strategy (
Venegas and Heras 2016). Options for face to face, blended, or online classes are also a very attractive offering.
This training could range from supplementary courses for educators of all levels, with the aim of identifying and preventing harassment situations, to those for experts in new technologies or in legal areas.
Women who have gone through the traumatic experience of gender violence in its crudest sense, may also face, in addition to the problems which the situation itself produces, an interruption to their professional training, or in other cases, an outdated knowledge. Universities, as entities which are responsible for social issues, should rise to this challenge and contribute to the full employability and social integration of victims of gender violence.
Organizing Contests and Other Participatory Initiatives
The organization of contests connected with the prevention of sexual harassment and harassment on the grounds of sex generate great interest in the educational community. Participants could present projects in which they have to delve into, and produce documentation about this subject. The projects presented could deliver a message of awareness which would be disseminated throughout all the sectors of the university. These contests could include photography, stories, etc.
4.3.6. Use of Information and Communication Technologies
Social Networks. Dissemination and Awareness
Universities, in the same way as other different establishments, utilize social networks to project a picture and to create solvency and enthusiasm for their standards and activities (
Mandelli and Cantoni 2010).
Social Networks. Identifying Harassment
Social networks additionally lamentably give new ways and channels to individuals to participate in harassment (
Brown and Hegarty 2018). Universities ought to be set up to recognize and act against students and workers utilizing these stages to pass on messages, perspectives, or activities of badgering (
Al-garadi et al. 2016).
Professional ICT Support—Detection of Spyware
Ferrier and Garud-Patkar (
2018) emphasize that victims sometimes do not know how to defend themselves from cyber harassment and need proficient assistance. This could be done through a program called troll-busters
1, which gives moment rescue services to help women writers, bloggers, and publishers who are focuses of cyber harassment.
Siddiquah and Salim (
2017) show that some students could face some problems regarding the use of ICT, which could lead to flaws that could facilitate an aggression. The authors argue that universities can count on a strong organization of experts and resources in the area of ICT. Thus, universities could set up their own similar services through their IT offices, with the goal of assessing and/or ensuring their employees and students that their computers are sheltered.
Communication Channels: Websites, Social Networks, Instant Messaging Apps
Regardless of the job, social networks enable methods for participating in violence (
Daspe et al. 2018). Universities need to depend on communication channels. Aside from customary media and assets, (for example, composed archives and a physical place where a victim can get help), likewise, online assets ought to be accessible. Notwithstanding the promptness it gives, communication can be anonymous (at any rate in the beginning), which can support some victims or witnesses to feel more comfortable utilizing it.
Programs to Avoid the Gender Digital Divide
Women are exploiting ICTs increasingly more in each everyday issue, and yet, a digital gender divide exists. This is not just demonstrated in the way that less women use ICTs, but also in the presence of gender-specific structural inequalities that comprise obstructions for their entrance and use.
Hence, since new online communication gives a chance to harassers (
Pina et al. 2017), colleges ought to compose and give courses and create IT instruments that decrease this harassment. ITC departments can develop ways to report cases, preserve evidences, and educational courses to identify and respond against attacks. In addition, machine learning techniques are able to identify hate speech and hazards in a text. In this manner, they could exploit university material and educating staff.
Specific Apps for Attention, Support, Social Participation, etc.
Numerous applications exist that facilitate the treatment of gender violence and harassment (
Revilla 2016), notwithstanding the recently referenced HarassMap (
Wael 2017). A few applications offer guidance about the proper behavior in specific circumstances of harassment, and incorporate real experiences of sexual harassment victims (
Lindsay et al. 2013). Another model is MyApp, which intends to help women in circumstances of violence in the university environment (
Alhusen et al. 2015).
4.4. Victim’s Acceptance
The measures under discussion require acceptance from the victim. Although these strategies can improve safety, they sometimes imply the recording of data, and this could be an interference in privacy. This can lead to a rejection by the victim.
Motti and Caine (
2014) presented a list of twenty human-centered design principles to have under consideration.
5. Case Study: The Management of Sexual Harassment and Harassment on Grounds of Sex in Spanish Public Universities
Moving to the guidelines in a university domain in Spain, the Organic Law of Universities (LO 6/2001, 21 December) stated the obligatory presentation of equal opportunity management units and, as a result of this, numerous residents who work at or go to Spanish universities have a more clear awareness about the seriousness of some sexual harassment cases, and about the need of having an approach to deal with these circumstances.
Because of this law, throughout the previous years, the entirety of the fifty state funded universities in Spain created explicit protocols on this issue. In any case, these documents are centered on addressing complaints, with a punitive character. In the following section we will study and particularize these university protocols.
Metodology
The responses from universities were studied quantitatively and qualitatively, with an explicit review of protocols, and through a survey, and in accordance with the previous bibliographic review. The existing protocols have all been read in depth, since the majority are available online from the website of each university. Issues with access were solved by requesting information from the university in question, or by contacting the Equality Department, or a similar body, by telephone or email.
A survey was sent to the fifty public universities, with the objective of learning about the normal handling of cases of harassment. Different aspects of the implementation of protocols for sexual harassment and harassment on the grounds of sex were explored, as were other good practices which were carried out in different universities. The survey was made available to equality units managers through a link. After they completed the survey, the information was collected and the analysis was carried out. Thirty six of the 50 universities responded.
The subject of study was protocols, the units of observation were answers to questions and the content of texts, with the units of analysis being drawn up in categories, which permitted an examination of the data obtained. These are grouped in the following way, as terms of analysis and a basis on which to structure the results, seeking suitability for the analysis:
Generalities. General aspects of training. In addition to economic aspects, the length of time the protocol has been in effect, and the environment, promotion and training/conscious-raising activities are addressed.
Response. Concrete actions in harassment cases. Many of these actions are carried out in a working environment, but also in a student environment, where there are also hierarchical relationships (professor/student) and situations of inequality between men and women.
Cooperation. Collaboration with other university services. This could improve the handling of an incident of this seriousness by providing a multidisciplinary focus.
Attention. For the victim, who needs integrated attention.
Early detection. Another essential point, but which requires professors and staff who are sufficiently trained and guided by a team of doctors and psychologists.
Action with the aggressor. Intervention programs which could prevent future cases. Monitoring the aggressor’s typical environment, since other cases could occur in the future.
Protocol efficiency. Evaluation and monitoring of protocols, and a specific time frame for their revision.
Recording and follow-up of cases. With the goal of identifying indicators of these situations in relation to the university.
Use of information and communication technologies.
Other measures. Information about any action not reflected in their protocols was requested from the departments responsible for equality issues.
6. Results: Analysis and Diagnosis
The content of the protocols will be studied, with the phases they include, and the measures they contain. The section will conclude with an analysis of the results from the survey of the Equality Departments.
6.1. Adoption of Protocols against Sexual Harassment and Harassment on the Grounds of Sex in Universities
All the public universities in Spain have a designed protocol for the treatment of sexual harassment and harassment on the grounds of sex, however, some universities have documents which aim to encourage a good working environment, and to prevent mobbing or workplace harassment, and other situations, specifically including sexual harassment and harassment on the grounds of sex. These documents also present a marked perspective in prevention of occupational hazards.
6.2. Study of the Content of Protocols against Sexual Harassment or Harassment on the Grounds of Sex in Spanish Public Universities
An analysis of the current situation leads us to suggest a series of proposals with the aim of improving the practical handling of cases of sexual harassment and harassment on the grounds of sex in Spanish universities.
6.2.1. Phases of Protocols
The analysis shows that almost all the protocols propose a series of stages which determine the steps to be followed when managing a case. In some universities, this path is more precise and detailed, and in others, it is less specific.
All the protocols studied include a defined channel through which to accept complaints and manage them. The generic procedure that is common to all the universities will be examined below, and used to analyze the phases through which a victim is taken.
First Phase: Initiation
A careful reading of the protocols shows that they all have a phase of initiation, which is to say that a protocol is a process which begins when a person presents a complaint or reports an incident.
The majority of protocols begin with a complaint, made by a member of the student body, faculty, or staff. Studying the protocols shows that students direct their complaints through intermediary figures such as student representatives, risk prevention services, or other channels they consider to be appropriate. In some universities, protocols are automatically activated when situations which could be considered harassment are detected. The Equality Department or a similar body (equality commission, or in some cases, risk prevention), normally takes charge of the process, once it has been initiated. At this point, and before beginning an inquiry, the case is in some instances sent to a prosecutor’s office for legal processing.
Second Phase: Inquiry
The term ‘inquiry phase’ is generally used to describe the different actions contemplated in the protocols to investigate the alleged events. This investigation determines whether or not to proceed with the activation of the protocol.
At this point, in some cases, such as that of the Universidad de Vigo, for instance, a person is assigned to head the inquiry. This person interviews the complainant and the accused separately, attempting to clarify what has happened with the greatest objectivity possible. They may also investigate the environment, carrying out inquiries into where the event took place, the people present, and so on. All of this should be appropriately documented in the most impartial way possible.
If it is decided not to activate the protocol, a final report should be made, and follow-up measures should be taken, if deemed necessary. Closing the case terminates the procedure. If it is decided to activate the protocol, the next phase begins.
Third Phase: Resolution
When the protocol is initiated, many universities assume an informal resolution to the conflict. This involves an agile procedure to seek mutual agreement through a mediator; normally the Equality Department. If an agreement is reached, it is duly documented and the measures which have been agreed on are reported. After this, the case is closed. This informal procedure seeks a rapid, mutually agreed solution. This agility can result in minimizing the situation, however, making it less visible.
Otherwise, a formal procedure is followed. This involves convening a commission. This commission is sometimes called before requesting expert assessment, and sometimes after. This means that in some cases, the actions of the person carrying out the interviews and evaluation are controlled, and other times, they are not. This depends on the degree of autonomy allowed to the person in charge.
The commission normally allows allegations by the accused, and with this, issues a decision. The case may now need to be presented to the prosecutor’s office, or, not excluding the previous possibility, administrative measures may be taken. If deemed necessary, disciplinary action is taken against the aggressor. Finally, a report documents the entire procedure, and follow-up measures can be proposed before closing the case.
6.2.2. Actions for Managing Situations of Sexual Harassment and Harassment on the Grounds of Sex
Apart from the development of a sequence of actions aimed at treating cases of sexual harassment or harassment on the grounds of sex, protocols generally include a series of actions that are intended to prevent these circumstances.
Training Actions
It is normal for universities to place great importance on the training given to the professionals who will deal with harassment cases in the education community, and so in practically all the protocols, there is provision for courses, although they are not carried out in all universities. Teaching staff can also receive specific training to help them identify cases of harassment, gender violence, and situations of gender discrimination.
There are also increasingly other training activities related to awareness about equal opportunity, for example, or courses on non-sexist language (
Burgos 2013).
Consciousness-Raising Actions
An awareness of sexual harassment and harassment on the grounds of sex as issues is necessary for the university community to understand its importance, and when these cases occur, to act with the expected censure.
System of Guarantees
Almost all protocols establish a system of explicit guarantees:
Equal treatment. Personal dignity and privacy. The identity of the complainant and the accused is protected (data protection).
Principles of objectivity, impartiality, and contradiction.
Principle of promptness.
The right of any of the implicated parties to abstain due to a conflict of interests or disqualification.
Safeguarding of rights when carrying out academic or work activities.
The right to a hearing, where allegations can be refuted.
The right of all the parties to information about the development of the process.
The accused is assured that no mention of the accusation will appear in their academic or work records if the complaint proves to be false.
Right to health care, including medical and psychological attention.
The absence of retaliation is guaranteed with the adoption of pertinent measures.
Judicial security; the administrators will follow the measures laid down in the protocol.
The victim has the right to have their original working conditions restored, if they had been modified.
Effective judicial protection is guaranteed. The protocol complements, and does not substitute for judicial proceedings.
Data Gathering Actions
The vast majority of universities collect data in annual reports. This ranged from every three months to every twenty four months among the sample. Although the collection of data is essential, the amount of detail included is unknown, since this information is not publicly available. Information about the profiles of victims and aggressors (for example, their relative hierarchical position), is necessary in order to understand what circumstances give rise to situations of sexual harassment or harassment on the grounds of sex, and to be able to intervene more directly.
It is important to note that universities are obliged to ensure that the data collected effectively safeguards the privacy of the victim, and in general, complies with the Organic Law 15/1999 of 13 December, pertaining to personal data protection, as well as the recent EU Regulation 2016/679, in effect since 25 May 2018.
6.3. Survey Results
The survey was carried out using a digital application of the Universidad de Murcia. It was distributed to the fifty public universities, with the objective of collecting information, mainly from those that already have a protocol for handling cases of sexual harassment and harassment on the grounds of sex. Thirty six of the 46 entities with a protocol responded. Although greater participation was hoped for, the results indicate tendencies and provide a picture of the real situation (albeit partial), which can be enlightening.
6.3.1. Economic Support from the University
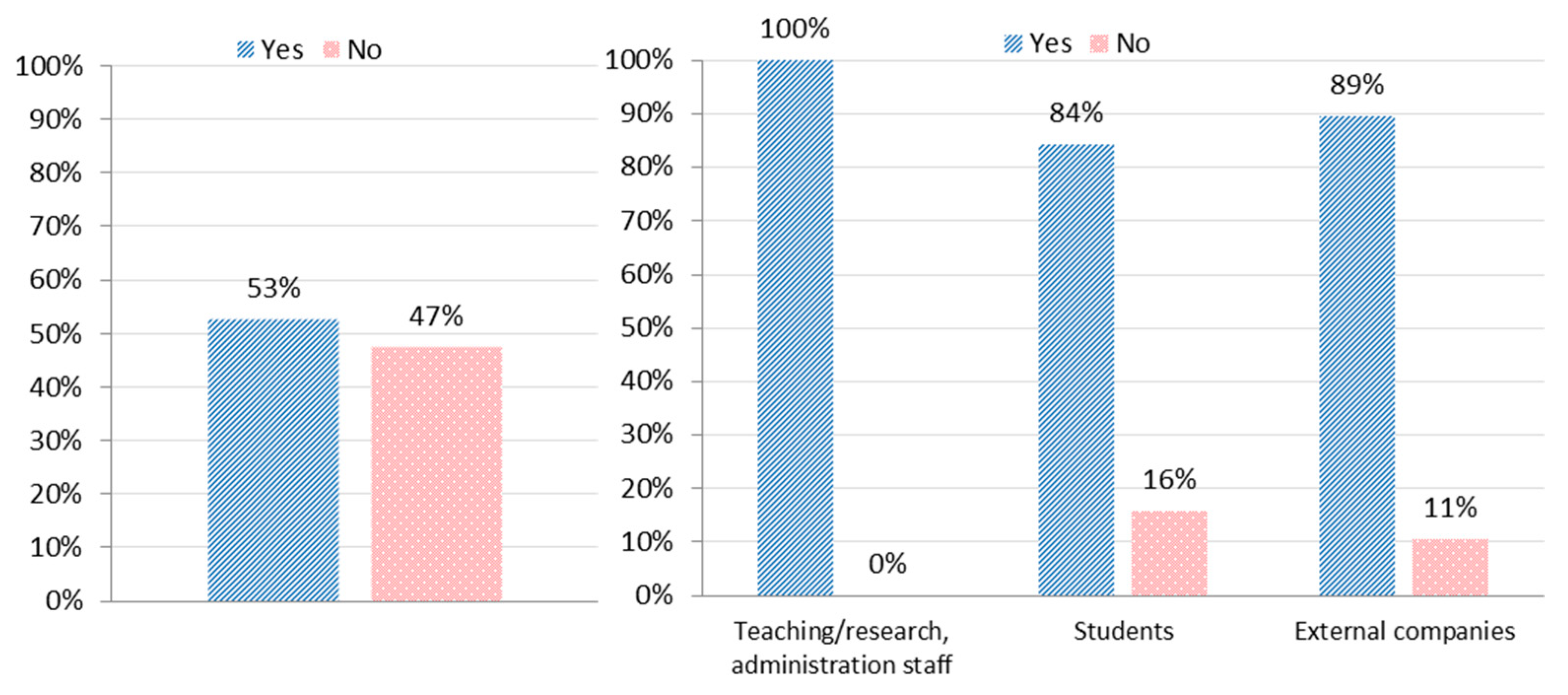
We asked about the existence of specific funding available to carry out the monitoring and development of the actions foreseen in the protocol. It is notable that 47% of the departments do not have a specific budgetary allocation for development, which makes adequate implementation difficult. (
Figure 1, left).
6.3.2. Scope of Application
The vast majority of protocols cover the whole university community (including proceedings with subcontracted personnel who work in and around the university). Only a small number of universities limit themselves solely to the organization’s staff. (
Figure 1, right).
6.3.3. Training and Consciousness-Raising Measures
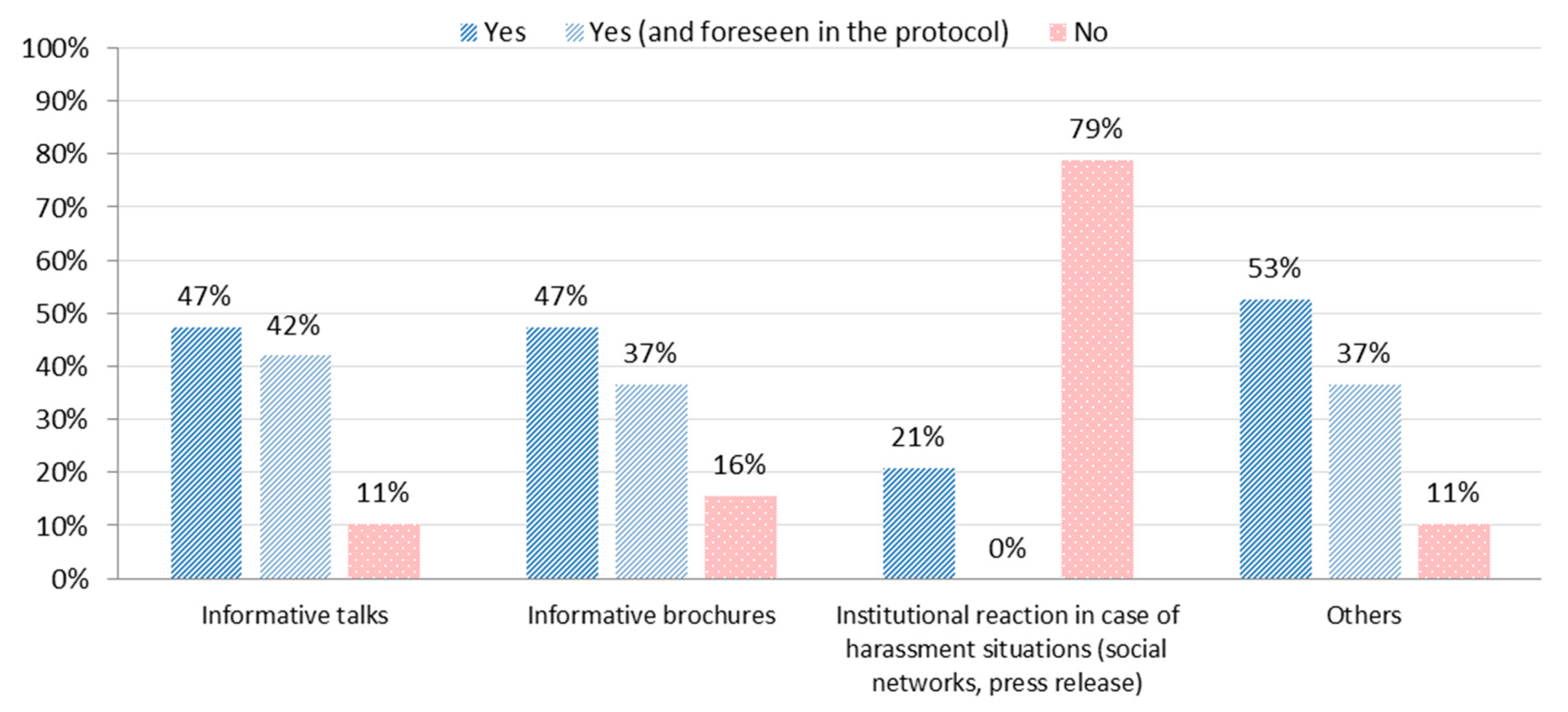
All the universities use talks and brochures to raise awareness. Nevertheless, it is surprising that in a large number of cases, they are carried out through initiatives by the Equality Department, and not because of protocol requirements. All the universities implemented other measures, for example, training external entities, and integrating consciousness-raising actions when welcoming first year students, however, only a few protocols include a vocal network and information about pertinent situations which have occurred in public life, either at the university or outside it, in the media. (
Figure 2).
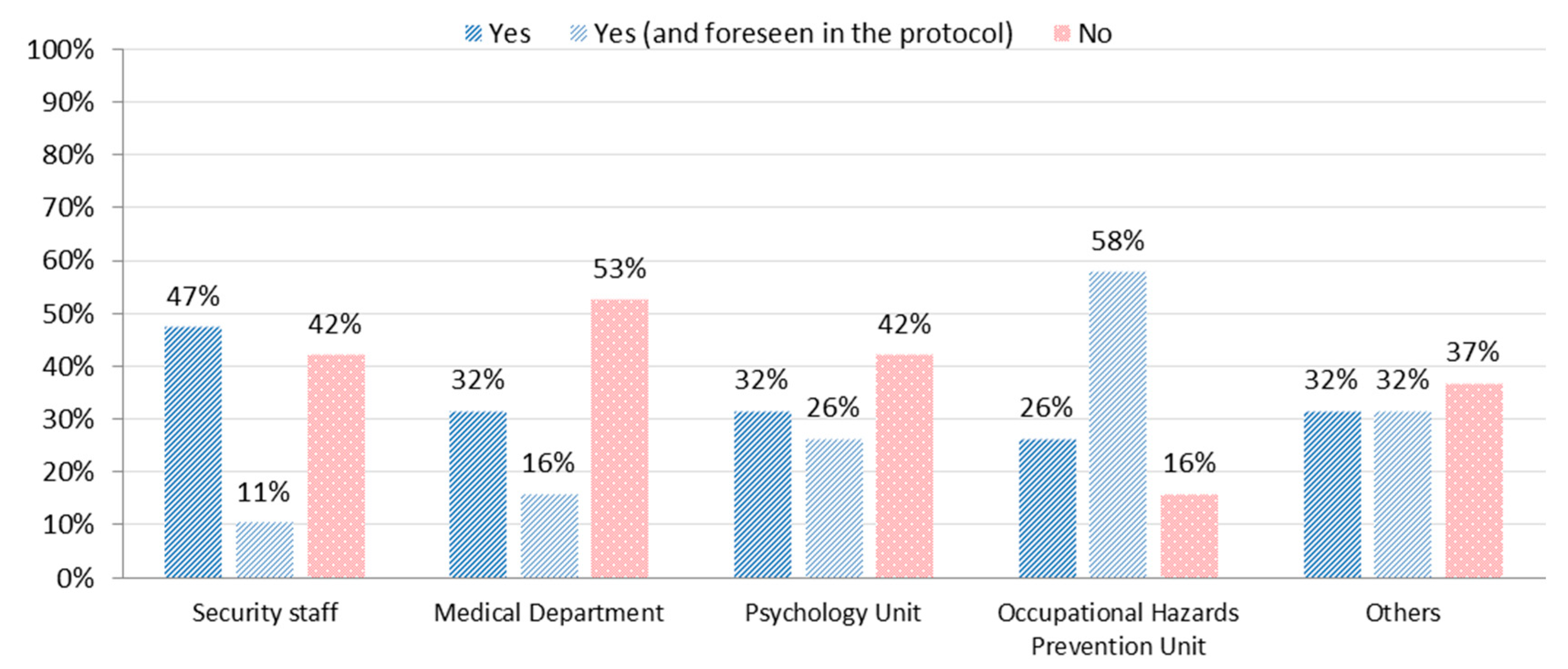
6.3.4. Collaboration with Other University Departments
Since the management of harassment is something that affects multiple facets of a person’s life, its focus should be multidisciplinary. This requires coordination with other professionals and services. Surveillance and security does seem to be, to some extent, integrated, followed by the involvement of doctors and psychologists, but this applies to about 50% of the universities, and is not always described in the protocol. Participation of the Occupational Risks Prevention Unit, whose specialty, applied psychosociology, is closely connected to the handling of harassment, is a special case. There is broad participation of these units in the majority of universities, but the protocol does not describe what this must comprise. (
Figure 3).
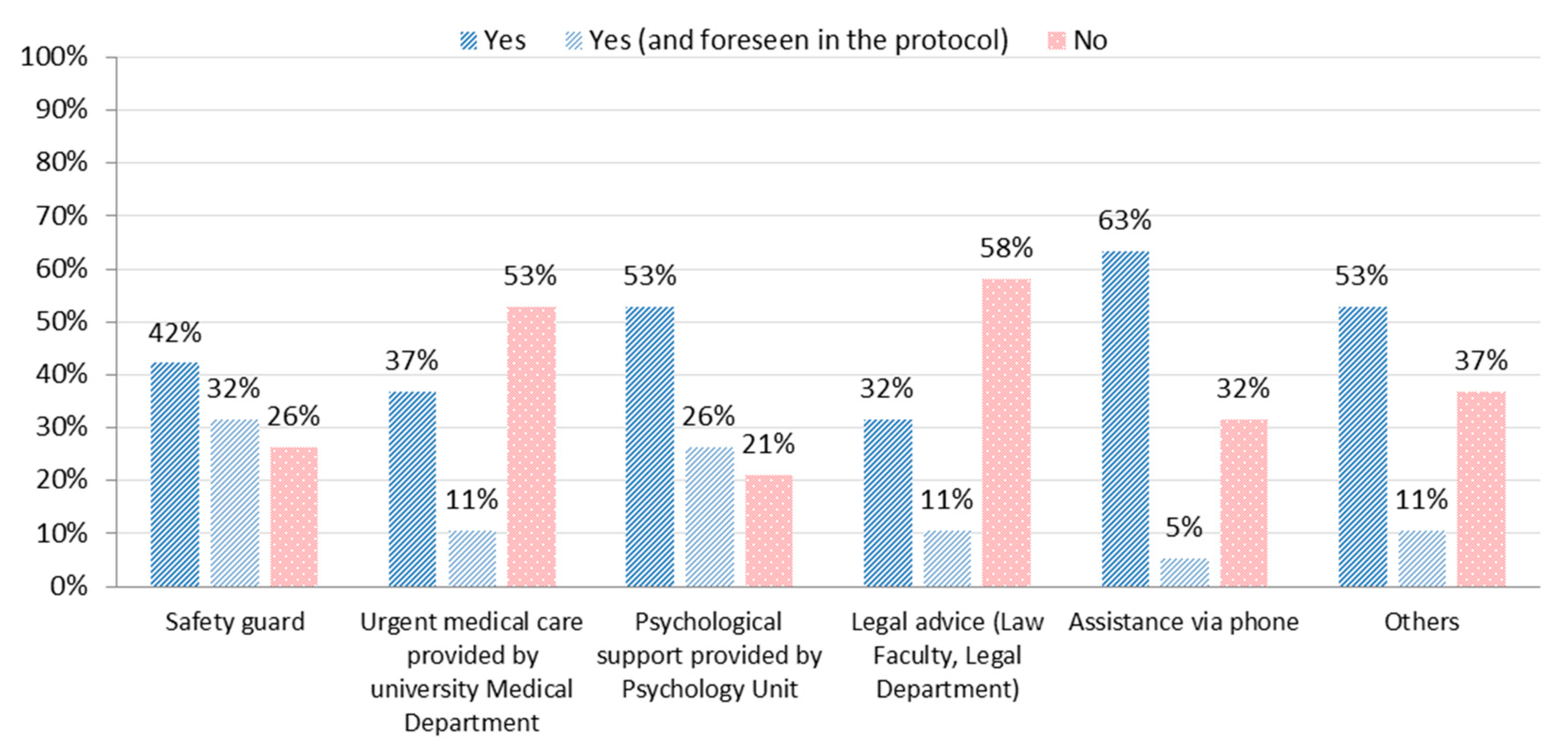
6.3.5. Specific Actions with the Victim
Measures to help victims are being put into practice in the vast majority of universities. Psychological and telephone assistance are the main measures, sometimes used together. Protection of the physical integrity of the victim, and medical attention, closely follows. The great majority of measures are explicitly indicated in the protocol. It is surprising that legal assistance was not more common in the responses, given that universities have legal departments which could provide this service. (
Figure 4).
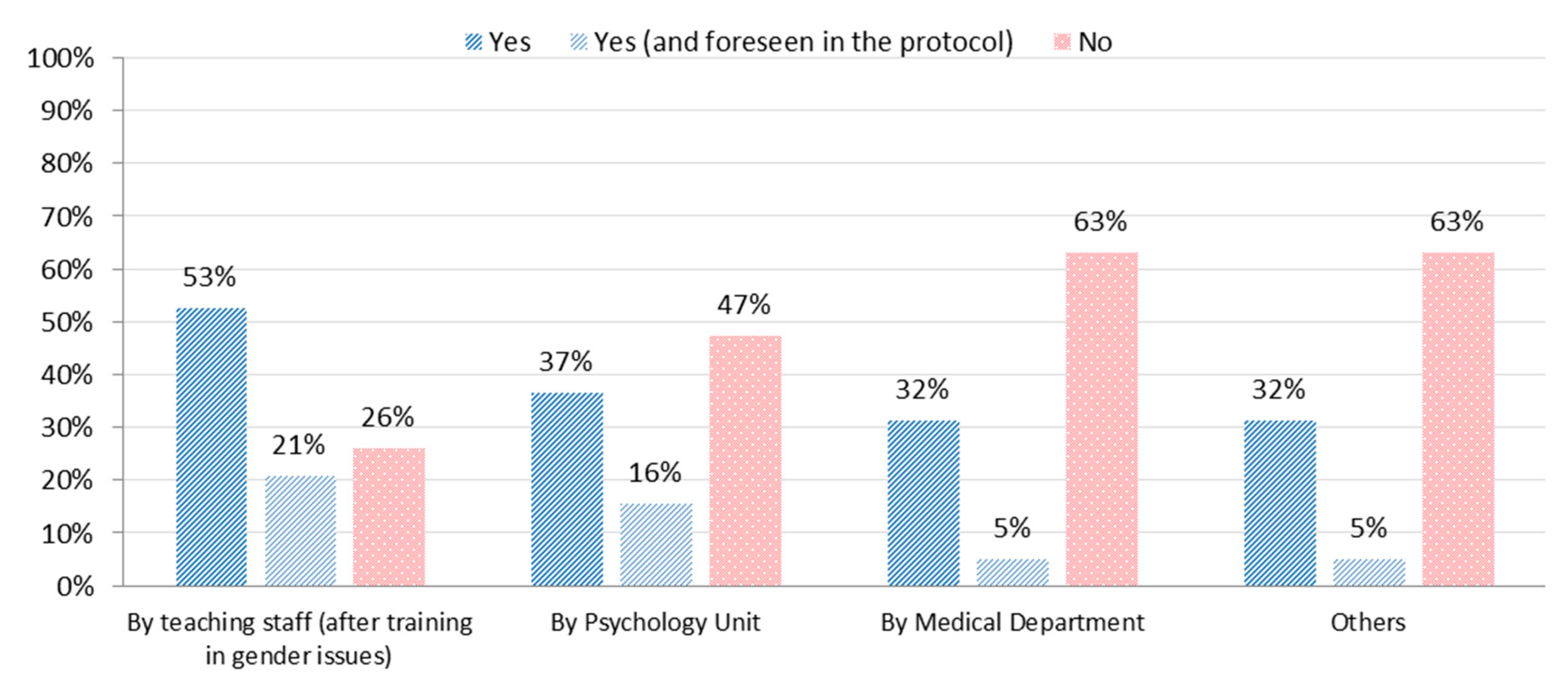
6.3.6. Measures of Early Detection
Events should be anticipated, or where they occur, addressed as quickly as possible. In order to do this, it is necessary to count on staff who are prepared to identify and conduct these situations in the right way. According to the survey results, faculties are reported to have training in this area, and in more than half of the protocols, this training is stipulated. (
Figure 5). Other types of detection, such as that carried out by psychologists or doctors, were also reported, but with less frequency. There are other kinds of early detection, such as tests that are given by the Occupational Hazard Department in order to evaluate psychosocial risks among personnel at the university. Understanding the factors which lead to sexual harassment could allow us to design an adequate strategy of anticipation (
Cuenca Piqueras 2015).
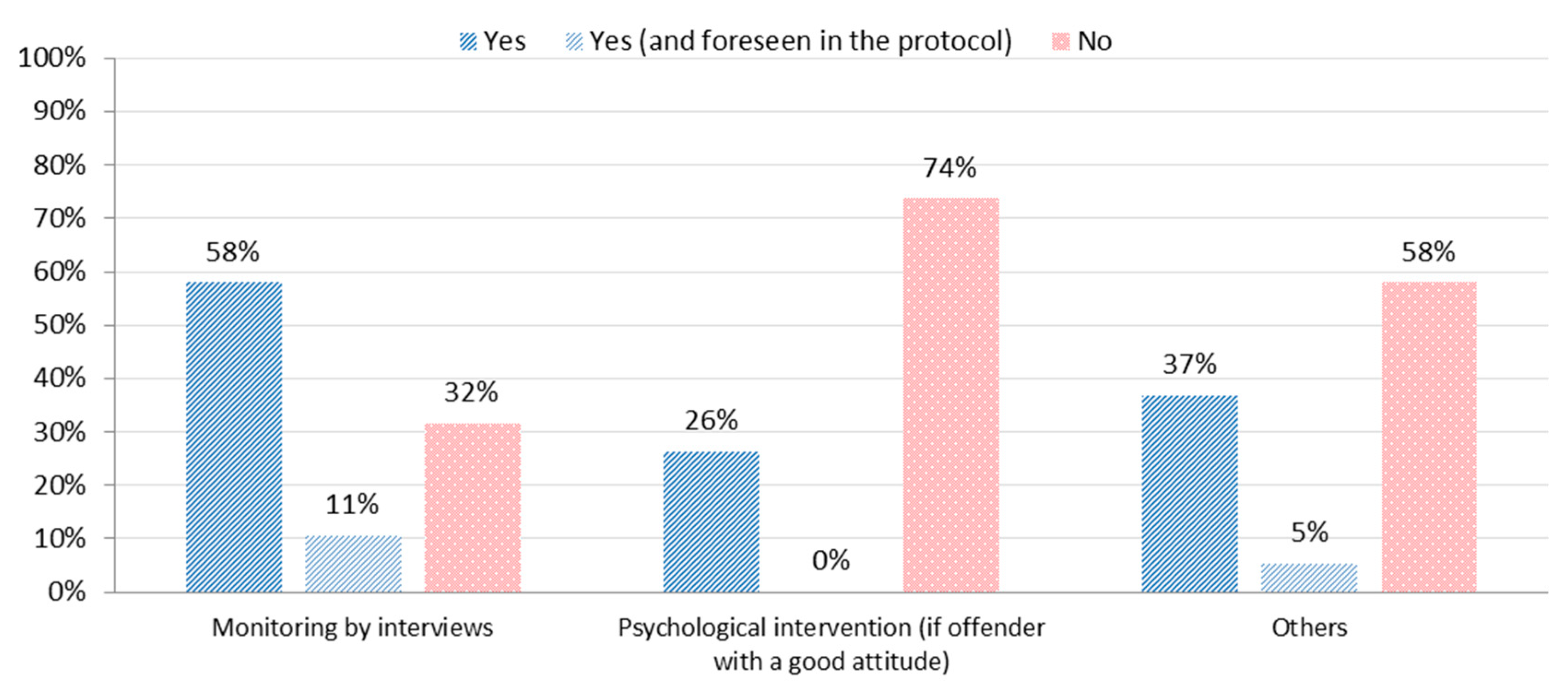
6.3.7. Specific Actions with the Aggressor
The aggressor also needs to be included in the protocol and its measures. An intervention will help to discourage reoccurrence, and monitoring can be carried out. This last action is being practiced in the majority of organizations under study. (
Figure 6).
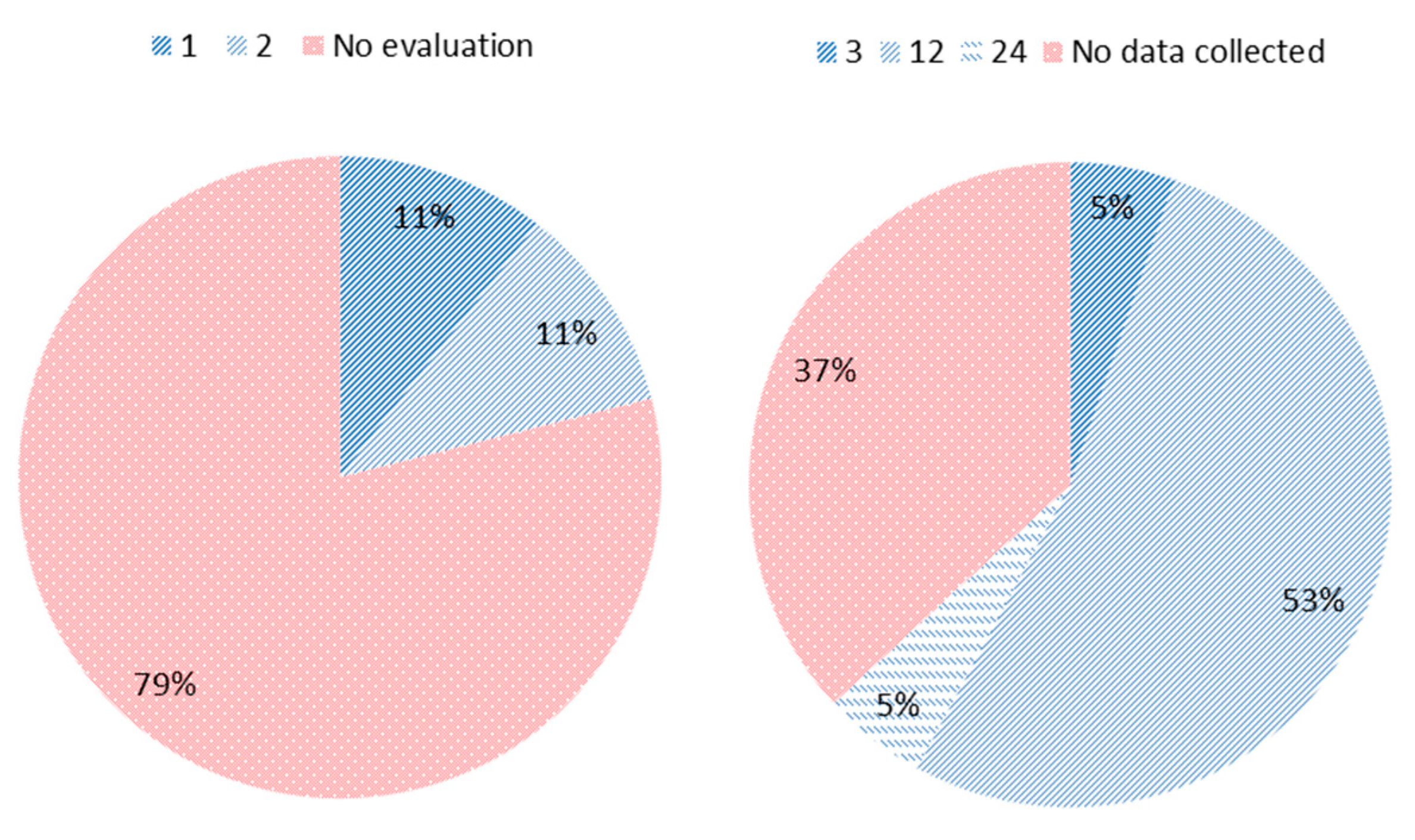
6.3.8. Evaluation Period of Protocols
Almost 80% of the universities which responded did not have a periodic revision of their protocol planned. Those who responded that they did, carried out the revision every one or two years, however, they are the minority. This important aspect is one of the measures which is advisable to improve in the future. (
Figure 7, left).
6.3.9. Data Collection
The majority of universities collect statistical data about events of sexual harassment and harassment on the grounds of sex. This is most commonly done annually, although more than a third of the protocols do not include requirements for data collection. (
Figure 7, right).
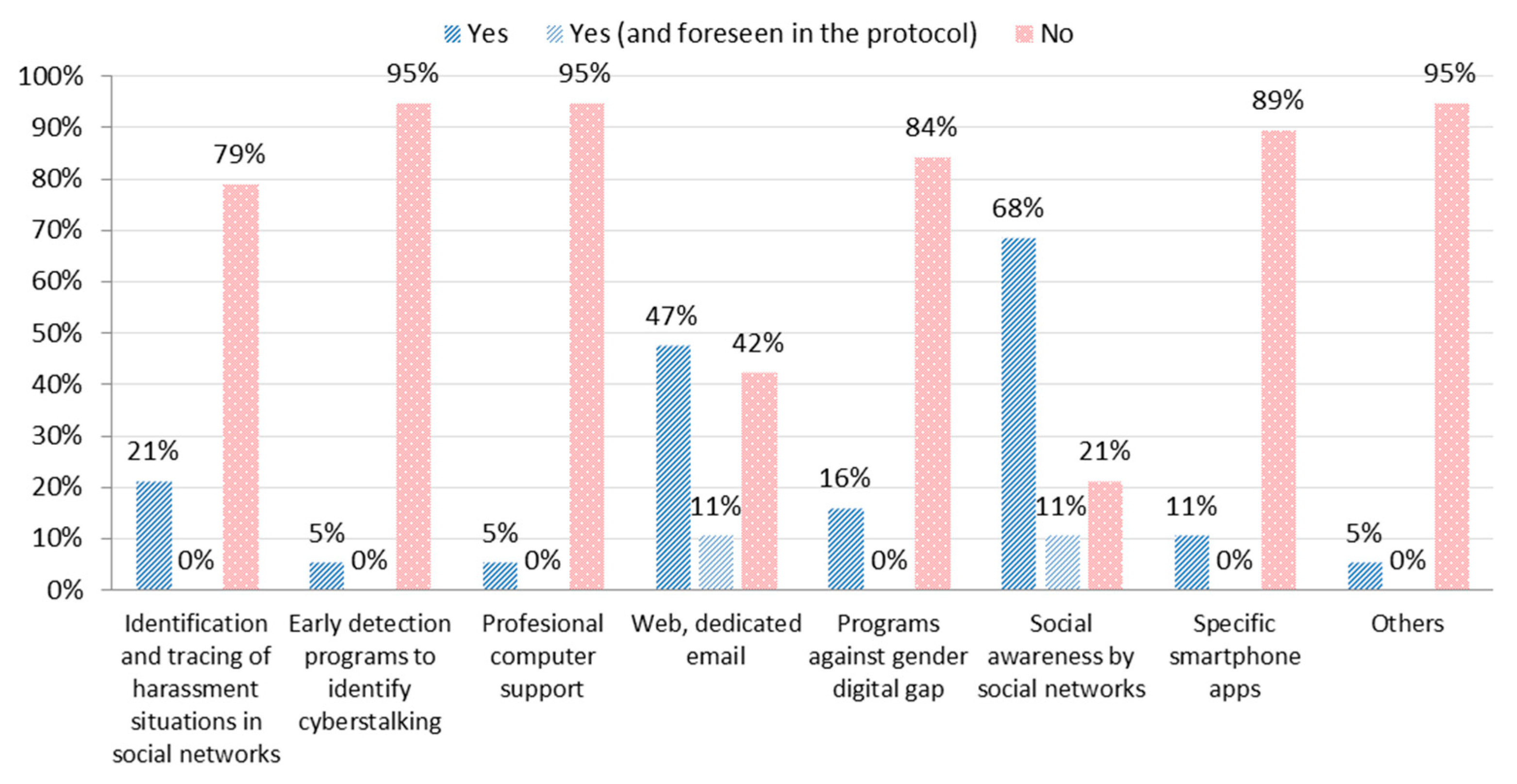
6.3.10. Use of Information and Communication Technologies
A study of the poll results makes obvious that universities have not actualized the assets described in the categories listed in
Section 4.3.3. Social networks and electronic media for victims exist, however they are not accommodated in the protocols. At the point when they exist, they do so as a result of the management groups’ positive initiatives.
The measure with the best acceptance among those reflected in
Figure 8 is without doubt the utilization of ICTs to disseminate information in social networks.
Padovani and Pavan (
2016) investigate the enormous impact of these systems both in the territory of advancing equal opportunity and in fighting violence against women.
The utilization of explicit sites and email addresses to record complaints or to coordinate solicitations for information is something different which these colleges broadly use. This is fundamental to the deployment in different establishments, and one of the first measures they adopted.
STATT (
2014) has actualized communication channels of this sort in Palestine and in Afghanistan, as they clarified in their 2014 report.
Thus, it is surprising that, despite the prominent nearness in social networks, most universities don’t have a systemized control over who can remark nor what they can remark on official university accounts. However machine learning tools exist that have been effectively utilized for this reason (
Frommholz et al. 2016). Likewise, these universities are just minimally utilizing their IT experts to help and secure cyber victims or possible victims.
7. Discussion
In practically all the protocols, a series of stages are proposed that mark the process to be followed. In some universities this path is more complete and concrete, and in others it is broader and more diffuse. Some include some actions that are not contemplated in others, and vice versa. Generally, the phases that should form the protocol do not have to be structured in a linear process, but should describe the possible sequence of multiple itineraries that a victim can follow in the process of reporting and seeking help. For this reason, it is very important to construct a route that contemplates all the variations, as well as evaluation and the monitoring of phases and actions. The final protocol should constitute a route that avoids removing the victim from the institutions and confining him/her to “the private” (
Sagot 2002).
That is why periodic evaluation and monitoring of the protocol is important. The degree of compliance with the objectives and the gap between what is desirable and what actually happens in a situation must be known throughout the phases of the protocol.
The scope of the actions and the level of coordination and intercommunication of the different levels must be taken into account. Duplication of efforts and resources must be avoided, and the need for specific training by the professionals involved is detected.
From the results of the survey, we understand that the economic support presented by the universities (or their equality units) to establish strategies is not always fixed, some cases may be non-existent and in any case it is insufficient. This will limit the forecast of long term planning, a marked strategy, and consequently the results that are to be obtained.
Furthermore, it has been seen that the protocols are mainly aimed at teachers. On some occasions there is no coverage for students and other people who may temporarily carry out their work on the university campus. This lack of coverage may lead (and has undoubtedly led) to situations where, between the person being harassed/stalker, one will be within the protocol and the other not. In any case, no distinction should be made between members of the university community and the coverage of sexual harassment protocols should be unanimously extended.
In the same sense, we see that other measures have a diverse implementation. Training actions are varied and, understanding that they must be adapted to the characteristics and circumstances of each university, many of them are not included or specified as forms of prevention of harassment situations in the protocols, undermining their potential (
Burgos 2013). It is also striking that there is no interdepartmental management with other sections of the university. The focus in the management of sexual harassment, as in other issues, must undoubtedly be multidisciplinary. Security, medical assistance and legal aid must be priority fields of action for the protection of the victim. This links, and should be reflected, in action measures with the victim, on the same issues (safety, health support, legal, etc.). It can be concluded that psychological and safety assistance is common, but others, such as emergency medical assistance and above all legal assistance, are still aspects to be improved. Today, universities have powerful services in these fields, and actions should be envisaged to help victims. On the other hand, the attention to the aggressor is also testimonial. We must understand that aggressors will often reoffend and a preventive strategy must be implemented.
The early detection of harassment situations is also an aspect that can be improved. Although teachers, in general, have received training in gender and harassment to detect situations of sexual harassment, we cannot forget that they are not necessarily professionals in this field, so on many occasions they may make mistakes. The preventive action of the psychology unit does seem to be foreseen in at least half of the cases studied, but undoubtedly its action should be increased, cooperating with other departments such as occupational risk prevention, computer science, etc. There are also no strategies for detecting sexual harassment during the periodic medical examinations to which the universities subject their workers.
On the other hand, it is also possible to improve the purely administrative action of managing the protocol. There are no mandatory periodic reviews, nor is data collection stipulated or uniform. This undoubtedly makes it difficult, and we have experienced this during the course of this work, to make a fair comparison of the protocols and the results they are producing. An effort should be made in this regard.
To conclude, the use of ICTs is a testimony. In the middle of 2020, with the rise of information technologies, harassment is taking on new forms and new ways of being carried out (
Padovani and Pavan 2016). Universities have to foresee them and include them in their protocols, since digital actions have become part of our daily life.
8. Conclusions
This work has discussed situations involving the management of sexual harassment and harassment on the grounds of sex which take place in Spanish public universities, whether through means of the pathways and written measures in protocols, or through other measures which do not appear in protocols, but are also carried out. We began by putting the norms into context, and studying previous works carried out in this area, generating an adequate basis for study, which served as a guide to the methodology implemented. This has been useful in analyzing secondary sources (specific protocols and bibliography on the subject), and in the drawing up of a survey and the analysis of responses. The results have been revealing enough to create a picture of the current situation. In this way, we conclude that the protocols studied vary in the phases they include, and in the paths stipulated. For this reason, sufficiently broad protocol phases have been proposed, in order to accommodate diverse situations.
At the same time, there are currently few measures in place. Training and consciousness-raising are duly implemented, as is a system of guarantees of process. Data collection requirements vary, and more importance needs to be given to this, and to evaluation. In addition, further measures could be implemented, like enhancing the protection of the victim from a holistic view, paying attention to the harasser, and improving the cooperation between departments.
Universities, as organizations of advanced education, should lead in the usage of protocols that utilize their computerized assets, including the availability of equipment and of their staff and faculties. Despite this, the use of ICT to manage protocols could sometimes be improved, aside from the dispersal of data in interpersonal organizations, and the accessibility of sites for accepting grievances.
In this article we have dug into numerous different activities being incorporated by various open and private associations, and we have made an aggregation of how colleges could apply these activities.
We will now propose numerous measures which, from an ambitious perspective, will respond to the weaknesses and deficiencies in the protocols and management of harassment. We begin by emphasizing the importance of attention to the victim, given that working in a transversal way is a recurrent idea in the Organic Law of Integral Protection Measures against Gender Violence. We also draw attention to the fact that the aggressor should also be treated.
We conclude that the management of situations of harassment in Spanish public universities is, on the one hand, varied, with uneven development and implementation. It can be improved, and an innovative approach which incorporates new actions with the objective of increasing protection for victims and avoiding serious situations like sexual harassment and harassment on the grounds of sex is recommended, including the protection of individuals against discrimination based on sexual orientation and identity. Satisfactory administration of sexual harassment (or digital harassment) episodes must incorporate the use of ICTs as necessary tools for expanding proficiency and for improving prevention, just as for the treatment of victims. This project will be the basis for future work, in which we will examine the specific proposals which have been presented here more deeply.