ACO Based Variable Least Significant Bits Data Hiding in Edges Using IDIBS Algorithm
Abstract
1. Introduction
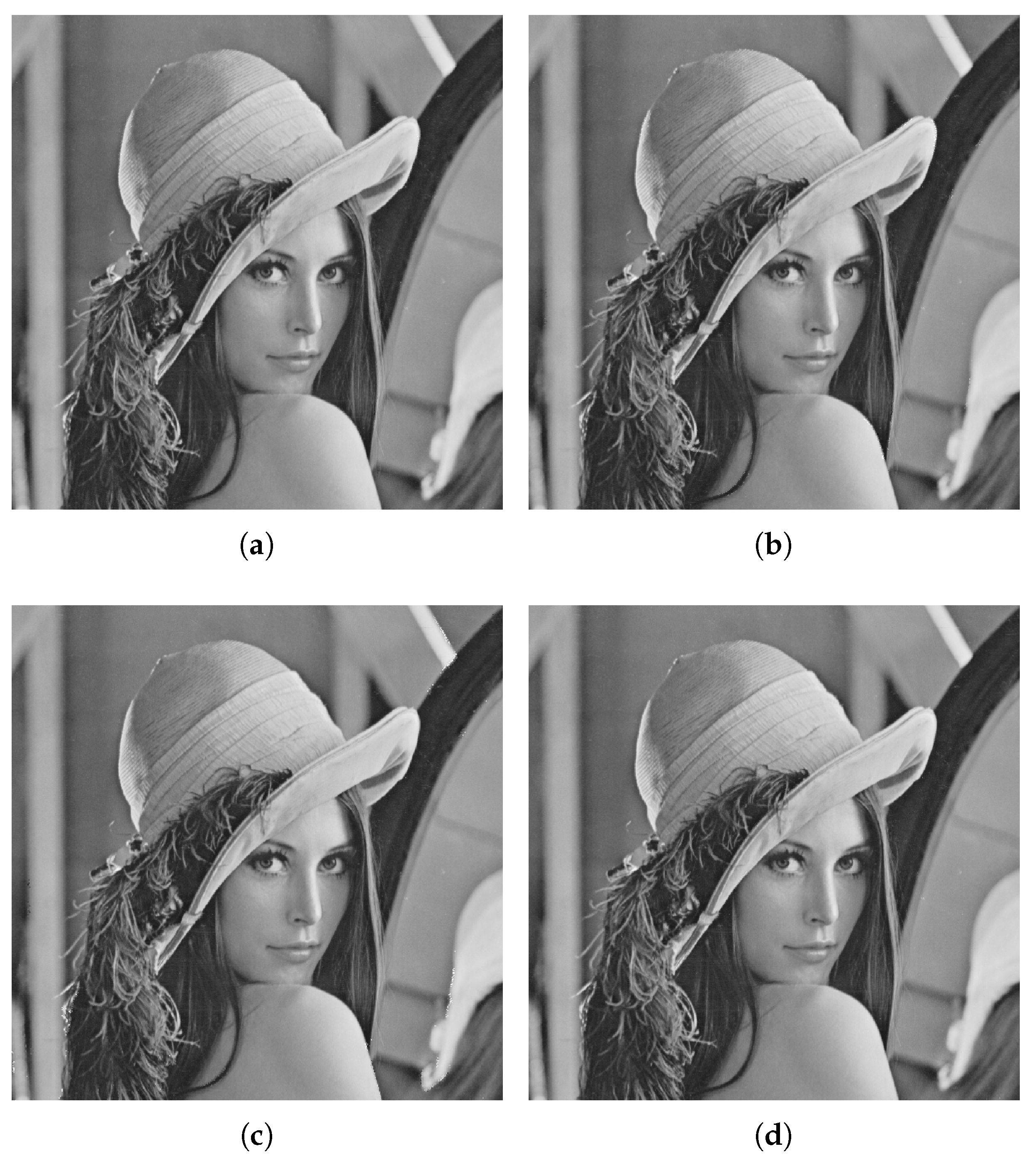
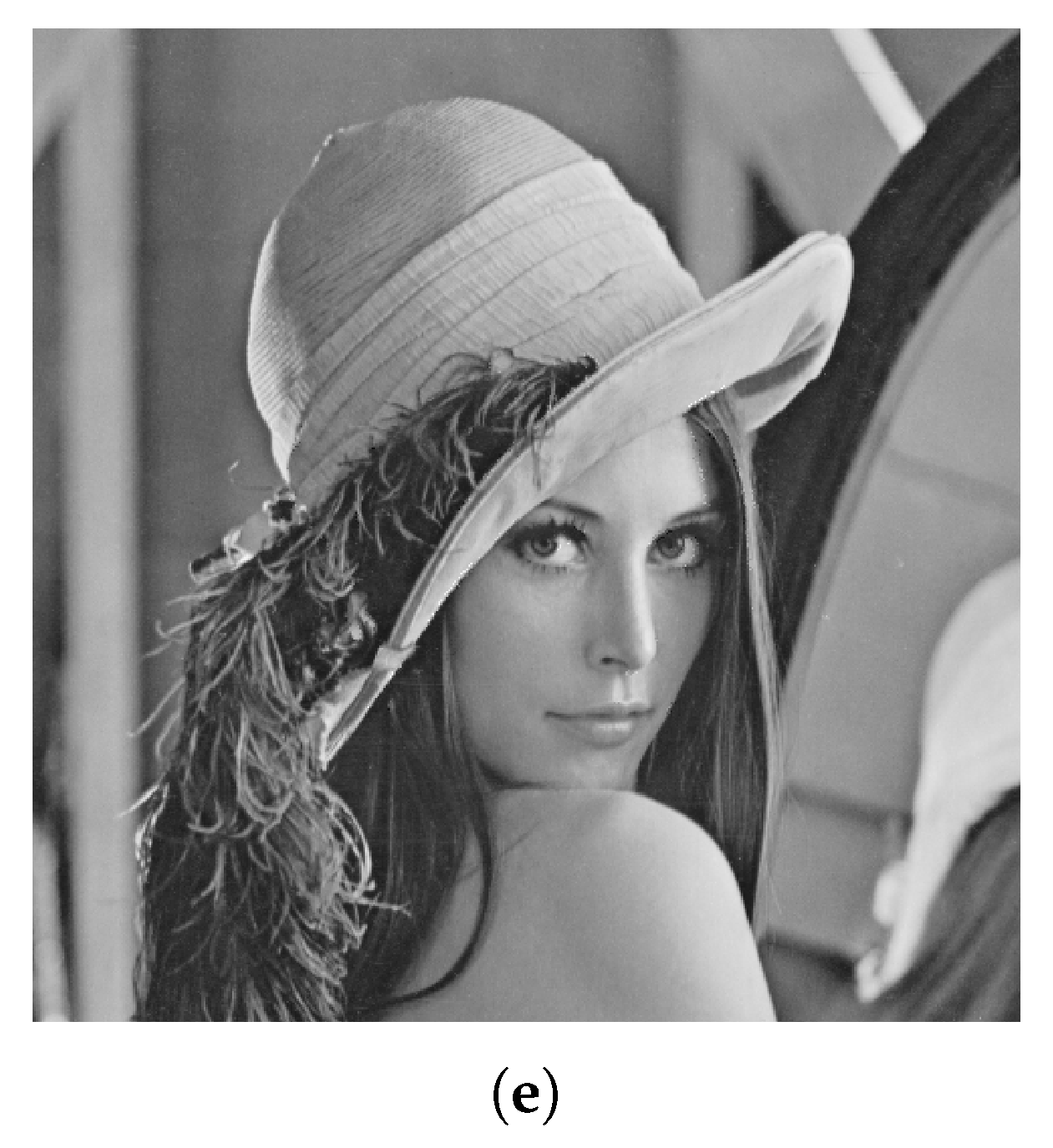
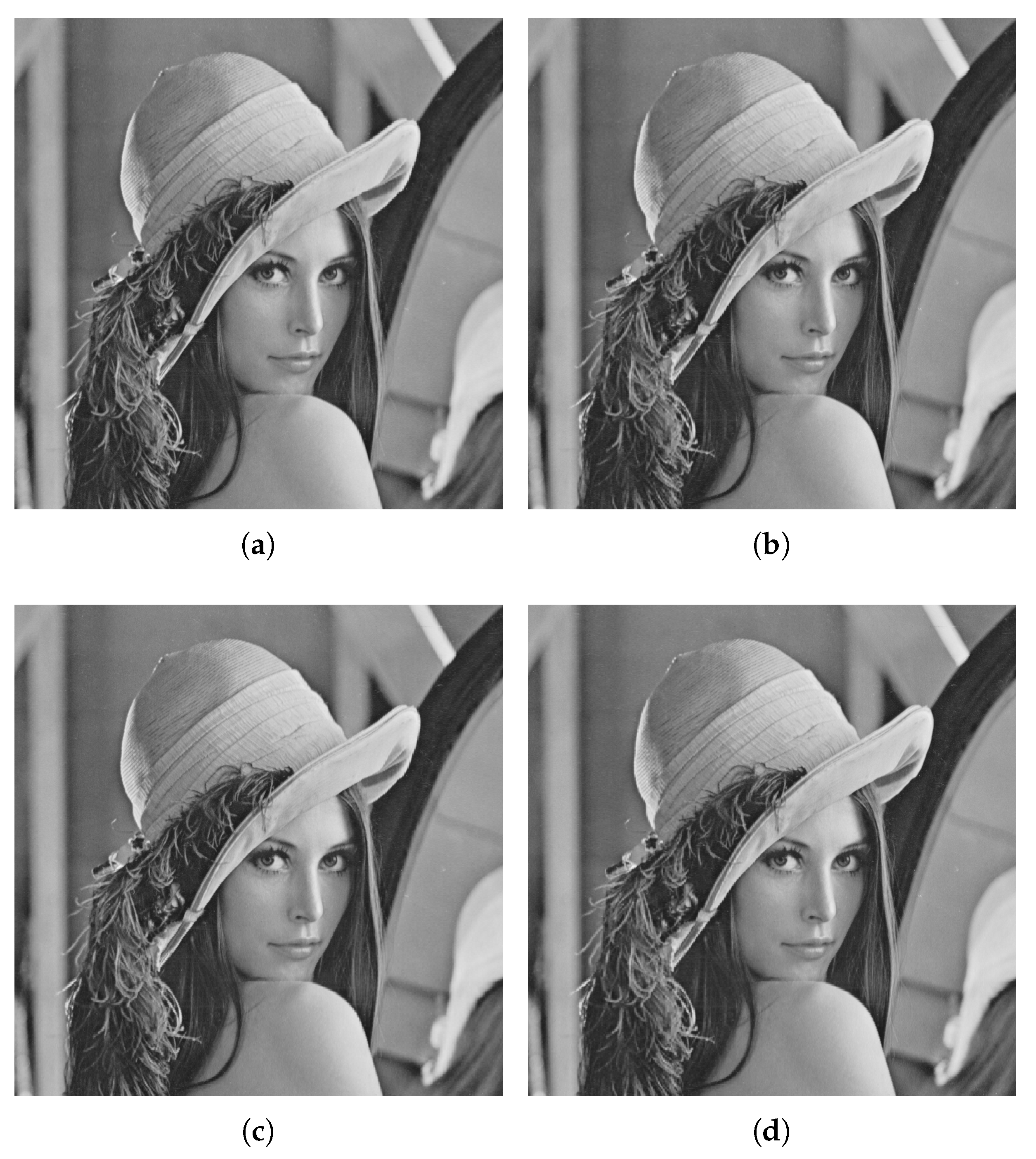
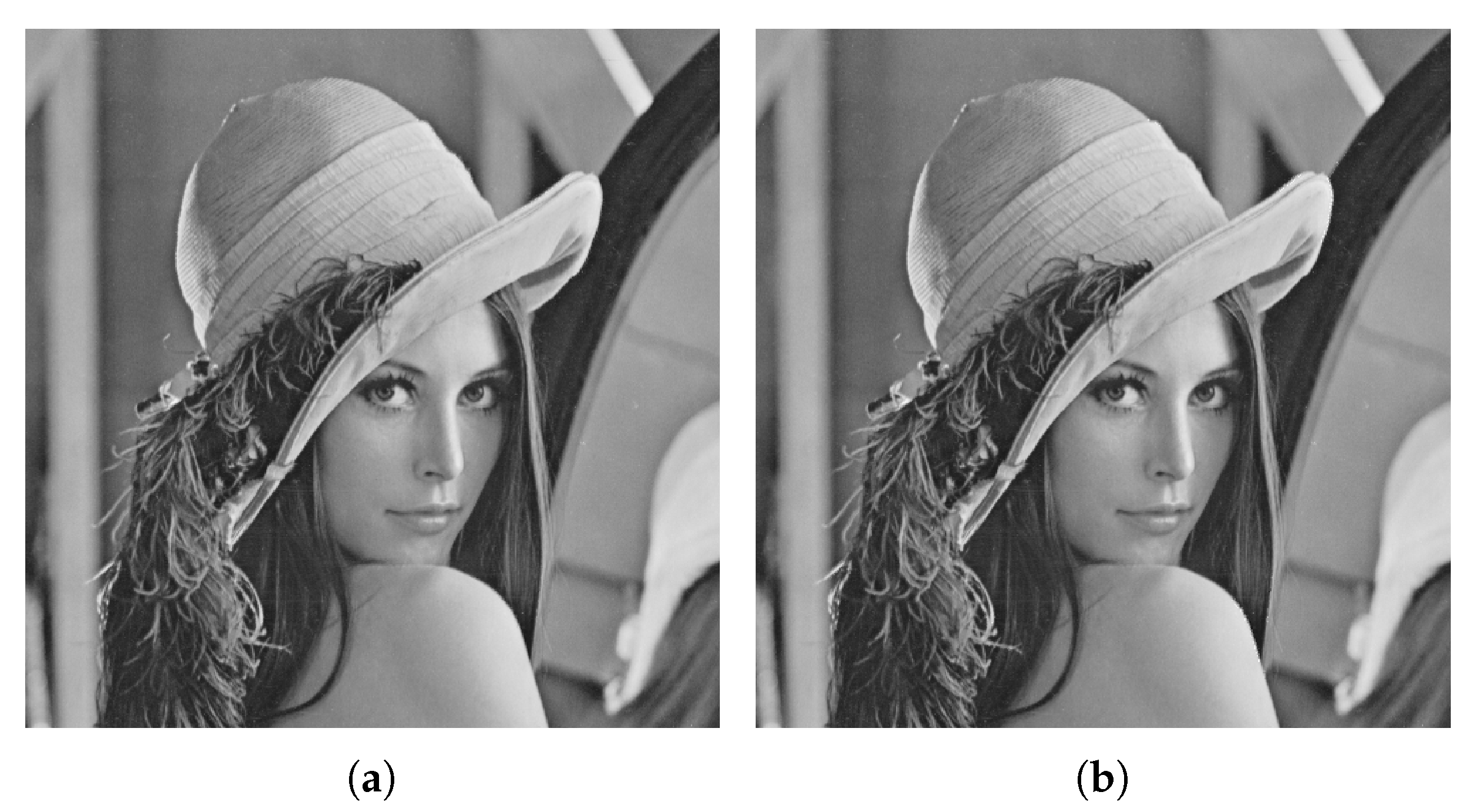
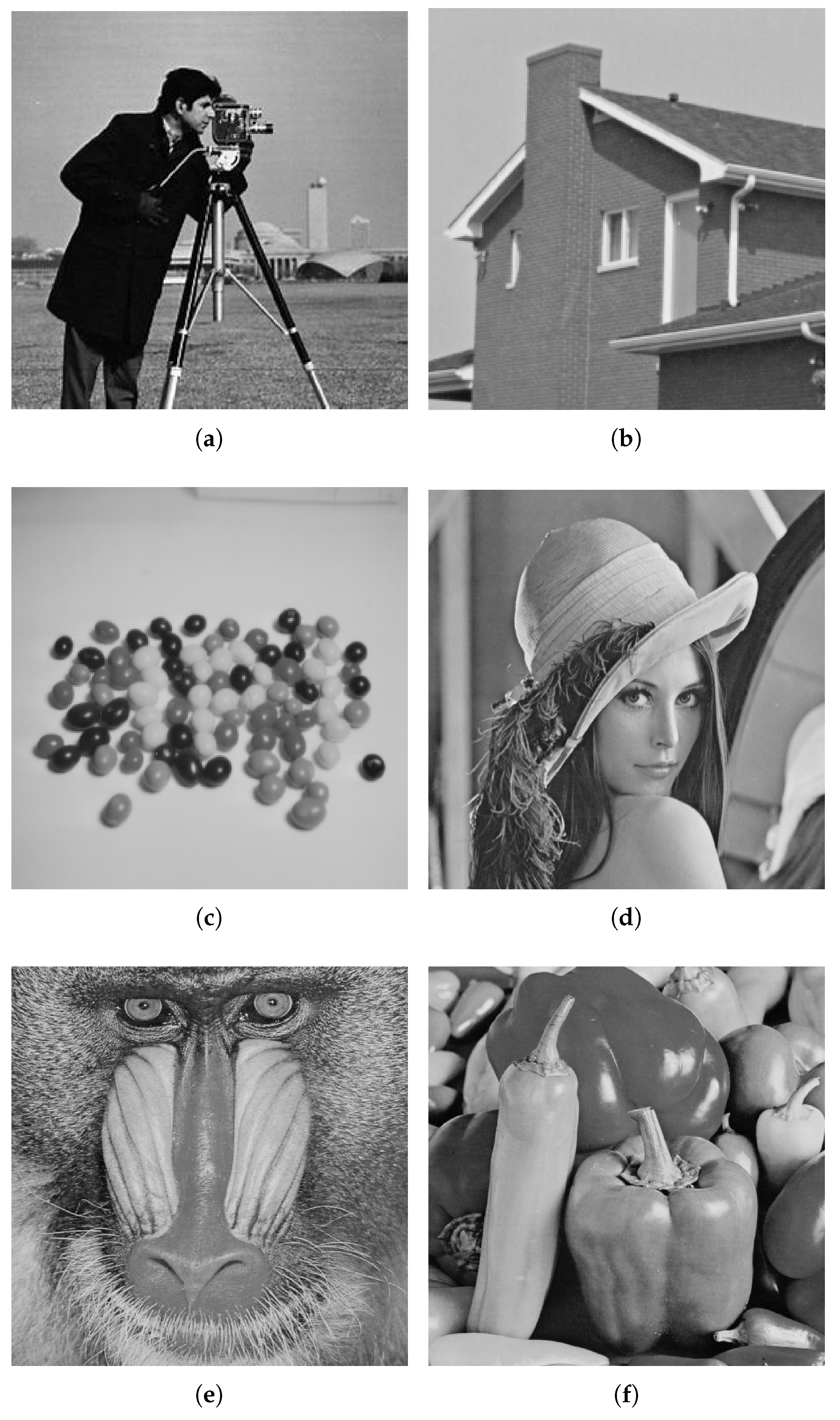
2. Proposed Technique
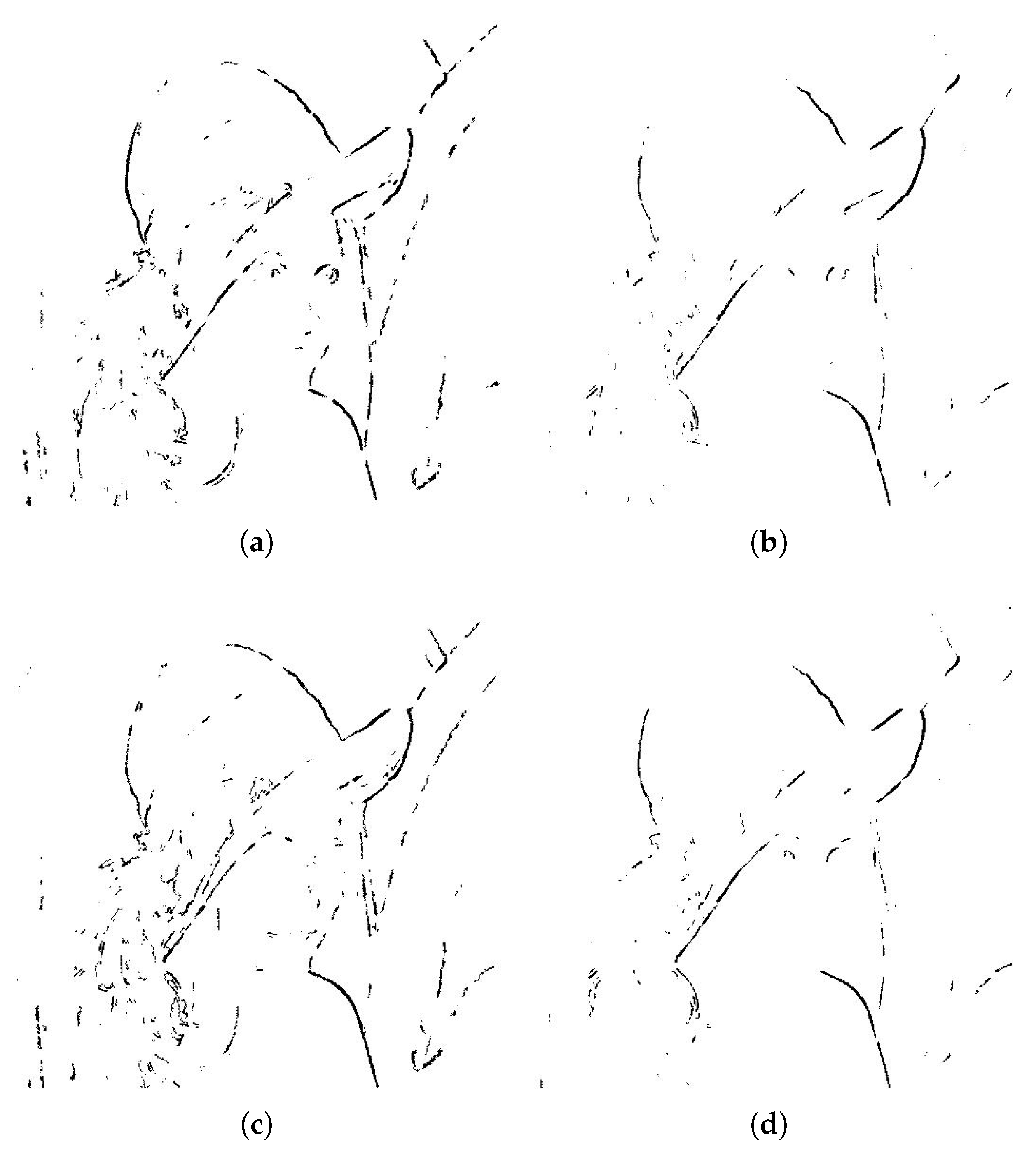
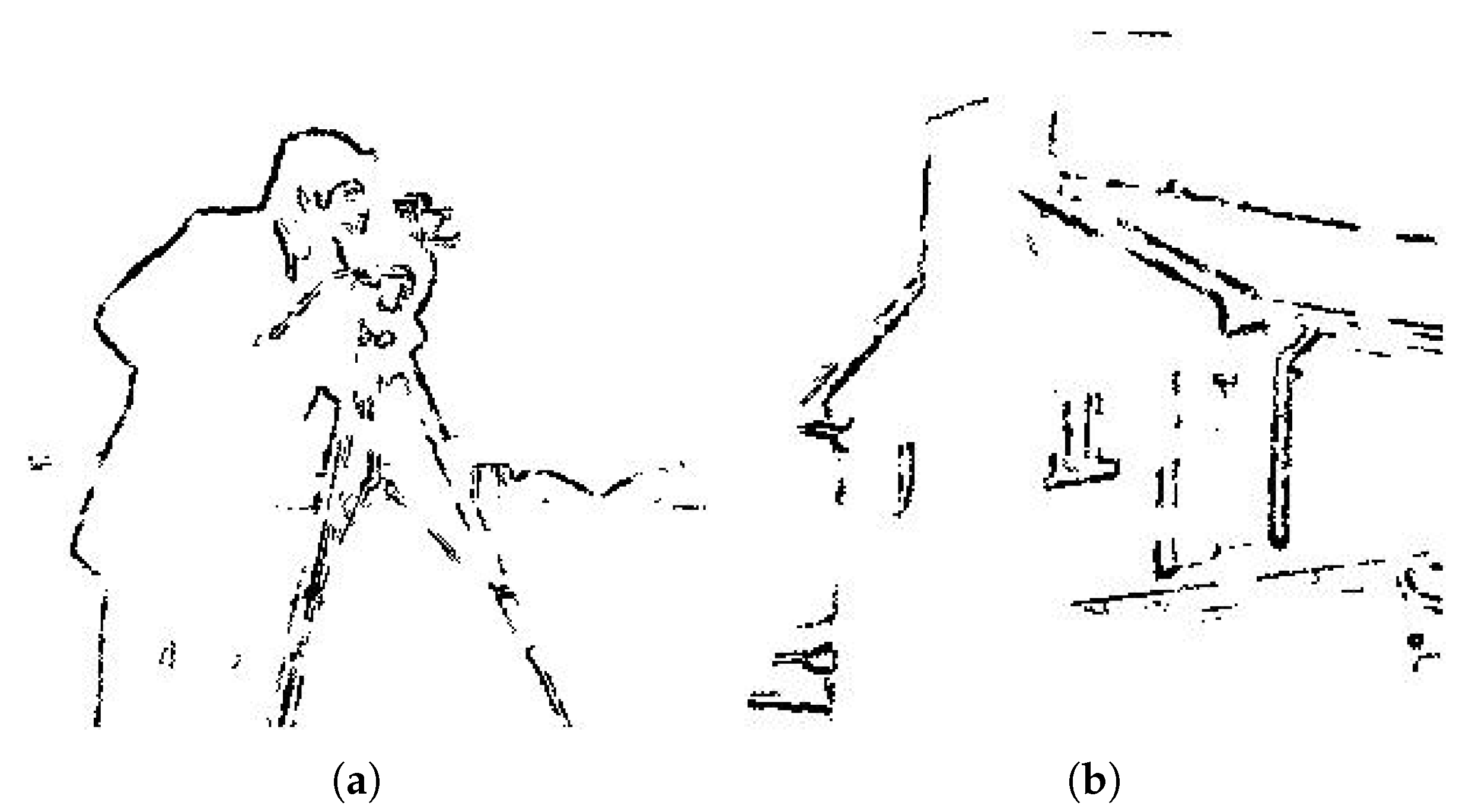
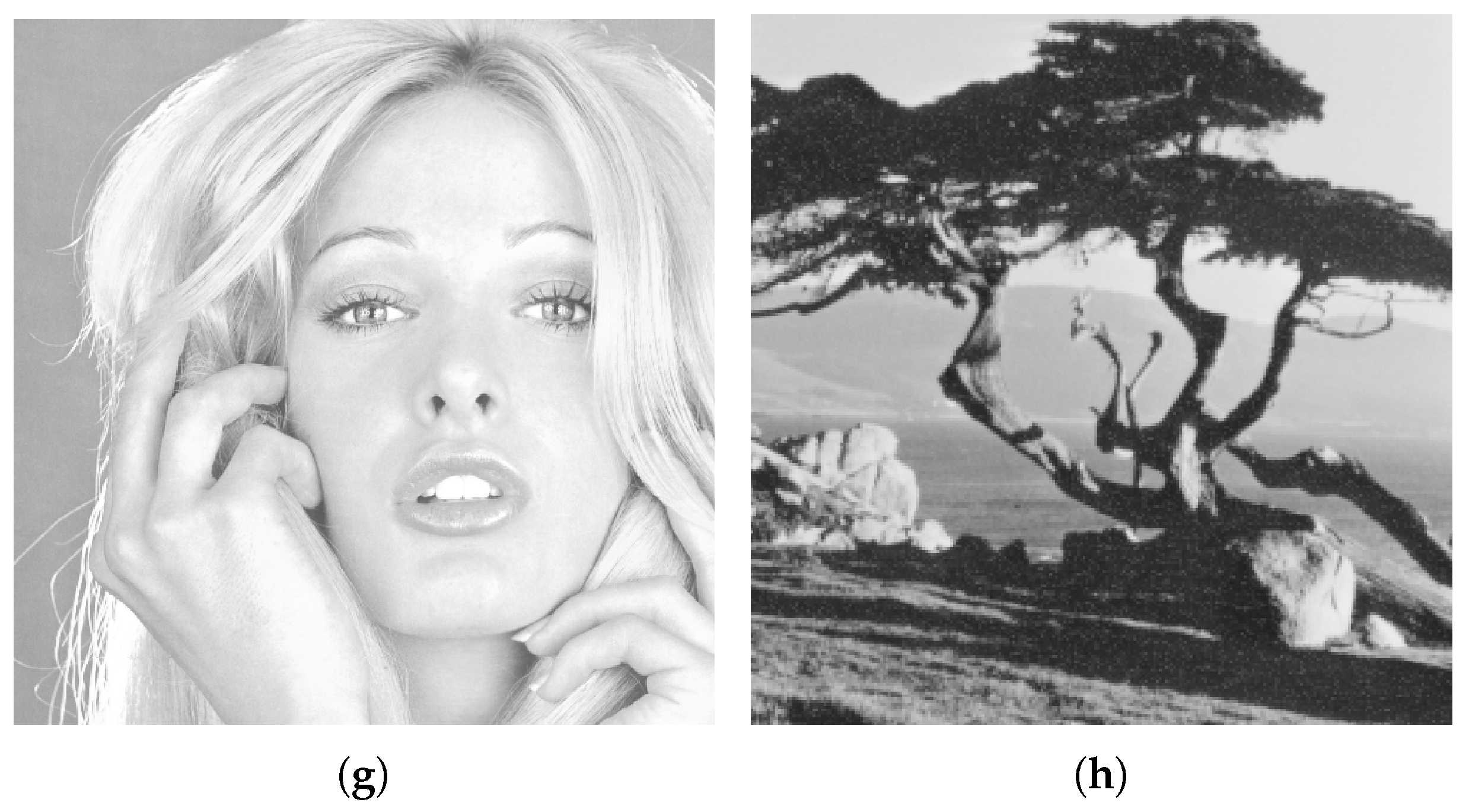
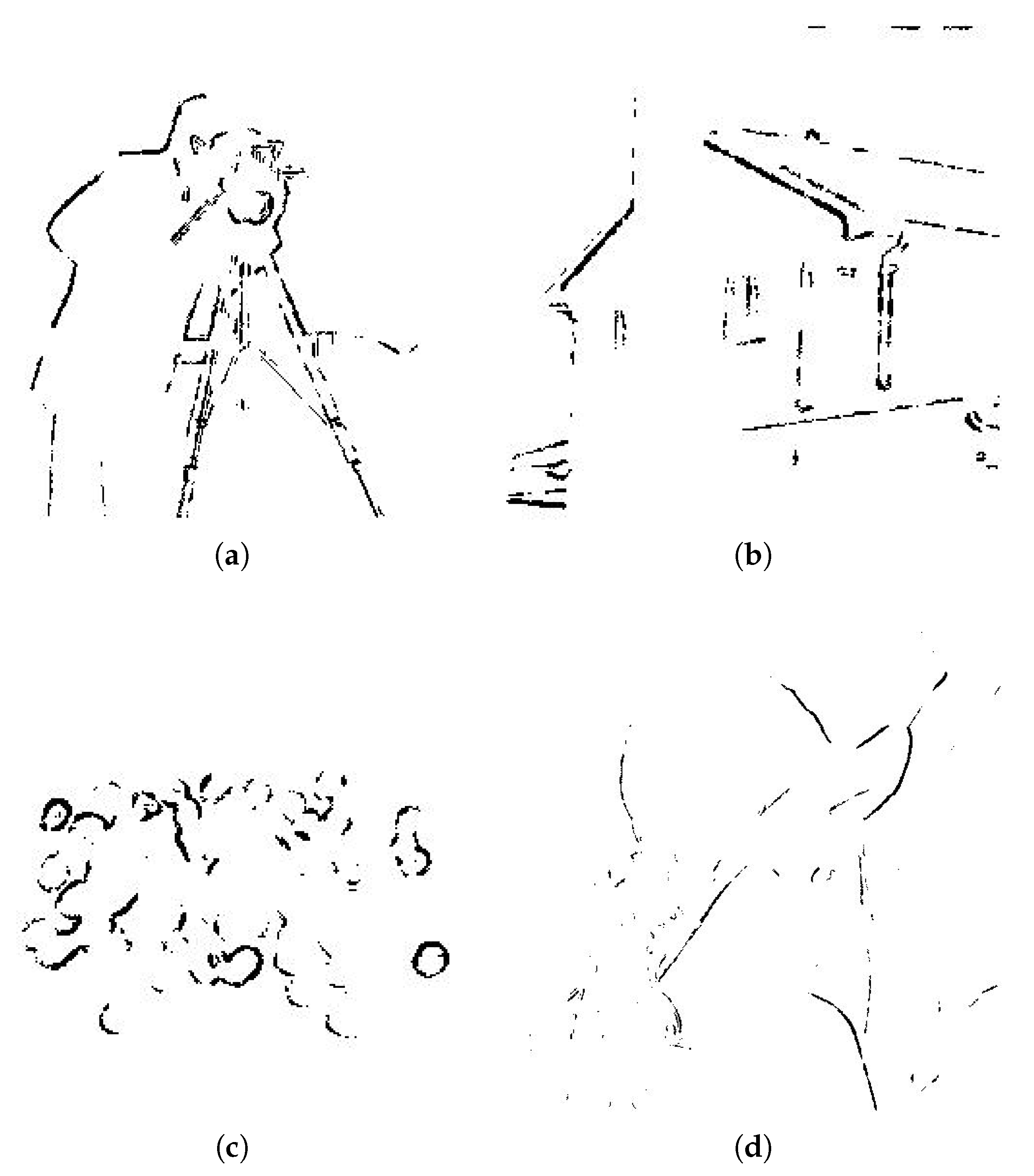
2.1. Edges Detection
- Initialization;
- Construction;
- Updating;
- Decision.
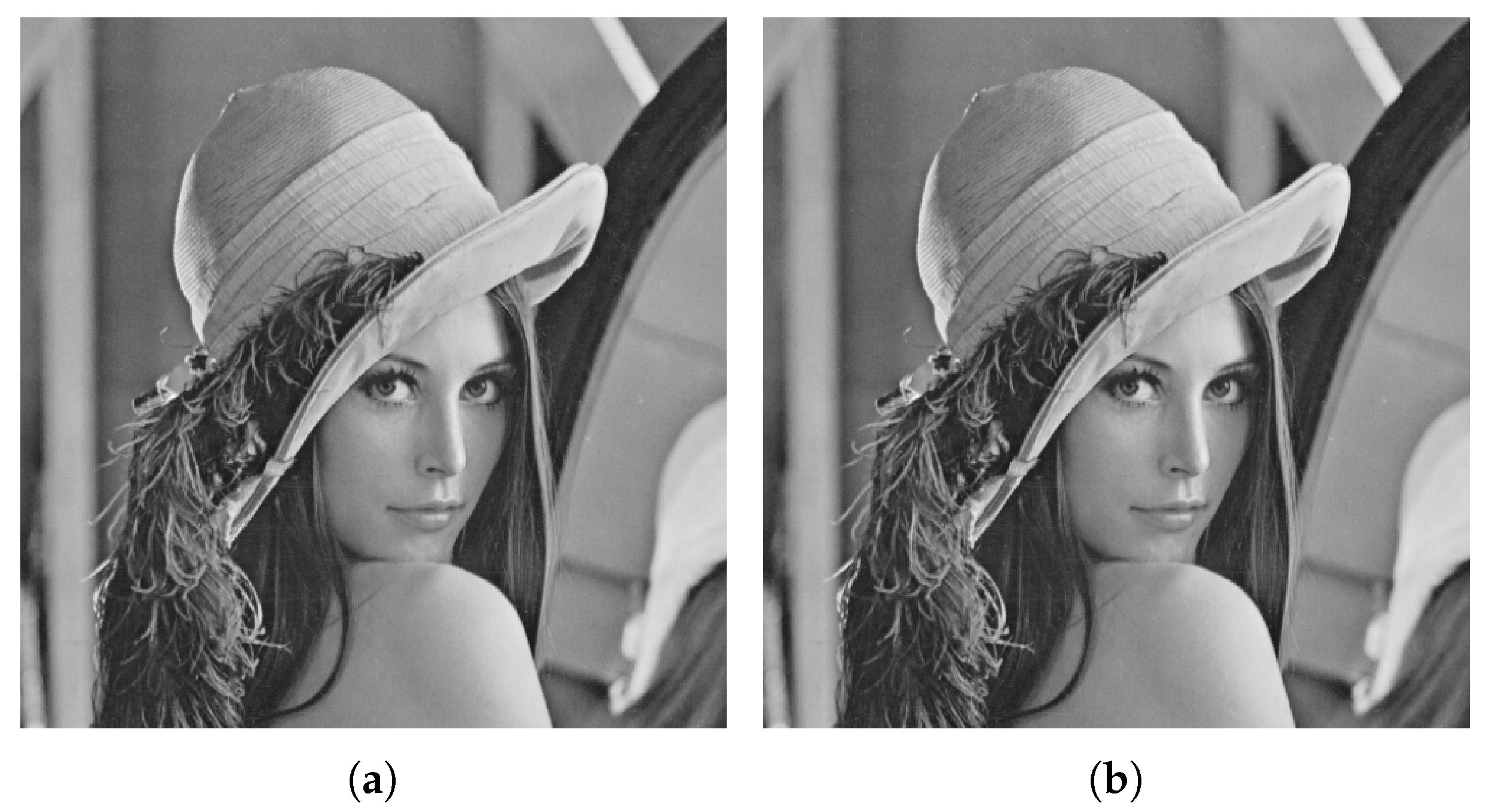
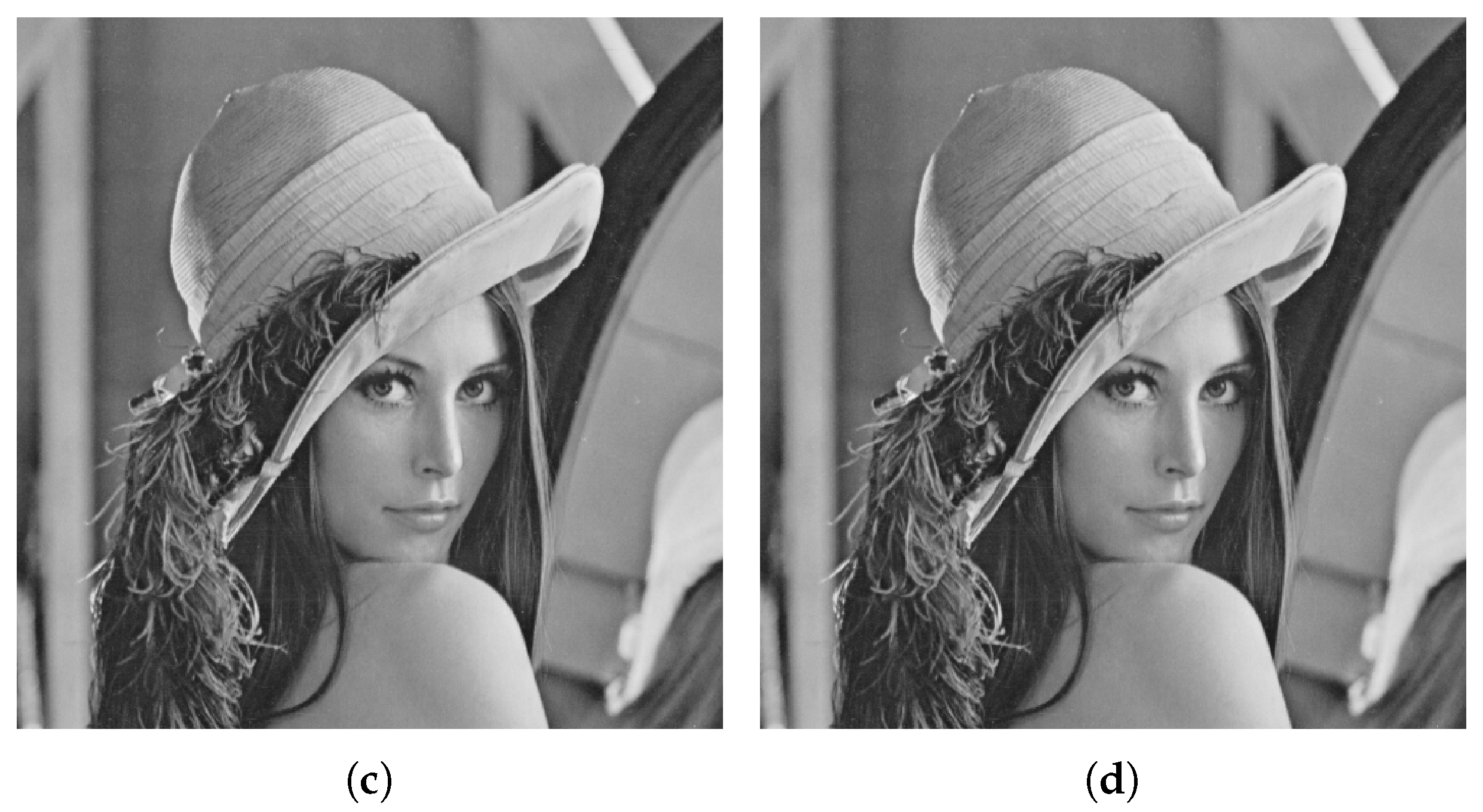
2.2. Data Hiding
2.3. Security of the Proposed Technique
2.4. Hiding Capacity and Quality Measuring Parameters of the Proposed Technique
3. Experimental Results and Analysis
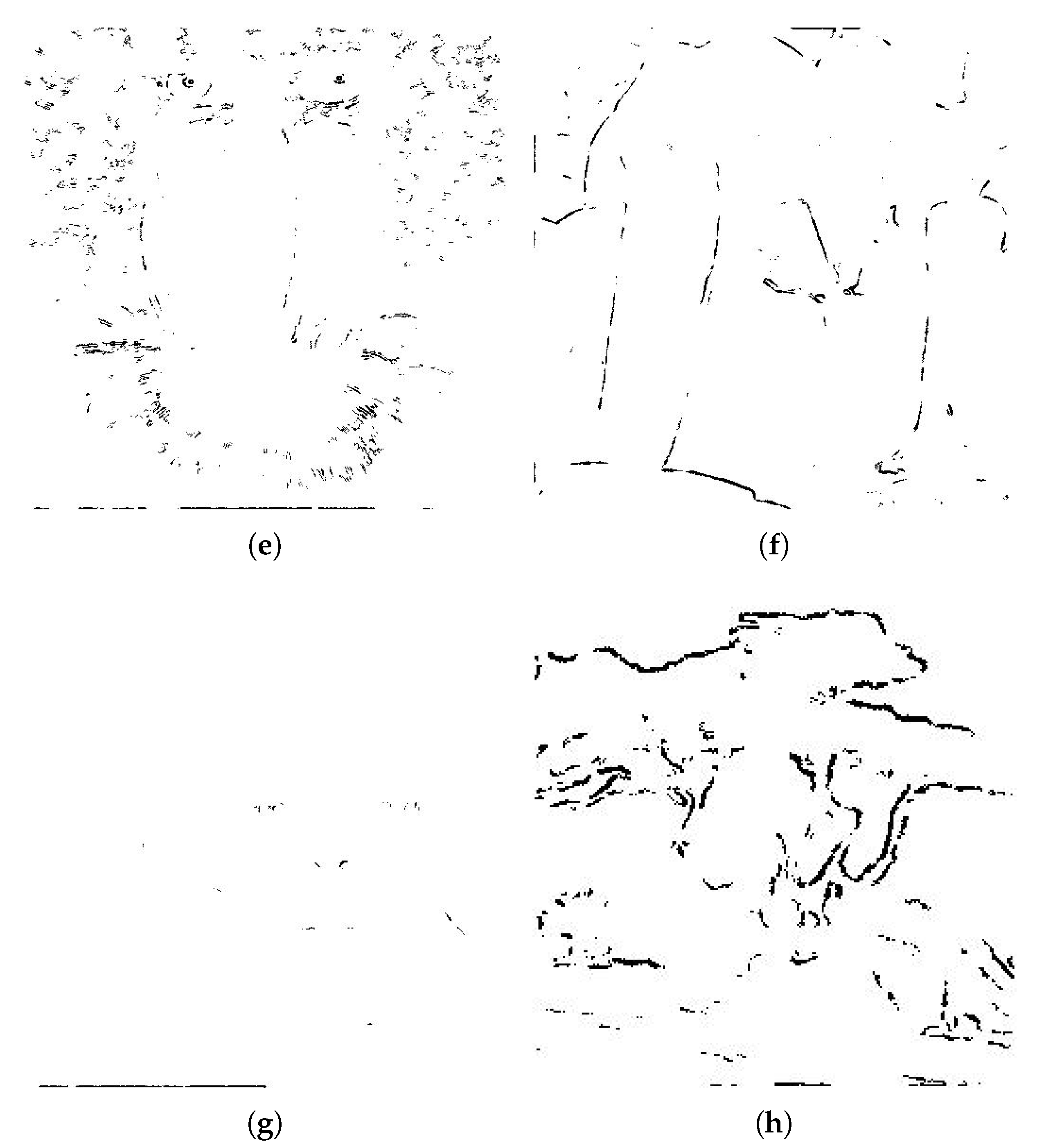
4. Comparison
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Johnson, N.; Jajodia, S. Exploring steganography: Seeing the unseen. Computer 1998, 31, 26–34. [Google Scholar] [CrossRef]
- Swanson, M.; Kobayashi, M.; Tewfik, A. Multimedia data-embedding and watermarking technologies. Proc. IEEE 1998, 86, 1064–1087. [Google Scholar] [CrossRef]
- Fridrich, J.; Goljan, M.; Du, R. Invertible authentication. In Security and Watermarking of Multimedia Contents III; International Society for Optics and Photonics: Bellingham, WA, USA, 2001; Volume 4314, pp. 197–208. [Google Scholar]
- Honsinger, C.; Jones, P.; Rabbani, M.; Stoffel, J. Lossless Recovery of an Original Image Containing Embedded Data. U.S. Patent 6,278,791, 21 August 2001. [Google Scholar]
- Kaur, D.; Verma, H.K.; Singh, R.K. Image Steganography: Hiding Secrets in Random LSB Pixels; Springer: Berlin/Heidelberg, Germany, 2020; pp. 331–341. [Google Scholar]
- Khan, S.; Yousaf, M.H.; Akram, J. Implementation of Variable Least Significant Bits Stegnography using DDDB Algorithm. Int. J. Comput. Sci. Issues 2011, 8, 292–296. [Google Scholar]
- Irfan, M.; Ahmad, N.; Khan, S. Analysis of Varying Least Significant Bits DCT and Spatial Domain Stegnography. Sindh Univ. Res. J. 2014, 46, 301–306. [Google Scholar]
- Khan, S.; Ahmad, N.; Wahid, M. Varying index varying bits substitution algorithm for the implementation of VLSB steganography. J. Chin. Inst. Eng. 2016, 39, 101–109. [Google Scholar] [CrossRef]
- Lin, J.; Lin, C.C.; Chang, C.C. Reversible Steganographic Scheme for AMBTC-Compressed Image Based on (7, 4) Hamming Code. Symmetry 2019, 11, 1236. [Google Scholar]
- Hong, W.; Ma, Y.B.; Wu, H.C.; Chen, T.S. An efficient reversible data hiding method for AMBTC compressed images. Multimed. Tools Appl. 2017, 76, 5441–5460. [Google Scholar] [CrossRef]
- Shelupanov, A.; Evsyutin, O.; Konev, A.; Kostyuchenko, E.; Kruchinin, D.; Nikiforov, D. Information Security Methods—Modern Research Directions. Symmetry 2019, 11, 150. [Google Scholar] [CrossRef]
- Khan, S.; Ismail, M.; Khan, T.; Ahmad, N. Enhanced stego block chaining (ESBC) for low bandwidth channels. Secur. Commun. Netw. 2016, 9, 6239–6247. [Google Scholar] [CrossRef]
- Khan, S.; Irfan, M.A.; Arif, A.; Ali, A.; Memon, Z.A.; Khaliq, A. Reversible-Enhanced Stego Block Chaining Image Steganography: A Highly Efficient Data Hiding Technique. Can. J. Electr. Comput. Eng. 2020, 43, 66–72. [Google Scholar] [CrossRef]
- Zakaria, A.A.; Hussain, M.; Wahab, A.W.A.; Idris, M.Y.I.; Abdullah, N.A.; Jung, K.H. High-capacity image steganography with minimum modified bits based on data mapping and LSB substitution. Appl. Sci. 2018, 8, 2199. [Google Scholar] [CrossRef]
- Sadat, E.S.; Faez, K.; Saffari Pour, M. Entropy-based video steganalysis of motion vectors. Entropy 2018, 20, 244. [Google Scholar] [CrossRef]
- Khan, S.; Ahmad, N.; Ismail, M.; Minallah, N.; Khan, T. A secure true edge based 4 least significant bits steganography. In Proceedings of the 2015 International Conference on Emerging Technologies (ICET), Peshawar, Pakistan, 19–20 December 2015; pp. 1–4. [Google Scholar]
- Rong, W.; Li, Z.; Zhang, W.; Sun, L. An improved CANNY edge detection algorithm. In Proceedings of the 2014 IEEE International Conference on Mechatronics and Automation, Tianjin, China, 6 August 2014; pp. 577–582. [Google Scholar]
- Bourennane, E.; Gouton, P.; Paindavoine, M.; Truchetet, F. Generalization of Canny–Deriche filter for detection of noisy exponential edge. Signal Process. 2002, 82, 1317–1328. [Google Scholar] [CrossRef]
- Khan, S.; Bianchi, T. Fast Image Clustering Based on Camera Fingerprint Ordering. In Proceedings of the 2019 IEEE International Conference on Multimedia and Expo (ICME), Shanghai, China, 12 July 2019; pp. 766–771. [Google Scholar]
- Gupta, S.; Mazumdar, S.G. Sobel edge detection algorithm. Int. J. Comput. Sci. Manag. Res. 2013, 2, 1578–1583. [Google Scholar]
- Yang, L.; Wu, X.; Zhao, D.; Li, H.; Zhai, J. An improved Prewitt algorithm for edge detection based on noised image. In Proceedings of the 2011 4th International Congress on Image and Signal Processing, Shanghai, China, 17 October 2011; Volume 3, pp. 1197–1200. [Google Scholar]
- Maini, R.; Aggarwal, H. Study and comparison of various image edge detection techniques. Int. J. Image Process. 2009, 3, 1–11. [Google Scholar]
- Tian, J.; Yu, W.; Xie, S. An ant colony optimization algorithm for image edge detection. In Proceedings of the 2008 IEEE Congress on Evolutionary Computation (IEEE World Congress on Computational Intelligence), Hong Kong, China, 1 June 2008; pp. 751–756. [Google Scholar]
- Guan, N.; Tao, D.; Luo, Z.; Yuan, B. NeNMF: An optimal gradient method for nonnegative matrix factorization. IEEE Trans. Signal Process. 2012, 60, 2882–2898. [Google Scholar] [CrossRef]
- Hong, W.; Chen, T. A novel data embedding method using adaptive pixel pair matching. IEEE Trans. Inf. Forensics Secur. 2011, 7, 176–184. [Google Scholar] [CrossRef]
- Hsu, C.; Tu, S. Probability-based tampering detection scheme for digital images. Opt. Commun. 2010, 283, 1737–1743. [Google Scholar] [CrossRef]
- Subhedar, M.; Mankar, V. Current status and key issues in image steganography: A survey. Comput. Sci. Rev. 2014, 13, 95–113. [Google Scholar] [CrossRef]
- Hong, W.; Chen, T.; Shiu, C. Reversible data hiding for high quality images using modification of prediction errors. J. Syst. Softw. 2009, 82, 1833–1842. [Google Scholar] [CrossRef]
- Jung, K.; Yoo, K. Data hiding using edge detector for scalable images. Multimed. Tools Appl. 2014, 71, 1455–1468. [Google Scholar] [CrossRef]
- Khan, S.; Bianchi, T. Ant colony optimization (aco) based data hiding in image complex region. Int. J. Electr. Comput. Eng. 2018, 8, 379–389. [Google Scholar] [CrossRef]
- Dorigo, M.; Thomas, S. Ant Colony Optimization; MIT Press: Cambridge, UK, 2004. [Google Scholar]
- Duan, H. Ant Colony Algorithms: Theory and Applications; Chinese Science: Beijing, China, 2005. [Google Scholar]
- Wang, Z.; Bovik, A. A universal image quality index. IEEE Signal Process. Lett. 2002, 9, 81–84. [Google Scholar] [CrossRef]
- Wang, Z.; Bovik, A.; Sheikh, H.; Simoncelli, E. Image quality assessment: From error visibility to structural similarity. IEEE Trans. Image Process. 2004, 13, 600–612. [Google Scholar] [CrossRef]
- Macq, B.; Dewey, F. Trusted headers for medical images. In Proceedings of the DFG VIII-D II Watermarking Workshop, Erlangen, Germany, 3 October 1999; Volume 10. [Google Scholar]
- Lin, Y.C.; Li, T.S. Reversible Image Data Hiding Using Quad-tree Segmentation and Histogram Shifting. J. Multimed. 2011, 6, 349–358. [Google Scholar] [CrossRef]
- Jaiswal, S.P.; Au, O.; Jakhetiya, V.; Guo, A.Y.; Tiwari, A.K. Adaptive predictor structure based interpolation for reversible data hiding. In Proceedings of the International Workshop on Digital Watermarking, Taipei, Taiwan, 1 October 2014; pp. 276–288. [Google Scholar]
- Goljan, M.; Fridrich, J.; Du, R. Distortion-free data embedding for images. In Proceedings of the International Workshop on Information Hiding, Pittsburgh, PA, USA, 27 April 2001; pp. 27–41. [Google Scholar]
- Vleeschouwer, C.; Delaigle, J.; Macq, B. Circular interpretation of histogram for reversible watermarking. In Proceedings of the 2001 IEEE Fourth Workshop on Multimedia Signal Processing, Cannes, France, 5 October 2001; pp. 345–350. [Google Scholar]

| Evaluation Metrics | ||||
|---|---|---|---|---|
| LSBs | HC (%) | MSE | PSNR (dB) | SSIM |
| 1–7 | 4.9957 | 0.0984 | 58.2014 | 0.9998 |
| 1–6 | 4.4098 | 0.0833 | 58.9269 | 0.9999 |
| 1–5 | 3.8597 | 0.1238 | 57.2022 | 0.9999 |
| 1–4 | 3.2623 | 0.1669 | 55.907 | 0.9998 |
| 2–7 | 5.5374 | 0.613 | 50.2564 | 0.9993 |
| 3–7 | 6.115 | 2.1942 | 44.7181 | 0.9953 |
| 4–7 | 6.6452 | 4.2274 | 41.8701 | 0.9814 |
| 5–7 | 7.1396 | 1.3091 | 46.9611 | 0.9993 |
| 6–7 | 7.6271 | 2.3995 | 44.3295 | 0.9955 |
| Evaluation Metrics | ||||
|---|---|---|---|---|
| LSBs | HC (%) | MSE | PSNR (dB) | SSIM |
| 1–7 | 2.4155 | 0.0466 | 61.4498 | 0.9999 |
| 1–6 | 2.1362 | 0.0472 | 61.3876 | 0.9999 |
| 1–5 | 1.8539 | 0.0709 | 59.6267 | 1 |
| 1–4 | 1.5465 | 0.1843 | 55.4764 | 0.9999 |
| 2–7 | 2.6779 | 0.2758 | 53.7246 | 0.9997 |
| 3–7 | 2.9373 | 0.522 | 50.9538 | 0.9994 |
| 4–7 | 3.1715 | 2.2708 | 44.569 | 0.9944 |
| 5–7 | 3.4027 | 0.5484 | 50.7398 | 0.9997 |
| 6–7 | 3.6476 | 1.1575 | 47.4955 | 0.998 |
| Evaluation Metrics | ||||
|---|---|---|---|---|
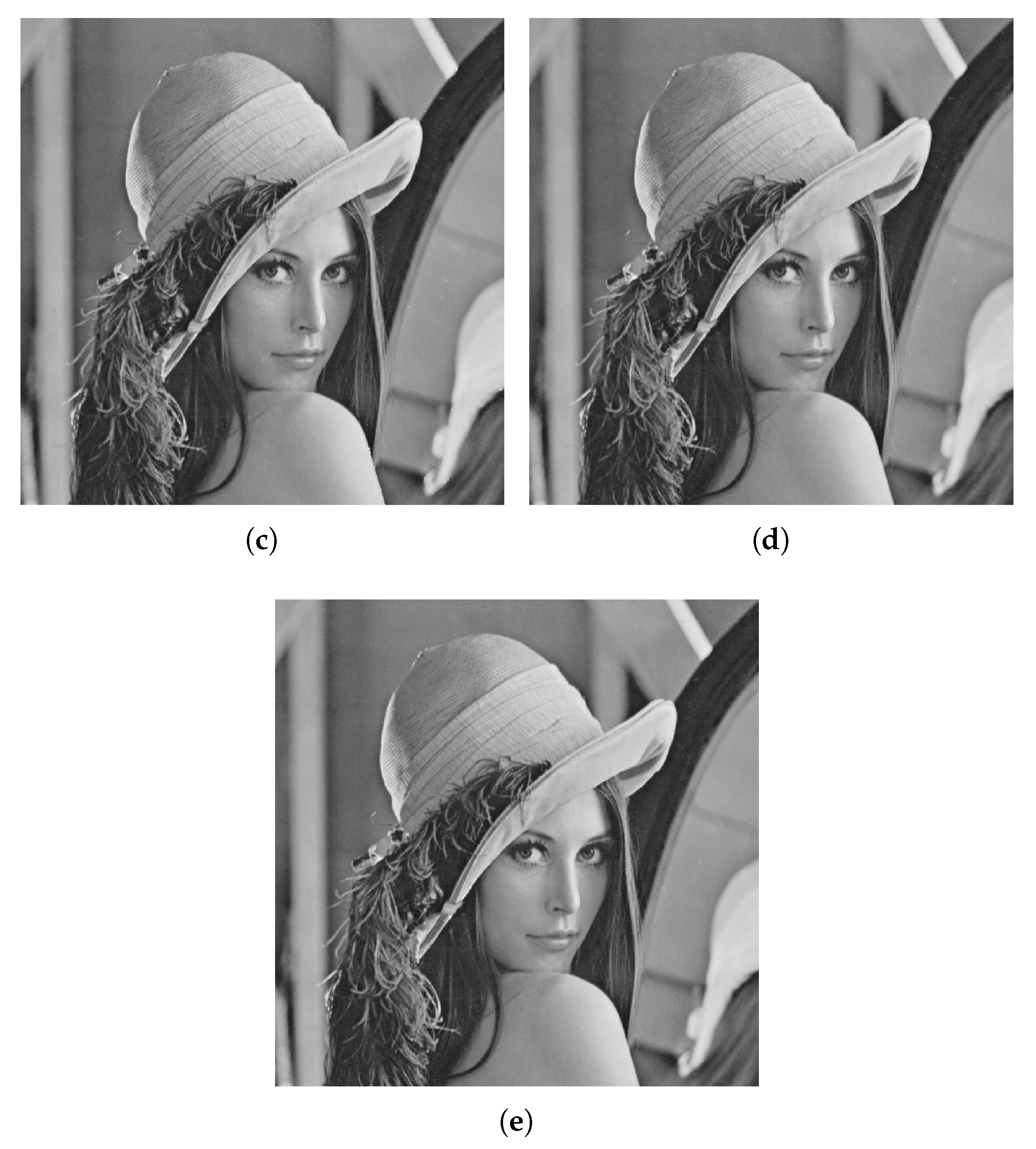
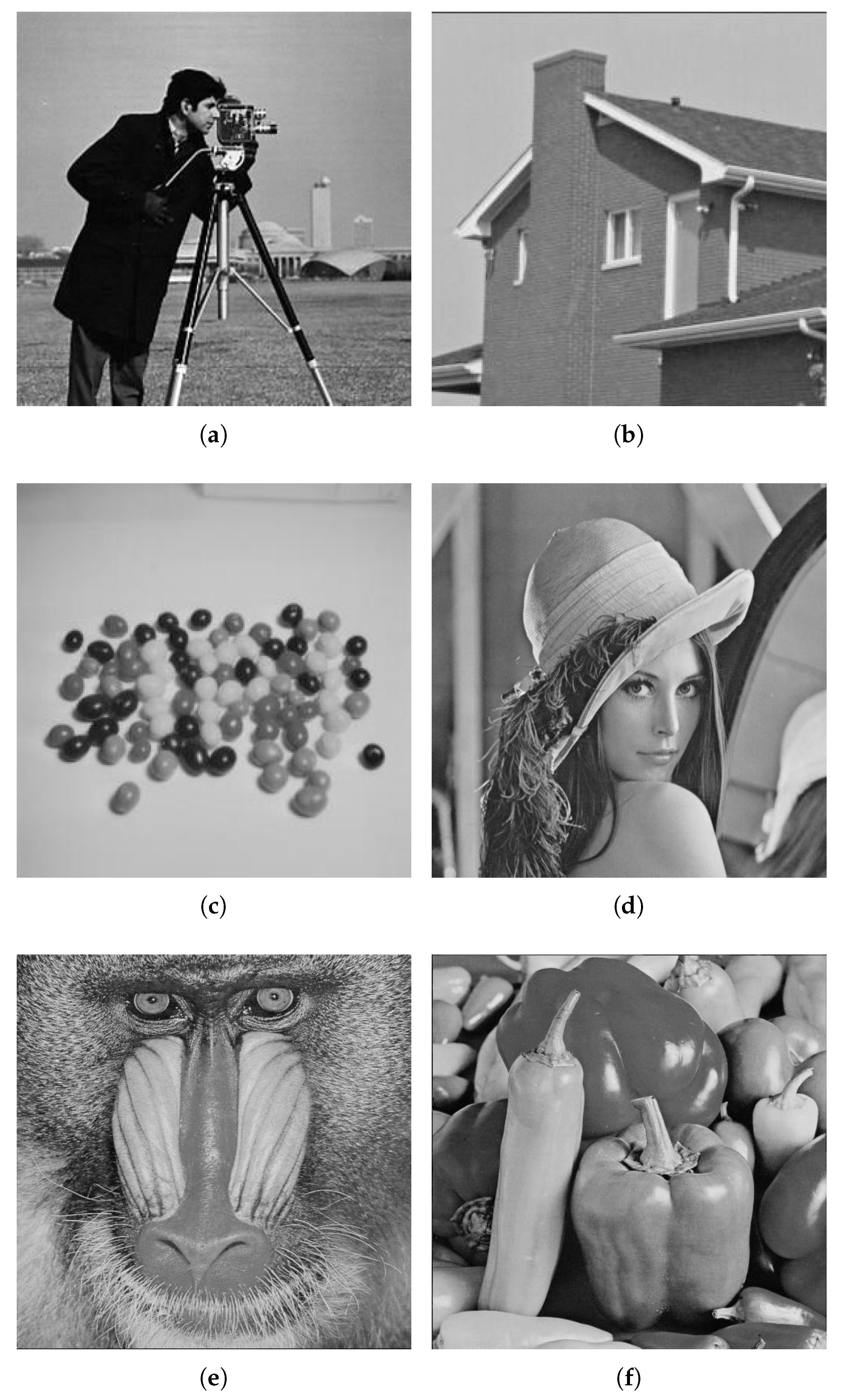
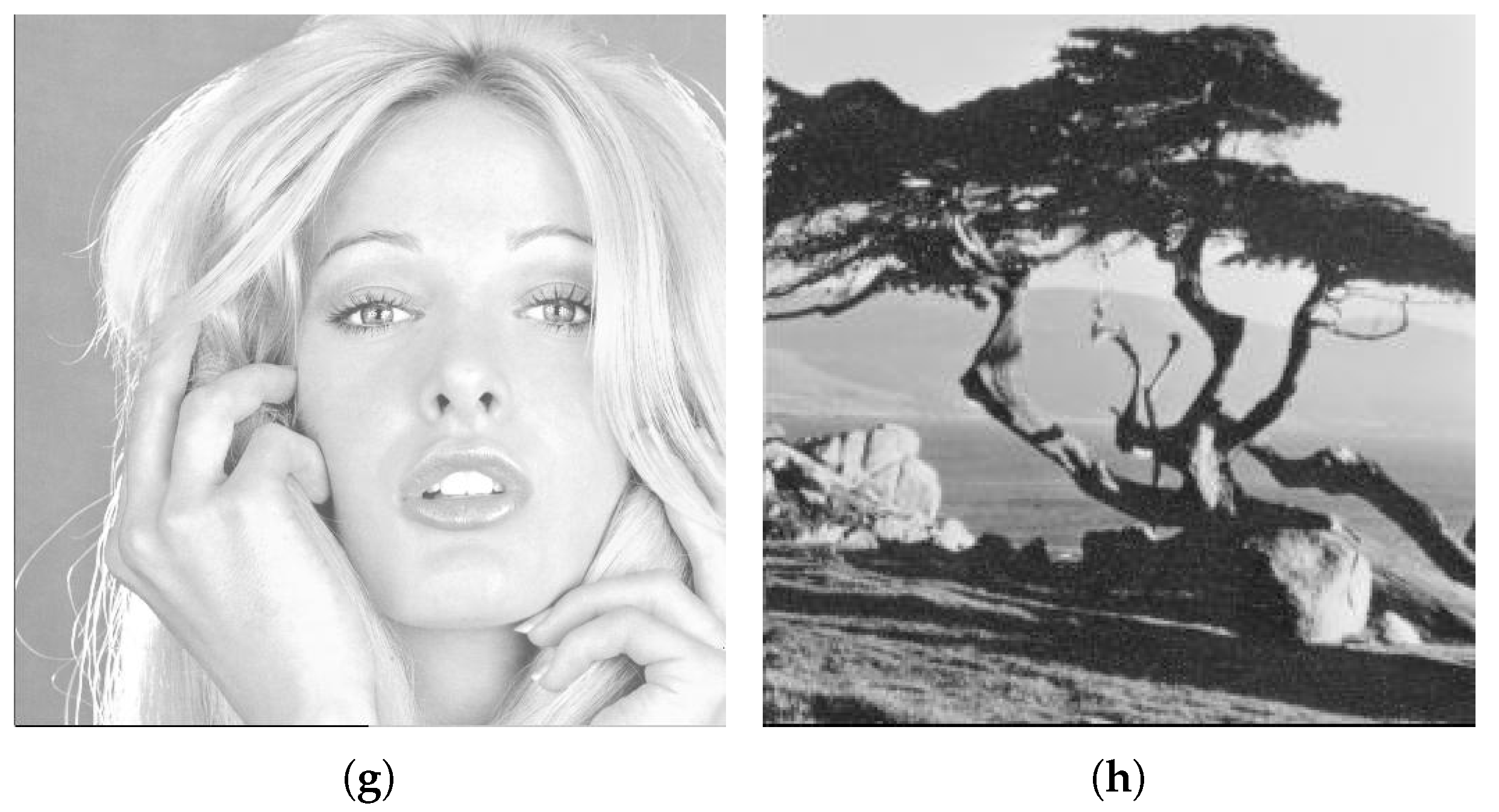
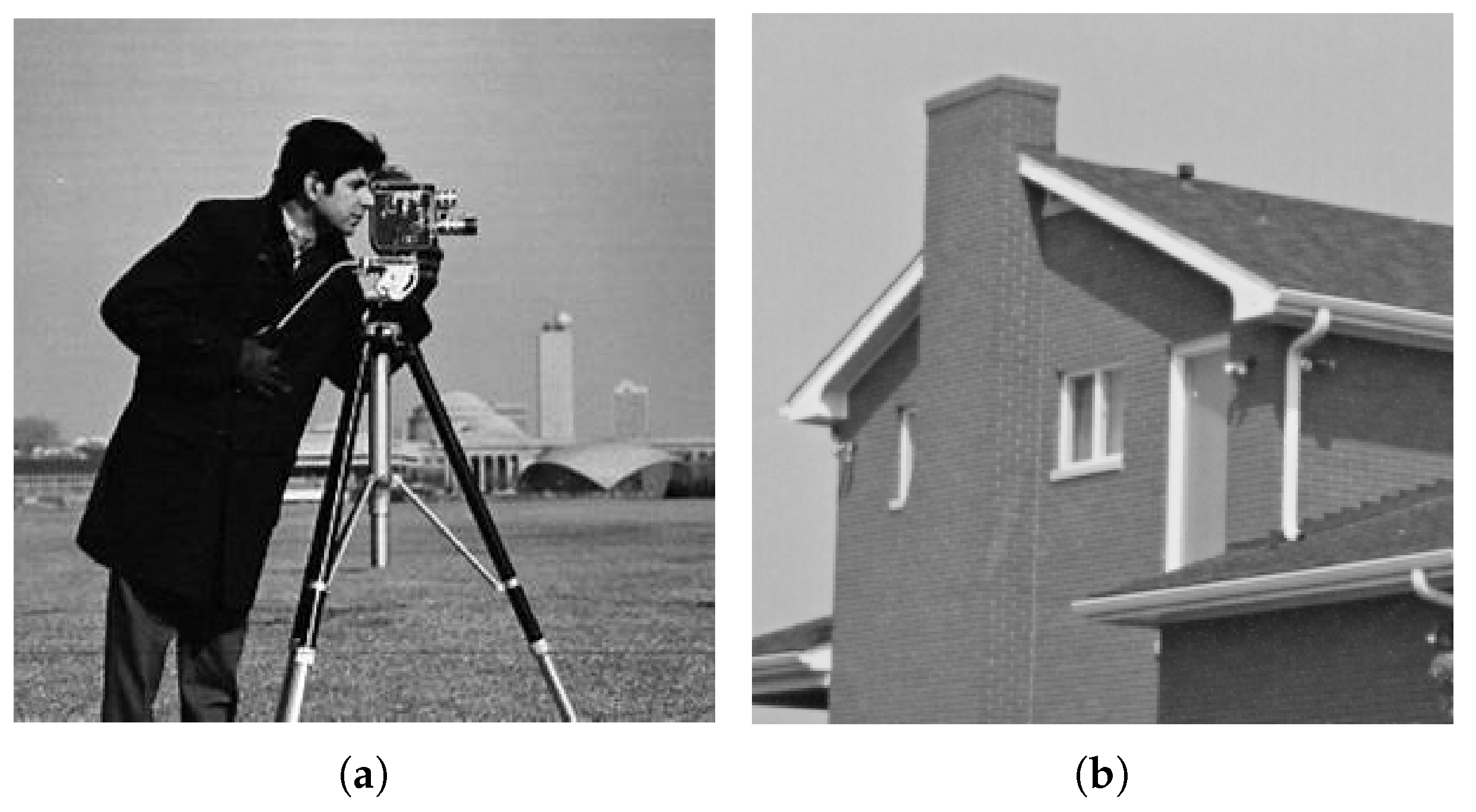
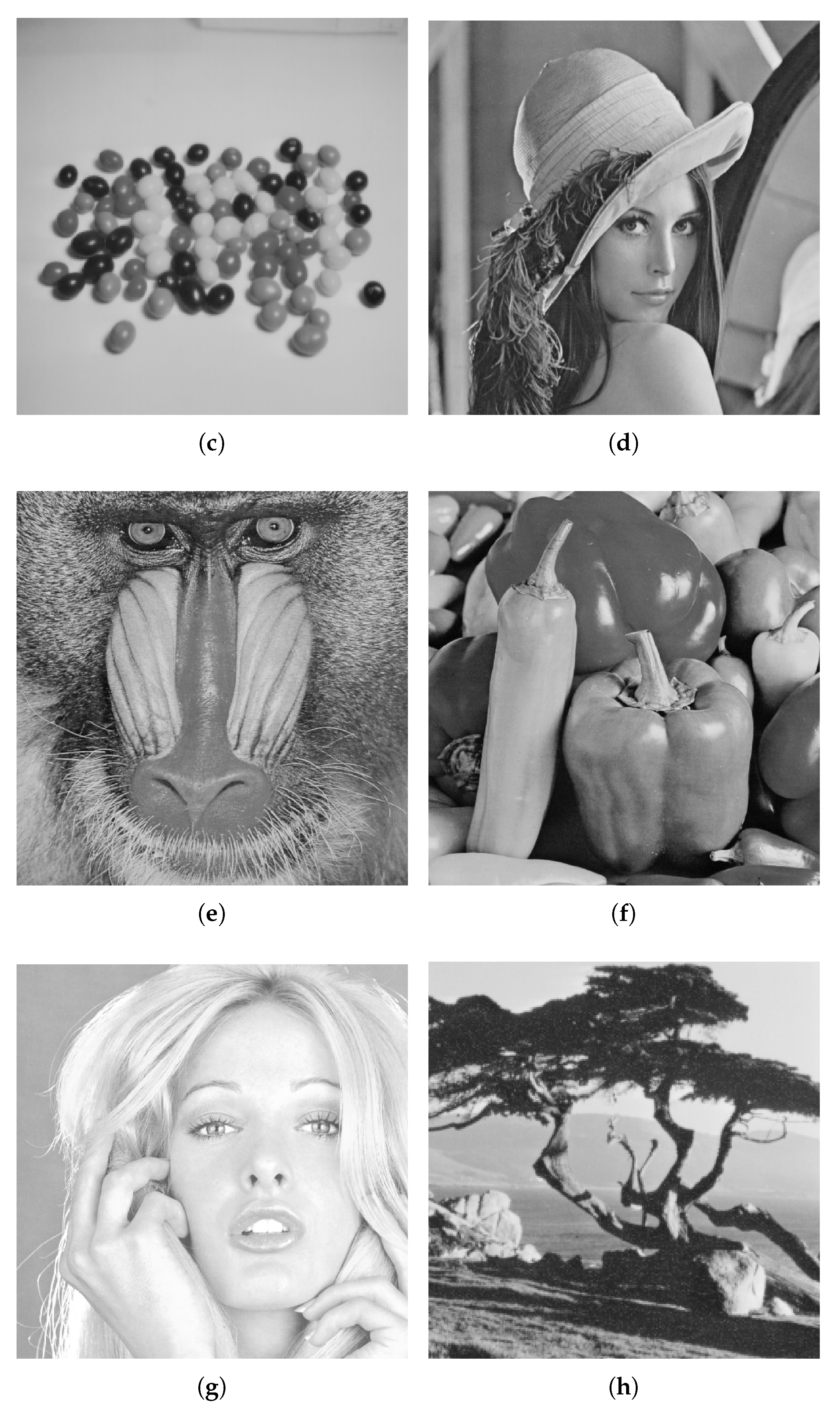
| Cover Image | HC (%) | MSE | PSNR (dB) | SSIM |
| Cameraman | 3.45 | 0.2899 | 53.509 | 0.9998 |
| House | 4.2465 | 0.3486 | 52.7071 | 0.9997 |
| Jellybeans | 3.4813 | 0.175 | 55.6992 | 0.9998 |
| Lena | 4.9957 | 0.0984 | 58.2014 | 0.9998 |
| Mandrill | 6.2538 | 0.299 | 53.3739 | 0.9997 |
| Pepper | 5.8495 | 0.1755 | 55.6871 | 0.9998 |
| Tiffany | 5.2208 | 0.1346 | 56.8389 | 0.9997 |
| Tree | 6.1729 | 0.1013 | 58.0739 | 0.9999 |
| Evaluation Metrics | ||||
|---|---|---|---|---|
| Cover Image | HC (%) | MSE | PSNR (dB) | SSIM |
| Cameraman | 2.4826 | 0.262 | 53.9474 | 0.9999 |
| House | 1.738 | 0.1282 | 57.0528 | 0.9999 |
| Jellybeans | 2.1805 | 0.071 | 59.6155 | 0.9999 |
| Lena | 2.4155 | 0.0466 | 61.4498 | 0.9999 |
| Mandrill | 2.9213 | 0.1093 | 57.744 | 0.9999 |
| Pepper | 3.6858 | 0.0898 | 58.5989 | 0.9999 |
| Tiffany | 2.1339 | 0.0425 | 61.8489 | 0.9999 |
| Tree | 4.6516 | 0.1425 | 56.5921 | 0.9999 |
| Technique | Lena | Mandrill | ||||
|---|---|---|---|---|---|---|
| Honsinger et al. | <0.0156 | - | - | <0.0156 | - | - |
| Macq and Dewey | 0.0325 | 48.45 | 0.9891 | 0.12 | 49.34 | 0.9979 |
| Fridrich et al. | 0.0156 | - | - | 0.0156 | - | - |
| Lin and Li [36] | 0.0038 | 52.4572 | 0.9981 | 0.0038 | 53.3997 | 0.9995 |
| Jaiswal et al. [37] | 0.0.2630 | 48.7501 | 0.9754 | 0.0948 | 48.3449 | 0.9963 |
| Goljan et al. | 0.36 | 39.00 | 0.9915 | 0.44 | 39.00 | 0.9871 |
| Vleeschouwer et al. | 0.0156 | 30.00 | 0.8662 | 0.0156 | 29.00 | 0.8469 |
| Khan et al. | 0.33 | 46.23 | 0.8771 | 0.669 | 44.12 | 0.9508 |
| Khan and Tiziano | 0.0310 | 42.95 | 0.9976 | 0.0211 | 37.64 | 0.9912 |
| Proposed Technique (Flat) | 4.9957 | 58.2014 | 0.9998 | 6.2538 | 53.3739 | 0.9997 |
| Proposed Technique (Gaussian) | 2.1455 | 61.4498 | 0.9999 | 2.9213 | 57.744 | 0.9999 |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Khan, S.; Irfan, M.A.; Khan, K.; Khan, M.; Khan, T.; Khan, R.U.; Ijaz, M.F. ACO Based Variable Least Significant Bits Data Hiding in Edges Using IDIBS Algorithm. Symmetry 2020, 12, 781. https://doi.org/10.3390/sym12050781
Khan S, Irfan MA, Khan K, Khan M, Khan T, Khan RU, Ijaz MF. ACO Based Variable Least Significant Bits Data Hiding in Edges Using IDIBS Algorithm. Symmetry. 2020; 12(5):781. https://doi.org/10.3390/sym12050781
Chicago/Turabian StyleKhan, Sahib, Muhammad Abeer Irfan, Khalil Khan, Mushtaq Khan, Tawab Khan, Rehan Ullah Khan, and Muhammad Fazal Ijaz. 2020. "ACO Based Variable Least Significant Bits Data Hiding in Edges Using IDIBS Algorithm" Symmetry 12, no. 5: 781. https://doi.org/10.3390/sym12050781
APA StyleKhan, S., Irfan, M. A., Khan, K., Khan, M., Khan, T., Khan, R. U., & Ijaz, M. F. (2020). ACO Based Variable Least Significant Bits Data Hiding in Edges Using IDIBS Algorithm. Symmetry, 12(5), 781. https://doi.org/10.3390/sym12050781






