Quantum-Safe Blockchain: Mapping Research Fronts in Post-Quantum Cryptography, Quantum Threat Models, and QKD Integration
Abstract
1. Introduction
2. Methodology
2.1. Reporting Framework and Overview
2.2. Data Sources and Retrieval
2.3. Search Strategy and Query Design
2.3.1. Concept Blocks
- G1: Blockchain and ledger systems. Captures blockchain-related architectures and applications, including distributed ledgers, cryptocurrencies, smart contracts, and DeFi.
- G2: Quantum threat models and quantum-safe security. Captures quantum-era threat signals and countermeasure lines, including post-quantum and quantum-resistant framing, canonical quantum algorithms used in threat discussions, quantum computing, and QKD.
2.3.2. Operational Query
G1: (blockchain OR “distributed ledger*” OR cryptocurrency OR “smart contract*” OR DeFi)
G2: (“post-quantum” OR “quantum-safe” OR “quantum safe” OR “quantum-resistant” OR “quantum resistant” OR “quantum attack*” OR shor OR grover OR “quantum computing” OR “quantum key distribution” OR QKD)
Final query: G1 AND G2
2.4. Eligibility Criteria
2.4.1. Inclusion Criteria
- Document type: journal articles, including items indexed as early access.
- Language: English.
2.4.2. Exclusion Criteria
- Language: non-English publications (Chinese, Korean, and Spanish records were excluded).
- Document type: conference papers, books and book chapters, review articles, proceeding papers, retracted items, and editorial material.
2.5. Record Management, Deduplication, and PRISMA Flow
2.6. Bibliometric Performance Indicators and Selection of Highly Cited Contributions
2.7. Thematic Analysis Based on Author Keywords
2.8. Keyword Preprocessing for Thematic Mapping
blockchain, blockchains, technology, technologies, system, systems, architecture, framework, model, models, modeling, security, cryptography, quantum, post-quantum, post quantum, quantum computing, protocol, protocols, algorithm, algorithms, scheme, schemes, approach, methods, performance, evaluation, validation, testing, implementation, design, development, management, issues, future, proposals, state, communication, computing, computation, computers, computer, networks, network, servers, devices, data, information, vectors, costs, efficient/efficiency, secure, smart, artificial, internet of, na, privacy, internet, challenges, efficient, things, 0, current, article, review, reviews, surveys, literature review, systematic, systematic review, bibliometrics, bibliometric analysis, analysis, taxonomy, research, research trends, trends, intelligence, protection, optimization, signature, signatures, functions.
3. Results
3.1. Scientific Production by Year
3.2. Geographic Distribution
3.2.1. Publications by Country
3.2.2. International Collaboration Network Between Countries
3.2.3. Corresponding Authors by Country
3.3. Leading Institutional Affiliations
3.4. Most Relevant Sources
3.5. Overview of the Most Salient Studies
| Title | Year | TC | TC/Year | Study |
|---|---|---|---|---|
| Security and Privacy for 6G: A Survey on Prospective Technologies and Challenges | 2021 | 322 | 53.67 | [35] |
| The Roadmap to 6G Security and Privacy | 2021 | 240 | 40.00 | [36] |
| Metaverse for Healthcare: A Survey on Potential Applications, Challenges and Future Directions | 2023 | 202 | 50.50 | [41] |
| Quantum-secured blockchain | 2018 | 180 | 20.00 | [37] |
| Advancements in Computing: Emerging Trends in Computational Science with Next-Generation Computing | 2024 | 180 | 60.00 | [42] |
| Cybersecurity in logistics and supply chain management: An overview and future research directions | 2021 | 121 | 20.17 | [43] |
| A Secure Cryptocurrency Scheme Based on Post-Quantum Blockchain | 2018 | 117 | 13.00 | [38] |
| Applications of Distributed Ledger Technologies to the Internet of Things: A Survey | 2020 | 116 | 16.57 | [44] |
| AI-Empowered Fog/Edge Resource Management for IoT Applications: A Comprehensive Review, Research Challenges, and Future Perspectives | 2024 | 115 | 38.33 | [45] |
| Security Considerations for Internet of Things: A Survey | 2020 | 113 | 16.14 | [46] |
| Modern computing: Vision and challenges | 2024 | 86 | 28.67 | [39] |
| Integrating Post-Quantum Cryptography and Blockchain to Secure Low-Cost IoT Devices | 2025 | 21 | 10.50 | [40] |
3.6. Author Keywords Word Cloud
3.7. Co-Occurrence Network of Author Keywords
3.8. Thematic Map of Author Keywords
4. Discussion
4.1. Acceleration of the Field and the Consolidation of a Recent Research Surge
4.2. Geographic Concentration, Collaboration Structure, and Leadership Profiles
4.3. Institutional Structure and Dissemination Channels
4.4. Influence Profile of Highly Cited Contributions and What It Implies for Research Maturity
4.5. Thematic Structure: Coupling of IoT Deployment, Post-Quantum Migration, Privacy, and Quantum Communication
4.6. Data-Lifetime-Sensitive Interpretation of Quantum Threats in Blockchain Systems
4.7. Implications for the Development of Quantum-Safe Blockchain Research
4.8. Limitations of This Review
5. Conclusions
Supplementary Materials
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Zheng, Z.; Xie, S.; Dai, H.; Chen, X.; Wang, H. An Overview of Blockchain Technology: Architecture, Consensus, and Future Trends. In 2017 IEEE International Congress on Big Data (BigData Congress), Honolulu, HI, USA, 25–30 June 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 557–564. [Google Scholar] [CrossRef]
- Androulaki, E.; Barger, A.; Bortnikov, V.; Cachin, C.; Christidis, K.; De Caro, A.; Enyeart, D.; Ferris, C.; Laventman, G.; Manevich, Y.; et al. Hyperledger Fabric: A Distributed Operating System for Permissioned Blockchains. In Proceedings of the Thirteenth EuroSys Conference (EuroSys 2018), Porto, Portugal, 23–26 April 2018; Association for Computing Machinery: New York, NY, USA, 2018; pp. 1–15. [Google Scholar] [CrossRef]
- Christidis, K.; Devetsikiotis, M. Blockchains and Smart Contracts for the Internet of Things. IEEE Access 2016, 4, 2292–2303. [Google Scholar] [CrossRef]
- Tschorsch, F.; Scheuermann, B. Bitcoin and Beyond: A Technical Survey on Decentralized Digital Currencies. IEEE Commun. Surv. Tutor. 2016, 18, 2084–2123. [Google Scholar] [CrossRef]
- Xiao, Y.; Zhang, N.; Lou, W.; Hou, Y.T. A Survey of Distributed Consensus Protocols for Blockchain Networks. IEEE Commun. Surv. Tutor. 2020, 22, 1432–1465. [Google Scholar] [CrossRef]
- Saberi, S.; Kouhizadeh, M.; Sarkis, J.; Shen, L. Blockchain Technology and Its Relationships to Sustainable Supply Chain Management. Int. J. Prod. Res. 2019, 57, 2117–2135. [Google Scholar] [CrossRef]
- Dunphy, P.; Petitcolas, F.A.P. A First Look at Identity Management Schemes on the Blockchain. IEEE Secur. Priv. 2018, 16, 20–29. [Google Scholar] [CrossRef]
- Hasselgren, A.; Kralevska, K.; Gligoroski, D.; Pedersen, S.A.; Faxvaag, A. Blockchain in healthcare and health sciences—A scoping review. Int. J. Med. Inform. 2020, 134, 104040. [Google Scholar] [CrossRef]
- Fernández-Caramés, T.M.; Fraga-Lamas, P. A Review on the Use of Blockchain for the Internet of Things. IEEE Access 2018, 6, 32979–33001. [Google Scholar] [CrossRef]
- Bonneau, J.; Miller, A.; Clark, J.; Narayanan, A.; Kroll, J.A.; Felten, E.W. SoK: Research Perspectives and Challenges for Bitcoin and Cryptocurrencies. In 2015 IEEE Symposium on Security and Privacy, San Jose, CA, USA, 17–21 May 2015; IEEE: Piscataway, NJ, USA, 2015; pp. 104–121. [Google Scholar] [CrossRef]
- Liu, J.; Liu, Z. A Survey on Security Verification of Blockchain Smart Contracts. IEEE Access 2019, 7, 77894–77904. [Google Scholar] [CrossRef]
- Nielsen, M.A.; Chuang, I.L. Quantum Computation and Quantum Information, 10th Anniversary ed.; Cambridge University Press: Cambridge, UK, 2010. [Google Scholar] [CrossRef]
- Chen, L.; Jordan, S.; Liu, Y.-K.; Moody, D.; Peralta, R.; Perlner, R.; Smith-Tone, D. Report on Post-Quantum Cryptography; NIST Internal Report (NISTIR) 8105; National Institute of Standards and Technology (NIST): Gaithersburg, MD, USA, 2016. [CrossRef]
- Shor, P.W. Polynomial-Time Algorithms for Prime Factorization and Discrete Logarithms on a Quantum Computer. SIAM J. Comput. 1997, 26, 1484–1509. [Google Scholar] [CrossRef]
- Pirandola, S.; Andersen, U.L.; Banchi, L.; Berta, M.; Bunandar, D.; Colbeck, R.; Englund, D.; Gehring, T.; Lupo, C.; Ottaviani, C.; et al. Advances in Quantum Cryptography. Adv. Opt. Photonics 2020, 12, 1012–1236. [Google Scholar] [CrossRef]
- Moody, D.; Perlner, R.; Regenscheid, A.; Robinson, A.; Cooper, D. Transition to Post-Quantum Cryptography Standards; NIST Internal Report (NISTIR) 8547 ipd, Initial Public Draft; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2024. [CrossRef]
- Aggarwal, D.; Brennen, G.; Lee, T.; Santha, M.; Tomamichel, M. Quantum Attacks on Bitcoin, and How to Protect Against Them. Ledger 2018, 3, 68–90. [Google Scholar] [CrossRef]
- Wehner, S.; Elkouss, D.; Hanson, R. Quantum Internet: A Vision for the Road Ahead. Science 2018, 362, eaam9288. [Google Scholar] [CrossRef]
- Wang, Y.; Ismail, E.S. A Review on the Advances, Applications, and Future Prospects of Post-Quantum Cryptography in Blockchain and IoT. IEEE Access 2025, 13, 112962–112977. [Google Scholar] [CrossRef]
- Chang, S.-Y.; Khan, Q. Post-Quantum Cryptography in Networking Protocols: Challenges, Solutions, and Future Directions. Cryptography 2026, 10, 12. [Google Scholar] [CrossRef]
- Thabet, M.; Tsili, A.; Krilakis, K.; Syvridis, D. Post-Quantum PKI: A Survey of Applications and Benchmarking Practices. Cryptography 2026, 10, 11. [Google Scholar] [CrossRef]
- Zong, C. Some Mathematical Problems Behind Lattice-Based Cryptography. Cryptography 2026, 10, 10. [Google Scholar] [CrossRef]
- Nutu, M.; Akhalaia, G.; Bocu, R.; Iavich, M. An Extended Survey Concerning the Vector Commitments. Appl. Sci. 2025, 15, 9510. [Google Scholar] [CrossRef]
- Buser, M.; Dowsley, R.; Esgin, M.F.; Gritti, C.; Kermanshahi, S.K.; Kuchta, V.; LeGrow, J.; Liu, J.; Phan, R.; Sakzad, A.; et al. A Survey on Exotic Signatures for Post-quantum Blockchain: Challenges and Research Directions. ACM Comput. Surv. 2023, 55, 251. [Google Scholar] [CrossRef]
- Sezer, B.B.; Akleylek, S.; Nuriyev, U. PP-PQB: Privacy-Preserving in Post-Quantum Blockchain-Based Systems: A Systematization of Knowledge. IEEE Access 2025, 13, 41382–41405. [Google Scholar] [CrossRef]
- Sabrina, F.; Sohail, S.; Tariq, U.U. A Review of Post-Quantum Privacy Preservation for IoMT Using Blockchain. Electronics 2024, 13, 2962. [Google Scholar] [CrossRef]
- Thanalakshmi, P.; Rishikhesh, A.; Marceline, J.M.; Joshi, G.P.; Cho, W. A Quantum-Resistant Blockchain System: A Comparative Analysis. Mathematics 2023, 11, 3947. [Google Scholar] [CrossRef]
- Ibrahim, H.; Ahakonye, L.A.C.; Lee, J.-M.; Kim, D.-S. Bibliometric Analysis of Secure IoT for Quantum Computing. Internet Things 2026, 36, 101872. [Google Scholar] [CrossRef]
- Bhatia, M.; Charul, K.M. Emerging security paradigms in IoT: A scientometric analysis of research trends and future prospects. Comput. Sci. Rev. 2026, 59, 100840. [Google Scholar] [CrossRef]
- Kumar, R.; Dutta, J.; Vamsi, N.; Varri, U.S.; Puthal, D. Next-Generation Security in the 6G Era: The Role of AI in Safeguarding Future Networks. IEEE Access 2026, 14, 17347–17380. [Google Scholar] [CrossRef]
- Eren, H.; Karaduman, Ö.; Gençoğlu, M.T. Security and Privacy in the Internet of Everything (IoE): A Review on Blockchain, Edge Computing, AI, and Quantum-Resilient Solutions. Appl. Sci. 2025, 15, 8704. [Google Scholar] [CrossRef]
- Scalise, P.; Boeding, M.; Hempel, M.; Sharif, H.; Delloiacovo, J.; Reed, J. A Systematic Survey on 5G and 6G Security Considerations, Challenges, Trends, and Research Areas. Future Internet 2024, 16, 67. [Google Scholar] [CrossRef]
- Naik, A.S.; Yeniaras, E.; Hellstern, G.; Prasad, G.; Vishwakarma, S.K.L.P. From portfolio optimization to quantum blockchain and security: A systematic review of quantum computing in finance. Financ. Innov. 2025, 11, 88. [Google Scholar] [CrossRef]
- Kundu, S.; Gupta, T.; Sardar, A.; Bandyopadhyay, A.; Swain, S.; Mallik, S. A survey on quantum computing: Transforming cryptography, AI/ML, blockchain, and network communication. Frankl. Open 2025, 12, 100371. [Google Scholar] [CrossRef]
- Nguyen, V.-L.; Lin, P.-C.; Cheng, B.-C.; Hwang, R.-H.; Lin, Y.-D. Security and Privacy for 6G: A Survey on Prospective Technologies and Challenges. IEEE Commun. Surv. Tutor. 2021, 23, 2384–2428. [Google Scholar] [CrossRef]
- Porambage, P.; Gür, G.; Moya Osorio, D.P.; Liyanage, M.; Gurtov, A.; Ylianttila, M. The Roadmap to 6G Security and Privacy. IEEE Open J. Commun. Soc. 2021, 2, 1094–1122. [Google Scholar] [CrossRef]
- Kiktenko, E.O.; Pozhar, N.O.; Anufriev, M.N.; Trushechkin, A.S.; Yunusov, R.R.; Kurochkin, Y.V.; Lvovsky, A.I.; Fedorov, A.K. Quantum-secured blockchain. Quantum Sci. Technol. 2018, 3, 035004. [Google Scholar] [CrossRef]
- Gao, Y.-L.; Chen, X.-B.; Chen, Y.-L.; Sun, Y.; Niu, X.-X.; Yang, Y.-X. A Secure Cryptocurrency Scheme Based on Post-Quantum Blockchain. IEEE Access 2018, 6, 27205–27213. [Google Scholar] [CrossRef]
- Gill, S.S.; Wu, H.; Patros, P.; Ottaviani, C.; Arora, P.; Casamayor Pujol, V.; Haunschild, D.; Parlikad, A.K.; Cetinkaya, O.; Lutfiyya, H.; et al. Modern computing: Vision and challenges. Telemat. Inform. Rep. 2024, 13, 100116. [Google Scholar] [CrossRef]
- Castiglione, A.; Esposito, J.G.; Loia, V.; Nappi, M.; Pero, C.; Polsinelli, M. Integrating Post-Quantum Cryptography and Blockchain to Secure Low-Cost IoT Devices. IEEE Trans. Ind. Inform. 2025, 21, 1674–1683. [Google Scholar] [CrossRef]
- Chengoden, R.; Victor, N.; Huynh-The, T.; Yenduri, G.; Jhaveri, R.H.; Alazab, M.; Bhattacharya, S.; Hegde, P.; Maddikunta, P.K.R.; Gadekallu, T.R. Metaverse for Healthcare: A Survey on Potential Applications, Challenges and Future Directions. IEEE Access 2023, 11, 12765–12795. [Google Scholar] [CrossRef]
- Ajani, S.N.; Khobragade, P.; Dhone, M.; Ganguly, B.; Shelke, N.; Parati, N. Advancements in Computing: Emerging Trends in Computational Science with Next-Generation Computing. Int. J. Intell. Syst. Appl. Eng. 2024, 12, 546–559. [Google Scholar]
- Cheung, K.-F.; Bell, M.G.H.; Bhattacharjya, J. Cybersecurity in logistics and supply chain management: An overview and future research directions. Transp. Res. Part E Logist. Transp. Rev. 2021, 146, 102217. [Google Scholar] [CrossRef]
- Zhu, Q.; Loke, S.W.; Trujillo-Rasua, R.; Jiang, F.; Xiang, Y. Applications of Distributed Ledger Technologies to the Internet of Things: A Survey. ACM Comput. Surv. 2020, 52, 120. [Google Scholar] [CrossRef]
- Walia, G.K.; Kumar, M.; Gill, S.S. AI-Empowered Fog/Edge Resource Management for IoT Applications: A Comprehensive Review, Research Challenges, and Future Perspectives. IEEE Commun. Surv. Tutor. 2024, 26, 619–669. [Google Scholar] [CrossRef]
- Jurcut, A.; Niculcea, T.; Ranaweera, P.; Le-Khac, N.-A. Security Considerations for Internet of Things: A Survey. SN Comput. Sci. 2020, 1, 193. [Google Scholar] [CrossRef]


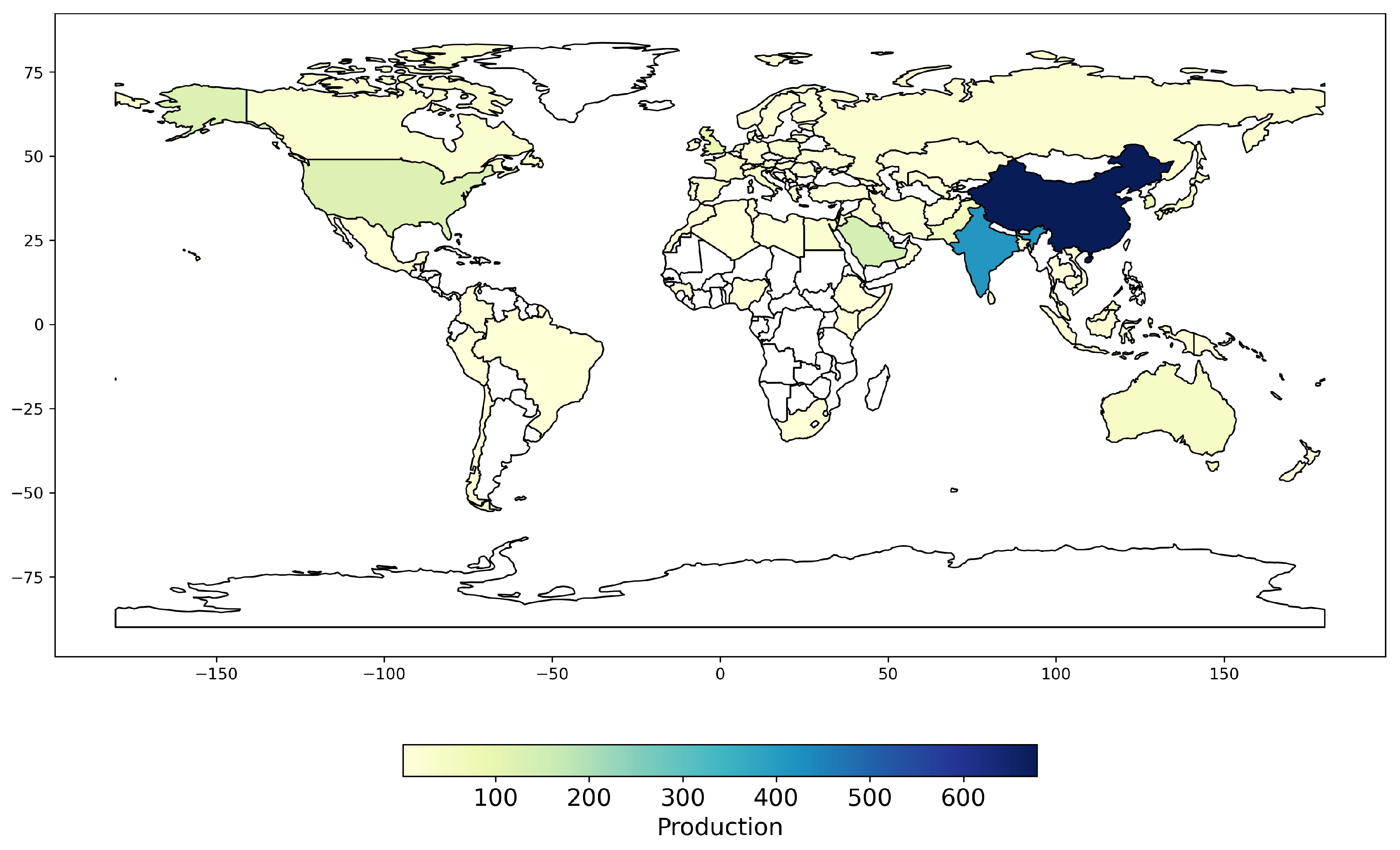




| Country | Publications | Publications (%) | SCP | SCP (%) | MCP | MCP (%) |
|---|---|---|---|---|---|---|
| China | 178 | 27.5% | 144 | 80.9% | 34 | 19.1% |
| India | 144 | 22.2% | 102 | 70.8% | 42 | 29.2% |
| Saudi Arabia | 34 | 5.2% | 21 | 61.8% | 13 | 38.2% |
| Korea | 33 | 5.1% | 21 | 63.6% | 12 | 36.4% |
| United States | 27 | 4.2% | 20 | 74.1% | 7 | 25.9% |
| United Kingdom | 21 | 3.2% | 10 | 47.6% | 11 | 52.4% |
| Australia | 16 | 2.5% | 15 | 93.8% | 1 | 6.3% |
| Pakistan | 13 | 2.0% | 6 | 46.2% | 7 | 53.8% |
| Italy | 10 | 1.5% | 9 | 90.0% | 1 | 10.0% |
| Canada | 9 | 1.4% | 7 | 77.8% | 2 | 22.2% |
| Iraq | 9 | 1.4% | 7 | 77.8% | 2 | 22.2% |
| Japan | 8 | 1.2% | 4 | 50.0% | 4 | 50.0% |
| Malaysia | 7 | 1.1% | 2 | 28.6% | 5 | 71.4% |
| Spain | 7 | 1.1% | 4 | 57.1% | 3 | 42.9% |
| Iran | 6 | 0.9% | 6 | 100.0% | 0 | 0.0% |
| Poland | 6 | 0.9% | 5 | 83.3% | 1 | 16.7% |
| Ireland | 5 | 0.8% | 2 | 40.0% | 3 | 60.0% |
| Morocco | 5 | 0.8 % | 5 | 100.0% | 0 | 0.0% |
| Kazakhstan | 4 | 0.6% | 3 | 75.0% | 1 | 25.0% |
| Russia | 4 | 0.6% | 3 | 75.0% | 1 | 25.0% |
| United Arab Emirates | 4 | 0.6% | 0 | 0.0% | 4 | 100.0% |
| Egypt | 3 | 0.5% | 2 | 66.7% | 1 | 33.3% |
| France | 3 | 0.5% | 2 | 66.7% | 1 | 33.3% |
| Germany | 3 | 0.5% | 1 | 33.3% | 2 | 66.7% |
| Indonesia | 3 | 0.5% | 2 | 66.7% | 1 | 33.3% |
| Jordan | 3 | 0.5% | 1 | 33.3% | 2 | 66.7% |
| Portugal | 3 | 0.5% | 3 | 100.0% | 0 | 0.0% |
| Affiliation(s) | Articles/Affiliation |
|---|---|
| Beihang University, Beijing University Posts and Telecommunications | 38 |
| King Saud University | 24 |
| International Institute of Information Technology | 21 |
| Xi’an University Posts and Telecommunications, Zhengzhou University of Light Industry | 19 |
| Beijing Electronic Science and Technology Institute | 16 |
| Majmaah University, University of Salerno | 13 |
| Guizhou University, North China University of Technology, School of Artificial Intelligence, Shanghai Jiao Tong University | 12 |
| Central University of Himachal Pradesh, Korea University, North China Electric Power University | 11 |
| Deakin University, Guangzhou University, The Hong Kong Polytechnic University, National Institute of Technology, Seoul National University of Science and Technology, Shenzhen University | 10 |
| Amrita School of Computing, Kyungpook National University, Manipal University Jaipur, National Institute of Technology Hamirpur, University of Oxford | 9 |
| Chongqing University Posts and Telecommunications, Ege University, King Faisal University, Kumoh National Institute of Technology, Lovely Professional University, Muroran Institute of Technology, Nanjing University of Information Science and Technology, School of Cyberspace Science and Technology, University of Sfax | 8 |
| Communication University of China, Feng Chia University, Prince Sattam bin Abdulaziz University, Qufu Normal University, SRM Institute of Science and Technology, Sun Yat-sen University, Texas A&M University, Thapar Institute of Engineering and Technology, University of Tabuk, University of Tartu, University of Warsaw, Xidian University | 7 |
| Source(s) | Articles/Journal |
|---|---|
| IEEE Access (Q1) | 44 |
| IEEE Internet of Things Journal (Q1) | 18 |
| Scientific Reports (Q1) | 17 |
| IEEE Transactions on Consumer Electronics (Q1) | 16 |
| CMC-Computers, Materials & Continua (Q2) | 15 |
| Computers & Electrical Engineering (Q1), Quantum Information Processing (Q1) | 13 |
| Sensors (Q1) | 12 |
| Applied Sciences (Switzerland) (Q2), IEEE Transactions on Intelligent Transportation Systems (Q1) | 10 |
| Cryptography (Q2) | 9 |
| Entropy (Q2), Internet of Things (Q1), Journal of Information Security and Applications (Q1), Security and Communication Networks (Q2; discontinued) | 8 |
| Cluster Computing (Q1), Computer Networks (Q1), IEEE Transactions on Information Forensics and Security (Q1), Information Sciences (Q1), The Journal of Supercomputing (Q2) | 7 |
| IEEE Communications Surveys & Tutorials (Q1), IEEE Transactions on Dependable and Secure Computing (Q1), IEEE Transactions on Network Science and Engineering (Q1), Journal of Discrete Mathematical Sciences and Cryptography (Q3), Mathematics (Q2), SN Computer Science (Q2) | 6 |
| Concurrency and Computation: Practice & Experience (Q2), IEEE Open Journal of the Communications Society (Q1), International Journal of Advanced Computer Science and Applications (Q3), Peer-to-Peer Networking and Applications (Q2) | 5 |
| Signature Family | Representative Scheme | Public Key Size (Bytes) | Signature Size (Bytes) | Typical Magnitude for Blockchain Integration | Expected Ledger-Level Impact | Evidence Status in the Reviewed Literature |
|---|---|---|---|---|---|---|
| Classical baseline | Ed25519 | 32 | 64 | Byte-scale footprint; practical baseline for interpreting post-quantum overhead. | Minimal per-transaction footprint; limited pressure on block occupancy, propagation bandwidth, and long-term ledger growth. | Contextual classical benchmark included for scale comparison. |
| Lattice-based PQ signatures | CRYSTALS-Dilithium-5 | 2592 | 4595 | Few-kilobyte public key and signature; substantially larger than classical baselines but still within a comparatively moderate post-quantum range. | Clear transaction-footprint inflation; fewer transactions per block, higher propagation overhead, and stronger storage pressure, especially in constrained IoT or long-lived blockchain deployments. | Directly reported in the implementation-oriented corpus and explicitly discussed as a scalability concern in blockchain-enabled IoT settings [40]. |
| Stateless hash-based PQ signatures | SPHINCS+/ SLH-DSA | 32–64 | 7856–49,856 | Small public key but very large signature output; signature-dominated overhead regime. | Strongest block-space and bandwidth pressure among the representative rows; likely substantial transaction inflation and long-term ledger growth penalties in high-volume chains. | Contextual stateless-hash benchmark included for cross-family comparison; useful for interpreting trade-offs between statelessness and ledger footprint. |
| Threat Category | Typical Blockchain Layer Affected | Migration Implication |
|---|---|---|
| Retrospective confidentiality risks to long-lived protected data | Off-chain data ecosystem, access-control and credential layers, key-establishment interfaces, and blockchain-supported trust architectures in long-horizon application contexts. | Prioritize earlier migration in contexts where secrecy duration matters, even if immediate transaction forgery is not yet the dominant operational concern. |
| Active signature and authorization risks in live blockchain operation | Transaction-signing layer, key management, account control, and user- or device-level authorization mechanisms. | Prioritize post-quantum signatures and related identity mechanisms where failure would directly compromise transaction validity, state-transition correctness, or asset control. |
| Consensus- and control-plane risks | Consensus, mining or validation logic, node authentication, message-authentication workflows, and communication-trust substrate. | Prioritize protocol-level redesign where needed, including stronger authentication assumptions, revised hash-security margins, and, in selected permissioned settings, specialized mechanisms such as QKD-supported authentication. |
| Reporting Dimension | Minimum Information to Report | Why It Matters |
|---|---|---|
| Threat model and blockchain context | Blockchain type (public, permissioned, or hybrid), affected layer (e.g., transaction signing, consensus, smart contracts, control plane, off-chain trust layer), exposure type (retrospective confidentiality, active authorization/integrity, or consensus/control-plane), and assumed adversarial capabilities (e.g., Shor-type, Grover-type, side-channel, fault injection). | Makes security claims interpretable and allows readers to determine which blockchain layer and threat timing the evaluation actually addresses. |
| PQC mechanism and parameterization | Exact scheme name, cryptographic family, parameter set, security level, hybrid composition if applicable, and sizes of public key, private key, signature, ciphertext, or other relevant cryptographic artifacts. | Prevents vague references to “post-quantum” mechanisms and enables technically meaningful comparison across studies. |
| Implementation environment | Hardware platform, processor class, memory profile, operating system or firmware environment, software stack, compiler settings, cryptographic library or codebase version, and number of nodes if a distributed experiment is involved. | Establishes the execution context needed to reproduce performance results and interpret feasibility claims. |
| Blockchain and workload configuration | Consensus mechanism, block size or equivalent capacity constraint, transaction format, workload type, transaction rate, benchmark duration, validation setting, network topology, and whether results derive from simulation, emulation, testbed, or deployed prototype. | Ensures that ledger-level effects are not interpreted in isolation from the operational conditions that generate them. |
| Ledger-level performance metrics | Transaction footprint, block occupancy or block-space usage, throughput, end-to-end latency or finality latency, propagation overhead, and storage growth over time. | Translates cryptographic design choices into system-level blockchain costs, which are central to deployment viability. |
| Cryptographic execution metrics | Key generation time, signing time, verification time, encapsulation or decapsulation time if applicable, and any batching or aggregation behavior used in the evaluation. | Allows assessment of whether the proposed mechanism is viable for the intended application layer and workload profile. |
| Resource and energy metrics | CPU utilization, memory consumption, communication overhead, and energy consumption or power profile, especially for constrained IoT, edge, or embedded environments. | Clarifies whether a scheme is practical under resource-constrained deployment conditions rather than only in abstract security terms. |
| Security-relevant implementation details | Countermeasures against side-channel or fault attacks if applicable, key-management assumptions, authentication assumptions between nodes, hash-security margins, and observed scalability or failure limits. | Makes implementation security explicit and prevents system claims from relying on hidden or unrealistic assumptions. |
| Reproducibility artifacts | Availability of code, scripts, configuration files, datasets or benchmark workloads, measurement procedure, random seeds when relevant, and sufficient documentation to reconstruct the experiment. | Enables independent verification and turns isolated demonstrations into reusable evidence for cumulative research. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.
Share and Cite
Díaz, F.; Cerna, N.; Liza, R.; Motta, B. Quantum-Safe Blockchain: Mapping Research Fronts in Post-Quantum Cryptography, Quantum Threat Models, and QKD Integration. Computers 2026, 15, 240. https://doi.org/10.3390/computers15040240
Díaz F, Cerna N, Liza R, Motta B. Quantum-Safe Blockchain: Mapping Research Fronts in Post-Quantum Cryptography, Quantum Threat Models, and QKD Integration. Computers. 2026; 15(4):240. https://doi.org/10.3390/computers15040240
Chicago/Turabian StyleDíaz, Félix, Nhell Cerna, Rafael Liza, and Bryan Motta. 2026. "Quantum-Safe Blockchain: Mapping Research Fronts in Post-Quantum Cryptography, Quantum Threat Models, and QKD Integration" Computers 15, no. 4: 240. https://doi.org/10.3390/computers15040240
APA StyleDíaz, F., Cerna, N., Liza, R., & Motta, B. (2026). Quantum-Safe Blockchain: Mapping Research Fronts in Post-Quantum Cryptography, Quantum Threat Models, and QKD Integration. Computers, 15(4), 240. https://doi.org/10.3390/computers15040240









