A Methodology for Generating Systems Architectural Glimpse Statements Using the 5W1H Maxim
Abstract
:1. Introduction and Problem Statement
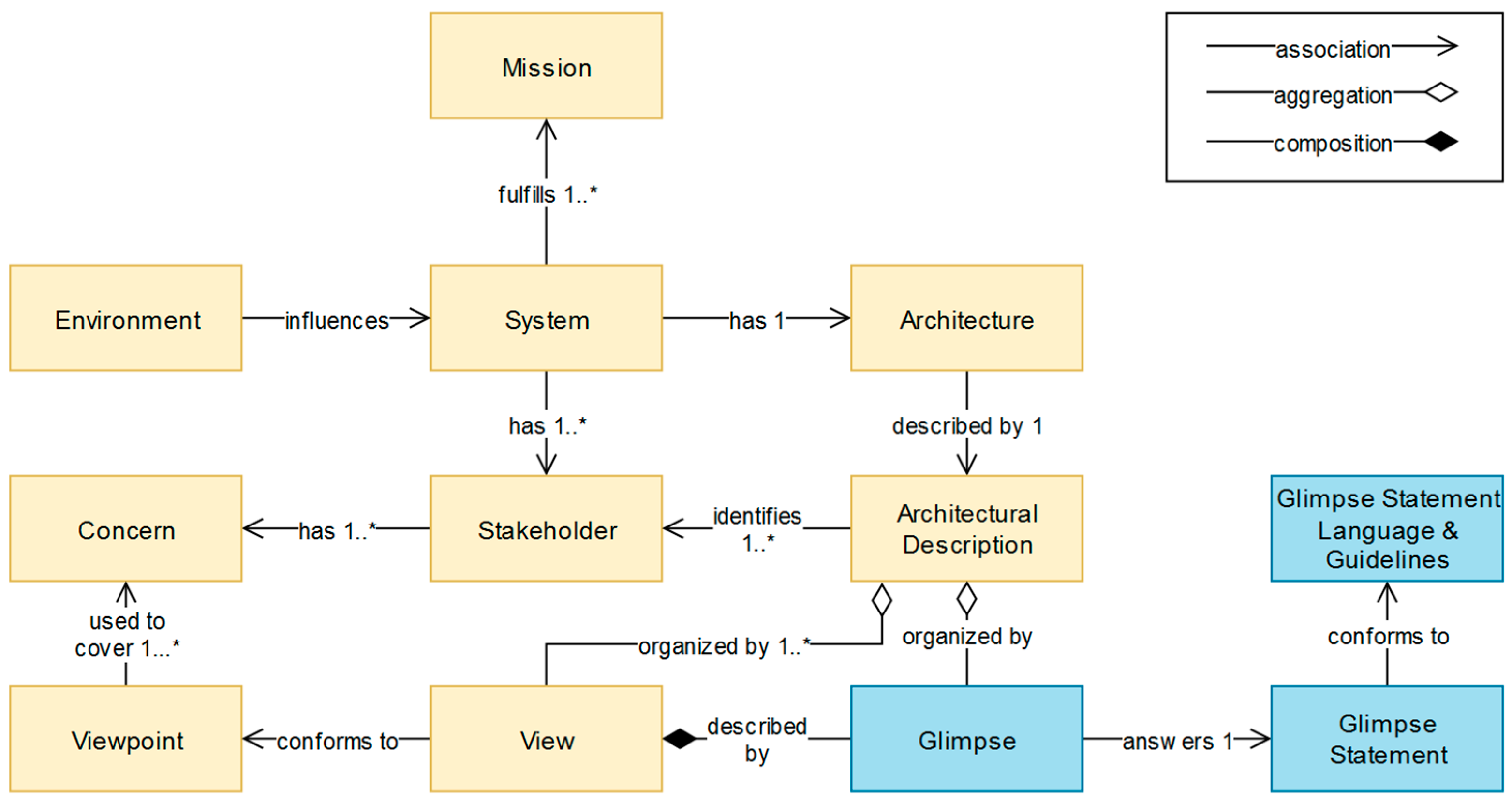
1.1. Systems Architecture and Architecting
1.2. Motivation, Contributions, and Paper Structure
2. Related Work: Architectural Views and Other Approaches
- Architectural design methodology: “Systematic approach to creating an architectural design consisting of the ordered application of a specific collection of tools, techniques, and guidelines”.
- Architectural style: “Definition of a family of systems in terms of a pattern of structural organization”. Depending on the styles used, an architecture may be layered, component-based, (micro-) service-oriented, function-oriented, object-oriented, data-centric, event-driven, rule-based, etc.
- Architecture framework (AF): A reusable architectural design (models and/or code) that can be refined (specialized) and extended to provide some portion of the overall functionality of many applications. A framework is usually implemented in terms of one or more viewpoints or architecture description languages.”
- Architectural model: “A semantically closed abstraction of a system or a complete description of a system from a particular perspective.”
- Architectural views: “A representation of a whole system from the perspective of a related set of concerns.”
- Architecture description language (ADL): “Any means of expression used to describe a software architecture.”
3. Architectural Glimpses
4. Glimpse Statements Language (GSL)
4.1. Context: Asking the Right Questions (5W1H Maxim)
- What: It identifies the main entity of interest that can act as a subject in a glimpse statement (see Section 4.2 and Section 4.3 for further elaboration).
- Who: It addresses concepts such as “role”, “actor”, “stakeholder”, or “beneficiary”.
- Where: It addresses concepts related to physical or conceptual “location”.
- When: It addresses concepts related to “time” (duration, sequence, etc.).
- Why: It addresses concepts related to “purpose”, “goals”, etc.
- How: It addresses concepts related to “processes”, implementation of “activities”, ways of conduct, etc.
4.2. Vocabulary: Entities of Interest and Verbs
- Criterion 1: aggregate terms from several systems engineering domains, in order to provide a holistic view of all the corresponding related concepts and avoid focusing on terms that are too domain- or application-specific.
- Criterion 2: use as sources standards, in order to support standardization activities and ensure “interoperability” of the produced vocabulary with other initiatives.
- Criterion 3: have an extensive number of terms and, ideally, the meanings of the terms, in order to make it possible to work on a big pool of terms.
- Criterion 4: have a public dissemination level, in order to make it possible for the authors of this article to easily access the said sources on the one hand, and, on other hand, to freely republish content from the sources.
4.3. Semantics: Relations between and Groups of Entity Types and Verbs
- Synonymy: Synonyms are words that are pronounced/spelled differently but contain the same meaning (e.g., buyer—customer).
- Relational Antonymy: A pair of words that refer to a relationship from opposite points of view (e.g., supplier—consumer).
- Graded Antonymy: A pair of words that denotes one end of a scale while the other term denotes the other end (e.g., centralized-decentralized).
- Complementary Antonymy: A pair of words wherein affirmative use of one entails the negative of the other with no gradability (e.g., installed—uninstalled).
- Holonymy and meronymy. A meronym is in a part-of relationship with its holonym (e.g., a “task” includes “activities”).
4.4. Syntax: Asking Questions the Right Way
- Rule 2: Each glimpse statement has to include a “What” phrase and a Verb phrase (in that order), and may include one or more “Who”, “Where”, “When”, “Why”, and “How” phrases (their order being irrelevant). If more than one phrases (Who, Where, When, Why, How) of the same type (e.g., two different “Where” phrases) appear, they should be grouped together and not have phrases of a different type in between them.
- Rule 3: A What phrase consists of the interrogative word “What” and the plural (if it exists) of a What entity type. For example: “What requirements”, “What functional user requirements”, “What equipment”, etc.
- Rule 4: A Verb phrase consists of one transitive passive verb (as in Table 1) preceded by a passive auxiliary verb. For example: “have to be developed”, “can be tested”, “were transferred”, etc.
- Rule 5: The rest of the phrases have to include a preposition, followed by the word “what” and an entity type (most of the times, different from that of the What phrase). For example: “by what process” (how), “due to what requirement” (why), “from what stakeholder” (who), “with what order” (when), “at what building” (where).
- “… where?” (Approach 1)
- “… to devices?” (Approach 2)
- “… to what devices?” (Approach 3)
- “… to device with ID XYZ.123?” (Approach 4)
5. Glimpse Statements and Glimpses: Creation Guidelines
5.1. Glimpse Statements Generator
- Step 1: Populate the generator with entity types and verbs of interest either by choosing words from Table 1 and Table 2, by identifying them intuitively or by following the methodology in Section 4.2.
- Step 2: From the first column (“What” phrase column) select the entity type for which a glimpse statement has to be generated.
- Step 3: From the third column, select the verb that expresses the action of interest that is performed on the chosen “What” entity type.
- Step 4: From the second column, choose the auxiliary verb that adds the desired context to the statement.
- Step 5: Create a fundamental glimpse statement by writing the question “What [selected entity type (plural)] [selected auxiliary verb] [selected verb]”.
- Step 6: Decide whether you want to make the statement more complex by adding (another/) a “Who” phrase. If the answer is yes, move to Step 7. If the answer is no, move to Step 11.
- Step 7: From the fourth column, select the preposition that you deem it adds appropriate context to the statement.
- Step 8: Based on the chosen preposition in Step 7, select an appropriate “Who” entity type in the fifth column.
- Step 9: Create a “Who” phrase in the form of “[selected preposition] what [selected entity type (plural)]” and add it to the formed glimpse statement.
- Step 10: Go back to Step 6.
- Step 11: Decide whether you want to make the statement more complex by adding (another) a “When” phrase. If the answer is yes, repeat Step 7 to 10 in the context of a “When” phrase. If the answer is no, repeat this step for all the remaining types of 5W1H phrases, until there are no extra phrases to add to the glimpse statement.
- Step 12: Go back to Step 4 and repeat all Steps from 5 to 11. Then go to Step 13.
- Step 13: Go back to Step 3 and repeat all Steps from 4 to 12. Then go to Step 14.
- Step 14: Go back to Step 2 and repeat all Steps from 3 to 13, until there are no “What” entity types of interest left.
5.2. Glimpses Creation Guidelines
- Step 1: [Optional] Choose a view or perspective that you want to address.
- Step 2: Populate the glimpse statements generator (Table 3) with the corresponding words deemed sufficient to produce useful and complex statements.
- Step 3: Follow the methodology introduced in Section 5.1 and produce all the necessary glimpse statements.
- Step 4: Identify the appropriate techniques, methods, means that could be used to instantiate the glimpses based on the glimpse statements.
- Step 5: Identify which glimpses could be combined to produce richer and more complex architectural artifacts.
- Step 6: Identify a schedule/sequence for the actual production of glimpses, keeping in mind that architecture activities are performed iteratively and at different stages of the initial software development life-cycle, as well as over the evolution of a system.
- Step 7: Give answers to glimpse statements by replacing the Entity Types with the corresponding Entities.
- Step 8: Produce the corresponding products (visualizing/describing glimpses) based on the outcomes of Steps 7 (What), 6 (When) and 5 (How).
- Step 9: [Optional/If Step 1 was skipped]: Group the glimpses/final products in architectural views.
6. Glimpse Statements and Glimpses Examples in Case Studies
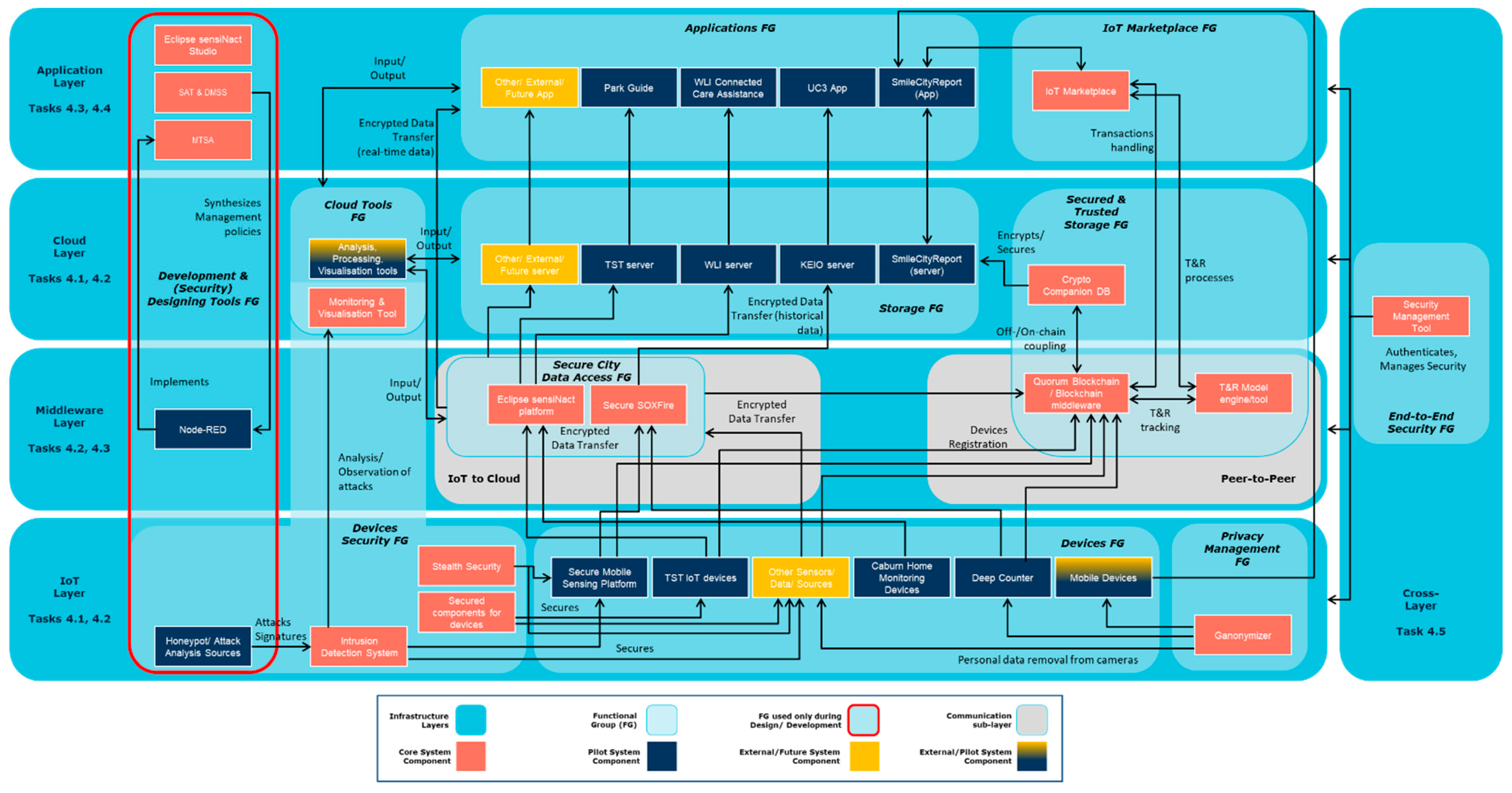
6.1. M-Sec Case Study: A Bottom-Up Approach
6.2. C4ISR Case Study: Compatibility with Other Architectures
7. Discussion and Future Work
8. Conclusions
Supplementary Materials
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- IEEE. Recommended Practice for Architectural Description for Software-Intensive Systems; IEEE Std. 1471-2000; IEEE: New York, NY, USA, 2000; pp. 1–30. [Google Scholar] [CrossRef]
- ISO; IEC; IEEE. International Standard—Systems and Software Engineering—Vocabulary; ISO/IEC/IEEE 24765:2017(E); IEEE: New York, NY, USA, 2017; pp. 1–541. [Google Scholar] [CrossRef]
- Hofmeister, C.; Kruchten, P.; Nord, R.L.; Obbink, H.; Ran, A.; America, P. A general model of software architecture design derived from five industrial approaches. J. Syst. Softw. 2007, 80, 106–126. [Google Scholar] [CrossRef]
- Rechtin, E. The art of systems architecting. IEEE Spectr. 1992, 29, 66–69. [Google Scholar] [CrossRef]
- Percivall, G.; Taylor, T. Connecting the Internet of Things to the eo community and the geospatially enabled web using OGC standards. In Proceedings of the 2017 IEEE International Geoscience and Remote Sensing Symposium (IGARSS), Fort Worth, TX, USA, 23–28 July 2017; pp. 5577–5580. [Google Scholar] [CrossRef]
- ISO; IEC; IEEE. International Standard—Software, Systems and Enterprise—Architecture Processes; ISO/IEC/IEEE 42020:2019(E); IEEE: New York, NY, USA, 2019; pp. 1–126. [Google Scholar] [CrossRef]
- Hilliard, R.; Malavolta, I.; Muccini, H.; Pelliccione, P. On the Composition and Reuse of Viewpoints across Architecture Frameworks. In Proceedings of the 2012 Joint Working IEEE/IFIP Conference on Software Architecture and European Conference on Software Architecture, Helsinki, Finland, 20–24 August 2012; pp. 131–140. [Google Scholar] [CrossRef] [Green Version]
- Marca, D.; McGowan, C. Structured Analysis and Design Technique; McGraw-Hill: New York, NY, USA, 1987; ISBN 0-07-040235-3. [Google Scholar]
- IEEE. Standard for Functional Modeling Language—Syntax and Semantics for IDEF0.2.1.60; IEEE Standard 1320.1-1998 (R2004); IEEE: New York, NY, USA, 1998. [Google Scholar]
- IEEE. Standard for an Architectural Framework for the Internet of Things (IoT); IEEE Std 2413-2019; IEEE: New York, NY, USA, 2020; pp. 1–269. [Google Scholar] [CrossRef]
- Reuter, A.; Andrikopoulos, V. Architectures of Cloud-enabled Cyber Physical Systems—A Systematic Mapping Study. In Proceedings of the 46th Euromicro Conference on Software Engineering and Advanced Applications (SEAA), Portoroz, Slovenia, 26–28 August 2020; pp. 455–462. [Google Scholar] [CrossRef]
- Oquendo, F. Formally Describing the Architectural Behavior of Software-Intensive Systems-of-Systems with SosADL. In Proceedings of the 21st International Conference on Engineering of Complex Computer Systems (ICECCS), Dubai, United Arab Emirates, 6–8 November 2016; pp. 13–22. [Google Scholar] [CrossRef]
- Cavalcante, E.; Batista, T.; Oquendo, F. Supporting Dynamic Software Architectures: From Architectural Description to Implementation. In Proceedings of the 12th Working IEEE/IFIP Conference on Software Architecture, Montreal, QC, Canada, 4–8 May 2015; pp. 31–40. [Google Scholar] [CrossRef]
- IEEE; ISO; IEC. Draft International Standard for Systems and Software Engineering—Architecture Description; ISO/IEC/IEEE P42010/DIS; IEEE: New York, NY, USA, 2020; pp. 1–68. [Google Scholar]
- Kruchten, P.B. The 4+1 View Model of architecture. IEEE Softw. 1995, 12, 42–50. [Google Scholar] [CrossRef] [Green Version]
- ISO/IEC DIS 10746-3. Basic Reference Model of Open Distributed Processing—Part 3: Prescriptive Model; ISO: Geneva, Switzerland, 1994. [Google Scholar]
- C4ISR Architecture Working Group. C4ISR Architecture Framework Version 2.0.; U.S. Department of Defense: Washington, DC, USA, 1997.
- Bauer, M.; Boussard, M.; Bui, N.; Carrez, F.; Jardak, C.; De-Loof, J.; Magerkurth, C.; Meissner, S.; Nettstraeter, A.; Olivereau, A.; et al. Internet of Things—Architecture IoT-A Deliverable D1.5—Final Architectural Reference Model for the IoT v3.0.; European Commission: Brussels, Belgium, 2013. [Google Scholar]
- Shames, P.; Skipper, J. Toward a Framework for Modeling Space Systems Architectures. In Proceedings of the SpaceOps 2006 Conference, Rome, Italy, 19–23 June 2015. [Google Scholar] [CrossRef] [Green Version]
- Woods, E. Operational: The Forgotten Architectural View. IEEE Softw. 2016, 33, 20–23. [Google Scholar] [CrossRef]
- Object Management Group, Inc. OMG Unified Modeling Language™. Version 2.5. March 2015. Available online: http://www.omg.org/spec/UML/2.5 (accessed on 20 August 2021).
- Jeong-Dong, K.; Jiseong, S.; Doo-Kwon, B. CA5W1H onto: Ontological Context-Aware Model Based on 5W1H. Int. J. Distrib. Sens. Netw. 2012, 2012, 247346. [Google Scholar] [CrossRef]
- ISO; IEC; IEEE. International Standard—Systems and Software Engineering—Vocabulary; ISO/IEC/IEEE 24765:2010(E); IEEE: New York, NY, USA, 2010; pp. 1–418. [Google Scholar] [CrossRef]
- SEVOCAB: Software and Systems Engineering Vocabulary. Available online: www.computer.org/sevocab (accessed on 28 August 2021).
- Fromkin, V.; Victoria, R. Introduction to Language, 6th ed.; Harcourt Brace College Publishers: Fort Worth, TX, USA, 1998; ISBN 978-0-03-018682-0. [Google Scholar]
- M-Sec. Available online: https://www.msecproject.eu/ (accessed on 30 August 2021).
| What | Verb |
|---|---|
| fact, data, information, knowledge, file | abstracted, defined, designed, specified, formulated |
| input, output | mapped, categorized, classified |
| service, function, functionality, capability | acquired, bought, purchased, consumed, supplied |
| activity, task, action, operation, procedure, process | produced, developed, created, constructed |
| product, result, application | owned, outsourced, delegated, (re)used, adopted |
| document, deliverable | modified, enhanced, refined, adapted |
| component, module, unit, subsystem, system | collected, aggregated, combined |
| algorithm, program, code, S/W | delivered, documented, inquired, notified |
| computer, H/W, device, equipment, machine | read, written, deleted, edited, changed |
| sector, domain, industry | transferred, communicated, accessed, retrieved |
| environment, problem, scenario, use case | searched, discovered |
| technology, protocol | managed, maintained |
| asset, resource, artifact | (un)installed, configured, deployed |
| supply, commodity, material, consumable | processed, analyzed, transformed |
| instrument, tool, facility, building | stored, saved, encapsulated |
| budget, fund | performed, executed, invoked, called |
| element, entity, object, Thing, artifact | tested, emulated, demonstrated |
| criterion, class, type, dimension, category | verified, checked, evaluated |
| attribute, characteristic | presented, represented, visualized |
| association, relation, interaction, flow, group | digitalized, virtualized, automated |
| constraint, restriction, limitation | protected, secured |
| interface, node, level, layer | considered, faced, mitigated, constrained, limited |
| error, fault, failure, risk, threat | distributed, centralized |
| event, contingency, condition, probability | (de)modularized, connected, integrated |
| agreement, decision | detected, monitored, predicted, forecasted, modeled |
| Who | Where | When | Why | How |
|---|---|---|---|---|
| role | location, place | time, date | requirement, need | action |
| team, organization | space | duration | objective, goal | procedure, process |
| individual, human | address | timing, schedule | mission, vision | rule |
| actor, stakeholder | layer, level, node | period | Rationale | standard |
| acquirer, supplier | device, machine | phase | strategy, plan | constraint, condition |
| buyer, customer | building, facility | event, contingency | condition, constraint | instruction, plan |
| owner | construct | scenario, use case | restriction, prohibition | cost, quality |
| user, consumer | priority | rule, law | ||
| agent, delegate | order, sequence | policy | ||
| analyst, architect | concurrence | |||
| expert, engineer | synchronicity |
| What Phrase | Verb Phrase | Who Phrase | ||
|---|---|---|---|---|
| What Entity Type | Auxiliary Verb. | Verb | Preposition | Who Entity Type |
| functional components | have to be | collected | by | Organizations |
| functional requirements | must be | extracted | from | Users |
| health data | have been | developed | to | Individuals |
| environmental device | shall be | transferred | for | Stakeholders |
| Indicative Glimpses Instantiation/Representation Tools |
|---|
| block diagram, configuration diagram, system resources chart, bubble chart, flowchart, graph, input-process-output chart, structure chart, box diagram, control flow diagram, Chapin chart, Nassi-Shneiderman chart, program structure diagram, call graph, call tree, tier chart, context diagram, decomposition diagram, entity-relationship (E-R) diagram, entity-relationship map, data structure diagram, flowchart, flow diagram, Gantt chart, Petri Net graph, influence diagram, organizational breakdown structure, state diagram, timing diagram, use case diagram, use case model |
| What | Verb | Where | When | How |
|---|---|---|---|---|
| What components | have been developed | through what tasks | ||
| What integration points | have been materialized | between what components | through what means | |
| What components | have been used | on what layers | at what project phases | |
| What components | can be reused | in what external projects | at what project phases | with what infrastructure |
| What components | are interconnected | at what project phases | through what functional groups | |
| What types of data | are transferred | from what components to what components | through what integration points |
| Code | Product Name | Description |
|---|---|---|
| SV-1 | System Interface Description | Identification of systems and system components and their interfaces, within and between nodes |
| SV-2 | Systems Communication Description | Physical nodes and their related communications laydowns |
| SV-4 | Systems Functionality Description | Functions performed by systems and the information flow among system functions |
| SV-5 | Operational Activity to System Function Traceability Matrix | Mapping of system functions back to operational activities |
| SV-6 | System Information Exchange Matrix | Detailing of information exchanges among system elements, applications and H/W allocated to system elements |
| SV-10b | Systems State Transition Description | Systems activity sequence and timing—responses of a system to events |
| Code | Glimpse Statement |
|---|---|
| SV-1 | • What systems are exposed, within what nodes, between what nodes, through what interfaces? • What system components are exposed, within what nodes, between what nodes, through what interfaces? |
| SV-2 | • What communication laydowns are deployed, in what physical nodes? |
| SV-4 | • What functions are performed, by what systems? • What information is forwarded from what system function to what system function? |
| SV-5 | • What operational activities are supported by what system functions? • What operational activities are exposed through what system functions? |
| SV-6 | • What H/W is allocated to what system elements? • What information is forwarded e.g., from what system elements to what system elements? |
| SV-10b | • What events are handled, by what systems, through what activities, in what sequence, with what timing? |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Voutyras, O.; Bokhari, A.H.; Tsuge, A.; Palaiokrassas, G.; Kawasaki, T.; Cases-Camats, X.; Nakazawa, J.; Litke, A.; Okoshi, T.; Varvarigou, T. A Methodology for Generating Systems Architectural Glimpse Statements Using the 5W1H Maxim. Computers 2021, 10, 131. https://doi.org/10.3390/computers10100131
Voutyras O, Bokhari AH, Tsuge A, Palaiokrassas G, Kawasaki T, Cases-Camats X, Nakazawa J, Litke A, Okoshi T, Varvarigou T. A Methodology for Generating Systems Architectural Glimpse Statements Using the 5W1H Maxim. Computers. 2021; 10(10):131. https://doi.org/10.3390/computers10100131
Chicago/Turabian StyleVoutyras, Orfefs, Aamir H. Bokhari, Akira Tsuge, Georgios Palaiokrassas, Takafumi Kawasaki, Xavier Cases-Camats, Jin Nakazawa, Antonios Litke, Tadashi Okoshi, and Theodora Varvarigou. 2021. "A Methodology for Generating Systems Architectural Glimpse Statements Using the 5W1H Maxim" Computers 10, no. 10: 131. https://doi.org/10.3390/computers10100131
APA StyleVoutyras, O., Bokhari, A. H., Tsuge, A., Palaiokrassas, G., Kawasaki, T., Cases-Camats, X., Nakazawa, J., Litke, A., Okoshi, T., & Varvarigou, T. (2021). A Methodology for Generating Systems Architectural Glimpse Statements Using the 5W1H Maxim. Computers, 10(10), 131. https://doi.org/10.3390/computers10100131







