4.1. Correlation Analysis of Darknet Traffic and IDS Alerts
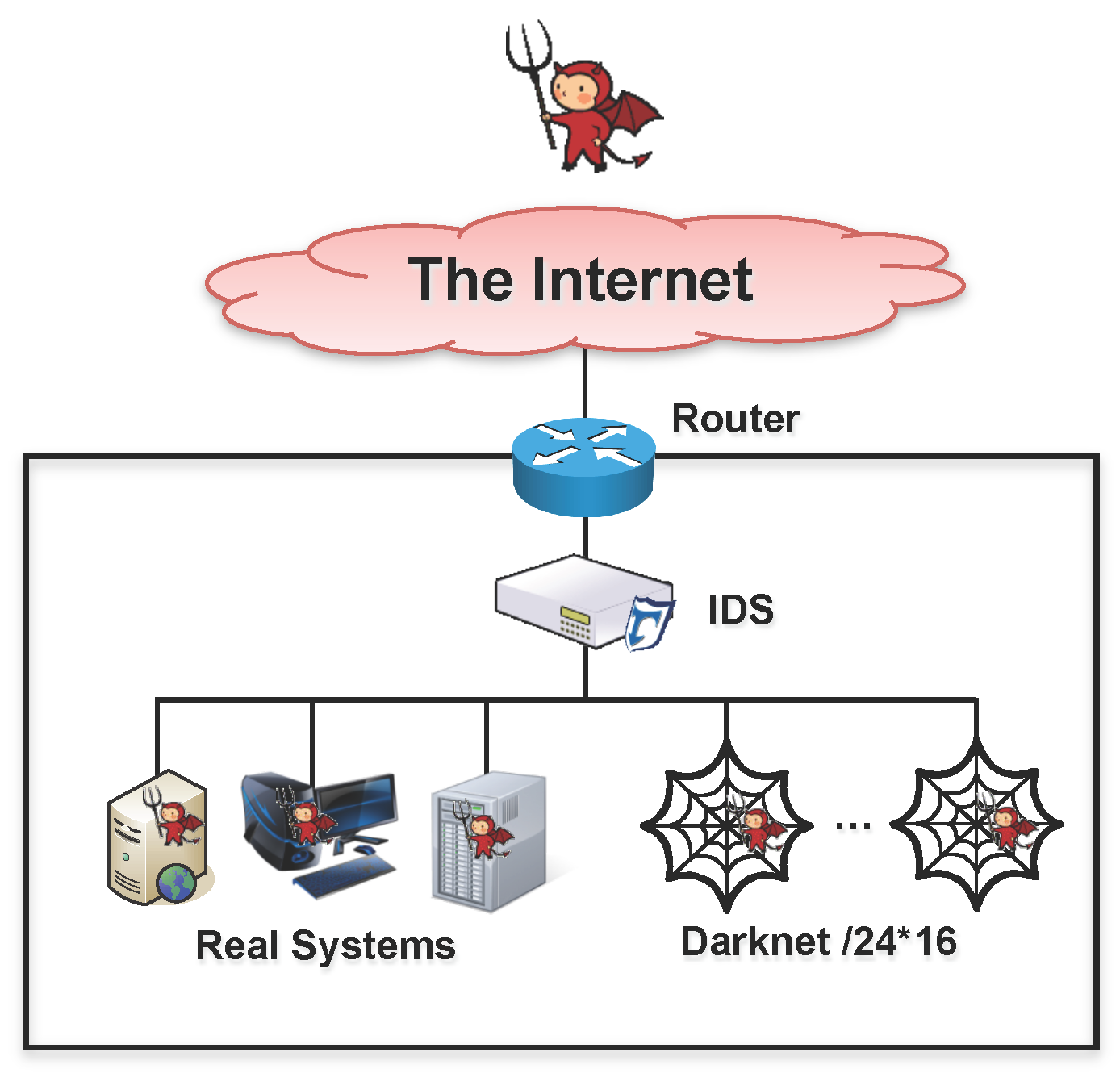
Figure 2 shows the experimental environment. In order to carry out correlation analysis between darknet traffic and IDS alerts, we prepared 16*/24 darknet (i.e., 4080 IP addresses) in Korea and collected all of the darknet traffic during six months (January 2013 to June 2013). Furthermore, we deployed a dedicated IDS in the boundary network of the 16*/24 darknet IP addresses.
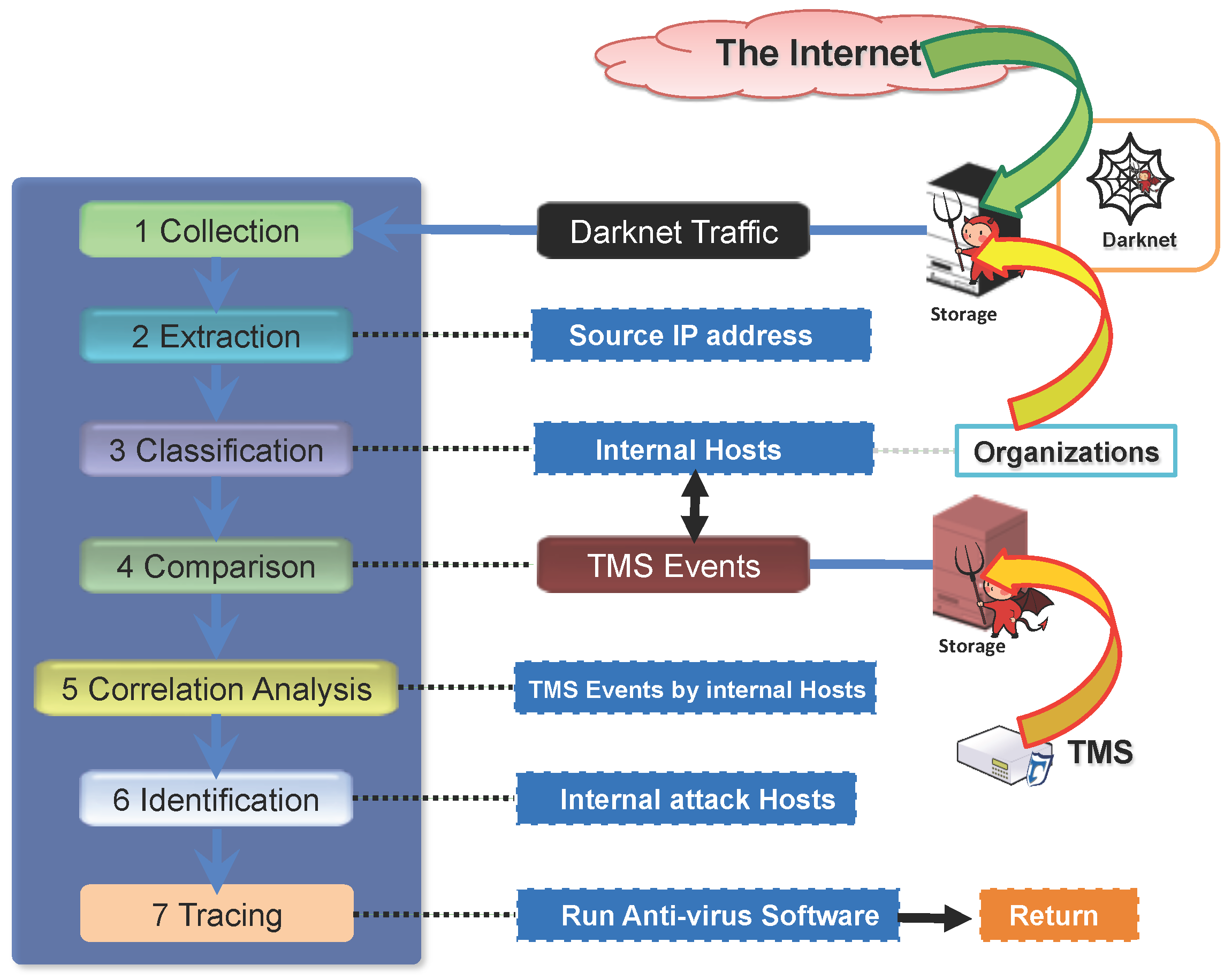
According to the procedure described in
Section 3, we conducted the correlation analysis between all of the incoming darknet traffic and IDS alerts that were raised by a dedicated IDS.
Extraction: We extracted source IP addresses from the entirety of the darknet traffic. We observed that 300 unique source IP addresses per day sent packets to our darknet on average.
Classification: We then classified the source IP addresses into the internal hosts and the external hosts. After the classification phase, we observed that only eight internal hosts sent attack packets to our darknet.
Table 1 shows the overview of the eight internal hosts observed on our darknet and the number of IDS alerts that were caused by the eight internal hosts. Note that we sanitized the IP addresses of the eight internal hosts and organizations for privacy.
Comparison: We extracted the IDS alerts whose source IP addresses are matched to the eight internal hosts. In this comparison phase, we set the time interval to one month for comparing the darknet traffic and the IDS alerts. For example, if an internal host sent packets to the darknet on 15 January, we extracted the IDS alerts whose source IP addresses are the same as the internal host from 1 January to 31 January. As a result, as shown in
Table 1, among the eight internal hosts, we can see that seven IP addresses also raised one and more IDS alerts during the predefined time interval, i.e., one month.
Correlation analysis: In our further investigation, we observed that four internal hosts (i.e., the 5th, 6th, 7th and 8th internal hosts in
Table 1) raised multiple types (i.e., scanning and web vulnerability) of IDS alerts, while three internal hosts (i.e., the 1st, 2nd and 3rd internal hosts in
Table 1) raised a single type of IDS alert (i.e., scanning or web vulnerability).
Identification: From these results, it could be concluded that seven internal hosts were infected by one and more malware, and consequently, they triggered many IDS alerts with different types; and their malicious activities were also observed on the darknet.
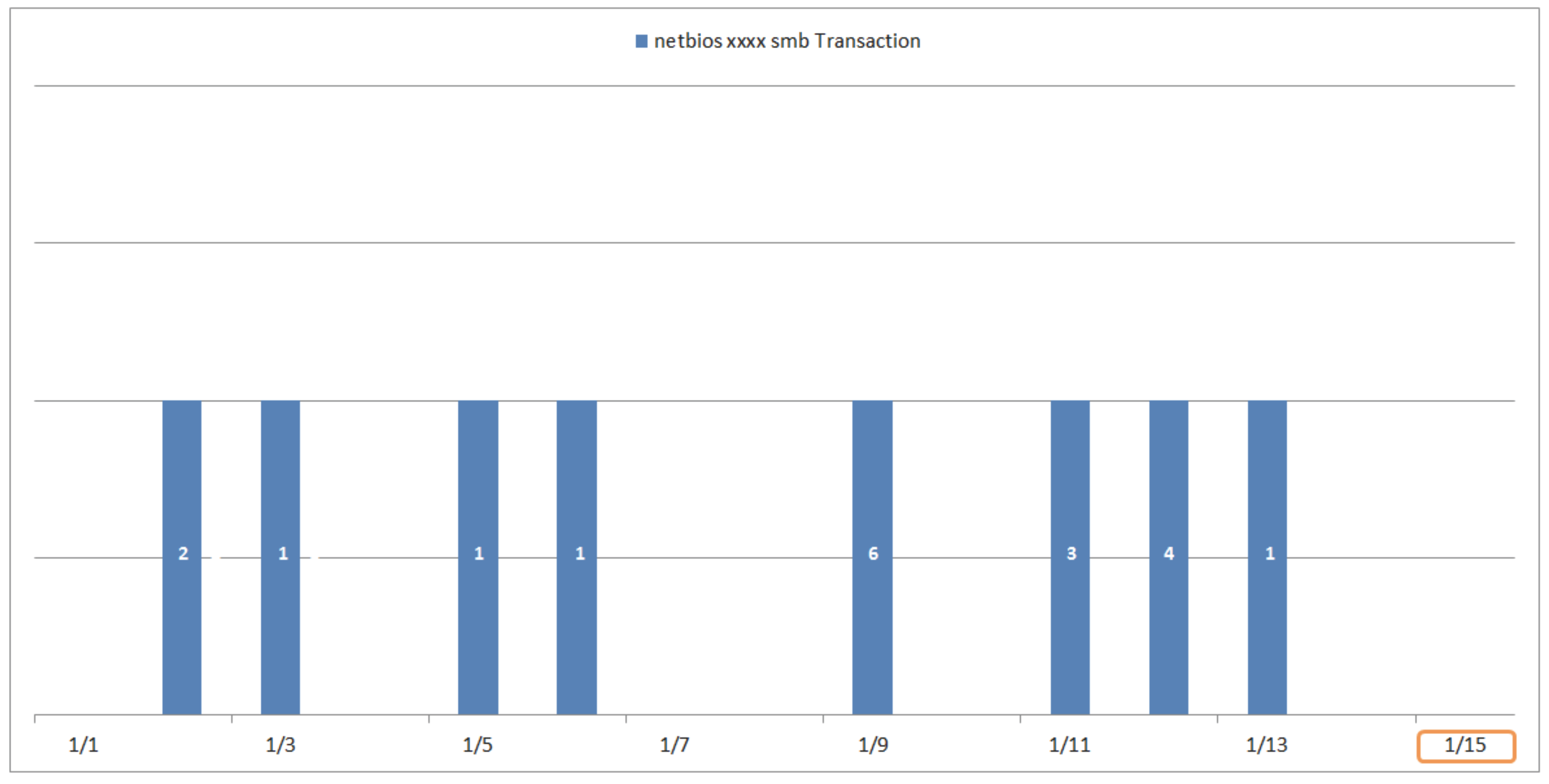
Figure 3,
Figure 4,
Figure 5,
Figure 6,
Figure 7,
Figure 8 and
Figure 9 show the IDS alerts related to the seven internal hosts (i.e., the 1st, 2nd, 3rd, 5th, 6th, 7th and 8th) that sent packets to the darknet and also raised one or more IDS alerts. In
Figure 3,
Figure 4,
Figure 5,
Figure 6,
Figure 7,
Figure 8 and
Figure 9, the horizontal axis means the time, and the orange square boxes indicate the detection time of packets observed on the darknet. The Arabic numeral in the colored square boxes (e.g., blue, red, green, purple, etc.) indicates the number of IDS alerts that were triggered by the seven internal hosts, i.e., potential attackers. Furthermore, the color of the square boxes represents the type of IDS alerts. Furthermore,
Table 2,
Table 3,
Table 4,
Table 5,
Table 6,
Table 7 and
Table 8 show the additional information (i.e., detection time, protocol, source and destination ports, packet size) for the corresponding internal hosts, i.e., the 1st, 2nd, 3rd, 5th, 6th, 7th and 8th, respectively.
From
Figure 3, we can see that the first internal host raised one type of IDS alert. The name of the IDS alerts is “netbios xxxx smb Transaction”. Note that we sanitized the name of IDS alerts due to security. The first internal host raised 19 IDS alerts before the detection time (i.e., 15 January) of darknet traffic. From
Table 2, the first internal host used the TCP protocol, and the darknet traffic was destined to port 1925, while the IDS alerts were destined to many different ports. The packet sizes of darknet traffic and the IDS alerts were 304 and 846 bytes.
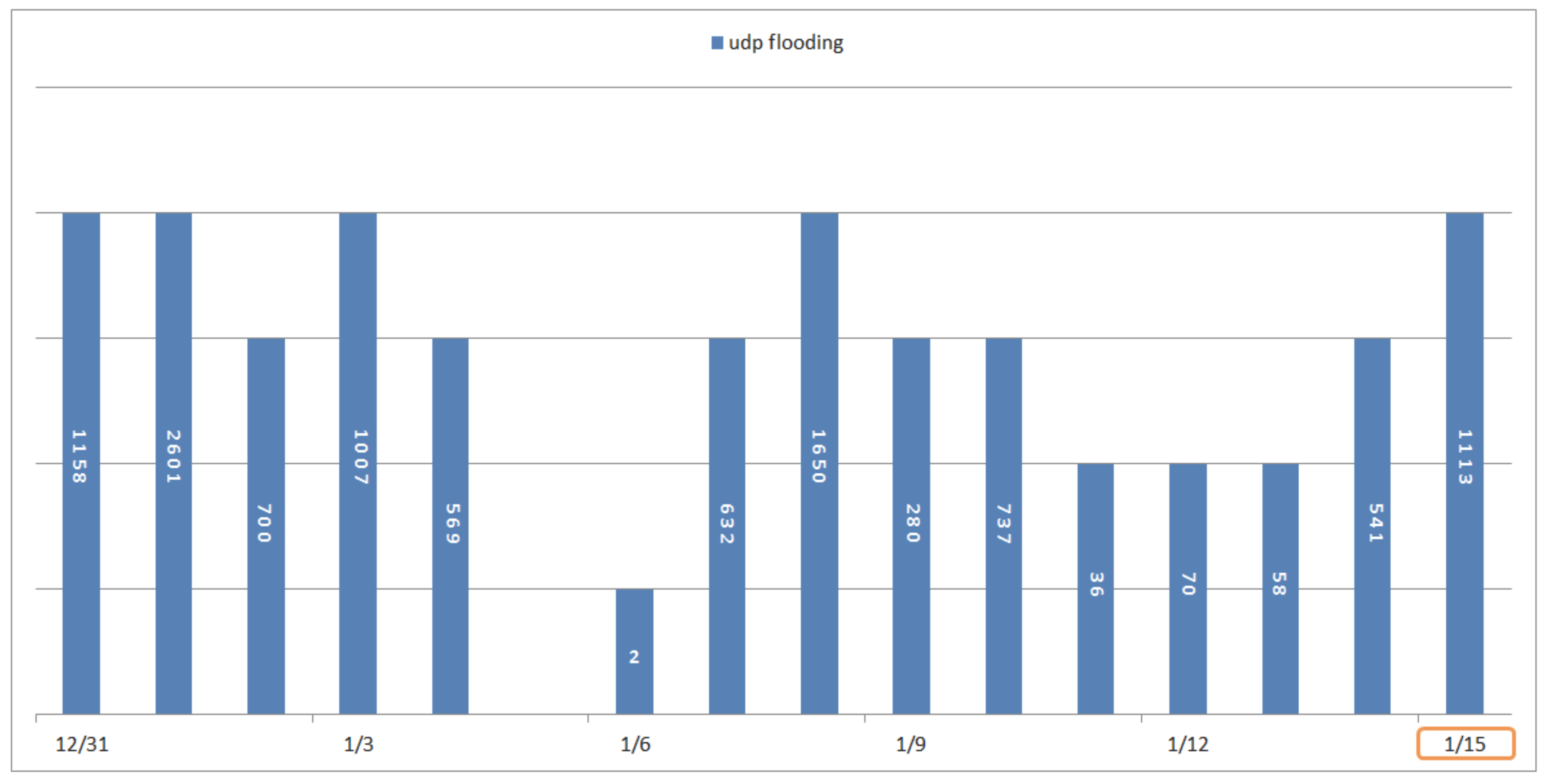
From
Figure 4, we can see that the second internal host raised one type of IDS alert. The name of the IDS alert is “udpflooding”. The second internal host raised many IDS alerts constantly before the detection time (i.e., 15 January) of darknet traffic. From
Table 3, the second internal host used the UDP protocol, and the darknet traffic was destined to port 34902, while the IDS alerts were destined to many different ports. The packet size of darknet traffic was 352 bytes, while the IDS alerts have many different sizes of packets.
From
Figure 5, we can see that the third internal host raised one type of IDS alert. The name of IDS alerts is “udp flooding”. The third internal host raised 31 IDS alerts after the detection time (i.e., 23 January) of darknet traffic. From
Table 4, the third internal host used the UDP protocol, and the darknet traffic was destined to port 47684, while the IDS alerts were destined to many different ports. The packet size of darknet traffic was 352 bytes, while the IDS alerts have many different sizes of packets.
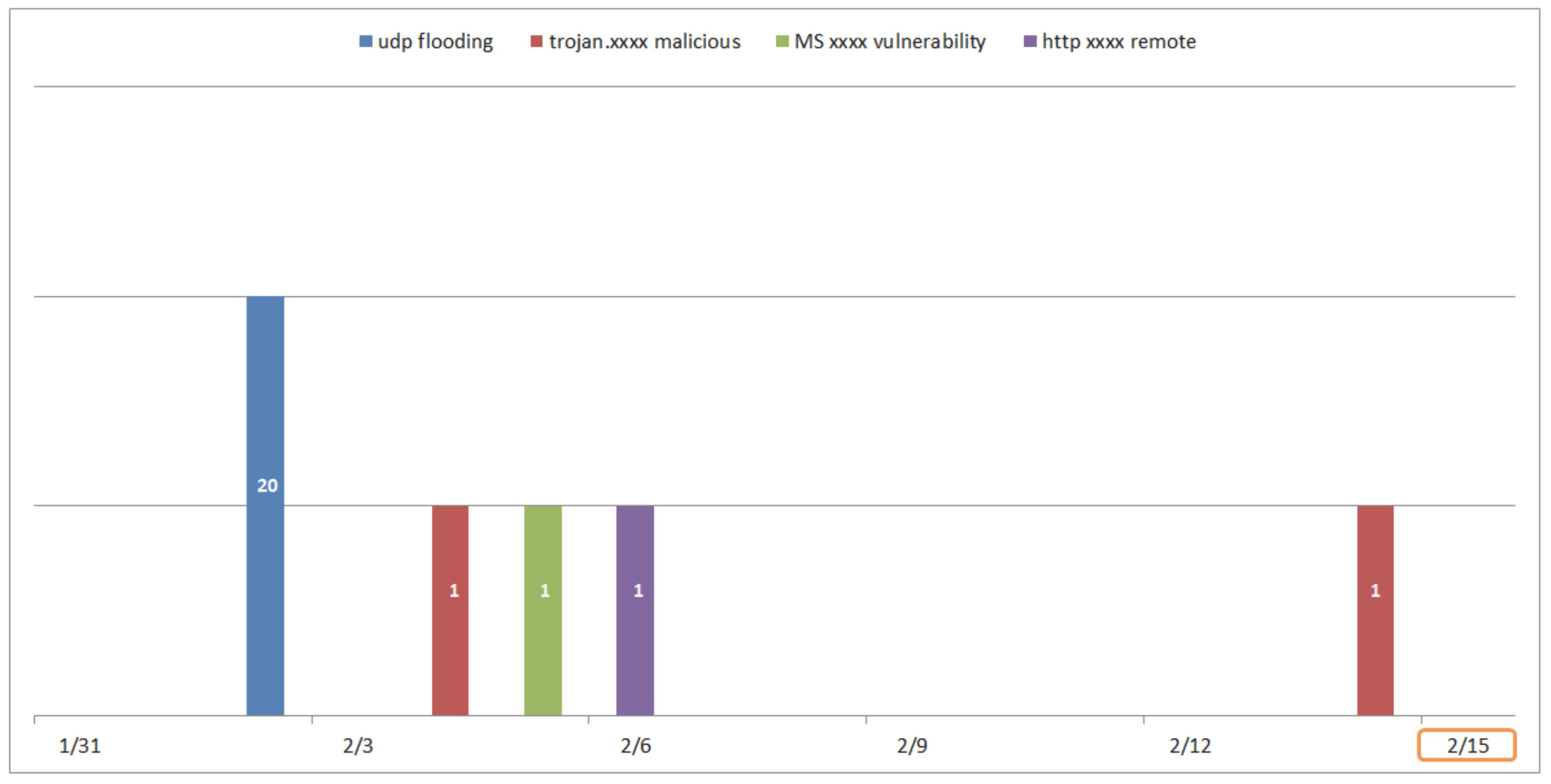
From
Figure 6, we can see that the fifth internal host raised four types of IDS alerts. The names of the IDS alerts are “udp flooding”, “trojan.xxxx malicious”, “MicroSoft (MS)xxxx vulnerability” and “http xxxx remote”. The fifth internal host raised 24 IDS alerts before the detection time (i.e., 15 February) of darknet traffic. From
Table 5, the fifth internal host used UDP and the TCP protocol, and the darknet traffic was destined to port 16609, while the IDS alerts were destined to many different ports, including 16609. The packet size of darknet traffic was 352 bytes, while the IDS alerts have many different sizes of packets.
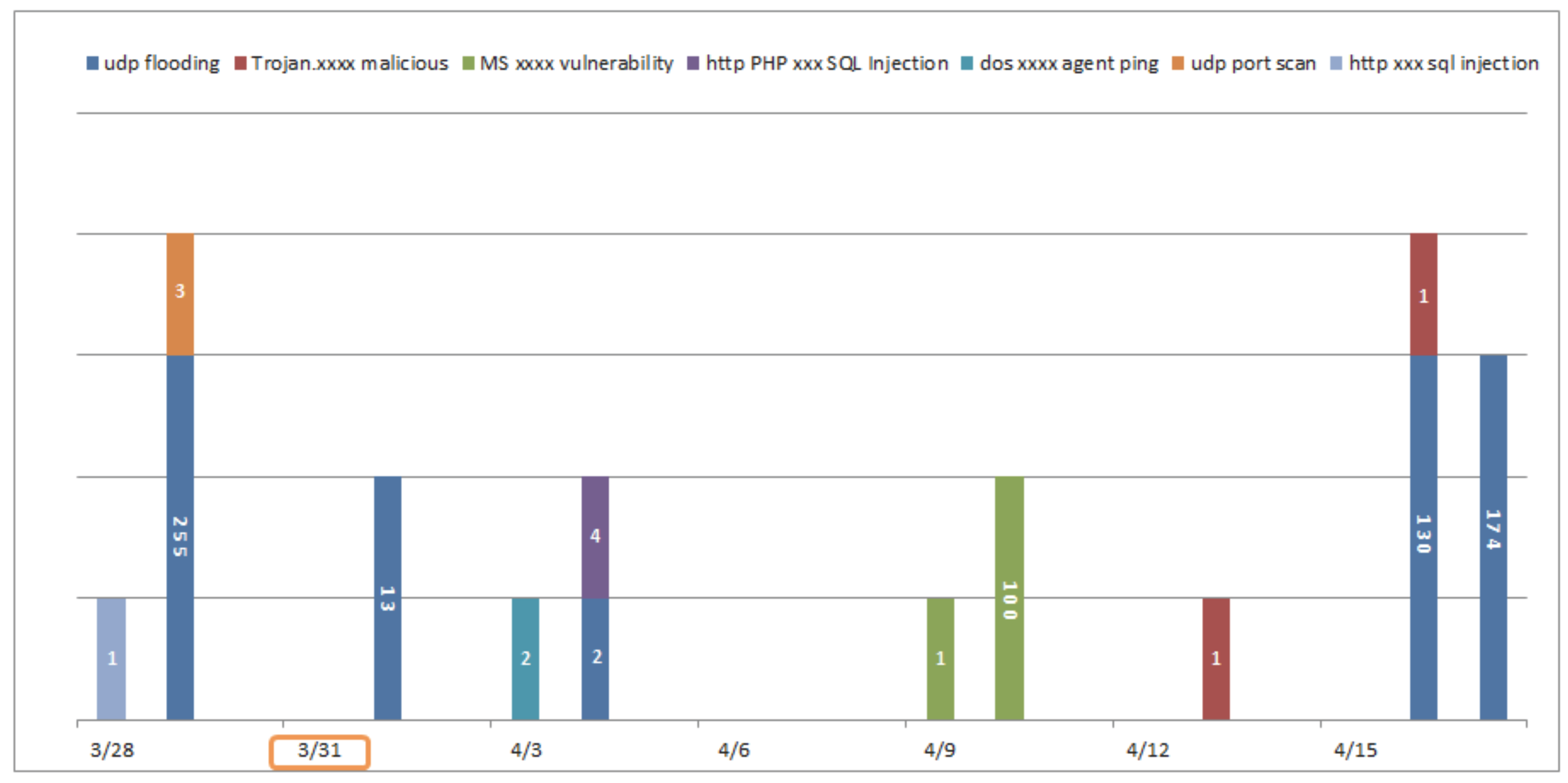
From
Figure 7, we can easily see that the sixth internal host raised seven different types of IDS alerts. Particularly, two alerts (i.e., “http xxx sqlinjection” and “udp port scan”) were recorded before the detection time (i.e., 31 March) of darknet traffic, while four alerts (i.e., “Trojan.xxxx malicious”, “MS xxxx vulnerability”, “http PHP xxxx SQL Injection” and “dos xxxx agent ping”) were raised after the detection time of darknet traffic.
From
Table 6, the sixth internal host used UDP and the TCP protocol, and the darknet traffic was destined to port 50226, while the IDS alerts were destined to many different ports, including 50226. The packet size of darknet traffic was 352 bytes, while the IDS alerts have many different sizes of packets.
From
Figure 8, we can see that the seventh internal host raised four types of IDS alerts. The names of IDS alerts are “udp flooding”, “trojan.xxxx malicious”, “dos xxxx agent ping” and “udp port scan”. The seventh internal host raised many IDS alerts before and after the detection time (i.e., 4 April) of darknet traffic. From
Table 7, the seventh internal host used UDP and the TCP protocol, and the darknet traffic was destined to port 15730, while the IDS alerts were destined to many different ports, including 15730. The packet size of darknet traffic was 352 bytes, while the IDS alerts have many different sizes of packets.
From
Figure 9, we can see that the eight internal host raised six different types of IDS alerts. Especially, four alerts (i.e., “udp port scan”, “dos xxxx agent ping”, “dosxxxx agent ping 2” and “malware-hacking-mail”) were recorded before the detection time (i.e., 11 May) of darknet traffic, while one alert (i.e., “http web attack tool”) was triggered after the detection time of darknet traffic. From
Table 8, the eight internal host used UDP and the TCP protocol, and the darknet traffic was destined to port 46201, while the IDS alerts were destined to many different ports, including 46201. The packet size of darknet traffic was 248 bytes, while the IDS alerts have many different sizes of packets.
In addition, from
Figure 3,
Figure 4,
Figure 7,
Figure 8 and
Figure 9, we can easily see that ‘udp flooding’ IDS alerts were raised during a long period of time. As a result, from these results, we can conclude that if an internal host sends any packet(s) to the darknet, it was already compromised by some malware. Therefore, it is strongly recommended to have a response against the internal host, such as blocking the IP address, removing the malware using security software, and so on.
4.2. Tracing and Identifying Potential Attackers
In order to carry out the in-depth analysis of potential attackers, i.e., attack hosts, that sent packets to the darknet, we prepared more experimental data collected from the same experimental environment in
Figure 2. Similar to the correlation analysis in
Section 4.1, we also deployed a dedicated IDS in the boundary network of the 16*/24 darknet IP addresses. We used the darknet traffic and IDS alerts of two months (September 2013 to October 2013) for tracing and identifying potential attackers from them.
According to the procedure described in
Section 3, we conducted the in-depth analysis between all of the incoming darknet traffic and IDS alerts that were raised by the dedicated IDS.
Extraction: We extracted source IP addresses from the entire darknet traffic.
Classification: We then classified the source IP addresses into the internal hosts and the external hosts. After the classification phase, we observed that only 17 internal hosts sent attack packets to our darknet.
Table 9 shows the overview of 17 internal hosts observed on our darknet. Note that we sanitized the IP addresses of the 17 internal hosts and organizations for privacy.
Comparison: We extracted the IDS alerts whose source IP addresses are matched to the 17 internal hosts. In this comparison phase, we set the time interval between darknet traffic and the IDS alerts as one month. For example, if an internal host sent packets to the darknet on 16 September, we extracted the IDS alerts whose source IP addresses are the same as the internal host from 1 September to 1 October. As a result, as shown in
Table 10, among the 17 internal hosts, we can see that five IP addresses (i.e., internal attack hosts) also raised one and more IDS alerts during one month.
Correlation analysis: In our further investigation, we observed that one internal host raised multiple types of IDS alerts, while four internal hosts raised a single type of IDS alerts.
Identification and tracing: We run anti-virus software to identify and trace malware on the five internal attack hosts. As a result, we observed that two attack hosts (i.e., the third and ninth in
Table 9) were infected with 30 and 144 different types of malware; while the anti-virus software could not detect any malware from the other hosts (i.e., the 11th, 12th and 16th in
Table 9). From these results, it could be concluded that two internal attack hosts were infected by many malwares, and consequently, they triggered many IDS alerts with different types; and their malicious activities were also observed on the darknet. Furthermore, there is a high possibility that the other three internal hosts were infected by unknown malwares that were not detected by the anti-virus software. Since the darknet traffic itself is caused by malicious activities, if the dedicated IDS records the corresponding security events, they also can be regarded as true positives, not false positives.
Figure 10,
Figure 11,
Figure 12,
Figure 13,
Figure 14,
Figure 15,
Figure 16,
Figure 17,
Figure 18 and
Figure 19 show the IDS alerts related to the five internal attack hosts (i.e., the 3rd, 9th, 11th, 12th and 19th) that sent packets to the darknet and also raised one and more IDS alerts, and the examples of the IDS alerts related to the five internal attack hosts.In
Figure 10,
Figure 12,
Figure 14,
Figure 16 and
Figure 18, the horizontal axis means the time, and the orange square boxes indicate the detection time of packets observed on the darknet.
The Arabic numeral in the colored square boxes (e.g., blue, red, green, purple, etc.) indicates the number of IDS alerts that were triggered by the five internal attack hosts. The color of the square boxes represents the type of IDS alert.
Table 11,
Table 12,
Table 13,
Table 14 and
Table 15 show the additional information (i.e., detection time, protocol, source and destination ports, packet size) for the corresponding internal attack hosts, i.e., the 3rd, 9th, 11th, 12th and 19th, respectively.
From
Figure 10, we can see that the third internal attack host raised one type of IDS alert. The name of IDS alert is “udp flooding”. The third internal attack host raised 28 IDS alerts before the detection time (i.e., 16 September) of darknet traffic.
Figure 11 shows the examples of the “udp flooding” alerts. Note that we sanitized the name of the IDS alerts and the IP addresses for security. From
Table 11, the third internal attack host used the UDP protocol, and the darknet traffic and the IDS alerts were destined to many different ports. The packet size of darknet traffic was 316 bytes, while the IDS alerts have many different sizes of packets. In addition, as described in
Table 9, the anti-virus software detected 30 different types of malware on the third internal attack host.
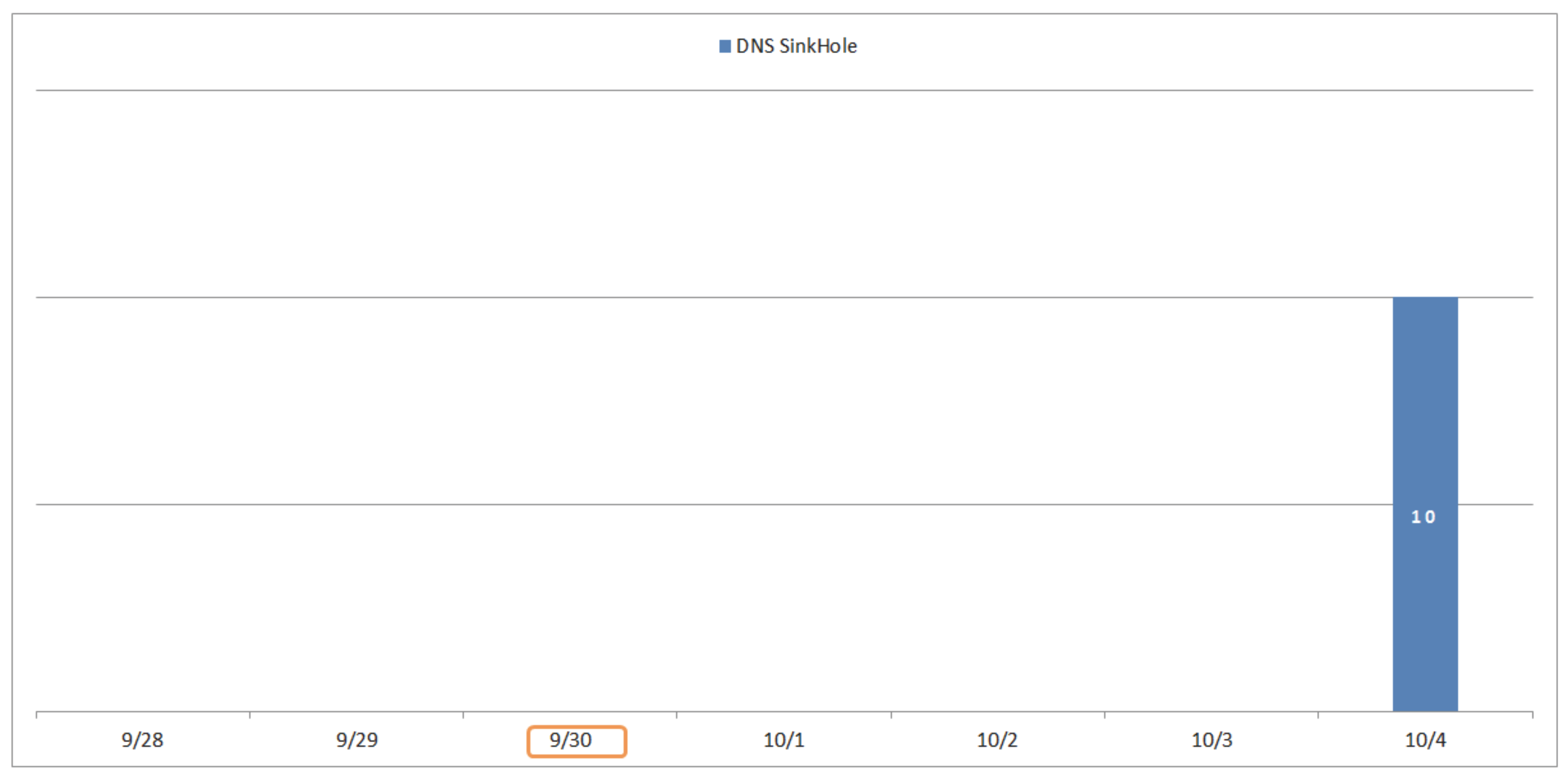
From
Figure 12, we can see that the ninth internal attack host raised one type of IDS alert. The name of IDS alert is “DNS Sinkhole”. The ninth internal attack host raised 10 IDS alerts after the detection time (i.e., 30 September) of darknet traffic.
Figure 13 shows the examples of the “DNS Sinkhole” alerts. From
Table 12, the ninth internal attack host used TCP protocol, and the darknet traffic was destined to many different ports, while the destination ports of the IDS alerts were 5218 and 217. The packet size of darknet traffic was 264 bytes, while the IDS alerts have many different sizes of packets. In addition, as described in
Table 9, the anti-virus software detected 144 different types of malwares on the ninth internal attack host.
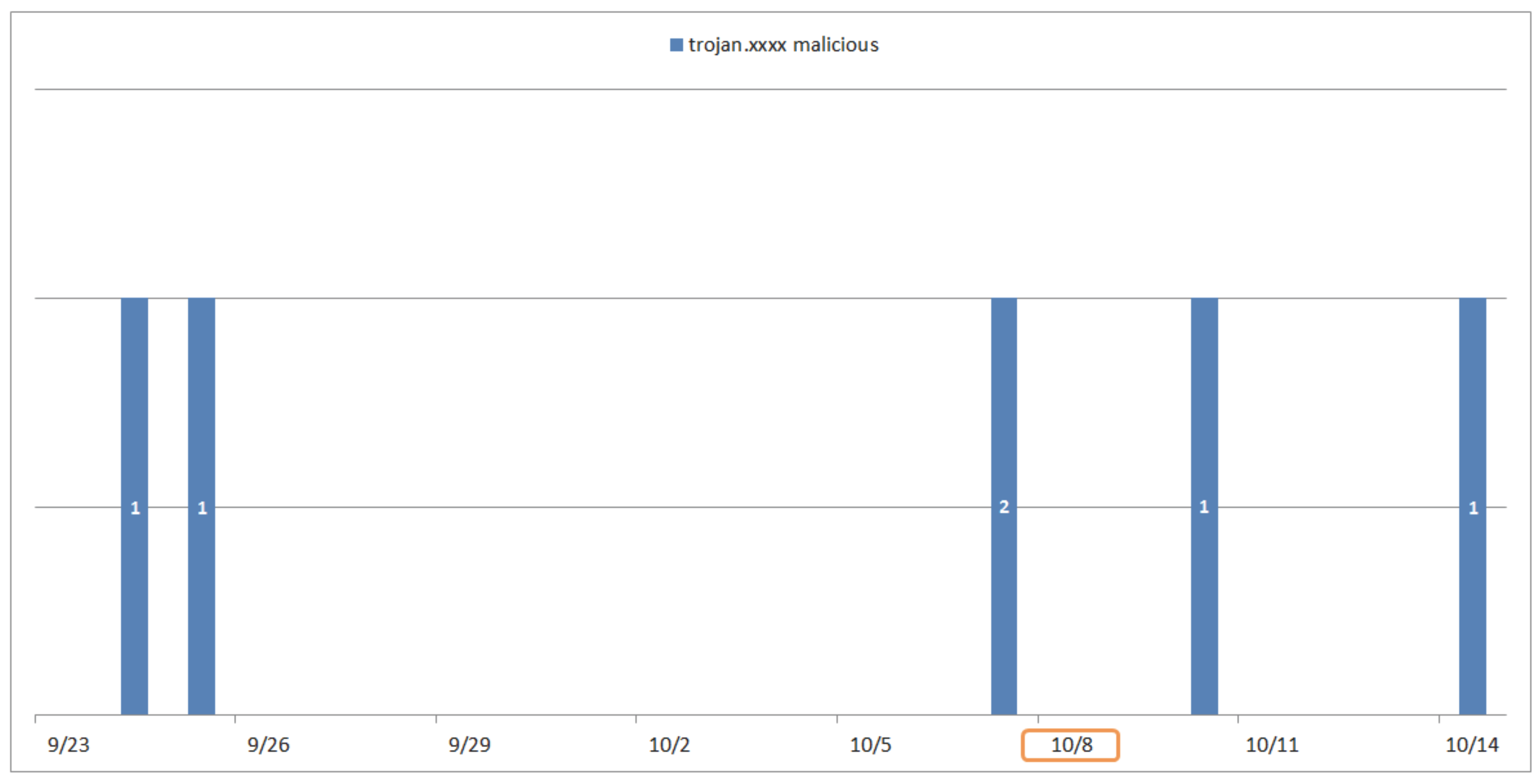
From
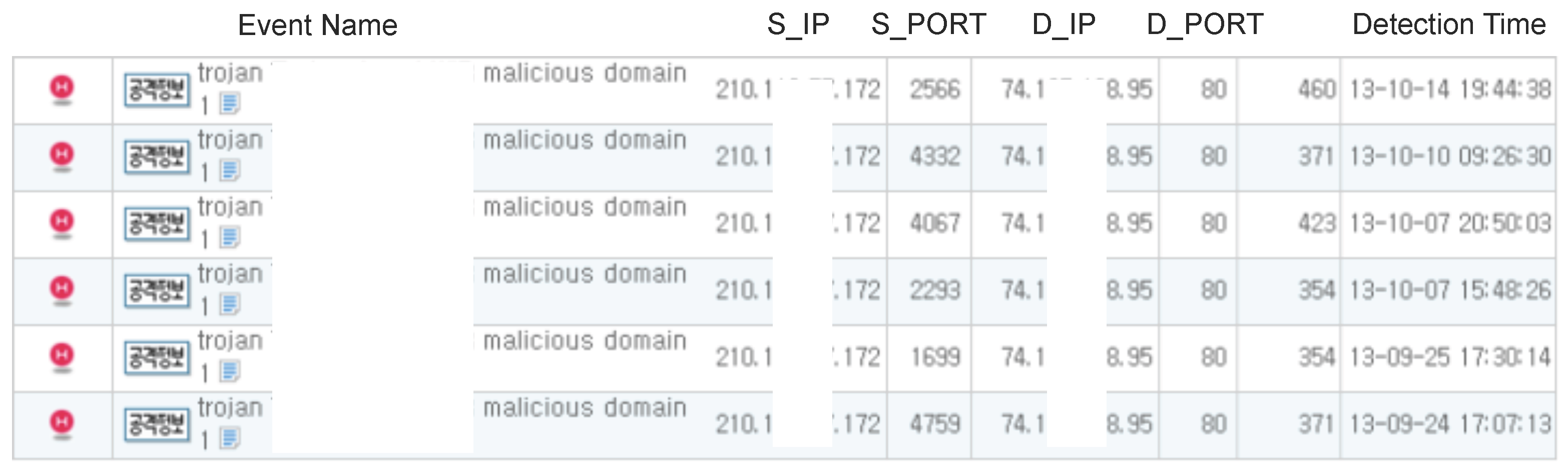
Figure 14, we can see that the 11th internal attack host raised one type of IDS alerts. The name of the IDS alert is “trojan.xxxx malicious”. The 11th internal attack host raised six IDS alerts before and after the detection time (i.e., 8 October) of darknet traffic.
Figure 15 shows the examples of the “trojan.xxxx malicious” alerts. From
Table 13, the 11th internal attack host used UDP and the TCP protocol, and the darknet traffic was destined to port 5489, while IDS alerts were destined to many different ports. The packet size of darknet traffic was 556 bytes, while the IDS alerts have many different sizes of packets. In addition, as described in
Table 9, the anti-virus software could not detect any malware on the 11th internal attack host. This means that the 11th internal attack host was compromised by unknown malware.
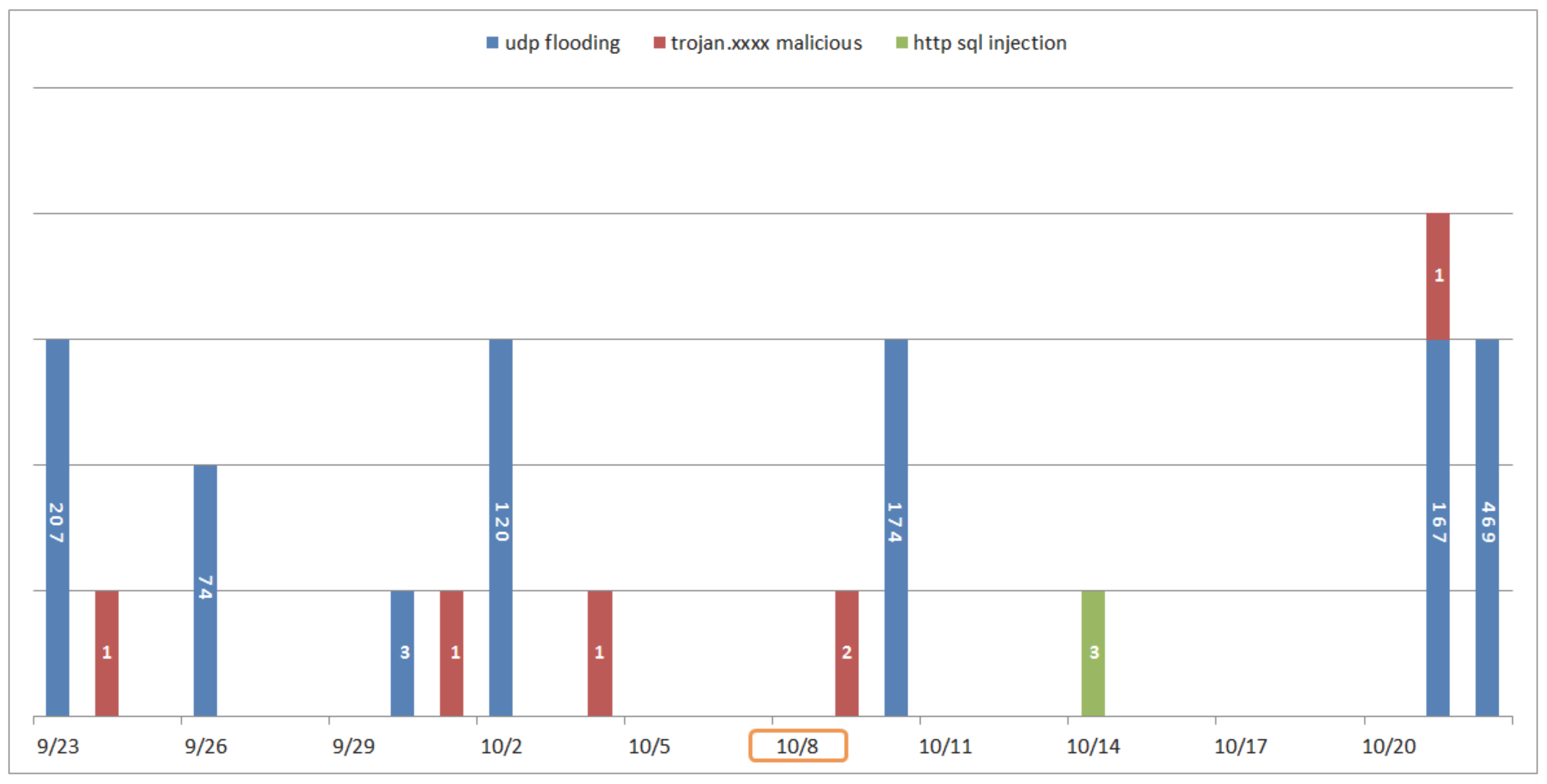
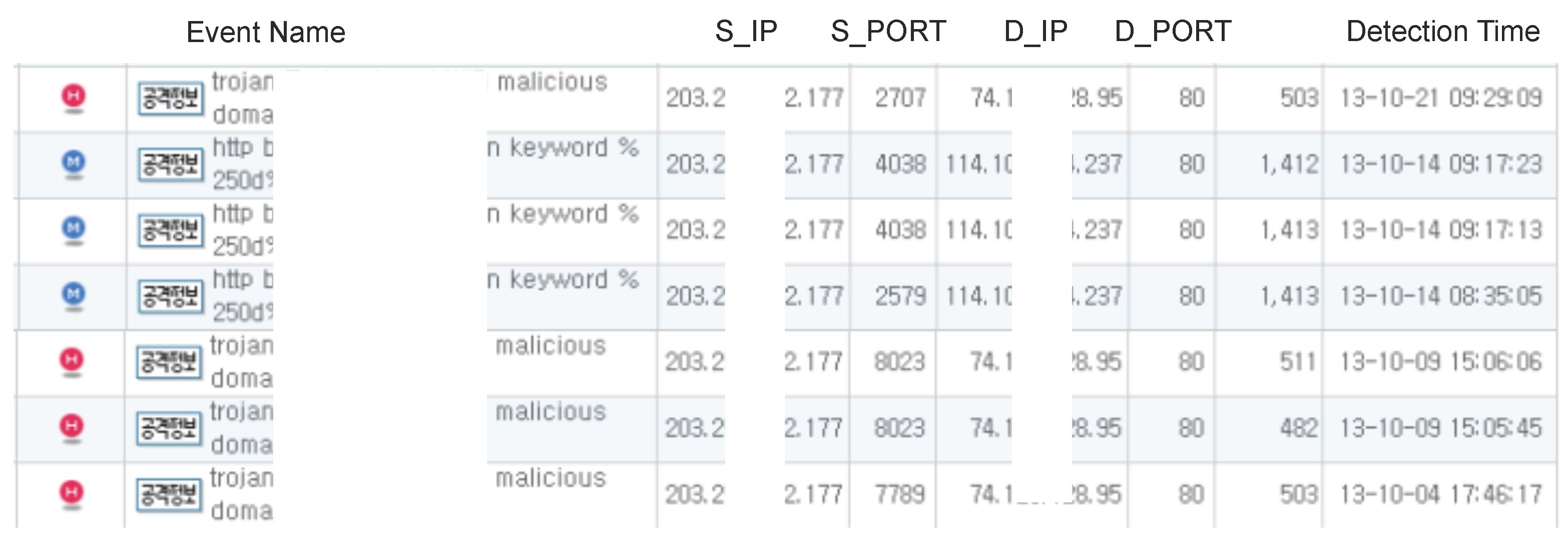
From
Figure 16, we can see that the 12th internal attack host raised three types of IDS alerts. The names of IDS alerts are “udp flooding”, “trojan.xxxx malicious” and “http sql injection”. The 12th internal attack host raised many IDS alerts before and after the detection time (i.e., 8 October) of darknet traffic.
Figure 17 shows the examples of the “udp flooding”, “trojan.xxxx malicious” and “http sql injection” alerts. From
Table 14, the 12th internal attack host used UDP and the TCP protocol, and the darknet traffic was destined to port 5489, while IDS alerts were destined to many different ports. The packet size of darknet traffic was 556 bytes, while the IDS alerts have many different sizes of packets. In addition, as described in
Table 9, the anti-virus software could not detect any malware on the 12th internal attack host. This means that the 12th internal attack host was infected by unknown malware.
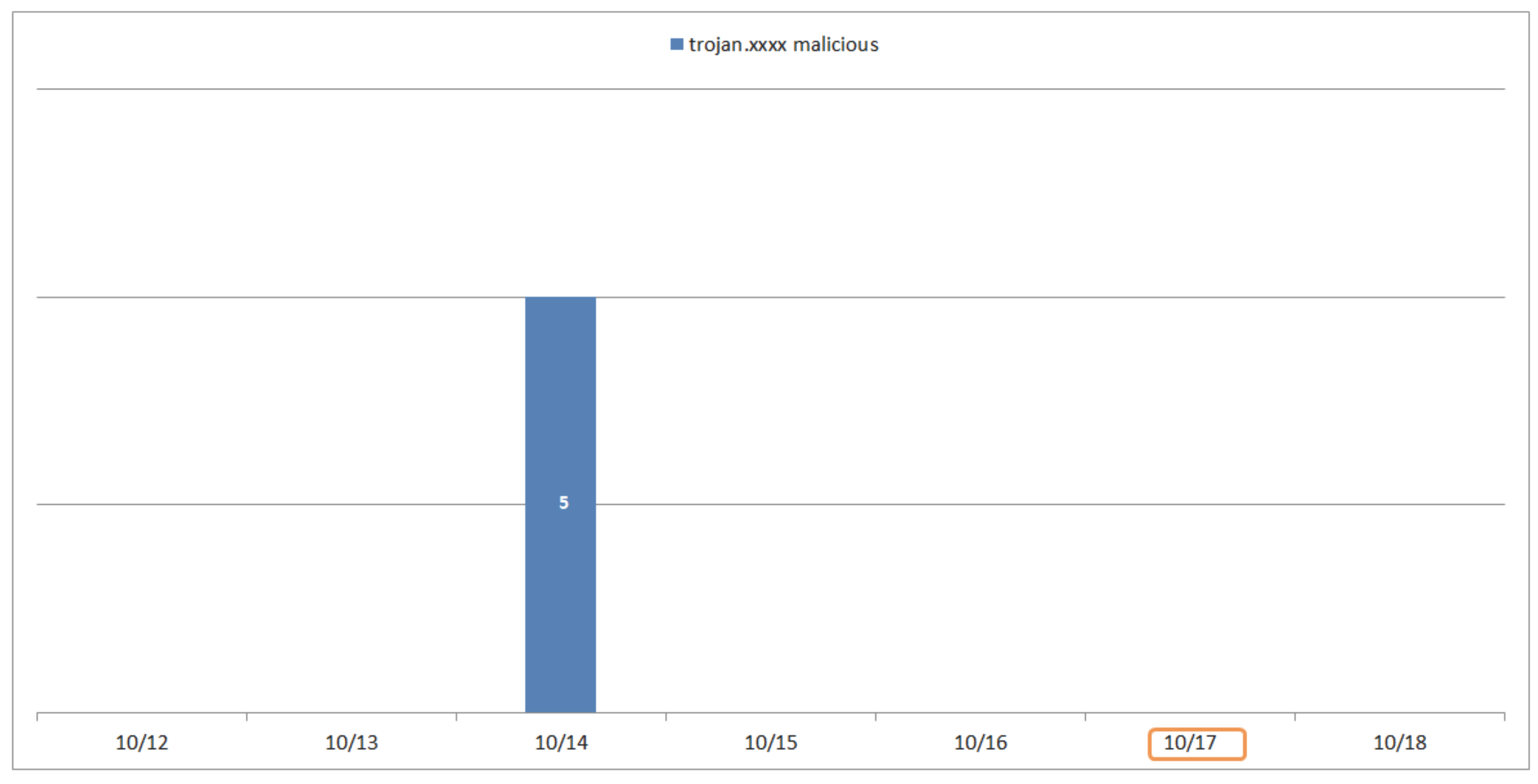
From
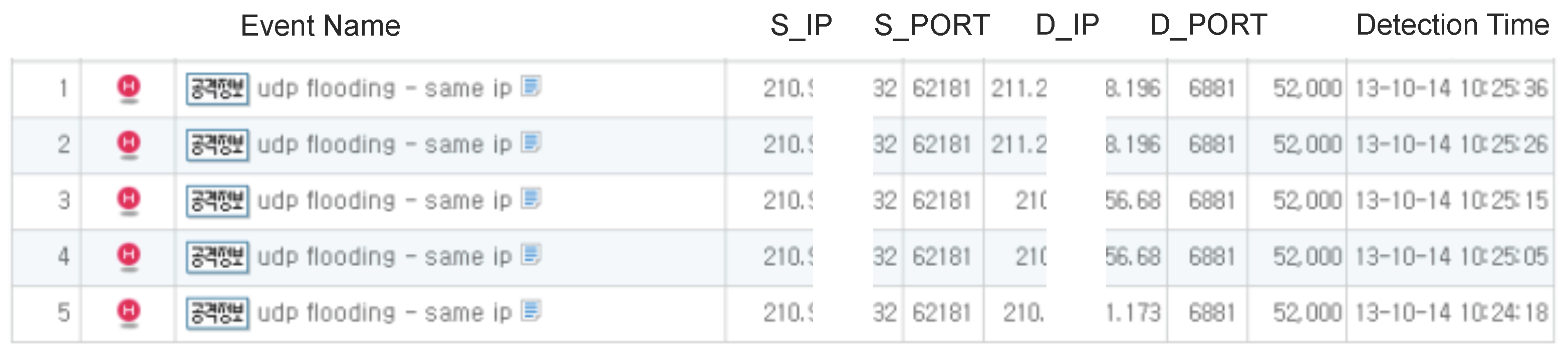
Figure 18, we can see that the 16th internal attack host raised one type of IDS alert. The name of the IDS alert is “trojan.xxxx malicious”. The 16th internal attack host raised five IDS alerts before the detection time (i.e., 17 October) of darknet traffic.
Figure 19 shows the examples of the “trojan.xxxx malicious” alerts. From
Table 15, the 16th internal attack host used the UDP protocol, and the darknet traffic was destined to many different ports, which the IDS alert was destined to port 62181. The packet size of darknet traffic has many different sizes of packets, while the packet size of the IDS alerts was 52,000 bytes. In addition, as described in
Table 9, the anti-virus software could not detect any malware on the 16th internal attack host. This means that the 16th internal attack host was infected by unknown malware.