A Hybrid Traceability Technology Selection Approach for Sustainable Food Supply Chains
Abstract
:1. Introduction
2. Traceability Technologies and Selection Criteria
2.1. Technologies
2.1.1. Paper-Based Recording
2.1.2. 1D Barcode
2.1.3. 2D Barcode
2.1.4. RFID Passive LF Read-Only
2.1.5. RFID Passive LF Read-Write
2.1.6. RFID Passive HF Read-Only
2.1.7. RFID Passive HF Read-Write
2.1.8. RFID Passive HF with Sensor
2.1.9. RFID Passive UHF Read Only
2.1.10. RFID Passive UHF Read-Write
2.1.11. RFID Passive UHF with Sensor
2.1.12. Semi-Passive RFID
2.1.13. Active RFID
2.1.14. NFC
2.1.15. WSN
2.1.16. Smart Packaging Indicator
2.2. Technology Criteria
2.2.1. Cost (C1)
2.2.2. Vulnerability to Water (C2)
2.2.3. Flexibility (C3)
2.2.4. Accuracy of Information (C4)
2.2.5. Reading Range (C5)
2.2.6. Data Transfer Speed (C6)
2.2.7. Multiple Tags Readability (C7)
2.2.8. Identification Capacity (C8)
2.2.9. Tag Writing Cycle (C9)
2.2.10. Memory Capacity (C10)
2.2.11. Environmental Parameters Recording (C11)
2.2.12. Real-Time Location Recording (C12)
2.2.13. Real-Time Alert (C13)
2.2.14. Durability of Data Carrier (C14)
2.2.15. World-Wide Standard (C15)
2.2.16. Data Security (C16)
2.2.17. Manual Data Readability (C17)
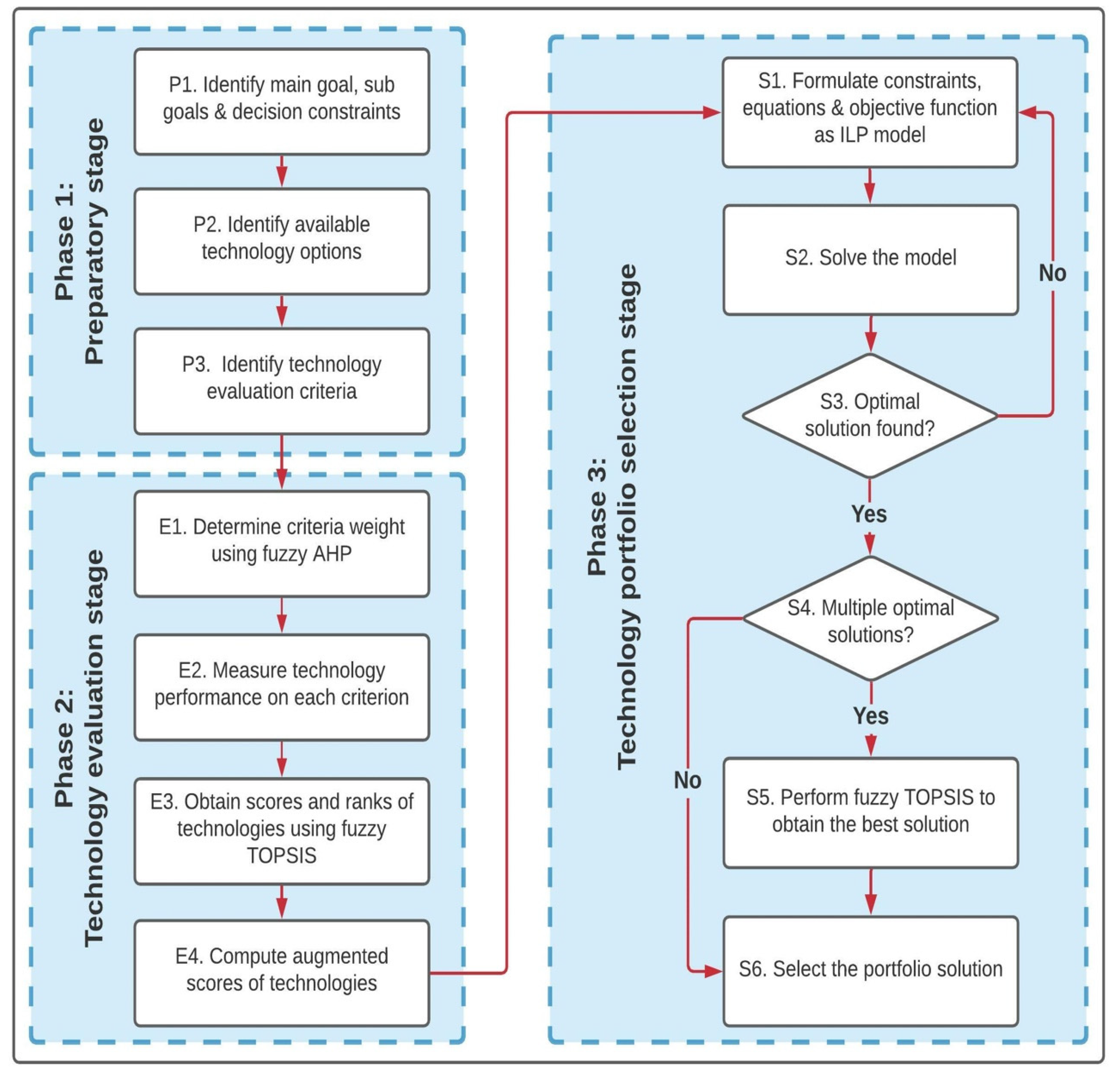
3. Proposed Framework
3.1. Phase 1: Preparatory Stage
3.2. Phase 2: Technology Evaluation Stage
3.3. Phase 3: Technology Portfolio Selection Stage
4. Case Study
4.1. Case 1
4.2. Case 2
4.3. Case 3
4.4. Case 4
5. Discussion
6. Conclusions
Supplementary Materials
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Luo, H.; Zhu, M.; Ye, S.; Hou, H.; Chen, Y.; Bulysheva, L. An intelligent tracking system based on internet of things for the cold chain. Internet Res. 2016, 26, 435–445. [Google Scholar] [CrossRef]
- Wu, J.Y.; Hsiao, H.I. Food quality and safety risk diagnosis in the food cold chain through failure mode and effect analysis. Food Control 2021, 120, 107501. [Google Scholar] [CrossRef]
- Jedermann, R.; Ruiz-Garcia, L.; Lang, W. Spatial temperature profiling by semi-passive RFID loggers for perishable food transportation. Comput. Electron. Agric. 2009, 65, 145–154. [Google Scholar] [CrossRef] [Green Version]
- FAO. Food Wastage Footprint: Impacts on Natural Resources. Summary Report. 2013. Available online: http://www.fao.org/3/i3347e/i3347e.pdf (accessed on 2 February 2021).
- Kummu, M.; de Moel, H.; Porkka, M.; Siebert, S.; Varis, O.; Ward, P.J. Lost food, wasted resources: Global food supply chain losses and their impacts on freshwater, cropland, and fertiliser use. Sci. Total Environ. 2012, 438, 477–489. [Google Scholar] [CrossRef] [PubMed]
- Ndraha, N.; Hsiao, H.I.; Vlajic, J.; Yang, M.F.; Lin, H.T.V. Time-temperature abuse in the food cold chain: Review of issues, challenges, and recommendations. Food Control 2018, 89, 12–21. [Google Scholar] [CrossRef] [Green Version]
- Alfian, G.; Rhee, J.; Ahn, H.; Lee, J.; Farooq, U.; Ijaz, M.F.; Syaekhoni, M.A. Integration of RFID, wireless sensor networks, and data mining in an e-pedigree food traceability system. J. Food Eng. 2017, 212, 65–75. [Google Scholar] [CrossRef]
- Óskarsdóttir, K.; Oddsson, G.V. Towards a decision support framework for technologies used in cold supply chain traceability. J. Food Eng. 2019, 240, 153–159. [Google Scholar] [CrossRef] [Green Version]
- Islam, S.; Cullen, J.M. Food Traceability: A Generic Theoretical Framework. Food Control 2021, 123, 107848. [Google Scholar] [CrossRef]
- Islam, S.; Cullen, J.M.; Manning, L. Visualising food traceability systems: A novel system architecture for mapping material and information flow. Trends Food Sci. Technol. 2021, 112, 708–719. [Google Scholar] [CrossRef]
- Bertolini, M.; Bottani, E.; Rizzi, A.; Volpi, A.; Renzi, P. Shrinkage reduction in perishable food supply chain by means of an RFID-based FIFO management policy. Int. J. RF Technol. 2013, 5, 123–136. [Google Scholar] [CrossRef]
- Boss, R.W. The technology of RFID. Libr. Technol. Rep. 2009, 39, 18–24. Available online: https://journals.ala.org/index.php/ltr/article/view/4724/5625 (accessed on 3 January 2021).
- Balbinot-Alfaro, E.; Craveiro, D.V.; Lima, K.O.; Costa, H.L.G.; Lopes, D.R.; Prentice, C. Intelligent Packaging with pH Indicator Potential. Food Eng. Rev. 2019, 11, 235–244. [Google Scholar] [CrossRef]
- Jedermann, R.; Nicometo, M.; Uysal, I.; Lang, W. Reducing food losses by intelligent food logistics. Philos. Trans. R. Soc. A Math. Phys. Eng. Sci. 2014, 372, 20130302. [Google Scholar] [CrossRef]
- Qian, J.P.; Yang, X.T.; Wu, X.M.; Zhao, L.; Fan, B.L.; Xing, B. A traceability system incorporating 2D barcode and RFID technology for wheat flour mills. Comput. Electron. Agric. 2012, 89, 76–85. [Google Scholar] [CrossRef]
- Liegeard, J.; Manning, L. Use of intelligent applications to reduce household food waste. Crit. Rev. Food Sci. Nutr. 2020, 60, 1048–1061. [Google Scholar] [CrossRef]
- Vijayakumar, V.; Balakrishnan, N. Artificial intelligence-based agriculture automated monitoring systems using WSN. J. Ambient Intell. Humaniz. Comput. 2021, 12, 8009–8016. [Google Scholar] [CrossRef]
- Jiang, Z.; Zhang, H.; Sutherland, J.W. Development of multi-criteria decision making model for remanufacturing technology portfolio selection. J. Clean. Prod. 2011, 19, 1939–1945. [Google Scholar] [CrossRef]
- Jadhav, A.S.; Sonar, R.M. Evaluating and selecting software packages: A review. Inf. Softw. Technol. 2009, 51, 555–563. [Google Scholar] [CrossRef]
- Finkenzeller, K. RFID Handbook Fundamentals and Applications in Contactless Smart Cards, Radio Frequency Identification and Near-Field Communication, 3rd ed.; John Wiley & Sons: West Sussex, UK, 2010; pp. 1–435. [Google Scholar]
- Musa, A.; Gunasekaran, A.; Yusuf, Y. Supply chain product visibility: Methods, systems and impacts. Expert Syst. Appl. 2014, 41, 176–194. [Google Scholar] [CrossRef]
- Tu, Y.J.; Zhou, W.; Piramuthu, S. Critical risk considerations in auto-ID security: Barcode vs. RFID. Decis. Support. Syst. 2021, 142, 113471. [Google Scholar] [CrossRef]
- Martínez-Sala, A.S.; Egea-López, E.; García-Sánchez, F.; García-Haro, J. Tracking of returnable packaging and transport units with active RFID in the grocery supply chain. Comput. Ind. 2009, 60, 161–171. [Google Scholar] [CrossRef] [Green Version]
- Qi, L.; Xu, M.; Fu, Z.; Mira, T.; Zhang, X. C2SLDS: A WSN-based perishable food shelf-life prediction and LSFO strategy decision support system in cold chain logistics. Food Control 2014, 38, 19–29. [Google Scholar] [CrossRef] [Green Version]
- Liu, Y.; Eckert, C.M.; Earl, C. A review of fuzzy AHP methods for decision-making with subjective judgements. Expert Syst. Appl. 2020, 161, 113738. [Google Scholar] [CrossRef]
- Hamzeh, R.; Xu, X. Technology selection methods and applications in manufacturing: A review from 1990 to 2017. Comput. Ind. Eng. 2019, 138, 106123. [Google Scholar] [CrossRef]
- Jahanshahloo, G.R.; Lotfi, F.H.; Izadikhah, M. Extension of the TOPSIS method for decision-making problems with fuzzy data. Appl. Math. Comput. 2006, 181, 1544–1551. [Google Scholar] [CrossRef]
- Saaty, T.L. Analytic hierarchy process. Wiley StatsRef Stat. Ref. Online 2014. [Google Scholar] [CrossRef]
- Ayça Erdoğan, S.; Kahraman, C.; Yasin Ateş, N.; Gülbay, M.; Çevik, S. Hierarchical fuzzy TOPSIS model for selection among logistics information technologies. J. Enterp. Inf. Manag. 2007, 20, 143–168. [Google Scholar] [CrossRef]
- Dinmohammadi, A.; Shafiee, M. Determination of the most suitable technology transfer strategy for wind turbines using an integrated AHP-TOPSIS decision model. Energies 2017, 10, 642. [Google Scholar] [CrossRef] [Green Version]
- Anand, M.B.; Vinodh, S. Application of fuzzy AHP–TOPSIS for ranking additive manufacturing processes for microfabrication. Rapid Prototyp. J. 2018, 24, 424–435. [Google Scholar] [CrossRef]
- Rajak, M.; Shaw, K. Evaluation and selection of mobile health (mHealth) applications using AHP and fuzzy TOPSIS. Technol. Soc. 2019, 59, 101186. [Google Scholar] [CrossRef]
- Zadeh, L.A. Fuzzy sets. In Fuzzy Sets, Fuzzy Logic, and Fuzzy Systems: Selected Papers by Lotfi A Zadeh; Klir, G.J., Yuan, B., Eds.; World Scientific: Singapore, 1996; Volume 6, pp. 394–432. [Google Scholar] [CrossRef]
- Mavrotas, G.; Diakoulaki, D.; Caloghirou, Y. Project prioritization under policy restrictions. A combination of MCDA with 0–1 programming. Eur. J. Oper. Res. 2006, 171, 296–308. [Google Scholar] [CrossRef]
- Tavana, M.; Keramatpour, M.; Santos-Arteaga, F.J.; Ghorbaniane, E. A fuzzy hybrid project portfolio selection method using data envelopment analysis, TOPSIS and integer programming. Expert Syst. Appl. 2015, 42, 8432–8444. [Google Scholar] [CrossRef]
- Kabli, M.R. A Multi-Attribute Decision Making Methodology for Selecting New R&D Projects Portfolio with a Case Study of Saudi Oil Refining Industry. Ph.D. Thesis, University of Nottingham, Nottingham, UK, 2009. [Google Scholar]
- Büyüközkan, G.; Karabulut, Y.; Arsenyan, J. RFID service provider selection: An integrated fuzzy MCDM approach. Measurement 2017, 112, 88–98. [Google Scholar] [CrossRef]
- Alibaba. Available online: www.alibaba.com (accessed on 1 March 2021).
- Amazon. Available online: www.amazon.co.uk (accessed on 1 March 2021).
- McCathie, L.; Michael, K. Is it the end of barcodes in supply chain management? In Proceedings of the Collaborative Electronic Commerce Technology and Research Conference LatAm, University of Talca, Talca, Chile, 3–5 October 2005; pp. 1–19. [Google Scholar]
- Senneset, G.; Forås, E.; Fremme, K.M. Challenges regarding implementation of electronic chain traceability. Br. Food J. 2007, 109, 805–818. [Google Scholar] [CrossRef]
- Fan, B.; Qian, J.; Wu, X.; Du, X.; Li, W.; Ji, Z.; Xin, X. Improving continuous traceability of food stuff by using barcode-RFID bidirectional transformation equipment: Two field experiments. Food Control 2019, 98, 449–456. [Google Scholar] [CrossRef]
- Erman Erkan, T.; Feryal Can, G. Selecting the best warehouse data collecting system by using AHP and FAHP methods. Teh. Vjesn. Tech. Gaz. 2014, 21, 87–93. [Google Scholar]
- D’Hont, S. The Cutting Edge of RFID Technology and Applications for Manufacturing and Distribution. Tex. Instrum. TIRIS 2004, 16, 1–13. Available online: http://idc-online.com/technical_references/pdfs/instrumentation/The%20Cutting%20Edge%20of%20RFID%20Technology.pdf (accessed on 15 March 2021).
- GS1. EAN/UPC Barcodes. Available online: https://www.gs1.org/standards/barcodes/ean-upc (accessed on 26 April 2021).
- Aroor, S.R.; Deavours, D.D. Evaluation of the state of passive UHF RFID: An experimental approach. IEEE Syst. J. 2007, 1, 168–176. [Google Scholar] [CrossRef]
- RFID4U. How to Select a Correct Tag—Frequency. Available online: https://rfid4u.com/rfid-frequency (accessed on 29 December 2020).
- Chawla, V.; Ha, D.S. An overview of passive RFID. IEEE Commun. Mag. 2007, 45, 11–17. [Google Scholar] [CrossRef]
- Impinj. Types of RFID Systems. Available online: https://www.impinj.com/products/technology/how-can-rfid-systems-be-categorized (accessed on 10 January 2021).
- ISO/IEC. ISO/IEC 18000-2:2009 Information Technology—Radio Frequency Identification for Item Management—Part 2: Parameters for Air Interface Communications Below 135 kHz. 2009. Available online: https://bsol.bsigroup.com/Bibliographic/BibliographicInfoData/000000000030273596 (accessed on 1 May 2021).
- GS1. EPC Tag Data Standard—Defines the Electronic Product CodeTM and Specifies the Memory Contents of Gen 2 RFID Tags. 2019. Available online: https://www.gs1.org/sites/default/files/docs/epc/GS1_EPC_TDS_i1_13.pdf (accessed on 26 April 2021).
- Costa, C.; Antonucci, F.; Pallottino, F.; Aguzzi, J.; Sarriá, D.; Menesatti, P. A review on agri-food supply chain traceability by means of RFID technology. Food Bioprocess. Technol. 2013, 6, 353–366. [Google Scholar] [CrossRef]
- Favre, R. Using Radio Frequency Identification (RFID) for Monitoring Trees in the Forest: State-of-the-Technology Investigation; United States Department of Agriculture (USDA): Washington, DC, USA, 2014; Report. Available online: https://www.fs.fed.us/t-d/pubs/pdfpubs/pdf14191805/pdf14191805dpi100.pdf (accessed on 24 May 2021).
- Feng, J.; Fu, Z.; Wang, Z.; Xu, M.; Zhang, X. Development and evaluation on a RFID-based traceability system for cattle/beef quality safety in China. Food Control 2013, 31, 314–325. [Google Scholar] [CrossRef]
- Abad, E.; Palacio, F.; Nuin, M.; De Zárate, A.G.; Juarros, A.; Gómez, J.M.; Marco, S. RFID smart tag for traceability and cold chain monitoring of foods: Demonstration in an intercontinental fresh fish logistic chain. J. Food Eng. 2009, 93, 394–399. [Google Scholar] [CrossRef]
- ISO/IEC. ISO/IEC 18000-3:2010 Information technology—Radio Frequency Identification for Item Management—Part 3: Parameters for Air Interface Communications at 13.56 MHz. 2010. Available online: https://bsol.bsigroup.com/Bibliographic/BibliographicInfoData/000000000030219362 (accessed on 1 May 2021).
- Tan, J.; Sathyamurthy, M.; Rolapp, A.; Gamez, J.; Hennig, E.; Schäfer, E.; Sommer, R. A Fully Passive RFID Temperature Sensor SoC With an Accuracy of ±0.4 °C (3σ) From 0 °C to 125 °C. IEEE J. Radio Freq. Identif. 2019, 3, 35–45. [Google Scholar] [CrossRef]
- Thakur, M.; Forås, E. EPCIS based online temperature monitoring and traceability in a cold meat chain. Comput. Electron. Agric. 2015, 117, 22–30. [Google Scholar] [CrossRef]
- Bukkapatnam, S.; Govardhan, J.M.; Hariharan, S.; Rajamani, V.; Gardner, B.; Contreras, A. Sensor (RFID) Networks and Complex Manufacturing Systems Monitoring (COMMSENS): Laboratory for RFID Research; Unpublished Research; Oklahoma State University: Stillwater, OK, USA, 2005; Available online: https://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.817.9444&rep=rep1&type=pdf (accessed on 15 February 2021).
- GS1. EPCTM Radio-Frequency Identity Protocols Generation-2 UHF RFID. 2015. Available online: https://www.gs1.org/sites/default/files/docs/epc/Gen2_Protocol_Standard.pdf (accessed on 26 April 2021).
- Blom, E.D.; Wan, J.; Urie, S.H.U.S. RFID Temperature Logger Incorporating a Frequency Ratio Digitizing Temperature Sensor. Patent No. 7,474,230, 6 January 2009. [Google Scholar]
- Islam, S.; Manning, L.; Cullen, J.M. Advances in traceability systems in agri-food supply chains. In Developing Smart Agri-Food Supply Chains: Using Technology to Improve Safety and Quality; Manning, L., Ed.; Burleigh Dodds Science Publishing Ltd.: Cambridge, UK, 2021. [Google Scholar]
- Hammervoll, T.; Jensen, L.M.; Hafliðason, T.; Ólafsdóttir, G.; Bogason, S.; Stefánsson, G. Criteria for temperature alerts in cod supply chains. Int. J. Phys. Distrib. Logist. Manag. 2012, 42, 355–371. [Google Scholar] [CrossRef]
- Crossbow Technology Datasheet. Crossbow’s TelosB Mote (TPR2400) Datasheet. Available online: https://www.willow.co.uk/TelosB_Datasheet.pdf (accessed on 3 March 2021).
- Wang, J.; Wang, H.; He, J.; Li, L.; Shen, M.; Tan, X.; Min, H.; Zheng, L. Wireless sensor network for real-time perishable food supply chain management. Comput. Electron. Agric. 2015, 110, 196–207. [Google Scholar] [CrossRef]
- Huang, V.; Javed, M.K. Semantic sensor information description and processing. In Proceedings of the Second International Conference on Sensor Technologies and Applications (Sensorcomm 2008), Cap Esterel, France, 25–31 August 2008; IEEE Computer Society: Washington, DC, USA, 2008; pp. 456–461. [Google Scholar] [CrossRef]
- Lee, C.C. Security and Privacy in Wireless Sensor Networks: Advances and Challenges. Sensors 2020, 20, 744. [Google Scholar] [CrossRef] [Green Version]
- Dobrucka, R.; Cierpiszewski, R. Active and intelligent packaging food-Research and development-A Review. Pol. J. Food Nutr. Sci. 2014, 64, 7–15. [Google Scholar] [CrossRef] [Green Version]
- Tan, J.; Koo, S.G. A survey of technologies in internet of things. In Proceedings of the 2014 IEEE International Conference on Distributed Computing in Sensor Systems, Marina Del Rey, CA, USA, 26–28 May 2014; IEEE: Piscataway, NJ, USA, 2014; pp. 269–274. [Google Scholar] [CrossRef]
- Zhang, X.; Zhang, J.; Liu, F.; Fu, Z.; Mu, W. Strengths and limitations on the operating mechanisms of traceability system in agro food, China. Food Control 2010, 21, 825–829. [Google Scholar] [CrossRef]
- Von Reischach, F.; Karpischek, S.; Adelmann, R.; Michahelles, F. Evaluation of 1D barcode scanning on mobile phones. In Proceedings of the 2010 Internet of Things (IOT), Tokyo, Japan, 29 November–1 December 2010; IEEE: Piscataway, NJ, USA, 2010; pp. 2–5. [Google Scholar] [CrossRef]
- Tec-IT. Barcode Overview. Available online: https://www.tec-it.com/en/support/knowbase/barcode-overview/linear/Default.aspx (accessed on 30 April 2021).
- Palmer, R.C. The Bar Code Book: Reading, Printing, and Specification of Bar Code Symbols, 3rd ed.; Helmers Publishing Inc.: Peterborough, NH, USA, 1989. [Google Scholar]
- ISO/IEC. ISO/IEC 15963:2009 Information Technology—Radio Frequency Identification for Item Management—Unique Identification for RF Tags. 2009. Available online: https://bsol.bsigroup.com/Bibliographic/BibliographicInfoData/000000000030273595 (accessed on 1 May 2021).
- Occhiuzzi, C.; Caizzone, S.; Marrocco, G. Passive UHF RFID antennas for sensing applications: Principles, methods, and classifications. IEEE Antennas Propag. Mag. 2013, 55, 14–34. [Google Scholar] [CrossRef] [Green Version]
- Vaz, A.; Ubarretxena, A.; Zalbide, I.; Pardo, D.; Solar, H.; Garcia-Alonso, A.; Berenguer, R. Full passive UHF tag with a temperature sensor suitable for human body temperature monitoring. IEEE Trans. Circuits Syst. II Express Briefs 2010, 57, 95–99. [Google Scholar] [CrossRef]
- Howard, J. Combination RFID and GPS Functionality on Intelligent Label. U.S. Patent No. 6,614,392, 2 September 2003. [Google Scholar]
- Mainetti, L.; Patrono, L.; Stefanizzi, M.L.; Vergallo, R. An innovative and low-cost gapless traceability system of fresh vegetable products using RF technologies and EPCglobal standard. Comput. Electron. Agric. 2013, 98, 146–157. [Google Scholar] [CrossRef]
- Trafton, A. Detecting Gases Wirelessly and Cheaply. Available online: https://news.mit.edu/2014/wireless-chemical-sensor-for-smartphone-1208 (accessed on 8 December 2014).
- Aung, M.M.; Chang, Y.S. Traceability in a food supply chain: Safety and quality perspectives. Food Control 2014, 39, 172–184. [Google Scholar] [CrossRef]
- Ruiz-Garcia, L.; Lunadei, L.; Barreiro, P.; Robla, I. A Review of Wireless Sensor Technologies and Applications in Agriculture and Food Industry: State of the Art and Current Trends. Sensors 2009, 9, 4728–4750. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Leenen, M.A.M.; Arning, V.; Thiem, H.; Steiger, J.; Anselmann, R. Printable electronics: Flexibility for the future. Phys. Status Solidi A 2009, 206, 588–597. [Google Scholar] [CrossRef]
- Fan, T.J.; Chang, X.Y.; Gu, C.H.; Yi, J.J.; Deng, S. Benefits of RFID technology for reducing inventory shrinkage. Int. J. Prod. Econ. 2014, 147, 659–665. [Google Scholar] [CrossRef]
- Ruiz-Garcia, L.; Lunadei, L. Monitoring cold chain logistics by means of RFID. In Sustainable Radio Frequency Identification Solutions; Turcu, C., Ed.; IntechOpen: London, UK, 2010; Volume 2, pp. 37–50. Available online: http://oa.upm.es/9615/1/Sustainable_RFID_Solutions.pdf (accessed on 4 April 2021).
- Qu, Z.; Sun, X.; Chen, X.; Yuan, S. A novel RFID multi-tag anti-collision protocol for dynamic vehicle identification. PLoS ONE 2019, 14, e0219344. [Google Scholar] [CrossRef]
- Karlsen, K.M.; Donnelly, K.A.M.; Olsen, P. Granularity and its importance for traceability in a farmed salmon supply chain. J. Food Eng. 2011, 102, 1–8. [Google Scholar] [CrossRef]
- Kumar, P.; Reinitz, H.W.; Simunovic, J.; Sandeep, K.P.; Franzon, P.D. Overview of RFID Technology and Its Applications in the Food Industry. J. Food Sci. 2009, 74, R101–R106. [Google Scholar] [CrossRef]
- ISO/IEC. ISO/IEC 18000-6:2013 Information Technology. Radio Frequency Identification for Item Management. 2013. Available online: https://bsol.bsigroup.com/Bibliographic/BibliographicInfoData/000000000030246358 (accessed on 1 May 2021).
- Chou, C.H.; Liang, G.S.; Chang, H.C. A fuzzy AHP approach based on the concept of possibility extent. Qual. Quant. 2013, 47, 1–14. [Google Scholar] [CrossRef]
- Chen, C.T.; Huang, S.F. Order-fulfillment ability analysis in the supply-chain system with fuzzy operation times. Int. J. Prod. Econ. 2006, 101, 185–193. [Google Scholar] [CrossRef]
- Mohammed, A.; Setchi, R.; Filip, M.; Harris, I.; Li, X. An integrated methodology for a sustainable two-stage supplier selection and order allocation problem. J. Clean. Prod. 2018, 192, 99–114. [Google Scholar] [CrossRef] [Green Version]
- Lupo, T.; Bellomo, E. DINESERV along with fuzzy hierarchical TOPSIS to support the best practices observation and service quality improvement in the restaurant context. Comput. Ind. Eng. 2019, 137, 106046. [Google Scholar] [CrossRef]
- Li, Q. A novel Likert scale based on fuzzy sets theory. Expert Syst. Appl. 2013, 40, 1609–1618. [Google Scholar] [CrossRef]
- Rana, R.L.; Tricase, C.; De Cesare, L. Blockchain technology for a sustainable agri-food supply chain. Br. Food J. 2021. [Google Scholar] [CrossRef]
- Violino, S.; Pallottino, F.; Sperandio, G.; Figorilli, S.; Antonucci, F.; Ioannoni, V.; Fappiano, D.; Costa, C. Are the innovative electronic labels for extra virgin olive oil sustainable, traceable, and accepted by consumers? Foods 2019, 8, 529. [Google Scholar] [CrossRef] [PubMed] [Green Version]
| Benefit | Overall Cost (C1) | Vulnerability to Water (C2) | Flexibility (C3) | Accuracy of Information (C4) | Reading Range (C5) | Data Transfer Speed (C6) | Multiple Tags Readability (C7) | Identification Capacity (C8) | Tag Writing Cycle (C9) | Memory Capacity (C10) | Environmental Parameters Recording (C11) | Real Time Location Recording (C12) | Real Time Alert (C13) | Durability of Data Carrier (C14) | World-Wide Standard (C15) | Data Security (C16) | Manual Data Readability (C17) | |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Technology | ||||||||||||||||||
| Paper based recording | More than barcode for no encoding [38,39] (Lowest) | Most susceptible to damage [8] (Highest) | High carrier weight for no encoding [40] (Lowest) | Least accurate for human error [41] (Lowest) | (Not applicable) | Slowest data transfer [40] (Negligible) | (Not applicable) | Item level unique identification (Highest) | (Not applicable) | (Not applicable) | (Not applicable) | (Certainly not) | (Certainly not) | Limited durability (Lowest) | No standardization [8] (Certainly not) | No encryption or password protection (Certainly not) | Manually readable (Highest) | |
| 1D Barcode | Encoding capacity and lowest carrier cost [38,39] (Between negligible and lowest) | Noticeable performance downturn [40] (Fair) | Light weight, printable and wearable tag [40] (Highest) | Minimum 80% accuracy for human error, line-of-sight and harsh environment [40] (Medium high to high) | Line-of-sight and close-contact reading up to 10 cm [42] (Lowest) | Line-of-sight and shortest reading distance causes around 4 s/read [20] (Low) | Read tag individually [43] (Certainly not) | Product class/SKU identification [40,44] (Fair) | Single writing tag [21] (Lowest) | 20–80 alphanumeric characters (Lowest) | (Certainly not) | (Certainly not) | (Certainly not) | Limited durability for environmental damage [22] (Lowest) | Global symbology standard [40,45] (Highest) | Simple encryption of data visible physically [22,46] (Low) | Manual readability by accompanied alphanumeric code [40] (Highest) | |
| 2D barcode | Encoding capacity with lowest carrier cost [38,39] (Between negligible and lowest) | Noticeable performance downturn [40] (Fair) | Light weight, printable and wearable tag [40] (Highest) | Minimum 80% accuracy for human error, line-of-sight, and harsh environment [40] (Medium high to high) | Line-of-sight and close-contact reading up to 10 cm [42] (Lowest) | Line-of-sight and shortest reading distance causes around 4 s/read [20] (Low) | Reads tag individually [43] (Certainly not) | Item level unique identification [40] (Highest) | Single writing tag [21] (Lowest) | 2335–4296 alphanumeric and ASCII characters (Medium high) | (Certainly not) | (Certainly not) | (Certainly not) | Limited durability for environmental damage [22] (Lowest) | Global standard for symbology [40,45] (Highest) | Deep encryption of data visible physically [42] (Fair) | No instant manual readability [40] (Certainly not) | |
| RFID passive LF read-only | Higher tag cost than HF and UHF for heavier antenna design [38,39] (Fair) | Waterproof [47] (Certainly not) | Heavier than HF, UHF RFID tags and barcodes [47,48] (Fair) | Most accurate for minimum human dependency and environment insensitivity [20] (Highest) | Non-line-of-sight and close contact reading between 1–10 cm [49] (Low) | Data transfer at 8 kb/s [50] (Between Low and medium low) | Reads tag individually [20] (Certainly not) | Item level unique identification [51] (Highest) | No writing capacity [52] (Certainly not) | 64–96b TID written by manufacturer (Low) | (Certainly not) | (Certainly not) | (Certainly not) | 10–20 years [53] (Highest) | ISO11784, ISO 11785, ISO/IEC 15963 [20] (Highest) | Binary encryption of data, invisible outside but low protection against unauthorized memory access [20] (Fair) | No instant manual readability [40] (Certainly not) | |
| RFID passive LF read-write | Higher tag cost than HF and UHF for heavier antenna design [38,39] (Fair) | Waterproof [47] (Certainly not) | Heavier than HF, UHF RFID tags and barcodes [47,48] (Fair) | Most accurate for minimum human dependency and environment insensitivity [20] (Highest) | Non-line-of-sight and close contact reading between 1–10 cm [49] (Low) | Data transfer at 8 kb/s [50] (Between Low and medium low) | Reads small number of tags at once [20] (Low) | Item level unique identification [51] (Highest) | Multiple writing tag [54] (Highest) | 128–256 b memory [38,39] (Medium Low) | (Certainly not) | (Certainly not) | (Certainly not) | 10–20 years [53] (Highest) | ISO/IEC 15963, ISO/IEC 14223, ISO/IEC 18000-2 [20] (Highest) | Binary encryption, password and cryptographic protection [20] (Highest) | No instant manual readability [40] (Certainly not) | |
| RFID passive HF read-only | Lower tag cost and higher reader cost than LF [38,39] (Fair) | Waterproof [47,55] (Certainly not) | Thinner than LF tags but thicker than UHF tags [47,48] (High) | Most accurate for minimum human dependency and environment insensitivity [20] (Highest) | Contactless reading between 10 cm–1 m [49] (Fair) | Data transfer at 105.9 kb/s [56] (Fair) | Reads more tags than LFsimultaneously [20] (Fair) | Item level unique identification [51] (Highest) | No writing capacity [52] (Certainly not) | 64–96 b TID written by manufacturer (Low) | (Certainly not) | (Certainly not) | (Certainly not) | 10–20 years [53] (Highest) | ISO/IEC 15963, ISO/IEC 15693, [20] (Highest) | Binary encrypted data, invisible outside but low protection against unauthorized memory access [20] (Fair) | No instant manual readability [40] (Certainly not) | |
| RFID passive HF read-write | Lower tag cost, and higher reader cost than LF [38,39] (Fair) | Waterproof [47,55] [Certainly not] | Thinner than LF tags but thicker than UHF tags [47,48] (High) | Most accurate for minimum human dependency and environment insensitivity [20] (Highest) | Contactless reading between 10 cm–1 m [49] (Fair) | Data transfer at 105.9 kb/s [56] (Fair) | Reads more tags than LFsimultaneously [20] (Fair) | Item level unique identification [51] (Highest) | Multiple writing tag [54] (Highest) | 256–1024 b [38,39] (Fair) | (Certainly not) | (Certainly not) | (Certainly not) | 10–20 years [53] (Highest) | ISO/IEC 15963, ISO/IEC 15693, ISO/IEC 18000-3 [20] (Highest) | Binary encryption, password and cryptographic protection [20] (Highest) | No instant manual readability [40] (Certainly not) | |
| RFID passive HF with sensor | Lower tag cost, and higher reader cost than LF [38,39] (Fair) | Waterproof [47,55] (Certainly not) | Thinner than LF tags but thicker than UHF tags [47,48] (High) | Most accurate for minimum human dependency and environment insensitivity [20] (Highest) | Reading range impaired by onboard sensor [20] (Low) | Data transfer at 105.9 kb/s [56] (Fair) | Reads more tags than LFsimultaneously [56] (Fair) | Item level unique identification [33,51] (Highest) | Multiple writing tag [54] (Highest) | 256–1024 b [38,39] (Fair) | Records only when powered by reader [57,58] Fair) | (Certainly not) | (Certainly not) | 10–20 years [53] (Highest) | ISO/IEC 15963, ISO/IEC 15693, ISO/IEC 18000-3 [20] (Highest) | Binary encryption, password and cryptographic protection [20] (Highest) | No instant manual readability [40] (Certainly not) | |
| RFID passive UHF read only | Higher reader cost than HF and LF [38,39] (Medium high) | Affects readability [55,59] (Between medium high and high) | Thinner than HF tags [47,48] (Highest) | Most accurate for minimum human dependency and environment insensitivity [20] (Highest) | Contactless reading between 3 cm–9 m [47] (High) | Data transfer at 40–640 kb/s [60] (Medium high to high) | Reads more tags than HFsimultaneously [20] (Between medium high and high) | Item level unique identification [51] (Highest) | No writing capacity [52] (Certainly not) | 64–96 b TID written by manufacturer (Low) | (Certainly not) | (Certainly not) | (Certainly not) | 10–20 years [53] (Highest) | ISO/IEC 15963, ISO/IEC 18000-6, EPC gen2 UHF protocol [20] (Highest) | Binary encrypted data, invisible outside but low protection against unauthorized memory access [20] (Fair) | No instant manual readability [20] (Certainly not) | |
| RFID passive UHF read-write | Higher reader cost than HF and LF [38,39] (Medium high) | Affects readability [55,59] (Between medium high and high) | Thinner than HF tags [47,48] (Highest) | Most accurate for minimum human dependency and environment insensitivity [20] (Highest) | Contactless reading between 3 cm–9 m [47] (High) | Data transfer at 40–640 kb/s [60] (Medium high to high) | Reads more tags than HFsimultaneously [20] (Between medium high and high) | Item level unique identification [51] (Highest) | Multiple writing tag [54] (Highest) | 256 b–8 kb [38,39] (Medium high) | (Certainly not) | (Certainly not) | (Certainly not) | 10–20 years [53] (Highest) | ISO/IEC 15963, ISO/IEC 18000-6C, EPC gen2 UHF protocol [20] (Highest) | Binary encryption, password and cryptographic protection [20] (Highest) | No instant manual readability [40] (Certainly not) | |
| RFID passive UHF read write with sensor | Higher reader cost than HF and LF [38,39] (Medium high) | Affects readability [55,59] (Between medium high and high) | Thinner than HF tags [47,48] (Highest) | Most accurate for minimum human dependency and environment insensitivity [20] (Highest) | Reading range impaired by onboard sensor [20] (Fair) | Data transfer at 40–640 kb/s [60] (Medium high to high) | Reads more tags than HFsimultaneously [20] (Between medium high and high) | Item level unique identification [51] (Highest) | Multiple writing tag [54] (Highest) | 256 b–8 kb [38,39] (Medium high) | Records only when powered by reader [57,58] (Fair) | (Certainly not) | (Certainly not) | 10–20 years [53] (Highest) | ISO/IEC 15963, ISO/IEC 18000-6C, EPC gen2 UHF protocol [20] (Highest) | Binary encryption, password and cryptographic protection [20] (Highest) | No instant manual readability [40] (Certainly not) | |
| Semi passive RFID | Higher tag cost than UHF due to battery [38,39] (Between high and highest) | Affects readability [55,59] (Between medium high and high) | Heavier than passive LF due to onboard battery [8,47] (Low) | Most accurate for minimum human dependency and environment insensitivity [20] (Highest) | Contactless reading between 3 cm–15 m [20] (High) | Larger reading speed than UHF due to battery [20] (High) | Reads more tags than HFsimultaneously [20] (Between medium high and high) | Item level unique identification [51] (Highest) | Multiple writing tag [20] (Highest) | Up to 20 kb [38,39] (High) | Real time recording of product physical data with onboard battery [61] (Highest) | Real time recording of location with onboard battery and sensor [8] (Highest) | Connect alert module with onboard battery [8] (Highest) | 2–7 years for limited battery life [20] (Fair to medium high) | ISO/IEC 15963, ISO/IEC 18000-6 [20] (Highest) | Binary encryption, password and cryptographic protection [20] (Highest) | No instant manual readability [40] (Certainly not) | |
| Active RFID | Higher tag cost than semi passive due to transmitter [38,39] (Highest) | Waterproof [59] (Certainly not) | Heaviest tag with onboard battery and transceiver [47] (Certainly not) | Most accurate for minimum human dependency and environment insensitivity [20] (Highest) | Contactless reading up to 100 m [49] (Highest) | Maximum read speed for high frequency, battery, and transceiver [20] (Highest) | Reads maximum number of tags simultaneously as tags include own batteries and transceivers (Highest) | Item level unique identification [51] (Highest) | Multiple writing tag [54] (Highest) | More than 20 kb [38,39] (Highest) | Real time recording of product physical data with onboard battery [23] (Highest) | Real time recording of location with onboard battery and sensor [8] (Highest) | Connects alert module with onboard battery [8] (Highest) | 2–7 years for limited battery life [20] (Fair to medium high) | ISO/IEC 15963 [20] (Highest) | Binary encryption, password and cryptographic protection [20] (Highest) | No instant manual readability [40] (Certainly not) | |
| NFC | No additional reader cost as smartphone reading is possible [38,39] (Low) | Waterproof [47,55] (Certainly not) | Thinner than LF tags [47,48] (High) | Most accurate for minimum human dependency and environment insensitivity [20] (Highest) | Contactless reading between 1–3 cm (Low) | Data transfer at 105.9 kb/s [56] (Fair) | Reads multiple tagssimultaneously as HF RFID [20] (Fair) | Item level unique identification [51] (Highest) | Multiple writing tag [62] (Highest) | 256–1024 b [38,39] (Fair) | (Certainly not) | (Certainly not) | (Certainly not) | 10–20 years [53] (Highest) | ISO14443A, ISO/IEC 18000-3 [20] (Highest) | Binary encryption, password and cryptographic protection [20] (Highest) | No instant manual readability [40] (Certainly not) | |
| WSN | Highest cost as a node comprising multiple components [38,39] (Highest) | Waterproof [8] (Certainly not) | Heaviest node consisting of several components [8] (Certainly not) | Can be as high as ±0.5 °C for temperature sensors [63] (Highest) | Contactless reading up to 100 m [64] (Highest) | Data transfer at 250 kb/s [64] (Between fair and medium high) | (Not applicable) | (Not applicable) | (Not applicable) | Limited memory capacity [63] (Low) | Real time recording of product physical data with onboard battery [65] (Highest) | Real time recording of location with onboard battery and sensor [8] (Highest) | Includes real time alert module [63] (Highest) | 2–7 years for limited battery life [8] (Fair to medium high) | IEEE 802.15.4 Zigbee protocol and computer readable data standard [62,66] (Highest) | Password and cryptographic protection against unauthorized access [67] (Highest) | No instant manual readability [24] (Certainly not) | |
| Smart packaging indicator | High cost due to absence of reuse capability [38,39] (High) | Waterproof [63] (Certainly not) | Light weight, printable and wearable [8] (Highest) | Can be as high as ±0.5 °C for TTIs [63] (Highest) | (Not applicable) | Slowest manual data transfer [63] (Negligible) | (Not applicable) | (Not applicable) | (Not applicable) | Records full temperature history [68] (Highest) | Records environmental parameters with own battery [13] (Highest) | (Certainly not) | Can emit a signal in response to any change [13] (Highest) | Single use only [8] (Lowest) | No technical or data standard [24] (Certainly not) | No encryption or password protection [8] (Certainly not) | Manual readability [24] (Highest) | |
| Saaty’s Scale | Linguistic Term | Fuzzy Number |
|---|---|---|
| 1 | Equally important | (1, 1, 1) |
| 2 | Between equally and weakly important | (1, 2, 3) |
| 3 | Weakly important | (2, 3, 4) |
| 4 | Between weakly and fairly important | (3, 4, 5) |
| 5 | Fairly important | (4, 5, 6) |
| 6 | Between fairly and strongly important | (5, 6, 7) |
| 7 | Strongly important | (6, 7, 8) |
| 8 | Between strongly and absolutely important | (7, 8, 9) |
| 9 | Absolutely important | (9, 9, 9) |
| Linguistic Term | Fuzzy Number |
|---|---|
| Certainly not/negligible/not applicable | (0.0, 0.0, 0.0) |
| Lowest | (0.0, 0.1, 0.2) |
| Low | (0.1, 0.2, 0.3) |
| Medium low | (0.2, 0.3, 0.4) |
| Fair | (0.3, 0.5, 0.7) |
| Medium high | (0.5, 0.7, 0.8) |
| High | (0.7, 0.8, 0.9) |
| Highest | (0.8, 0.9, 1.0) |
| Criteria | C4 | C5 | C6 | C8 | C11 | C15 | C16 | C10 | C9 | C1 |
|---|---|---|---|---|---|---|---|---|---|---|
| C4 | (1, 1, 1) | (0.14, 0.17, 0.2) | (0.18, 0.22, 0.29) | (0.16, 0.19, 0.24) | (0.14, 0.17, 0.20) | (1, 2, 3) | (2.45, 3.46, 4.47) | (0.29, 0.41, 0.71) | (0.29, 0.41, 0.71) | (2.45, 3.46, 4.47) |
| C5 | (5, 6, 7) | (1, 1, 1) | (1.41, 2.45, 3.46) | (0.82, 1.23, 2) | (0.58, 1, 1.7) | (6, 7, 8) | (7.94, 8.49, 9) | (3.46, 4.47, 5.48) | (3.46, 4.47, 5.48) | (7.94, 8.49, 9) |
| C6 | (3.46, 4.47, 5.48) | (0.29, 0.41, 0.71) | (1, 1, 1) | (0.45, 0.71, 1) | (0.29, 0.41, 0.71) | (4.47, 5.48, 6.48) | (6, 7, 8) | (2, 3, 4) | (1.73, 2.83, 3.87) | (5.92, 6.93, 7.94) |
| C8 | (4.24, 5.29, 6.33) | (0.50, 0.82, 1.22) | (1, 1.41, 2.24) | (1, 1, 1) | (0.63, 0.87, 1.16) | (5.29, 6.33, 7.35) | (6.71, 7.35, 7.94) | (2.24, 3.46, 4.58) | (2.83, 3.87, 4.90) | (6.48, 7.48, 8.49) |
| C11 | (4.90, 5.92, 6.93) | (0.58, 1, 1.73) | (1.41, 2.45, 3.46) | (0.87, 1.16, 1.58) | (1, 1, 1) | (5.92, 6.93, 7.94) | (7.94, 8.49, 9) | (3.46, 4.47, 5.48) | (3.16, 4.24, 5.29) | (7.35, 7.94, 8.49) |
| C15 | (0.33, 0.50, 1) | (0.13, 0.14, 0.17) | (0.15, 0.18, 0.22) | (0.14, 0.16, 0.19) | (0.13, 0.14, 0.17) | (1, 1, 1) | (1.41, 2.45, 3.46) | (0.22, 0.29, 0.41) | (0.22, 0.29, 0.41) | (1.41, 2.45, 3.46) |
| C16 | (0.22, 0.29, 0.41) | (0.11, 0.12, 0.13) | (0.13, 0.14, 0.17) | (0.13, 0.14, 0.15) | (0.11, 0.12, 0.13) | (0.29, 0.41, 0.71) | (1, 1, 1) | (0.17, 0.20, 0.25) | (0.17, 0.20, 0.26) | (0.58, 1, 1.73) |
| C10 | (1.41, 2.45, 3.46) | (0.18, 0.22, 0.29) | (0.25, 0.33, 0.50) | (0.22, 0.29, 0.45) | (0.18, 0.22, 0.29) | (2.45, 3.46, 4.47) | (4, 5, 6) | (1, 1, 1) | (0.577, 1, 1.732) | (3.873, 4.899, 5.916) |
| C9 | (1.414, 2.449, 3.464) | (0.183, 0.224, 0.289) | (0.258, 0.354, 0.577) | (0.204, 0.258, 0.354) | (0.189, 0.236, 0.316) | (2.449, 3.464, 4.472) | (3.873, 4.899, 5.916) | (0.577, 1, 1.732) | (1, 1, 1) | (4, 5, 6) |
| C1 | (0.223, 0.289, 0.408) | (0.111, 0.118, 0.126) | (0.126, 0.144, 0.169) | (0.118, 0.134, 0.154) | (0.118, 0.126, 0.136) | (0.289, 0.408, 0.707) | (0.577, 1, 1.732) | (0.169, 0.204, 0.258) | (0.167, 0.200, 0.250) | (1, 1, 1) |
| Score | |||
|---|---|---|---|
| Technologies | |||
| 1D barcode | 0.194035 | 1 | |
| Paper-based records | 0.244571 | 2 | |
| 2D barcode | 0.292840 | 4 | |
| RFID passive LF read-only | 0.300240 | 8 | |
| RFID passive LF read-write | 0.323311 | 16 | |
| NFC | 0.355787 | 32 | |
| RFID passive HF read-only | 0.407741 | 64 | |
| RFID passive HF read-write | 0.430721 | 128 | |
| Smart packaging indicator | 0.456266 | 256 | |
| RFID passive HF with sensor | 0.497800 | 512 | |
| RFID passive UHF read only | 0.503904 | 1024 | |
| RFID passive UHF read-write | 0.525985 | 2048 | |
| RFID passive UHF read-write with sensor | 0.631567 | 4096 | |
| WSN | 0.694005 | 8192 | |
| Semi-passive RFID | 0.916533 | 16384 | |
| Active RFID | 0.962911 | 32768 | |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Islam, S.; Manning, L.; Cullen, J.M. A Hybrid Traceability Technology Selection Approach for Sustainable Food Supply Chains. Sustainability 2021, 13, 9385. https://doi.org/10.3390/su13169385
Islam S, Manning L, Cullen JM. A Hybrid Traceability Technology Selection Approach for Sustainable Food Supply Chains. Sustainability. 2021; 13(16):9385. https://doi.org/10.3390/su13169385
Chicago/Turabian StyleIslam, Samantha, Louise Manning, and Jonathan M. Cullen. 2021. "A Hybrid Traceability Technology Selection Approach for Sustainable Food Supply Chains" Sustainability 13, no. 16: 9385. https://doi.org/10.3390/su13169385
APA StyleIslam, S., Manning, L., & Cullen, J. M. (2021). A Hybrid Traceability Technology Selection Approach for Sustainable Food Supply Chains. Sustainability, 13(16), 9385. https://doi.org/10.3390/su13169385






