2.1. Research of the Concept of CII
In the last decade, critical infrastructure study has been directed based on interdependencies from various points. The research is mainly concerned with policies in this field [
36,
37]. Risk analyses and comments into the existing legal framework have been described in [
38,
39]. The interdependent essential infrastructures are presented in [
40,
41,
42,
43,
44]. These works are mainly focused on engineering or computer science, to design better modeling, in order to manage the infrastructure, as well as to protect the vital infrastructure [
45,
46].
As indicated in the Directive [
47], essential infrastructure is a system, asset, or part thereof that is situated in countries, and that is very important for the control of critical societal functions and safety, etc., and the failure or breakdown of which would have a great influence on a country; as consequence of an error in keeping up those functions.
The trends and current geopolitical and geostrategic perspectives expand more and more the concept of “national security” for environmental, financial, information technology and communication, and diplomatic components. Essential infrastructures are usually sensitive to the actions of some internal or external attributes, and they are under a risk of being destroyed or made non-operational [
48].
The European Union and other countries use different definitions of critical infrastructure. According to the law of the Republic of Lithuania, CII are electronic communication networks or parts of an information system or a component of a complex of information systems, or a process control system, or part of it, a cyber-incident of which can cause significant damage to national security, state economy and public interests [
49]. France notes that vital infrastructure is the structure or equipment that provides critical goods and services in the formation of a society and its lifestyle [
50]. The Slovenian national importance of critical infrastructure includes its necessary capabilities and services, the violation of which will have a huge influence on national security, essential social or financial operations, safety, and social security [
51]. According to the Canadian National Strategy for Critical Infrastructure, critical infrastructure refers to processes, technologies, etc., that are necessary for the health, safety, or economic well-being of the population, and the impactful operation of a country [
52].
Based on relevant state concepts, it can be said that each country has its own perception of critical infrastructure. Identifying critical infrastructure is not sufficient to just rely on the definition. To achieve this goal, various methods and techniques should be used. In this case, the problem of CII identification was solved by applying the MCDM approach.
2.2. Achieving the Sustainability of CII, and Potential Threats to CII
Currently, the problem of natural disasters is considered to be one of the most pressing. In recent years, there have been significant changes in views on the sustainable state and development of natural systems. This is also interrelated with the intensive development of scientific and technical (information technology (IT)) and economic potential, and the industrial development of new territories. Often the cause of environmental disasters and devastating consequences lies in the failure of a critical information resource. For example, a failure in the refining industry may cause tens or hundreds of thousands of tons of crude oil or fuel oil to be released into the marine environment. Such an accident has enormous losses, which are very difficult to estimate due to its magnitude. Accordingly, knowledge of the criticality of information infrastructures that affect natural disasters, the timely development of precautionary measures, and the restoration of destroyed territories and their socio-economic systems and ecosystems is an essential attribute for the sustainable development of systems at various levels of EU countries.
Globalization, rapid technological change, and other factors change the global security situation, and expand the list of traditional threats [
53,
54,
55]. A new type of risk has appeared, such as terrorist attacks, cyber-attacks, cyber wars, etc. [
56,
57,
58].
When the distributed denial-of-service (DDoS) attacks on Lithuanian websites began in 2003. Lithuania recognized that the threat of cyber-attacks is real [
59]. It should be noted that by the end of 2016, a list of CII of Lithuania was approved [
60]. Other countries have also previously faced cyber threats towards the critical infrastructure. In 2007, Estonia suffered greatly from politically motivated cyber-attacks (the first cyberwar) [
61].
In recent years, companies of all types, including those offering critical and emergency services, have been the victims of social engineering attacks [
62]. The last most infamous type of cyber threat was the WannaCry ransomware, which was one of the most impactful and propagated malware in 2017. This international wave of cyber threats is reported to have struck over 150 countries worldwide [
63]. These events have increased the awareness of potential threats towards critical infrastructure that potentially endanger national security. States began to realize that new types of threats could be directed against national critical infrastructures. This infrastructure is the most sensitive and vulnerable infrastructure, which can entail a huge impact on the state and its environment.
Critical infrastructure plays the main role in countries in with regard to the importance of nationwide, socio-economic, or public security [
64]. Potential threats to the critical infrastructure of its countries prompted the EU Member State to take measures to protect the essential infrastructure each country. Identifying essential infrastructure is the first step toward protect the country and the interests of people who depend on critically crucial services. Accurately defining critical infrastructure can defend them against potential threats.
The following characteristics must be considered:
types of threats;
threat objects;
sources of threats.
The main types of threats directed towards sustainability include the violation of the accessibility, integrity, and confidentiality of information.
The objects, which are usually influential to CII work, can be represented as a network, an information or automated system, a process control system, etc.
The sources of key threats affecting the reliability of CII can be of two types:
External (computer hackers (competitors), carrying out targeted destructive effects, including using computer viruses and other types of malicious codes (human-made, external), terrorists, criminal elements and structures);
Internal (employees of an organization who are legal participants in information processing and acting outside their authority; employees of an organization who are legitimate participants in information processing and operating within their jurisdiction);
Common acting of external and internal threats with the aim of affecting CII.
The consequences of the threats can be catastrophic, so that it is essential to take all possible actions to protect and ensure the operation of CII.
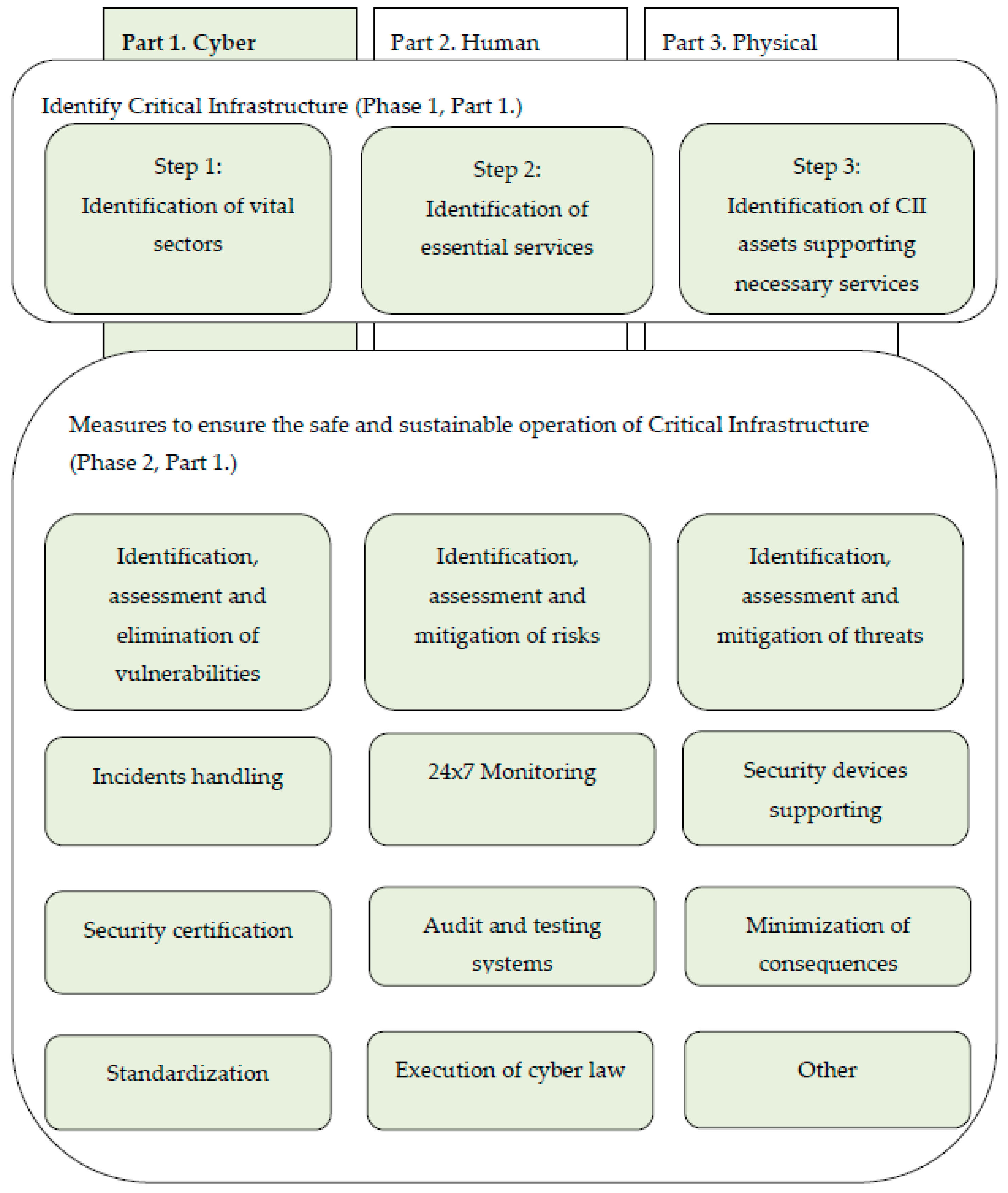
Figure 1 shows one of the options that are proposed by the authors for providing the process of sustainable functioning of CII.
As can be seen from
Figure 1, the identification of CII is the first phase to protect critical infrastructure. Various methods can be used to identify CII.
2.3. CII Identification Models
Various models and methodologies, which were proposed earlier by other researchers and governments, are considered in this paper.
The article by Almeida on the identification of critical infrastructure offers a multi-criteria evaluation model [
66]. In the Canadian Critical Infrastructure Assessment Model, Macbeth is proposed to solve the problem, using M-MACBETH software. This method was chosen because it has a social-technical approach to development problems, and it is more convenient for decision-makers. The proposed Macbeth model is improved by the Canadian model, but this is only a theoretical model that has not been tested in practice, and the adequacy of real applicability is not evaluated [
66]. Despite this, there are a large number of scientific articles that offer other methods.
Applying the AHP method for a multi-criteria task in determining the level of criticality of the water management system is proposed in [
67]. This area is an important sector for all countries, and it is critical infrastructure. The goal is to identify and develop the criteria, and a list of items that will be used to identify the properties of the critical level. The AHP method is the MCDM approach that can help a decision-taker, met with the difficult issue of a multitude of criteria [
68]. AHP is an effective tool that can speed up the decision-making process. It is one of the most popular methods with a comprehensive, logical and structured system. Thus, this method was useful in analyzing quantitative information in the water supply industry, and the effectiveness of water management [
67].
Izuakor and White [
69] continued the analysis of the methods used in relation to critical infrastructures. After research, the novel method to identify essential infrastructure was proposed, and further study in this area is suggested using several criteria of decision theory.
The countries of the European Union apply the Critical service-dependent method, which identifies the most important services. Based on these services, they are trying to identify objects or other assets that belong to the CII. This method consists of three steps, which are shown in
Figure 1 [
63].
The goal of most of the methods is to determine the essential resources on which governments depend, and tp guarantee that they are adequately detecting faults.
Currently, there are more than 220 identified operators of critical infrastructure. In turn, 1000 critical resources are identified [
70].
The different methods to identify CII could be applied. Each of the discussed methods has its advantages and disadvantages, but the government chooses the most appropriate method, taking into account their national characteristics.
The identified critical sectors and subsectors services are shown in
Table 1 [
65].
The European Commission provides a brief of 11 essential areas: energy; information and communication technologies; water; food; health; financial public order and safety; civil administration; transport; chemical and nuclear industry; space and research [
70].
To identify the objects of CII supporting critical services it is essential to determine the main factors that allow determining the degree of influence (
Table 2) [
65].
An important criterion is an impact on the population, which indicates the number of people affected, health problems, heavy injuries, etc. Equally important is the economic impact, which reflects the impact on Gross domestic product GDP, the importance of economic losses, as well as products and the deterioration of service quality. Environmental impact testing indicates an impact on a person and the surrounding landscape and takes the main part in assessing the importance of infrastructure. Infrastructure assessment should take into account the interdependence of criteria that show a certain dependence on infrastructure with another critical infrastructure. It may also be subject to political criteria that reflect confidence in the ability of the government [
72]. The European Union has, in particular, estimated the destruction of infrastructure or the severity of the consequences of its destruction, based on six criteria: impact on society, economic consequences, environmental effects, political effects, psychological effects, consequences for public health.
Some criteria for the sectoral and sub-sectoral assessment of the Lithuanian critical infrastructure are presented in
Table 3. These criteria indicate the level of impact of the destruction of the particular sector, the object of the subsector, or its inability to manage critical services.
The work is not limited to the criteria for evaluating the sectoral or sub-sectoral criteria. In addition, criteria are included that indicate the significance of the impact of the destruction or damage to the object.
To apply the methodology of the Lithuanian government, the problem of CII identification was solved for three objects. Since the assessment of the critical infrastructure was not publicly available, and this data was not available, the table would be filled with random numbers in the range, from 0 to 3 points. The studied objects provided services for air transport, road transport, rail transport, sea transport, postal subsectors, so the weight of the first criterion was 1. Other results are presented in
Table 4.
The number of objects is not limited, but in the example, there are three objects.
The weighted sum method (WSM) is used to calculate the estimates. The results obtained are: Object 1 and Object 2 have 15 scores, and Object 3 has 18 scores. Thus, object 3 has the highest priority, while object 1 and object 2 both share the second priority position. It is impossible to determine which of these objects is more significant, since the importance of the two objects is the same.
Having determined that the WSM method that is used in the above-mentioned method of identifying a CII is currently inappropriate, another MCDM method is further discussed. A methodology should be used to better define the CII, and to solve the problems of the applied WSM model. The use of points from 0 to 3 must be replaced with new ones.
Researchers have proposed different methods for define subjective or objective weights of criteria. The basic idea of assessing the significance of the criterion is that the most critical criterion gains the biggest weight.
An integrated definition of the objective significance of a criterion in the MCDM method is proposed in [
74]. In practice, usually, a subjective weight is used, determined by professionals or experts. Many methods have been developed to identify the criteria weights in terms of experts’ assessment of the importance (weights). The most widely used approaches include the Delphi [
75], the expert judgment [
76], the Analytic Hierarchy Process (AHP) [
77,
78], the Analytic Network Process, Step-wise weight assessment ratio analysis method (SWARA) [
79], and others. For example, criteria weights are determined by applying the AHP method: the weights of the criteria are calculated based on Saaty’s judgment scale and the new original scale, as presented by the authors. The ARAS (Additive Ratio Assessment) method (the MCDM approach) is applied, to solve the problem under investigation. The developed assessment method involves the Leadership in Energy and Environmental Design (LEED) system’s criteria [
80].
During the evaluation process, the criteria values, and the degree of domination of each criterion, i.e., the objective weight criteria, could be considered. Unlike their subjective analogues, the objective weights are rarely used in practice. The Entropy method [
81,
82,
83], the LINMAP method [
84], the correlation coefficient, and the standard deviation based on the objective value determination method [
85], and the prediction algorithm [
86] are practical methods that are often used. Combined weighing is based on the integration of both objective and subjective judgments [
87,
88].
In our case, according to [
89], the fuzzy WASPAS method was chosen.
2.4. An MCDM Process to Identify CII
This article presents an MCDM-based model of the applicability of the MCDM method for determining CII.
One of the main stages to determine CII is the design of a mathematical model consisting of:
a choice of essential variables;
drawing up restrictions, which are satisfied by variables;
a compilation of the objective function, which reflects the critical criteria for selecting the assignment of an object to a vital one.
The solution of the problem depends on the set of criteria for classifying objects as critical, as well as on their significance.
The task of classifying an information object is complicated by the presence of incomparable values of criteria, since particular criteria respectively have different units of measure, their scales are not comparable, and therefore, comparing the results that are obtained for each criterion is difficult.
Besides, the scales must be reduced and dimensionless—normalized values of criteria are used. Formally, describing the principle of optimality (the criteria of “correctness of the solution”) is difficult, due to the following reasons:
The objects considered by the theory of decision-making are so diverse that it is difficult to establish uniform principles of optimality for all classes of problems.
The goals of the decision-making stakeholders are different and often opposite.
The criteria for the correctness of the decision depend on the nature of the task, its goals, etc., and also on how correctly they were chosen for a particular country.
The difficulties in selecting a solution may be hidden in the specific formulation of the problem, if unrealistic results are required.
Alternative objects are characterized by the correctness of the definition of vital criteria and their significances. They have essential meaning. This is possible, by establishing the criticality of information objects and the priority of the compared options. Using international experience and expert assessments, as well as information sources, the values of the criteria are determined [
73].
In this paper, the MCDM method performs the following functions:
The identification of CII among the available information objects;
The comparison of CII, and the formation of a comparative table.
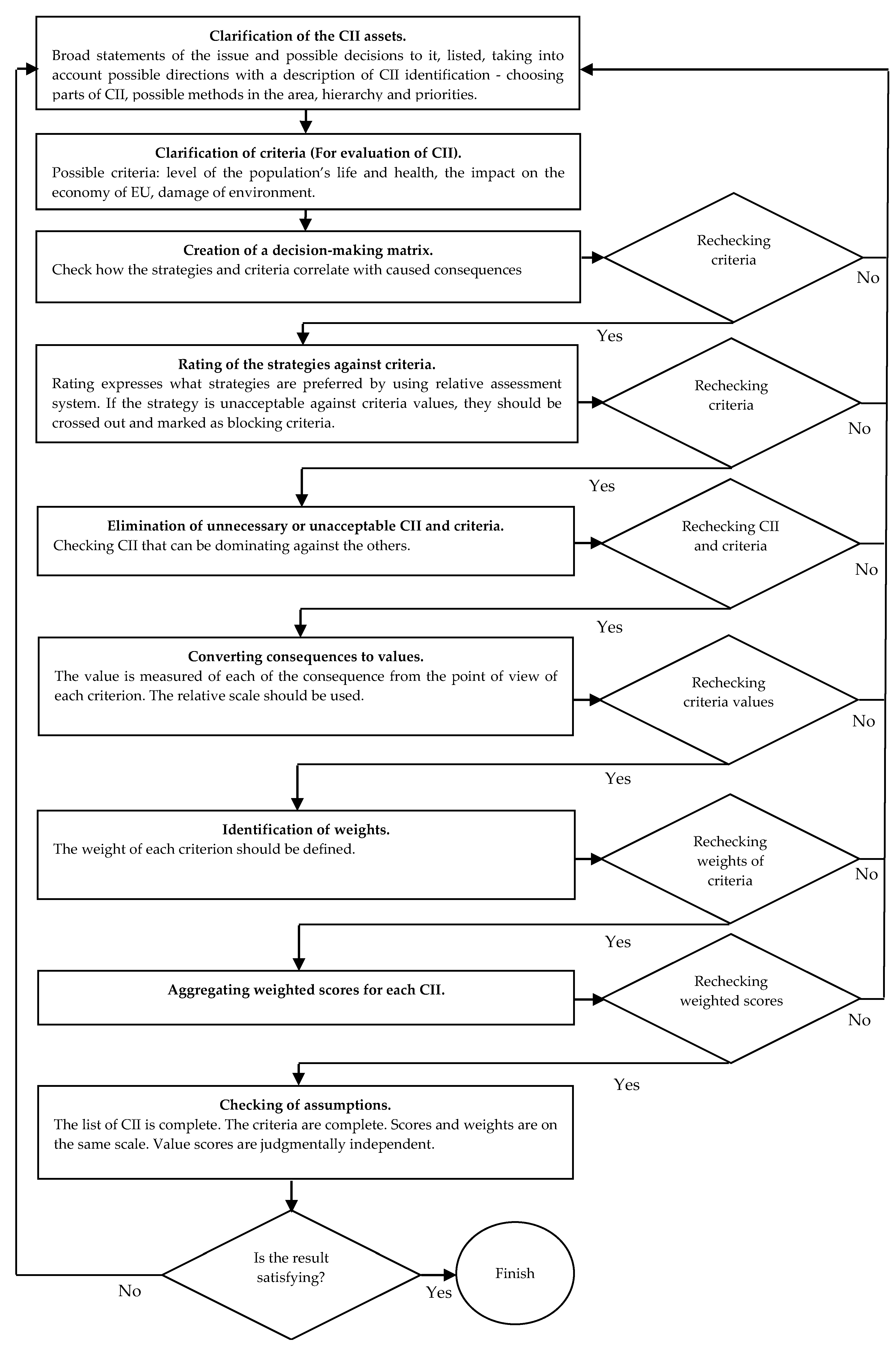
The proposed model and the stages identified for the method for the CII identification structure are shown in
Figure 2.
The procedure should concentrate on an essentially imperative task: to identify the decision-taker, and to differentiate it from the issue analysis. Various variants are possible for the criteria optimization, as well as synthesizing all criteria into one criterion of defining the optimum. The criteria are exceedingly conditioned, with the priorities and critical assets being identified. The criteria for the CII evaluation should be identified with a focus on country-critical services. The main stage in forming the criteria involves choosing the basic criteria for CII identification that can be divided into sub-criteria during the procedure. This could be the criteria for the life and health of the population, the criteria for the impact on the economy of the country, the criteria for environmental damage, etc. Criteria groups have various influences on significance.
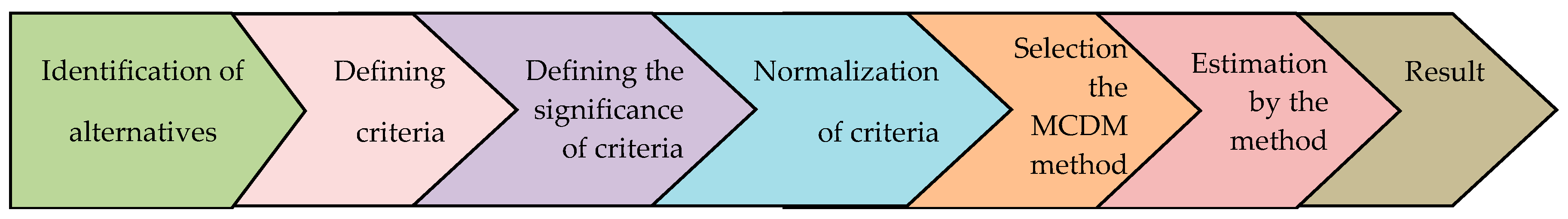
To form the steps of the MCDM method of CII, we use the model described in the article [
90].
Another model, which is used for identifying CII by the MCDM method, is shown in
Figure 3.
There are several cases in which different MCDM approaches have various decisions. It might be explained because of the various mathematical artefacts that are used by different MCDM methods. However, the issue of applying a convenient MCDM approach in a specific case still exists. The choice of MCDM methods based on various parameters has already been studied by earlier researchers in [
91]. When a particular MCDM method is finally recommended for a particular application, it is observed that its decision accuracy and ranking efficiency strongly depends on the value of its control parameter [
92].
The most suitable solution of a problem in different areas, considering a number of criteria, such as environment, engineering, finance, etc., is the use of the MCDM method [
67].
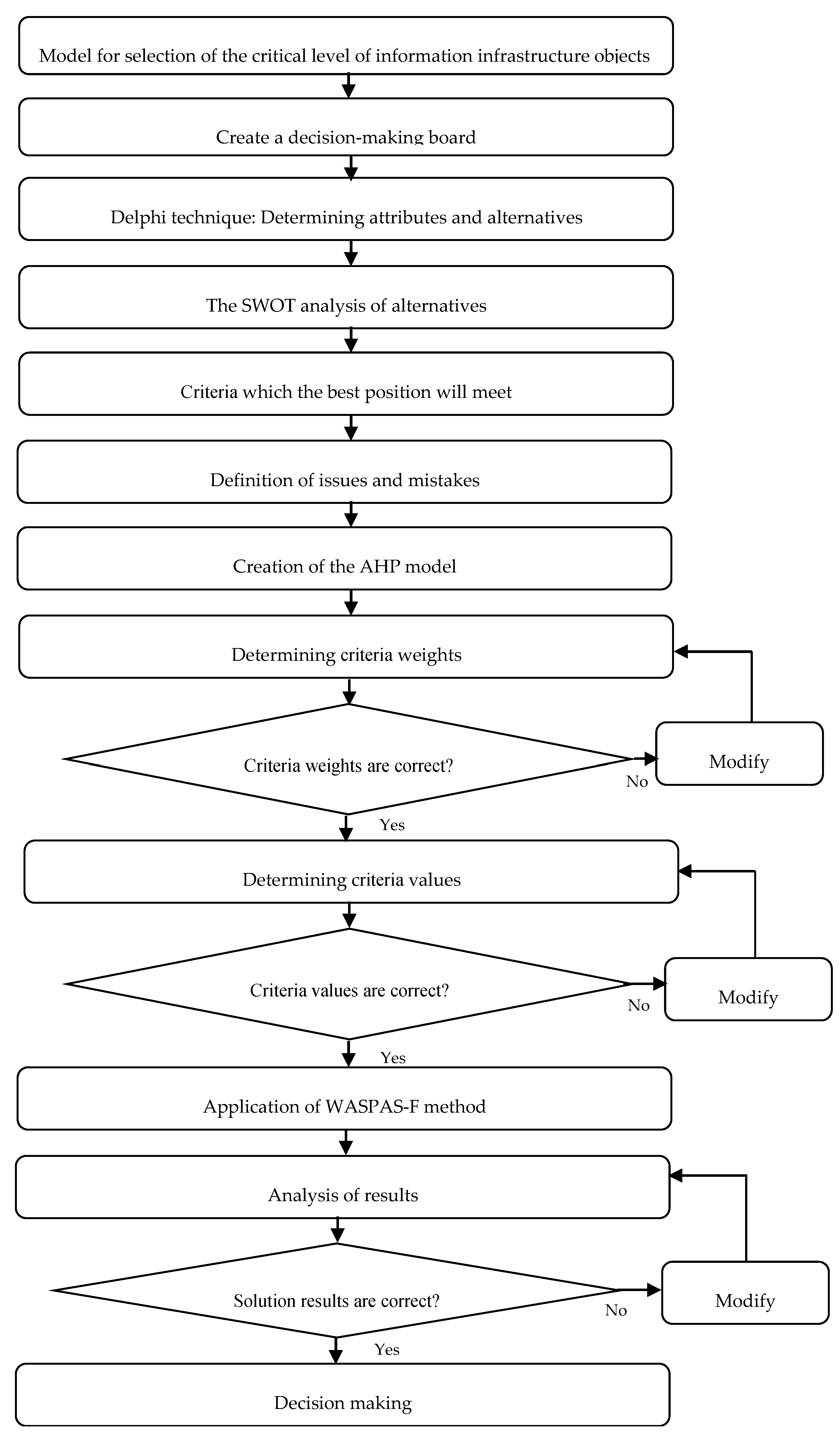
The flowchart of the proposed issue is shown in
Figure 4.
Often, due to the lack of accurate data, employees spend a lot of time discussing various expert opinions. The problem-solving approach still stands.
The fuzzy set theory is a class of objects with a continuum of membership grades. Here, a fuzzy set
A, presented in space
, is an ordered set of pairs. The components with 0 degrees can be unlisted:
where
is described by its function
, which associates with each component
, a real number
. The function
at
identifies the grade of membership of
in
, and is accounted for by the membership degree to which
belongs to
A.
An ordinary subset
A of
is presented like a fuzzy set in
, with a membership function as its characteristic function:
If the universe of discourse is discrete and finite with cardinality
n, that is
,
is calculated as:
If the universe of discourse
is an interval of real numbers, the
A could be shown as follows:
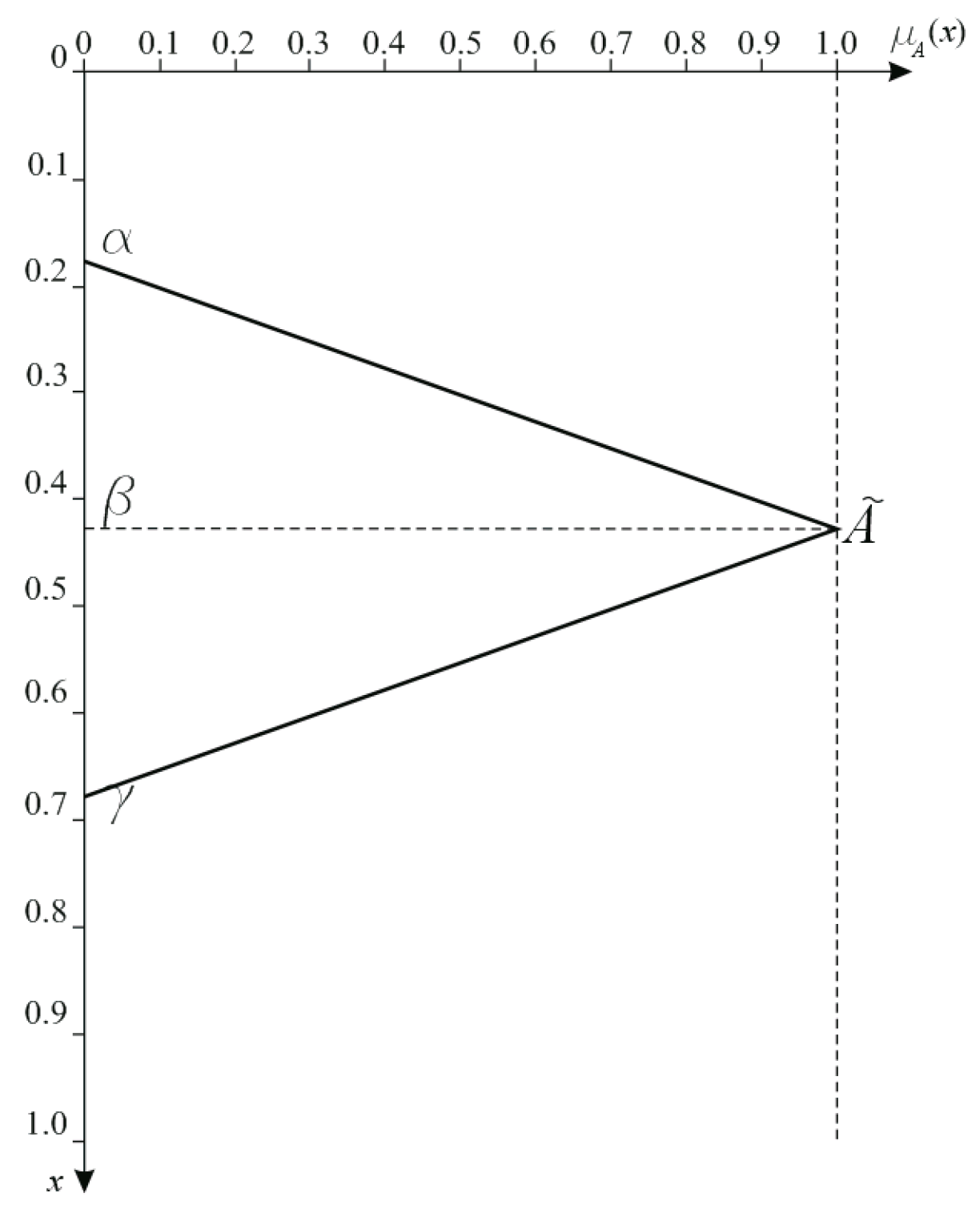
The fuzzy number
A is determined to be a fuzzy triangular number, with
α- lower,
β-modal, and
γ-upper values, if its membership function
is defined as:
To obtain a crisp output, a defuzzification is implemented, which produces a quantifiable result in fuzzy logic, given the fuzzy sets and their corresponding membership degrees.
The fuzzy number is generally an expert’s given subjective data.
Figure 5 presents the ordinary fuzzy set membership function.
Table 5 presents the following basic arithmetic operations for two triangular fuzzy numbers: (6) two triangular fuzzy numbers; (7) addition; (8) subtraction; (9) multiplication; (10) multiplication by constant; (11) division; (12) determining the reciprocal value; (13) the fuzzy power of raising the fuzzy numbers [
94].
Experts have determined the weight values
. It is known that many methods are able to assess weights. Sometimes, some expert data cannot be accurately described by using numerical values. There are four main options that describe various ways of measuring the number of things in quantitative terms: nominal, ordinal, interval, or ratio scales. Likert items were proposed in [
95].
Raising a fuzzy triangular number of the power of another fuzzy triangular number, if , and this is special for this situation of research.
In the analysis, an initial data matrix is created initially, in which the rows contain alternatives, and in the columns, there are selected significant indicators. Each indicator is assigned to whether it is maximized or minimized.
2.5. The WASPAS Method
The WSM approach calculates the total score of the alternative as a weighted sum of the criteria. The WPM approach was created to prevent alternatives that have poor attributes or criterion values. Zavadskas et al. used the multiplicative exponential weighting method (or WPM) to solve dynamically changing environment problems [
27].
The problem solution process by applying the WASPAS-F method is shown below.
Create the fuzzy decision-making matrix by using the values and the criteria weights as the decision-making matrix entries. Determine the linguistic ratings.
Usually, experts play a main role in identifying the system of criteria, the linguistic values of the qualitative criteria, and the initial criteria weights.
The initial fuzzy decision-making matrix shows the preferences for
m reasonable alternatives rated on
n attributes:
where
is a fuzzy value that presents the performance value of the
i alternative in terms of the
j criteria. A tilde symbol “~” means a fuzzy set.
The process of normalization of the initial values of all criteria
eliminates different criteria measurement units. The values of the normalized decision-making matrix
:
are determined as follows:
Determine the weighted normalized fuzzy decision-making matrix
for the WSM:
Determine the weighted normalized fuzzy decision-making matrix
for the WPM:
Calculate the multi-attribute utility function values:
The WSM for
i alternative:
The WPM for
i alternative:
The center-of-area is the most practical and easy to use for the defuzzification of the fuzzy performance measurement:
The utility function value
Ki of the WASPAS-F method is calculated as follows:
where:
Rank preference orders the alternatives, starting from the highest value, Ki.
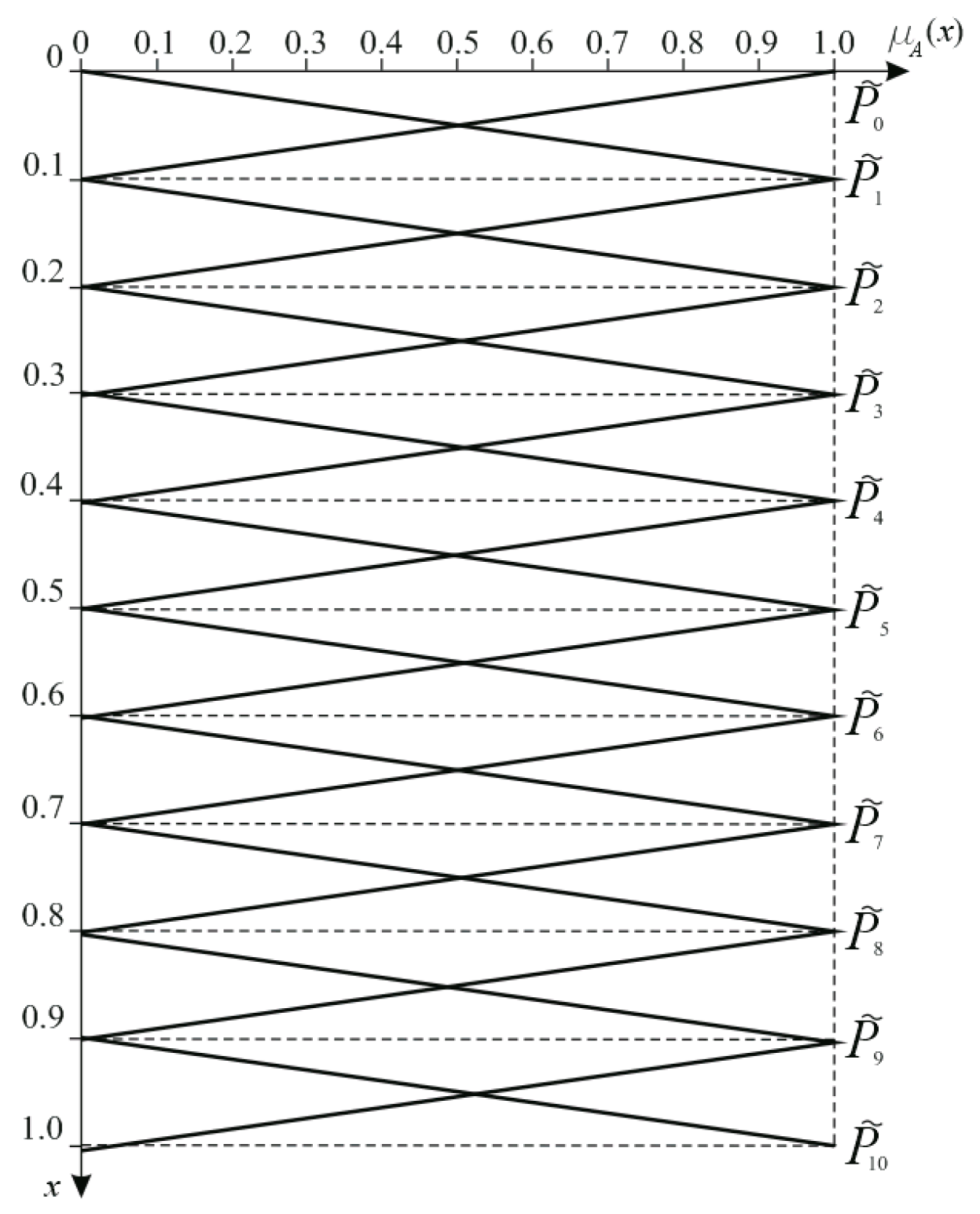
A Likert-type 10-point scale was adopted to solve the problem (
Figure 6).
A detailed description of the problem-solving process using the AHP and WASPAS-F methods could be found in [
93].