A Comparison of Competing Models for Understanding Industrial Organization’s Acceptance of Cloud Services
Abstract
:1. Introduction
2. Literature Review and Research Hypotheses
2.1. Diffusion of Innovations Theory
2.2. Technology–Organization–Environment Framework
2.3. Constructs and Hypotheses Development
2.3.1. Service Compatibility (SC)
2.3.2. Entrepreneurship (ES)
2.3.3. Social Influence (SI)
2.3.4. Perceived Information Security Assurance (PISA)
2.3.5. Perceived Cost Savings (PCS)
2.3.6. Top Management Support (TMS)
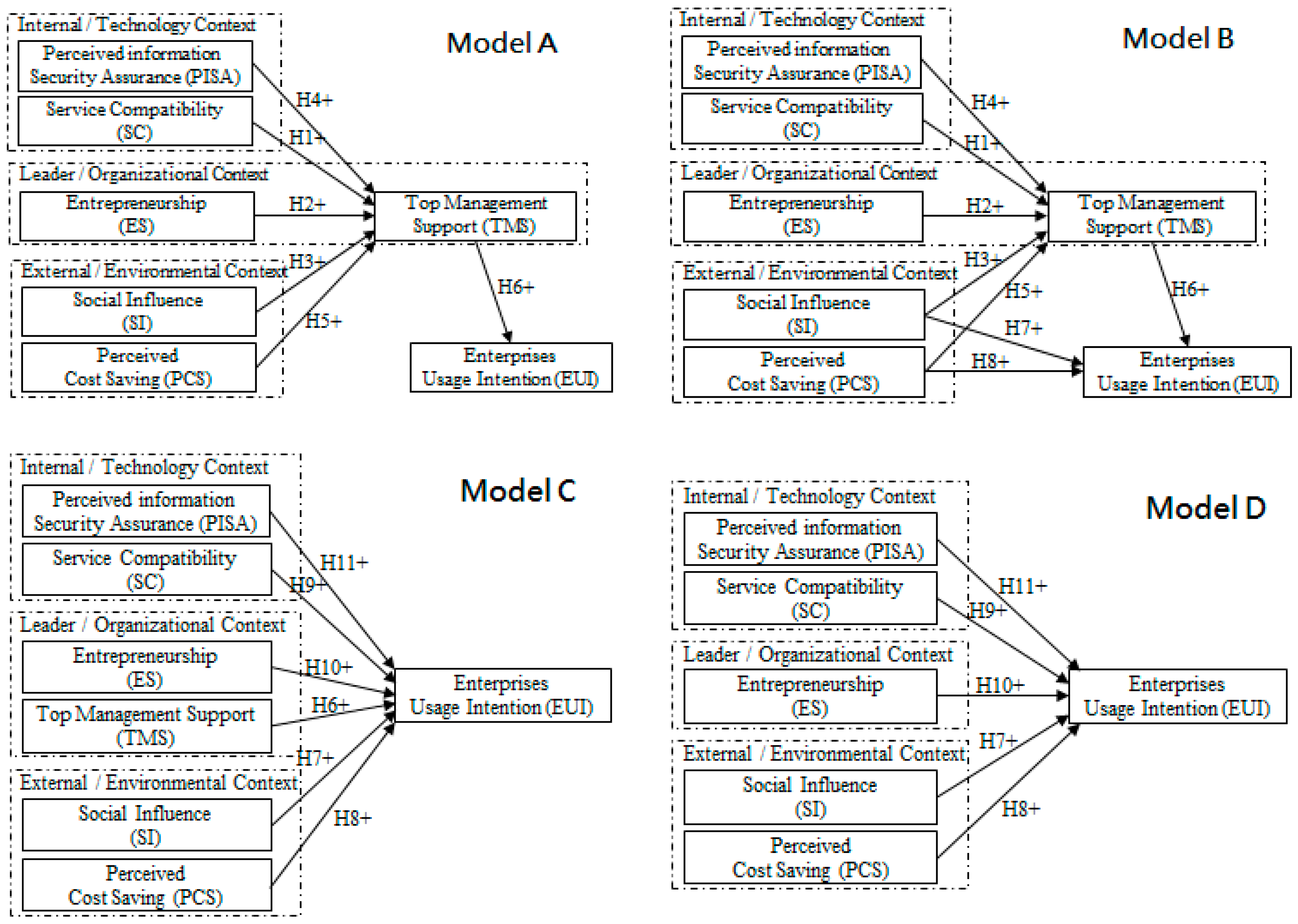
2.4. Research Competing Models
3. Research Methodology
3.1. Measures
3.2. Data Collection
3.3. Common Method Variance (CMV) Testing
3.4. Data Analysis
4. Results
4.1. Measurement Model
4.2. Structural Model
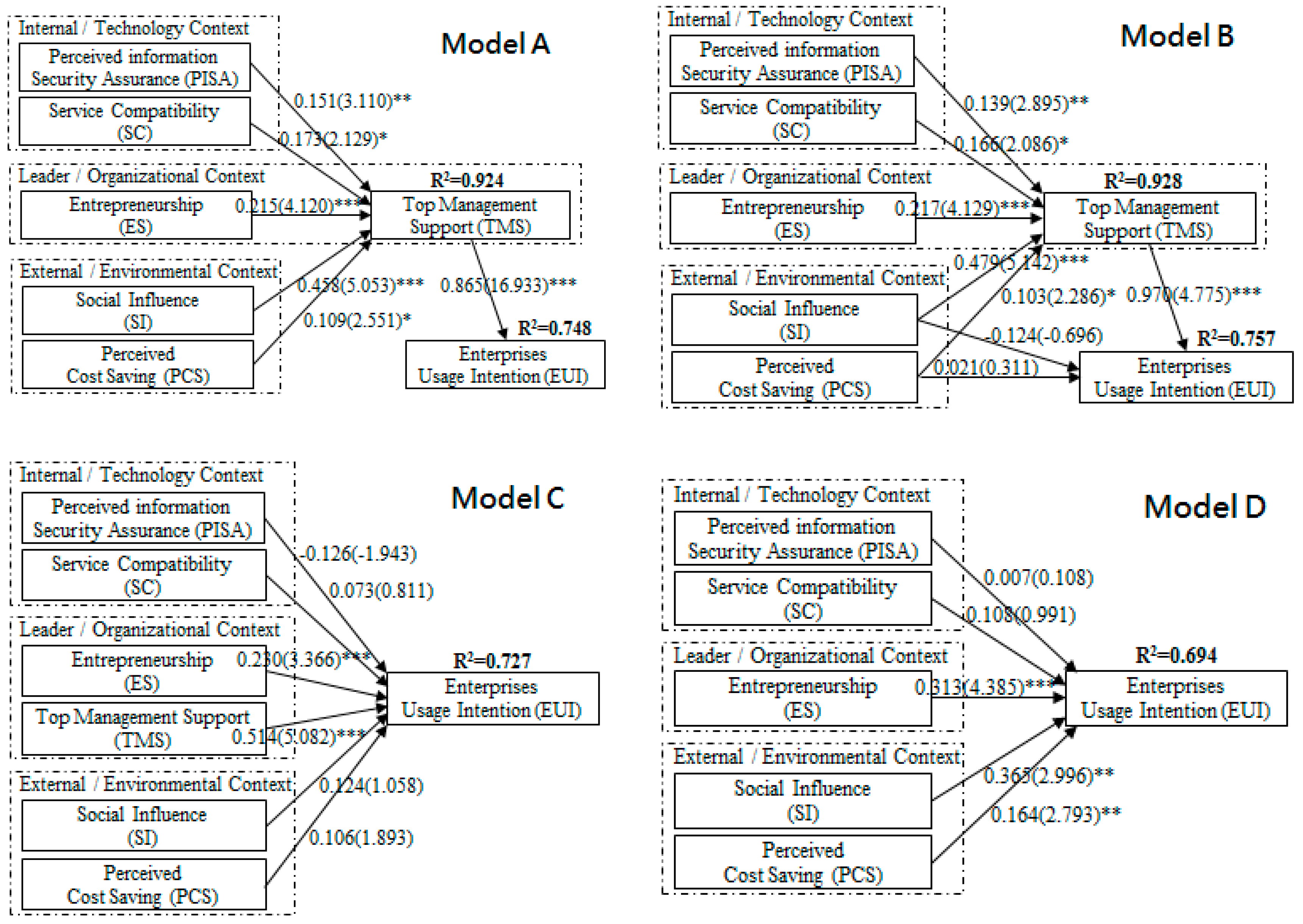
4.3. Comparison of the Research Competing Models
4.3.1. First Stage: Nested Model Comparison between Model A and Model B
4.3.2. Second Stage: Non-Nested Model Comparison among Model A, Model C, and Model D
5. Discussion and Implications
6. Conclusions
Author Contributions
Conflicts of Interest
References
- Brown, E. Final Version of NIST Cloud Computing Definition Published. Available online: http://www.nist.gov/itl/csd/cloud-102511.cfm (accessed on 5 May 2017).
- Lin, A.; Chen, N.C. Cloud computing as an innovation: Perception, attitude, and adoption. Int. J. Inf. Manag. 2012, 32, 533–540. [Google Scholar] [CrossRef]
- Arpaci, I.; Kilicer, K.; Bardakci, S. Effects of Security and Privacy Concerns on Educational Use of Cloud Services. Comput. Hum. Behav. 2015, 45, 93–98. [Google Scholar] [CrossRef]
- Forbes. Roundup of Cloud Computing Forecasts. Available online: https://www.forbes.com/sites/louiscolumbus/2017/04/29/roundup-of-cloud-computing-forecasts-2017/#1a33506931e8 (accessed on 28 February 2018).
- Market Research Media, Government Cloud Computing Markets to Thrive in 2018–2023. Available online: https://www.marketresearchmedia.com/?p=863 (accessed on 14 June 2017).
- Low, C.; Chen, Y.; Wu, M. Understanding the determinants of cloud computing adoption. Ind. Manag. Data Syst. 2011, 111, 1006–1023. [Google Scholar] [CrossRef]
- Ajzen, I. From Intentions to Actions: A Theory of Planned Behavior; Springer: Berlin/Heidelberg, Germany, 1985. [Google Scholar]
- Davis, F.D. A Technology Acceptance Model for Empirically Testing New End-User Information Systems: Theory and Results. Ph.D. Thesis, Massachusetts Institute of Technology, Cambridge, MA, USA, 1985. [Google Scholar]
- Tornatzky, L.; Fleischer, M. The Process of Technology Innovation; Lexington Books: New York, NY, USA, 1990. [Google Scholar]
- Rogers, E.M. Diffusion of Innovations, 4th ed.; The Free Press: New York, NY, USA, 1995. [Google Scholar]
- Venkatesh, V.; Morris, M.G.; Davis, G.B.; Davis, F.D. User acceptance of information technology: Toward a unified view. MIS Q. 2003, 27, 425–478. [Google Scholar] [CrossRef]
- Chong, A.Y.L.; Lin, B.; Ooi, K.B.; Raman, M. Factors affecting the adoption level of c-commerce: An empirical study. J. Comput. Inf. Syst. 2009, 50, 13–22. [Google Scholar]
- Oliveira, T.; Thomas, M.; Espadanal, M. Assessing the determinants of cloud computing adoption: An analysis of the manufacturing and services sectors. Inf. Manag. 2014, 51, 497–510. [Google Scholar] [CrossRef]
- Oliveira, T.; Martins, M.F. Firms Patterns of e-Business Adoption: Evidence for the European Union-27. Electron. J. Inf. Syst. 2010, 13, 47–56. [Google Scholar]
- Yang, H.; Tate, M. A descriptive literature review and classification of cloud computing research. Commun. Assoc. Inf. Syst. 2012, 31, 35–60. [Google Scholar]
- Martens, B.; Teuteberg, F. Decision-making in cloud computing environments: A cost and risk based approach. Inf. Syst. Front. 2012, 14, 871–893. [Google Scholar] [CrossRef]
- Wei, L.; Zhu, H.; Cao, Z.; Dong, X.; Jia, W.; Chen, Y.; Vasilakos, A.V. Security and privacy for storage and computation in cloud computing. Inf. Sci. 2014, 258, 371–386. [Google Scholar] [CrossRef]
- Almorsy, M.; Grundy, J.; Müller, I. An analysis of the cloud computing security problem. arXiv, 2016; arXiv:1609.01107. [Google Scholar]
- Shaukat, K.; Hassan, M.U. Cloud Security through Encryption Techniques. Transylv. Rev. 2017, XXV, 4037–4042. [Google Scholar]
- Abdollahzadegan, A.; Hussin, C.; Razak, A.; Moshfegh Gohary, M.; Amini, M. The organizational critical success factors for adopting cloud computing in SMEs. J. Inf. Syst. Res. Innov. 2013, 4, 67–74. [Google Scholar]
- Hsu, P.F.; Ray, S.; Li-Hsieh, Y.Y. Examining cloud computing adoption intention, pricing mechanism, and deployment model. Int. J. Inf. Manag. 2014, 34, 474–488. [Google Scholar] [CrossRef]
- Tim, A. Connectivity Made Simple How the Cloud Can Benefit Your SME. Available online: http://www.telegraph.co.uk/connect/small-business/business-solutions/how-the-cloud-can-benefit-smes (accessed on 9 October 2017).
- Rogers, E.M. Diffusion of Innovations; The Free Press: New York, NY, USA, 1962. [Google Scholar]
- Ifinedo, P. An empirical analysis of factors influencing Internet/e-business technologies adoption by SMEs in Canada. Int. J. Inf. Technol. Decis. Mak. 2011, 10, 731–766. [Google Scholar] [CrossRef]
- Rogers, E.M. Diffusion of Innovations, 5th ed.; The Free Press: New York, NY, USA, 2003. [Google Scholar]
- Jwaifell, M.; Gasaymeh, A.M. Using the Diffusion of Innovation Theory to Explain the Degree of English Teachers’ Adoption of Interactive Whiteboards in the Modern Systems School in Jordan: A Case Study. Contemp. Educ. Technol. 2013, 4, 138–149. [Google Scholar]
- Gangwar, H.; Date, H.; Ramaswamy, R. Understanding determinants of cloud computing adoption using an integrated TAM-TOE model. J. Enterp. Inf. Manag. 2015, 28, 107–130. [Google Scholar] [CrossRef]
- Tashkandi, A.N.; Al-Jabri, I.M. Cloud computing adoption by higher education institutions in Saudi Arabia: an exploratory study. Clust. Comput. 2015, 18, 1527–1537. [Google Scholar] [CrossRef]
- Oliveira, T.; Martins, M.F. Literature Review of Information Technology Adoption Models at Firm Level. Electron. J. Inf. Syst. 2011, 14, 10–121. [Google Scholar]
- Stieninger, M.; Nedbal, D.; Wetzlinger, W.; Wagner, G.; Erskine, M.A. Impacts on the organizational adoption of cloud computing: A reconceptualization of influencing factors. Procedia Technol. 2014, 16, 85–93. [Google Scholar] [CrossRef]
- Sebora, T.C.; Theerapatvong, T.; Lee, S.M. Corporate entrepreneurship in the face of changing competition: A case analysis of six Thai manufacturing firms. J. Organ. Chang. Manag. 2010, 23, 453–470. [Google Scholar] [CrossRef]
- Zhu, K.; Dong, S.; Xu, S.X.; Kraemer, K.L. Innovation diffusion in global contexts: Determinants of post-adoption digital transformation of European companies. Eur. J. Inf. Syst. 2006, 15, 601–616. [Google Scholar] [CrossRef]
- Li, Y.H. An empirical investigation on the determinants of e-procurement adoption in Chinese manufacturing enterprises. In Proceedings of the 15th Annual Conference, International Conference on Management Science and Engineering (ICMSE), Long Beach, CA, USA, 10–12 September 2008; pp. 32–37. [Google Scholar]
- Ramdani, B.; Kawalek, P.; Lorenzo, O. Predicting SMEs’ adoption of enterprise systems. J. Enterp. Inf. Manag. 2009, 22, 10–24. [Google Scholar] [CrossRef]
- Wang, Y.M.; Wang, Y.S.; Yang, Y.F. Understanding the determinants of RFID adoption in the manufacturing industry. Technol. Forecast. Soc. Chang. 2010, 77, 803–815. [Google Scholar] [CrossRef]
- Ghobakhloo, M.; Arias-Aranda, D.; Benitez-Amado, J. Adoption of e-commerce applications in SMEs. Ind. Manag. Data Syst. 2011, 111, 1238–1269. [Google Scholar] [CrossRef]
- Rogers, E.M. Diffusion of Innovations, 3rd ed.; The Free Press: New York, NY, USA, 1983. [Google Scholar]
- Tan, K.S.; Eze, U.C. An empirical study of internet-based ICT adoption among Malaysian SMEs. Commun. IBIMA 2008, 1, 1–12. [Google Scholar]
- Mathieson, K. Predicting user intentions: Comparing the technology acceptance model with the theory of planned behavior. Inf. Syst. Res. 1991, 2, 173–191. [Google Scholar] [CrossRef]
- Borgman, H.P.; Bahli, B.; Heier, H.; Schewski, F. Cloudrise: Exploring cloud computing adoption and governance with the TOE framework. In Proceedings of the IEEE 46th Hawaii International Conference System Sciences (HICSS), Wailea, Maui, HI, USA, 7–10 January 2013; pp. 4425–4435. [Google Scholar]
- Shukla, A. What Is Entrepreneurship? 2017. Available online: http://www.paggu.com/entrepreneurship/what-is-entrepreneurship (accessed on 12 October 2017).
- BusinessDictionary. What Is Entrepreneurship Definition and Meaning. Available online: http://www.businessdictionary.com/definition/entrepreneurship.html (accessed on 15 June 2017).
- Ratten, V. Technological innovations in the m-commerce industry: A conceptual model of mobile banking intentions. J. High Technol. Manag. Res. 2008, 18, 111–117. [Google Scholar] [CrossRef]
- Subramanianls. Entrepreneurship and Cloud Computing. Available online: http://cloudbus.blogspot.com/2011/05/entrepreneurship-and-cloud-computing.html#!/2011/05/entrepreneurship-and-cloud-computing.html (accessed on 10 September 2017).
- Chen, K.Y.; Chang, M.L. User acceptance of ‘near field communication’ mobile phone service: An investigation based on the ‘unified theory of acceptance and use of technology’ model. Serv. Ind. J. 2013, 33, 609–623. [Google Scholar] [CrossRef]
- Fisbein, M.; Ajzen, I. Belief, Attitude, Intention and Behavior: An Introduction to Theory and Research; Addison-Wiley Publishing Company: Boston, MA, USA, 1975. [Google Scholar]
- Ajzen, I. The theory of planned behavior. Organ. Behav. Hum. Decis. Process. 1991, 50, 179–211. [Google Scholar] [CrossRef]
- Dillon, A.; Morris, M.G. User acceptance of new information technology: Theories and models. J. Am. Soc. Inf. Sci. 1996, 31, 3–32. [Google Scholar]
- Hartwick, J.; Barki, H. Explaining the role of user participation in information system use. Manag. Sci. 1994, 40, 440–465. [Google Scholar] [CrossRef]
- Thompson, R.L.; Higgins, C.A.; Howell, J.M. Influence of experience on personal computer utilization: Testing a conceptual model. J. Manag. Inf. Syst. 1994, 11, 167–187. [Google Scholar] [CrossRef]
- Wikipedia. Information Security. Available online: http://en.wikipedia.org/wiki/Information_security (accessed on 9 June 2017).
- Devine, S.M. Dangers in the Cloud. 2013. Available online: http://dl.acm.org/citation.cfm?id=2304460 (accessed on 4 April 2017).
- Brodkin, J. Gartner: Seven Cloud-Computing Security Risks. 2008. Available online: http://www.infoworld.com/article/2652198/security/gartner--seven-cloud-computing-security-risks.html (accessed on 20 May 2017).
- Subashini, S.; Kavitha, V. A survey on security issues in service delivery models of cloud computing. J. Netw. Comput. Appl. 2011, 34, 1–11. [Google Scholar] [CrossRef]
- Casaló, L.V.; Flavián, C.; Guinalíu, M. The generation of trust in the online services and product distribution: the case of Spanish electronic commerce. J. Electron. Commer. Res. 2011, 12, 199–213. [Google Scholar]
- Organisation for Economic Corporation and Development (OECD). Enhancing the Competitiveness of SMEs in the Global Economy: Strategies and Policies. Available online: http://www.oecd.org/cfe/smes/enhancingsmecompetitivenesstheoecdbolognaministerialconferencebologna14-15june2000.htm (accessed on 7 May 2017).
- James, J. Sustainable Internet access for the rural poor? Elements of an emerging Indian mode. Futures 2003, 35, 461–472. [Google Scholar] [CrossRef]
- Leavitt, N. Is cloud computing really ready for prime time? IEEE Comput. Soc. 2009, 42, 15–20. [Google Scholar] [CrossRef]
- Marston, S.; Li, Z.; Bandyopadhyay, S.; Zhang, J.; Ghalsasi, A. Cloud computing—The business perspective. Decis. Support Syst. 2011, 51, 176–189. [Google Scholar] [CrossRef]
- Premkumar, G.; Roberts, M. Adoption of new information technologies in rural small businesses. Omega Int. J. Manag. Sci. 1999, 27, 467–484. [Google Scholar] [CrossRef]
- Buyya, R.; Yeo, C.S.; Venugopal, S.; Broberg, J.; Brandic, I. Cloud computing and emerging IT platforms: Vision, hype, and reality for delivering computing as the 5th utility. Future Gener. Comput. Syst. 2009, 25, 599–616. [Google Scholar] [CrossRef]
- Teo, T.S.; Srivastava, S.C.; Jiang, L. Trust and electronic government success: An empirical study. J. Manag. Inf. Syst. 2008, 25, 99–132. [Google Scholar] [CrossRef]
- Swink, M. Technological innovativeness as a moderator of new product design integration and top management support. J. Prod. Innov. Manag. 2000, 17, 208–220. [Google Scholar] [CrossRef]
- Ragu-Nathan, B.S.; Apigian, C.H.; Ragu-Nathan, T.S.; Tu, Q. A path analytic study of the effect of top management support for information systems performance. Omega Int. J. Manag. Sci. 2004, 32, 459–471. [Google Scholar] [CrossRef]
- Kearns, G.S. The effect of top management support of SISP on strategic IS management: Insights from the US electric power industry. Omega Int. J. Manag. Sci. 2006, 34, 236–253. [Google Scholar] [CrossRef]
- Damanpour, F.; Schneider, M. Phases of the adoption of innovation in organizations: Effects of environment, organization and top managers. Br. J. Manag. 2006, 17, 215–236. [Google Scholar] [CrossRef]
- Pinheiro, A.B. How do managers control technology-intensive work? J. Technol. Manag. Innov. 2010, 5, 1–12. [Google Scholar] [CrossRef]
- Bollen, K.A. Structural Equations with Latent Variables; John Wiley and Sons, Inc.: New York, NY, USA, 1989. [Google Scholar]
- Epstein, R. The principle of parsimony and some applications in psychology. J. Mind Behav. 1984, 5, 119–130. [Google Scholar]
- Foster, I.; Zhao, Y.; Raicu, I.; Lu, S. Cloud computing and grid computing 360-degree compared. In Proceedings of the Grid Computing Environments Workshop, Austin, TX, USA, 12–16 November 2008; pp. 1–10. [Google Scholar]
- Mathwick, C.; Malhotra, N.K.; Rigdon, E. The effect of dynamic retail experiences on experiential perceptions of value: An Internet and catalog comparison. J. Retail. 2002, 78, 51–60. [Google Scholar] [CrossRef]
- Meuter, M.L.; Bitner, M.J.; Ostrom, A.L.; Brown, S.W. Choosing among alternative service delivery modes: An investigation of customer trial of self-service technologies. J. Mark. 2005, 69, 61–83. [Google Scholar] [CrossRef]
- O’Cass, A.; Weerawardena, J. Examining the role of international entrepreneurship, innovation and international market performance in SME internationalization. Eur. J. Mark. 2009, 43, 1325–1348. [Google Scholar] [CrossRef]
- Gonzalez, G.C.; Sharma, P.N.; Galletta, D.F. The antecedents of the use of continuous auditing in the internal auditing context. Int. J. Account. Inf. Syst. 2012, 13, 248–262. [Google Scholar] [CrossRef]
- Dabholkar, P.A.; Bagozzi, R.P. An attitudinal model of technology-based self-service: Moderating effects of consumer traits and situational factors. J. Acad. Mark. Sci. 2002, 30, 184–201. [Google Scholar] [CrossRef]
- Podsakoff, P.M.; MacKenzie, S.B.; Lee, J.Y.; Podsakoff, N.P. Common method biases in behavioral research: A critical review of the literature and recommended remedies. J. Appl. Psychol. 2003, 88, 879. [Google Scholar] [CrossRef] [PubMed]
- Verkasalo, H.; López-Nicolás, C.; Molina-Castillo, F.J.; Bouwman, H. Analysis of users and non-users of smartphone applications. Telemat. Inf. 2010, 27, 242–255. [Google Scholar] [CrossRef]
- Huang, S.Y.; Huang, Y.C.; Chang, W.H.; Chang, L.Y.; Kao, P.H. Exploring the Effects of Teacher Job Satisfaction on Teaching Effectiveness: Using’Teaching Quality Assurance’ as the Mediator. Int. J. Mod. Educ. Forum 2013, 2, 17–30. [Google Scholar]
- Huang, S.Y. Relevance of IT Integration into Teaching to Learning Satisfaction and Learning Effectiveness. World J. Educ. 2014, 4. [Google Scholar] [CrossRef]
- Wright, S. The method of path coefficients. Ann. Math. Stat. 1934, 5, 161–215. [Google Scholar] [CrossRef]
- Schreiber, J.B.; Nora, A.; Stage, F.K.; Barlow, E.A.; King, J. Reporting Structural Equation Modeling and Confirmatory Factor Analysis Results: A Review. J. Educ. Res. 2006, 99, 323–338. [Google Scholar] [CrossRef]
- Kyriakidou, V.; Michalakelis, C.; Sphicopoulos, T. Assessment of information and communications technology maturity level. Telecommun. Policy 2013, 37, 48–62. [Google Scholar] [CrossRef]
- Newsom. Nested Models, Model Modifications, and Correlated Errors. Available online: http://web.pdx.edu/~newsomj/semclass/ho_nested.pdf (accessed on 7 July 2017).
- Being. Non-Nested SEM Model Comparison. Available online: http://zencaroline.blogspot.tw/2007/08/non-nested-sem-model.html (accessed on 26 July 2017).
- Werne, C.; Schermelleh-Enge, K. Deciding between Competing Models-Chi-Square Difference Tests. Available online: http://www.psychologie.uzh.ch/dam/jcr:ffffffff-b371-2797-0000-00000fda8f29/chisquare_diff_en.pdf (accessed on 25 June 2017).
- Merkle, E.C.; You, D.; Preacher, K.J. Testing Nonnested Structural Equation Models. Available online: http://arxiv.org/pdf/1402.6720.pdf (accessed on 8 February 2017).
- Bagozzi, R.P.; Yi, Y. On the evaluation of structural equation models. J. Acad. Mark. Sci. 1988, 16, 74–94. [Google Scholar] [CrossRef]
- Hair, J.F.; Black, W.C.; Babin, B.J.; Anderson, R.E. Multivariate Data Analysis, 7th ed.; Prentice Hall: Upper Saddle River, NJ, USA, 2010. [Google Scholar]
- Fornell, C.; Larcker, D.F. Evaluating structural equation models with unobservable variables and measurement error. J. Mark. Res. 1981, 18, 39–50. [Google Scholar] [CrossRef]
- Bagozzi, R.P.; Phillips, L.W. Representing and testing organizational theories: A holistic construal. Adm. Sci. Q. 1982, 27, 459–489. [Google Scholar] [CrossRef]
- CHIN, W.W. The partial least squares approach to structural equation modeling. Mod. Methods Bus. Res. 1988, 295, 295–336. [Google Scholar]
- Rust, R.T.; Lee, C.; Valente, E. Comparing covariance structure models: A general methodology. Int. J. Res. Mark. 1995, 12, 279–291. [Google Scholar] [CrossRef]
| Theoretical Model | Innovation Diffusion and Adoption (Dependent Variable) | Primarily Constructs (Independent Variables) | Source | |||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Relative Advantage | Compatibility | Complexity | Security | Tech. Readiness | Firm Size | Top Management Support | Cost | External Pressure | External Support | |||
| TOE and DOI | E-business | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | [32] | ||
| TOE, DOI and institutional theory | E-procurement | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | [33] | |||
| TOE and DOI | Collaborative commerce | ✓ | ✓ | ✓ | ✓ | ✓ | [12] | |||||
| TOE | Knowledge management and enterprise systems adoption | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | [34] | ||||
| TOE and DOI | RFID | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | [35] | ||||
| TOE | E-commerce | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | [36] | ||||
| TOE and DOI | Cloud computing adoption | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | [6] | |||
| TOE | Cloud computing adoption | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | [20] | |||
| TOE and DOI | Cloud computing adoption | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | [13] |
| Constructs | Measurement Items | Reference |
|---|---|---|
| Perceived Information Security Assurance (PISA) | The cloud services provider has an efficient replication and recovery mechanism to restore data if a disaster occurs (PISA5). The cloud services provider is willing to accept an occasional survey of contractual commitment (PISA6). The data should be viable, even when another company acquires the cloud services provider (PISA7). | [53,70] |
| Service Compatibility (SC) | Using cloud services fits my firm needs (SC1). Using cloud services is in line with my colleagues and my preferences (SC3). | [71,72] |
| Entrepreneurship (ES) | The changes in products and services have been dramatic (ES3). The owner or manager emphasizes RandD expenditure, technological leadership, and innovation (ES4). The owner or manager has a very competitive “beat-the-competitors” posture (ES6). | [73] |
| Top Management Support (TMS) | The owner or manager enthusiastically supports the adoption of cloud services (TMS1). The owner or manager actively encourages employees to use cloud services in their daily tasks (TMS4). | [60] |
| Social Influence (SI) | People or companies who influence my firm behavior think/would think that my firm should use cloud services (SI1). People or companies who are important to my firm think/would think that my firm should use cloud services (SI2). My firm has supported/would support the use of cloud services (SI4). | [11,74] |
| Perceived Cost Savings (PCS) | The costs of cloud services adoption are far greater than the benefits (PCS1). The costs of maintaining and supporting cloud services are not high for our business (PCS2). The amount of money and time invested in training employees to use cloud services is not high for our business (PCS3). | [60] |
| Enterprise Usage Intention (EUI) | If possible, my firm will use cloud services soon (EUI4). I’m certain that my firm will use cloud services soon (EUI5). My firm definitely will use cloud services soon (EUI6). | [75] |
| Sample size | Number of distributed questionnaires | 500 |
| Number of returned questionnaires | 304 | |
| Number of valid samples | 227 | |
| Effective response rate | 45.4% | |
| Frequency | Percentage (%) | |
| Industry type | ||
| Manufacturing | 64 | 28.2% |
| Service | 163 | 71.8% |
| Number of employees | ||
| More than 200 | 130 | 57.3% |
| 100–199 | 30 | 13.2% |
| 50–99 | 15 | 6.6% |
| 20–49 | 31 | 13.7% |
| 6–19 | 15 | 6.6% |
| Less than 5 | 6 | 2.6% |
| Model | χ2 | DF | ∆DF | ∆χ2 |
|---|---|---|---|---|
| Single-factor | 1272.8 | 152 | 21 | 1079.2 *** |
| Multi-factors | 193.6 | 131 |
| Constructs | Items | Factor Loading | t-Value | CR | AVE |
|---|---|---|---|---|---|
| SC | SC1 | 0.949 | 18.743 | 0.920 | 0.853 |
| SC3 | 0.897 | 17.053 | |||
| ES | ES3 | 0.903 | 17.153 | 0.907 | 0.764 |
| ES4 | 0.902 | 17.120 | |||
| ES6 | 0.815 | 14.592 | |||
| SI | SI1 | 0.893 | 17.014 | 0.915 | 0.782 |
| SI2 | 0.847 | 15.634 | |||
| SI4 | 0.912 | 17.632 | |||
| PISA | PISA5 | 0.901 | 16.845 | 0.889 | 0.727 |
| PISA6 | 0.870 | 15.963 | |||
| PISA7 | 0.783 | 13.632 | |||
| PCS | PCS1 | 0.780 | 13.250 | 0.861 | 0.675 |
| PCS2 | 0.873 | 15.531 | |||
| PCS3 | 0.809 | 13.953 | |||
| TMS | TMS1 | 0.902 | 17.342 | 0.892 | 0.806 |
| TMS4 | 0.893 | 17.057 | |||
| EUI | EUI4 | 0.923 | 18.248 | 0.967 | 0.908 |
| EUI5 | 0.979 | 20.301 | |||
| EUI6 | 0.955 | 19.380 |
| Construct | Correlation | Standard Errors | Confidence Interval | |
|---|---|---|---|---|
| SC–ES | 0.660 | 0.044 | 0.572 | 0.748 |
| SC–TMS | 0.885 | 0.023 | 0.839 | 0.931 |
| SC–SI | 0.871 | 0.023 | 0.825 | 0.917 |
| SC–PISA | 0.672 | 0.043 | 0.586 | 0.758 |
| SC–PCS | 0.529 | 0.056 | 0.417 | 0.641 |
| SC–EUI | 0.730 | 0.035 | 0.660 | 0.800 |
| ES–TMS | 0.788 | 0.033 | 0.722 | 0.854 |
| ES–SI | 0.745 | 0.036 | 0.673 | 0.817 |
| ES–PISA | 0.527 | 0.055 | 0.417 | 0.637 |
| ES–PCS | 0.485 | 0.059 | 0.367 | 0.603 |
| ES–EUI | 0.746 | 0.034 | 0.678 | 0.814 |
| TMS–SI | 0.928 | 0.018 | 0.892 | 0.964 |
| TMS–PISA | 0.759 | 0.037 | 0.685 | 0.833 |
| TMS–PCS | 0.618 | 0.051 | 0.516 | 0.720 |
| TMS–EUI | 0.873 | 0.022 | 0.829 | 0.917 |
| SI–PISA | 0.634 | 0.047 | 0.540 | 0.728 |
| SI–PCS | 0.506 | 0.058 | 0.390 | 0.622 |
| SI–EUI | 0.784 | 0.030 | 0.724 | 0.844 |
| PISA–PCS | 0.575 | 0.054 | 0.467 | 0.683 |
| PISA–EUI | 0.573 | 0.049 | 0.475 | 0.671 |
| PCS–EUI | 0.560 | 0.052 | 0.456 | 0.664 |
| RCMs | ||||
|---|---|---|---|---|
| Model B | Model A | Model C | Model D | |
| Paths | ||||
| Service compatibility → Top management support | 0.166 * | 0.173 * | ||
| Entrepreneurship → Top management support | 0.217 *** | 0.215 *** | ||
| Social influence → Top management support | 0.479 *** | 0.458 *** | ||
| Perceived information security assurance → Top management support | 0.139 ** | 0.151 ** | ||
| Perceived cost savings → Top management support | 0.103 * | 0.109 * | ||
| Top management support → Enterprise Usage Intention | 0.970 *** | 0.865 *** | 0.514 *** | |
| Social influence → Enterprise Usage Intention | −0.124 | 0.124 | 0.365 ** | |
| Perceived cost savings → Enterprise Usage Intention | 0.021 | 0.106 | 0.164 ** | |
| Perceived information security assurance → Enterprise Usage Intention | −0.126 | 0.007 | ||
| Service compatibility → Enterprise Usage Intention | 0.073 | 0.108 | ||
| Entrepreneurship → Enterprise Usage Intention | 0.230 *** | 0.313 *** | ||
| Explanatory power (R2; SMC) | ||||
| Top management support | 0.928 | 0.924 | ||
| Enterprise Usage Intention | 0.757 | 0.748 | 0.727 | 0.694 |
| Model fit measures | ||||
| Absolute fit measures | ||||
| χ2 | 209.038 | 201.019 | 255.536 | 219.598 |
| d.f. | 134 | 136 | 168 | 137 |
| χ2/d.f. | 1.560 | 1.544 | 1.521 | 1.603 |
| GFI | 0.913 | 0.912 | 0.907 | 0.909 |
| RMSEA | 0.050 | 0.049 | 0.048 | 0.052 |
| Incremental fit measures | ||||
| AGFI | 0.877 | 0.878 | 0.872 | 0.874 |
| NFI | 0.953 | 0.953 | 0.950 | 0.950 |
| CFI | 0.983 | 0.983 | 0.982 | 0.980 |
| Parsimony fit measures | ||||
| AIC | 318.019 | 381.536 | 325.598 | |
| BIC | 502.966 | 597.308 | 507.120 | |
| ECVI | 1.407 | 1.688 | 1.441 | |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Chen, S.-L.; Chen, J.-H.; Lee, Y.H. A Comparison of Competing Models for Understanding Industrial Organization’s Acceptance of Cloud Services. Sustainability 2018, 10, 673. https://doi.org/10.3390/su10030673
Chen S-L, Chen J-H, Lee YH. A Comparison of Competing Models for Understanding Industrial Organization’s Acceptance of Cloud Services. Sustainability. 2018; 10(3):673. https://doi.org/10.3390/su10030673
Chicago/Turabian StyleChen, Shui-Lien, June-Hong Chen, and Yung Hsin Lee. 2018. "A Comparison of Competing Models for Understanding Industrial Organization’s Acceptance of Cloud Services" Sustainability 10, no. 3: 673. https://doi.org/10.3390/su10030673
APA StyleChen, S.-L., Chen, J.-H., & Lee, Y. H. (2018). A Comparison of Competing Models for Understanding Industrial Organization’s Acceptance of Cloud Services. Sustainability, 10(3), 673. https://doi.org/10.3390/su10030673






