A Hierarchical Multitier Approach for Privacy Policies in e-Government Environments
Abstract
:1. Introduction
2. Privacy Policies and Preferences in e-Government Environments
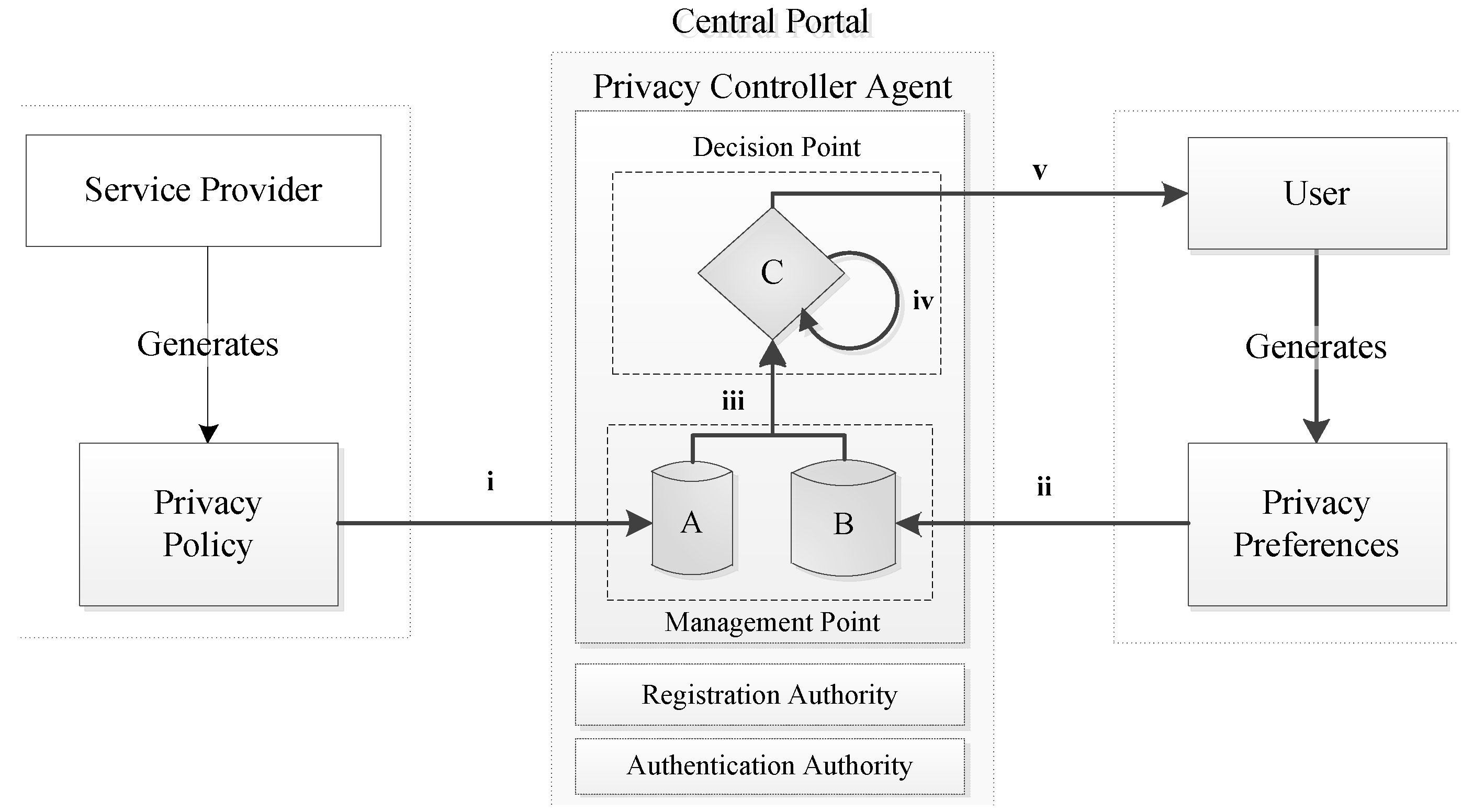
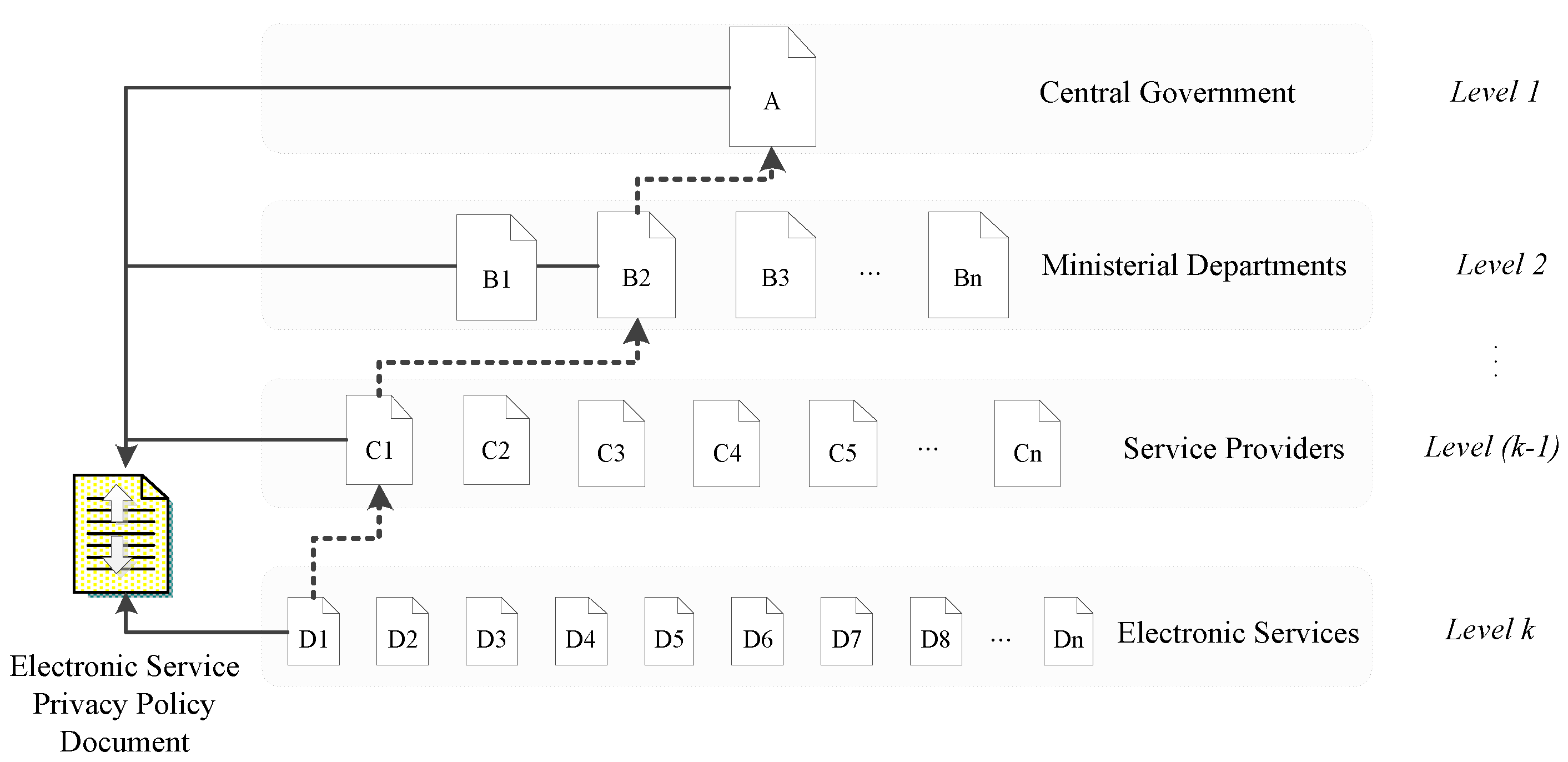
3. Privacy Policies Multitier Approach
3.1. Hierarching Privacy Policies
3.2. Privacy Policies Formation
3.3. Approach Evaluation
4. Case Study
4.1. Annual Vehicle Tax Electronic Service
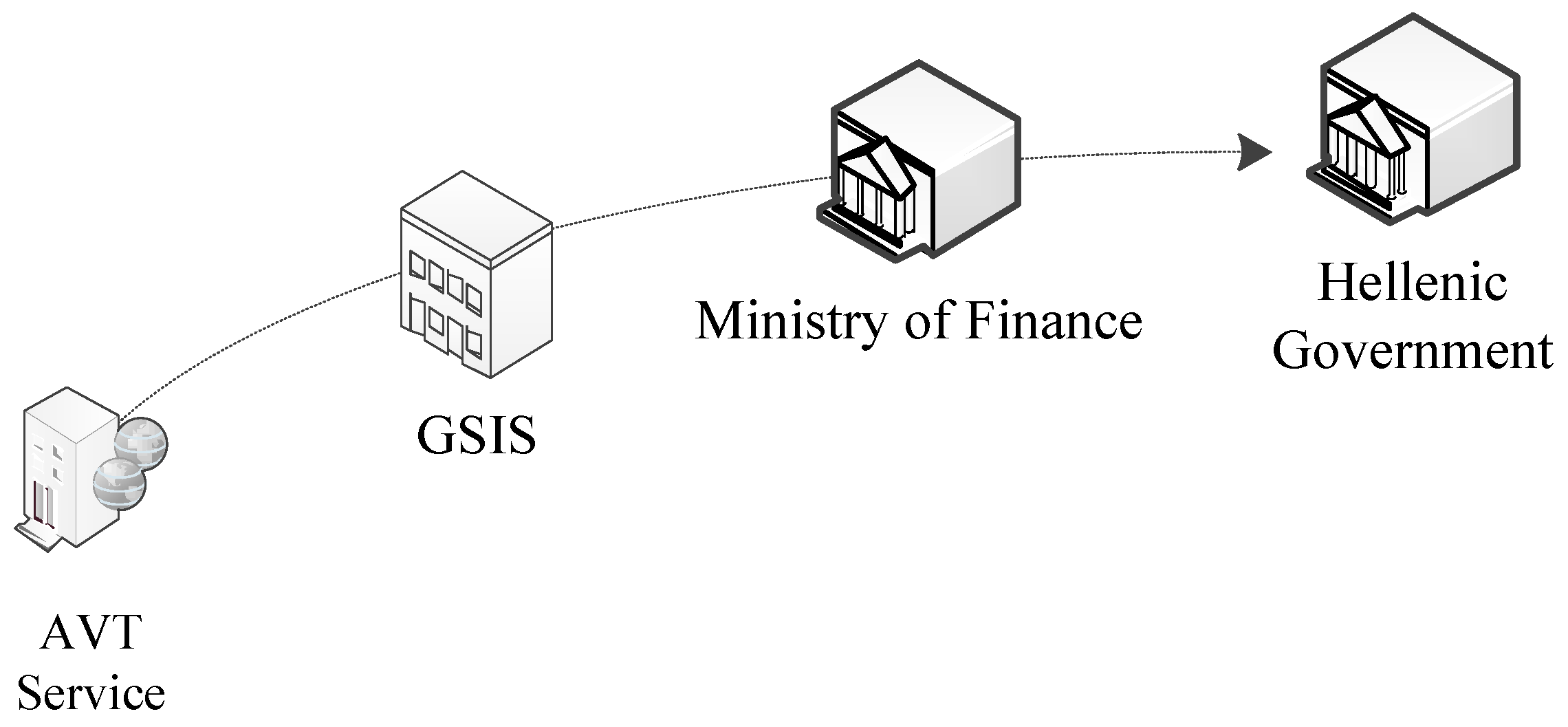
4.2. Privacy Policies
| Line | Privacy Policy Content |
|---|---|
| A.1 | <Privacy_Policy> |
| A.2 | <Policy_ID="001"> |
| A.3 | <Description> Hellenic Government Privacy Policy </Description> |
| A.4 | </Policy_ID> |
| A.5 | <Data> |
| A.6 | <Personal_Identifiers> |
| A.7 | <Identifier_ID="26"> National Taxation Identifier (AFM) |
| A.8 | <Processed="Confidential"> </Processed> |
| A.9 | <Storage="Yes"> </Storage> |
| A.10 | <Transmitted="Yes" </Transmitted> |
| A.11 | </Identifier_ID> |
| A.12 | </Personal_Identifiers> |
| A.13 | <Personal_Data> |
| A.14 | <Data_ID="873"> License Plate |
| A.15 | <Processed="Confidential"> </Processed> |
| A.16 | <Storage="Yes"> </Storage> |
| A.17 | <Transmitted="Yes" </Transmitted> |
| A.18 | </Data_ID> |
| A.19 | <Data_ID="32"> First and Last Name |
| A.20 | <Processed="Confidential"> </Processed> |
| A.21 | <Storage="Yes"> </Storage> |
| A.22 | <Transmitted="Yes" </Transmitted> |
| A.23 | </Data_ID> |
| A.24 | </Personal_Data> |
| A.25 | </Data> |
| A.26 | </Privacy_Policy> |
| Line | Privacy Policy Content |
|---|---|
| B.1 | <Privacy_Policy> |
| B.2 | <Policy_ID="024"> |
| B.3 | <Description> Ministry of Finance Privacy Policy </Description> |
| B.4 | </Policy_ID> |
| B.5 | <Data> |
| B.6 | <Personal_Identifiers> |
| B.7 | <Identifier_ID="26" P_Ref_ID="001"> National Taxation Identifier (AFM) |
| B.8 | <Processed="Confidential"> Identification </Processed> |
| B.9 | <Storage="Yes" Retention="365"> </Storage> |
| B.10 | </Identifier_ID> |
| B.11 | </Personal_Identifiers> |
| B.12 | <Personal_Data> |
| B.13 | <Data_ID="873" P_Ref_ID ="001"> License Plate |
| B.14 | <Processed="Confidential"> </Processed> |
| B.15 | <Storage="Yes" Retention ="365"> </Storage> |
| B.16 | </Data_ID> |
| B.17 | <Data_ID="32" p_Ref_ID="001"> First and Last Name |
| B.18 | <Processed="Confidential"> </Processed> |
| B.19 | <Storage="Yes" Retention="90"> </Storage> |
| B.20 | </Data_ID> |
| B.21 | </Personal_Data> |
| B.22 | </Data> |
| B.23 | </Privacy_Policy> |
| Line | Privacy Policy Content |
|---|---|
| C.1 | <Privacy_Policy> |
| C.2 | <Policy_ID="587"> |
| C.3 | <Description> GSIS Privacy Policy </Description> |
| C.4 | </Policy_ID> |
| C.5 | <Data> |
| C.6 | <Personal_Identifiers> |
| C.7 | <Identifier_ID="26" P_Ref_ID="024"> National Taxation Identifier (AFM) |
| C.8 | <Storage="Yes" Retention="180"></Storage> |
| C.9 | </Identifier_ID> |
| C.10 | </Personal_Identifiers> |
| C.11 | <Personal_Data> |
| C.12 | <Data_ID="873" P_Ref_ID ="024"> License Plate </Data_ID> |
| C.13 | <Data_ID="32" p_Ref_ID="024"> First and Last Name </Data_ID> |
| C.14 | </Personal_Data> |
| C.15 | </Data> |
| C.16 | </Privacy_Policy> |
| Line | Privacy Policy Content |
|---|---|
| D.1 | <Privacy_Policy> |
| D.2 | <Policy_ID="1038"> |
| D.3 | <Service_Provider> General Secretary of Information Systems (GSIS) |
| D.4 | </Service_Provider> |
| D.5 | <Electronic_Service> Annual Vehicle Tax </Electronic_Service> |
| D.6 | <Description> Privacy Policy for Annual Vehicle Tax Electronic Service |
| D.7 | </Description> |
| D.8 | </Policy_ID> |
| D.9 | <Data> |
| D.10 | <Personal_Identifiers> |
| D.11 | <Identifier_ID="26" P_Ref_ID="587"> National Taxation Identifier (AFM) |
| D.12 | <Transmitted="No" </Transmitted> |
| D.13 | </Identifier_ID> |
| D.14 | </Personal_Identifiers> |
| D.15 | <Personal_Data> |
| D.16 | <Data_ID="873" P_Ref_ID ="587"> License Plate |
| D.17 | <Processed="Confidential"> Identification </Processed> |
| D.18 | <Storage="Yes" Retention="90"> </Storage> |
| D.19 | </Data_ID> |
| D.20 | <Transmitted="Yes" </Transmitted> |
| D.21 | <Data_ID="32" p_Ref_ID="587"> First and Last Name |
| D.22 | <Processed="Confidential"> Identification </Processed> |
| D.23 | <Storage="No" Retention="0"> </Storage> |
| D.24 | </Data_ID> |
| D.25 | </Personal_Data> |
| D.26 | </Data> |
| D.27 | </Privacy_Policy> |
| Identifier | AVT | GSIS | Ministry of Finance | Central Government | ||||||||||||||||
| Storage | Process | Purpose | Retention | Transmit | Storage | Process | Purpose | Retention | Transmit | Storage | Process | Purpose | Retention | Transmit | Storage | Process | Purpose | Retention | Transmit | |
| AFM | ► | ► | ► | ► | No | ► | ► | ► | 180 | ► | ► | ► | I | 365 | ► | Yes | C | ◄ | ◄ | Yes |
| License Plate | ► | ► | I | 90 | ► | ► | ► | ◄ | ► | ► | ► | ► | ◄ | 365 | ► | Yes | C | ◄ | ◄ | Yes |
| Name | No | ► | I | ► | ► | ► | ► | ◄ | ► | ► | ► | ► | ◄ | 90 | ► | Yes | C | ◄ | ◄ | Yes |
4.3. Non-Hierarchical Privacy Policies
| Line | Privacy Policy Content |
|---|---|
| D.1 | <Privacy_Policy> |
| D.2 | <Policy_ID="1038"> |
| D.3 | <Service_Provider> General Secretary of Information Systems (GSIS) |
| D.4 | </Service_Provider> |
| D.5 | <Electronic_Service> Annual Vehicle Tax </Electronic_Service> |
| D.6 | <Description> Privacy Policy for Annual Vehicle Tax Electronic |
| D.7 | Service </Description> |
| D.8 | </Policy_ID> |
| D.9 | <Data> |
| D.10 | <Personal_Identifiers> |
| D.11 | <Identifier_ID="26"> National Taxation Identifier (AFM) |
| D.12 | <Processed="Confidential"> Identification </Processed> |
| D.13 | <Storage="Yes" Retention="90"> </Storage> |
| D.14 | <Transmitted="Yes" </Transmitted> |
| D.15 | </Identifier_ID> |
| D.16 | </Personal_Identifiers> |
| D.17 | <Personal_Data> |
| D.18 | <Data_ID="873"> License Plate |
| D.19 | <Processed="Confidential"> Identification </Processed> |
| D.20 | <Storage="Yes" Retention="90"> </Storage> |
| D.21 | <Transmitted="Yes" </Transmitted> |
| D.22 | </Data_ID> |
| D.23 | <Transmitted="Yes" </Transmitted> |
| D.24 | <Data_ID="32"> First and Last Name |
| D.25 | <Processed="Confidential"> Identification </Processed> |
| D.26 | <Storage="No" Retention="0"> </Storage> |
| D.27 | </Data_ID> |
| D.28 | </Personal_Data> |
| D.29 | </Data> |
| D.30 | </Privacy_Policy> |
5. Related Works
6. Conclusions
Author Contributions
Conflicts of Interest
References
- Belanger, F.; Hiller, J. A Framework for e-Government: Privacy Implications. Bus. Process Manag. J. 2006, 12, 48–60. [Google Scholar]
- McRobb, S.; Stahl, B. Privacy as a shared feature of the e-phenomenon: A comparison of privacy policies in e-government, e-commerce and e-teaching. Int. J. Inf. Technol. Manag. 2007, 6, 232–249. [Google Scholar] [CrossRef]
- Carter, L.; McBride, A. Information Privacy Concerns and e-Government: A Research Agenda. Transform. Gov. People Process Policy 2010, 4, 10–13. [Google Scholar]
- Vrakas, N.; Kalloniations, C.; Tsohou, A.; Lambrinoudakis, C. Privacy Requirements Engineering for Trustworthy e-Government Services. In Proceedings of the 3rd International Conference on Trust and Trustworthy Computing, Berlin, Germany, 21–23 June 2010; Springer Verlang: Berlin, Germany, 2010; pp. 298–307. [Google Scholar]
- Bussard, L.; Pinsdorf, U. Abstract Privacy Policy Framework: Addressing Privacy Problems in SOA. In Proceeingds of the IFIP WG 11.4 International Workshop, iNetSec, Lucerne, Switzerland, 9 June 2011; Springer LNCS: Berlin, Germany, 2012; pp. 104–118. [Google Scholar]
- Oyomno, W.; Jäppinen, P.; Kerttula, E. Privacy Policy Enforcement for Ambient Ubiquitous Services. In Proceedings of the First International Joint Conference on Ambient Intelligence (AML 2010), Malaga, Spain, 10–12 November 2010; Springer LNCS: Berlin, Germany, 2010; pp. 265–269. [Google Scholar]
- Lee, K.; Lee, J.; Chun, M. Incorporating Privacy Policy into an Anonymity-Based Privacy-Preserving ID-Based Service Platform. In Proceedings of the 9th International Conference in Knowledge-Based Intelligent Information and Engineering Systems (KES 2005), Melbourne, Australia, 14–16 September 2005; Springer LNCS: Berlin, Germany, 2005; pp. 1028–1035. [Google Scholar]
- Drogkaris, P.; Gritzalis, S.; Lambrinoudakis, C. Employing Privacy Policies and Preferences in Modern e-Government Environments. Int. J. Electron. Gov. 2013, 6, 101–116. [Google Scholar] [CrossRef]
- Drogkaris, P.; Gritzalis, A.; Lambrinoudakis, C. Empowering Users to Specify and Manage their Privacy Preferences in e-Government Environment. In Proceedings of the 3rd International Conference on Electronic Government and the Information Systems Perspective (EGOVIS 2014), Munich, Germany, 1–3 September 2014; Springer LNCS: Cham, Switzerland, 2014; pp. 237–245. [Google Scholar]
- Hong, Y.; Lu, S.; Liu, Q.; Wang, L.; Dssouli, R. A hierarchical approach to the specification of privacy preferences. In Proceedings of the 4th International Conference on Innovations in Information Technology (IIT’07), Dubai, United Arab Emirates, 18–20 November 2007.
- Nurseitov, N.; Paulson, M.; Reynolds, R.; XIzurieta, C. Comparison of JSON and XML Data Interchange Formats: A Case Study. In Proceedings of the ISCA 22nd International Conference on Computer Applications in Industry and Engineering, San Francisco, CA, UFA, 4–6 November 2009.
- Zhiwei, G.; Yingxin, H.; Kai, L. CPTIAS: A new fast PKI authentication scheme based on certificate path trust index. J. Ambient Intell. Humaniz. Comput. 2015, 6, 1–11. [Google Scholar] [CrossRef]
- Zhao, S.; Aggarwal, A.; Kent, R. PKI-Based Authentication Mechanisms in Grid Systems. In Proceedings of the International Conference on Networking, Architecture, and Storage (NAS 2007), Guilin, China, 29–31 July 2007; pp. 83–90.
- Satizábal, C.; Forné, J.; Hernández-Serrano, J.; Pegueroles, J. Building Hierarchical Public Key Infrastructures in Mobile Ad-Hoc Networks. In Proceedings of the Second International Conference on Mobile Ad-hoc and Sensor Networks (MSN 2006), Hong Kong, China, 13–15 December 2006; Springer LNCS: Berlin, Germany, 2006; pp. 485–496. [Google Scholar]
- Zhao, M.; Smith, S. Modeling and Evaluation of Certification Path Discovery in the Emerging Global PKI. In Proceedings of the Third European PKI Workshop: Theory and Practice, EuroPKI 2006, Turin, Italy, 19–20 June 2006; Springer LNCS: Berlin, Germany, 2006; pp. 16–30. [Google Scholar]
- Lambrinoudakis, C.; Gritzalis, S.; Dridi, F.; Pernul, G. Security requirements for e-government services: A methodological approach for developing a common PKI-based security policy. Comput. Commun. 2003, 26, 1873–1883. [Google Scholar] [CrossRef]
- Charalabidis, Y.; Lampathaki, F.; Sarantis, D.; Mouzakitis, S.; Gionis, G.; Koussouris, S.; Ntanos, C.; Tsiakaliaris, C.; Tountopoulos, V.; Askounis, D.; et al. The Greek electronic government interoperability framework: Standards and infrastructures for one stop service provision. In Proceedings of the Panhellenic Conference on Informatics (PCI’08), Samos, Greece, 28–30 August 2008; pp. 66–70.
- Drogkaris, P.; Geneiatakis, D.; Gritzalis, S.; Lambrinoudakis, C.; Mitrou, L. Towards an Enhanced Authentication Framework for eGovernment Services: The Greek Case. In Proceedings of the 7th International Conference on Electronic Government (EGOV’08), Torino, Italy, 1–5 September 2008; Trauner Verlag: Linz, Austria, 2008; pp. 189–196. [Google Scholar]
- Janssen, M.; Charalabibis, Y.; Kuk, G.; Cresswell, T. E-government Interoperability, Infrastructure and Architecture: State-of-the-art and Challenges. J. Theor. Appl. Electron. Commer. Res. 2001, 6, 1–8. [Google Scholar]
- Irwin, K.; Yu, T. Determining user privacy preferences by asking the right questions: An automated approach. In Proceedings of the ACM Workshop on Privacy in the Electronic Society, Alexandria, USA, 7–10 November 2005; pp. 47–50.
- Apostolou, D.; Stojanovic, L.; Lobo, T.; Miró, J.; Papadakis, A. Configuring e-government service using ontologies. In Proceedings of the 5th IFIP Conference e-Commerce, e-Business, and e-Government (I3E’2005), Poznan, Poland, 28–30 October 2005; pp. 141–155.
- Magoutas, B.; Halaris, C.; Mentzas, G. An ontology for the multi-perspective evaluation of quality in e-government services. In Proceedings of the 6th International Conference on e-Government, EGOV 2007, Regensburg, Germany, 3–7 September 2007; pp. 318–329.
© 2015 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Drogkaris, P.; Gritzalis, S.; Kalloniatis, C.; Lambrinoudakis, C. A Hierarchical Multitier Approach for Privacy Policies in e-Government Environments. Future Internet 2015, 7, 500-515. https://doi.org/10.3390/fi7040500
Drogkaris P, Gritzalis S, Kalloniatis C, Lambrinoudakis C. A Hierarchical Multitier Approach for Privacy Policies in e-Government Environments. Future Internet. 2015; 7(4):500-515. https://doi.org/10.3390/fi7040500
Chicago/Turabian StyleDrogkaris, Prokopios, Stefanos Gritzalis, Christos Kalloniatis, and Costas Lambrinoudakis. 2015. "A Hierarchical Multitier Approach for Privacy Policies in e-Government Environments" Future Internet 7, no. 4: 500-515. https://doi.org/10.3390/fi7040500
APA StyleDrogkaris, P., Gritzalis, S., Kalloniatis, C., & Lambrinoudakis, C. (2015). A Hierarchical Multitier Approach for Privacy Policies in e-Government Environments. Future Internet, 7(4), 500-515. https://doi.org/10.3390/fi7040500







