Vehicular Internet: Security & Privacy Challenges and Opportunities
Abstract
:1. Introduction
2. Applications for VANETs
- i.
- Safety applications: Notifications for crashes, hazards on the roads (slippery or wet road conditions), traffic violation warnings, curve speed warnings, emergency electronics brake light, pre-crash sensing, co-operative forward collision warnings, etc. This could also include generating warning messages that inform drivers of approaching emergency vehicles.
- ii.
- Convenience applications: Navigation, personal routing etc., Congestion advice, toll collection, parking availability information, etc. Also, in disaster situations, the critical things are power failure and network breakdown. The connected vehicles can play a very significant role in such situations as they have on-board batteries and many sensors including cameras, etc., thus providing valuable images and SOS calls. The vehicular network can become the emergency communication mechanism. Similarly, road and weather conditions can be monitored by sharing the data from on-board vehicle sensors [9].
- iii.
- Commercial applications: Vehicle diagnostics exchanges for avoiding possible car problems, location-based services such as advertisements and entertainment, i.e., data/video relay, social networking updates, etc.
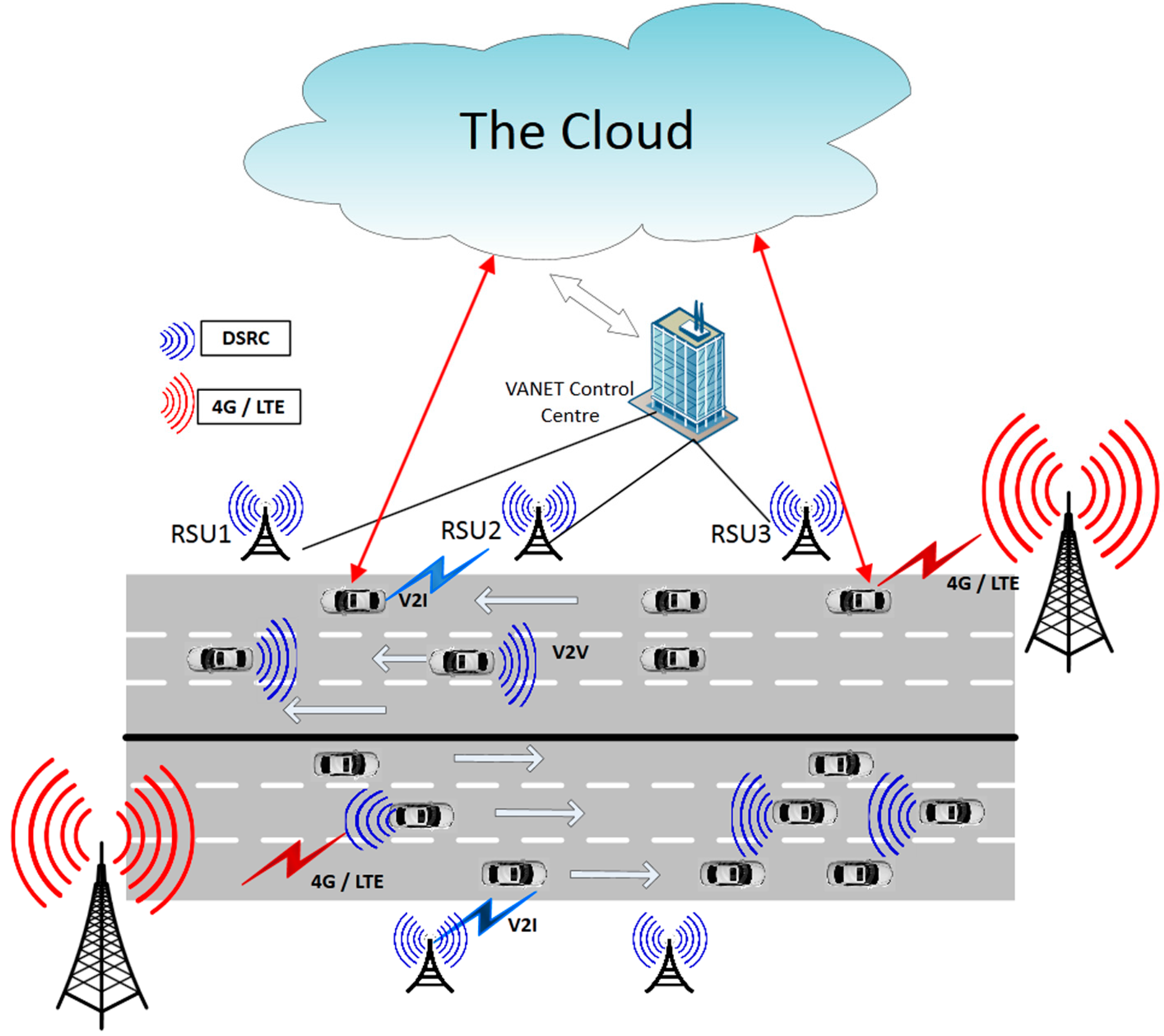
3. VANET and the Cloud
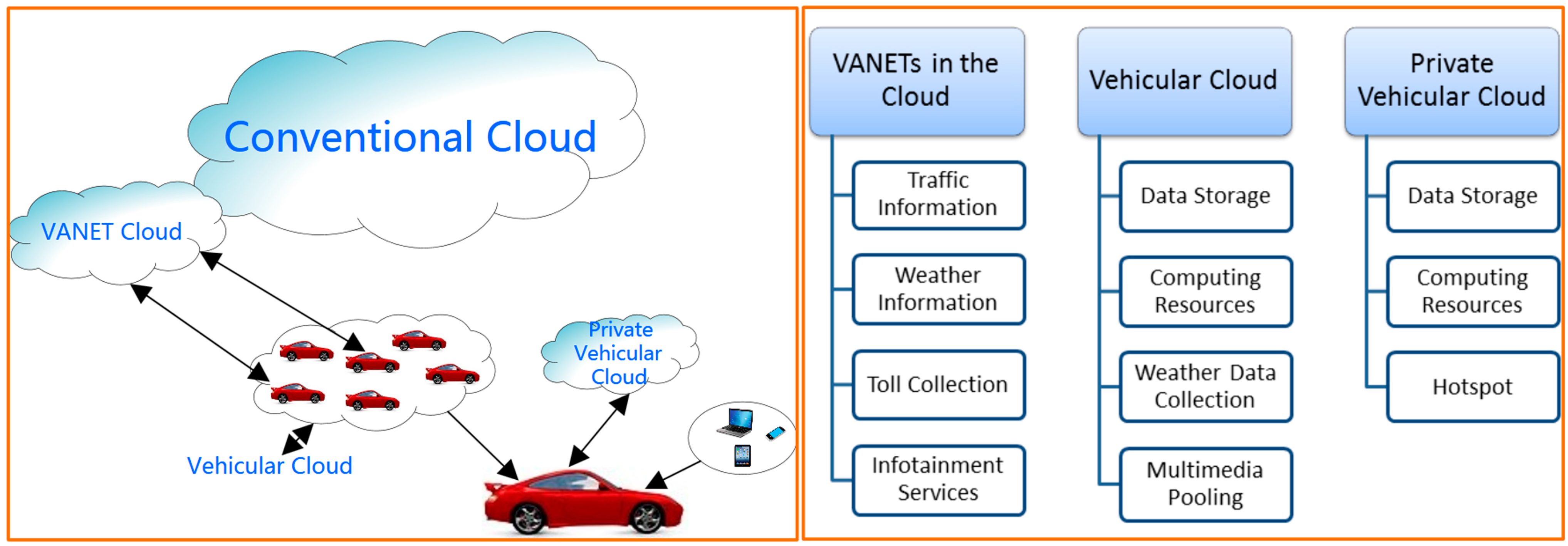
3.1. VANETs in the Cloud
3.2. Vehicular Cloud
3.3. Private Vehicular Cloud
4. Autonomous Vehicle
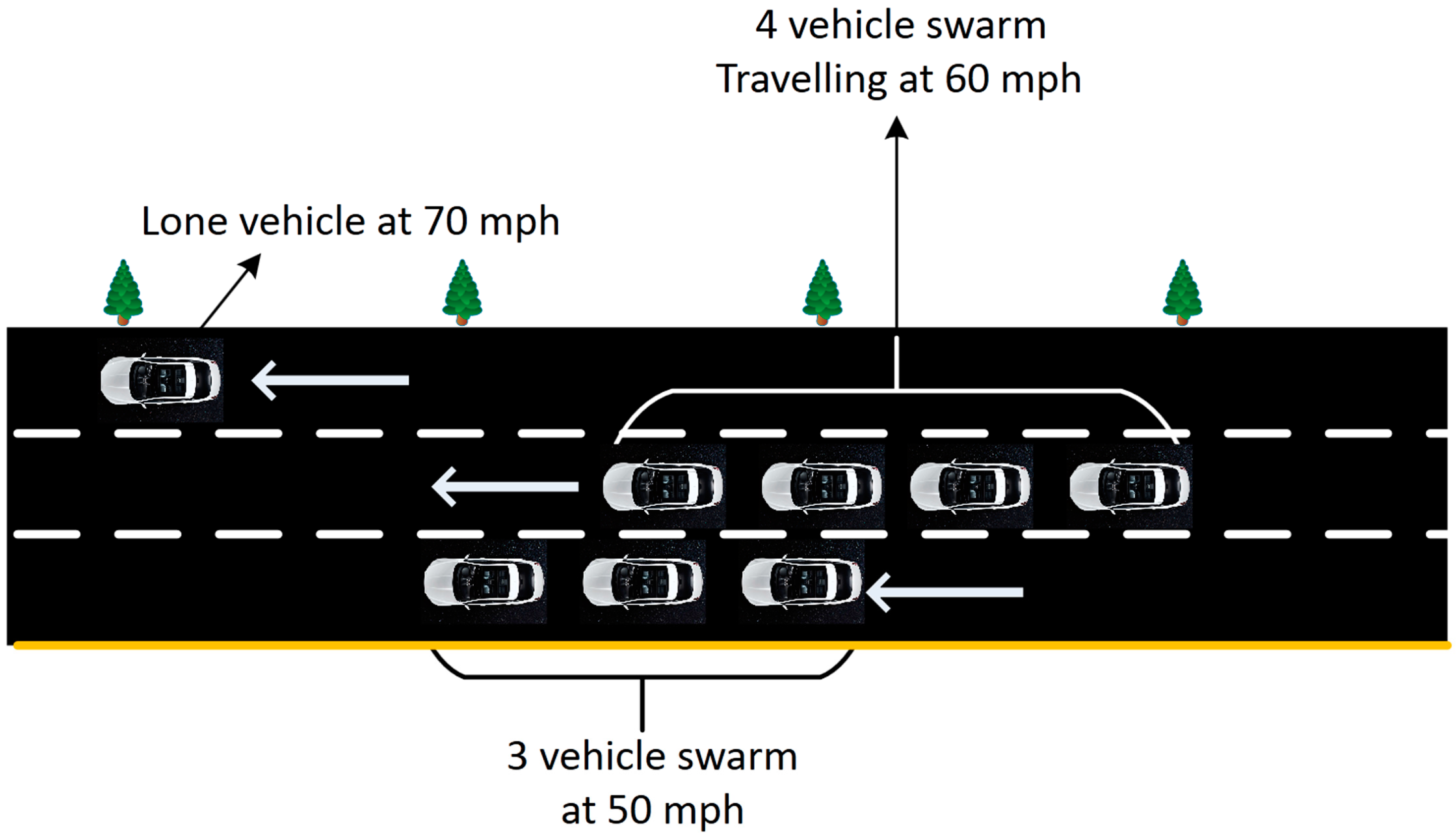
5. Vehicle Platoon/Swarm
6. Security and Privacy Issues
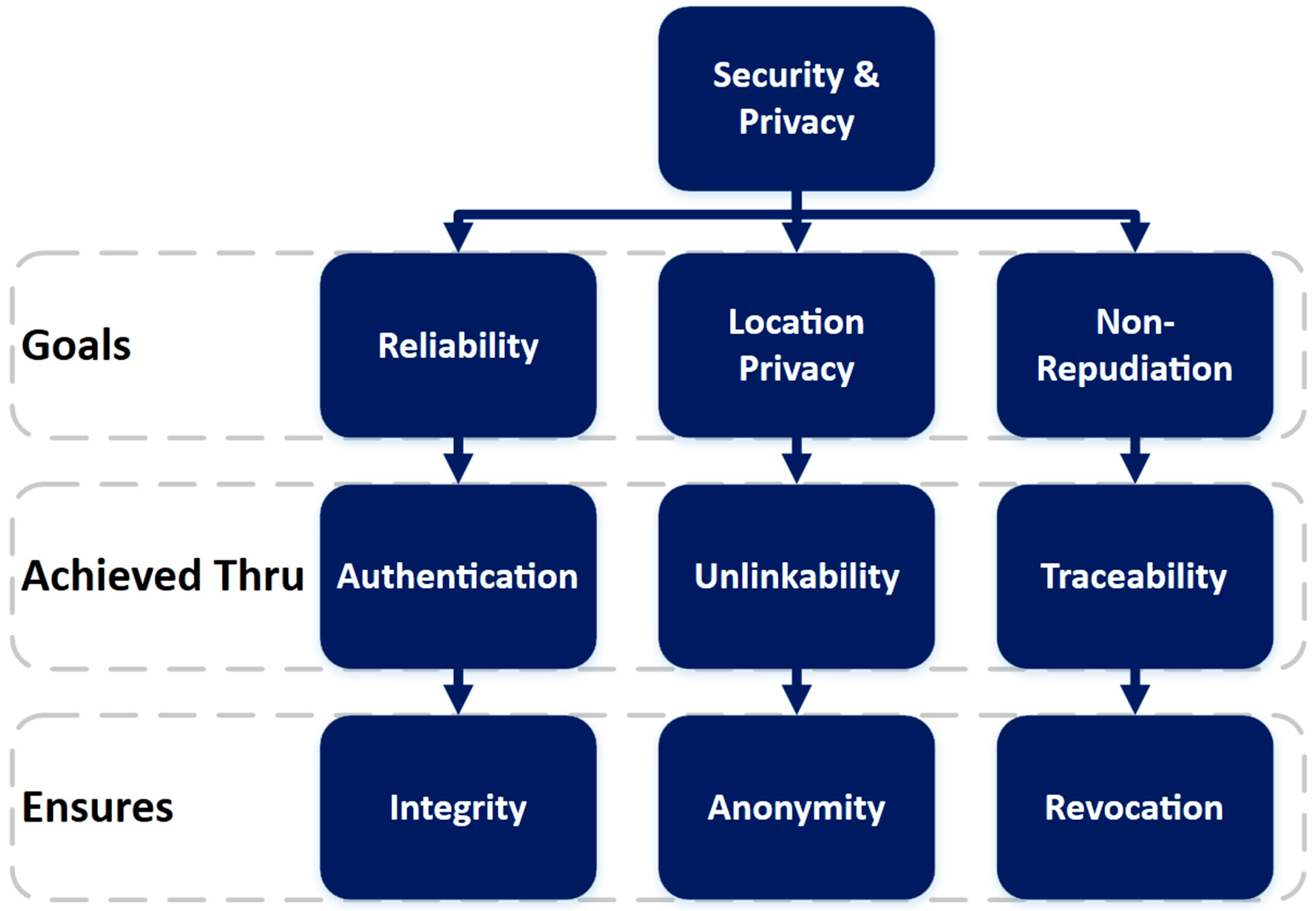
- Pseudonyms coupled with public key infrastructure (PKI)
- Trust-based schemes
- Group signatures
- k-anonymity schemes
- Identity-based signature schemes
7. Review of Security and Privacy-Preserving Schemes in VANETs
7.1. Pseudonyms Coupled with PKI-Based Schemes
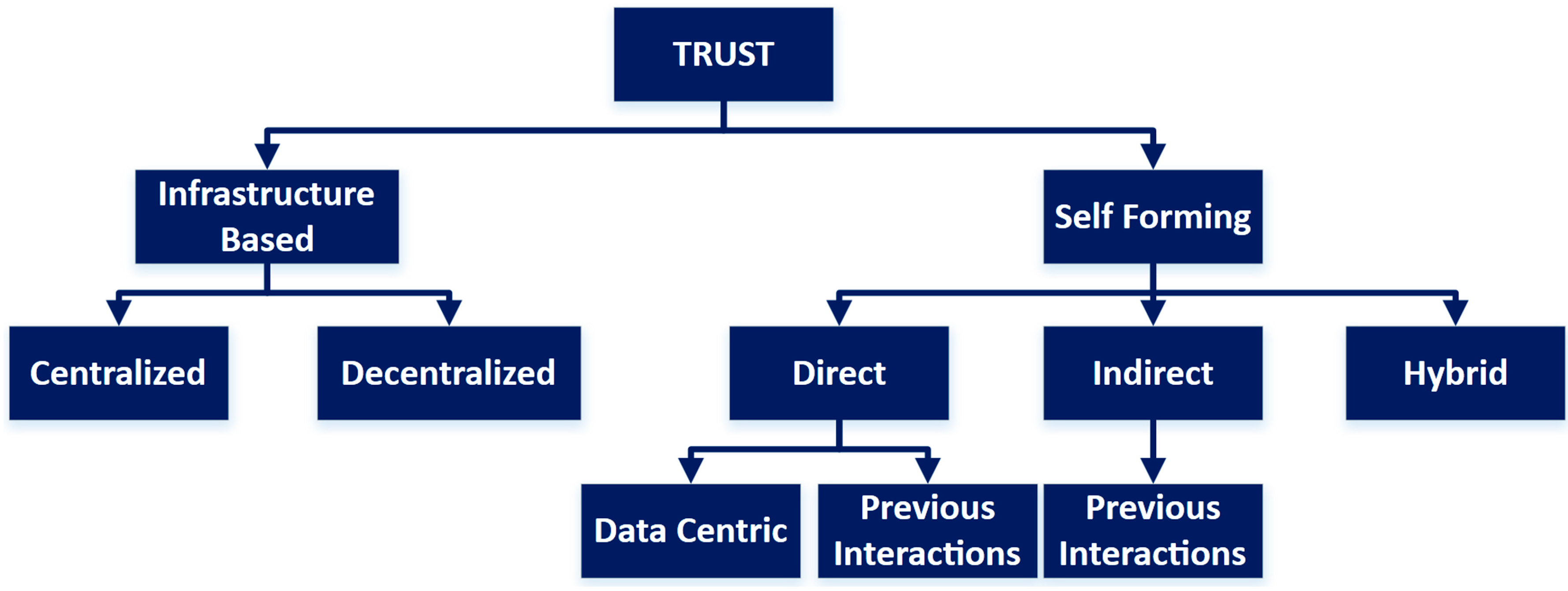
7.2. Trust-Based Schemes
7.3. Group Signatures
7.4. Identity-Based Encryption Schemes with Pseudonyms
7.5. k-Anonymity Schemes
8. Performance Comparison
- Scalability: Scalability is a well-defined performance metric for network protocols and architectures and it means how well a system can cope with the expansion of the network while maintaining the performance standards. A LOW in this category means that the scheme is not suitable for a network in which the number of nodes can grow beyond a small number. A MED in this category means that the scheme can work well for a limited number of nodes but it should not exceed that limit. A HIGH means that the scheme is highly scalable and can work well for a very large number of nodes.
- Computing cost: The computing cost has been chosen as a metric because it is always in demand and usually it is always less than what is desired. Furthermore, experience has shown that the appetite of programs and data eats up the computing power available very quickly. We have considered the computing cost at both the RSU and OBU. This metric is especially important at the OBU end where we can have reasonable, but never excessive, computing power. A LOW here means that the computing resources required are much less than available. HIGH means that computing resources available might fall short of what is required. MED means that the computation resources are sufficient.
- Privacy: This is the fundamental requirement of all schemes studied and has been rated according to the merits and demerits of each when viewed in its entirety, e.g., in the case of pseudonym cum PKI schemes, the privacy has been rated as MED as the PNs changing and their maintenance poses a serious challenge for the successful deployment in VANETs. HIGH means strong, MED means acceptable but risky, and LOW means unacceptable or no level of privacy.
- Latency: This is another well-known parameter for networks that means delays which are experienced in a network due to any reason. A network with LOW latency is considered to be fast and vice versa.
- Cost of deployment: This parameter indicates whether the infrastructure requirements make it easy to deploy in the practical world or not. A scheme with HIGH cost of deployment is obviously high-cost and difficult to deploy, i.e., with many additions/changes to the existing network making it impractical. A scheme which gets a LOW in this metric will be low-cost to deploy and will require a few changes to the existing network to make it feasible.
| S/No | Scheme | Scalability | Computing cost | Privacy | Latency | Deployment cost | |
|---|---|---|---|---|---|---|---|
| RSU | OBU | ||||||
| 1 | Pseudonym cum PKI | HIGH | HIGH | HIGH | MED | MED | HIGH |
| 2 | Group Signatures | LOW | MED | HIGH | HIGH | HIGH | HIGH |
| 3 | Trust-Based Schemes | LOW | HIGH | HIGH | LOW | HIGH | HIGH |
| 4 | K-anonymity | LOW | MED | HIGH | HIGH | HIGH | MED |
| 5 | Identity-Based Encryption (IBE) with Pseudonyms | HIGH | MED | HIGH | HIGH | HIGH | HIGH |
| S/No | Schemes | Features | Disadvantages |
|---|---|---|---|
| 1 | Pseudonym cum PKI | (a) User privacy is achieved by using pseudonym coupled with PKI; (b) Certificates (public, private key pairs) are downloaded from trusted authority; (c) Pseudonyms are changed continuously for preserving privacy. | (a) Thousands of certificates to be downloaded to OBU; (b) Certificates need to be replenished periodically; (c) CRL has to be maintained and it keeps on changing and is time- and resource-hungry; (d) The CA can link pseudonyms with vehicles, and therefore have to be secure. |
| 2 | Group Signatures | (a) Privacy achieved by forming groups; (b) Reduced transmission by ways of periodic broadcasts by a single member of group. | (a) TA can reveal the real identity of user (b) CRL has to be maintained and checked and it increases with the size of the group. |
| 3 | Trust-Based Schemes | Information accepted based on trust. Trust established based on previous record in a centralized authority or based on current and previous interactions with the user in the same session. | (a) No initial trust information available as centralized system would be too slow/too huge; (b) Protection against inside attackers is difficult; (c) Trust score has to be maintained and checked. |
| 4 | K-anonymity | (a) Messages are disseminated by ways of flooding it to neighbours; (b) Ensures privacy as long as size of group is adequate. | Flooding is used to disseminate messages which if not effective, can overwhelm the network and eat up bandwidth for the same message. Efficient and practical algorithm missing. |
| 5 | Identity-Based Encryption (IBE) With Pseudonyms | (a) User’s public key is derived from his public identification such as VIN, etc., which eliminates the need for public key distribution (b) No need for certificate downloads and storage in OBUs (c) Additional information such as a time stamp can also be added. | (a) Secure channel needed for private key distribution; (b) PKG has to be highly secure; (c) TRA can reveal the real identity of the user, therefore must be secure; (d) Revocation is still an open problem. |
9. Challenges
9.1. Security
9.2. Privacy
9.3. Cost
10. Possible Solutions to Security Issues
| Parameter | Value |
|---|---|
| Simulation Time | 500 s |
| Scenario | 3 Lane Highway |
| Highway Length | 5-Kms |
| Max Vehicle Speed | 28 m/s or 100 Km/h |
| Mobility Tool | VACaMobil |
| Network Simulation Package | OMNET++ |
| Vehicular Traffic Generation Tool | SUMO |
| Number of Vehicles | 330 |
| Vehicle Density | 20–30 veh/Km |
| Wireless Protocol | 802.11p |
| Transmission Range | 500 m in each direction |
11. Conclusions
Author Contributions
Conflicts of Interest
References
- The Telegraph. Available online: http://tinyurl.com/telegraph-co-uk-finance-budget (accessed on 10 June 2015).
- General Motors. Available online: http://media.gm.com/media/us/en/gm/news.detail.html/content/Pages/news/us/en/2013/Feb/0225_4g-lte.html (accessed on 10 June 2015).
- IEEE Intelligent Transportation System Society. Available online: http://its.ieee.org/2014/09/15/you-wont-need-a-drivers-license-by-2040/ (accessed on 07 June 2015).
- Ford. Available online: https://developer.ford.com/ (accessed on 09 June 2015).
- General Motors. Available online: https://developer.gm.com/ (accessed on 10 June 2015).
- Hartenstein, H.; Laberteaux, K.P. A Tutorial Survey on Vehicular Adhoc Networks. IEEE Commun. Mag. 2008, 46, 164–171. [Google Scholar] [CrossRef]
- Faezipour, M.; Nourani, M.; Saeed, A.; Addepalli, S. Progress and Challenges in Intelligent Vehicle Area Networks. Commun. ACM 2012, 55, 90–100. [Google Scholar] [CrossRef]
- Haas, J.J.; Hu, Y.; Laberteaux, K.P. Real-World VANET Security Protocol Performance. In Proceedings of the IEEE GLOBECOM 2009, Global Telecommunications Conference, Honolulu, HI, USA, 30 November–4 December 2009.
- United States Department of Transportation. Available online: http://www.its.dot.gov/connected_vehicle/connected_vehicle_apps.htm (accessed on 09 June 2015).
- Ericsson. Available online: http://archive.ericsson.net/service/internet/picov/get?DocNo=28701-FGD101192&Lang=EN&HighestFree=Y (accessed on 08 June 2015).
- The SARTRE Project. Available online: http://www.sartre-project.eu/en/Sidor/default.aspx (accessed on 09 June 2015).
- New Scientist. Available online: http://tinyurl.com/newscientist-com-article (09 June 2015).
- Benin, J.; Nowatkowski, M.; Owen, H. Unified pseudonym distribution in VANETs. In Proceedings of the 2010 IEEE 6th International Conference on Wireless and Mobile Computing, Networking and Communications (WiMob), Niagara Falls, ON, USA, 11–13 October 2010; pp. 529–533.
- Vehicle Safety Communications Project Final Report: Identify Intelligent Vehicle Safety Applications Enabled by DSRC; DOT HS 809 859; U.S. Department of Transportation, National Highway Traffic Safety Administration: Washington, DC, USA, 2005.
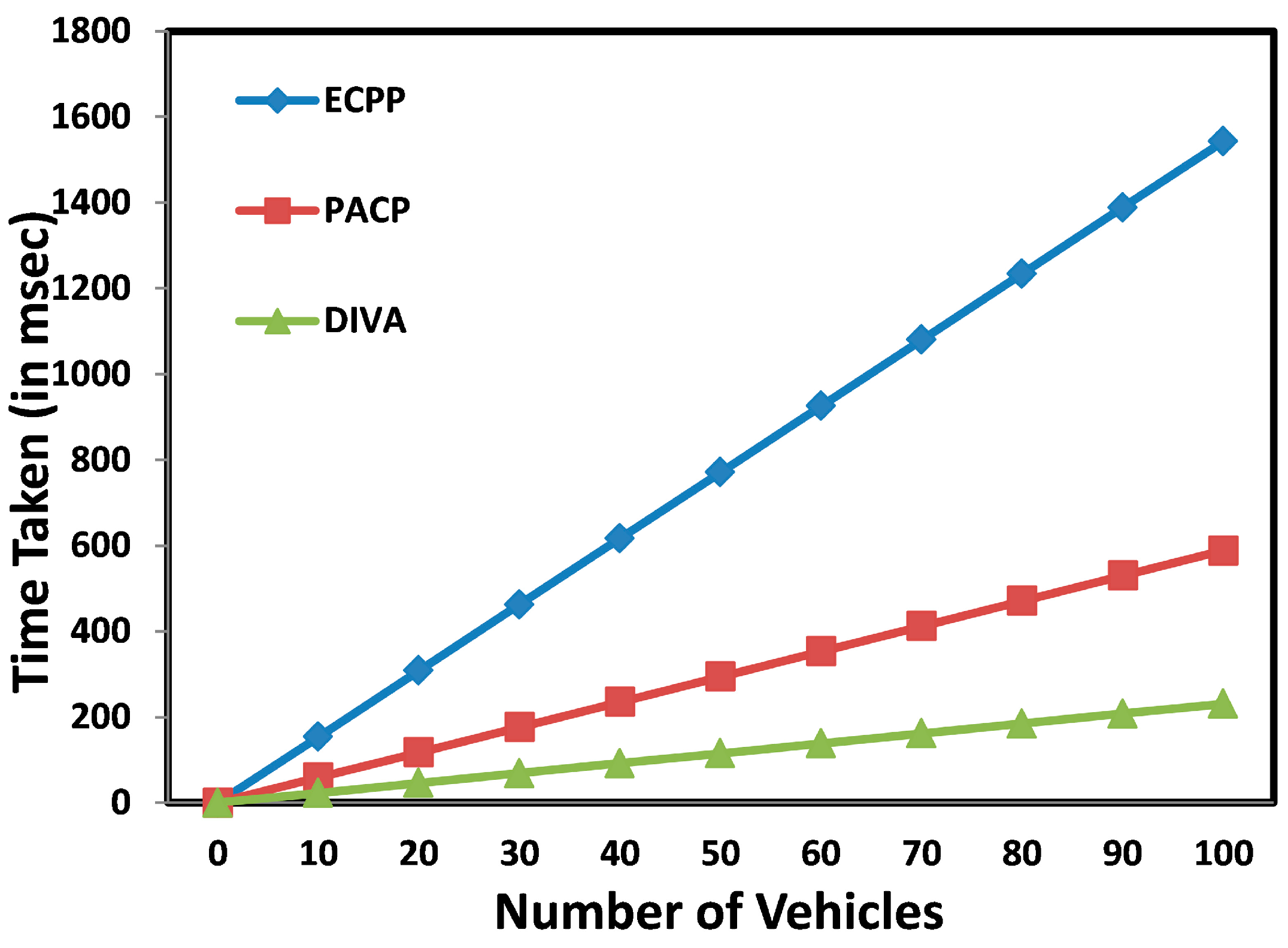
- Zaidi, K.; Rahulamathavan, Y.; Rajarajan, M. DIVA-Digital Identity in VANETs: A multi-authority framework for VANETs. In Proceedings of the 2013 19th IEEE International Conference on Networks (ICON), Singapore, Singapore, 11–13 December 2013; pp. 1–6.
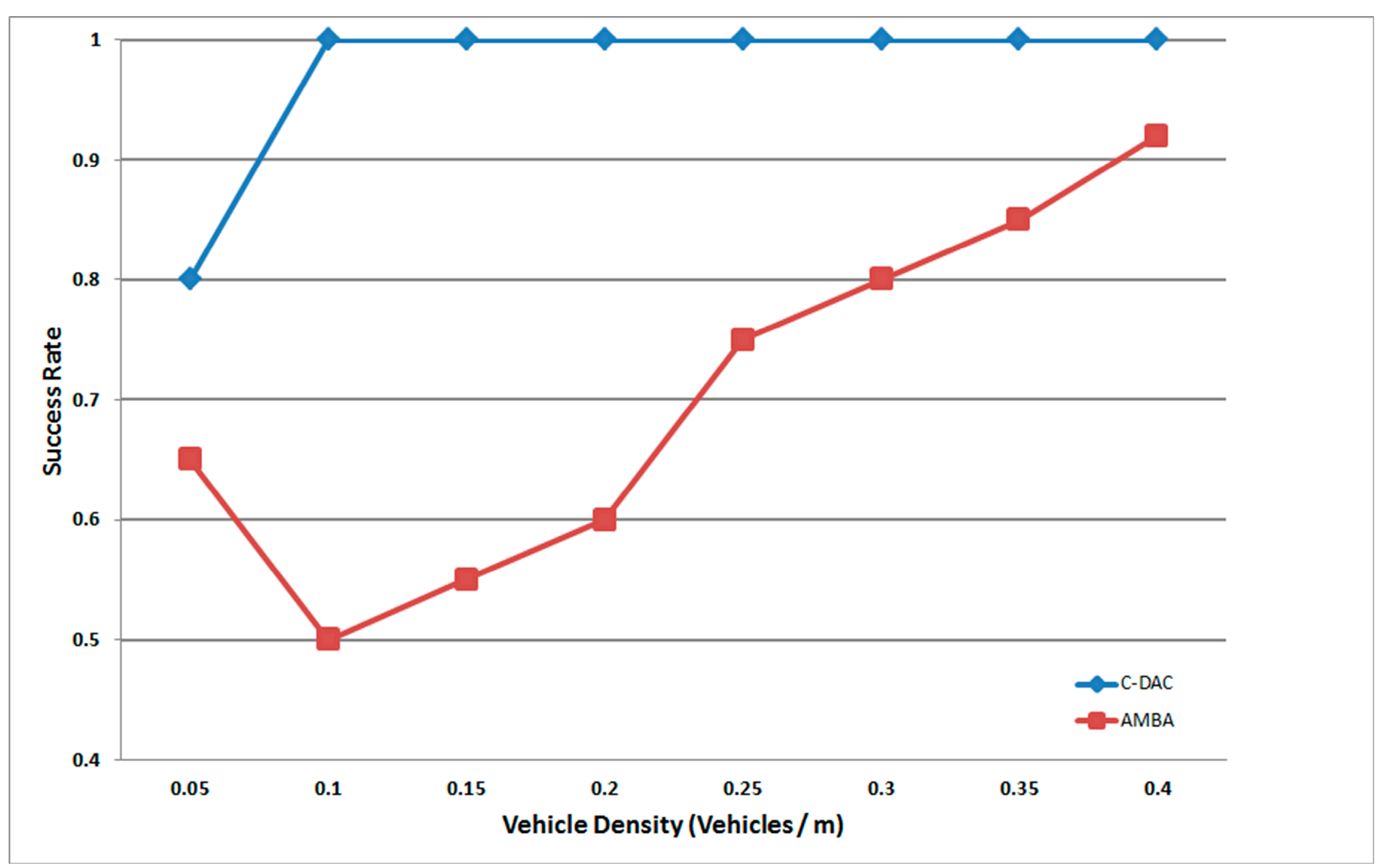
- Abumansoor, O.; Boukerche, A. Towards a Secure Trust Model for Vehicular Ad Hoc Networks Services. In Proceedings of the 2011 IEEE Global Telecommunications Conference (GLOBECOM 2011), Houston, TX, USA, 5–9 December 2011; pp. 1–5.
- Liu, B.; Chiang, J.; Haas, J.; Hu, Y. Short paper: A practical view of “mixing” identities in vehicular networks. In WiSec’11, Proceedings of the Fourth ACM Conference on Wireless Network Security; ACM: New York, NY, USA, 2011; pp. 157–162. [Google Scholar]
- Studer, A.; Shi, E.; Bai, F.; Perrig, A. TACKing Together Efficient Authentication, Revocation, and Privacy in VANETs. In Proceedings of the 6th Annual IEEE Communications Society Conference on Sensor, Mesh and Ad Hoc Communications and Networks (SECON’09), Rome, Italy, 22–26 June 2009; pp. 1–9.
- Benin, J.; Nowatkowski, M.; Owen, H. Framework to Support Per Second Shifts of Pseudonyms in Regional VANETs. In Proceedings of the 2010 IEEE 72nd Vehicular Technology Conference, Fall (VTC 2010-Fall), Ottawa, ON, USA, 6–9 September 2010; pp. 1–5.
- Lu, R.; Lin, X.; Luan, T.H.; Liang, X.; Shen, X. Pseudonym Changing at Social Spots: An Effective Strategy for Location Privacy in VANETs. IEEE Trans. Veh. Technol. 2012, 61, 86–96. [Google Scholar]
- Haas, J.J.; Hu, Y.-C.; Laberteaux, K.P. Design and analysis of a lightweight certificate revocation mechanism for VANET. In Proceedings of VANET; ACM: New York, NY, USA, 2009; pp. 89–98. [Google Scholar]
- Raya, M.; Papadimitratos, P.; Aad, I.; Jungels, D.; Hubaux, J.-P. Eviction of misbehaving and faulty nodes in vehicular networks. IEEE J. Sel. Areas Commun. 2007, 25, 1557–1568. [Google Scholar] [CrossRef]
- Zhang, J. A Survey on Trust Management for VANETs. In Proceedings of the 2011 IEEE International Conference on Advanced Information Networking and Applications (AINA), Biopolis, Singapore, 22–25 March 2011; pp. 105–112. [CrossRef]
- Wex, P.; Breuer, J.; Held, A.; Leinmuller, T.; Delgrossi, L. Trust Issues for Vehicular Ad Hoc Networks. In Proceedings of the Vehicular Technology Conference, 2008, Singapore, Singapore, 11–14 May 2008; pp. 2800–2804. [CrossRef]
- Kargl, F.; Papadimitratos, P.; Buttyan, L.; Muter, M.; Schoch, E.; Wiedersheim, B.; Thong, T.-V.; Calandriello, G.; Held, A.; Kung, A.; et al. Secure vehicular communication systems: Implementation, performance, and research challenges. IEEE Commun. Mag. 2008, 46, 110–118. [Google Scholar] [CrossRef]
- Zaidi, K.; Milojevic, M.; Rakocevic, V.; Rajarajan, M. Data-centric Rogue Node Detection in VANETs. In Proceedings of the 2014 IEEE 13th International Conference on Trust, Security and Privacy in Computing and Communications (TrustCom), Beijing, China, 24–26 September 2014; pp. 398–405.
- Sampigethaya, K.; Huang, L.; Li, M.; Poovendran, R.; Matsuura, K.; Sezaki, K. CARAVAN: Providing location privacy for vanet. In Proceedings of the Workshop on Embedded Security in Cars (ESCAR), Cologne, Germany, 29–30 November 2005.
- Ma, D.; Tsudik, G. Security and privacy in emerging wireless networks [Invited Paper]. IEEE Wirel. Commun. 2010, 17, 12–21. [Google Scholar] [CrossRef]
- Shamir, A. Identity-based cryptosystems and signature schemes. In Advances in Crypto’84; Lecture Notes in Computer Science; Springer-Verlag: Berlin, Germany; Heidelberg, Germany, 1984; Volume 196, pp. 47–53. [Google Scholar]
- Shim, K. CPAS: An Efficient Conditional Privacy-Preserving Authentication Scheme for Vehicular Sensor Networks. IEEE Trans. Veh. Technol. 2012, 61, 1874–1883. [Google Scholar] [CrossRef]
- Lu, H.; Li, J.; Guizani, M. A Novel ID-based Authentication Framework with Adaptive Privacy Preservation for VANETs. In Proceedings of the Computing, Communications and Applications Conference (ComComAp), Hong Kong, China, 11–13 January 2012.
- Zhang, C.; Lin, X.; Lu, R.; Ho, P. RAISE: An efficient RSU-aided message authentication scheme in vehicular communication networks. In Proceedings of the IEEE International Conference on Communications (ICC’08), Beijing, China, 19–23 May 2008; pp. 1451–1457.
- Lu, R.; Lin, X.; Zhu, H.; Ho, P.H.; Shen, X. ECPP: Efficient Conditional Privacy Preservation Protocol for Secure Vehicular Communications. In Proceedings of the IEEE 27th Conference on Computer Communications, Phoenix, AZ, USA, 13–18 April 2008; pp. 1229–1237.
- Dijiang, H.; Misra, S.; Verma, M.; Xue, G. PACP: An Efficient Pseudonymous Authentication-Based Conditional Privacy Protocol for VANETs. IEEE Trans. Intell. Transp. Syst. 2011, 12, 736–746. [Google Scholar]
- Behrisch, M.; Bieker, L.; Erdmann, J.; Krajzewicz, D. Sumo-Simulation of Urban Mobility: An overview. In Proceedings of the SIMUL 2011, the 3rd International Conference on Advances in System Simulation, Barcelona, Spain, 23–29 October 2011; pp. 63–68.
- Baguena, M.; Tornell, S.; Torres, A.; Calafate, C.; Cano, J.-C.; Manzoni, P. Vacamobil: Vanet car mobility manager for omnet++. In Proceedings of the 2013 IEEE International Conference on Communications Workshops (ICC), Budapest, Hungary, 9–13 June 2013; pp. 1057–1061.
- Hafeez, K.A.; Zhao, L.; Ma, B.; Mark, J.W. Performance Analysis and Enhancement of the DSRC for VANET’s Safety Applications. IEEE Trans. Veh. Technol. 2013, 62, 3069–3083. [Google Scholar] [CrossRef]
© 2015 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Zaidi, K.; Rajarajan, M. Vehicular Internet: Security & Privacy Challenges and Opportunities. Future Internet 2015, 7, 257-275. https://doi.org/10.3390/fi7030257
Zaidi K, Rajarajan M. Vehicular Internet: Security & Privacy Challenges and Opportunities. Future Internet. 2015; 7(3):257-275. https://doi.org/10.3390/fi7030257
Chicago/Turabian StyleZaidi, Kamran, and Muttukrishnan Rajarajan. 2015. "Vehicular Internet: Security & Privacy Challenges and Opportunities" Future Internet 7, no. 3: 257-275. https://doi.org/10.3390/fi7030257
APA StyleZaidi, K., & Rajarajan, M. (2015). Vehicular Internet: Security & Privacy Challenges and Opportunities. Future Internet, 7(3), 257-275. https://doi.org/10.3390/fi7030257





