Survey on Biometric Authentication for Decentralized Identity Management: Trends, Challenges, and Future Directions
Abstract
1. Introduction
Background and Motivation
2. Survey Focus, Research Questions and Methodology
2.1. Research Questions
- RQ1: What trade-offs characterize decentralized identity systems in balancing user autonomy and security with scalability, interoperability, and trust?
- RQ2: In what ways does biometric authentication outperform or fall short of traditional methods in securing digital identities, especially within decentralized identity frameworks?
- RQ3: What approaches integrate biometric authentication into decentralized identity systems, and how effective are privacy-preserving techniques in ensuring security?
- RQ4: How does the adoption of multimodal biometrics within decentralized identity frameworks create new opportunities for security and usability, and what trade-offs does it entail?
- RQ5: What are the key research gaps and future directions for developing robust, scalable, and secure biometric authentication systems for decentralized identity?
2.2. Methodology: PRISMA-Based Systematic Literature Review
2.2.1. Identification
2.2.2. Screening
2.2.3. Eligibility
- Inclusion Criteria (IC):Studies were deemed eligible for inclusion if they satisfied the following criteria:
- –
- IC1: Published between 2020 and 2025;
- –
- IC2: Written in English;
- –
- IC3: Propose, evaluate, or review biometric authentication methods, either unimodal or multimodal, within the scope of decentralized identity (DID) systems.
- –
- IC4: Address issues of security, privacy, scalability, interoperability or regulatory compliance in biometric-enabled identity frameworks;
- –
- IC5: Published in established scientific outlets, including peer-reviewed journals, conference proceedings, preprints, or academic books offering conceptual or methodological insights.
- Exclusion Criteria (EC): Studies were excluded if they fulfilled any of the following:
- –
- EC1: Not published in English;
- –
- EC2:Did not address biometric authentication in decentralized identity systems (focused on general cybersecurity, non-biometric authentication methods, or centralized identity models);
- –
- EC3: Appeared in non-academic or informal sources, including blogs, online articles, web pages, social media content, editorials, lecture notes, or unpublished theses;
- –
- EC4: Lacked methodological rigor, provided insufficient technical depth, or failed to clearly define its scientific contribution;
- –
- EC5: Represented duplicate or substantially redundant publications already covered by other included studies.
3. RQ1: What Trade-Offs Characterize Decentralized Identity Systems in Balancing User Autonomy and Security with Scalability, Interoperability, and Trust?
3.1. Decentralized Identity System
3.1.1. From Centralized to Decentralized Identity: Evolution of Identity Models
3.1.2. Workflow of Decentralized Identity Systems
- DID Generation: A user or entity generates a Decentralized Identifier (DID) by first generating a cryptographic key pair (public and private keys) to enable secure identity verification and authentication [10,16]. Next, a DID Document is assembled, containing essential components such as public keys, service endpoints, and relevant metadata. This document is then published to a decentralized network, such as a blockchain or distributed ledger, using a specific DID method (did:ethr, did:sov, did:ion) [10,16,17,18]. This process ensures that the DID is globally resolvable and cryptographically verifiable, establishing a secure and interoperable identity anchor within decentralized ecosystems.
- Credential Issuance: Once a DID is established, trusted issuers (governments, universities, or service providers) issue Verifiable Credentials (VCs) to the holder. The issuer verifies the user’s real-world attributes (such as identity or qualifications) and generates a digitally signed VC containing the corresponding claims and metadata. The credential is then transmitted to the user and securely stored in a digital wallet, which manages DIDs, credentials, and associated cryptographic keys in a privacy-preserving manner [2,10,14,16,19,20].
- Credential Presentation: When proving identity or claims, the user creates a Verifiable Presentation (VP), often using zero-knowledge proofs to disclose only necessary information. The VP is signed with the user’s private key, ensuring authenticity and integrity.
- Verification: The verifier retrieves the DID Document from the blockchain to verify authenticity, then validates the VC’s signature using the issuer’s public key. It also checks for revocation, expiry, and confirms the presenter’s control over the DID via cryptographic challenge-response. If all checks pass, the credential is accepted; otherwise, it is rejected. This process ensures secure, verifiable, and privacy-preserving identity and claim validation [2,17,20].
3.1.3. Trade-Offs in Decentralized Identity Systems
4. RQ2: In What Ways Does Biometric Authentication Outperform or Fall Short of Traditional Methods in Securing Digital Identities, Especially Within Decentralized Identity Frameworks?
5. RQ3: What Approaches Integrate Biometric Authentication into Decentralized Identity Systems, and How Effective Are Privacy-Preserving Techniques in Ensuring Security?
5.1. Integration of Biometrics into the DID Systems
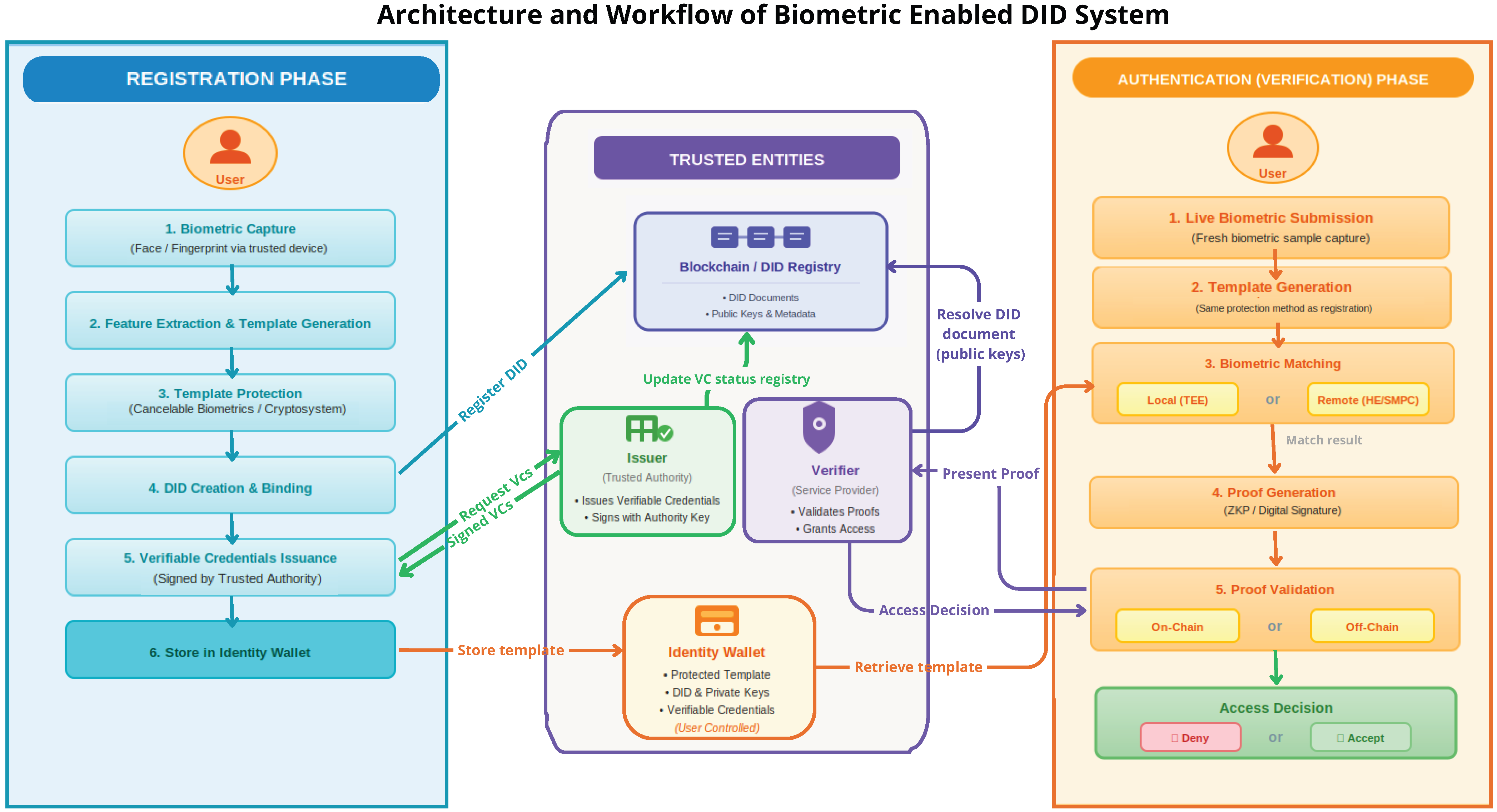
5.1.1. Architecture and Workflow of Biometric-Enabled Decentralized Identity Systems
- Registration (Enrollment) Phase: The registration phase involves securely capturing and linking the user’s biometric identity to a decentralized identifier (DID). This phase proceeds as follows:
- 1.
- Biometric Capture: A user provides biometric input (face, fingerprint) through a trusted capture device, typically a smartphone or kiosk equipped with secure sensors.
- 2.
- Feature Extraction and Template Generation: Once the biometric data is collected, it undergoes preprocessing to remove noise and enhance quality. This may include normalization, alignment, and contrast adjustment, depending on the modality. The system then applies feature extraction techniques to identify the most relevant and distinguishing characteristics of the biometric signal. These features are used to generate biometric templates using either traditional methods or AI-based approaches. The resulting template captures the unique traits of the user in a compressed, efficient, and discriminative format suitable for matching and verification.
- 3.
- Template Protection:To prevent security and privacy risks, the raw biometric template is never stored or transmitted directly. Instead, it is transformed using a protection mechanism such as cancelable biometrics or a biometric cryptosystem. This transformation ensures that the stored template is non-invertible.
- 4.
- DID Creation and Binding: The user creates a decentralized identifier (DID), which is associated with the protected biometric template through Metadata linkage (in the DID document or off-chain storage reference), Or cryptographic commitments (Pedersen commitments or zk-SNARKs) that prove possession of the biometric without revealing it.
- 5.
- Issuance of Verifiable Credentials (VCs): A trusted authority may issue one or more verifiable credentials that attest to identity attributes. These credentials are cryptographically signed and linked to the user’s DID, optionally incorporating biometric-based challenge-response proofs during issuance.
- 6.
- Store Identity Artifacts Locally: All sensitive identity components, including the protected biometric template, the user’s DID, and any Verifiable Credentials, are securely stored on the user’s personal device—typically in a digital identity wallet or secure enclave. These components are under the user’s control and are not stored on-chain, ensuring that sensitive data remains private and decentralized.
- Authentication (Verification) Phase: In the authentication phase, the user proves control over the DID and biometric credential by repeating the biometric process and submitting a proof of identity to the verifier.
- 1.
- Biometric Verification Attempt: The user submits a live biometric sample, from which a fresh template is generated and protected using the same method as during registration.
- 2.
- Matching Process: The biometric matching process in decentralized identity systems can be performed either locally or remotely, depending on system design and privacy requirements. In local (on-device) matching, the fresh biometric template is compared directly with the reference template stored securely on the user’s device, often within a trusted execution environment (TEE) or secure enclave. This approach offers low latency and eliminates the need to transmit sensitive data externally. In contrast, remote or off-chain matching involves transmitting the protected biometric template (typically encrypted) to an external verifier for processing. To preserve privacy in this setting, advanced cryptographic techniques are employed. Homomorphic encryption enables matching over encrypted templates without revealing biometric data [4], while secure multiparty computation (SMPC) allows multiple parties to jointly compute a match score without disclosing their respective inputs [61]. These methods ensure that biometric verification remains secure and privacy-preserving, even in untrusted environments.
- 3.
- Proof Generation: Upon a successful biometric match, the system generates a cryptographic proof binding the authentication result to the user’s DID without exposing sensitive data. This can be done via zero-knowledge proofs (ZKPs) that confirm the match without revealing the biometric data or the template itself [62]. Alternatively, the user can sign a challenge using their DID-linked private key. In scenarios where verifiable credentials (VCs) are involved, the user may present these credentials to a verifier, optionally applying selective disclosure or ZKP-based credential presentation (such as BBS+ signatures or JSON-LD ZKPs) to reveal only the necessary claims while maintaining privacy.
- 4.
- Proof Validation and Access: After generating a cryptographic proof of successful biometric authentication, the user submits it to a verifier for validation and access authorization. This process can occur either on-chain or off-chain, depending on the system design. In on-chain validation, a smart contract verifies the proof, such as a zero-knowledge proof (ZKP) or digital signature, using public keys stored in the user’s DID document. If valid, the contract confirms the user’s identity and automatically triggers predefined actions, such as granting access to digital assets, executing transactions, or updating identity records. In off-chain validation, a verifier retrieves the DID document and checks the proof or verifiable credential through cryptographic methods, including signature and integrity verification. Upon successful validation, the verifier authorizes access such as logging the user into a service, unlocking a device, or assigning system permissions.
5.1.2. Integration Challenges and Architectural Trade-Offs in Biometric-Based Decentralized Identity Systems
- Overview of Research Objectives and Reported Challenges: Biometric-based Decentralized Identity (DID) systems offer a compelling alternative to traditional identity management systems by enhancing security, promoting user sovereignty, and reducing reliance on centralized authorities. However, integrating privacy-preserving biometric authentication into decentralized architectures introduces architectural trade-offs and systemic limitations that challenge practical implementation, scalability, and interoperability. To better understand the current state of research on biometric-enabled DID systems, it is essential to examine the objectives, contributions, and challenges reported in the literature. Table 2 summarizes key findings from representative research papers, presenting their stated objectives, primary contributions, and the main challenges encountered in implementing biometric-based decentralized identity systems.Table 2. Objectives, Contributions, and Challenges in Biometric-Based Decentralized Identity Systems.Table 2. Objectives, Contributions, and Challenges in Biometric-Based Decentralized Identity Systems.
Reference Objective Contributions Challenges Faced [10,21,62,63,64] Design a blockchain-based biometric authentication framework aligned with decentralized identity principles Proposes a decentralized authentication protocol combining blockchain, cancelable biometrics, and zero-knowledge proofs (ZKPs); introduces template protection methods ensuring revocability; integrates DID with verifiable credentials for trustless verification High computational cost of ZKPs/Homomorphic Encryption (HE) affects scalability; template revocation remains difficult; blockchain adds latency, fees, and metadata leaks; trade-off between privacy and usability; lack of global standards for biometric-DID interoperability; limited real-world deployments, with most solutions still at prototype stage [64] Enhance security and interoperability in self-sovereign identity systems using biometrics Develops biometric-backed VC model; demonstrated cross-domain use cases (healthcare, finance); provides an architecture for binding biometric proofs to DID documents Limited interoperability due to lack of standardization; revocation of biometric-linked credentials is difficult; privacy risks in cross-domain data sharing; reliance on secure hardware (wallets, TEEs) reduces accessibility [21] Maps research on decentralized and self-sovereign identity, with attention to biometric integration Reviews 179 papers on SSI, identifying biometrics as a major authentication trend; highlights template protection techniques (fuzzy vault, fuzzy commitment); identifies blockchain and verifiable credentials as common enablers for biometric-DID systems Fragmentation of approaches: no unified global standards for biometrics in DID; privacy-preserving methods (SMPC, HE, FL) still impractical at scale; real-world deployments are limited; persistent tension between usability and strong security [8] Develop a framework integrating biometric capture, preprocessing, and template protection with blockchain; propose DID and VC issuance via smart contract-based verification Introduces end-to-end integration of biometric processing and blockchain-based verification Biometrics irreversible if leaked; blockchain scalability and high costs; compliance challenges with GDPR/CCPA; algorithmic bias in recognition; adoption barriers (cost, literacy) [65] Examine how DIDs and biometrics can jointly enable self-sovereign identity systems Showed DIDs with biometrics improve privacy and user control; emphasized W3C standards, VCs, and selective disclosure Blockchain scalability bottlenecks; interoperability gaps; risks from improper biometric handling; regulatory conflicts across regions; limited real-world adoption studies - DID-Specific Integration Challenges and Architectural Implications: Decentralized identity (DID) architectures fundamentally alter biometric authentication by redistributing trust and control across wallets, issuers, and verifiers. Consequently, biometric integration in DID systems introduces distinct architectural constraints that affect matching location, protection mechanisms, and stakeholder trade-offs. A first critical implication of this shift concerns where biometric matching is performed. In this context, local biometric matching is particularly well suited for wallet-centric operations where biometrics serve as local authorization rather than global identity verification. It is typically used to unlock the identity wallet, release cryptographic keys, and authorize verifiable credential presentations [66,67]. In this model, biometric data remain on the user’s device and are not shared with issuers or verifiers. This preserves self-sovereignty and limits cross-service linkability. As a result, local matching is appropriate for low- to medium-assurance scenarios, such as accessing digital services, signing transactions, or proving credential possession. However, this approach provides limited verifiable assurance to external parties. It also shifts trust to the wallet software, operating system, and device manufacturer. These factors restrict its applicability in regulated or adversarial environments [66]. In contrast, remote biometric matching is intended for DID scenarios requiring stronger identity guarantees. Examples include remote onboarding, cross-border identity verification, and access to regulated services. These scenarios require verifiers to establish a robust binding between biometric traits and claimed identities beyond the local wallet, introducing significant privacy and architectural challenges. In particular, remote matching risks re-centralizing biometric processing and weakening user control. Although privacy-enhancing techniques such as zero-knowledge proofs or secure multiparty computation have been proposed, their computational cost, protocol complexity, and integration overhead limit real-world deployment [68]. Consequently, most remote biometric verification architectures remain at the proof-of-concept stage and fail to scale beyond controlled environments. In addition to the matching location, the roles of decentralized identifiers (DIDs), verifiable credentials, and identity wallets strongly constrain biometric protection and authentication choices in decentralized identity systems. Wallets primarily safeguard private keys, credentials, and user consent; consequently, biometrics are mainly used as local authenticators to protect cryptographic material rather than for continuous or global identity recognition. This naturally favors on-device matching and hardware-backed isolation [66]. When biometrics are involved in credential issuance or high-assurance verification, core DID principles—such as selective disclosure, unlinkability, and data minimization—make centralized biometric storage and matching unsuitable. As a result, system designs increasingly rely on privacy-enhancing techniques, including cancelable biometrics, biometric cryptosystems, and zero-knowledge-based verification. However, many of these approaches remain difficult to deploy in practice due to incompatibilities with wallet-centric architectures and resource-constrained environments. Finally, biometric authentication in DID ecosystems involves stakeholders with divergent priorities. Users prioritize usability and privacy, favoring fast, local biometric authentication without external data exposure. Wallet providers balance usability, security, and liability, typically relying on platform biometric APIs and trusted hardware to avoid direct biometric handling. In contrast, issuers and verifiers emphasize assurance, fraud resistance, and regulatory compliance, often favoring stronger or remote biometric verification at the cost of usability or privacy. Regulators further impose auditability and data protection requirements, adding additional constraints. These competing objectives cannot be jointly optimized within a single biometric–DID architecture, which explains why many existing solutions implicitly favor specific stakeholders and struggle to scale across domains.
- Scalability limits from heavy cryptography, AI biometrics, and blockchain latency/fees.
- Privacy and compliance risks due to biometric immutability, storage overhead, and weak governance.
- Security issues including spoofing, fragile key management, and poor revocation.
- Interoperability gaps stemming from limited standardization across DID methods, credential formats, biometric representations, and blockchain platforms.
- Usability challenges from complex workflows, enrollment errors, weak recovery.
- Governance and centralization risks from third-party reliance and unclear oversight.
- Regulatory and ethical uncertainties around biometric data collection, compliance and adoption risks.
- Ecosystem immaturity with most solutions still at prototype stage, weak tooling, and limited real-world deployment.
5.2. Privacy-Preserving Techniques for Biometric Identity in Decentralized Identity Systems
5.2.1. Template Protection Techniques
- Cancellable Biometrics: Cancelable biometrics are a privacy-preserving approach that transforms original biometric data using a non-invertible function before storage, ensuring the stored template cannot be reversed to reveal the original features. If compromised, templates can be revoked and regenerated by applying a different transformation, offering reusability and security. Techniques such as bio-hashing, salting with random projections, geometric and feature-space transformations, block permutation, and surface folding are used to make reconstruction of the original data computationally infeasible, while enabling secure and flexible template management [69,70,71,72].
- Biometric Cryptosystems: Biometric cryptosystems are advanced template protection methods that combine biometric data with cryptographic techniques. Their primary purpose is either to secure a cryptographic key using biometric characteristics or to generate a key directly from the unique features of an individual’s biometric data. In biometric cryptosystems, securing cryptographic keys involves two main strategies: key generation and key binding, each addressing the challenge of biometric variability while preserving security and privacy. In key generation, cryptographic keys are derived directly from biometric inputs using primitives like secure sketches and fuzzy extractors. Secure sketches enable recovery of the original or a close approximation of a biometric sample from a noisy input without revealing significant biometric information, while fuzzy extractors generate stable, uniformly random keys and accompanying helper data that allow reliable key regeneration from similar future samples. These mechanisms provide strong error tolerance and privacy guarantees, making them ideal for decentralized identity systems that avoid persistent key storage [73,74,75,76]. In contrast, key binding securely associates an existing key with a biometric template such that the key can only be retrieved when a closely matching biometric sample is presented. Even if the helper data is exposed, neither the key nor the biometric can be reconstructed without the correct input [74,77]. Two prominent constructions for key binding are the fuzzy vault, which encodes a key into a polynomial hidden among biometric and chaff points [78,79], and the fuzzy commitment, which uses error-correcting codes to bind a key to binary biometric data, enabling recovery and verification via hashing [58,80,81]. Both methods offer robust protection against biometric noise and unauthorized access, making them foundational tools in privacy-preserving biometric authentication.
5.2.2. Privacy-Preserving Techniques for Computation and Verification
- Zero-Knowledge Proofs (ZKPs): Zero-Knowledge Proofs (ZKPs) allow users to prove possession of valid biometric credentials or a match with stored templates without revealing the biometric data itself, ensuring privacy even on public blockchains. They also enable selective disclosure, letting users reveal only chosen attributes or prove knowledge of a key linked to biometric secrets. Efficient variants like zk-SNARKs and zk-STARKs make ZKPs suitable for smart contracts in decentralized identity systems, though their high computational cost poses challenges for use on lightweight or edge devices [82,83,84].
- Homomorphic Encryption (HE): Homomorphic Encryption (HE) enables computations directly on encrypted biometric data, allowing identity verification without ever exposing raw features. In biometric systems, templates are encrypted during enrollment and stored securely; during authentication, the fresh sample is also encrypted and compared through ciphertext-based similarity checks. This ensures that neither matching scores nor biometric data are exposed, protecting against reconstruction attacks in decentralized settings, though the high computational cost of Fully Homomorphic Encryption (FHE) limits real-time use, making lighter HE variants more practical for biometric applications [85,86].
- Secure Multiparty Computation (SMPC): Secure Multiparty Computation (SMPC) enables multiple parties to jointly compute functions over private biometric data without revealing it, ensuring privacy and correctness even under semi-honest or malicious threat models. Techniques like Yao’s Garbled Circuits and the BGW/GMW protocols support decentralized biometric verification aligned with DIDs, though the approach remains resource-intensive due to its communication and computation overhead [61,87].
5.2.3. Decentralized Learning and Privacy-Aware Model Training
- Federated Learning: Federated Learning (FL) is increasingly recognized as an important mechanism for enabling privacy-aware training of biometric models in decentralized identity (DID) systems, as it avoids the need to centralize sensitive biometric data while still allowing collaborative model improvement [88,89,90]. By keeping raw biometric samples on user devices and aggregating only model updates, FL aligns well with the principles of data minimization, user sovereignty, and decentralized trust that underpin DID architectures. Across the literature, FL is shown to mitigate large-scale data leakage risks and to support the development of robust biometric recognition and liveness detection models in distributed and cross-organizational settings [88,89]. Recent studies show that federated learning mitigates the privacy–data accessibility trade-off in deep biometric systems while preserving accuracy and generalization, supporting its use in decentralized identity environments with fragmented data [89,90]. However, the effectiveness of FL in biometric-enabled DID systems is constrained by several limitations. Biometric data are typically highly heterogeneous and non-IID due to variations in sensors, acquisition conditions, and user populations, which can negatively impact convergence and accuracy under standard federated optimization schemes [91]. In addition, FL alone does not provide strong privacy guarantees, as model updates may still leak sensitive information through inference or reconstruction attacks, necessitating complementary protections such as secure aggregation or differential privacy. Practical deployment is further challenged by communication overhead, device variability, and limited standardization. As a result, while federated learning is a promising building block for privacy-preserving biometric-DID systems, it remains insufficient as a standalone solution.
- Differential Privacy: Differential Privacy (DP) offers formal and quantifiable protection against biometric data leakage by introducing calibrated noise that limits the influence of any single individual on released outputs or learned models. In biometric-enabled decentralized identity (DID) systems, DP is primarily applied during biometric model training or update sharing, where it mitigates inference and reconstruction attacks on sensitive biometric information. When combined with Federated Learning, DP is typically enforced by perturbing local model updates before aggregation, thereby strengthening privacy guarantees while preserving collaborative learning across distributed users [92]. However, the effectiveness of DP depends on careful calibration of the privacy budget, as excessive noise can degrade biometric recognition accuracy, highlighting an inherent trade-off between privacy strength and system performance.
6. RQ4: How Does the Adoption of Multimodal Biometrics Within Decentralized Identity Frameworks Create New Opportunities for Security and Usability, and What Trade-Offs Does It Entail?
6.1. Unimodal vs. Multimodal Biometric Authentication: A Comparative Analysis
6.2. Multimodal Fusion Strategies and Their Relevance to DID Architectures
6.3. Opportunities and Challenges of Multimodal Biometric Authentication in Decentralized Identity Systems
7. RQ5: What Are the Key Research Gaps and Future Directions for Developing Robust, Scalable, and Secure Biometric Authentication Systems for Decentralized Identity?
7.1. Privacy–Efficiency Trade-Offs and Scalability Constraints
7.2. Biometric Lifecycle Management and Revocability
7.3. Standardization and Interoperability Across DID and Biometric Ecosystems
7.4. Usability and Inclusiveness
7.5. Governance, Trust, and Real-World Validation
8. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
Abbreviations
| RQ | Research Question |
| DID | Decentralized Identity |
| ZKP | Zero-knowledge Proof |
| FL | Federated Learning |
| DP | Differential Privacy |
| SMPC | Secure Multi-Party Computation |
References
- Le, H.V.A.; Nguyen, Q.D.N.; Tadashi, N.; Tran, T.H. Blockchain-Based Decentralized Identity Management System with AI and Merkle Trees. Computers 2025, 14, 289. [Google Scholar] [CrossRef]
- Ahmed, M.; Islam, A.K.M.; Shatabda, S.; Islam, S. Blockchain-Based Identity Management System and Self-Sovereign Identity Ecosystem: A Comprehensive Survey. IEEE Access 2022, 10, 113436–113481. [Google Scholar] [CrossRef]
- Albalawi, S.; Alshahrani, L.; Albalawi, N.; Kilabi, R.; Alhakamy, A. A comprehensive overview on biometric authentication systems using artificial intelligence techniques. Int. J. Adv. Comput. Sci. Appl. 2022, 13, 1–11. [Google Scholar] [CrossRef]
- Marcolla, C.; Sucasas, V.; Manzano, M.; Bassoli, R.; Fitzek, F.H.; Aaraj, N. Survey on Fully Homomorphic Encryption: Theory and Applications. Proc. IEEE 2022, 110, 1572–1609. [Google Scholar] [CrossRef]
- Lindell, Y. Secure Multiparty Computation. Commun. ACM 2020, 64, 86–96. [Google Scholar] [CrossRef]
- Sun, X.; Yu, F.R.; Zhang, P.; Sun, Z.; Xie, W.; Peng, X. A survey on zero-knowledge proof in blockchain. IEEE Netw. 2021, 35, 198–205. [Google Scholar] [CrossRef]
- De Keyser, A.; Bart, Y.; Gu, X.; Liu, S.Q.; Robinson, S.G.; Kannan, P.K. Opportunities and Challenges of Using Biometrics for Business: Developing a Research Agenda. J. Bus. Res. 2021, 136, 52–62. [Google Scholar] [CrossRef]
- Gudala, L.; Reddy, A.K.; Sadhu, A.K.R.; Venkataramanan, S. Leveraging biometric authentication and blockchain technology for enhanced security in identity and access management systems. J. Artif. Intell. Res. 2022, 2, 21–50. [Google Scholar]
- Ogunmakinde, O.E.; Egbelakin, T.; Sher, W.; Omotayo, T.; Ogunnusi, M. Establishing the Limitations of Sustainable Construction in Developing Countries: A Systematic Literature Review Using PRISMA. Smart Sustain. Built Environ. 2024, 13, 609–624. [Google Scholar] [CrossRef]
- Dib, O.; Rababah, B. Decentralized Identity Systems: Architecture, Challenges, Solutions and Future Directions. Ann. Emerg. Technol. Comput. 2020, 4, 19–40. [Google Scholar] [CrossRef]
- Soltani, R.; Nguyen, U.T.; An, A. A Survey of Self-Sovereign Identity Ecosystem. Secur. Commun. Netw. 2021, 2021, 8873429. [Google Scholar] [CrossRef]
- Hosseini, S.M.; Ferreira, J.; Bartolomeu, P.C. Blockchain-Based Decentralized Identification in IoT: An Overview of Existing Frameworks and Their Limitations. Electronics 2023, 12, 1283. [Google Scholar] [CrossRef]
- Kyriakidou, D.N.; Papathanasiou, A.M.; Polyzos, G. Decentralized Identity with Applications to Security and Privacy for the Internet of Things. Comput. Netw. Commun. 2023, 1, 244–271. [Google Scholar] [CrossRef]
- Mazzocca, C.; Acar, A.; Uluagac, S.; Montanari, R.; Bellavista, P.; Conti, M. A survey on decentralized identifiers and verifiable credentials. IEEE Commun. Surv. Tutor. 2025, 27, 3641–3671. [Google Scholar] [CrossRef]
- Schumm, D.; Müller, K.O.E.; Stiller, B. Are we there yet? A study of decentralized identity applications. IEEE Access 2025, 13, 125232–125259. [Google Scholar] [CrossRef]
- Alizadeh, M.; Andersson, K.; Schelén, O. Comparative Analysis of Decentralized Identity Approaches. IEEE Access 2022, 10, 92273–92283. [Google Scholar] [CrossRef]
- Agarkar, A.A.; Karyakarte, M.; Chavhan, G.; Patil, M.; Talware, R.; Kulkarni, L. Blockchain-Aware Decentralized Identity Management and Access Control System. Meas. Sens. 2024, 31, 101032. [Google Scholar] [CrossRef]
- Satybaldy, A.; Subedi, A.; Idrees, S.M. Decentralized Key Management for Digital Identity Wallets. In Blockchain Transformations: Navigating the Decentralized Protocols Era; Springer Nature: Cham, Switzerland, 2024; pp. 47–58. [Google Scholar]
- Fang, J.; Feng, T.; Guo, X.; Wang, X. Privacy-Enhanced Distributed Revocable Identity Management Scheme Based on Self-Sovereign Identity. J. Cloud Comput. 2024, 13, 154. [Google Scholar] [CrossRef]
- Bai, Y.; Lei, H.; Li, S.; Gao, H.; Li, J.; Li, L. Decentralized and Self-Sovereign Identity in the Era of Blockchain: A Survey. In Proceedings of the 2022 IEEE International Conference on Blockchain; IEEE: Piscataway, NJ, USA, 2022; pp. 500–507. [Google Scholar]
- Čučko, Š.; Turkanović, M. Decentralized and Self-Sovereign Identity: Systematic Mapping Study. IEEE Access 2021, 9, 139009–139027. [Google Scholar] [CrossRef]
- Butincu, C.N.; Alexandrescu, A. Design Aspects of Decentralized Identifiers and Self-Sovereign Identity Systems. IEEE Access 2024, 12, 60928–60942. [Google Scholar] [CrossRef]
- Buttar, A.M.; Shahid, M.A.; Arshad, M.N.; Akbar, M.A. Decentralized identity management using blockchain technology: Challenges and solutions. In Blockchain Transformations: Navigating the Decentralized Protocols Era; Springer Nature: Cham, Switzerland, 2024; pp. 131–166. [Google Scholar]
- Moreno, R.T.; García-Rodríguez, J.; Bernabé, J.B.; Skarmeta, A. A trusted approach for decentralised and privacy-preserving identity management. IEEE Access 2021, 9, 105788–105804. [Google Scholar] [CrossRef]
- Sedlmeir, J.; Smethurst, R.; Rieger, A.; Fridgen, G. Digital identities and verifiable credentials. Bus. Inf. Syst. Eng. 2021, 63, 603–613. [Google Scholar] [CrossRef]
- Montagna, S.; Ferretti, S.; Klopfenstein, L.C.; Florio, A.; Pengo, M.F. Data Decentralisation of LLM-Based Chatbot Systems in Chronic Disease Self-Management. In Proceedings of the 2023 ACM Conference on Information Technology for Social Good (GoodIT ’23); ACM: New York, NY, USA, 2023; pp. 205–212. [Google Scholar]
- Vizgirda, V.; Zhao, R.; Goel, N. SocialGenPod: Privacy-Friendly Generative AI Social Web Applications with Decentralised Personal Data Stores. In Companion Proceedings of the ACM Web Conference 2024; ACM: New York, NY, USA, 2024; pp. 1067–1070. [Google Scholar]
- Ramírez-Gordillo, T.; Maciá-Lillo, A.; Pujol, F.A.; García-D’Urso, N.; Azorín-López, J.; Mora, H. Decentralized identity management for Internet of Things (IoT) devices using IOTA blockchain technology. Future Internet 2025, 17, 49. [Google Scholar] [CrossRef]
- Fugkeaw, S. Achieving Decentralized and Dynamic SSO-Identity Access Management System for Multi-Application Outsourced in Cloud. IEEE Access 2023, 11, 25480–25491. [Google Scholar] [CrossRef]
- Luecking, M.; Fries, C.; Lamberti, R.; Stork, W. Decentralized Identity and Trust Management Framework for Internet of Things. In Proceedings of the 2020 IEEE International Conference on Blockchain and Cryptocurrency (ICBC); IEEE: Piscataway, NJ, USA, 2020; pp. 1–9. [Google Scholar]
- Meisami, S.; Dabadie, H.; Li, S.; Tang, Y.; Duan, Y. SigScope: Detecting and Understanding Off-Chain Message Signing-Related Vulnerabilities in Decentralized Applications. In Proceedings of the ACM Web Conference 2025 (WWW ’25); ACM: New York, NY, USA, 2025; pp. 4284–4299. [Google Scholar]
- Zhu, X.; He, D.; Bao, Z.; Luo, M.; Peng, C. An Efficient Decentralized Identity Management System Based on Range Proof for Social Networks. IEEE Open J. Comput. Soc. 2023, 4, 84–96. [Google Scholar] [CrossRef]
- Murcia, J.M.B.; Cánovas, E.; García-Rodríguez, J.; Zarca, A.M.; Skarmeta, A. Decentralised identity management solution for zero-trust multi-domain computing continuum frameworks. Future Gener. Comput. Syst. 2025, 162, 107479. [Google Scholar] [CrossRef]
- Kim, T.M.; Ko, T.; Hwang, B.W.; Paek, H.G.; Lee, W.Y. Self-Sovereign Management Scheme of Personal Health Record with Personal Data Store and Decentralized Identifier. Comput. Struct. Biotechnol. J. 2025, 28, 16–28. [Google Scholar] [CrossRef]
- Liu, Z.; Pang, R. Blockchain Applications in Multiple Domains: Current Status, Challenges and Prospects. In Proceedings of the 2025 International Conference on Digital Economy and Information Systems (DEIS ’25); ACM: New York, NY, USA, 2025; pp. 225–230. [Google Scholar]
- Kleppmann, M.; Frazee, P.; Gold, J.; Graber, J.; Holmgren, D.; Ivy, D.; Johnson, J.; Newbold, B.; Volpert, J. Bluesky and the AT Protocol: Usable Decentralized Social Media. In Proceedings of the ACM CoNEXT 2024 Workshop on the Decentralization of the Internet (DIN ’24); ACM: New York, NY, USA, 2024; pp. 1–7. [Google Scholar]
- Ma, W.; Zhu, C.; Liu, Y.; Xie, X.; Li, Y. A Comprehensive Study of Governance Issues in Decentralized Finance Applications. ACM Trans. Softw. Eng. Methodol. 2025, 34, 208. [Google Scholar] [CrossRef]
- Frost, E.; Afrin, A.; Nieße, A.; Ardakanian, O. Robustness in Multi-Agent Energy Systems: The Trade-Off Between Decentralization and Security. In Proceedings of the 16th ACM International Conference on Future and Sustainable Energy Systems; ACM: New York, NY, USA, 2025; pp. 994–995. [Google Scholar]
- Bhattacharyya, D.; Ranjan, R.; Alisherov, F.; Choi, M. Biometric Authentication: A Review. Int. J. u- e-Serv. Sci. Technol. 2009, 2, 13–28. [Google Scholar]
- Alrawili, R.; AlQahtani, A.A.S.; Khan, M.K. Comprehensive Survey: Biometric User Authentication Application, Evaluation, and Discussion. Comput. Electr. Eng. 2024, 119, 109485. [Google Scholar] [CrossRef]
- Agarwal, A.; Ramachandra, R.; Venkatesh, S.; Prasanna, S.M. Biometrics in Extended Reality: A Review. Discov. Artif. Intell. 2024, 4, 81. [Google Scholar] [CrossRef]
- Ayeswarya, S.; Singh, K.J. A Comprehensive Review on Secure Biometric-Based Continuous Authentication and User Profiling. IEEE Access 2024, 12, 82996–83021. [Google Scholar] [CrossRef]
- Gunuganti, A. Behavioral Biometrics for Continuous Authentication. J. Biosens. Bioelectron. Res. 2023, 1, 1–5. [Google Scholar] [CrossRef]
- Hassan, W.; Sabahat, N. Towards Secure Identification: A Comparative Analysis of Biometric Authentication Techniques. VFAST Trans. Softw. Eng. 2024, 12, 105–120. [Google Scholar] [CrossRef]
- Ryu, R.; Yeom, S.; Herbert, D.; Dermoudy, J. The design and evaluation of adaptive biometric authentication systems: Current status, challenges and future direction. ICT Express 2023, 9, 1183–1197. [Google Scholar] [CrossRef]
- Syed, W.K.; Mohammed, A.; Reddy, J.K.; Dhanasekaran, S. Biometric authentication systems in banking: A technical evaluation of security measures. In 2024 IEEE 3rd World Conference on Applied Intelligence and Computing (AIC); IEEE: Piscataway, NJ, USA, 2024; pp. 1331–1336. [Google Scholar]
- Lee, Y.K.; Jeong, J. Securing Biometric Authentication System Using Blockchain. ICT Express 2021, 7, 322–326. [Google Scholar] [CrossRef]
- Ryu, R.; Yeom, S.; Kim, S.-H.; Herbert, D. Continuous Multimodal Biometric Authentication Schemes: A Systematic Review. IEEE Access 2021, 9, 34541–34557. [Google Scholar] [CrossRef]
- Iskandar, A.; Alfonse, M.; Roushdy, M.; El-Horbaty, E.-S.M. Biometric Systems for Identification and Verification Scenarios Using Spatial Footsteps Components. Neural Comput. Appl. 2024, 36, 3817–3836. [Google Scholar] [CrossRef]
- Lucia, C.; Zhiwei, G.; Nappi, M. Biometrics for Industry 4.0: A Survey of Recent Applications. J. Ambient Intell. Humaniz. Comput. 2023, 14, 11239–11261. [Google Scholar] [CrossRef]
- Vatchala, S.; Yogesh, C.; Govindarajan, Y.; Raja, M.K.; Ganesan, V.P.A.; Arul, A.V.; Ramesh, D. Multi-Modal Biometric Authentication: Leveraging Shared Layer Architectures for Enhanced Security. IEEE Access 2025, 13, 28029–28041. [Google Scholar] [CrossRef]
- Pahuja, S.; Goel, N. Multimodal Biometric Authentication: A Review. AI Commun. 2024, 37, 525–547. [Google Scholar] [CrossRef]
- Shethiya, A.S. AI-enhanced biometric authentication: Improving network security with deep learning. Acad. Nexus J. 2024, 3, 1–7. [Google Scholar]
- Abdul-Al, M.; Kyeremeh, G.K.; Qahwaji, R.; Ali, N.T.; Abd-Alhameed, R.A. The Evolution of Biometric Authentication: A Deep Dive into Multi-Modal Facial Recognition: A Review Case Study. IEEE Access 2024, 12, 179010–179038. [Google Scholar] [CrossRef]
- Patra, G.K.; Rajaram, S.K.; Boddapati, V.N.; Kuraku, C.; Gollangi, H.K. Advancing Digital Payment Systems: Combining AI, Big Data, and Biometric Authentication for Enhanced Security. Int. J. Eng. Comput. Sci. 2022, 11, 10-18535. [Google Scholar] [CrossRef]
- Salem, S.H.G.; Hassan, A.Y.; Moustafa, M.S.; Hassan, M.N. Blockchain-Based Biometric Identity Management. Clust. Comput. 2024, 27, 3741–3752. [Google Scholar] [CrossRef]
- Abo Alzahab, N.; Rafaiani, G.; Battaglioni, M.; Cavalli, A.; Chiaraluce, F.; Baldi, M. BiometricIdentity dApp: Decentralized Biometric Authentication Based on Fuzzy Commitment and Blockchain. SoftwareX 2024, 28, 101932. [Google Scholar] [CrossRef]
- Alzahab, N.A.; Rafaiani, G.; Battaglioni, M.; Chiaraluce, F.; Baldi, M. Decentralized Biometric Authentication Based on Fuzzy Commitments and Blockchain. In Proceedings of the 2024 6th International Conference on Blockchain Computing and Applications (BCCA); IEEE: Piscataway, NJ, USA, 2024; pp. 64–72. [Google Scholar]
- Sarier, N.D. Privacy Preserving Biometric Authentication on the Blockchain for Smart Healthcare. Pervasive Mob. Comput. 2022, 86, 101683. [Google Scholar] [CrossRef]
- Ou, H.H.; Pan, C.H.; Tseng, Y.M.; Lin, I.C. Decentralized Identity Authentication Mechanism: Integrating FIDO and Blockchain for Enhanced Security. Appl. Sci. 2024, 14, 3551. [Google Scholar] [CrossRef]
- Zhou, I.; Tofigh, F.; Piccardi, M.; Abolhasan, M.; Franklin, D.; Lipman, J. Secure Multi-Party Computation for Machine Learning: A Survey. IEEE Access 2024, 12, 53881–53899. [Google Scholar] [CrossRef]
- Xie, T.; Zhang, Y.; Song, D. Orion: Zero Knowledge Proof with Linear Prover Time. In Proceedings of the Annual International Cryptology Conference; Springer Nature: Cham, Switzerland, 2022. [Google Scholar]
- Faruk, M.J.H.; Islam, M.; Alam, F.; Shahriar, H.; Rahman, A. Bie Vote: A Biometric Identification Enabled Blockchain-Based Secure and Transparent Voting Framework. In Proceedings of the 2022 Fourth International Conference on Blockchain Computing and Applications (BCCA); IEEE: Piscataway, NJ, USA, 2022; pp. 253–258. [Google Scholar]
- Lai, J.; Wang, T.; Zhang, S.; Yang, Q.; Liew, S.C. BioZero: An Efficient and Privacy-Preserving Decentralized Biometric Authentication Protocol on Open Blockchain. arXiv 2024, arXiv:2409.17509. [Google Scholar]
- Sharma, S.; Saini, A.; Chaudhury, S. Multimodal biometric user authentication using improved decentralized fuzzy vault scheme based on blockchain network. J. Inf. Secur. Appl. 2024, 82, 103740. [Google Scholar] [CrossRef]
- Abraham, A.; Schinnerl, C.; More, S. SSI strong authentication using a mobile-phone based identity wallet reaching a high level of assurance. In Proceedings of the 18th International Conference on Security and Cryptography (SECRYPT 2021); SciTePress: Setúbal, Portugal, 2021; pp. 137–148. [Google Scholar]
- Iqbal, S.; Irfan, M.; Ahsan, K.; Hussain, M.A.; Awais, M.; Shiraz, M.; Hamdi, M.; Alghamdi, A. A Novel Mobile Wallet Model for Elderly Using Fingerprint as Authentication Factor. IEEE Access 2020, 8, 177405–177423. [Google Scholar] [CrossRef]
- Blanton, M.; Murphy, D. Privacy-Preserving Biometric Authentication for Fingerprints and Beyond. In Proceedings of the Fourteenth ACM Conference on Data and Application Security and Privacy; ACM: New York, NY, USA, 2024; pp. 367–378. [Google Scholar]
- Bernal-Romero, J.C.; Ramirez-Cortes, J.M.; Rangel-Magdaleno, J.D.J.; Gomez-Gil, P.; Peregrina-Barreto, H.; Cruz-Vega, I. A Review on Protection and Cancelable Techniques in Biometric Systems. IEEE Access 2023, 11, 8531–8568. [Google Scholar] [CrossRef]
- El-Shafai, W.; Mohamed, F.A.H.E.; Elkamchouchi, H.M.; Abd-Elnaby, M.; Elshafee, A. Efficient and Secure Cancelable Biometric Authentication Framework Based on Genetic Encryption Algorithm. IEEE Access 2021, 9, 77675–77692. [Google Scholar] [CrossRef]
- Yang, W.; Wang, S.; Shahzad, M.; Zhou, W. A Cancelable Biometric Authentication System Based on Feature-Adaptive Random Projection. J. Inf. Secur. Appl. 2021, 58, 102704. [Google Scholar] [CrossRef]
- El-Hameed, H.A.A.; Ramadan, N.; El-Shafai, W.; Khalaf, A.A.; Ahmed, H.E.H.; Elkhamy, S.E.; El-Samie, F.E.A. Cancelable Biometric Security System Based on Advanced Chaotic Maps. Vis. Comput. 2022, 38, 2171–2187. [Google Scholar] [CrossRef]
- Yang, W.; Wang, S.; Hu, J.; Tao, X.; Li, Y. Feature Extraction and Learning Approaches for Cancellable Biometrics: A Survey. CAAI Trans. Intell. Technol. 2024, 9, 4–25. [Google Scholar] [CrossRef]
- Tantubay, N.; Bharti, J. A Survey of Biometric Key-Binding Biocrypto-System Using Different Techniques. Int. J. Emerg. Technol. 2020, 11, 421–432. [Google Scholar]
- Wang, Y.; Li, B.; Zhang, Y.; Wu, J.; Ma, Q. A Secure Biometric Key Generation Mechanism via Deep Learning and Its Application. Appl. Sci. 2021, 11, 8497. [Google Scholar] [CrossRef]
- Kuznetsov, O.; Zakharov, D.; Frontoni, E. Deep Learning-Based Biometric Cryptographic Key Generation with Post-Quantum Security. Multimed. Tools Appl. 2024, 83, 56909–56938. [Google Scholar] [CrossRef]
- Abd-Aljabbar, A.A.; Hammood, D.A.; Abed, L.H. Secure Cloud Storage Using Multi-Modal Biometric Cryptosystem: A Deep Learning-Based Key Binding Approach. J. Al-Qadisiyah Comput. Sci. Math. 2025, 17, 214–229. [Google Scholar] [CrossRef]
- Geißner, H.; Rathgeb, C. Closing the Performance Gap in Biometric Cryptosystems: A Deeper Analysis on Unlinkable Fuzzy Vaults. arXiv 2025, arXiv:2506.22347. [Google Scholar] [CrossRef]
- Ponce-Hernandez, W.; Blanco-Gonzalo, R.; Liu-Jimenez, J.; Sanchez-Reillo, R. Fuzzy Vault Scheme Based on Fixed-Length Templates Applied to Dynamic Signature Verification. IEEE Access 2020, 8, 11152–11164. [Google Scholar] [CrossRef]
- Elrefaei, L.A.; Al-Mohammadi, A.M. Machine Vision Gait-Based Biometric Cryptosystem Using a Fuzzy Commitment Scheme. J. King Saud Univ.-Comput. Inf. Sci. 2022, 34, 204–217. [Google Scholar] [CrossRef]
- Fohr, V.; Rathgeb, C. Deep Multi-Biometric Fuzzy Commitment Scheme: Fusion Methods and Performance. EURASIP J. Inf. Secur. 2025, 2025, 20. [Google Scholar] [CrossRef]
- Tran, Q.N.; Turnbull, B.P.; Wang, M.; Hu, J. A Privacy-Preserving Biometric Authentication System with Binary Classification in a Zero Knowledge Proof Protocol. IEEE Open J. Comput. Soc. 2021, 3, 1–10. [Google Scholar] [CrossRef]
- Guo, C.; You, L.; Hu, G. A Novel Biometric Identification Scheme Based on Zero-Knowledge Succinct Noninteractive Argument of Knowledge. Secur. Commun. Netw. 2022, 2022, 2791058. [Google Scholar] [CrossRef]
- Guo, C.; You, L.; Li, X.; Hu, G.; Wang, S.; Cao, C. A Novel Biometric Authentication Scheme with Privacy Protection Based on SVM and ZKP. Comput. Secur. 2024, 144, 103995. [Google Scholar] [CrossRef]
- Yang, W.; Wang, S.; Cui, H.; Tang, Z.; Li, Y. A Review of Homomorphic Encryption for Privacy-Preserving Biometrics. Sensors 2023, 23, 3566. [Google Scholar] [CrossRef]
- Palma, D.; Montessoro, P.L. For Your Eyes Only: A Privacy-Preserving Authentication Framework Based on Homomorphic Encryption and Retina Biometrics. IEEE Access 2024, 12, 183688–183706. [Google Scholar] [CrossRef]
- Wu, D.; Liang, B.; Lu, Z.; Ding, J. Efficient Secure Multi-Party Computation for Multi-Dimensional Arithmetics and Its Application in Privacy-Preserving Biometric Identification. In Proceedings of the International Conference on Cryptology and Network Security (CANS); Springer Nature: Singapore, 2024; pp. 3–25. [Google Scholar]
- Guo, J.; Mu, H.; Liu, X.; Ren, H.; Han, C. Federated Learning for Biometric Recognition: A Survey. Artif. Intell. Rev. 2024, 57, 208. [Google Scholar] [CrossRef]
- Srinivasarao, G.; Bhargavi, T. Federated learning to train facial and eye blink recognition models over a decentralized network. Int. J. Mod. Trends Sci. Technol. 2025, 11, 326–332. [Google Scholar]
- Campanile, L.; De Biase, M.S.; Marulli, F. Design and Evaluation of a Privacy-Preserving Multi-Level Federated Learning Architecture for Airport Biometric Check-in. Future Gener. Comput. Syst. 2025, 176, 108217. [Google Scholar] [CrossRef]
- Lian, F.Z.; Huang, J.D.; Liu, J.X.; Chen, G.; Zhao, J.H.; Kang, W.X. FedFV: A Personalized Federated Learning Framework for Finger Vein Authentication. Mach. Intell. Res. 2023, 20, 683–696. [Google Scholar] [CrossRef]
- El Ouadrhiri, A.; Abdelhadi, A. Differential Privacy for Deep and Federated Learning: A Survey. IEEE Access 2022, 10, 22359–22380. [Google Scholar] [CrossRef]
- Vinothkanna, R.; Wahi, A. A Multimodal Biometric Approach for the Recognition of Fingerprint, Palm Print and Hand Vein Using Fuzzy Vault. Int. J. Biomed. Eng. Technol. 2020, 33, 54–76. [Google Scholar] [CrossRef]
- Rúa, E.A.; Preuveneers, D.; Joosen, W. On the Security of Biometrics and Fuzzy Commitment Cryptosystems: A Study on Gait Authentication. IEEE Trans. Inf. Forensics Secur. 2021, 16, 5211–5224. [Google Scholar] [CrossRef]
- Shahreza, H.O.; Rathgeb, C.; Osorio-Roig, D.; Hahn, V.K.; Marcel, S.; Busch, C. Hybrid Protection of Biometric Templates by Combining Homomorphic Encryption and Cancelable Biometrics. In Proceedings of the 2022 IEEE International Joint Conference on Biometrics (IJCB); IEEE: Piscataway, NJ, USA, 2022; pp. 1–10. [Google Scholar]
- Yin, W. Zero-Knowledge Proof Intelligent Recommendation System to Protect Students’ Data Privacy in the Digital Age. Appl. Artif. Intell. 2023, 37, 2222495. [Google Scholar] [CrossRef]
- Wen, J.; Zhang, Z.; Lan, Y.; Cui, Z.; Cai, J.; Zhang, W. A Survey on Federated Learning: Challenges and Applications. Int. J. Mach. Learn. Cybern. 2023, 14, 513–535. [Google Scholar] [CrossRef]
- Liu, B.; Lv, N.; Guo, Y.; Li, Y. Recent Advances on Federated Learning: A Systematic Survey. Neurocomputing 2024, 597, 128019. [Google Scholar] [CrossRef]
- Wang, X.; Shi, Y.; Zheng, K.; Zhang, Y.; Hong, W.; Cao, S. User Authentication Method Based on Keystroke Dynamics and Mouse Dynamics with Scene-Irrelated Features in Hybrid Scenes. Sensors 2022, 22, 6627. [Google Scholar] [CrossRef]
- Alharbi, B.; Alshanbari, H.S. Face-Voice Based Multimodal Biometric Authentication System via FaceNet and GMM. PeerJ Comput. Sci. 2023, 9, e1468. [Google Scholar] [CrossRef]
- Singh, A.; Kant, C. Optimized Hybrid SVM-RF Multi-Biometric Framework for Enhanced Authentication Using Fingerprint, Iris, and Face Recognition. PeerJ Comput. Sci. 2025, 11, e2699. [Google Scholar]
- Sumalatha, U.; Prakasha, K.K.; Prabhu, S.; Nayak, V.C. A Comprehensive Review of Unimodal and Multimodal Fingerprint Biometric Authentication Systems: Fusion, Attacks, and Template Protection. IEEE Access 2024, 12, 64300–64334. [Google Scholar] [CrossRef]
- Madduluri, S.; Kishorekumar, T. Multimodal Biometric Authentication System for Military Weapon Access: Face and ECG Authentication. Int. J. Comput. Exp. Sci. Eng. 2024, 10, 952–961. [Google Scholar] [CrossRef]
- Chen, G.; Luo, D.; Lian, F.; Tian, F.; Yang, X.; Kang, W. A Multimodal Biometric Recognition Method Based on Federated Learning. IET Biom. 2024, 5873909. [Google Scholar] [CrossRef]
- Ghafourian, M.; Sumer, B.; Vera-Rodriguez, R.; Fierrez, J.; Tolosana, R.; Moralez, A.; Kindt, E. Combining Blockchain and Biometrics: A Survey on Technical Aspects and a First Legal Analysis. arXiv 2023, arXiv:2302.10883. [Google Scholar] [CrossRef]

| Research Area | References | Contributions | Advantages | Limitations |
|---|---|---|---|---|
| Core Architecture and Ecosystem | [2,10,11,15,20,21,22,23] | Systematic analysis of DID/SSI architectures, clarifying core components such as DIDs, verifiable credentials, and trust frameworks, while identifying adoption and interoperability challenges. | User-centric identity control, selective disclosure, portability, enhanced privacy and resilience, and cryptographic interoperability. | Lack of standardized governance, limited cross-platform interoperability, scalability constraints, and regulatory uncertainty. |
| Privacy and Credential Management | [19,24,25,26,27] | Development of privacy-preserving mechanisms for credential issuance, presentation, and revocation, improving resilience against single points of failure. | Fine-grained credential control, reduced over-disclosure, regulatory compliance, and enhanced user data sovereignty. | Cryptographic complexity, performance overhead, difficult revocation mechanisms, and usability challenges related to key management. |
| Infrastructure and Performance | [12,14,16,28,29,30,31] | Comparative evaluation of DLT-, DHT-, and hybrid DID infrastructures, including IoT-oriented designs, to assess scalability–latency trade-offs. | Clear characterization of storage, scalability, and flexibility trade-offs; lightweight protocols for IoT environments. | Latency in DHT-based systems, unresolved biometric data risks, limited large-scale IoT validation, increased complexity in hybrid models, and scarce real-world benchmarks. |
| Domain-Specific Applications | [32,33,34,35,36] | Investigation of DID adoption in application domains such as social networks, decentralized social media, finance, healthcare, education, and supply chains. | Improved privacy and anonymity, enhanced user agency and portability, and increased transparency, traceability, and compliance. | Dependence on external trust anchors, privacy exposure of public data, limited scalability and adoption, and regulatory and interoperability barriers. |
| Governance, Security, and Power Structures | [37,38] | Analysis of governance and security issues in decentralized ecosystems, identifying persistent centralization risks and proposing taxonomies and safeguards. | Improved understanding of governance vulnerabilities, ownership concentration, and the need for transparent standards and safeguards. | Inconsistent governance models, Sybil and voting attacks, investor dominance, lack of unified frameworks, and challenges enforcing safeguards across heterogeneous ecosystems. |
| Method | Advantages | Limitations | References |
|---|---|---|---|
| Cancelable Biometrics | Irreversible feature transformations; revocable and re-issuable; unlinkable across applications; resistant to replay/linkage attacks | Potential accuracy drop; some modalities difficult to transform; transformation functions may be vulnerable to inversion attacks | [69,70,71,72] |
| Fuzzy Vault | Hides key with chaff; supports unordered data; avoids storage of raw biometric data | Difficult revocation; sensitivity to noise and alignment errors; susceptibility to statistical and correlation attacks | [78,79,93] |
| Fuzzy Commitment | Error-correcting codes tolerate biometric variability; efficient for binary data; stores only helper data | Noise/misalignment issues; weak hashes risks; limited reusability | [58,80,81,94] |
| Homomorphic Encryption | Enables computation directly on encrypted biometric data; prevents data exposure during outsourced processing | Very high computational overhead; impractical for low-resource or real-time settings; complex key management | [85,86,95] |
| SMPC | No single trusted entity; protects privacy by distributing computation among multiple parties | High communication overhead; complex protocol setup; limited scalability in large deployments | [61,87] |
| ZKPs | Allow proving possession/validity without exposing biometric template: strong privacy; ideal for trustless systems | Complex proof design; limited support for biometric feature operations; high computation/storage overhead | [82,83,84,96] |
| Federated Learning | Data stay local; supports collaborative and decentralized model training; reduces large-scale data exposure | Vulnerable to inference/membership attacks; sensitive to non-IID data, requires secure aggregation infrastructure | [88,97,98] |
| Differential Privacy | Formal privacy guarantees; limits information leakage from data or model updates; composable with other methods | Accuracy loss due to injected noise; challenging privacy–utility trade-off | [92] |
| References | Techniques Used | Opportunities | Challenges |
|---|---|---|---|
| [65] | AI-driven biometrics (fingerprint, face, iris, behavioral) with AI models (CNNs, RNNs, anomaly detection) and trends like multimodal, continuous authentication, and blockchain-based identity |
|
|
| [104] |
|
|
|
| [105] |
|
|
|
| [58] |
|
|
|
| RQ(s) | Research Dimension | Key Research Gaps | Future Research Directions |
|---|---|---|---|
| RQ1, RQ3 | Privacy-Preserving Techniques | Privacy-enhancing mechanisms for biometric-enabled DID systems incur high computational and communication overhead, limiting scalability and real-time deployment in decentralized environments. | Development of efficient ZKPs, HE, SMPC schemes, and AI-based methods, alongside low-cost biometric solutions, suitable for real-time and large-scale environments. |
| RQ2, RQ4 | Biometric Revocability and Lifecycle Management | Limited support for revocation, re-binding, and adaptation to biometric evolution in long-lived decentralized identity systems undermines long-term reliability. | Design of cancelable, adaptive, and multimodal biometric templates that enable recovery after compromise. |
| RQ3, RQ4 | Standardization and Interoperability | Fragmentation across decentralized identity platforms, credential formats, biometric representations, and blockchain infrastructures hinders cross-domain and cross-chain identity verification. | Establishment of unified standards for DID protocols, credential formats, biometric modalities, and blockchain frameworks. |
| RQ1, RQ2, RQ3 | Security | Persistent vulnerabilities related to spoofing attacks, key compromise, and inadequate recovery or revocation mechanisms remain insufficiently addressed. | Integration of advanced liveness detection techniques, resilient key management schemes, and robust recovery/revocation strategies to mitigate vulnerabilities. |
| RQ1, RQ2, RQ4 | User-Centric Design and Inclusiveness | Usability, accessibility, and demographic bias remain insufficiently considered in biometric-enabled decentralized identity systems. | Development of inclusive and bias-aware authentication mechanisms, intuitive user interfaces, and effective error handling and recovery workflows. |
| RQ3, RQ4 | Multimodality | Integration of multimodal biometric systems into decentralized identity frameworks remains underexplored due to fusion complexity and system overhead. | Investigation of efficient fusion strategies and adaptive modality selection to improve robustness, reliability, and inclusiveness across diverse user populations. |
| RQ1, RQ2, RQ3, RQ4 | Governance and Empirical Validation | Transparent governance models and large-scale real-world validation of biometric-enabled decentralized identity systems are largely lacking. | Design of transparent decentralized governance frameworks, regulatory-aligned system architectures, and real-world pilot deployments in high-stakes application domains. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.
Share and Cite
Rjab, I.; Sliman, L. Survey on Biometric Authentication for Decentralized Identity Management: Trends, Challenges, and Future Directions. Future Internet 2026, 18, 126. https://doi.org/10.3390/fi18030126
Rjab I, Sliman L. Survey on Biometric Authentication for Decentralized Identity Management: Trends, Challenges, and Future Directions. Future Internet. 2026; 18(3):126. https://doi.org/10.3390/fi18030126
Chicago/Turabian StyleRjab, Imen, and Layth Sliman. 2026. "Survey on Biometric Authentication for Decentralized Identity Management: Trends, Challenges, and Future Directions" Future Internet 18, no. 3: 126. https://doi.org/10.3390/fi18030126
APA StyleRjab, I., & Sliman, L. (2026). Survey on Biometric Authentication for Decentralized Identity Management: Trends, Challenges, and Future Directions. Future Internet, 18(3), 126. https://doi.org/10.3390/fi18030126








