Blockchain for Security in Digital Twins
Abstract
1. Introduction
- Providing a comprehensive analysis of various security threats faced by DTs, focusing on data integrity, unauthorized access, and system weaknesses;
- Exploring blockchain-based solutions to mitigate these risks, including secure data transmission, smart contracts, and dual blockchain frameworks;
- Comparing blockchain technology with traditional security methods, emphasizing its decentralized and immutable nature, which significantly reduces vulnerabilities;
- Reviewing common metrics for assessing the performance of both blockchain and DT systems;
- Identifying open challenges in integrating blockchain with DTs, such as scalability, data privacy, and quantum resilience, and suggesting future research directions.
2. Background
2.1. Digital Twins
2.1.1. Digital Twin Architecture
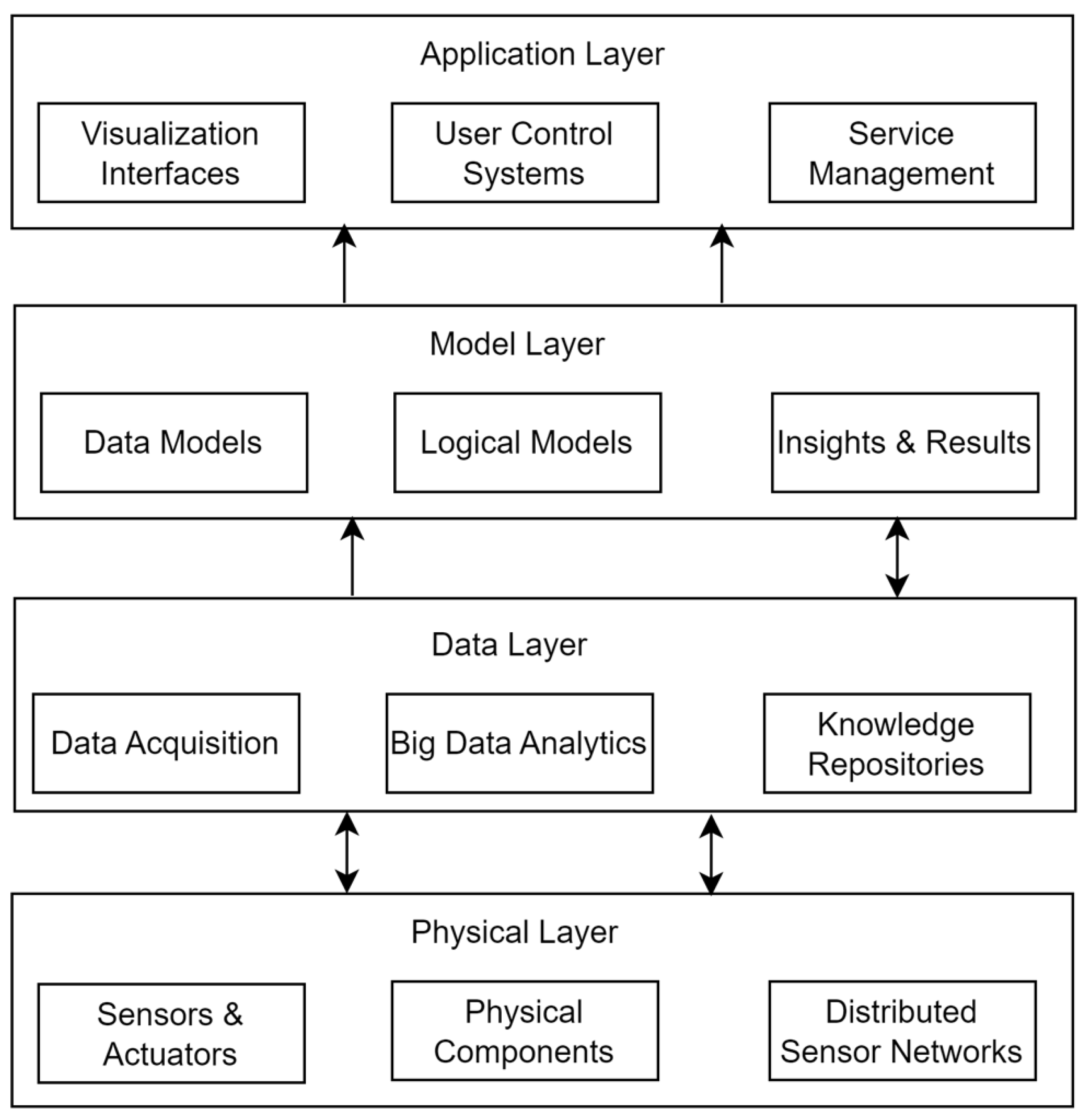
2.1.2. Digital Twin Functional Layers
2.1.3. Physical Layer
2.1.4. Data Layer
2.1.5. Model Layer
2.1.6. Application Layer
2.2. Blockchain Technology
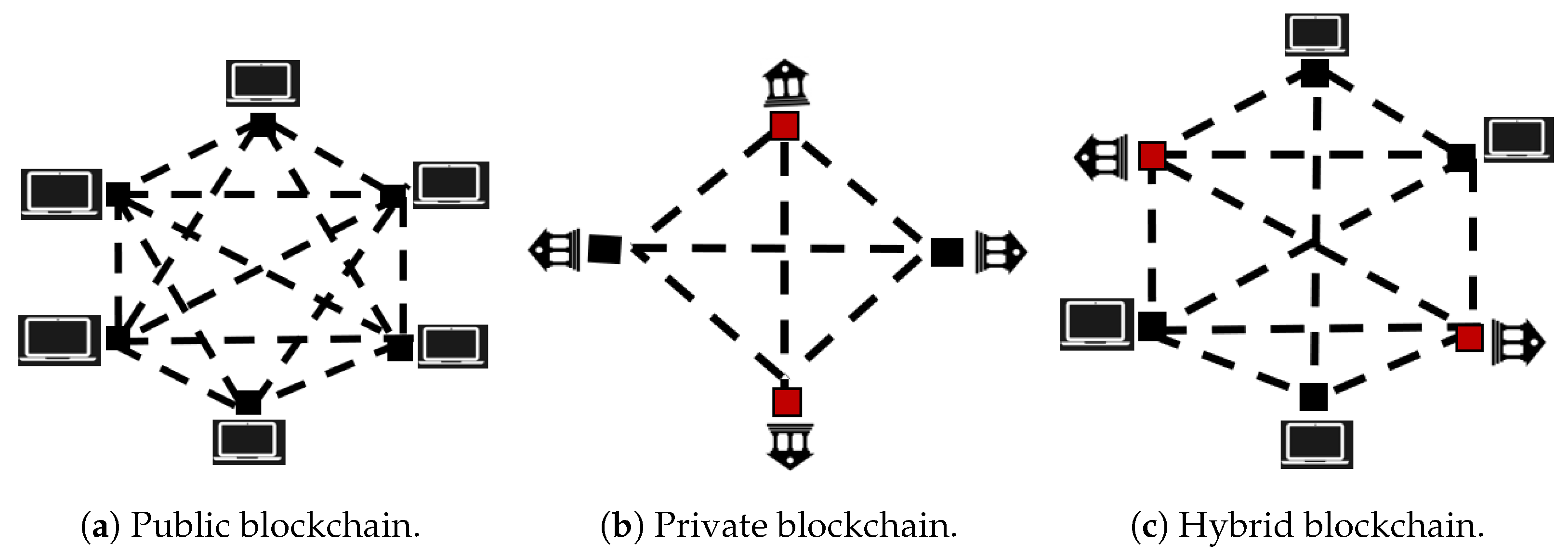
2.2.1. Types of Blockchain
2.2.2. Blockchain Consensus Mechanisms
- Proof of Work (PoW): This is a type of blockchain consensus mechanism that uses cryptographic methods and a significant amount of computing power to ensure integrity and network consensus. In PoW, finding a valid solution is challenging, but it is easy to verify that solution. In this mechanism, participants continuously try to find a valid hash by altering a variable called a nonce [64] in the block header until they generate a hash value that meets or falls below a specific target defined within the block header. All participants in the network engage in this process, and once a participant finds a valid hash, others must verify its correctness. The set of transactions used to compute the valid hash is considered and added as a new block to the blockchain. The participants are referred to as ‘miners’, and the process is referred to as mining. Since mining is resource-intensive and time-consuming, miners get rewards to encourage participation. Occasionally, two miners may generate a valid block simultaneously, potentially leading to a temporary split in the blockchain known as a fork.
- Proof of Stake (PoS): This is a kind of consensus that was introduced as a substitute. This mechanism chooses validators to generate new blocks by considering how much cryptocurrency they have locked up in the system or staked. A validator is randomly chosen to validate the data within a block; the likelihood of being chosen increases with the number of tokens staked. Once the block is successfully validated, the chosen validator receives transaction fees as a reward, and the cycle begins again. Since PoS relies on validators who stake their tokens, this helps ensure the network’s security and integrity. To discourage negligent behavior, slashing [65] is used to penalize and remove underperforming validators. With this method, hardware costs and energy usage are reduced, allowing validators to earn rewards through honest participation. One shortcoming of PoS is that it can potentially lead to centralization and make the network vulnerable to long-range attacks [66] if a node accumulates a large share of the total currency.
- Practical Byzantine Fault Tolerance (PBFT): This algorithm effectively achieves consensus in distributed systems. PBFT is specifically designed to address Byzantine failures where nodes in the network may crash, fail to respond, or deliberately provide incorrect information. It maintains security and functionality if not more than one-third of the total nodes are faulty [67]. It relies on a structured voting process among all participating nodes to reach consensus. The network adds a block to the ledger only if it secures consensus from more than two-thirds of its nodes [65]. This voting-based mechanism ensures fault tolerance and strengthens the system’s integrity, making PBFT suitable for DT environments where reliability and security are critical.
2.3. Advantages of Integrating Blockchain with Digital Twins
2.3.1. Digital Uniqueness
2.3.2. Distributed Infrastructure
2.3.3. Securing and Tracing Digital Twin Data
2.3.4. Accessibility and Safeguarding Life Cycle Data
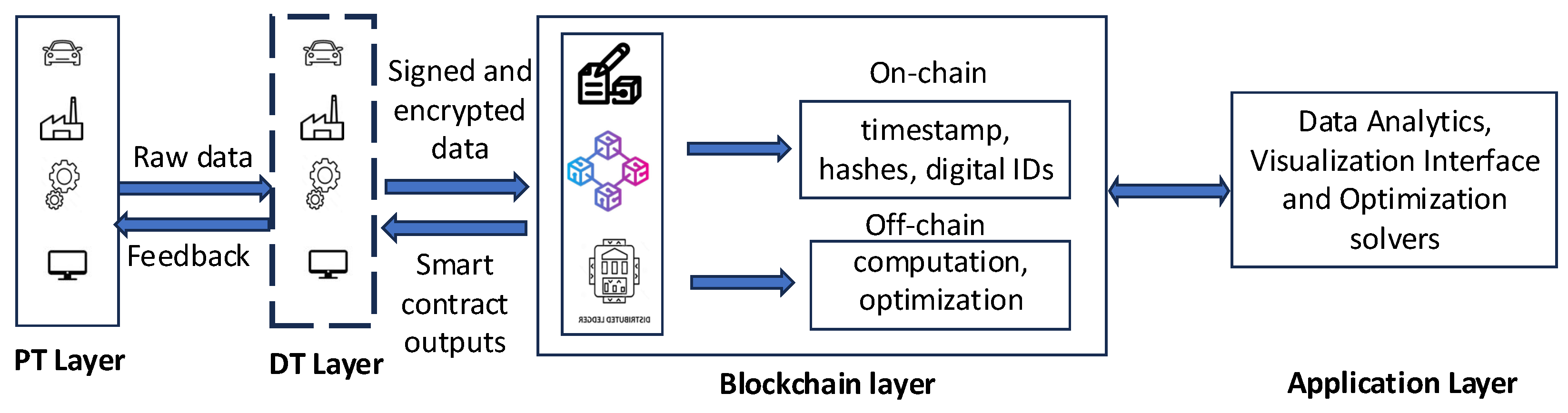
3. Blockchain-Based Digital Twins Architecture
- Latency and immutability: Blockchain transactions that result in data immutability and trust add delays, whereas in DT environments, these delays might disrupt the frequency of DT-PT updates, which in turn might impact time-sensitive decisions. For example, Ethereum finality takes between 10 and 60 seconds, whereas industrial DT operations take milliseconds.
- Data storage and cost: If the blockchain requires on-chain storage, the frequent DT updates that need to be stored will incur significant costs. For example, storing 10 MB of data on Ethereum on-chain costs hundreds of dollars in fuel.
- Complexity and trust: Introducing blockchains into a DT application ensures data integrity, but it adds several other components like smart contracts, consensus layers, and ledgers, which add a lot of operational and architectural complexities. This might require a significantly higher development overhead and also scalability issues.
4. Security Attacks and Privacy Concerns
4.1. Attacks on Digital Twins and CPSs
- Physical damage: If a DT is compromised, attackers could gain insight into the physical system’s configuration and potentially access important resources through the DT [80]. This information can be leveraged to breach individual privacy or launch cyber attacks. Cyber attacks on critical infrastructure data can significantly impact physical processes, disrupt control capabilities, and much more.
- Single point of failure: Attackers may attempt to destroy critical devices or servers, posing a single point of failure. This disruption can impact the regular operation of DT services, affecting core functionality such as optimization and monitoring, and ultimately destabilize the entire system [81].
4.2. Attack on Digital Twin Operation Modes
4.3. Attacks on the Digital Twin Layers
4.3.1. Physical Layer
4.3.2. Data Layer
4.3.3. Model Layer
4.3.4. Application Layer
5. Blockchain Solutions for Digital Twins
5.1. Data Authentication
5.2. Smart Contracts
5.3. Decentralized Identity (DID)
5.4. Data Provenance Tracking
5.5. Blockchain with Gamification
6. Blockchain Technology vs. Traditional Methods for Digital Twins
6.1. Decentralization
6.2. Immutability
6.3. Data Integrity and Provenance
7. Common Metrics Used for Blockchain and Digital Twins Solutions
7.1. Security Analysis
7.2. Cost Analysis
7.3. Blockchain
7.4. Latency and Throughput
7.5. Accuracy
8. A Theoretical Blockchain-Based Digital Twin Framework
- Signature verification: Ensures incoming data originates from authenticated and trusted devices, preventing malicious injections;
- Modeling and analysis: Builds virtual models that simulate traffic flow and city conditions, enabling predictive insights;
- Computation optimization: Applies AI/ML algorithms to optimize traffic management, energy use, or resource allocation;
- Visualization/API: Provides interfaces for stakeholders to interact with the twin, including dashboards and APIs for integration with external applications.
- Latency and throughput: The blockchain’s performance can be assessed using both metrics. The transaction latency calculates the time from when the DT publishes the data to when the blockchain confirms it. Throughput helps determine real-time tracking efficiency by knowing the number of transactions processed per second.
- Collision risk detection accuracy: To determine the accuracy of collision predictions, the true positive rate can be used to calculate the number of correct predictions that are collisions. In contrast, the number of false alarms can be obtained using the false positive rate (FPR). Time to Collision (TTC) error can also be obtained by subtracting the actual TTC from the predicted TTC.
- Cost metrics: The operational cost of the model can be computed by determining the gas fees per transaction in publishing DT updates to the blockchain per vehicle. The cost of false alerts from rerouting or unnecessary braking due to incorrect warnings can be measured.
Implementation Tools
9. Open Challenges and Future Directions
9.1. Scalability
9.2. Data Privacy and Security
9.3. Quantum Resilience
9.4. Real-Time Interaction
10. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Qian, C.; Liu, X.; Ripley, C.; Qian, M.; Liang, F.; Yu, W. Digital twin—Cyber replica of physical things: Architecture, applications and future research directions. Future Internet 2022, 14, 64. [Google Scholar] [CrossRef]
- Qian, C.; Guo, Y.; Hussaini, A.; Musa, A.; Sai, A.; Yu, W. A new layer structure of cyber-physical systems under the era of digital twin. ACM Trans. Internet Technol. 2024. [Google Scholar] [CrossRef]
- Lampropoulos, G.; Siakas, K. Enhancing and securing cyber-physical systems and Industry 4.0 through digital twins: A critical review. J. Software Evol. Process 2023, 35, e2494. [Google Scholar] [CrossRef]
- Lin, J.; Yu, W.; Zhang, N.; Yang, X.; Zhang, H.; Zhao, W. A Survey on Internet of Things: Architecture, Enabling Technologies, Security and Privacy, and Applications. IEEE Internet Things J. 2017, 4, 1125–1142. [Google Scholar] [CrossRef]
- Xu, H.; Liu, X.; Yu, W.; Griffith, D.; Golmie, N. Reinforcement Learning-Based Control and Networking Co-Design for Industrial Internet of Things. IEEE J. Sel. Areas Commun. 2020, 38, 885–898. [Google Scholar] [CrossRef]
- Liu, Y.; Peng, Y.; Wang, B.; Yao, S.; Liu, Z. Review on cyber-physical systems. IEEE/CAA J. Autom. Sin. 2017, 4, 27–40. [Google Scholar] [CrossRef]
- Gao, W.; Hatcher, W.G.; Yu, W. A Survey of Blockchain: Techniques, Applications, and Challenges. In Proceedings of the 2018 27th International Conference on Computer Communication and Networks (ICCCN), Hangzhou, China, 30 July–2 August 2018; pp. 1–11. [Google Scholar] [CrossRef]
- Lee, J.; Azamfar, M.; Singh, J.; Siahpour, S. Integration of digital twin and deep learning in cyber-physical systems: Towards smart manufacturing. IET Collab. Intell. Manuf. 2020, 2, 34–36. [Google Scholar] [CrossRef]
- Falayi, A.; Wang, Q.; Liao, W.; Yu, W. Survey of Distributed and Decentralized IoT Securities: Approaches Using Deep Learning and Blockchain Technology. Future Internet 2023, 15, 178. [Google Scholar] [CrossRef]
- Hatcher, W.G.; Yu, W. A Survey of Deep Learning: Platforms, Applications and Emerging Research Trends. IEEE Access 2018, 6, 24411–24432. [Google Scholar] [CrossRef]
- Attaran, M.; Celik, B.G. Digital Twin: Benefits, use cases, challenges, and opportunities. Decis. Anal. J. 2023, 6, 100165. [Google Scholar] [CrossRef]
- Name, A. Digital Twins Market by Technology, Twinning Type, Cyber-to-Physical Solutions, Use Cases and Applications in Industry Verticals 2024–2029. 2024. Available online: https://www.researchandmarkets.com/reports/5308850/digital-twins-market-by-technology-twinning? (accessed on 28 July 2024).
- Marr, B. What is Extended Reality Technology? A Simple Explanation for Anyone. Forbes, 12 August 2019. [Google Scholar]
- Lv, Z.; Xie, S. Artificial intelligence in the digital twins: State of the art, challenges, and future research topics: [version 2; peer review: 2 approved]. Digital Twin 2024, 1, 12. [Google Scholar] [CrossRef]
- Onaji, I.; Tiwari, D.; Soulatiantork, P.; Song, B.; Tiwari, A. Digital twin in manufacturing: Conceptual framework and case studies. Int. J. Comput. Integr. Manuf. 2022, 35, 831–858. [Google Scholar] [CrossRef]
- Mazzetto, S. A Review of Urban Digital Twins Integration, Challenges, and Future Directions in Smart City Development. Sustainability 2024, 16, 8337. [Google Scholar] [CrossRef]
- Alazab, M.; Khan, L.U.; Koppu, S.; Ramu, S.P.; Boobalan, P.; Baker, T.; Maddikunta, P.K.R.; Gadekallu, T.R.; Aljuhani, A. Digital twins for healthcare 4.0—Recent advances, architecture, and open challenges. IEEE Consum. Electron. Mag. 2022, 12, 29–37. [Google Scholar] [CrossRef]
- Sai, A.M.V.V.; Wang, C.; Cai, Z.; Li, Y. Navigating the digital twin network landscape: A survey on architecture, applications, privacy and security. High-Confid. Comput. 2024, 4, 100269. [Google Scholar] [CrossRef]
- Hemdan, E.E.D.; El-Shafai, W.; Sayed, A. Integrating digital twins with IoT-based blockchain: Concept, architecture, challenges, and future scope. Wirel. Pers. Commun. 2023, 131, 2193–2216. [Google Scholar] [CrossRef]
- Wang, Q.; Liao, W.; Guo, Y.; McGuire, M.; Yu, W. Blockchain-Empowered Federated Learning Through Model and Feature Calibration. IEEE Internet Things J. 2024, 11, 5770–5780. [Google Scholar] [CrossRef]
- Ferone, A.; Verrilli, S. Exploiting Blockchain Technology for Enhancing Digital Twins’ Security and Transparency. Future Internet 2025, 17, 31. [Google Scholar] [CrossRef]
- Dong, W.; Yang, B.; Wang, K.; Yan, J.; He, S. A dual blockchain framework to enhance data trustworthiness in digital twin network. In Proceedings of the 2021 IEEE 1st International Conference on Digital Twins and Parallel Intelligence (DTPI), Beijing, China, 15 July–15 August 2021; IEEE: Piscataway, NJ, USA, 2021; pp. 144–147. [Google Scholar]
- Yaqoob, I.; Salah, K.; Uddin, M.; Jayaraman, R.; Omar, M.; Imran, M. Blockchain for digital twins: Recent advances and future research challenges. IEEE Netw. 2020, 34, 290–298. [Google Scholar] [CrossRef]
- Suhail, S.; Hussain, R.; Jurdak, R.; Hong, C.S. Trustworthy digital twins in the industrial internet of things with blockchain. IEEE Internet Comput. 2021, 26, 58–67. [Google Scholar] [CrossRef]
- Gehrmann, C.; Gunnarsson, M. A digital twin based industrial automation and control system security architecture. IEEE Trans. Ind. Inform. 2019, 16, 669–680. [Google Scholar] [CrossRef]
- Salim, M.M.; Comivi, A.K.; Nurbek, T.; Park, H.; Park, J.H. A blockchain-enabled secure digital twin framework for early botnet detection in IIoT environment. Sensors 2022, 22, 6133. [Google Scholar] [CrossRef]
- Karaarslan, E.; Babiker, M. Digital twin security threats and countermeasures: An introduction. In Proceedings of the 2021 International Conference on Information Security and Cryptology (ISCTURKEY), Ankara, Turkey, 2–3 December 2021; IEEE: Piscataway, NJ, USA, 2021; pp. 7–11. [Google Scholar]
- Chen, Q.; Zhu, Z.; Si, S.; Cai, Z. Intelligent maintenance of complex equipment based on blockchain and digital twin technologies. In Proceedings of the 2020 IEEE International Conference on Industrial Engineering and Engineering Management (IEEM), Singapore, 14–17 December 2020; IEEE: Piscataway, NJ, USA, 2020; pp. 908–912. [Google Scholar]
- Onwubiko, A.; Singh, R.; Awan, S.; Pervez, Z.; Ramzan, N. Enabling trust and security in digital twin management: A blockchain-based approach with ethereum and ipfs. Sensors 2023, 23, 6641. [Google Scholar] [CrossRef]
- Zheng, Q.; Wang, J.; Shen, Y.; Ding, P.; Cheriet, M. Blockchain based trustworthy digital twin in the Internet of Things. In Proceedings of the 2022 International Conference on Information Processing and Network Provisioning (ICIPNP), Beijing, China, 15–16 September 2022; IEEE: Piscataway, NJ, USA, 2022; pp. 152–155. [Google Scholar]
- Grieves, M. Digital twin: Manufacturing excellence through virtual factory replication. White Pap. 2014, 1, 1–7. [Google Scholar]
- Allen, B.D. Digital twins and living models at NASA. In Proceedings of the Digital Twin Summit, Virtual, 3–4 November 2021. [Google Scholar]
- Grieves, M.W. Virtually intelligent product systems: Digital and physical twins. In Complex Systems Engineering: Theory and Practice; American Institute of Aeronautics and Astronautics: Reston, VA, USA, 2019. [Google Scholar]
- Delgado, J.M.D.; Oyedele, L. Digital Twins for the built environment: Learning from conceptual and process models in manufacturing. Adv. Eng. Inform. 2021, 49, 101332. [Google Scholar] [CrossRef]
- Wlazlo, P.; Sahu, A.; Mao, Z.; Huang, H.; Goulart, A.; Davis, K.; Zonouz, S. Man-in-the-middle attacks and defence in a power system cyber-physical testbed. IET Cyber-Phys. Syst. Theory Appl. 2021, 6, 164–177. [Google Scholar] [CrossRef]
- Qi, Q.; Tao, F.; Hu, T.; Anwer, N.; Liu, A.; Wei, Y.; Wang, L.; Nee, A.Y. Enabling technologies and tools for digital twin. J. Manuf. Syst. 2021, 58, 3–21. [Google Scholar] [CrossRef]
- Neupane, S.; Fernandez, I.A.; Patterson, W.; Mittal, S.; Rahimi, S. A temporal anomaly detection system for vehicles utilizing functional working groups and sensor channels. In Proceedings of the 2022 IEEE 8th International Conference on Collaboration and Internet Computing (CIC), Atlanta, GA, USA, 14–16 December 2022; IEEE: Piscataway, NJ, USA, 2022; pp. 99–108. [Google Scholar]
- Feng, K.; Ji, J.; Zhang, Y.; Ni, Q.; Liu, Z.; Beer, M. Digital twin-driven intelligent assessment of gear surface degradation. Mech. Syst. Signal Process. 2023, 186, 109896. [Google Scholar] [CrossRef]
- Moiceanu, G.; Paraschiv, G. Digital twin and smart manufacturing in industries: A bibliometric analysis with a focus on industry 4.0. Sensors 2022, 22, 1388. [Google Scholar] [CrossRef]
- Al-Ali, A.R.; Gupta, R.; Zaman Batool, T.; Landolsi, T.; Aloul, F.; Al Nabulsi, A. Digital twin conceptual model within the context of internet of things. Future Internet 2020, 12, 163. [Google Scholar] [CrossRef]
- Redelinghuys, A.J.; Kruger, K.; Basson, A. A six-layer architecture for digital twins with aggregation. In Service Oriented, Holonic and Multi-Agent Manufacturing Systems for Industry of the Future; Proceedings of SOHOMA 2019; Springer: Berlin/Heidelberg, Germany, 2020; pp. 171–182. [Google Scholar]
- Jeremiah, S.R.; El Azzaoui, A.; Xiong, N.N.; Park, J.H. A comprehensive survey of digital twins: Applications, technologies and security challenges. J. Syst. Archit. 2024, 151, 103120. [Google Scholar] [CrossRef]
- Luan, T.H.; Liu, R.; Gao, L.; Li, R.; Zhou, H. The paradigm of digital twin communications. arXiv 2021, arXiv:2105.07182. [Google Scholar] [CrossRef]
- Tao, F.; Qi, Q.; Wang, L.; Nee, A. Digital twins and cyber–physical systems toward smart manufacturing and industry 4.0: Correlation and comparison. Engineering 2019, 5, 653–661. [Google Scholar] [CrossRef]
- Yang, L.; Xu, Z. Research on industrial digital twin technology system and key technologies. Inf. Commun. Technol. Policy 2021, 47, 8. [Google Scholar]
- da Silva Mendonça, R.; de Oliveira Lins, S.; de Bessa, I.V.; de Carvalho Ayres Jr, F.A.; de Medeiros, R.L.P.; de Lucena Jr, V.F. Digital twin applications: A survey of recent advances and challenges. Processes 2022, 10, 744. [Google Scholar] [CrossRef]
- Singh, S.; Shehab, E.; Higgins, N.; Fowler, K.; Reynolds, D.; Erkoyuncu, J.A.; Gadd, P. Data management for developing digital twin ontology model. Proc. Inst. Mech. Eng. Part B J. Eng. Manuf. 2021, 235, 2323–2337. [Google Scholar] [CrossRef]
- Liu, Z.; Bai, W.; Du, X.; Zhang, A.; Xing, Z.; Jiang, A. Digital twin-based safety evaluation of prestressed steel structure. Adv. Civ. Eng. 2020, 2020, 8888876. [Google Scholar] [CrossRef]
- Russo, E.; Costa, G.; Longo, G.; Armando, A.; Merlo, A. Lidite: A full-fledged and featherweight digital twin framework. IEEE Trans. Dependable Secur. Comput. 2023, 20, 4899–4912. [Google Scholar] [CrossRef]
- Guo, J.; Bilal, M.; Qiu, Y.; Qian, C.; Xu, X.; Choo, K.K.R. Survey on digital twins for Internet of Vehicles: Fundamentals, challenges, and opportunities. Digit. Commun. Netw. 2024, 10, 237–247. [Google Scholar] [CrossRef]
- Haq, H.B.U.; Irfan, M.; Saqlain, M. The concept of blockchain and its application: A review. Theor. Appl. Comput. Intell. 2023, 1, 49–57. [Google Scholar] [CrossRef]
- Gong, F.; Kong, L.; Lu, Y.; Qian, J.; Min, X. An overview of blockchain scalability for storage. In Proceedings of the 2023 26th International Conference on Computer Supported Cooperative Work in Design (CSCWD), Rio de Janeiro, Brazil, 24–26 May 2023; IEEE: Piscataway, NJ, USA, 2023; pp. 516–521. [Google Scholar]
- Rezaeighaleh, H.; Zou, C.C. Efficient off-chain transaction to avoid inaccessible coins in cryptocurrencies. In Proceedings of the 2020 IEEE 19th International Conference on Trust, Security and Privacy in Computing and Communications (TrustCom), Guangzhou, China, 29 December–1 January 2020; IEEE: Piscataway, NJ, USA, 2020; pp. 1903–1909. [Google Scholar]
- Daniel, E.; Tschorsch, F. IPFS and friends: A qualitative comparison of next generation peer-to-peer data networks. IEEE Commun. Surv. Tutor. 2022, 24, 31–52. [Google Scholar] [CrossRef]
- Hewa, T.; Ylianttila, M.; Liyanage, M. Survey on blockchain based smart contracts: Applications, opportunities and challenges. J. Netw. Comput. Appl. 2021, 177, 102857. [Google Scholar] [CrossRef]
- Varlamis, I.; Himeur, Y.; Chronis, C.; Sardianos, C. Blockchain technology for secure digital twin data management. In Blockchain and Digital Twin for Smart Healthcare; Elsevier: Amsterdam, The Netherlands, 2025; pp. 439–452. [Google Scholar]
- Bashir, I. Mastering Blockchain: A Deep Dive into Distributed Ledgers, Consensus Protocols, Smart Contracts, DApps, Cryptocurrencies, Ethereum, and More; Packt Publishing Ltd.: Birmingham, UK, 2020. [Google Scholar]
- Zafar, S.; Bhatti, K.; Shabbir, M.; Hashmat, F.; Akbar, A.H. Integration of blockchain and Internet of Things: Challenges and solutions. Ann. Telecommun. 2022, 77, 13–32. [Google Scholar] [CrossRef]
- Xie, J.; Tang, H.; Huang, T.; Yu, F.R.; Xie, R.; Liu, J.; Liu, Y. A survey of blockchain technology applied to smart cities: Research issues and challenges. IEEE Commun. Surv. Tutor. 2019, 21, 2794–2830. [Google Scholar] [CrossRef]
- Groopman, J. Permissioned vs. Permissionless Blockchains: Key Differences: TechTarget, CIO. 2023. Available online: https://www.techtarget.com/searchcio/tip/Permissioned-vs-permissionless-blockchains-Key-differences (accessed on 6 May 2024).
- Tripathi, G.; Ahad, M.A.; Casalino, G. A comprehensive review of blockchain technology: Underlying principles and historical background with future challenges. Decis. Anal. J. 2023, 9, 100344. [Google Scholar] [CrossRef]
- Cash, M.; Bassiouni, M. Two-tier permission-ed and permission-less blockchain for secure data sharing. In Proceedings of the 2018 IEEE International Conference on Smart Cloud (SmartCloud), New York, NY, USA, 21–23 September 2018; IEEE: Piscataway, NJ, USA, 2018; pp. 138–144. [Google Scholar]
- Lashkari, B.; Musilek, P. A comprehensive review of blockchain consensus mechanisms. IEEE Access 2021, 9, 43620–43652. [Google Scholar] [CrossRef]
- Lepore, C.; Ceria, M.; Visconti, A.; Rao, U.P.; Shah, K.A.; Zanolini, L. A survey on blockchain consensus with a performance comparison of PoW, PoS and pure PoS. Mathematics 2020, 8, 1782. [Google Scholar] [CrossRef]
- Arslan, C.; Sipahioğlu, S.; Şafak, E.; Gözütok, M.; Köprülü, T. Comparative analysis and modern applications of PoW, PoS, PPoS blockchain consensus mechanisms and new distributed ledger technologies. Adv. Sci. Technol. Eng. Syst. J. 2021, 6, 279–290. [Google Scholar] [CrossRef]
- Lin, Z. Comparative Analysis of Blockchain Consensus. In Proceedings of the 2024 2nd International Conference on Image, Algorithms and Artificial Intelligence (ICIAAI 2024), Singapore, 9–11 August 2024; Springer Nature: Berlin/Heidelberg, Germany, 2024; Volume 115, p. 264. [Google Scholar]
- Yadav, A.K.; Singh, K.; Amin, A.H.; Almutairi, L.; Alsenani, T.R.; Ahmadian, A. A comparative study on consensus mechanism with security threats and future scopes: Blockchain. Comput. Commun. 2023, 201, 102–115. [Google Scholar] [CrossRef]
- Tao, F.; Zhang, Y.; Cheng, Y.; Ren, J.; Wang, D.; Qi, Q.; Li, P. Digital twin and blockchain enhanced smart manufacturing service collaboration and management. J. Manuf. Syst. 2022, 62, 903–914. [Google Scholar] [CrossRef]
- Bamakan, S.M.H.; Far, S.B. Distributed and trustworthy digital twin platform based on blockchain and Web3 technologies. Cyber Secur. Appl. 2025, 3, 100064. [Google Scholar] [CrossRef]
- Hasan, H.R.; Salah, K.; Jayaraman, R.; Omar, M.; Yaqoob, I.; Pesic, S.; Taylor, T.; Boscovic, D. A Blockchain-Based Approach for the Creation of Digital Twins. IEEE Access 2020, 8, 34113–34126. [Google Scholar] [CrossRef]
- Hasan, H.R.; Madine, M.; Yaqoob, I.; Salah, K.; Jayaraman, R.; Boscovic, D. Using NFTs for ownership management of digital twins and for proof of delivery of their physical assets. Future Gener. Comput. Syst. 2023, 146, 1–17. [Google Scholar] [CrossRef]
- Liang, F.; Yu, W.; An, D.; Yang, Q.; Fu, X.; Zhao, W. A Survey on Big Data Market: Pricing, Trading and Protection. IEEE Access 2018, 6, 15132–15154. [Google Scholar] [CrossRef]
- Suhail, S.; Hussain, R.; Jurdak, R.; Oracevic, A.; Salah, K.; Hong, C.S.; Matulevičius, R. Blockchain-based digital twins: Research trends, issues, and future challenges. ACM Comput. Surv. (CSUR) 2022, 54, 1–34. [Google Scholar] [CrossRef]
- Guo, H.; Yu, X. A survey on blockchain technology and its security. Blockchain Res. Appl. 2022, 3, 100067. [Google Scholar] [CrossRef]
- Kumar, N.; Aggarwal, S.; Raj, P. The Blockchain Technology for Secure and Smart Applications Across Industry Verticals; Academic Press: Cambridge, MA, USA, 2021; Volume 121. [Google Scholar]
- Dihan, M.S.; Akash, A.I.; Tasneem, Z.; Das, P.; Das, S.K.; Islam, M.R.; Islam, M.M.; Badal, F.R.; Ali, M.F.; Ahamed, M.H.; et al. Digital twin: Data exploration, architecture, implementation and future. Heliyon 2024, 10, e26503. [Google Scholar] [CrossRef]
- Shahaab, A.; Khan, I.; Maude, R.; Hewage, C. A hybrid blockchain implementation to ensure data integrity and interoperability for public service organisations. In Proceedings of the 2021 IEEE International Conference on Blockchain (Blockchain), Sydney, Australia, 3–6 May 2021; IEEE: Piscataway, NJ, USA, 2021; pp. 295–305. [Google Scholar]
- Hu, B.A.; Liu, Y.; Rong, H. Trustless Autonomy: Understanding Motivations, Benefits and Governance Dilemma in Self-Sovereign Decentralized AI Agents. arXiv 2025, arXiv:2505.09757. [Google Scholar] [CrossRef]
- Senarathna, J.I. The Role of Cryptography in Blockchain: Ensuring Immutability, Transparency and Security. Preprints 2025, 2025041814. [Google Scholar] [CrossRef]
- Wang, Y.; Su, Z.; Guo, S.; Dai, M.; Luan, T.H.; Liu, Y. A survey on digital twins: Architecture, enabling technologies, security and privacy, and future prospects. IEEE Internet Things J. 2023, 10, 14965–14987. [Google Scholar] [CrossRef]
- Wang, Y.; Su, Z.; Ni, J.; Zhang, N.; Shen, X. Blockchain-empowered space-air-ground integrated networks: Opportunities, challenges, and solutions. IEEE Commun. Surv. Tutor. 2021, 24, 160–209. [Google Scholar] [CrossRef]
- Eckhart, M.; Ekelhart, A. Digital twins for cyber-physical systems security: State of the art and outlook. In Security and Quality in Cyber-Physical Systems Engineering: With Forewords by Robert M. Lee and Tom Gilb; Springer: Berlin/Heidelberg, Germany, 2019; pp. 383–412. [Google Scholar]
- Minerva, R.; Crespi, N. Digital Twins: Properties, Software Frameworks, and Application Scenarios. IT Prof. 2021, 23, 51–55. [Google Scholar] [CrossRef]
- Dietz, M.; Pernul, G. Unleashing the Digital Twin’s Potential for ICS Security. IEEE Secur. Priv. 2020, 18, 20–27. [Google Scholar] [CrossRef]
- Suhail, S.; Jurdak, R.; Matulevicius, R.; Hong, C.S. Securing Cyber-Physical Systems Through Blockchain-Based Digital Twins and Threat Intelligence. arXiv 2021, arXiv:2105.08886. [Google Scholar]
- Mavis. The Digital Twin Automotive Revolution: An ultimate guide, TXOne Networks. 2023. Available online: https://www.txone.com/blog/digital-twins-benefits-and-challenges-revolutionary-technology-in-automotive-industries/ (accessed on 6 May 2024).
- Zhang, X.; Zhu, X.; Lessard, L. Online Data Poisoning Attacks. In Proceedings of the 2nd Conference on Learning for Dynamics and Control, Berkeley, CA, USA, 10–11 June 2020; Bayen, A.M., Jadbabaie, A., Pappas, G., Parrilo, P.A., Recht, B., Tomlin, C., Zeilinger, M., Eds.; PMLR, Proceedings of Machine Learning Research. Volume 120, pp. 201–210. [Google Scholar]
- Botín-Sanabria, D.M.; Mihaita, A.S.; Peimbert-García, R.E.; Ramírez-Moreno, M.A.; Ramírez-Mendoza, R.A.; Lozoya-Santos, J.d.J. Digital Twin Technology Challenges and Applications: A Comprehensive Review. Remote Sens. 2022, 14, 1335. [Google Scholar] [CrossRef]
- Singh, A.K.; Patro, B. Security Attacks on RFID and their Countermeasures. In Computer Communication, Networking and IoT: Proceedings of ICICC 2020; Springer: Berlin/Heidelberg, Germany, 2021; pp. 509–518. [Google Scholar]
- Aljanabi, M.; Omran, A.H.; Mijwil, M.M.; Abotaleb, M.; El-kenawy, E.S.M.; Mohammed, S.Y.; Ibrahim, A. Data poisoning: Issues, challenges, and needs. In Proceedings of the 7th IET Smart Cities Symposium (SCS 2023), Hybrid Conference, Manama, Bahrain; London, UK, 3–5 December 2023; IET: London, UK, 2023; Volume 2023, pp. 359–363. [Google Scholar]
- Xu, H.; Yu, W.; Liu, X.; Griffith, D.; Golmie, N. On Data Integrity Attacks against Industrial Internet of Things. In Proceedings of the 2020 IEEE Intl Conf on Dependable, Autonomic and Secure Computing, Intl Conf on Pervasive Intelligence and Computing, Intl Conf on Cloud and Big Data Computing, Intl Conf on Cyber Science and Technology Congress (DASC/PiCom/CBDCom/CyberSciTech), Calgary, AB, Canada, 17–22 August 2020; pp. 21–28. [Google Scholar] [CrossRef]
- Alharbi, S.; Guo, Y.; Yu, W. Collusive Backdoor Attacks in Federated Learning Frameworks for IoT Systems. IEEE Internet Things J. 2024, 11, 19694–19707. [Google Scholar] [CrossRef]
- Constantin, L. How Data Poisoning Attacks Corrupt Machine Learning Models. 2021. Available online: https://www.csoonline.com/article/570555/how-data-poisoning-attacks-corrupt-machine-learning-models.html (accessed on 6 May 2024).
- Zhou, S.; Liu, C.; Ye, D.; Zhu, T.; Zhou, W.; Yu, P.S. Adversarial attacks and defenses in deep learning: From a perspective of cybersecurity. ACM Comput. Surv. 2022, 55, 1–39. [Google Scholar] [CrossRef]
- Goldblum, M.; Tsipras, D.; Xie, C.; Chen, X.; Schwarzschild, A.; Song, D.; Mądry, A.; Li, B.; Goldstein, T. Dataset Security for Machine Learning: Data Poisoning, Backdoor Attacks, and Defenses. IEEE Trans. Pattern Anal. Mach. Intell. 2023, 45, 1563–1580. [Google Scholar] [CrossRef]
- Johnson, A. Session Hijacking: What is a Session Hijacking and How Does It Work? 2021. Available online: https://us.norton.com/blog/id-theft/session-hijacking (accessed on 6 May 2024).
- Aggarwal, P.; Narwal, B.; Purohit, S.; Mohapatra, A.K. BPADTA: Blockchain-based privacy-preserving authentication scheme for digital twin empowered aerospace industry. Comput. Electr. Eng. 2023, 111, 108889. [Google Scholar] [CrossRef]
- Gautam, D.; Thakur, G.; Kumar, P.; Das, A.K.; Park, Y. Blockchain Assisted Intra-Twin and Inter-Twin Authentication Scheme for Vehicular Digital Twin System. IEEE Trans. Intell. Transp. Syst. 2024, 25, 15002–15015. [Google Scholar] [CrossRef]
- Dai, Y.; Wu, J.; Mao, S.; Rao, X.; Gu, B.; Qu, Y.; Lu, Y. Blockchain empowered access control for digital twin system with attribute-based encryption. Future Gener. Comput. Syst. 2024, 160, 564–576. [Google Scholar] [CrossRef]
- Iyer, A.; Lee, C.; Reddy, T.; Rosenberg, C.; Wang, R.; Liu, B. SeBRUS: Mitigating Data Poisoning Attacks on Crowdsourced Datasets with Blockchain. In Proceedings of the 2023 IEEE MIT Undergraduate Research Technology Conference (URTC), Cambridge, MA, USA, 6–8 October 2023; IEEE: Piscataway, NJ, USA, 2023; pp. 1–5. [Google Scholar]
- Chatterjee, P.; Das, D.; Rawat, D.B.; Ghosh, U.; Banerjee, S.; Al-Numay, M.S. Digital Twins and Blockchain Fusion for Security in Metaverse-Driven Consumer Supply Chains. IEEE Trans. Consum. Electron. 2024, 70, 5688–5697. [Google Scholar] [CrossRef]
- Ruiu, P.; Nitti, M.; Pilloni, V.; Cadoni, M.; Grosso, E.; Fadda, M. Metaverse & Human Digital Twin: Digital Identity, Biometrics, and Privacy in the Future Virtual Worlds. Multimodal Technol. Interact. 2024, 8, 48. [Google Scholar] [CrossRef]
- Cordeiro, M.; Ferreira, J.C. Beyond Traceability: Decentralised Identity and Digital Twins for Verifiable Product Identity in Agri-Food Supply Chains. Appl. Sci. 2025, 15, 6062. [Google Scholar] [CrossRef]
- Tavakoli, P.; Yitmen, I.; Sadri, H.; Taheri, A. Blockchain-based digital twin data provenance for predictive asset management in building facilities. Smart Sustain. Built Environ. 2024, 13, 4–21. [Google Scholar] [CrossRef]
- Latifah, H.; Fauziah, Z. Blockchain teaching simulation using gamification. Aptisi Trans. Technopreneurship (ATT) 2022, 4, 184–191. [Google Scholar] [CrossRef]
- Suhail, S.; Iqbal, M.; Hussain, R.; Jurdak, R. ENIGMA: An explainable digital twin security solution for cyber–physical systems. Comput. Ind. 2023, 151, 103961. [Google Scholar] [CrossRef]
- Johnson, A. Blockchain Provides Security, Traceability for Smart Manufacturing. 2021. Available online: https://www.nist.gov/news-events/news/2019/02/nist-blockchain-provides-security-traceability-smart-manufacturing (accessed on 20 August 2024).
- Nabeeh, N.A.; Abdel-Basset, M.; Gamal, A.; Chang, V. Evaluation of Production of Digital Twins Based on Blockchain Technology. Electronics 2022, 11, 1268. [Google Scholar] [CrossRef]
- Huang, S.; Wang, G.; Yan, Y.; Fang, X. Blockchain-based data management for digital twin of product. J. Manuf. Syst. 2020, 54, 361–371. [Google Scholar] [CrossRef]
- Kumar, R.; Tripathi, R. Implementation of Distributed File Storage and Access Framework using IPFS and Blockchain. In Proceedings of the 2019 Fifth International Conference on Image Information Processing (ICIIP), Atlanta, GA, USA, 14–17 July 2019; pp. 246–251. [Google Scholar] [CrossRef]
- Kanuri, S.S. Securing Digital Twins with Decentralized Identity. LinkedIn. 2025. Available online: https://www.linkedin.com/pulse/securing-digital-twins-decentralized-identity-sasi-shekhar-kanuri-8nvfc (accessed on 18 July 2025).
- Hellenborn, B.; Eliasson, O.; Yitmen, I.; Sadri, H. Asset information requirements for blockchain-based digital twins: A data-driven predictive analytics perspective. Smart Sustain. Built Environ. 2024, 13, 22–41. [Google Scholar] [CrossRef]
- Wilson, S.; Adu-Duodu, K.; Li, Y.; Sham, R.; Almubarak, M.; Wang, Y.; Solaiman, E.; Perera, C.; Ranjan, R.; Rana, O. Blockchain-enabled provenance tracking for sustainable material reuse in construction supply chains. Future Internet 2024, 16, 135. [Google Scholar] [CrossRef]
- Suhail, S.; Jurdak, R.; Hussain, R. Security attacks and solutions for digital twins. arXiv 2022, arXiv:2202.12501. [Google Scholar]
- Vaigandla, K.K.; Karne, R.; Siluveru, M.; Kesoju, M. Review on blockchain technology: Architecture, characteristics, benefits, algorithms, challenges and applications. Mesopotamian J. Cybersecur. 2023, 2023, 73–84. [Google Scholar] [CrossRef]
- Bodkhe, U.; Tanwar, S.; Parekh, K.; Khanpara, P.; Tyagi, S.; Kumar, N.; Alazab, M. Blockchain for Industry 4.0: A Comprehensive Review. IEEE Access 2020, 8, 79764–79800. [Google Scholar] [CrossRef]
- Tosh, D.; Shetty, S.; Liang, X.; Kamhoua, C.; Njilla, L.L. Data provenance in the cloud: A blockchain-based approach. IEEE Consum. Electron. Mag. 2019, 8, 38–44. [Google Scholar] [CrossRef]
- Tikhomirov, S.; Voskresenskaya, E.; Ivanitskiy, I.; Takhaviev, R.; Marchenko, E.; Alexandrov, Y. Smartcheck: Static analysis of ethereum smart contracts. In Proceedings of the 1st International Workshop on Emerging Trends in Software Engineering for Blockchain, Gothenburg, Sweden, 27 May 2018; pp. 9–16. [Google Scholar]
- Nour El-Din, M.; Poças Martins, J.; Ramos, N.M.M.; Pereira, P.F. The Role of Blockchain-Secured Digital Twins in Promoting Smart Energy Performance-Based Contracts for Buildings. Energies 2024, 17, 3392. [Google Scholar] [CrossRef]
- Shakhbulatov, D.; Arora, A.; Dong, Z.; Rojas-Cessa, R. Blockchain Implementation for Analysis of Carbon Footprint across Food Supply Chain. In Proceedings of the 2019 IEEE International Conference on Blockchain (Blockchain), Atlanta, GA, USA, 14–17 July 2019; pp. 546–551. [Google Scholar] [CrossRef]
- Xu, C.; Zhang, P.; Xia, X.; Kong, L.; Zeng, P.; Yu, H. Digital-Twin-Assisted Intelligent Secure Task Offloading and Caching in Blockchain-Based Vehicular Edge Computing Networks. IEEE Internet Things J. 2025, 12, 4128–4143. [Google Scholar] [CrossRef]
- Sun, J.; Wang, Y. Data Security Mechanism of Digital Library Based on Blockchain. In Proceedings of the 2023 International Conference on Ambient Intelligence, Knowledge Informatics and Industrial Electronics (AIKIIE), Ballari, India, 2–3 November 2023; pp. 1–6. [Google Scholar] [CrossRef]
- Lv, Z.; Cheng, C.; Lv, H. Blockchain-Based Decentralized Learning for Security in Digital Twins. IEEE Internet Things J. 2023, 10, 21479–21488. [Google Scholar] [CrossRef]
- MathWorks. Simulink. 2025. Available online: https://www.mathworks.com/products/simulink.html (accessed on 15 July 2025).
- DLR. SUMO—Simulation of Urban MObility Documentation. 2025. Available online: https://sumo.dlr.de/docs/index.html (accessed on 15 July 2025).
- The Go Authors. The Go Programming Language. 2024. Available online: https://go.dev/ (accessed on 18 July 2025).
- OpenJS Foundation. Node.js. 2024. Available online: https://nodejs.org/ (accessed on 18 July 2025).
- NVIDIA. NVIDIA Omniverse. 2025. Available online: https://www.nvidia.com/en-us/omniverse/ (accessed on 15 July 2025).
- Raspberry Pi Foundation. Raspberry Pi. 2025. Available online: https://www.raspberrypi.com/ (accessed on 15 July 2025).
- OpenSSL Project. OpenSSL. 2025. Available online: https://www.openssl.org/ (accessed on 15 July 2025).
- REST API. RESTful API Documentation. 2025. Available online: https://www.restapi.com/ (accessed on 15 July 2025).
- TensorFlow. TensorFlow Privacy: A Library for Training Machine Learning Models with Differential Privacy. 2025. Available online: https://github.com/tensorflow/privacy (accessed on 15 July 2025).
- PyTorch. Opacus: Train PyTorch Models with Differential Privacy. 2025. Available online: https://github.com/pytorch/opacus (accessed on 15 July 2025).
- Hyperledger. Hyperledger Caliper. 2025. Available online: https://hyperledger.dk/caliper/ (accessed on 15 July 2025).
- Grafana Labs. Grafana. 2025. Available online: https://grafana.com/ (accessed on 15 July 2025).
- Sahal, R.; Alsamhi, S.H.; Brown, K.N.; O’Shea, D.; Alouffi, B. Blockchain-Based Digital Twins Collaboration for Smart Pandemic Alerting: Decentralized COVID-19 Pandemic Alerting Use Case. Comput. Intell. Neurosci. 2022, 2022, 7786441. [Google Scholar] [CrossRef]
- Zhou, Q.; Huang, H.; Zheng, Z.; Bian, J. Solutions to Scalability of Blockchain: A Survey. IEEE Access 2020, 8, 16440–16455. [Google Scholar] [CrossRef]
- Dorri, A.; Jurdak, R. Tree-Chain: A Fast Lightweight Consensus Algorithm for IoT Applications. In Proceedings of the 2020 IEEE 45th Conference on Local Computer Networks (LCN), Sydney, NSW, Australia, 16–19 November 2020; pp. 369–372. [Google Scholar] [CrossRef]
- Sasikumar, A.; Vairavasundaram, S.; Kotecha, K.; Indragandhi, V.; Ravi, L.; Selvachandran, G.; Abraham, A. Blockchain-based trust mechanism for digital twin empowered industrial internet of things. Future Gener. Comput. Syst. 2023, 141, 16–27. [Google Scholar]
- Amico, M.; Saleem, Z.H.; Kumph, M. Experimental study of Shor’s factoring algorithm using the IBM Q Experience. Phys. Rev. A 2019, 100, 012305. [Google Scholar] [CrossRef]
- Grover, L.K. A fast quantum mechanical algorithm for database search. In Proceedings of the Twenty-Eighth Annual ACM Symposium on Theory of Computing, Philadelphia, PA, USA, 22–24 May 1996; pp. 212–219. [Google Scholar]
- Popov, S. The tangle. White Pap. 2018, 1, 30. [Google Scholar]
- Giusto, E.; Vakili, M.G.; Gandino, F.; Demartini, C.; Montrucchio, B. Quantum pliers cutting the blockchain. IT Prof. 2020, 22, 90–96. [Google Scholar] [CrossRef]
- Fedorov, A.K.; Kiktenko, E.O.; Lvovsky, A.I. Quantum computers put blockchain security at risk. Nature 2018, 563, 465–467. [Google Scholar] [CrossRef]







| Acronym | Meaning |
|---|---|
| AI | Artificial Intelligence |
| CPS | Cyber-Physical Systems |
| DID | Decentralized Identity |
| DLT | Distributed Ledger Technology |
| DoS | Denial of Service |
| DT | Digital Twin |
| DTA | Digital Twin Aggregate |
| DTI | Digital Twin Instances |
| DTP | Digital Twin Prototype |
| HF | HyperLedger Fabric |
| IoT | Internet of Things |
| IPFS | InterPlanetary File System |
| MiTM | Man in the Middle |
| NFT | Non-Fungible Token |
| P2P | Peer-to-Peer |
| PBFT | Practical Byzantine Fault Tolerance |
| PDT | Performance Digital Twin |
| PoS | Proof of Stake |
| PT | Physical Twin |
| PoW | Proof of Work |
| TTC | Time to Collision |
| Reference | Solution Type | Domain | Year |
|---|---|---|---|
| [97] | Data Authentication | Blockchain and DT | 2023 |
| [98] | Data Authentication | Blockchain and DT | 2024 |
| [99] | Data Authentication | Blockchain and DT | 2024 |
| [70] | Smart Contract | Blockchain and DT | 2020 |
| [29] | Smart Contract | Blockchain and DT | 2023 |
| [100] | Smart Contract | Blockchain | 2023 |
| [101] | Smart Contract | Blockchain and DT | 2024 |
| [102] | Decentralized Identity | DT | 2024 |
| [103] | Decentralized Identity | Blockchain and DT | 2025 |
| [70] | Smart Contract | Blockchain and DT | 2020 |
| [104] | Data Provenance | Blockchain and DT | 2025 |
| [84] | Gamification | DT | 2020 |
| [105] | Gamification | Blockchain and DT | 2023 |
| [106] | Gamification | DT | 2023 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Suleiman, R.; Maradapu Vera Venkata Sai, A.; Yu, W.; Wang, C. Blockchain for Security in Digital Twins. Future Internet 2025, 17, 385. https://doi.org/10.3390/fi17090385
Suleiman R, Maradapu Vera Venkata Sai A, Yu W, Wang C. Blockchain for Security in Digital Twins. Future Internet. 2025; 17(9):385. https://doi.org/10.3390/fi17090385
Chicago/Turabian StyleSuleiman, Rahanatu, Akshita Maradapu Vera Venkata Sai, Wei Yu, and Chenyu Wang. 2025. "Blockchain for Security in Digital Twins" Future Internet 17, no. 9: 385. https://doi.org/10.3390/fi17090385
APA StyleSuleiman, R., Maradapu Vera Venkata Sai, A., Yu, W., & Wang, C. (2025). Blockchain for Security in Digital Twins. Future Internet, 17(9), 385. https://doi.org/10.3390/fi17090385







