Empowering Digital Twin for Future Networks with Graph Neural Networks: Overview, Enabling Technologies, Challenges, and Opportunities
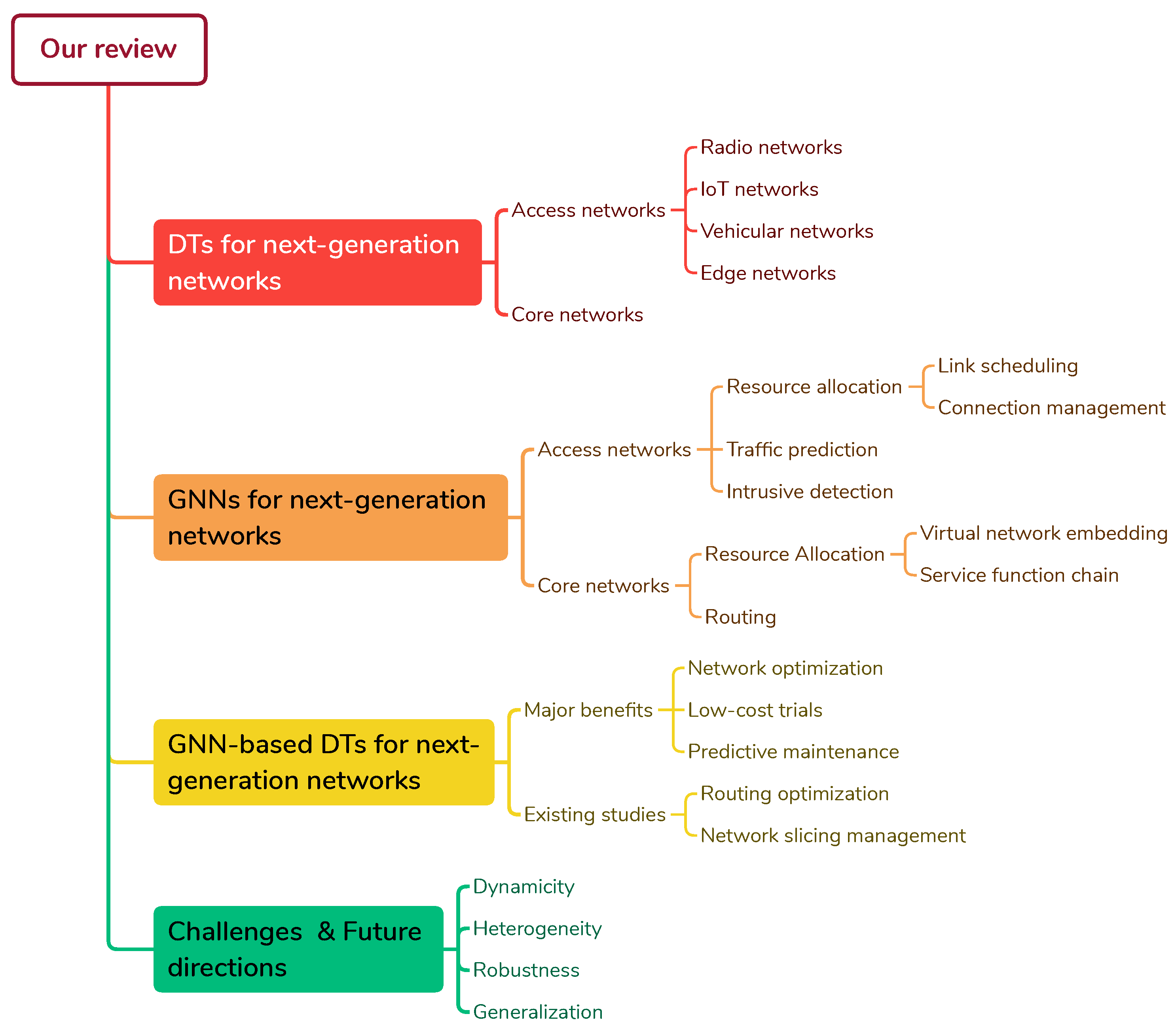
Abstract
:1. Introduction
1.1. Existing Reviews
1.2. Our Contributions
- A review of DTs applications and use cases for future networks, including both access and core networks.
- A review of several GNN-based models for network management, classified by problems and network domains.
- An analysis of potential applications of DTs based on GNNs for the Next-generation networks (GraphNDTs) and a study of existing works in this direction.
- Insights into challenges and future directions to be taken in order to improve the GraphNDTs to handle large-scale networks and their inherent sub-challenges.
1.3. Structure of the Survey
2. Digital Twins for Next-Generation Networks
2.1. Digital Twins for Access Networks
2.1.1. Radio Networks
2.1.2. Internet of Things Networks
2.1.3. Vehicular Networks
2.1.4. Edge Networks
2.2. Digital Twins for Core Networks
Lessons Learned
3. Graph Neural Networks for Next-Generation Networks
3.1. Backgrounds on Graph Neural Networks
3.1.1. Spectral-Based Graph Convolutional Networks
3.1.2. Message-Passing-Based Graph Neural Networks
3.2. GNN in Access Networks
3.2.1. Resource Allocation
| Ref. | Model | Baseline | Objective | Metric |
|---|---|---|---|---|
| [57] | DRL, GNN | Default | Throughput and coverage maximization and load balancing | Gain percentages |
| [58] | DRL, GCN | Random, CNN+DRL, PG | Data rate maximization | Data rate and convergence performances |
| [59] | DQN, GAT, A2C | DQN, A2C, Hard slicing | Data rate maximization while guaranteeing Quality of service (QoS) | Utility performances |
| [60] | GCN, Spectral clustering | Max. achievable and max. sum of rate and power | Power allocation and user association | Data rate |
| [61] | GCN, DNN | Default | Sum rate maximization | Accuracy, average sum rate |
| [62] | GCN, MWIS | Local greedy solver | Delay minimization | Accuracy, average sum rate |
Connection Management
Link Scheduling
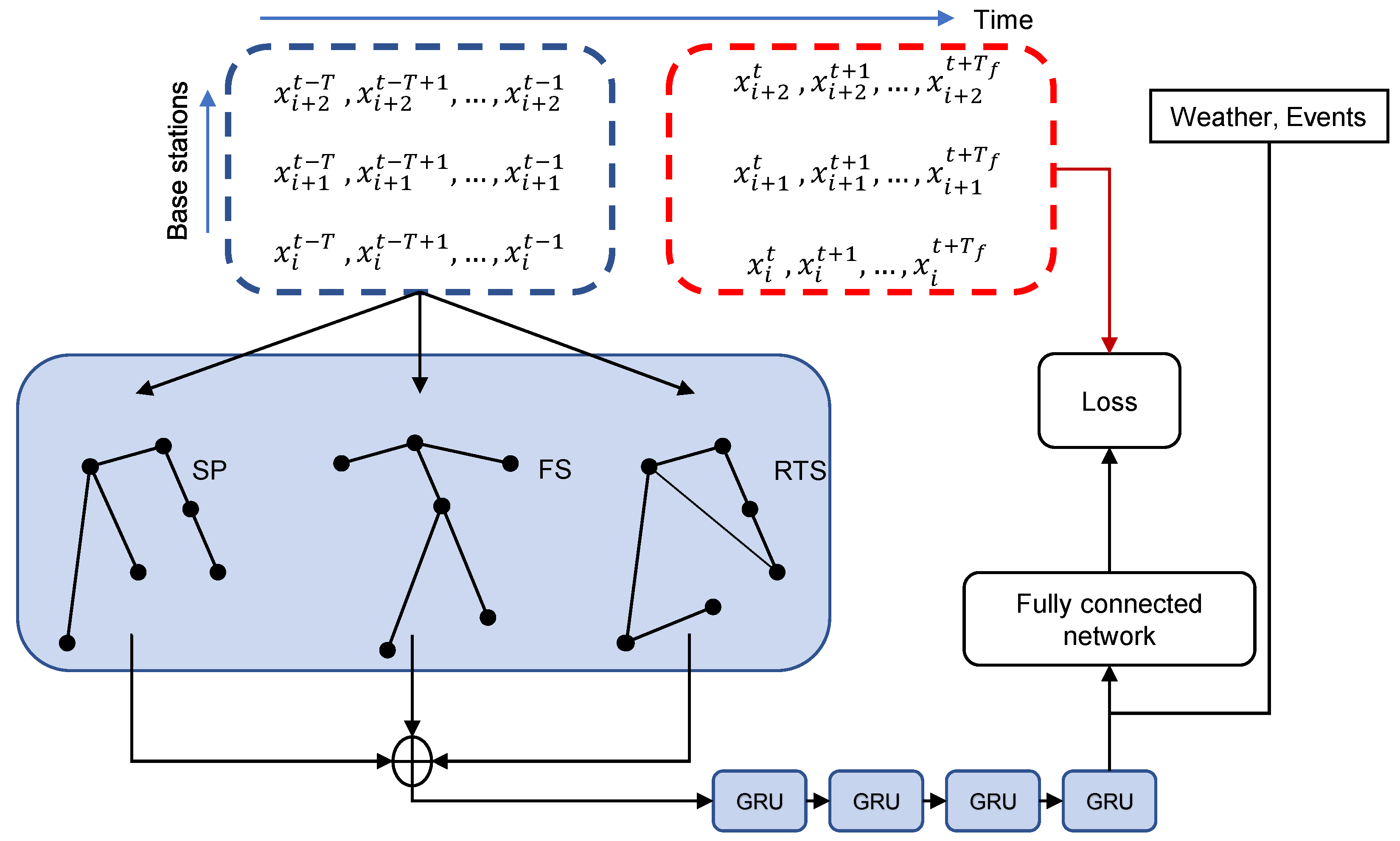
3.2.2. Traffic Prediction
3.2.3. Intrusive Detection
| Ref. | Learning | Target | Models | Dataset | Performance |
|---|---|---|---|---|---|
| [81] | Supervised | Node | GCN | - | Acc: 99.51%, 99.03% |
| [82] | Supervised | Node | Inferential SIR-GN | CAIDA + synthetic data | F1: 97.85–99.78% |
| [83] | Supervised | Node | GNN, GRU | CIC-IDS2017 | F1: 99% |
| [84] | Supervised | Node | Graph network | CTU-13 + synthetic data | ACC: 96% |
| [85] | Supervised | Edge | E-GraphSAGE, GraphSAGE | BoT-IoT, ToN-IoT, NF-BoT-IoT, NF-ToN-IoT | F1: 100%, 99%, 97%, 100% |
| [86] | Supervised | Node | E-GraphSAGE, GAT | UNSW-NB15, CIC-Darknet2020, ToN-IoT, CSE-CIC-IDS2018 | F1: 99.5%, 92.32%, 99.88%, 96.5% |
| [87] | Supervised | Node | GDN, GAT | SWaT, WADI | Acc: 99%, 98% |
| [88] | Semi-supervised | Node | GCN | CTU-13, Honeypot dataset | F1: 98.27%, 98.22% |
| [89] | Semi-supervised | Edge | GNN, Autoencoder, Attention mechanism | LANL2015, CERT, PicoDomain | F1: 89.28%, 91.28%, 92.68% |
| [90] | Supervised | Node | GIN, GNNExplainer | - | F1: 99.52%, 99.47% |
| [91] | Supervised | Node | DB-GNNExplainer | - | F1: 99.14% |
3.3. GNN in Core Networks
3.3.1. Resource Allocation
3.3.2. Routing
Lesson Learned
4. GNN-Based Digital Twins for Next-Generation Networks
4.1. Major Benefits of Using GNN-Based Digital Twins in Next-Generation Networks
4.1.1. Network Optimization
4.1.2. Low-Cost Trials
4.1.3. Predictive Maintenance
4.2. Existing Studies
4.2.1. Routing Optimization
4.2.2. Network Slicing Management
5. Challenges and Future Directions
5.1. Dynamicity
5.2. Heterogeneity
5.3. Robustness
5.4. Generalization
6. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
Abbreviations
| CSI | Channel state information |
| LSTM | Long short-term memory |
| GNN | Graph neural network |
| GCN | Graph convolutional network |
| CNN | Convolutional neural network |
| RNN | Recurrent neural network |
| GSP | Graph signal processing |
| GAT | Graph attention network |
| MAPE | Mean average percentage error |
| GRU | Gated recurrent unit |
| FL | Federated learning |
| URLLC | Ultra-reliable low-latency communication |
| UE | User equipment |
| SLA | Service level agreement |
| E2E | End-to-end |
| NDT | Network digital twin |
| DT | Digital twin |
| DRL | Deep reinforcement learning |
| RL | Reinforcement learning |
| MARL | Multi-agent reinforcement learning |
| BS | Base station |
| RAN | Radio access network |
| VNE | Virtual network embedding |
| SFC | Service function chain |
| VNF | Virtual network function |
| NFV | Network function virtualization |
| DL | Deep learning |
| SDN | Software-defined network |
| MPNN | Message-passing neural network |
| MEC | Multiple-access edge computing |
| IoT | Internet of things |
| IIoT | Industrial internet of things |
| ML | Machine learning |
| DDoS | Distributed denial of service |
| YANG | Yet another next generation |
| QoS | Quality of service |
| GFT | Graph fourier transformation |
| GraphNDT | Graph neural network-based network digital twin |
| AI | Artificial intelligence |
| NGN | Next-generation network |
References
- Almasan, P.; Ferriol-Galmes, M.; Paillisse, J.; Suarez-Varela, J.; Perino, D.; Lopez, D.; Perales, A.A.P.; Harvey, P.; Ciavaglia, L.; Wong, L.; et al. Network Digital Twin: Context, Enabling Technologies, and Opportunities. IEEE Commun. Mag. 2022, 60, 22–27. [Google Scholar] [CrossRef]
- Zhou, C.; Yang, H.; Duan, X.; Lopez, D.; Pastor, A.; Wu, Q.; Boucadair, M.; Jacquenet, C. Digital Twin Network: Concepts and Reference Architecture. 2023. Available online: https://datatracker.ietf.org/doc/draft-irtf-nmrg-network-digital-twin-arch/04/ (accessed on 1 October 2023).
- Kuruvatti, N.P.; Habibi, M.A.; Partani, S.; Han, B.; Fellan, A.; Schotten, H.D. Empowering 6G Communication Systems with Digital Twin Technology: A Comprehensive Survey. IEEE Access 2022, 10, 112158–112186. [Google Scholar] [CrossRef]
- Jiang, W. Graph-Based Deep Learning for Communication Networks: A Survey. Comput. Commun. 2022, 185, 40–54. [Google Scholar] [CrossRef]
- Vesselinova, N.; Steinert, R.; Perez-Ramirez, D.F.; Boman, M. Learning Combinatorial Optimization on Graphs: A Survey with Applications to Networking. IEEE Access 2020, 8, 120388–120416. [Google Scholar] [CrossRef]
- Zhu, Y.; Du, Y.; Wang, Y.; Xu, Y.; Zhang, J.; Liu, Q.; Wu, S. A survey on deep graph generation: Methods and applications. arXiv 2022, arXiv:2203.06714. [Google Scholar]
- He, S.; Xiong, S.; Ou, Y.; Zhang, J.; Wang, J.; Huang, Y.; Zhang, Y. An overview on the application of graph neural networks in wireless networks. IEEE Open J. Commun. Soc. 2021, 2, 2547–2565. [Google Scholar] [CrossRef]
- Suárez-Varela, J.; Almasan, P.; Ferriol-Galmés, M.; Rusek, K.; Geyer, F.; Cheng, X.; Shi, X.; Xiao, S.; Scarselli, F.; Cabellos-Aparicio, A.; et al. Graph Neural Networks for Communication Networks: Context, Use Cases and Opportunities. arXiv 2022, arXiv:2112.14792. [Google Scholar] [CrossRef]
- Yuan, H.; Yu, H.; Gui, S.; Ji, S. Explainability in graph neural networks: A taxonomic survey. IEEE Trans. Pattern Anal. Mach. Intell. 2022, 45, 5782–5799. [Google Scholar] [CrossRef]
- Skarding, J.; Gabrys, B.; Musial, K. Foundations and modeling of dynamic networks using dynamic graph neural networks: A survey. IEEE Access 2021, 9, 79143–79168. [Google Scholar] [CrossRef]
- Abadal, S.; Jain, A.; Guirado, R.; López-Alonso, J.; Alarcón, E. Computing graph neural networks: A survey from algorithms to accelerators. ACM Comput. Surv. (CSUR) 2021, 54, 1–38. [Google Scholar] [CrossRef]
- Dong, G.; Tang, M.; Wang, Z.; Gao, J.; Guo, S.; Cai, L.; Gutierrez, R.; Campbel, B.; Barnes, L.E.; Boukhechba, M. Graph neural networks in IoT: A survey. ACM Trans. Sens. Netw. 2023, 19, 1–50. [Google Scholar] [CrossRef]
- Jiang, W.; Luo, J. Graph neural network for traffic forecasting: A survey. Expert Syst. Appl. 2022, 207, 117921. [Google Scholar] [CrossRef]
- Nguyen, H.X.; Trestian, R.; To, D.; Tatipamula, M. Digital Twin for 5G and Beyond. IEEE Commun. Mag. 2021, 59, 10–15. [Google Scholar] [CrossRef]
- Wu, Y.; Zhang, K.; Zhang, Y. Digital twin networks: A survey. IEEE Internet Things J. 2021, 8, 13789–13804. [Google Scholar] [CrossRef]
- Khan, L.U.; Han, Z.; Saad, W.; Hossain, E.; Guizani, M.; Hong, C.S. Digital Twin of Wireless Systems: Overview, Taxonomy, Challenges, and Opportunities. arXiv 2022, arXiv:2202.02559. [Google Scholar] [CrossRef]
- Suhail, S.; Hussain, R.; Jurdak, R.; Oracevic, A.; Salah, K.; Hong, C.S.; Matulevičius, R. Blockchain-based digital twins: Research trends, issues, and future challenges. ACM Comput. Surv. (CSUR) 2022, 54, 1–34. [Google Scholar] [CrossRef]
- Tao, F.; Cheng, J.; Qi, Q.; Zhang, M.; Zhang, H.; Sui, F. Digital twin-driven product design, manufacturing and service with big data. Int. J. Adv. Manuf. Technol. 2018, 94, 3563–3576. [Google Scholar] [CrossRef]
- Coupaye, T.; Bolle, S.; Derrien, S.; Folz, P.; Meye, P.; Privat, G.; Raïpin-Parvedy, P. A Graph-Based Cross-Vertical Digital Twin Platform for Complex Cyber-Physical Systems; Springer International Publishing: Cham, Switzerland, 2023; pp. 337–363. [Google Scholar] [CrossRef]
- Chen, X.; Kang, E.; Shiraishi, S.; Preciado, V.M.; Jiang, Z. Digital Behavioral Twins for Safe Connected Cars. In Proceedings of the 21th ACM/IEEE International Conference on Model Driven Engineering Languages and Systems, MODELS’18, New York, NY, USA, 14–19 October 2018; pp. 144–153. [Google Scholar] [CrossRef]
- Kumar, S.A.; Madhumathi, R.; Chelliah, P.R.; Tao, L.; Wang, S. A novel digital twin-centric approach for driver intention prediction and traffic congestion avoidance. J. Reliab. Intell. Environ. 2018, 4, 199–209. [Google Scholar] [CrossRef]
- Tripathy, A.K.; Tripathy, P.K.; Mohapatra, A.G.; Ray, N.K.; Mohanty, S.P. WeDoShare: A Ridesharing Framework in Transportation Cyber-Physical System for Sustainable Mobility in Smart Cities. IEEE Consum. Electron. Mag. 2020, 9, 41–48. [Google Scholar] [CrossRef]
- Conejos Fuertes, P.; Martínez Alzamora, F.; Carot, M.H.; Campos, J.C.A. Building and exploiting a Digital Twin for the management of drinking water distribution networks. Urban Water J. 2020, 17, 704–713. [Google Scholar] [CrossRef]
- Mortlock, T.; Muthirayan, D.; Yu, S.Y.; Khargonekar, P.P.; Abdullah Al Faruque, M. Graph Learning for Cognitive Digital Twins in Manufacturing Systems. IEEE Trans. Emerg. Top. Comput. 2022, 10, 34–45. [Google Scholar] [CrossRef]
- Digital Twin Network—Requirements and Architecture; Recommendation ITU-T Y.3090; International Telecommunication Union: Geneva, Switzerland, 2022.
- Pengnoo, M.; Barros, M.T.; Wuttisittikulkij, L.; Butler, B.; Davy, A.; Balasubramaniam, S. Digital Twin for Metasurface Reflector Management in 6G Terahertz Communications. IEEE Access 2020, 8, 114580–114596. [Google Scholar] [CrossRef]
- Jiang, S.; Alkhateeb, A. Digital Twin Based Beam Prediction: Can We Train in the Digital World and Deploy in Reality? arXiv 2023, arXiv:2301.07682. [Google Scholar]
- Akbarian, F.; Fitzgerald, E.; Kihl, M. Intrusion Detection in Digital Twins for Industrial Control Systems. In Proceedings of the 2020 International Conference on Software, Telecommunications and Computer Networks (SoftCOM), Split, Croatia, 17–19 September 2020; pp. 1–6. [Google Scholar] [CrossRef]
- Eckhart, M.; Ekelhart, A. Towards Security-Aware Virtual Environments for Digital Twins. In Proceedings of the 4th ACM Workshop on Cyber-Physical System Security, Incheon, Republic of Korea, 4 June 2018. [Google Scholar]
- Eckhart, M.; Ekelhart, A. A Specification-Based State Replication Approach for Digital Twins. In Proceedings of the 2018 Workshop on Cyber-Physical Systems Security and PrivaCy, CPS-SPC’18, New York, NY, USA, 15–19 October 2018; pp. 36–47. [Google Scholar] [CrossRef]
- Benedictis, A.D.; Flammini, F.; Mazzocca, N.; Somma, A.; Vitale, F. Digital Twins for Anomaly Detection in the Industrial Internet of Things: Conceptual Architecture and Proof-of-Concept. IEEE Trans. Ind. Inform. 2023, 19, 11553–11563. [Google Scholar] [CrossRef]
- Kephart, J.; Chess, D. The vision of autonomic computing. Computer 2003, 36, 41–50. [Google Scholar] [CrossRef]
- Hui, Y.; Zhao, G.; Li, C.; Cheng, N.; Yin, Z.; Luan, T.H.; Xiao, X. Digital Twins Enabled On-Demand Matching for Multi-Task Federated Learning in HetVNets. IEEE Trans. Veh. Technol. 2023, 72, 2352–2364. [Google Scholar] [CrossRef]
- Zhao, L.; Han, G.; Li, Z.; Shu, L. Intelligent digital twin-based software-defined vehicular networks. IEEE Netw. 2020, 34, 178–184. [Google Scholar] [CrossRef]
- Lu, Y.; Maharjan, S.; Zhang, Y. Adaptive Edge Association for Wireless Digital Twin Networks in 6G. IEEE Internet Things J. 2021, 8, 16219–16230. [Google Scholar] [CrossRef]
- Van Huynh, D.; Nguyen, V.D.; Sharma, V.; Dobre, O.A.; Duong, T.Q. Digital Twin Empowered Ultra-Reliable and Low-Latency Communications-based Edge Networks in Industrial IoT Environment. In Proceedings of the ICC 2022—IEEE International Conference on Communications, Seoul, Republic of Korea, 16–20 May 2022; pp. 5651–5656. [Google Scholar] [CrossRef]
- Do-Duy, T.; Van Huynh, D.; Dobre, O.A.; Canberk, B.; Duong, T.Q. Digital Twin-Aided Intelligent Offloading with Edge Selection in Mobile Edge Computing. IEEE Wirel. Commun. Lett. 2022, 11, 806–810. [Google Scholar] [CrossRef]
- Duong, T.Q.; Van Huynh, D.; Li, Y.; Garcia-Palacios, E.; Sun, K. Digital Twin-enabled 6G Aerial Edge Computing with Ultra-Reliable and Low-Latency Communications: (Invited Paper). In Proceedings of the 2022 1st International Conference on 6G Networking (6GNet), Paris, France, 6–8 July 2022; pp. 1–5. [Google Scholar] [CrossRef]
- Wang, D.; Zhang, Z.; Zhang, M.; Fu, M.; Li, J.; Cai, S.; Zhang, C.; Chen, X. The Role of Digital Twin in Optical Communication: Fault Management, Hardware Configuration, and Transmission Simulation. IEEE Commun. Mag. 2021, 59, 133–139. [Google Scholar] [CrossRef]
- Cho, K.; van Merrienboer, B.; Gülçehre, Ç.; Bahdanau, D.; Bougares, F.; Schwenk, H.; Bengio, Y. Learning Phrase Representations using RNN Encoder-Decoder for Statistical Machine Translation. In Proceedings of the 2014 Conference on Empirical Methods in Natural Language Processing, EMNLP 2014, Doha, Qatar, 25–29 October 2014; a Meeting of SIGDAT, a Special Interest Group of the ACL. Moschitti, A., Pang, B., Daelemans, W., Eds.; Association for Computational Linguistics: Kerrville, TX, USA, 2014; pp. 1724–1734. [Google Scholar] [CrossRef]
- Chen, T.; Guestrin, C. XGBoost: A Scalable Tree Boosting System. In Proceedings of the 22nd ACM SIGKDD International Conference on Knowledge Discovery and Data Mining (KDD’16), San Francisco, CA, USA, 13–17 August 2016; pp. 785–794. [Google Scholar] [CrossRef]
- Hochreiter, S.; Schmidhuber, J. Long Short-Term Memory. Neural Comput. 1997, 9, 1735–1780. [Google Scholar] [CrossRef] [PubMed]
- Seilov, S.Z.; Kuzbayev, A.T.; Seilov, A.A.; Shyngisov, D.S.; Goikhman, V.Y.; Levakov, A.K.; Sokolov, N.A.; Zhursinbek, Y.S. The Concept of Building a Network of Digital Twins to Increase the Efficiency of Complex Telecommunication Systems. Complexity 2021, 2021, 9480235. [Google Scholar] [CrossRef]
- Yigit, Y.; Bal, B.; Karameseoglu, A.; Duong, T.Q.; Canberk, B. Digital Twin-Enabled Intelligent DDoS Detection Mechanism for Autonomous Core Networks. IEEE Commun. Stand. Mag. 2022, 6, 38–44. [Google Scholar] [CrossRef]
- Ortega, A.; Frossard, P.; Kovačević, J.; Moura, J.M.F.; Vandergheynst, P. Graph Signal Processing: Overview, Challenges, and Applications. Proc. IEEE 2018, 106, 808–828. [Google Scholar] [CrossRef]
- Defferrard, M.; Bresson, X.; Vandergheynst, P. Convolutional Neural Networks on Graphs with Fast Localized Spectral Filtering Convolutional Neural Networks on Graphs with Fast Localized Spectral Filtering. Proc. Adv. Neural Inf. Process. Syst. 2016, 29, 3844–3852. [Google Scholar]
- Li, Y.; Yu, R.; Shahabi, C.; Liu, Y. Diffusion Convolutional Recurrent Neural Network: Data-Driven Traffic Forecasting. In Proceedings of the International Conference on Learning Representations (ICLR’18), Vancouver, BC, Canada, 30 April–3 May 2018. [Google Scholar]
- Kipf, T.N.; Welling, M. Semi-Supervised Classification with Graph Convolutional Networks. In Proceedings of the International Conference on Learning Representations (ICLR), Toulon, France, 24–26 April 2017. [Google Scholar]
- Gilmer, J.; Schoenholz, S.S.; Riley, P.F.; Vinyals, O.; Dahl, G.E. Neural Message Passing for Quantum Chemistry. In Proceedings of the 34th International Conference on Machine Learning—ICML’17, Sydney, Australia, 6–11 August 2017; Volume 70, pp. 1263–1272. [Google Scholar]
- Veličković, P.; Cucurull, G.; Casanova, A.; Romero, A.; Liò, P.; Bengio, Y. Graph Attention Networks. In Proceedings of the International Conference on Learning Representations, Vancouver, BC, Canada, 30 April–3 May 2018. [Google Scholar]
- Maas, A.L.; Hannun, A.Y.; Ng, A.Y. Rectifier Nonlinearities Improve Neural Network Acoustic Models. In Proceedings of the 30th International Conference on Machine Learning, Atlanta, GA, USA, 16–21 June 2013; Volume 28. [Google Scholar]
- Vaswani, A.; Shazeer, N.M.; Parmar, N.; Uszkoreit, J.; Jones, L.; Gomez, A.N.; Kaiser, L.; Polosukhin, I. Attention is All you Need. Adv. Neural Inf. Process. Syst. 2016, 30, 5998–6008. [Google Scholar]
- Zhou, J.; Cui, G.; Hu, S.; Zhang, Z.; Yang, C.; Liu, Z.; Wang, L.; Li, C.; Sun, M. Graph neural networks: A review of methods and applications. AI Open 2020, 1, 57–81. [Google Scholar] [CrossRef]
- Xu, K.; Hu, W.; Leskovec, J.; Jegelka, S. How Powerful are Graph Neural Networks? In Proceedings of the International Conference on Learning Representations, New Orleans, LA, USA, 6–9 May 2019. [Google Scholar]
- Alon, U.; Yahav, E. On the Bottleneck of Graph Neural Networks and its Practical Implications. In Proceedings of the International Conference on Learning Representations, Virtual, 3–7 May 2021. [Google Scholar]
- Rampášek, L.; Galkin, M.; Dwivedi, V.P.; Luu, A.T.; Wolf, G.; Beaini, D. Recipe for a General, Powerful, Scalable Graph Transformer. Adv. Neural Inf. Process. Syst. 2022, 35, 14501–14515. [Google Scholar]
- Orhan, O.; Swamy, V.N.; Tetzlaff, T.; Nassar, M.; Nikopour, H.; Talwar, S. Connection Management xAPP for O-RAN RIC: A Graph Neural Network and Reinforcement Learning Approach. In Proceedings of the 2021 20th IEEE International Conference on Machine Learning and Applications (ICMLA), Pasadena, CA, USA, 13–16 December 2021; pp. 936–941. [Google Scholar] [CrossRef]
- Zhao, D.; Qin, H.; Song, B.; Han, B.; Du, X.; Guizani, M. A Graph Convolutional Network-Based Deep Reinforcement Learning Approach for Resource Allocation in a Cognitive Radio Network. Sensors 2020, 20, 5216. [Google Scholar] [CrossRef]
- Shao, Y.; Li, R.; Hu, B.; Wu, Y.; Zhao, Z.; Zhang, H. Graph Attention Network-Based Multi-Agent Reinforcement Learning for Slicing Resource Management in Dense Cellular Network. IEEE Trans. Veh. Technol. 2021, 70, 10792–10803. [Google Scholar] [CrossRef]
- Hou, K.; Xu, Q.; Zhang, X.; Huang, Y.; Yang, L. User Association and Power Allocation Based on Unsupervised Graph Model in Ultra-Dense Network. In Proceedings of the 2021 IEEE Wireless Communications and Networking Conference (WCNC), Nanjing, China, 29 March–1 April 2021; pp. 1–6. [Google Scholar] [CrossRef]
- Lee, M.; Yu, G.; Li, G.Y. Wireless Link Scheduling for D2D Communications with Graph Embedding Technique. In Proceedings of the ICC 2020—2020 IEEE International Conference on Communications (ICC), Dublin, Ireland, 7–11 June 2020; pp. 1–6. [Google Scholar] [CrossRef]
- Zhao, Z.; Verma, G.; Swami, A.; Segarra, S. Delay-Oriented Distributed Scheduling Using Graph Neural Networks. In Proceedings of the ICASSP 2022—2022 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP), Singapore, 23–27 May 2022; pp. 8902–8906. [Google Scholar] [CrossRef]
- Zhang, K.; Yang, Z.; Başar, T. Multi-Agent Reinforcement Learning: A Selective Overview of Theories and Algorithms. In Handbook of Reinforcement Learning and Control; Vamvoudakis, K.G., Wan, Y., Lewis, F.L., Cansever, D., Eds.; Springer International Publishing: Cham, Switzerland, 2021; pp. 321–384. [Google Scholar] [CrossRef]
- Mnih, V.; Kavukcuoglu, K.; Silver, D.; Rusu, A.A.; Veness, J.; Bellemare, M.G.; Graves, A.; Riedmiller, M.A.; Fidjeland, A.K.; Ostrovski, G.; et al. Human-level control through deep reinforcement learning. Nature 2015, 518, 529–533. [Google Scholar] [CrossRef]
- Sutton, R.S.; McAllester, D.; Singh, S.; Mansour, Y. Policy Gradient Methods for Reinforcement Learning with Function Approximation. In Proceedings of the Advances in Neural Information Processing Systems; Solla, S., Leen, T., Müller, K., Eds.; MIT Press: Cambridge, MA, USA, 1999; Volume 12. [Google Scholar]
- Lohrasbinasab, I.; Shahraki, A.; Taherkordi, A.; Delia Jurcut, A. From statistical-to machine learning-based network traffic prediction. Trans. Emerg. Telecommun. Technol. 2022, 33, e4394. [Google Scholar] [CrossRef]
- Ye, J.; Zhao, J.; Ye, K.; Xu, C. How to build a graph-based deep learning architecture in traffic domain: A survey. IEEE Trans. Intell. Transp. Syst. 2020, 23, 3904–3924. [Google Scholar] [CrossRef]
- Wang, X.; Zhou, Z.; Xiao, F.; Xing, K.; Yang, Z.; Liu, Y.; Peng, C. Spatio-temporal analysis and prediction of cellular traffic in metropolis. IEEE Trans. Mob. Comput. 2018, 18, 2190–2202. [Google Scholar] [CrossRef]
- He, K.; Huang, Y.; Chen, X.; Zhou, Z.; Yu, S. Graph attention spatial-temporal network for deep learning based mobile traffic prediction. In Proceedings of the 2019 IEEE Global Communications Conference (GLOBECOM), Waikoloa, HI, USA, 9–13 December 2019; pp. 1–6. [Google Scholar]
- Yang, L.; Jiang, X.; Ji, Y.; Wang, H.; Abraham, A.; Liu, H. Gated graph convolutional network based on spatio-temporal semi-variogram for link prediction in dynamic complex network. Neurocomputing 2022, 505, 289–303. [Google Scholar] [CrossRef]
- Kalander, M.; Zhou, M.; Zhang, C.; Yi, H.; Pan, L. Spatio-temporal hybrid graph convolutional network for traffic forecasting in telecommunication networks. arXiv 2020, arXiv:2009.09849. [Google Scholar]
- Zhou, X.; Zhang, Y.; Li, Z.; Wang, X.; Zhao, J.; Zhang, Z. Large-scale cellular traffic prediction based on graph convolutional networks with transfer learning. Neural Comput. Appl. 2022, 34, 5549–5559. [Google Scholar] [CrossRef]
- Zhao, S.; Jiang, X.; Jacobson, G.; Jana, R.; Hsu, W.L.; Rustamov, R.; Talasila, M.; Aftab, S.A.; Chen, Y.; Borcea, C. Cellular network traffic prediction incorporating handover: A graph convolutional approach. In Proceedings of the 2020 17th Annual IEEE International Conference on Sensing, Communication, and Networking (SECON), Como, Italy, 22–25 June 2020; pp. 1–9. [Google Scholar]
- Wei, G. A Summary of Traffic Flow Forecasting Methods. J. Highw. Transp. Res. Dev. 2004, 21, 82–85. [Google Scholar]
- Feng, H.; Shu, Y. Study on network traffic prediction techniques. In Proceedings of the 2005 International Conference on Wireless Communications, Networking and Mobile Computing, Wuhan, China, 26 September 2005; Volume 2, pp. 1041–1044. [Google Scholar]
- Dalgkitsis, A.; Louta, M.D.; Karetsos, G.T. Traffic forecasting in cellular networks using the LSTM RNN. In Proceedings of the 22nd Pan-Hellenic Conference on Informatics, Athens, Greece, 29 November–1 December 2018. [Google Scholar]
- Yu, L.; Li, M.; Jin, W.; Guo, Y.; Wang, Q.; Yan, F.; Li, P. Step: A spatio-temporal fine-granular user traffic prediction system for cellular networks. IEEE Trans. Mob. Comput. 2020, 20, 3453–3466. [Google Scholar] [CrossRef]
- Wang, Z.; Hu, J.; Min, G.; Zhao, Z.; Chang, Z.; Wang, Z. Spatial-Temporal Cellular Traffic Prediction for 5 G and Beyond: A Graph Neural Networks-Based Approach. IEEE Trans. Ind. Inform. 2022, 19, 5722–5731. [Google Scholar] [CrossRef]
- Berndt, D.J.; Clifford, J. Using Dynamic Time Warping to Find Patterns in Time Series. In Proceedings of the KDD Workshop, Newport Beach, CA, USA, 14–17 April 1994. [Google Scholar]
- Lee, S.W.; sidgi Mohammed, H.; Mohammadi, M.; Rashidi, S.; Rahmani, A.M.; Masdari, M.; Hosseinzadeh, M. Towards secure intrusion detection systems using deep learning techniques: Comprehensive analysis and review. J. Netw. Comput. Appl. 2021, 187, 103111. [Google Scholar] [CrossRef]
- Zhou, J.; Xu, Z.; Rush, A.M.; Yu, M. Automating botnet detection with graph neural networks. arXiv 2020, arXiv:2003.06344. [Google Scholar]
- Carpenter, J.; Layne, J.; Serra, E.; Cuzzocrea, A. Detecting Botnet Nodes via Structural Node Representation Learning. In Proceedings of the 2021 IEEE International Conference on Big Data (Big Data), Orlando, FL, USA, 15–18 December 2021; pp. 5357–5364. [Google Scholar]
- Pujol-Perich, D.; Suarez-Varela, J.; Cabellos-Aparicio, A.; Barlet-Ros, P. Unveiling the potential of graph neural networks for robust intrusion detection. ACM SIGMETRICS Perform. Eval. Rev. 2022, 49, 111–117. [Google Scholar] [CrossRef]
- Protogerou, A.; Papadopoulos, S.; Drosou, A.; Tzovaras, D.; Refanidis, I. A graph neural network method for distributed anomaly detection in IoT. Evol. Syst. 2021, 12, 19–36. [Google Scholar] [CrossRef]
- Lo, W.W.; Layeghy, S.; Sarhan, M.; Gallagher, M.; Portmann, M. E-graphsage: A graph neural network based intrusion detection system for iot. In Proceedings of the NOMS 2022—2022 IEEE/IFIP Network Operations and Management Symposium, Budapest, Hungary, 25–29 April 2022; pp. 1–9. [Google Scholar]
- Chang, L.; Branco, P. Graph-based solutions with residuals for intrusion detection: The modified e-graphsage and e-resgat algorithms. arXiv 2021, arXiv:2111.13597. [Google Scholar]
- Deng, A.; Hooi, B. Graph neural network-based anomaly detection in multivariate time series. In Proceedings of the AAAI Conference on Artificial Intelligence, Virtual, 4–7 February 2021; Volume 35, pp. 4027–4035. [Google Scholar]
- Zhao, J.; Liu, X.; Yan, Q.; Li, B.; Shao, M.; Peng, H. Multi-attributed heterogeneous graph convolutional network for bot detection. Inf. Sci. 2020, 537, 380–393. [Google Scholar] [CrossRef]
- Sun, X.; Yang, J. HetGLM: Lateral Movement Detection by Discovering Anomalous Links with Heterogeneous Graph Neural Network. In Proceedings of the 2022 IEEE International Performance, Computing, and Communications Conference (IPCCC), Austin, TX, USA, 11–13 November 2022; pp. 404–411. [Google Scholar]
- Lo, W.W.; Kulatilleke, G.; Sarhan, M.; Layeghy, S.; Portmann, M. XG-BoT: An explainable deep graph neural network for botnet detection and forensics. Internet Things 2023, 22, 100747. [Google Scholar] [CrossRef]
- Zhu, X.; Zhang, Y.; Zhang, Z.; Guo, D.; Li, Q.; Li, Z. Interpretability evaluation of botnet detection model based on graph neural network. In Proceedings of the IEEE INFOCOM 2022—IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Austin, TX, USA, 11–13 November 2022; pp. 1–6. [Google Scholar]
- Aouedi, O.; Piamrat, K.; Muller, G.; Singh, K. Federated semisupervised learning for attack detection in industrial Internet of Things. IEEE Trans. Ind. Inform. 2022, 19, 286–295. [Google Scholar] [CrossRef]
- Ying, Z.; Bourgeois, D.; You, J.; Zitnik, M.; Leskovec, J. Gnnexplainer: Generating explanations for graph neural networks. Adv. Neural Inf. Process. Syst. 2019, 32, 9244–9255. [Google Scholar]
- Yan, Z.; Ge, J.; Wu, Y.; Li, L.; Li, T. Automatic Virtual Network Embedding: A Deep Reinforcement Learning Approach with Graph Convolutional Networks. IEEE J. Sel. Areas Commun. 2020, 38, 1040–1057. [Google Scholar] [CrossRef]
- Sun, P.; Lan, J.; Li, J.; Guo, Z.; Hu, Y. Combining Deep Reinforcement Learning with Graph Neural Networks for Optimal VNF Placement. IEEE Commun. Lett. 2021, 25, 176–180. [Google Scholar] [CrossRef]
- Sun, P.; Lan, J.; Guo, Z.; Zhang, D.; Chen, X.; Hu, Y.; Liu, Z. DeepMigration: Flow Migration for NFV with Graph-based Deep Reinforcement Learning. In Proceedings of the ICC 2020—2020 IEEE International Conference on Communications (ICC), Dublin, Ireland, 7–11 June 2020; pp. 1–6. [Google Scholar] [CrossRef]
- Habibi, F.; Dolati, M.; Khonsari, A.; Ghaderi, M. Accelerating Virtual Network Embedding with Graph Neural Networks. In Proceedings of the 2020 16th International Conference on Network and Service Management (CNSM), Izmir, Turkey, 2–6 November 2020; pp. 1–9. [Google Scholar] [CrossRef]
- Zhang, P.; Wang, C.; Kumar, N.; Zhang, W.; Liu, L. Dynamic Virtual Network Embedding Algorithm Based on Graph Convolution Neural Network and Reinforcement Learning. IEEE Internet Things J. 2022, 9, 9389–9398. [Google Scholar] [CrossRef]
- Heo, D.; Lange, S.; Kim, H.G.; Choi, H. Graph Neural Network based Service Function Chaining for Automatic Network Control. In Proceedings of the 2020 21st Asia-Pacific Network Operations and Management Symposium (APNOMS), Daegu, Republic of Korea, 22–25 September 2020; pp. 7–12. [Google Scholar] [CrossRef]
- Qi, S.; Li, S.; Lin, S.; Saidi, M.Y.; Chen, K. Energy-Efficient VNF Deployment for Graph-Structured SFC Based on Graph Neural Network and Constrained Deep Reinforcement Learning. In Proceedings of the 2021 22nd Asia-Pacific Network Operations and Management Symposium (APNOMS), Tainan, Taiwan, 8–10 September 2021; pp. 348–353. [Google Scholar] [CrossRef]
- Pei, J.; Hong, P.; Li, D. Virtual Network Function Selection and Chaining Based on Deep Learning in SDN and NFV-Enabled Networks. In Proceedings of the 2018 IEEE International Conference on Communications Workshops (ICC Workshops), Kansas City, MO, USA, 20–24 May 2018; pp. 1–6. [Google Scholar] [CrossRef]
- Hasselt, H.v.; Guez, A.; Silver, D. Deep Reinforcement Learning with Double Q-Learning. In Proceedings of the Thirtieth AAAI Conference on Artificial Intelligence, AAAI’16, Phoenix, AZ, USA, 12–17 February 2016; AAAI Press: Washington, DC, USA, 2016; pp. 2094–2100. [Google Scholar]
- Moy, J. OSPF Version 2. RFC 2328. 1998. Available online: https://www.rfc-editor.org/info/rfc2328 (accessed on 1 October 2023).
- Rekhter, Y.; Hares, S.; Li, T. A Border Gateway Protocol 4 (BGP-4). RFC 4271. 2006. Available online: https://www.rfc-editor.org/info/rfc4271 (accessed on 1 October 2023).
- Rusek, K.; Cholda, P. Message-Passing Neural Networks Learn Little’s Law. IEEE Commun. Lett. 2019, 23, 274–277. [Google Scholar] [CrossRef]
- Rusek, K.; Suárez-Varela, J.; Mestres, A.; Barlet-Ros, P.; Cabellos-Aparicio, A. Unveiling the Potential of Graph Neural Networks for Network Modeling and Optimization in SDN. In Proceedings of the 2019 ACM Symposium on SDN Research, San Jose, CA, USA, 3–4 April 2019; pp. 140–151. [Google Scholar] [CrossRef]
- Badia-Sampera, A.; Suárez-Varela, J.; Almasan, P.; Rusek, K.; Barlet-Ros, P.; Cabellos-Aparicio, A. Towards More Realistic Network Models Based on Graph Neural Networks. In Proceedings of the 15th International Conference on Emerging Networking EXperiments and Technologies, Orlando, FL, USA, 9–12 December 2019; pp. 14–16. [Google Scholar] [CrossRef]
- Suárez-Varela, J.; Carol-Bosch, S.; Rusek, K.; Almasan, P.; Arias, M.; Barlet-Ros, P.; Cabellos-Aparicio, A. Challenging the Generalization Capabilities of Graph Neural Networks for Network Modeling. In Proceedings of the ACM SIGCOMM 2019 Conference Posters and Demos, Beijing, China, 19–23 August 2019; pp. 114–115. [Google Scholar] [CrossRef]
- Ferriol-Galmés, M.; Suárez-Varela, J.; Paillissé, J.; Shi, X.; Xiao, S.; Cheng, X.; Barlet-Ros, P.; Cabellos-Aparicio, A. Building a Digital Twin for Network Optimization Using Graph Neural Networks. Comput. Netw. 2022, 217, 109329. [Google Scholar] [CrossRef]
- Ferriol-Galmés, M.; Paillisse, J.; Suárez-Varela, J.; Rusek, K.; Xiao, S.; Shi, X.; Cheng, X.; Barlet-Ros, P.; Cabellos-Aparicio, A. RouteNet-Fermi: Network Modeling with Graph Neural Networks. arXiv 2022, arXiv:2212.12070. [Google Scholar] [CrossRef]
- Sawada, K.; Kotani, D.; Okabe, Y. Network Routing Optimization Based on Machine Learning Using Graph Networks Robust against Topology Change. In Proceedings of the 2020 International Conference on Information Networking (ICOIN), Barcelona, Spain, 7–10 January 2020; pp. 608–615. [Google Scholar] [CrossRef]
- Chen, B.; Zhu, D.; Wang, Y.; Zhang, P. An Approach to Combine the Power of Deep Reinforcement Learning with a Graph Neural Network for Routing Optimization. Electronics 2022, 11, 368. [Google Scholar] [CrossRef]
- Sun, P.; Guo, Z.; Lan, J.; Li, J.; Hu, Y.; Baker, T. ScaleDRL: A Scalable Deep Reinforcement Learning Approach for Traffic Engineering in SDN with Pinning Control. Comput. Netw. 2021, 190, 107891. [Google Scholar] [CrossRef]
- Xu, Z.; Tang, J.; Meng, J.; Zhang, W.; Wang, Y.; Liu, C.H.; Yang, D. Experience-Driven Networking: A Deep Reinforcement Learning Based Approach. In Proceedings of the IEEE INFOCOM 2018—IEEE Conference on Computer Communications, Honolulu, HI, USA, 16–19 April 2018; pp. 1871–1879. [Google Scholar] [CrossRef]
- Swaminathan, A.; Chaba, M.; Sharma, D.K.; Ghosh, U. GraphNET: Graph Neural Networks for Routing Optimization in Software Defined Networks. Comput. Commun. 2021, 178, 169–182. [Google Scholar] [CrossRef]
- Boyan, J.; Littman, M. Packet Routing in Dynamically Changing Networks: A Reinforcement Learning Approach. Adv. Neural Inf. Process. Syst. 1993, 6, 671–678. [Google Scholar]
- Huang, R.; Guan, W.; Zhai, G.; He, J.; Chu, X. Deep Graph Reinforcement Learning Based Intelligent Traffic Routing Control for Software-Defined Wireless Sensor Networks. Appl. Sci. 2022, 12, 1951. [Google Scholar] [CrossRef]
- Stampa, G.; Arias, M.; Sanchez-Charles, D.; Muntés-Mulero, V.; Cabellos, A. A Deep-Reinforcement Learning Approach for Software-Defined Networking Routing Optimization. arXiv 2017, arXiv:1709.07080. [Google Scholar]
- Varga, A. The OMNeT++ Discrete Event Simulation System. In Proceedings of the European Simulation Multiconference (ESM’2001), Prague, Czech Republic, 6–9 June 2001. [Google Scholar]
- Williams, R.J. Simple Statistical Gradient-Following Algorithms for Connectionist Reinforcement Learning. Mach. Learn. 1992, 8, 229–256. [Google Scholar] [CrossRef]
- Konda, V.; Tsitsiklis, J. Actor-Critic Algorithms. Adv. Neural Inf. Process. Syst. 1999, 12, 1008–1014. [Google Scholar]
- Wang, H.; Wu, Y.; Min, G.; Miao, W. A Graph Neural Network-Based Digital Twin for Network Slicing Management. IEEE Trans. Ind. Inform. 2022, 18, 1367–1376. [Google Scholar] [CrossRef]
- Xu, Y.; Zhang, Y.; Guo, W.; Guo, H.; Tang, R.; Coates, M. Graphsail: Graph structure aware incremental learning for recommender systems. In Proceedings of the 29th ACM International Conference on Information & Knowledge Management, Virtual, 19–23 October 2020; pp. 2861–2868. [Google Scholar]
- Huang, V.; Sohail, S.; Mayo, M.; Botran, T.L.; Rodrigues, M.; Anderson, C.; Ooi, M. Keep It Simple: Fault Tolerance Evaluation of Federated Learning with Unreliable Clients. arXiv 2023, arXiv:2305.09856. [Google Scholar]
- Xu, C.; Qu, Y.; Xiang, Y.; Gao, L. Asynchronous federated learning on heterogeneous devices: A survey. arXiv 2021, arXiv:2109.04269. [Google Scholar] [CrossRef]
- Zhang, X.; Zitnik, M. Gnnguard: Defending graph neural networks against adversarial attacks. Adv. Neural Inf. Process. Syst. 2020, 33, 9263–9275. [Google Scholar]
- Zhu, D.; Zhang, Z.; Cui, P.; Zhu, W. Robust graph convolutional networks against adversarial attacks. In Proceedings of the 25th ACM SIGKDD International Conference on Knowledge Discovery & Data Mining, Anchorage, AK, USA, 4–8 August 2019; pp. 1399–1407. [Google Scholar]
- Zügner, D.; Akbarnejad, A.; Günnemann, S. Adversarial attacks on neural networks for graph data. In Proceedings of the 24th ACM SIGKDD International Conference on Knowledge Discovery & Data Mining, London, UK, 19–23 August 2018; pp. 2847–2856. [Google Scholar]
- He, C.; Balasubramanian, K.; Ceyani, E.; Yang, C.; Xie, H.; Sun, L.; He, L.; Yang, L.; Yu, P.S.; Rong, Y.; et al. FedGraphNN: A Federated Learning System and Benchmark for Graph Neural Networks. arXiv 2021, arXiv:2104.07145. [Google Scholar]
- Zhang, K.; Yang, C.; Li, X.; Sun, L.; Yiu, S.M. Subgraph Federated Learning with Missing Neighbor Generation. Adv. Neural Inf. Process. Syst. 2021, 34, 6671–6682. [Google Scholar]
- Liu, R.; Xing, P.; Deng, Z.; Li, A.; Guan, C.; Yu, H. Federated Graph Neural Networks: Overview, Techniques and Challenges. arXiv 2022, arXiv:2202.07256. [Google Scholar]
- Castro, F.M.; Marín-Jiménez, M.J.; Mata, N.G.; Schmid, C.; Karteek, A. End-to-End Incremental Learning. In Proceedings of the European Conference on Computer Vision, Munich, Germany, 8–14 September 2018. [Google Scholar]
- Kirkpatrick, J.; Pascanu, R.; Rabinowitz, N.C.; Veness, J.; Desjardins, G.; Rusu, A.A.; Milan, K.; Quan, J.; Ramalho, T.; Grabska-Barwinska, A.; et al. Overcoming catastrophic forgetting in neural networks. Proc. Natl. Acad. Sci. USA 2016, 114, 3521–3526. [Google Scholar] [CrossRef] [PubMed]
- McMahan, B.; Moore, E.; Ramage, D.; Hampson, S.; Arcas, B.A.y. Communication-Efficient Learning of Deep Networks from Decentralized Data. In Proceedings of the 20th International Conference on Artificial Intelligence and Statistics, PMLR, Fort Lauderdale, FL, USA, 20–22 April 2017; Volume 54, pp. 1273–1282. [Google Scholar]
- Pei, Y.; Mao, R.; Liu, Y.; Chen, C.; Xu, S.; Qiang, F. Decentralized Federated Graph Neural Networks. In Proceedings of the International Workshop on Federated and Transfer Learning for Data Sparsity and Confidentiality in Conjunction with IJCAI 2021, Montreal, QC, Canada, 21 August 2021. [Google Scholar]
- Wu, C.; Wu, F.; Cao, Y.; Huang, Y.; Xie, X. FedGNN: Federated Graph Neural Network for Privacy-Preserving Recommendation. Nat. Commun. 2022, 13, 3091. [Google Scholar] [CrossRef] [PubMed]
- Fu, X.; Zhang, J.; Meng, Z.; King, I. Magnn: Metapath aggregated graph neural network for heterogeneous graph embedding. In Proceedings of the Web Conference 2020, Taipei, Taiwan, 20–24 April 2020; pp. 2331–2341. [Google Scholar]
- Jiang, X.; Lu, Y.; Fang, Y.; Shi, C. Contrastive pre-training of gnns on heterogeneous graphs. In Proceedings of the 30th ACM International Conference on Information & Knowledge Management, Virtual, 1–5 November 2021; pp. 803–812. [Google Scholar]
- Sun, Y.; Wang, S.; Tang, X.; Hsieh, T.Y.; Honavar, V. Adversarial attacks on graph neural networks via node injections: A hierarchical reinforcement learning approach. In Proceedings of the Web Conference 2020, Taipei, Taiwan, 20–24 April 2020; pp. 673–683. [Google Scholar]
- Ferriol-Galmes, M.; Rusek, K.; Suarez-Varela, J.; Xiao, S.; Shi, X.; Cheng, X.; Wu, B.; Barlet-Ros, P.; Cabellos-Aparicio, A. RouteNet-Erlang: A Graph Neural Network for Network Performance Evaluation. In Proceedings of the IEEE INFOCOM 2022—IEEE Conference on Computer Communications, London, UK, 2–5 May 2022; pp. 2018–2027. [Google Scholar] [CrossRef]





| Ref. | Contributions | GNN | DT | Networking Applications |
|---|---|---|---|---|
| [5] | A comprehensive review of various combinatorial optimization problems on graphs, with a particular emphasis on their applications in the telecommunications domain. | * | x | * |
| [7] | A comprehensive overview of the application of GNN in wireless networks. | ✓ | x | * |
| [4,8] | A comprehensive review of graph-based deep learning models for solving problems in different types of communication networks including wireless, wired, and software-defined networks. | ✓ | x | ✓ |
| [12] | A comprehensive review of recent advances in the application of GNN to the IoT field, including a deep dive analysis of GNN design in various IoT sensing environments. | ✓ | x | * |
| [13] | A survey on traffic forecasting in the intelligent transportation system. | ✓ | x | x |
| [14] | A brief review on the application of DT with 5G networks and beyond. | x | ✓ | ✓ |
| [15] | A comprehensive survey on the digital twin network including the key features, technical challenges, and potential applications. | x | ✓ | * |
| [3] | A review of the potential use cases and scenarios in a 6G communication network where a digital twin could play an essential role. | x | * | ✓ |
| [16] | A comprehensive survey on the benefits of twins for wireless and wireless for twins. | x | ✓ | ✓ |
| [1] | Presentation of the application of GNN for the core components of network digital twins and coupling a network optimizer with the network digital twins. | * | ✓ | ✓ |
| Ours | A review of DT, GNN, and Graph neural network-based network digital twin (GraphNDT) in innovating the communication networks. | ✓ | ✓ | ✓ |
| Ref. | Models | Dataset | Baselines | Prediction Horizon | Performance |
|---|---|---|---|---|---|
| [68] | GNN | Unpublished | ARIMA, HW, LSTM | 30 min | MARE: 0.79 |
| [69] | GNN, RNN, Attention mechanism | Telecom Italia | HA, ARIMA, MLP, LSTM, CNN-LSTM | 10 min | MAE: 30.93 |
| [71] | GCN, GRU | Unpublished | HA, GCN, Attention GCN, DCRNN, Graph WaveNet | 15 min | MAE: 21.7, RMSE: 47.2 |
| [72] | Transfer learning, Attention mechanism, CNNs, and GCN | Telecom Italia | LSRM, STGCN, ASTGCN, DCRNN | 1 h | MAE: 55.46, RMSE: 116.92 |
| [73] | GCN, Gated Linear Unit | Unpublished | HW, ARIMA, LSTM | 15 min | RMSE: |
| [77] | GCN, GRU | Unpublished | ARIMA, LSTM, GNN | 5 s | MARE: |
| [78] | GNN, GAT | Telecom Italia | GNN, GRU | 10 min | MAE: 25.75, MAPE: 0.13, RMSE: 35.94 |
| Ref. | Model | Baseline | Objective | Metric |
|---|---|---|---|---|
| [94] | GCN, DRL | R-ViNE, D-ViNE, GRC, MCVNE, and NodeRank | VNE | Acceptance ratio, average revenue latency, node, and link resource utility |
| [95] | GNN, DRL | DDQN, MSGAS, Eigendecomposition | VNF placement | SFC rejection ratio, computation time |
| [96] | GNN, DRL | OFM, size-greedy, pairwise, random | Reduce flow migration cost | Migration cost, computation time |
| [97] | GNN, Kmeans | FirstFit, BestFit, GRC, NeuroViNE | Improve runtime and performance | Parallelizability, acceptance ratio, revenue and cost, CPU and link utilization |
| [98] | GNN, RL | NodeRank, MCST-VNE, GCN-VNE | Dynamic VNE, reduce resource fragmentation | Revenue, acceptance rate |
| [99] | GNN, ILP | DNN-based model | SFC | Cost (delay): average, fail ratio, overmax |
| [100] | GCN, DRL | LDG, DNN-DDQN | SFC | E2E delay |
| Ref. | Model | Baseline | Simulator | Metric |
|---|---|---|---|---|
| [105,106,107,108,109,110] | MPNN | Queueing theory, Fluid model, RouteNet | OMNeT++ | Delays in queuing networks |
| [111] | MPNN | Genetic Algorithm | - | Edge utilization |
| [112] | MPNN, DRL | Equal-cost multi-path, DRL [113,114] | OMNeT++ | Average E2E delay |
| [115] | MPNN, DRL | Shortest path, Q-Routing [116] | Mininet, Ryu | Packet delivery ratio and transmission delay |
| [117] | GCN, DRL | OSPF, DRL [118] | OMNeT++ | Packet loss rate, average delay, total number of packets forwarded |
| Challenges | Description | Future Directions |
|---|---|---|
| Dynamicity | The network topology is dynamic in a way that nodes or edges may appear or disappear, and the input data change over time. | 1. Incremental Learning can allow GNN-based models learning from new data without having to retrain from scratch, which could be particularly beneficial in dynamic environments where data continually evolve [123]. 2. FL plays a crucial role within the dynamic GNN model, particularly in handling complex, large scales, and adapting to shifts in the network structure over time [124,125]. |
| Heterogeneity | The different types of nodes and edges have different attributes, which are usually located in different feature spaces. | 1. Meta-path Aggregated Graph Neural Network (MAGNN) which can capture both the semantic and structural information in heterogeneous graphs. 2. Contrastive learning-based method, where the model is pre-trained in a self-supervised manner to learn both the semantic and structural properties of heterogeneous graphs. |
| Robustness | The ability of the model to maintain high performance even when faced with perturbations in the graph structure or feature information. | 1. Robust GNN architectures that are inherently more robust against adversarial attacks [126,127]. 2. Adversarial training methods involve integrating adversarial examples into the training process [128]. |
| Generalization | The ability to generalize GNN so that the GraphNDT can still provide accurate predictions in case of abnormal scenarios or configurations. This is mandatory for low-cost trial use cases. | 1. Train the models on additional data generated by simulations and testbeds. Transfer learning can be adopted to finetune the pre-trained models on the current NDT. 2. FL enables collaborative learning and model aggregation, allowing the GraphNDT to benefit from a broader understanding of various configurations while preserving the privacy of individual network systems [129,130,131]. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ngo, D.-T.; Aouedi, O.; Piamrat, K.; Hassan, T.; Raipin-Parvédy, P. Empowering Digital Twin for Future Networks with Graph Neural Networks: Overview, Enabling Technologies, Challenges, and Opportunities. Future Internet 2023, 15, 377. https://doi.org/10.3390/fi15120377
Ngo D-T, Aouedi O, Piamrat K, Hassan T, Raipin-Parvédy P. Empowering Digital Twin for Future Networks with Graph Neural Networks: Overview, Enabling Technologies, Challenges, and Opportunities. Future Internet. 2023; 15(12):377. https://doi.org/10.3390/fi15120377
Chicago/Turabian StyleNgo, Duc-Thinh, Ons Aouedi, Kandaraj Piamrat, Thomas Hassan, and Philippe Raipin-Parvédy. 2023. "Empowering Digital Twin for Future Networks with Graph Neural Networks: Overview, Enabling Technologies, Challenges, and Opportunities" Future Internet 15, no. 12: 377. https://doi.org/10.3390/fi15120377
APA StyleNgo, D.-T., Aouedi, O., Piamrat, K., Hassan, T., & Raipin-Parvédy, P. (2023). Empowering Digital Twin for Future Networks with Graph Neural Networks: Overview, Enabling Technologies, Challenges, and Opportunities. Future Internet, 15(12), 377. https://doi.org/10.3390/fi15120377







