25 Years of Bluetooth Technology
Abstract
1. Introduction
- We present the evolution of Bluetooth technology over the last two decades as well as current and future trends of Bluetooth.
- We describe internetworking solutions between Bluetooth and IP-based networks. We also present the communication protocols used between Bluetooth and Zigbee.
- We discuss recent attacks on Bluetooth and solutions to mitigate them.
- Finally, we highlight state-of-the-art research efforts that have been leveraging Bluetooth technology to provide innovative solutions in areas such as health, location tracking, and smart homes.
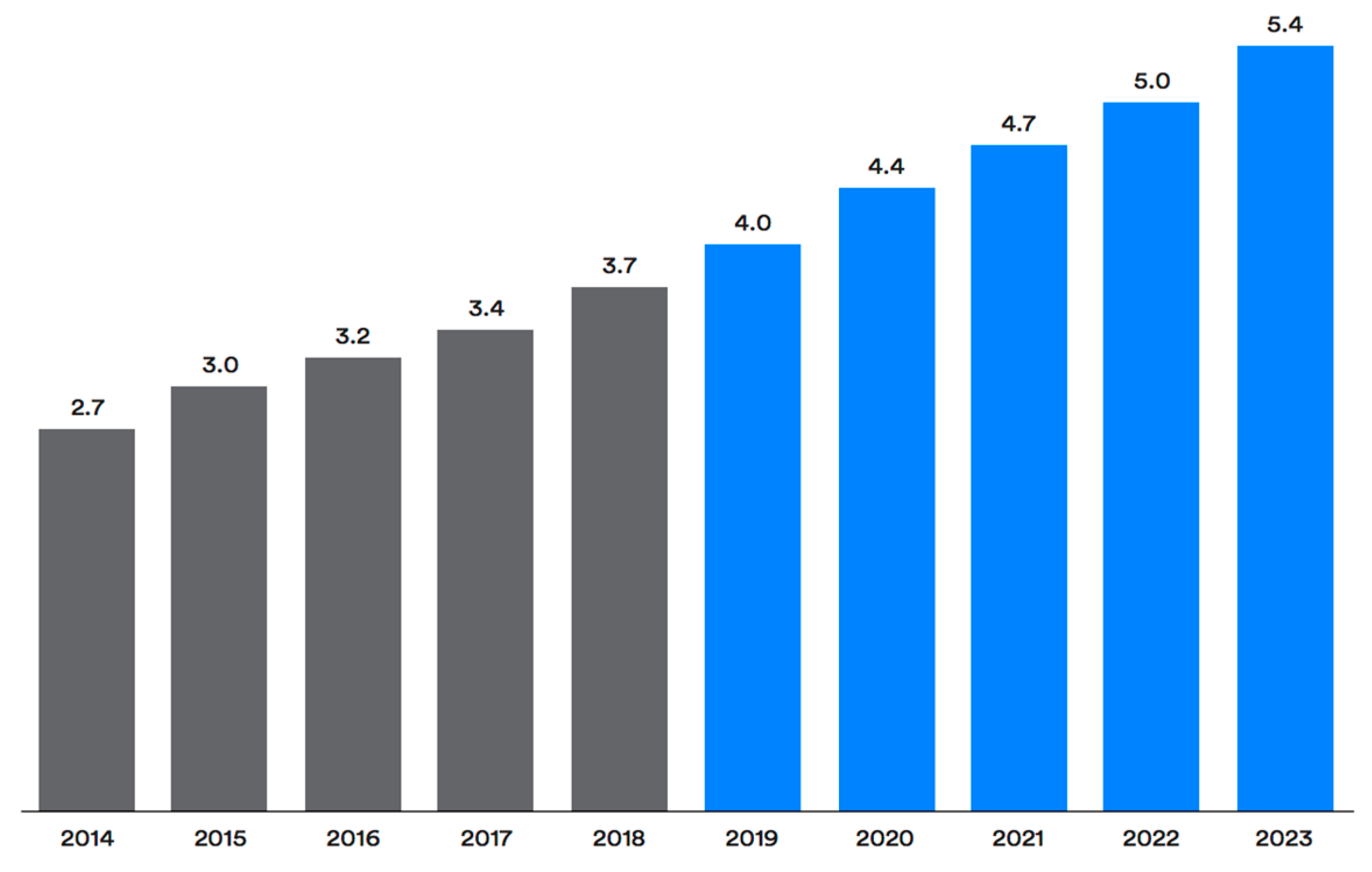
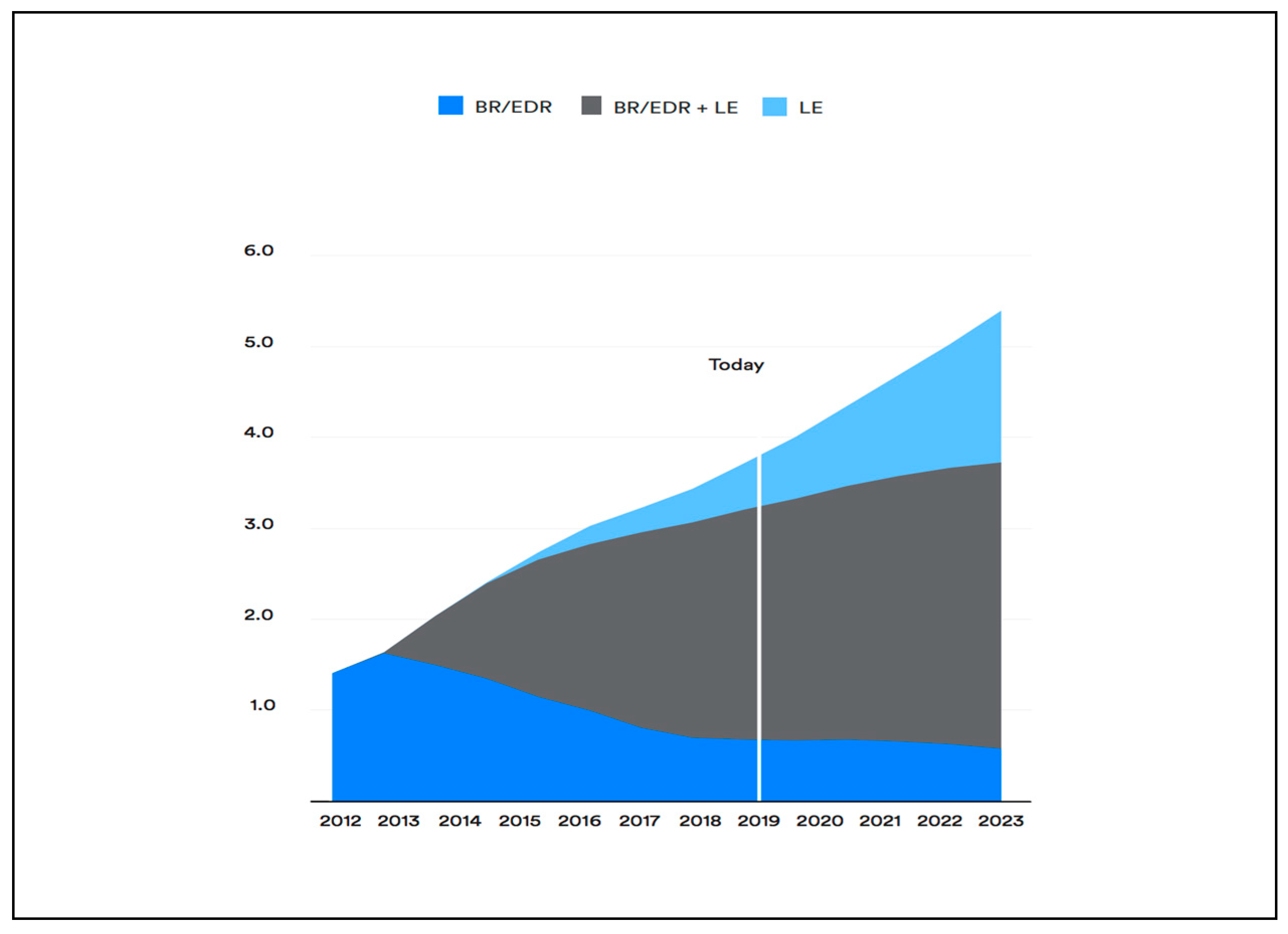
2. Bluetooth Technologies
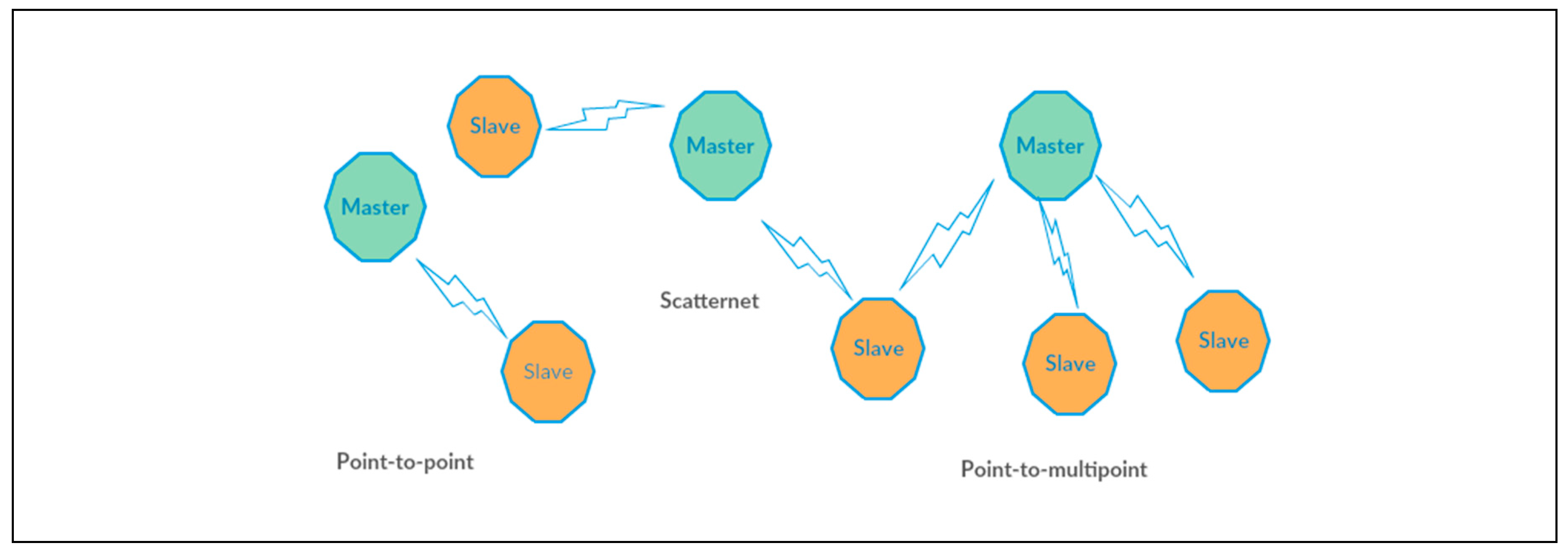
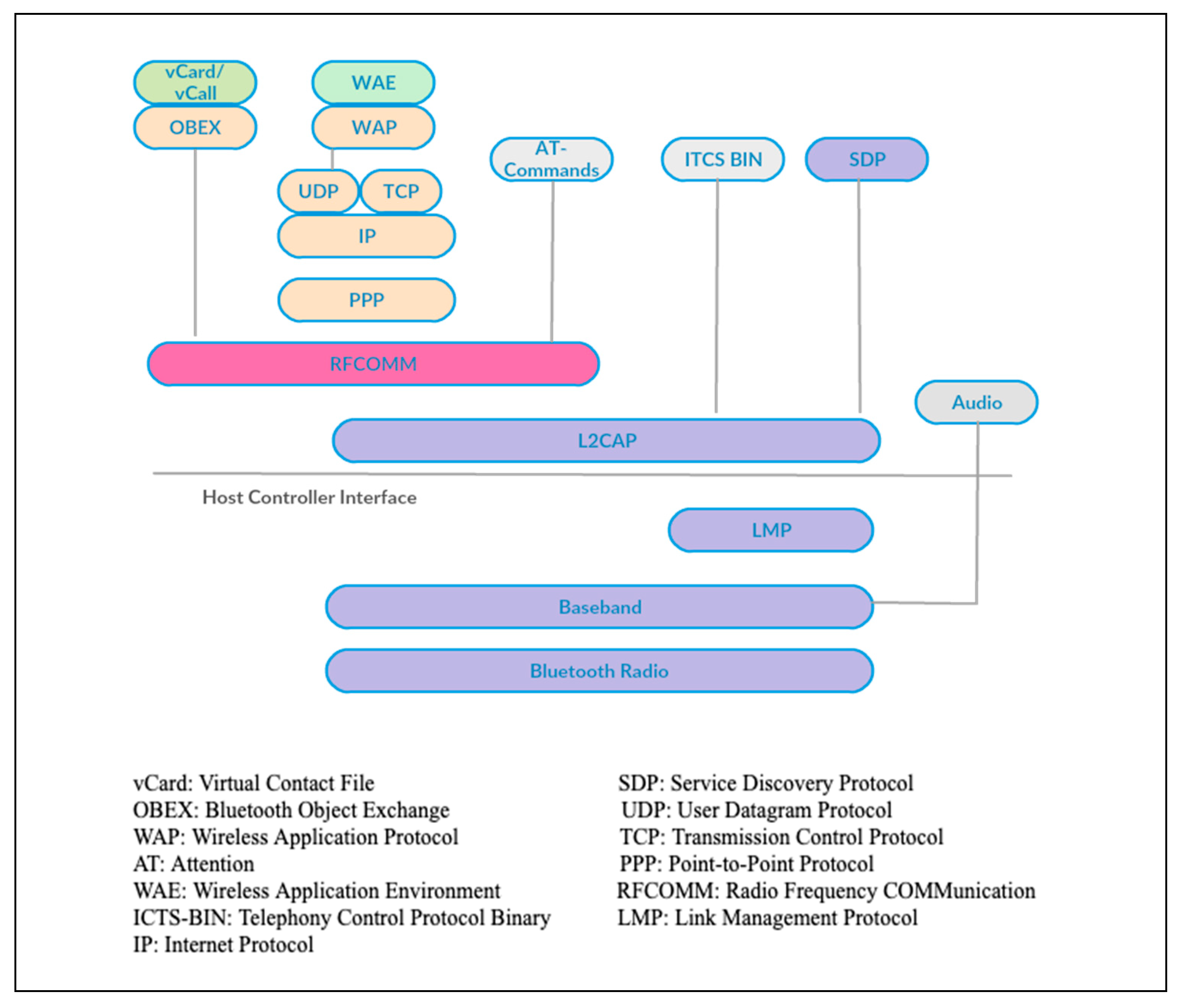
2.1. Bluetooth BR/EDR
2.1.1. Bluetooth Protocols
2.1.2. Applications of Bluetooth BR/EDR (Classic Bluetooth)
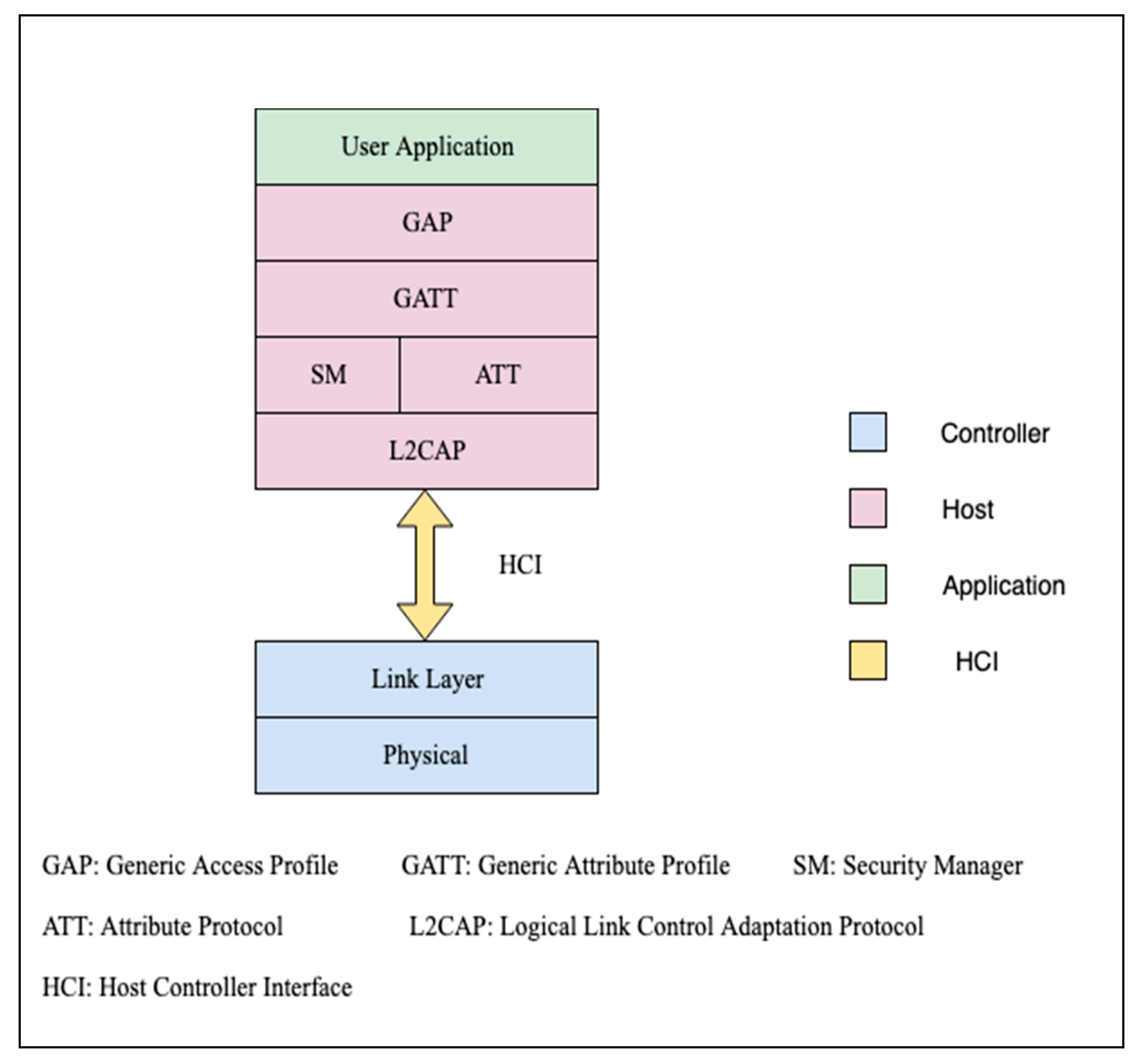
2.2. Bluetooth Low Energy
2.2.1. BLE Data Exchange Methods
2.2.2. Applications of Bluetooth Low Energy (Bluetooth Smart)
BLE Beacons
- Static Point of Interest (POI): Static POI refers to initiating an action when a user enters a specific physical area. For example, the location of the POI could map to a front reception desk or an elevator, etc. Once an individual is at or near a specific location, determining the position or direction of the user allows enhancing the user experience. For instance, a hotel could deploy BLE beacons and build applications for customers that offer the ability to unlock room doors by simply being in close proximity to the door.
- Indoor mapping: Many companies attempted to resolve the indoor geo-location issue and BLE beacons could be a potential solution. By creating applications and installing BLE beacons in big shopping centers, customers can steer through retail shops easily. This added value to customers will encourage them to keep the application open and the Bluetooth radio turned on.
- Two-way proximity: This allows the user device to act as the beacon. An action or event can be triggered on one device that sends the user’s ID and micro-location to a peer or administrator application, enabling the capability of locating other people such as friends, etc.
- Analytics: There are many prospects for marketers to collect valuable insights from BLE beacons: getting information such as who entered a specific region, at what time and for how long. Getting this information can provide insight about a specific location. Marketers can use this data to constantly customize offerings in order to instill confidence in their customers [10].
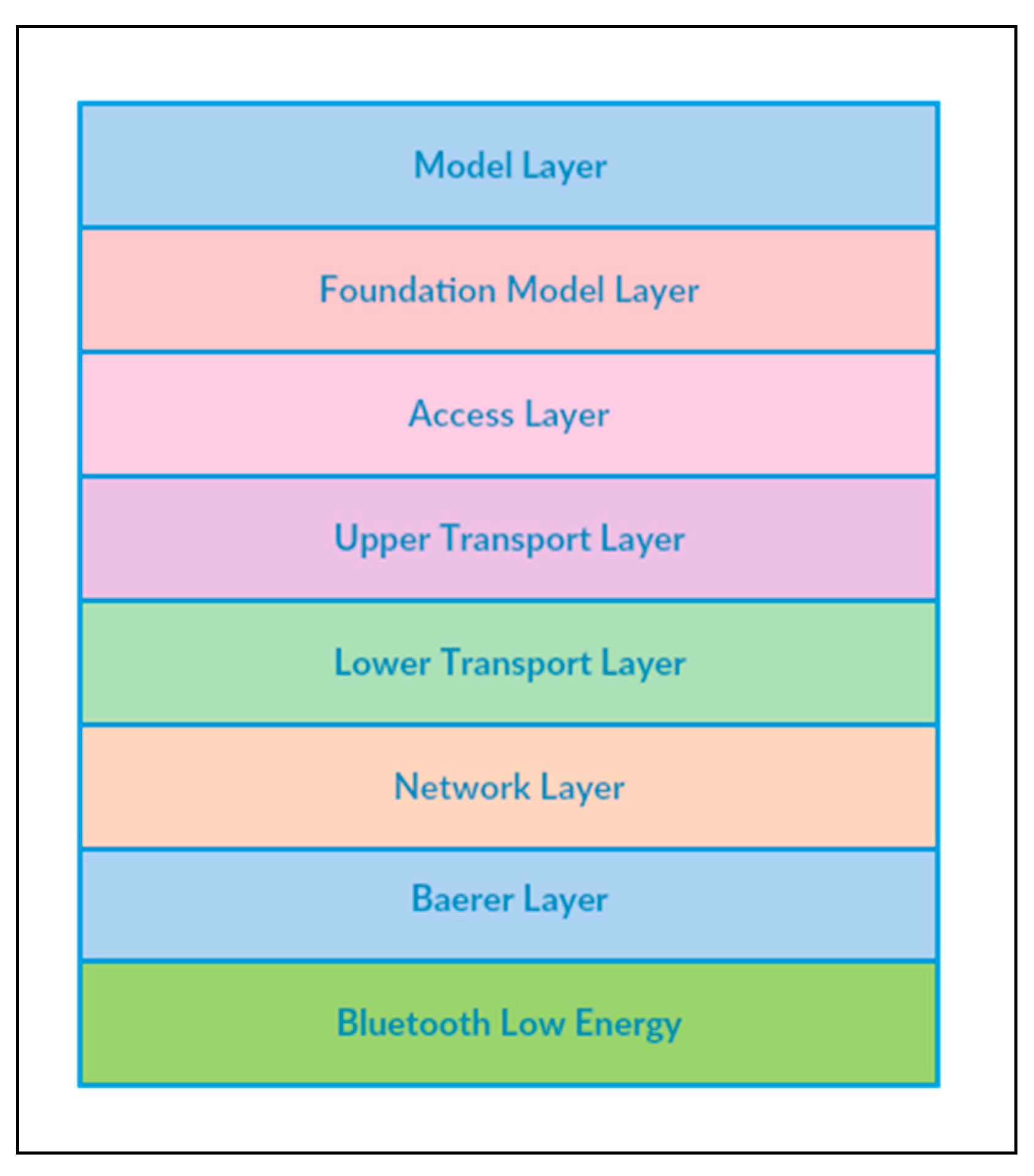
2.3. Bluetooth Mesh
2.3.1. Bluetooth Mesh Protocol Stack
- BLE Core Specification: The standard built on top of the BLE specification utilizes advertising and connection oriented features.
- Bearer layer: This layer provides an abstraction (called a “bearer”) for the underlying BLE specification for the top layers. Bearers could be Advertising (ADV) bearers or Generic Attribute Profile (GATT) bearers. The ADV bearer abstracts BLE advertising and the GATT bearer abstracts BLE connections.
- Network layer: This layer allows relaying and security.
- Transport layer: Segmenting and reassembly of messages are the primary responsibilities of this layer.
- Access layer: This layer is an interface between application focused layers and the layers below. The access layer enables correct exchange of messages between the layers above and below.
- Foundation model layer and the model layer: A model relates to the arrangement and administration of the mesh. It is possible for a Bluetooth mesh gadget to be described, as a grouping of various models, which represents a part of the application and together they represent the device. An application is implemented above this stack.
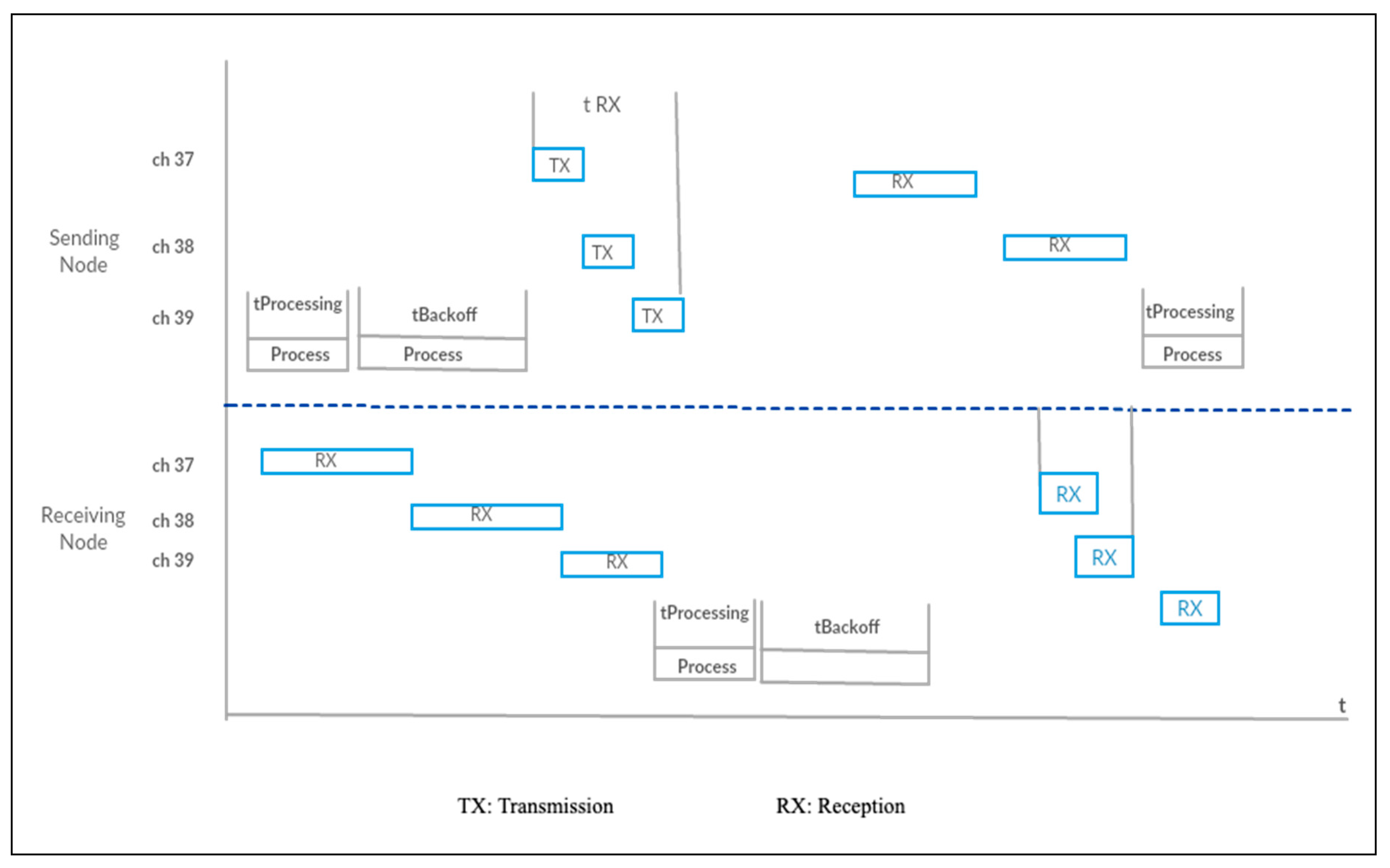
2.3.2. Communication in a Bluetooth Mesh
2.3.3. Applications of Bluetooth Mesh
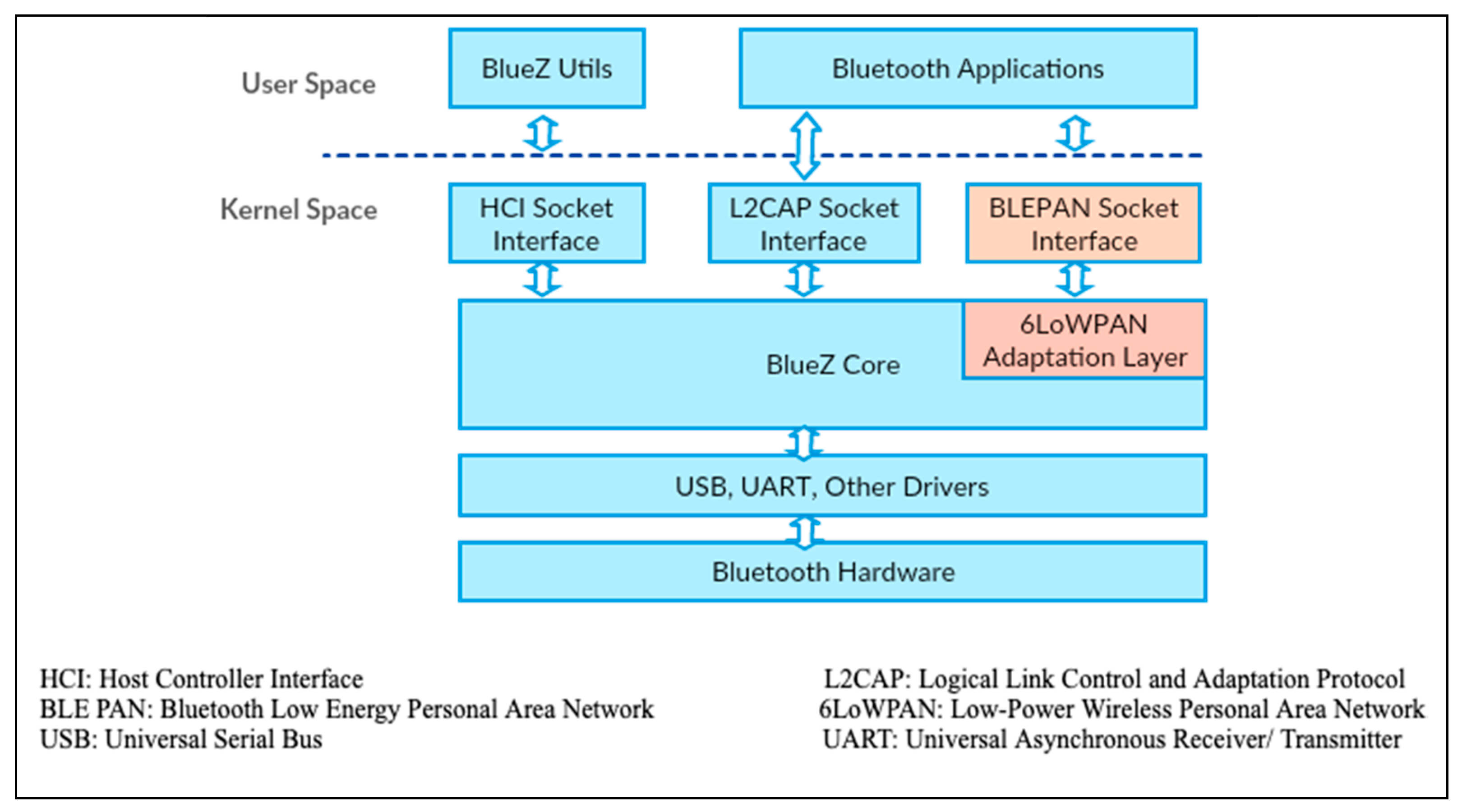
3. Connecting Bluetooth Devices to IP-Based Networks
4. Communication between Bluetooth and Zigbee
4.1. Zigbee
4.2. Bluetooth-Zigbee Interoperability
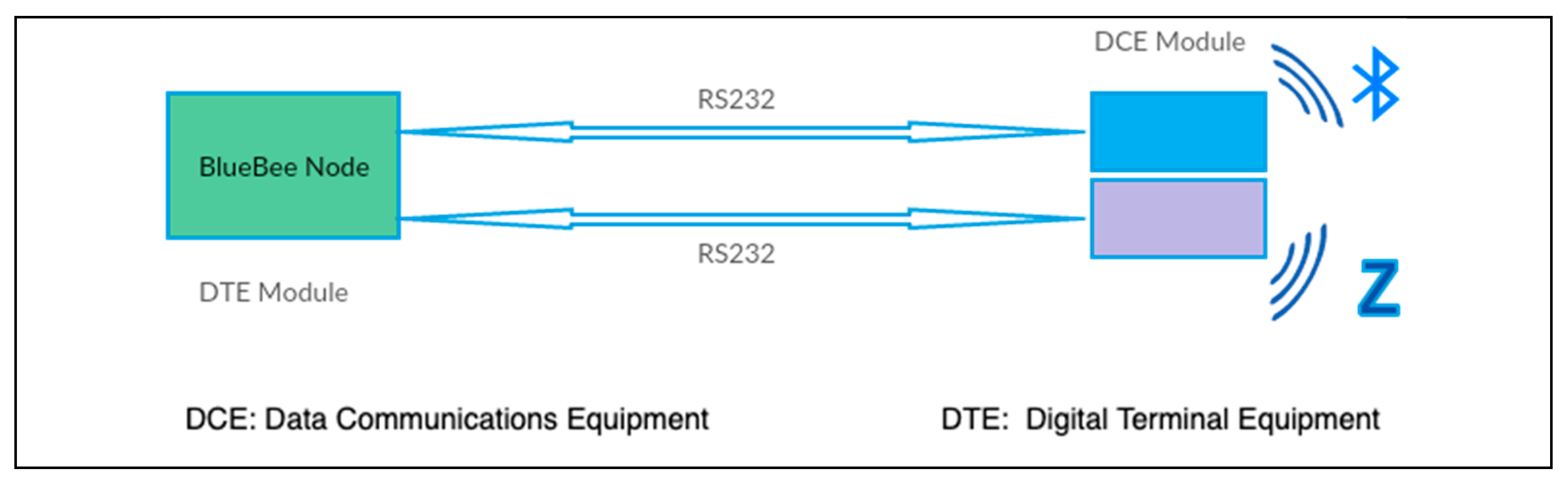
- dsPIC Microcontroller: Node settings are implemented via ATtention (AT) commands transmitted to the DCE module.
- Graphic Liquid Crystal Display (GLCD): GCLD allows the user to see various system settings and messages.
- Keyboard: Allows the user to type in text values.
- RS232 transceiver: Changes the RS232 voltage levels to UART voltages.
- Reset button: Helps restart the DTE module.
- Zigbee module: It is an Original Equipment Manufacturer (OEM) serial port adapter OZS311i Zigbee/IEEE 802.15.4 module launched by ConnectBlue [20], a manufacturer for data products and solutions. The OZS311i is an IEEE 802.15.4 implementation, with an internal antenna of approximately three-hundred-meter range.
- Bluetooth module: This is the OEM serial port adapter OBS433i that is a long range Bluetooth 2.1+EDR module (class 1), with support for the Serial Port Profile (SPP) for fast and secure transparent serial data transmissions, and the Personal Area Networking Profile (PAN). It is worth noting that the Serial Port Profile specifies the utilization of the Radio Frequency COMMunication (RFCOMM) protocol to emulate RS232 cable communications [21].
5. Bluetooth Security
- Disclosure threat: The information can leak from the target system to an eavesdropper that is not authorized to access the information.
- Integrity threat: The information can be deliberately altered to mislead the recipient.
- Denial of Service (DoS) threat: The users can be blocked from gaining access to a service by making it either unavailable or severely limiting its availability to an authorized user.
- PIN cracking
- MAC spoofing
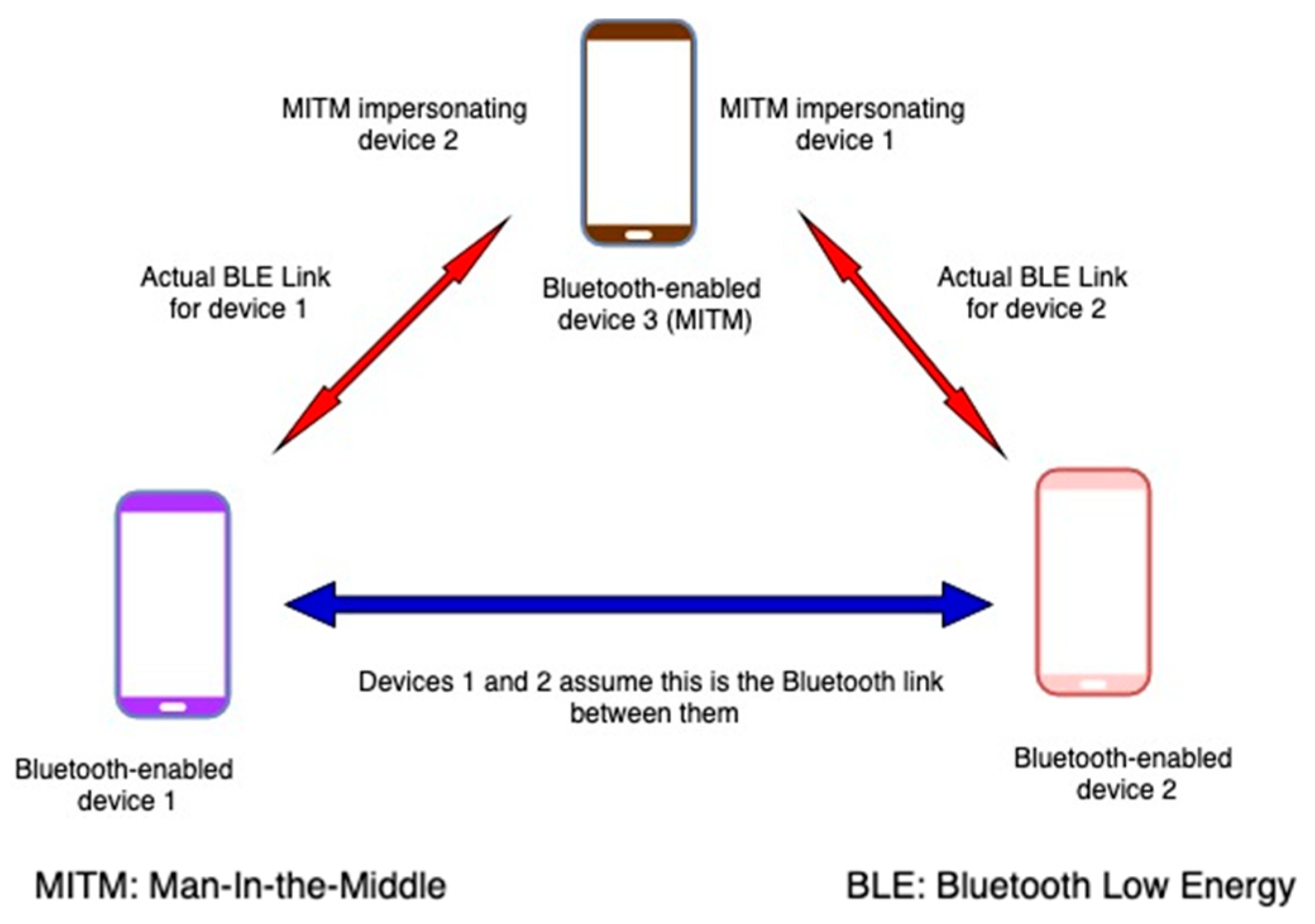
- Man-In-The-Middle (MITM) Attack
- Bluejacking attack
- BlueSnarfing attack
- Bluebugging attack
- Bluesmack attack
- BluePrinting attack
- Backdoor attack
- DoS attack
- BD_ADDR attack
- SCO/eSCO attack
- L2CAP guaranteed service attack
- Fuzzing
- BlueBorne
- MultiBlue
- Cabir worm
- Helemoto
- Reflection/Relay
Security Risks Specific to Bluetooth Low Energy
6. Recent Research Results on Bluetooth
6.1. Health
6.2. Location Tracking
6.3. Security
6.4. Smart Homes
7. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
Abbreviations
| ACL | Asynchronous Connectionless link |
| ADV | Advertising |
| API | Application Programming Interface |
| AT | Attention |
| BLE | Bluetooth Low Energy |
| BR | Basic Rate |
| CID | Context ID |
| CRC | Cyclic Redundancy Checks |
| DCE | Data Communications Equipment |
| DoS | Denial of Service |
| DPSK | Differential Phase Shift Keying |
| DQPSK | Differential Quadrature Phase Shift Keying |
| DTE | Digital Terminal Equipment |
| EDR | Enhanced Data Rate |
| FM | Frequency Modulation |
| GAP | Generic Access Profile |
| GATT | Generic Attribute Profile |
| GLCD | Graphic Liquid Crystal Display |
| GPRS | General Packet Radio Service |
| GSM | Global System for Mobile Communication |
| HCI | Host Controller Interface |
| HS | High Speed |
| IC | Integrated Circuit |
| IIoT | Industrial IoT |
| IoT | Internet of Things |
| IP | Internet Protocol |
| ISM | Industrial, Science and Medical |
| JSON | JavaScript Object Notation |
| L2CAP | Logical Link Control and Adaptation Layer Protocol |
| LAN | Local Area Network |
| LE | Low Power |
| LMP | Link Management Protocol |
| LTE | Long Term Evolution |
| MAC | Media Access Control |
| MITM | Man-In-The-Middle |
| OBEX | Bluetooth Object Exchange |
| OEM | Original Equipment Manufacturer |
| PC | Personal Computer |
| PDU | Protocol Data Unit |
| PHY | Physical |
| POI | Point of Interest |
| PSK | Frequency Modulation |
| RF | Radio Frequency |
| RFCOMM | Radio Frequency COMMunication |
| RX | Reception |
| SAR | Segmentation and Reassembly |
| SCO | Synchronous Connection-Oriented |
| SDP | Service Discovery Protocol |
| SIG | Special Interest Group |
| SM | Security Manager |
| SMS | Short Message Service |
| SPP | Serial Port Profile |
| SSP | Secure Simple Pairing |
| TCP | Transmission Control Protocol |
| TTL | Time-To-Live |
| TX | Transmission |
| UDP | User Datagram Protocol |
| vCard | Virtual Contact File |
| WAN | Wide Area Network |
| WAP | Wireless Application Protocol |
| WPAN | Wireless Personal Area Network |
| WSN | Wireless Sensor Network |
| XML | eXtensible Markup Language |
References
- Sairam, K.; Gunasekaran, N.; Redd, S. Bluetooth in wireless communication. IEEE Communications Magazine, 7 August 2002; 90–96. [Google Scholar]
- Bluetooth. Available online: https://www.bluetooth.com/ (accessed on 18 July 2019).
- Torvmark, K. Three Flavors of Bluetooth®: Which One to Choose? Texas Instruments White Paper. 2014. Available online: http://www.ti.com/lit/wp/swry007/swry007.pdf (accessed on 7 September 2019).
- Jaycon Systems Bluetooth Technology: What Has Changed Over the Years. Available online: https://medium.com/jaycon-systems/bluetooth-technology-what-has-changed-over-the-years-385da7ec7154 (accessed on 7 September 2019).
- Bluetooth. Available online: https://gtrusted.com/product/121524 (accessed on 7 September 2019).
- Mikulka, J.; Hanus, S. Bluetooth EDR Physical Layer Modeling. In Proceedings of the 18th International Conference on RadioElectronics, Prague, Czech Republic, 24–25 April 2008. [Google Scholar]
- Chada, S.; Singh, M.; Pardeshi, S. Bluetooth Technology: Principle, Applications and Current Status. Int. J. Comput. Sci. Commun. 2013, 4, 16–30. [Google Scholar]
- Dian, F.; Yousefi, A.; Lim, S. A practical study on Bluetooth Low Energy (BLE) Throughput. In Proceedings of the IEEE 9th Annual Information Technology, Electronics and Mobile Communication Conference (IEMCON), Vancouver, BC, Canada, 1–3 November 2018. [Google Scholar]
- Ethical Aspects of Nano Technology and Neuro-Computing. Bionic Gate. Available online: http://www.bionicgate.com/the-internet-of-things/ (accessed on 7 September 2019).
- Newman, N. Apple iBeacon technology briefing. J. Direct Data Digit. Mark. Pract. 2014, 15, 222–225. [Google Scholar] [CrossRef]
- Baert, M.; Rossey, J.; Shahid, A.; Hoebeke, J. The Bluetooth Mesh Standard: An Overview and Experimental Evaluation. Sensors 2018, 18, 2409. [Google Scholar] [CrossRef] [PubMed]
- The Highlights of Bluetooth Mesh Networking Technology. Silicon Labs. Available online: https://www.eetimes.com/document.asp?doc_id=1333715# (accessed on 7 September 2019).
- AN1137: Bluetooth Mesh Network Performance. Silicon Labs. Available online: https://www.silabs.com/documents/login/application-notes/an1137-bluetooth-mesh-network-performance.pdf (accessed on 7 September 2019).
- Positioning in Bluetooth and UWB Networks—Scientific Figure on ResearchGate. Available online: https://www.researchgate.net/figure/Milestones-in-the-Bluetooth-Evolution-Path_tbl2_316849796 (accessed on 7 September 2019).
- Wang, H.; Xi, M.; Liu, J.; Chen, C. Transmitting IPv6 packets over Bluetooth Low Energy based on BlueZ. In Proceedings of the 15th IEEE International Conference on Advanced Communications Technology, PyeongChang, Korea, 27–30 January 2013. [Google Scholar]
- Ed, J.; Thubert, P. Compression Format for IPv6 Datagrams over IEEE 802.15.4-Based Networks; RFC 6282; IETF: Fremont, CA, USA, 2011. [Google Scholar]
- Ramya, M.; Shanmugaraj, M.; Prabakaran, R. Study on Zigbee Technology. In Proceedings of the 3rd IEEE International Conference on Electronics Computer Technology, Kanyakumari, India, 8–10 April 2011. [Google Scholar]
- Rahman, T.; Chakraborty, S. Provisioning Technical Interoperability within Zigbee and BLE in IoT Environment. In Proceedings of the 2nd International Conference on Electronics, Materials Engineering & Nano-Technology (IEMENTech), Kolkata, India, 4–5 May 2018. [Google Scholar]
- Cano, E.; Garcia, I. Design and Development of a BlueBee Gateway for Bluetooth and Zigbee Wireless Protocols. In Proceedings of the IEEE Electronics, Robotics and Automotive Mechanics Conference, Cuernavaca, Mexico, 15–18 November 2011. [Google Scholar]
- ConnectBlue. Quality Data Products and Accessories. Available online: http://www.connectblue.com.au/ (accessed on 7 September 2019).
- Moron, M.; Luque, R.; Casilari, E. Modeling of the transmission delay in bluetooth piconets under serial port profile. IEEE Trans. Consum. Electron. 2010, 56, 2080–2085. [Google Scholar] [CrossRef]
- Chen, F.; Wang, N.; German, R.; Dressler, F. Simulation study of IEEE 802.15.4 LR-WPAN for industrial applications. Wirel. Commun. Mob. Comput. 2010, 10, 609–621. [Google Scholar] [CrossRef]
- Heynicke, R.; Krush, D.; Cammin, C.; Scholl, G.; Kaercher, B.; Ritter, J.; Gaggero, P.; Rentschler, M. O-Link Wireless enhanced factory automation communication for Industry 4.0 applications. J. Sens. Sens. Syst. 2018, 7, 131–142. [Google Scholar] [CrossRef]
- Ros, M.; D’Souza, M.; Postula, A.; MacColl, I. Location based services with personal area network for community and tourism applications. In Proceedings of the IET International Communication Conference on Wireless Mobile and Computing, Shanghai, China, 14–16 November 2011. [Google Scholar]
- Miyagawa, Y.; Segawa, N. Construction of Indoor Location Search System Using Bluetooth Low Energy. In Proceedings of the IEEE Nicograph International, Kyoto, Japan, 2–3 June 2017. [Google Scholar]
- Pule, M.; Yahya, A.; Chuma, J. Wireless sensor networks: A survey on monitoring water quality. J. Appl. Res. Technol. 2017, 15, 562–570. [Google Scholar] [CrossRef]
- Minar, N.; Tarique, M. Bluetooth Security Threats and Solutions. Int. J. Distrib. Parallel Syst. 2012, 3, 127. [Google Scholar] [CrossRef]
- Hassan, A.; Bibon, S.; Hossain, M.; Atiquzzaman, M. Security threats in Bluetooth technology. Comput. Secur. 2018, 74, 308–322. [Google Scholar] [CrossRef]
- Lonzetta, A.; Cope, P.; Campbell, J.; Mohd, B. Security Vulnerabilities in Bluetooth Technology as used in IoT. J. Sens. Actuator Netw. 2018, 7, 28. [Google Scholar] [CrossRef]
- Toivanen, P.; Haataja, K. Two practical man-in-the-middle attacks on Bluetooth secure simple pairing and countermeasures. IEEE Trans. Wirel. Commun. 2010, 9, 384–392. [Google Scholar]
- Sandhya, S.; Devi, S. Contention for Man-in-the-Middle Attacks in Bluetooth Networks. In Proceedings of the Fourth IEEE International Conference on Computational Intelligence and Communication Networks, Mathura, India, 3–5 November 2012. [Google Scholar]
- Kaviarasu, S.; Mathupandian, P. Bluejacking Technology: A Review. Int. J. Trend Res. Dev. 2016, 3. [Google Scholar] [CrossRef]
- Padgetta, J.; Batra, M.; Holtmann, M.; Chen, L.; Scarfone, L. Guide to Bluetooth Security; NIST Special Publication: Gaithersburg, MD, USA, 2017; Volume 800, p. 121. [Google Scholar]
- Dhuri, S. Bluetooth Attack and Security. Int. J. Curr. Trends Eng. Res. 2017, 3, 76–81. [Google Scholar]
- Browing, D.; Kessler, G. Bluetooth Hacking: A Case Study. Available online: https://www.garykessler.net/library/bluetooth_hacking_browning_kessler.pdf (accessed on 7 September 2019).
- Trifinite: BluePrinting. Available online: https://trifinite.org/trifinite_stuff_blueprinting.html (accessed on 7 September 2019).
- Musale, V.; Apte, S. Security Risks in Bluetooth Devices. Int. J. Comput. Appl. 2012, 51. [Google Scholar]
- Panse, P.; Panse, T. A Survey on Security Threats and Vulnerability Attacks on Bluetooth Communication. Int. J. Comput. Sci. Inf. Technol. 2013, 4, 741–746. [Google Scholar]
- Satam, P.; Satam, S.; Hariri, S. Bluetooth Intrusion Detection System. In Proceedings of the 15th IEEE International Conference on Computer Systems and Applications, Aqaba, Jordan, 28 October–1 November 2018. [Google Scholar]
- Dubey, V.; Vaishali, K.; Behar, N.; Vishwavidyalaya, G. A Review on Bluetooth Security Vulnerabilities and a Proposed Prototype Model for Enhancing Security against MITM Attack. Int. J. Res. Stud. Comput. Sci. Eng. 2015, 69–75. [Google Scholar]
- Tsira, V.; Nandi, G. Bluetooth Technology: Security Issues and its Prevention. Int. J. Comput. Technol. Appl. 2014, 5, 1833–1837. [Google Scholar]
- BlueBorne. Available online: https://armis.com/blueborne/ (accessed on 18 July 2019).
- Bon, M. A Basic Introduction to BLE Security. Available online: https://www.digikey.com/eewiki/display/Wireless/A+Basic+Introduction+to+BLE+Security (accessed on 7 September 2019).
- Wu, F.; Wu, T.; Yuce, M. Design and Implementation of a Wearable Sensor Network System for IoT-Connected Safety and Health Applications. In Proceedings of the IEEE 5th World Forum on Internet of Things (WF-IoT), Limerick, Ireland, 15–18 April 2019. [Google Scholar]
- Lam, S.; Szypula, A. Wearable emotion sensor on flexible substrate for mobile health applications. In Proceedings of the IEEE Sensors Applications Symposium (SAS), Seoul, Korea, 12–14 March 2018. [Google Scholar]
- Majumdar, S.; Rahman, M.; Islam, M.; Ghosh, D. Design and Implementation of a Wireless Health Monitoring System for Remotely Located Patients. In Proceedings of the 4th IEEE International Conference on Electrical Engineering and Information & Communication Technology (iCEEiCT), Dhaka, Bangladesh, 13–15 September 2018. [Google Scholar]
- Park, J.; Kim, J.; Kim, S. A Study on the Development of a Day-to-Day Mental Stress Monitoring System using Personal Physiological Data. In Proceedings of the 18th IEEE International Conference on Control, Automation and Systems (ICCAS), Daegwallyeong, Korea, 17–20 October 2018. [Google Scholar]
- Donati, M.; Celli, A.; Ruiu, A.; Saponara, S.; Fanucci, L. A Telemedicine Service System Exploiting BT/BLE Wireless Sensors for Remote Management of Chronic Patients. Technologies 2019, 7, 13. [Google Scholar] [CrossRef]
- Gunady, S.; Keoh, S. A Non-GPS based Location Tracking of Public Buses using Bluetooth Proximity Beacons. In Proceedings of the 5th IEEE World Forum on Internet of Things (WF-IoT), Limerick, Ireland, 15–18 April 2019. [Google Scholar]
- Kumpdetch, N.; Ayuthaya, S.; Kiattisin, S. Model of Tracking and Identification System in Micro-Location Base. In Proceedings of the 3rd IEEE Technology Innovation Management and Engineering Science International Conference (TIMES-iCON), Bangkok, Thailand, 12–14 December 2018. [Google Scholar]
- Rozum, S.; Sebesta, J. SIMO RSS measurement in Bluetooth low power indoor positioning system. In Proceedings of the 28th IEEE International Conference Radioelektronika, Prague, Czech Republic, 19–20 April 2018. [Google Scholar]
- Salti, T.; Orlando, M.; Hood, S.; Knelson, G.; Iarocci, M.; Lazzara, Z. A New Set of Bluetooth-Based Fingerprinting Algorithms for Indoor Location Services. In Proceedings of the 9th IEEE Annual Information Technology, Electronics and Mobile Communication, Vancouver, BC, Canada, 1–3 November 2018. [Google Scholar]
- Sthapit, P.; Gang, H.; Pyun, J. Bluetooth Based Indoor Positioning Using Machine Learning Algorithms. In Proceedings of the IEEE International Conference on Consumer Electronics—Asia (ICCE-Asia), Jeju, Korea, 24–26 June 2018. [Google Scholar]
- GKoufas, Y.; Braghin, S. Anatomy and Deployment of Robust AI-Centric Indoor Positioning System. In Proceedings of the IEEE International Conference on Pervasive Computing and Communications Workshops, Kyoto, Japan, 11–15 March 2019. [Google Scholar]
- Sevier, S.; Tekeaglu, A. Analyzing the Security of Bluetooth Low Energy. In Proceedings of the IEEE International Conference on Electronics, Information, and Communication (ICEIC), Auckland, New Zealand, 22–25 January 2019. [Google Scholar]
- Pallavi, S.; Narayanan, V. An Overview of Practical Attacks on BLE Based IOT Devices and Their Security. In Proceedings of the 5th IEEE International Conference on Advanced Computing & Communication Systems (ICACCS), Coimbatore, India, 15–16 March 2019. [Google Scholar]
- Martin, J.; Alpuche, D.; Bodeman, K.; Brown, L.; Fenske, E.; Foppe, L.; Mayberry, T.; Rye, E.; Sipes, B.; Teplov, S. Handoff All Your Privacy—A Review of Apple’s Bluetooth Low Energy Continuity Protocol. Proc. Priv. Enhancing Technol. 2019, 2019, 34–53. [Google Scholar] [CrossRef]
- Collotta, M.; Pau, G. A Novel Energy Management Approach for Smart Homes Using Bluetooth Low Energy. IEEE J. Sel. Areas Commun. 2015, 33, 2988–2996. [Google Scholar] [CrossRef]
- Collotta, M.; Pau, G. An Innovative Approach for Forecasting of Energy Requirements to Improve a Smart Home Management System Based on BLE. IEEE Trans. Green Commun. Netw. 2017, 1, 112–120. [Google Scholar] [CrossRef]
- Hong, J.; Levy, A.; Riliskis, L.; Levis, P. Don’t Talk Unless I Say So! Securing the Internet of Things with Default-Off Networking. In Proceedings of the IEEE/ACM Third International Conference on Internet-of-Things Design and Implementation, Orlando, FL, USA, 17–20 April 2018. [Google Scholar]
- Martinez, C.; Eras, L.; Dominguez, L. The Smart Doorbell: A proof-of-concept Implementation of a Bluetooth Mesh Network. In Proceedings of the Third IEEE Ecuador Technical Chapters Meeting (ETCM), Cuenca, Ecuador, 15–19 October 2018. [Google Scholar]
| Bluetooth Specification | v1.1 | v2.0 + EDR | v2.1 + EDR | v3.0 + HS | v4.0 + LE | v4.1 | v4.2 | v5.0 |
|---|---|---|---|---|---|---|---|---|
| Year | 2002 | 2004 | 2007 | 2009 | 2010 | 2013 | 2014 | 2016 |
| Basic Rate | YES | YES | YES | YES | YES | YES | YES | YES |
| Enhanced Data Rate (EDR) | NO | YES | YES | YES | YES | YES | YES | YES |
| High Speed (HS) | NO | NO | NO | YES | YES | YES | YES | YES |
| Low Power (LE) | NO | NO | NO | NO | YES | YES | YES | YES |
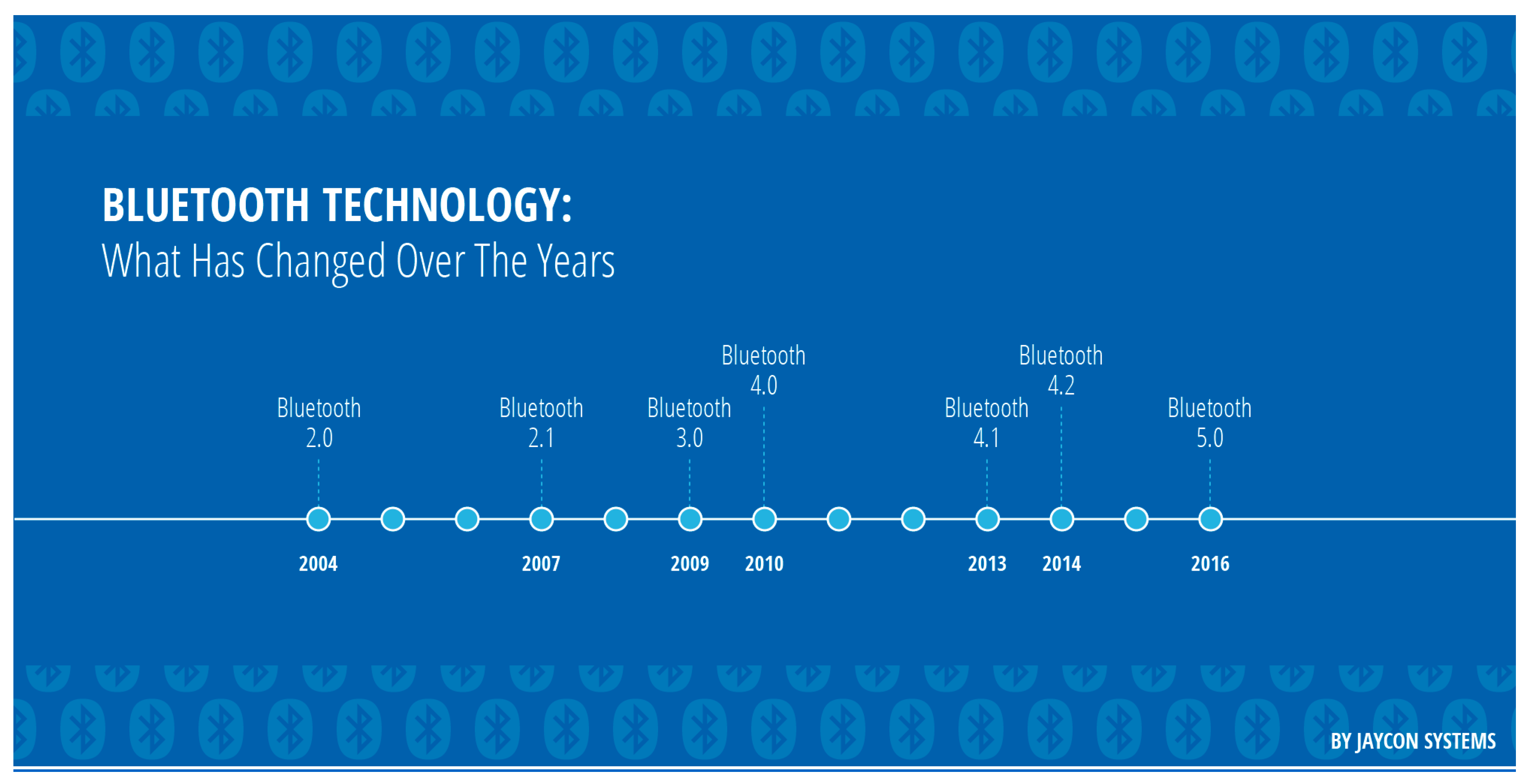
| Core Version | Issue Year | Major Improvements |
|---|---|---|
| 1.0 | 1999 | - |
| 1.2 | 2003 | Adaptive frequency hopping, inquiry-based RSSI |
| 2.0 | 2004 | 2.1 Mbps peak data rates |
| 2.1 | 2007 | 3.0 Mbps peak data rates |
| 3.0 | 2009 | 24 Mbps peak data rates |
| 4.0 | 2010 | Lower energy consumption, broadcasting, lower connection latency |
| 4.1 | 2013 | Improved device power management by pairing that allows automatic powering up and down |
| 4.2 | 2014 | Improved security, low energy data packet length extension, link layer privacy |
| 5.0 | 2016 | Higher data rates (48 Mbps), better energy efficiency, higher broadcasting message capacity, larger range and strong point-to-point connection and reliability |
| Attacks Prior to Pairing | Attacks after Pairing |
|---|---|
| BlueJacking | Backdoor |
| BlueSnarfing | Denial of Service (DoS) |
| BlueBugging | Worm |
| MAC spoofing | Bluesmack |
| Helemoto | MultiBlue |
| BluePrinting | Offline PIN recovery |
| Fuzzing | BD_ADDR |
| BlueBorne | Reflection/Relay |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Zeadally, S.; Siddiqui, F.; Baig, Z. 25 Years of Bluetooth Technology. Future Internet 2019, 11, 194. https://doi.org/10.3390/fi11090194
Zeadally S, Siddiqui F, Baig Z. 25 Years of Bluetooth Technology. Future Internet. 2019; 11(9):194. https://doi.org/10.3390/fi11090194
Chicago/Turabian StyleZeadally, Sherali, Farhan Siddiqui, and Zubair Baig. 2019. "25 Years of Bluetooth Technology" Future Internet 11, no. 9: 194. https://doi.org/10.3390/fi11090194
APA StyleZeadally, S., Siddiqui, F., & Baig, Z. (2019). 25 Years of Bluetooth Technology. Future Internet, 11(9), 194. https://doi.org/10.3390/fi11090194