Artificial Intelligence Implementations on the Blockchain. Use Cases and Future Applications
Abstract
:1. Introduction
2. On the Construction of an AI on a Blockchain
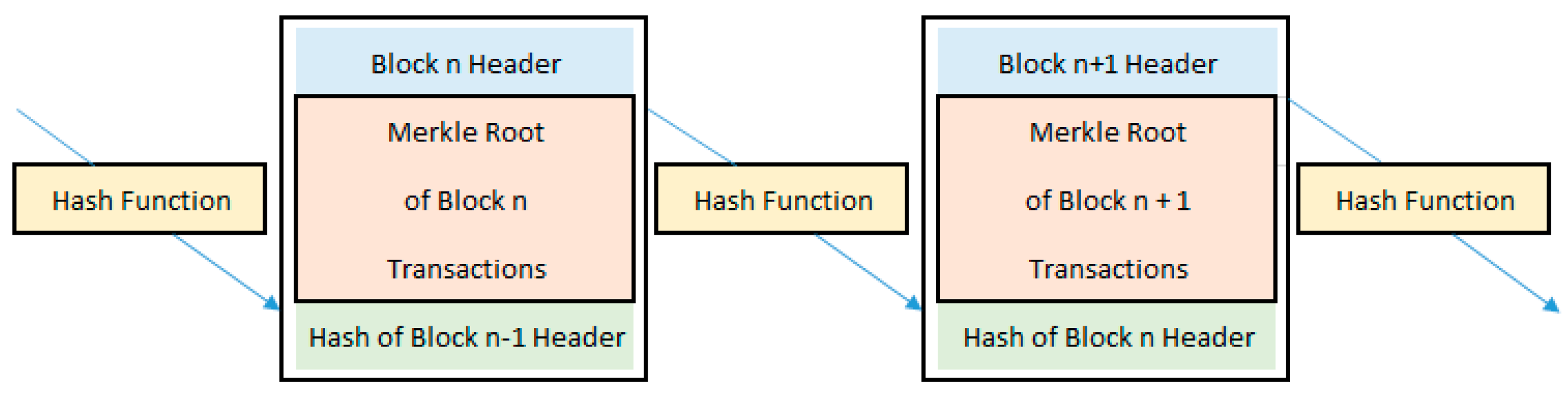
2.1. The Blockchain as a Transaction Platform
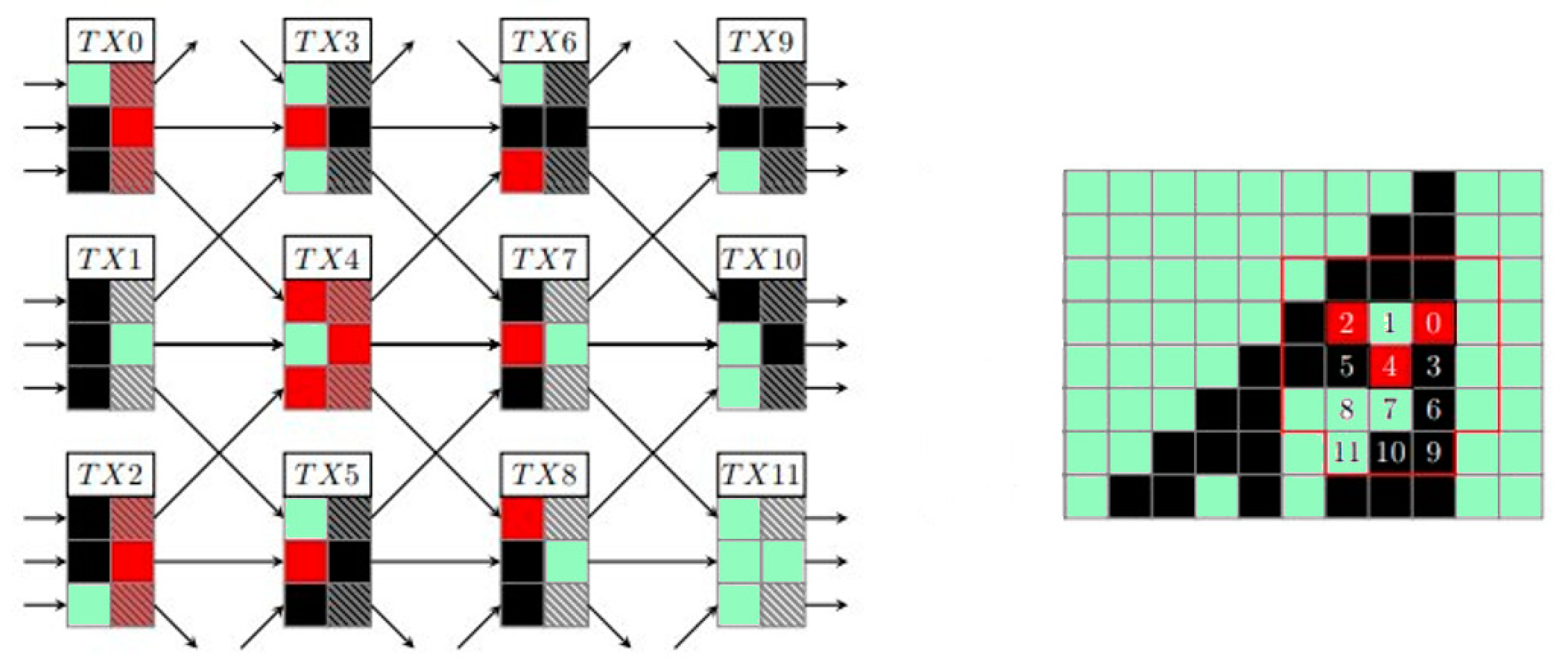
2.2. The Blockchain as a Computing Platform
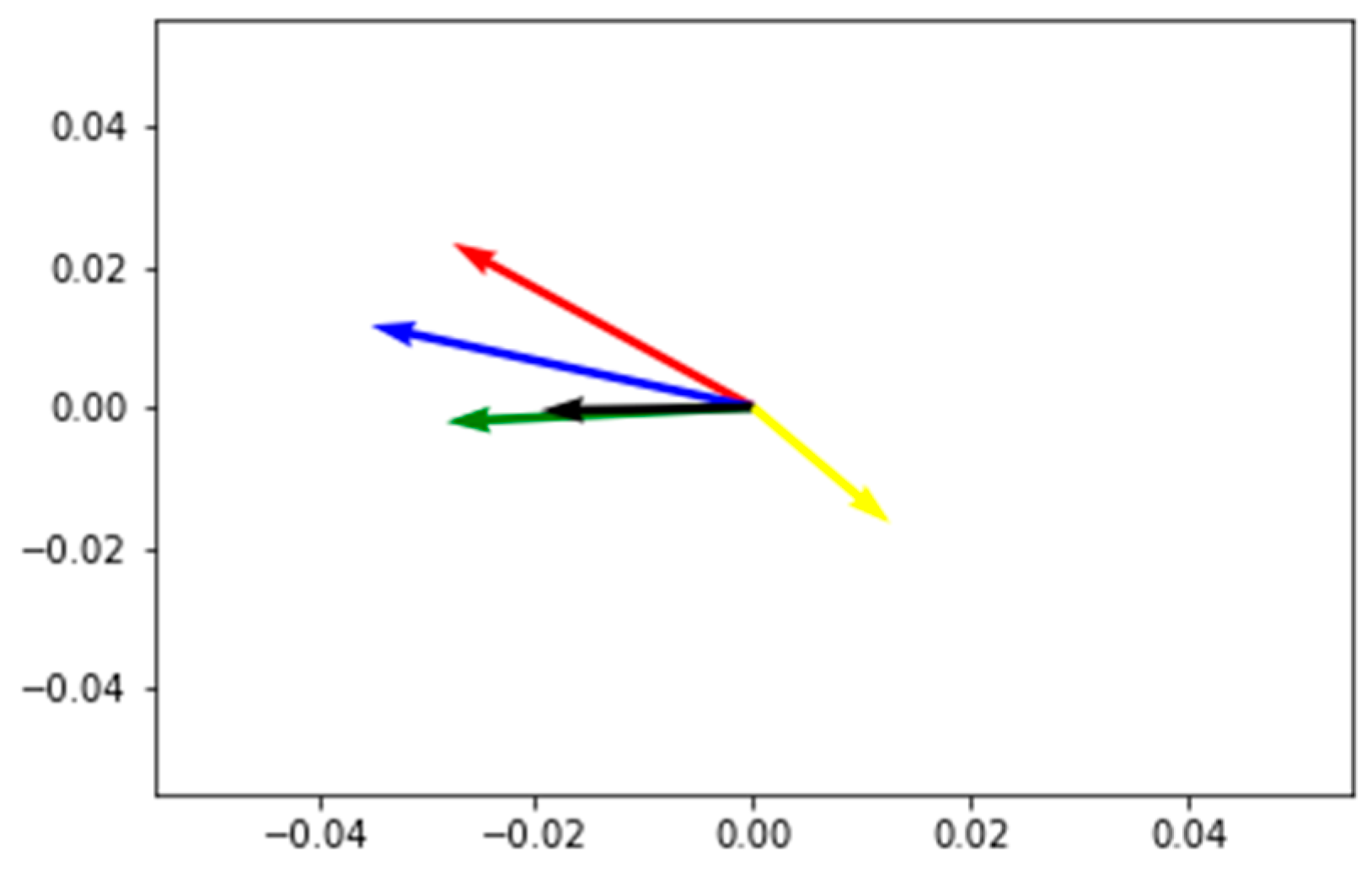
2.3. The Genetic Algorithm as a Direction for Machine Learning
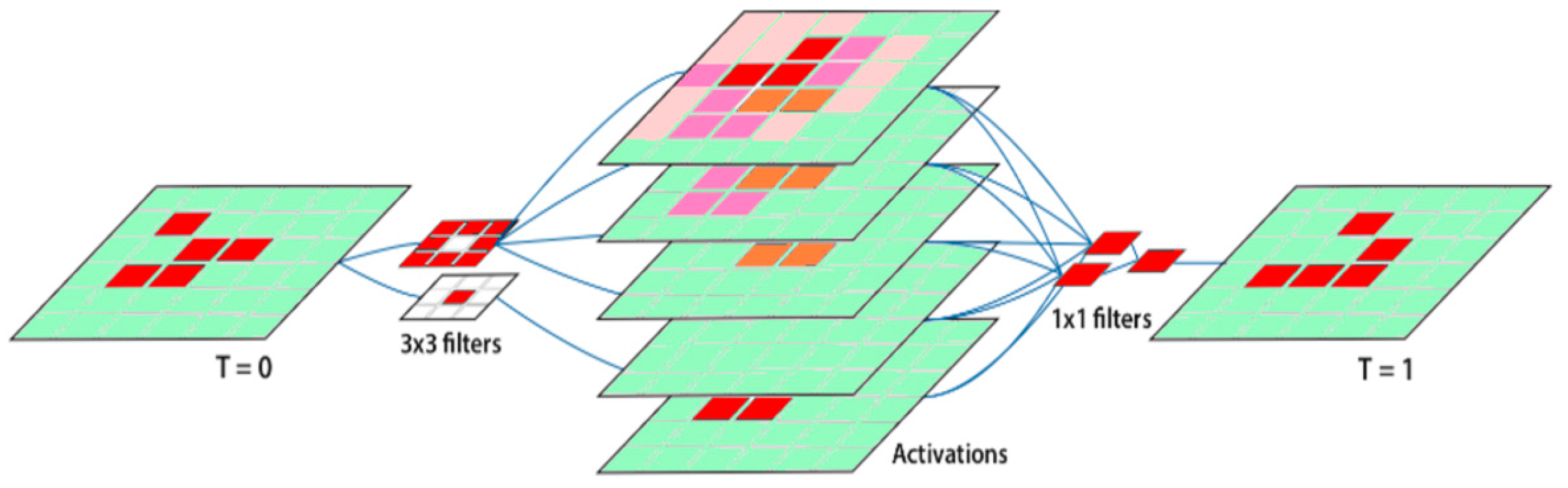
2.4. The Cellular Automaton as the Neuron of Genetic Algorithms
2.5. Implementing GAs on Blockchains
3. Use Cases and Future Applications
3.1. The Integrity and Validity of Information
3.2. Programs Stored on Chain and Composed Within Transactions—Pay Per Use
3.3. Trained AI Frameworks that can be Parsed Via Pay on Demand
3.4. Artificial Intelligence Agents Trained Via Submitted Blockchain Data and Operated on Chain.
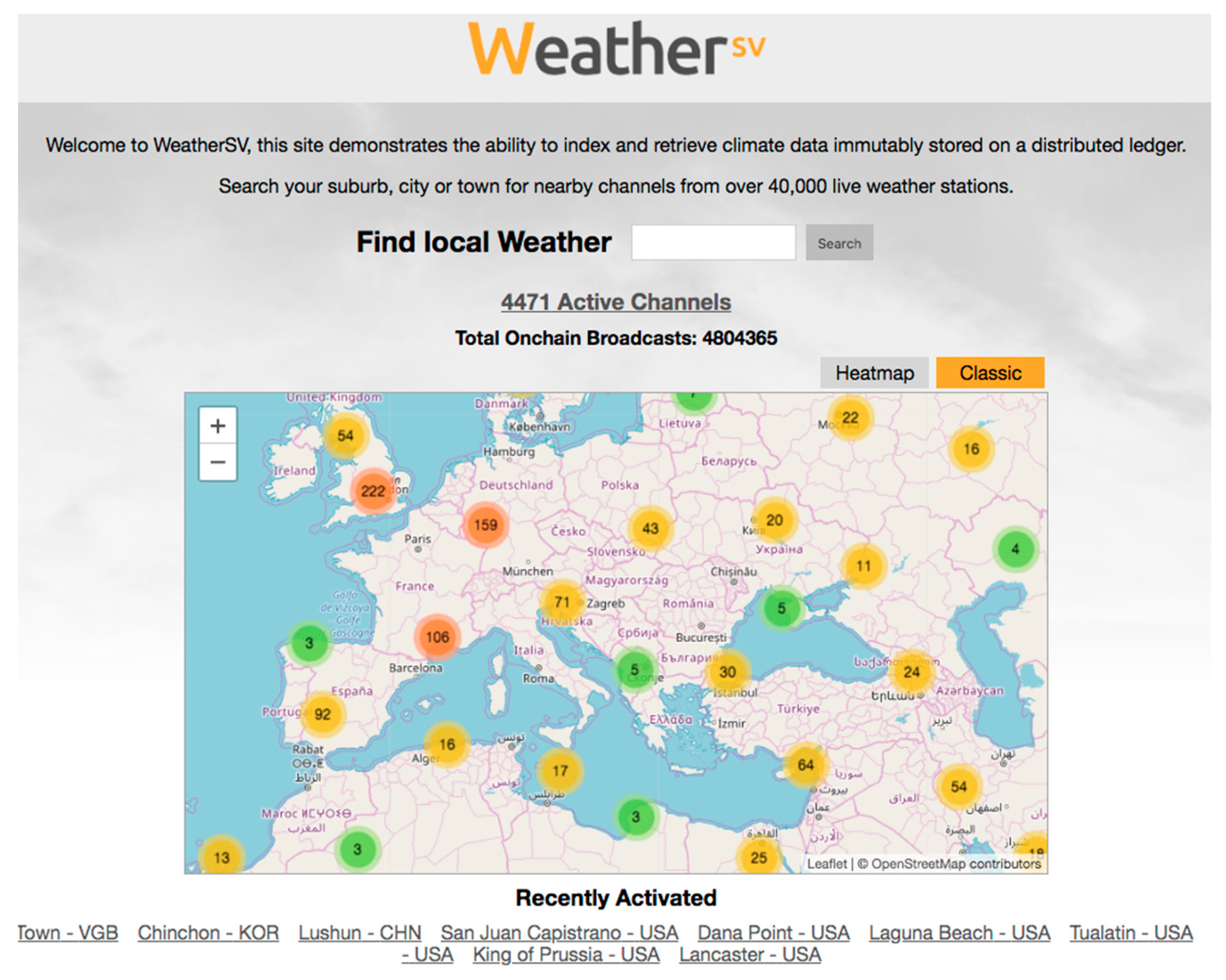
3.5. Proof of Work Via dSHA256 as a Source of Randomness and Monte Carlo Method Via ASICs
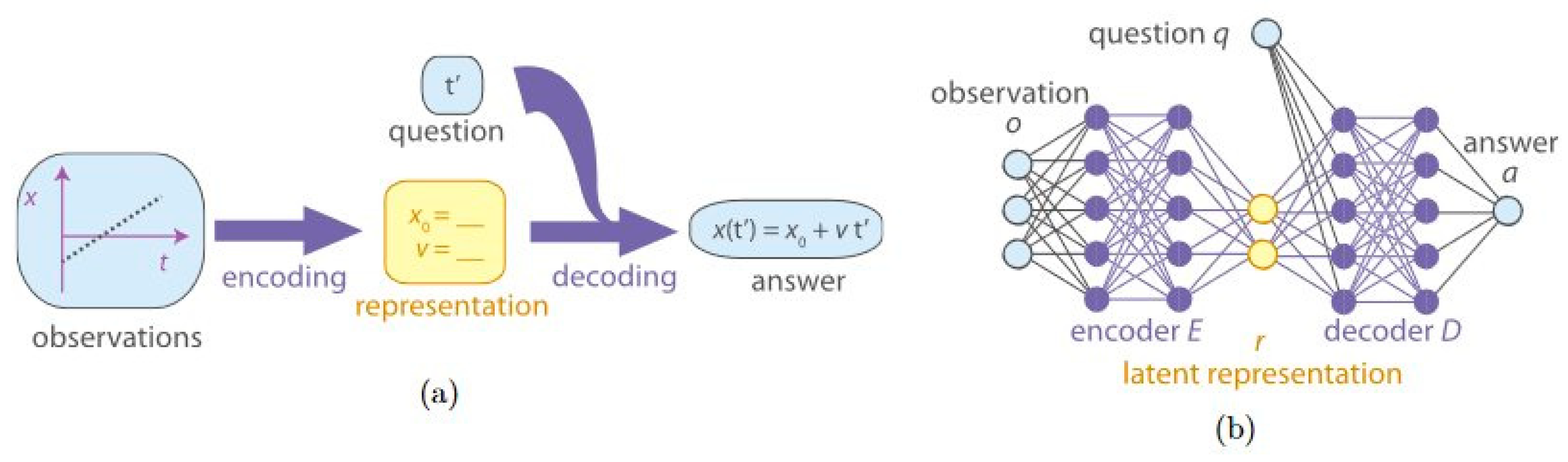
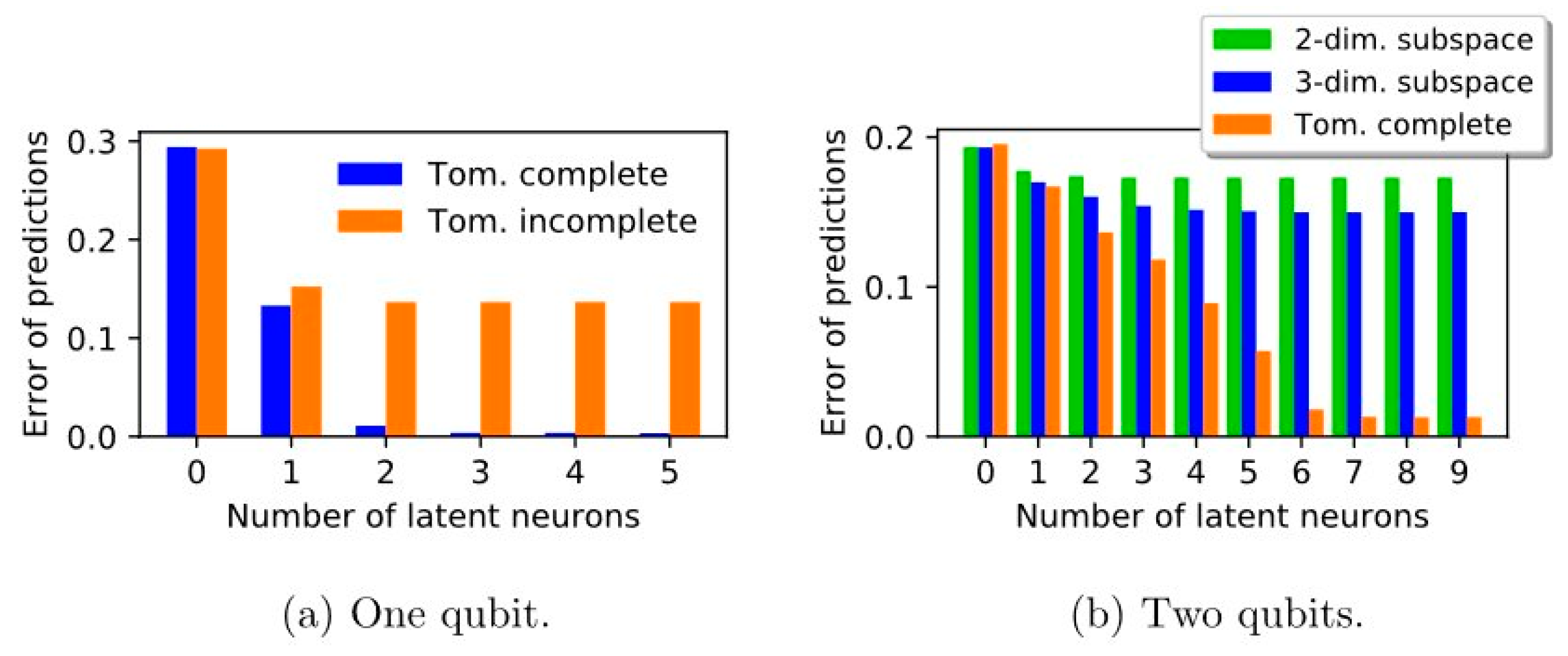
3.6. Solving Physical Problems via CNNs and Simulation of Quantum Computing
4. Discussion
5. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- The Archimedes Palimpsest; University of Pennsylvania Libraries: Philadelphia, PA, USA; Available online: http://archimedespalimpsest.net/ (accessed on 1 June 2016).
- Cultural Tragedy: Massive Inferno Engulfs 200-Year-Old Museum in Brazil. Available online: https://www.cbsnews.com/news/fire-national-museum-brazil-rio-de-janeiro-today-2018-09-02/ (accessed on 6 March 2019).
- Wright, C. (Pseudonym: Nakamoto, S). Bitcoin: A Peer-to-Peer Electronic Cash System; Whitepaper: Sydney, Australia, October 2008. [Google Scholar]
- Sgantzos, K. Implementing a Church-Turing-Deutsch Principle Machine on a Blockchain. In Proceedings of the 12th Hellenic Society for Computational Biology and Bioinformatics Conference, Athens, Greece, 11–13 October 2017; Available online: https://sites.google.com/site/hscbb17/program/HSCBB17-Booklet.pdf (accessed on 26 May 2019).
- Meiklejohn, S.; Pomarole, M.; Jordan, G.; Levchenko, K.; McCoy, D.; Voelker, G.M.; Savage, S. A fistful of bitcoins: Characterizing payments among men with no names. In Proceedings of the 2013 Conference on Internet Measurement Conference, Barcelona, Spain, 23–25 October 2013. [Google Scholar]
- Merkle, R.C. A Digital Signature based on a Conventional Encryption Function. In Advances in Cryptology—CRYPTO ’87, Santa Barbara, California, August 21-25, 1988, Lecture Notes in Computer Science; Springer: Berlin, Germany, 1988; Volume 293, pp. 369–378. [Google Scholar]
- Khalilov, M.C.K.; Levi, A. A Survey on Anonymity and Privacy in Bitcoin-like Digital Cash Systems. IEEE Commun. Surv. Tutor. 2017, 20, 2543–2585. [Google Scholar] [CrossRef]
- Opcode List in BitcoinSV (v. 0.2). ©2009 S. Nakamoto, ©2009–2016 The Bitcoin Core developers, ©2018-19 Bitcoin Association. Distributed under the Open BSV Software License. Available online: https://github.com/bitcoin-sv/bitcoin-sv/blob/master/src/script/script.h (accessed on 12 June 2019).
- Aisopos, K.; Kakarountas, A.P.; Michail, H.; Goutis, C.E. High throughput implementation of the new Secure Hash Algorithm through partial unrolling. In Proceedings of the IEEE 2005 International Workshop on Signal Processing Systems (SiPS’05), Athens, Greece, 2–4 November 2005; pp. 99–103. [Google Scholar]
- Wang, H. A Variant to Turing’s Theory of Computing Machines. JACM 1957, 4, 63–92. [Google Scholar] [CrossRef]
- Alberts, B.; Johnson, A.; Lewis, J.; Raff, M.; Roberts, K.; Walter, P. Molecular Biology of the Cell, 5th ed.; Garland Science: New York, NY, USA, 2007; pp. 264–328. [Google Scholar]
- What is DNA Replication? Available online: https://www.yourgenome.org/facts/what-is-dna-replication (accessed on 24 February 2017).
- Genetic Algorithms, Mathworks. 2017. Available online: https://www.mathworks.com/matlabcentral/fileexchange/11565-genetic-algorithms-application (accessed on 25 May 2019).
- von Neumann, J. The General and Logical Theory of Automata. In Cerebral Mechanisms in Behavior—The Hixon Symposium; Jeffress, L.A., Ed.; John Wiley & Sons: New York, NY, USA, 1951; pp. 1–31. [Google Scholar]
- Gardner, M. Mathematical Games: The fantastic combinations of John Conway’s new solitaire game of life. Sci. Am. 1970, 223, 120–123. [Google Scholar] [CrossRef]
- Wolfram, S. Statistical Mechanics of Cellular Automata. Rev. Mod. Phys. 1983, 55, 601–644. [Google Scholar] [CrossRef]
- Wolfram, S. A New Kind of Science; Wolfram Media Inc.: Champaign, IL, USA, 2002. [Google Scholar]
- William, G. Cellular automata as convolutional neural networks. Department of Applied Physics, Stanford University. arXiv 2018, arXiv:1809.02942. [Google Scholar]
- Michael, O.R. Turing, Church, Gödel, Computability, Complexity and Randomization: A Personal View. Available online: http://www.bu.edu/cphs/files/2013/08/Rabin.pdf (accessed on 26 May 2019).
- Nielsen, M. Interesting Problems: The Church–Turing–Deutsch Principle. Available online: http://michaelnielsen.org/blog/interesting-problems-the-church-turing-deutsch-principle/ (accessed on 31 May 2019).
- Deutsch, D. Quantum theory, the Church—Turing principle and the universal quantum computer. In Proceedings of the Royal Society, London, UK, July 1984. [Google Scholar]
- LeCun, Y.; Bengio, Y.; Hinton, G. Quantum Deep Learning Triuniverse. Nature 2015, 521, 436. Available online: https://www.scirp.org/reference/ReferencesPapers.aspx?ReferenceID=1899138 (accessed on 3 June 2019). [CrossRef] [PubMed]
- Chepurnoy, A.; Kharin, V.; Meshkov, D. Self-Reproducing Coins as Universal Turing Machine. 2018. Available online: https://arxiv.org/pdf/1806.10116.pdf (accessed on 6 June 2019).
- Justin, D.; Harris, B.W. Decentralized & Collaborative AI on Blockchain. In Proceedings of the 2019 IEEE International Conference on Blockchain (Blockchain), Atlanta, GA, USA, 14–17 July 2019. [Google Scholar]
- Donath, J. Why Fake News Stories Thrive Online. 2016. Available online: https://edition.cnn.com/2016/11/20/opinions/fake-news-stories-thrive-donath/ (accessed on 10 June 2019).
- Gerck, E. The Einstein Phenomenon and Fake News. 2019. Available online: https://www.researchgate.net/publication/331561385_The_Einstein_Phenomenon_and_fake_news (accessed on 10 June 2019).
- Tencent Keen Security Lab. Experimental Security Research of Tesla Autopilot. 2019. Available online: https://keenlab.tencent.com/en/whitepapers/Experimental_Security_Research_of_Tesla_Autopilot.pdf (accessed on 09 June 2019).
- Haber, S.; Stornetta, W.S. How to time-stamp a digital document. J. Cryptol. 1991, 3. [Google Scholar] [CrossRef]
- Grigg, I. Triple Entry Accounting. 2004. Available online: https://iang.org/papers/triple_entry.html (accessed on 26 June 2019).
- Grigg, I. PKI Considered Harmful. 2008. Available online: https://iang.org/ssl/pki_considered_harmful.html (accessed on 26 June 2019).
- Grigg, I. An Open Audit of an Open Certification Authority. Large Installation Systems Administration (LISA). 2008. Available online: https://iang.org/papers/open_audit_lisa.html (accessed on 26 June 2019).
- Media, B. Add any File to the BSV Blockchain. 2019. Available online: https://add.bico.media/ (accessed on 10 June 2019).
- Github.inc. The World’s Leading Software Development Platform. 2019. Available online: https://github.com/ (accessed on 10 June 2019).
- Agora Startup Page for Bitcoin SV Applications & Services. Available online: https://www.agora.icu/ (accessed on 12 June 2019).
- Grigg, I.; Petro, C.C. Using Electronic Markets to Achieve Efficient Task Distribution. In Proceedings of the Financial Cryptography First International Conference FC’97, Anguilla, British West Indies, 24–28 February 1997; Springer-Verlag: Germany 1997 LNCS1318. Available online: https://iang.org/papers/task_market.html (accessed on 10 June 2019).
- Money Button Is an API and a UI/UX Layer for the Bitcoin SV Blockchain. Available online: https://docs.moneybutton.com/ (accessed on 7 June 2019).
- Brownlee, J. A Gentle Introduction to Scikit-Learn: A Python Machine Learning Library. 2014. Available online: https://machinelearningmastery.com/a-gentle-introduction-to-scikit-learn-a-python-machine-learning-library/ (accessed on 26 June 2019).
- Hamel, L. Deep Learning Finds Fake News with 97% Accuracy. 2019. Available online: https://opendatascience.com/deep-learning-finds-fake-news-with-97-accuracy/ (accessed on 10 June 2019).
- Weiss, G. Multiagent Systems, 2nd ed.; The MIT Press: Cambridge, MA, USA, 2013. [Google Scholar]
- Stuart, J.R.; Norvig, P. Artificial Intelligence: A Modern Approach, 2nd ed.; Prentice Hall: Upper Saddle River, NJ, USA, 2003; Chapter 2; ISBN 0-13-790395-2. [Google Scholar]
- WeatherSV, Index and Retrieve Climate Data Immutably Stored on a Distributed Ledger. 2019. Available online: https://weathersv.app/find (accessed on 11 June 2019).
- Christodoulou, P.; Christodoulou, K.; Andreou, A. A decentralized application for logistics: Using blockchain in real-world applications. Cyprus Rev. 2018, 30, 171–183. [Google Scholar]
- McLaren, D.; Agyeman, J. Sharing Cities: A Case for Truly Smart and Sustainable Cities; MIT Press: Cambridge, MA, USA, 2015. [Google Scholar]
- Zweispace Starts to Record Tokyo Earthquake Detector Data into the Bitcoin SV (BSV) Blockchain. Available online: https://coingeek.com/zweispace-starts-to-record-tokyo-earthquake-detector-data-into-the-bitcoin-sv-bsv-blockchain/ (accessed on 14 June 2019).
- Eastlake, D., III; Hansen, T. US Secure Hash Algorithms (SHA and SHA-Based HMAC and HKDF), RFC 6234 (Informational), Internet Engineering Task Force. 2011. Available online: http://www.ietf.org/rfc/rfc6234.txt (accessed on 12 June 2019).
- Tschorsch, F.; Scheuermann, B. Bitcoin and Beyond: A Technical Survey on Decentralized Digital Currencies. IEEE Commun. Surv. Tutor. 2016, 18, 2084–2123. [Google Scholar] [CrossRef]
- George, P. Bitness: Bitcoin Usage in an Enterprise Environment, Opportunities and Challenges. Master’s Thesis, University of Greenwich, London, UK, 2013. [Google Scholar]
- Hashrate Comparing data. Available online: https://blockchair.com/compare (accessed on 14 June 2019).
- Kroese, D.P.; Brereton, T.; Taimre, T.; Botev, Z.I. Why the Monte Carlo method is so important today. WIREs Comput. Stat. 2014, 6, 386–392. [Google Scholar] [CrossRef]
- Mathieu, M.; Couprie, C.; LeCun, Y. Deep multi-scale video prediction beyond mean square error. arXiv 2016, preprint. arXiv:1511.05440. [Google Scholar]
- Iten, R.; Metger, T.; Wilming, H.; del Rio, L.; Renner, R. Discovering Physical Concepts with Neural Networks; Institute for Theoretical Physics: ETH Zurich, Zurich, Switzerland, 2018. [Google Scholar]
- Kurzweil, R. Don’t Fear Artificial Intelligence. 2014. Available online: http://time.com/3641921/dont-fear-artificial-intelligence/ (accessed on 14 June 2019).
- Watson, AI for Business, 2016–2019, ©IBM. Available online: https://www.ibm.com/watson/ (accessed on 14 June 2019).
- Gödel, K. Über formal unentscheidbare Sätze der Principia Mathematica und verwandter Systeme I. Monatshefte Math. Phys. 1931, 38, 173–198. [Google Scholar] [CrossRef]
- Asimov Isaac. The Last Question”, Science Fiction Quarterly. 1956. Available online: https://www.multivax.com/last_question.html (accessed on 14 June 2019).
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Sgantzos, K.; Grigg, I. Artificial Intelligence Implementations on the Blockchain. Use Cases and Future Applications. Future Internet 2019, 11, 170. https://doi.org/10.3390/fi11080170
Sgantzos K, Grigg I. Artificial Intelligence Implementations on the Blockchain. Use Cases and Future Applications. Future Internet. 2019; 11(8):170. https://doi.org/10.3390/fi11080170
Chicago/Turabian StyleSgantzos, Konstantinos, and Ian Grigg. 2019. "Artificial Intelligence Implementations on the Blockchain. Use Cases and Future Applications" Future Internet 11, no. 8: 170. https://doi.org/10.3390/fi11080170
APA StyleSgantzos, K., & Grigg, I. (2019). Artificial Intelligence Implementations on the Blockchain. Use Cases and Future Applications. Future Internet, 11(8), 170. https://doi.org/10.3390/fi11080170





