Distributed Uniform Streaming Framework: An Elastic Fog Computing Platform for Event Stream Processing and Platform Transparency †
Abstract
1. Introduction
2. Related Work
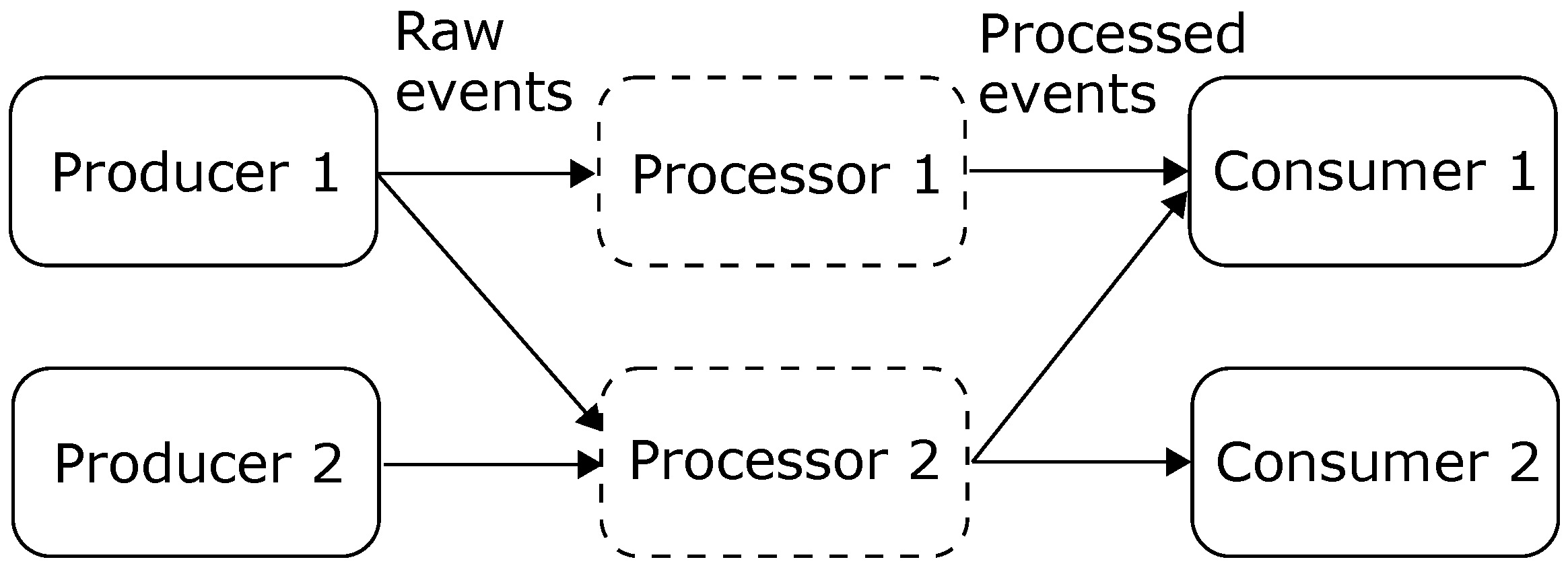
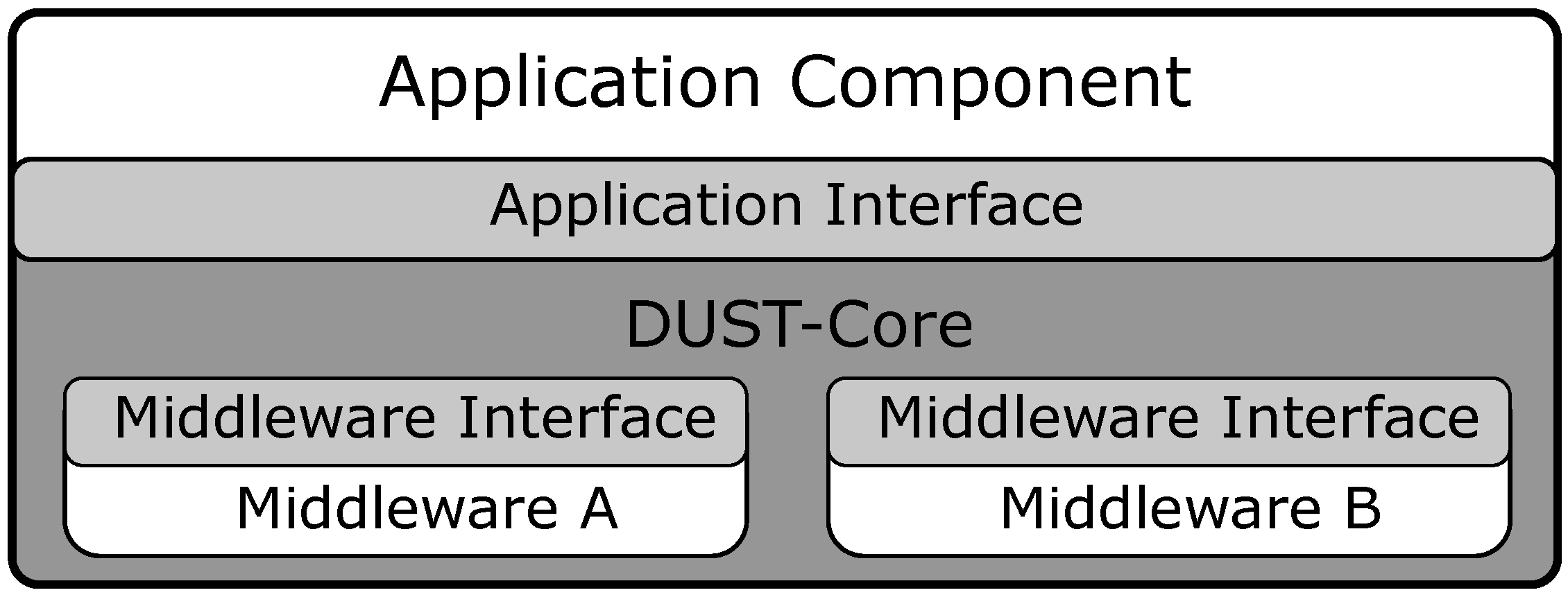
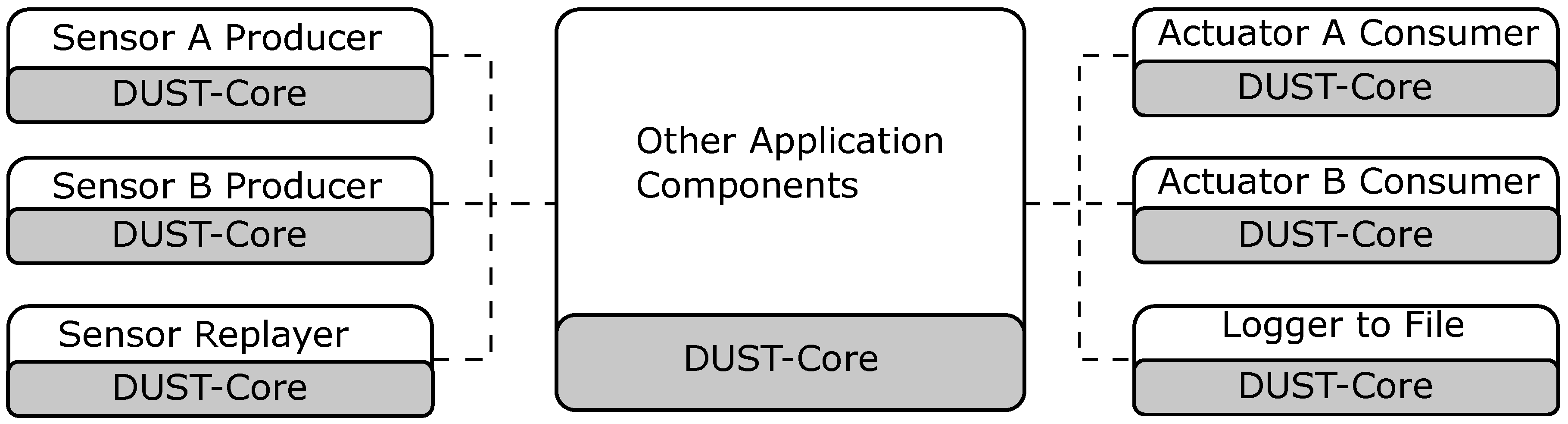
3. DUST Core for Event Streaming
3.1. Application Interface
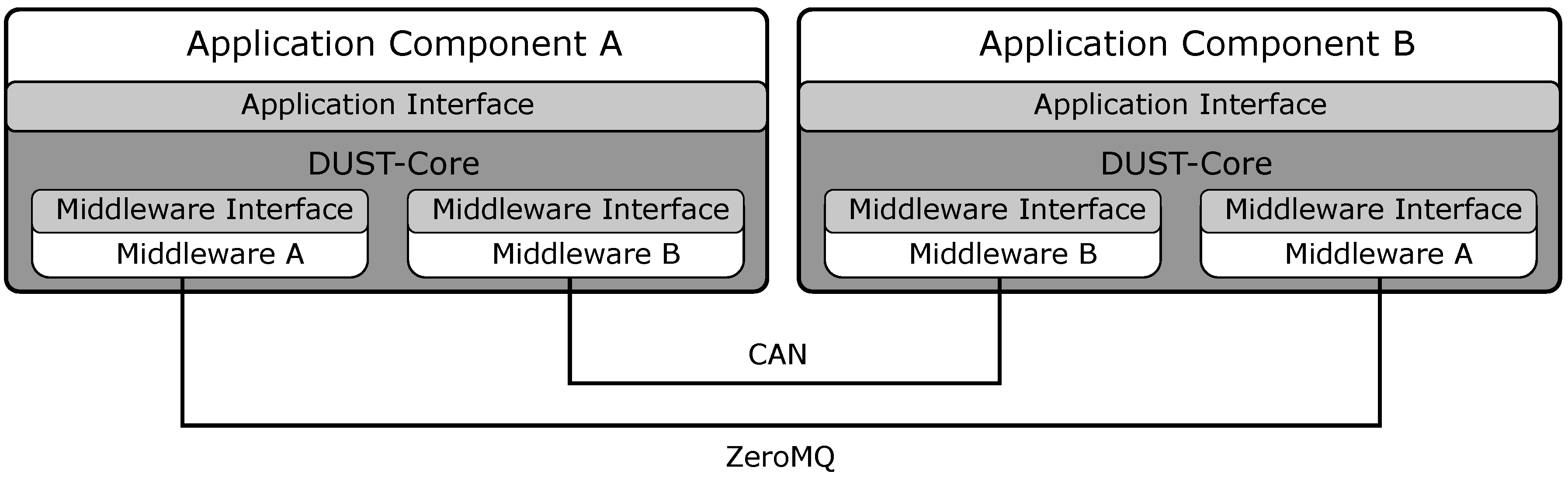
3.2. Middleware
3.3. Core Functionality
4. DUST Coordinator for Distributed Resource Optimization
4.1. DUST Coordinator System Architecture
4.2. Contract Net Protocol for Application Component Distribution
- Organizer auction In the first phase, every coordinator that detects that an application component can be moved to another device (only processing components are allowed to move) will make a random offer to become the next organizer. The coordinator that can make the highest offer will be the organizer for the next phase. Every offer of the coordinator is a random value to ensure that every coordinator has the same chance to become the next organizer. The offer is sent to every coordinator which will compare the offer with other values it received. Once a coordinator receives an offer that is higher than every previous offer, the coordinator will response with a vote.
- Organizer announcement The coordinator that received a vote from all the coordinators will become the organizer for the next phase. Once a coordinator receives a vote from every coordinator, it means that every coordinator received the offer and has determined that this offer is the highest. The organizer will respond with an announcement message and will initialize the next phase. In case that no coordinator has received a vote from every coordinator, it means that messages where lost during the auction and the auction will be reset after a certain timeout and the coordinators will restart from the first phase.
- Task announcement In this phase, the organizer will organize a new auction to determine the execution location of an application component that is running on its device. The organizer will do this by sending a task announcement message to every coordinator which contains the application component requirements. The application component requirements are defined by the application components.
- Task bidding In the task bidding phase, every coordinator will create an offer of the application components based on its requirements and based on the requirements of the application component that are running on the device of the coordinator. This offer is created with a cost function (see Section 4.3) that represents how the coordinator evaluates the capabilities of the device.
- Task awarding The organizer will receive an offer from every coordinator and will determine the device which generates the highest offer based on the cost function. In this state of the algorithm, a new configuration will be sent to all the coordinators to update the middleware settings to support the new execution location and start the application component on the new execution location.
- Organizer release Once the organizer finishes the auctions for the application components, it will release the organizer state by sending an organizer release message to every coordinator. This will trigger the first phase in every coordinator and the process repeats.
4.3. Cost-Function
5. Experiments
- The CPU usage
- The network usage
- The number of received messages
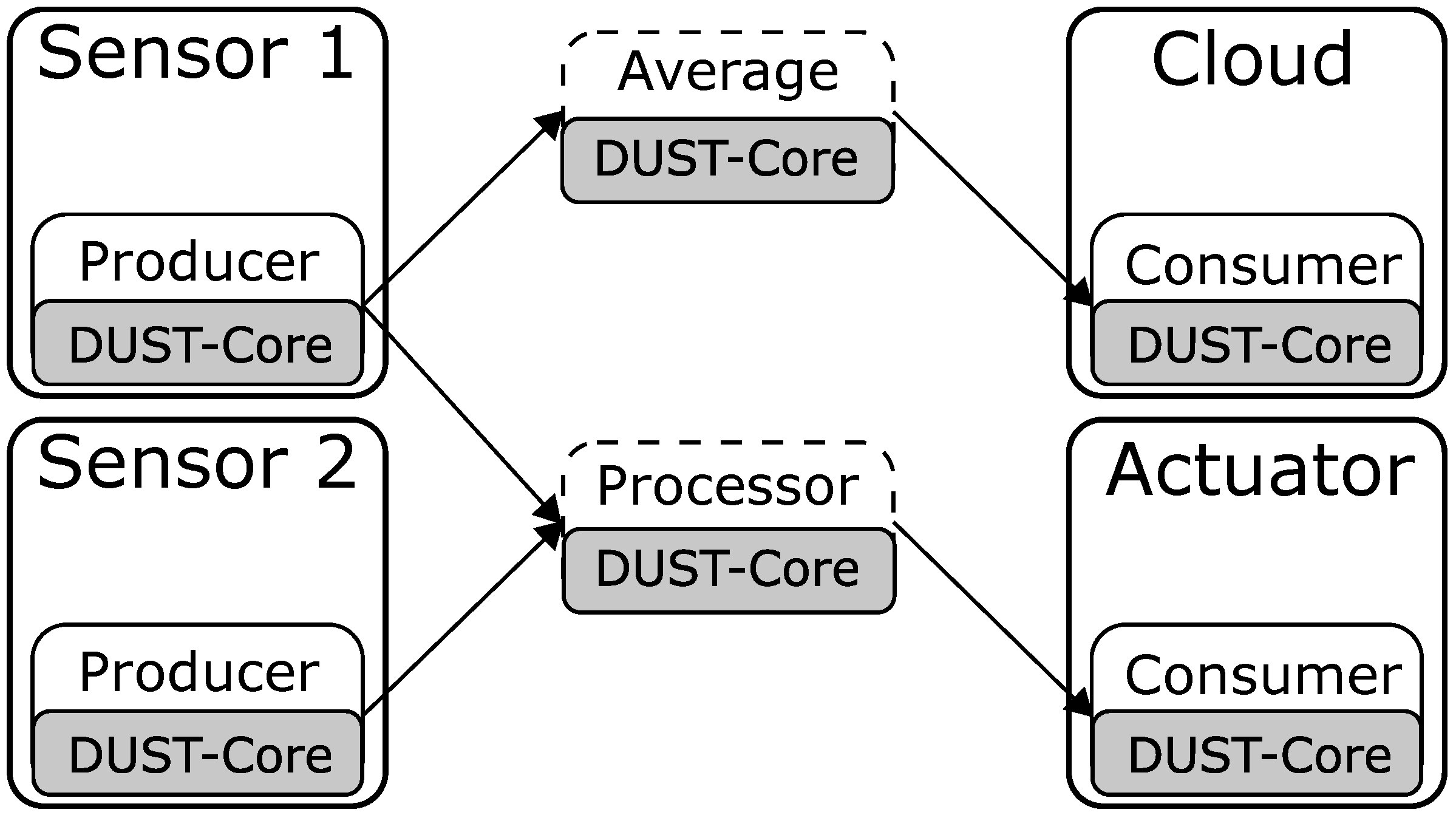
5.1. Use Case 1: Sensor to Cloud Streaming
5.2. Use Case 2: Fog Computing
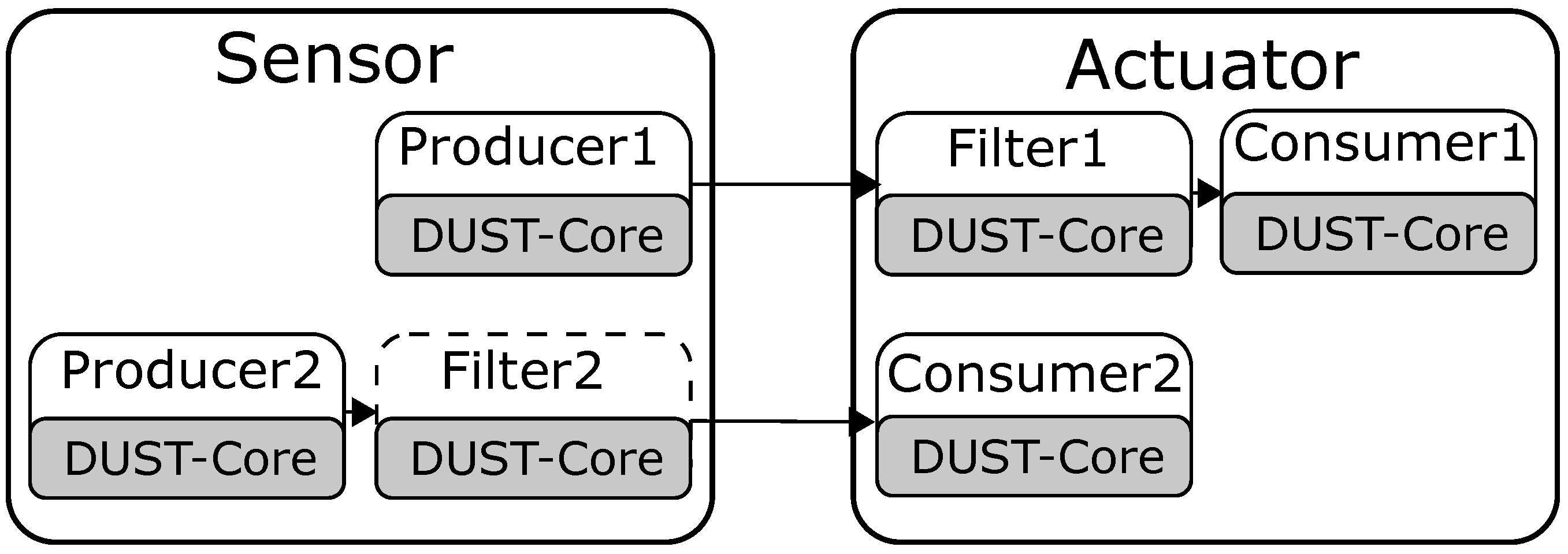
5.3. Use Case 3: Global Optimisations
6. Platform Transparency Using Dust: A Connected Driving Use Case
6.1. Application Component Architecture for Hardware Transparency
6.2. Middleware Transparency
6.3. Platform Transparency
7. Conclusions
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| CAN | Controller Area Network |
| CNET | Contract Net Protocol |
| DUST | Distributed Uniform Streaming |
| IoT | Internet of Things |
| KPI | Key Performance Indicator |
| OBU | Onboard Unit |
| OEM | original equipment manufacturer |
| V2X | Vehicle-to-everything |
| QoS | Quality of Service |
References
- Atzori, L.; Iera, A.; Morabito, G. The internet of things: A survey. Comput. Netw. 2010, 54, 2787–2805. [Google Scholar] [CrossRef]
- Gubbi, J.; Buyya, R.; Marusic, S.; Palaniswami, M. Internet of Things (IoT): A vision, architectural elements, and future directions. Future Gener. Comput. Syst. 2013, 29, 1645–1660. [Google Scholar] [CrossRef]
- Armbrust, M.; Fox, A.; Griffith, R.; Joseph, A.D.; Katz, R.; Konwinski, A.; Lee, G.; Patterson, D.A.; Rabkin, A.; Stoica, I.; et al. A view of cloud computing. Commun. ACM 2010, 53, 50–58. [Google Scholar] [CrossRef]
- Moxey, C.; Edwards, M.; Etzion, O.; Ibrahim, M.; Iyer, S.; Lalanne, H.; Monze, M.; Peters, M.; Rabinovich, Y.; Sharon, G.; et al. A Conceptual Model for Event Processing Systems. IBM Redguide Publication. 2010. Available online: http://www.redbooks.ibm.com/redpapers/pdfs/redp4642.pdf (accessed on 17 July 2018).
- Vanneste, S.; de Hoog, J.; Huybrechts, T.; Bosmans, S.; Sharif, M.; Mercelis, S.; Hellinckx, P. Distributed Uniform Streaming Framework: Towards an Elastic Fog Computing Platform for Event Stream Processing. In Advances on P2P, Parallel, Grid, Cloud and Internet Computing, 3PGCIC 2018; Xhafa, F., Leu, F.Y., Ficco, M., Yang, C.T., Eds.; Lecture Notes on Data Engineering and Communications Technologies; Springer: Cham, Switzerland, 2019; Volume 24. [Google Scholar]
- Habak, K.; Ammar, M.; Harras, K.A.; Zegura, E. Femto clouds: Leveraging mobile devices to provide cloud service at the edge. In Proceedings of the 2015 IEEE 8th International Conference on Cloud Computing (CLOUD), New York, NY, USA, 27 June–2 July 2015; pp. 9–16. [Google Scholar]
- Pan, J.; McElhannon, J. Future edge cloud and edge computing for internet of things applications. IEEE Internet Things J. 2018, 5, 439–449. [Google Scholar] [CrossRef]
- Teranishi, Y.; Kimata, T.; Yamanaka, H.; Kawai, E.; Harai, H. Dynamic Data Flow Processing in Edge Computing Environments. In Proceedings of the 2017 IEEE 41st Annual Computer Software and Applications Conference (COMPSAC), Turin, Italy, 4–8 July 2017; Volume 1, pp. 935–944. [Google Scholar]
- Hummer, W.; Satzger, B.; Dustdar, S. Elastic Stream Processing in the Cloud. Wiley Interdiscip. Rev. Data Min. Knowl. Discov. 2013, 3, 333–345. [Google Scholar] [CrossRef]
- Eyckerman, R.; Sharif, M.; Mercelis, S.; Hellinckx, P. Context-Aware Distribution in Constrained IoT Environments. In Proceedings of the International Conference on P2P, Parallel, Grid, Cloud and Internet Computing, Taichung, Taiwan, 27–29 October 2018; Springer: Cham, Switzerland, 2018; pp. 437–446. [Google Scholar]
- Fed4Fire. Federation For Fire Plus. Available online: https://www.fed4fire.eu/ (accessed on 5 July 2019).
- Byers, C. Architectural Imperatives for Fog Computing: Use Cases, Requirements, and Architectural Techniques for Fog-Enabled IoT Networks. IEEE Commun. Mag. 2017, 55, 14–20. [Google Scholar] [CrossRef]
- Paho-mqtt. Eclipse Paho MQTT Python Client Library. Available online: https://pypi.org/project/paho-mqtt/ (accessed on 16 May 2019).
- ZeroMQ. ZeroMQ Distributed Messaging. Available online: http://zeromq.org (accessed on 16 May 2019).
- OpenSplice DDS. Adlink OpenSplice DDS Community Edition. Available online: http://www.prismtech.com/dds-community/software-downloads (accessed on 16 May 2019).
- Kreps, J.; Narkhede, N.; Rao, J. Kafka: A distributed messaging system for log processing. In Proceedings of the NetDB’11, Athens, Greece, 12 June 2011; pp. 1–7. [Google Scholar]
- Smith, R.G. The contract net protocol: High-level communication and control in a distributed problem solver. IEEE Trans. Comput. 1980, 12, 1104–1113. [Google Scholar] [CrossRef]
- Wooldridge, M. An Introduction to MultiAgent Systems; Wiley: Chichester, UK, 2009; ISBN 978-0470519462. [Google Scholar]
- Sharif, M.; Mercelis, S.; Hellinckx, P. Context-Aware Optimization of Distributed Resources in Internet of Things Using Key Performance Indicators. In Proceedings of the International Conference on P2P, Parallel, Grid, Cloud and Internet Computing, Barcelona, Spain, 8–10 November 2017; Springer: Cham, Switzerland, 2017; pp. 733–742. [Google Scholar]
- Marquez-Barja, J.; Lannoo, B.; Naudtsy, D.; Braem, B.; Maglogiannisy, V.; Donato, C.; Mercelis, S.; Berkvens, R.; Hellinckx, P.; Weyn, M.; et al. Smart Highway: ITS-G5 and C2VX based testbed for vehicular communications in real environments enhanced by edge/cloud technologies. In Proceedings of the 28th European Conference on Networks and Communications (EuCNC 2019), Valencia, Spain, 18–21 June 2019. [Google Scholar]


| Type | Description | |
|---|---|---|
| ID | uint64 | A field that is incremented with one to create a unique number for every message. |
| Type | uint64 | An optional field in which the application can define the type of message that is send in the payload. |
| Timestamp | uint64 + uint32 | The UTC-time of sending an event message. |
| Key | bytes | An optional field to indicate the key which can be used by the application. |
| Payload | bytes | The payload of the message. The application can define the structure of the payload. |
| Source ID | string | The unique string that defines the source application component of the message. |
| Managed by | Filter before | Filter after | CPU Usage of | Messages | Total Network |
|---|---|---|---|---|---|
| DUST | Migration | Migration | Sensor/Cloud (%) | Received | Usage (MB) |
| ✗ | Sensor | Sensor | 29.2/1.1 | 44,420 | 5.20 |
| ✗ | Cloud | Cloud | 16.3/2.0 | 44,560 | 7.44 |
| ✓ | Sensor | Sensor | 29.2/1.5 | 44,460 | 5.48 |
| ✓ | Cloud | Sensor | 29.2/1.9 | 43,940 | 5.63 |
| Managed by | Filter before | Filter after | CPU Usage of | Messages | Total Network |
|---|---|---|---|---|---|
| DUST | Migration | Migration | Sensor/Cloud (%) | Received | Usage (MB) |
| ✗ | Sensor | Sensor | 89.1 /2.6 | 192,040 | 12.81 |
| ✗ | Cloud | Cloud | 89.7 /13.2 | 409,960 | 43.87 |
| ✓ | Sensor | Cloud | 89.3 /5.3 | 326,340 | 34.28 |
| ✓ | Cloud | Cloud | 86.9 /5.8 | 380,060 | 40.90 |
| Managed by | Device | Running Components | CPU Usage | Messages | Device Network |
|---|---|---|---|---|---|
| DUST | on the Device | of Device (%) | Received | Usage (MB) | |
| ✗ | Sensor 1 | Source | 59.9 | n.a. | 33.16 |
| ✗ | Sensor 2 | Source | 19.2 | n.a. | 11.54 |
| ✗ | Actuator | Processor, Sink | 77.9 | 237,045 | 25.18 |
| ✗ | Cloud | Average, Sink | 37.8 | 88 | 20.56 |
| ✓ | Sensor 1 | Source | 61.2 | n.a. | 33.97 |
| ✓ | Sensor 2 | Source, Average, | 191.5 | n.a. | 49.90 |
| Processor | |||||
| ✓ | Actuator | Sink | 57.1 | 291,620 | 25.75 |
| ✓ | Cloud | Sink | 20.3 | 87 | 8.240 |
| Managed by | Filter1/2 Start | Filter1/2 End | CPU Usage of | Messages | Total Network |
|---|---|---|---|---|---|
| DUST | Device | Device | Sensor/Actuator (%) | Received | Usage (MB) |
| ✗ | Actuator/Sensor | Actuator/Sensor | 63.4/64.3 | 133,270 | 38.40 |
| ✗ | Sensor/Actuator | Sensor/Actuator | 81.6/46.2 | 133,130 | 32.60 |
| ✓ | Actuator/Sensor | Actuator/Sensor | 64.5/63.4 | 132,718 | 39.00 |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Vanneste, S.; de Hoog, J.; Huybrechts, T.; Bosmans, S.; Eyckerman, R.; Sharif, M.; Mercelis, S.; Hellinckx, P. Distributed Uniform Streaming Framework: An Elastic Fog Computing Platform for Event Stream Processing and Platform Transparency. Future Internet 2019, 11, 158. https://doi.org/10.3390/fi11070158
Vanneste S, de Hoog J, Huybrechts T, Bosmans S, Eyckerman R, Sharif M, Mercelis S, Hellinckx P. Distributed Uniform Streaming Framework: An Elastic Fog Computing Platform for Event Stream Processing and Platform Transparency. Future Internet. 2019; 11(7):158. https://doi.org/10.3390/fi11070158
Chicago/Turabian StyleVanneste, Simon, Jens de Hoog, Thomas Huybrechts, Stig Bosmans, Reinout Eyckerman, Muddsair Sharif, Siegfried Mercelis, and Peter Hellinckx. 2019. "Distributed Uniform Streaming Framework: An Elastic Fog Computing Platform for Event Stream Processing and Platform Transparency" Future Internet 11, no. 7: 158. https://doi.org/10.3390/fi11070158
APA StyleVanneste, S., de Hoog, J., Huybrechts, T., Bosmans, S., Eyckerman, R., Sharif, M., Mercelis, S., & Hellinckx, P. (2019). Distributed Uniform Streaming Framework: An Elastic Fog Computing Platform for Event Stream Processing and Platform Transparency. Future Internet, 11(7), 158. https://doi.org/10.3390/fi11070158






