An Image Authentication Scheme Using Merkle Tree Mechanisms
Abstract
1. Introduction
2. Background
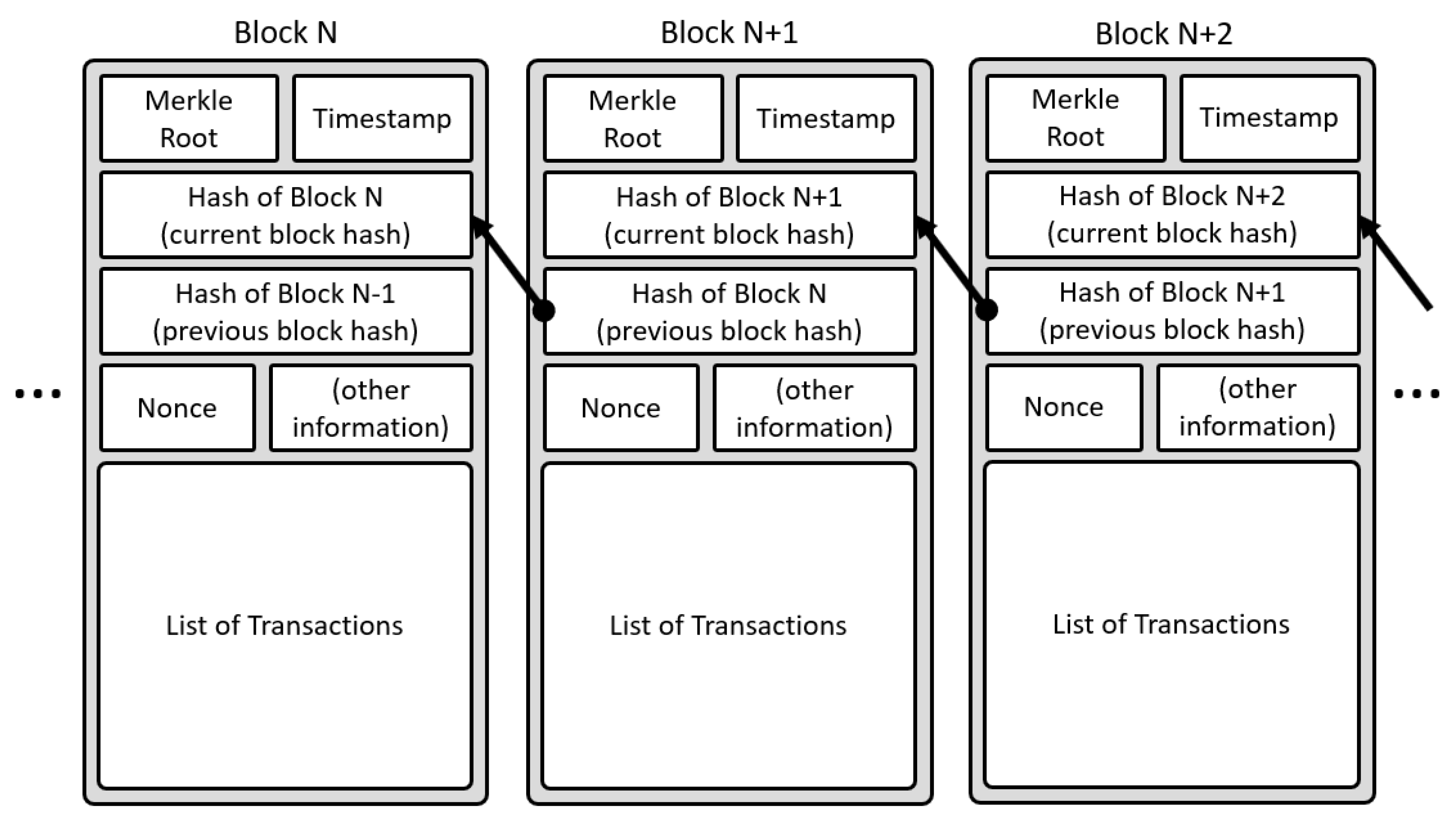
2.1. Blockchain Technology
- Decentralized: The basic structure of blockchain, the network is decentralized, meaning it has no need to rely on any server or node. The data can be recorded, stored, and updated by a group of nodes.
- Transparency: When data is transmitted on the blockchain, records on each node are open and transparent—this is the reason that blockchain can be trusted.
- Open Source: The records of blockchain systems are publicly verifiable for any user, and the user can also use the blockchain system to develop any application.
- Autonomy: Based on the consensus mechanism, each node in the blockchain can transmit or update data to each other in a secure situation. This idea is from a single entity to the entire system so that no one can interfere with it.
- Immutable: Any records will always be kept and stored and will not be altered unless the remaining nodes have a record where greater than 51% of the record will be changed.
- Anonymity: The blockchain technology solves the problem of trust on the node-to-node, so the data transmission or the transaction can be hidden, and only when the trader’s blockchain address is known will it be exposed.
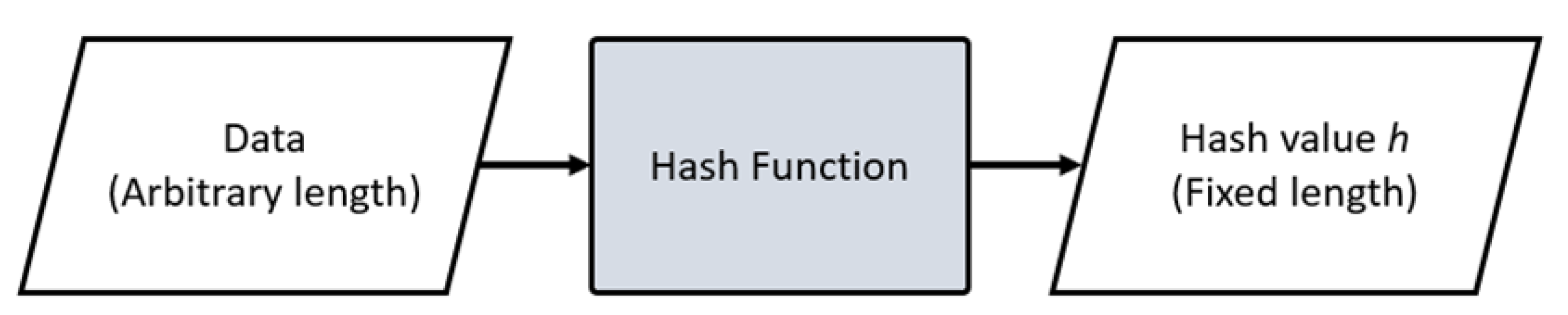
2.2. Hash Function
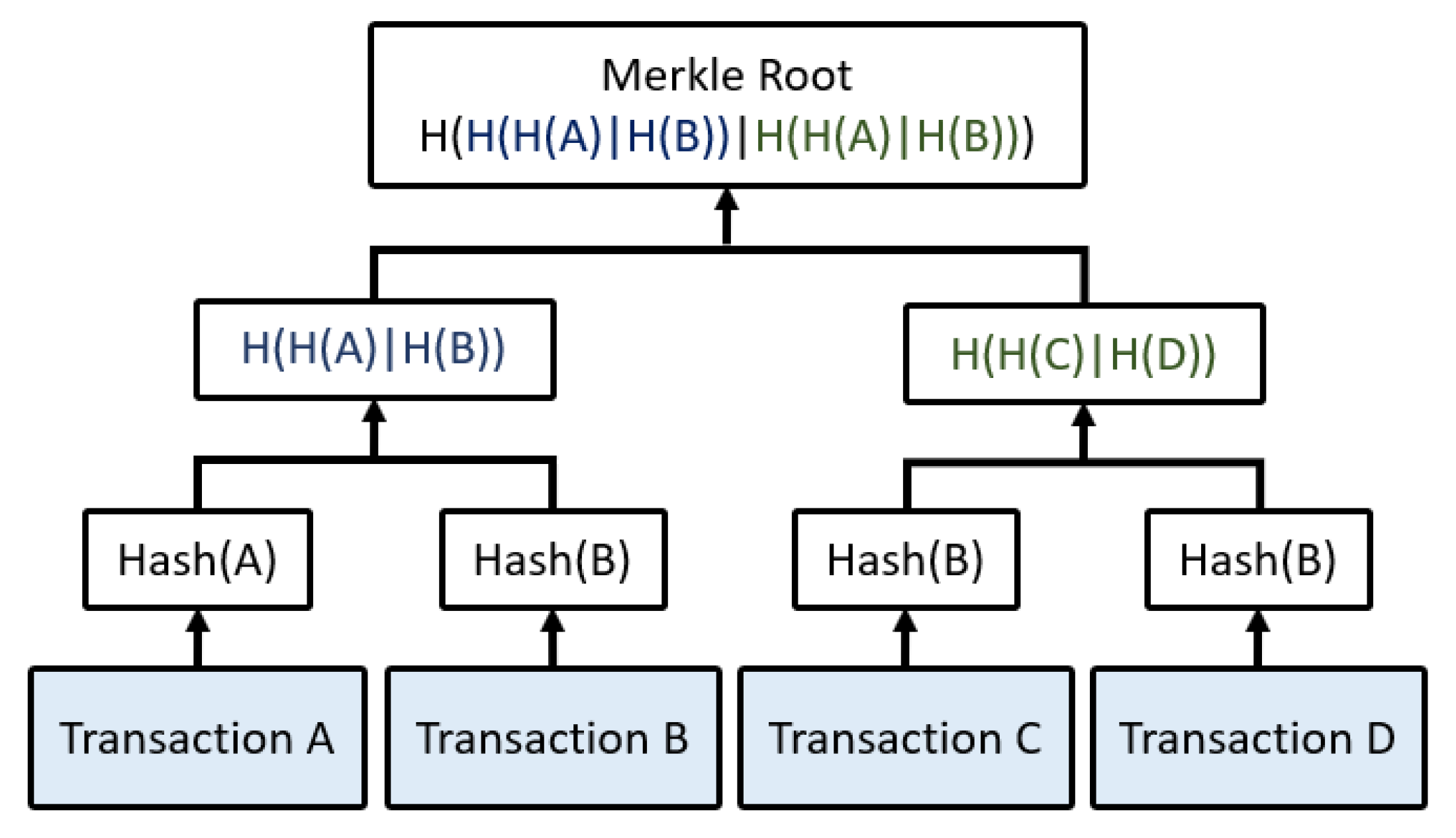
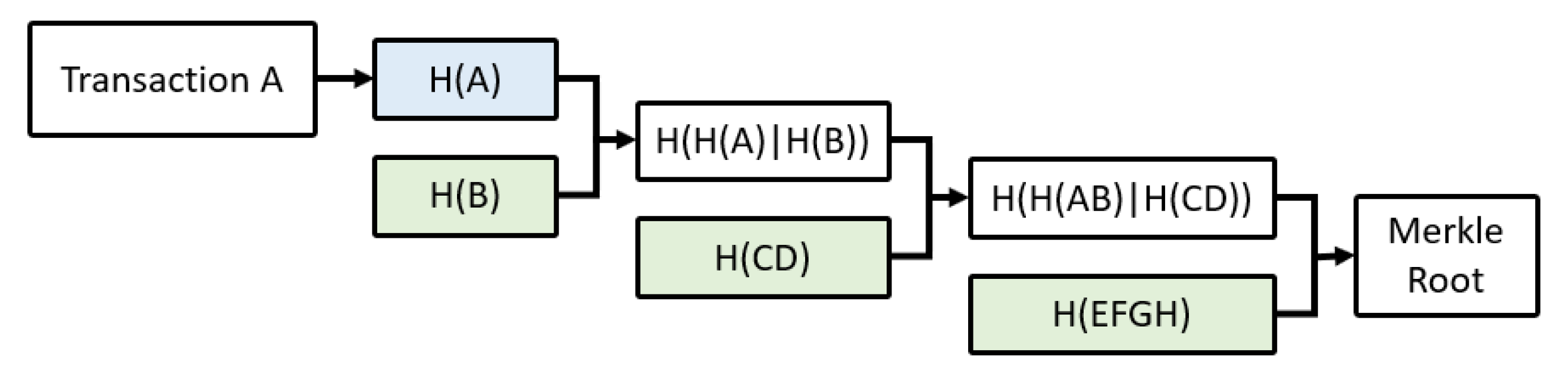
2.3. Merkle Tree
2.4. Image Authentication
2.5. Decentralized Storage: IPFS
3. Proposed Method
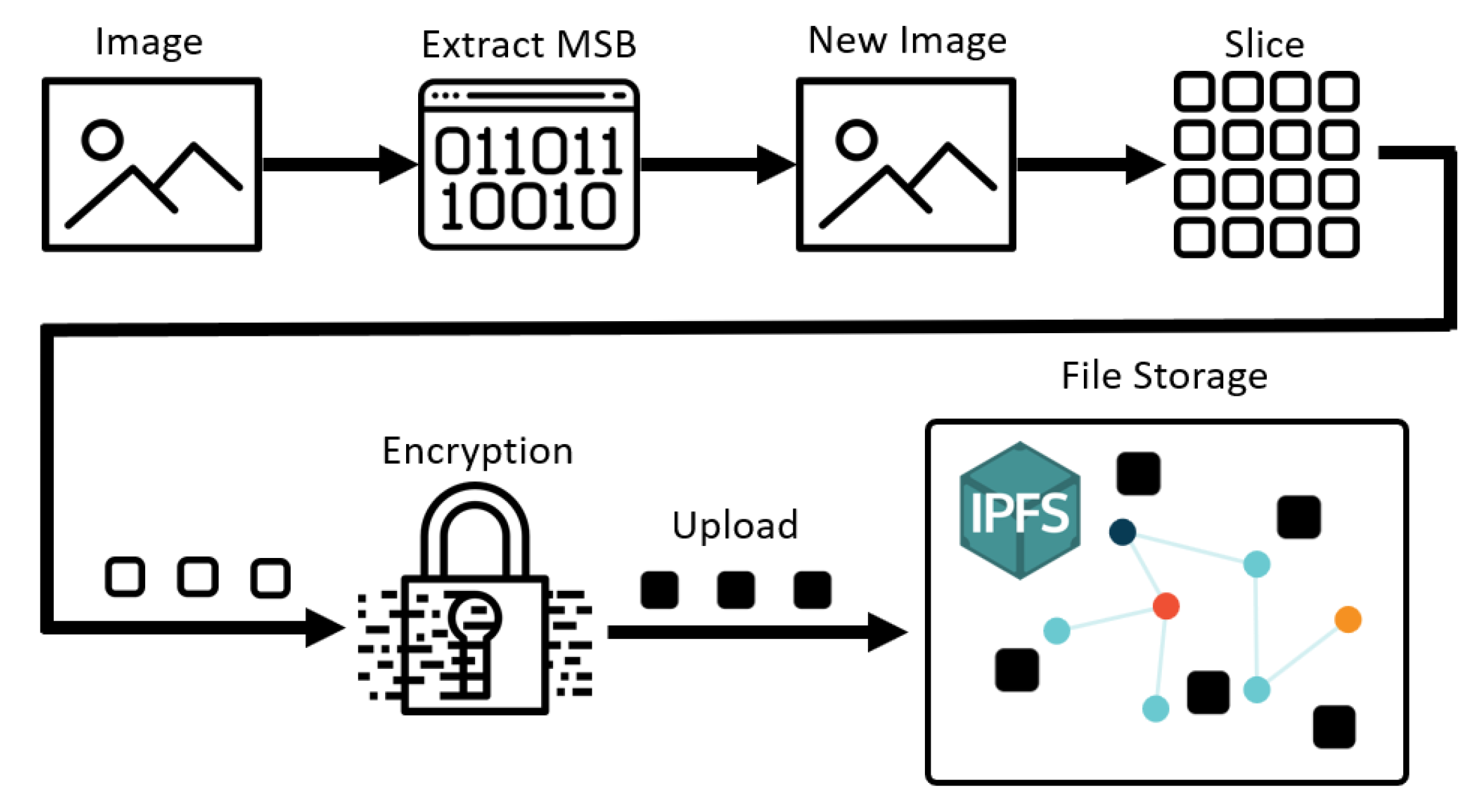
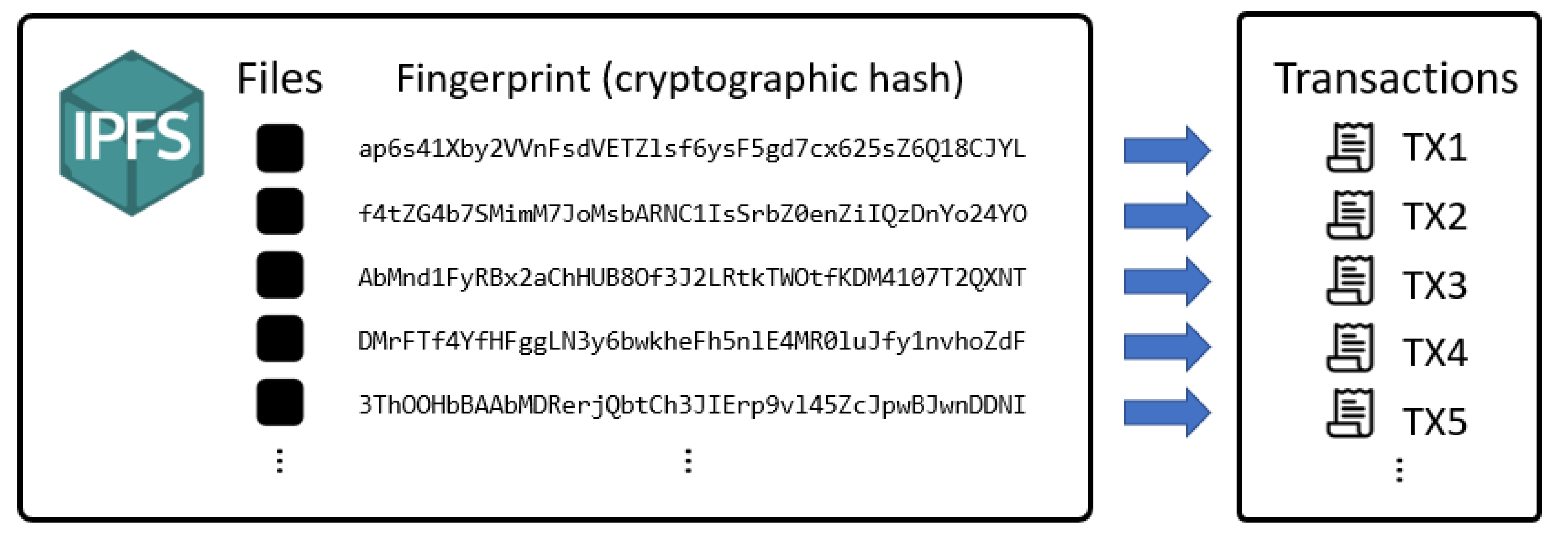
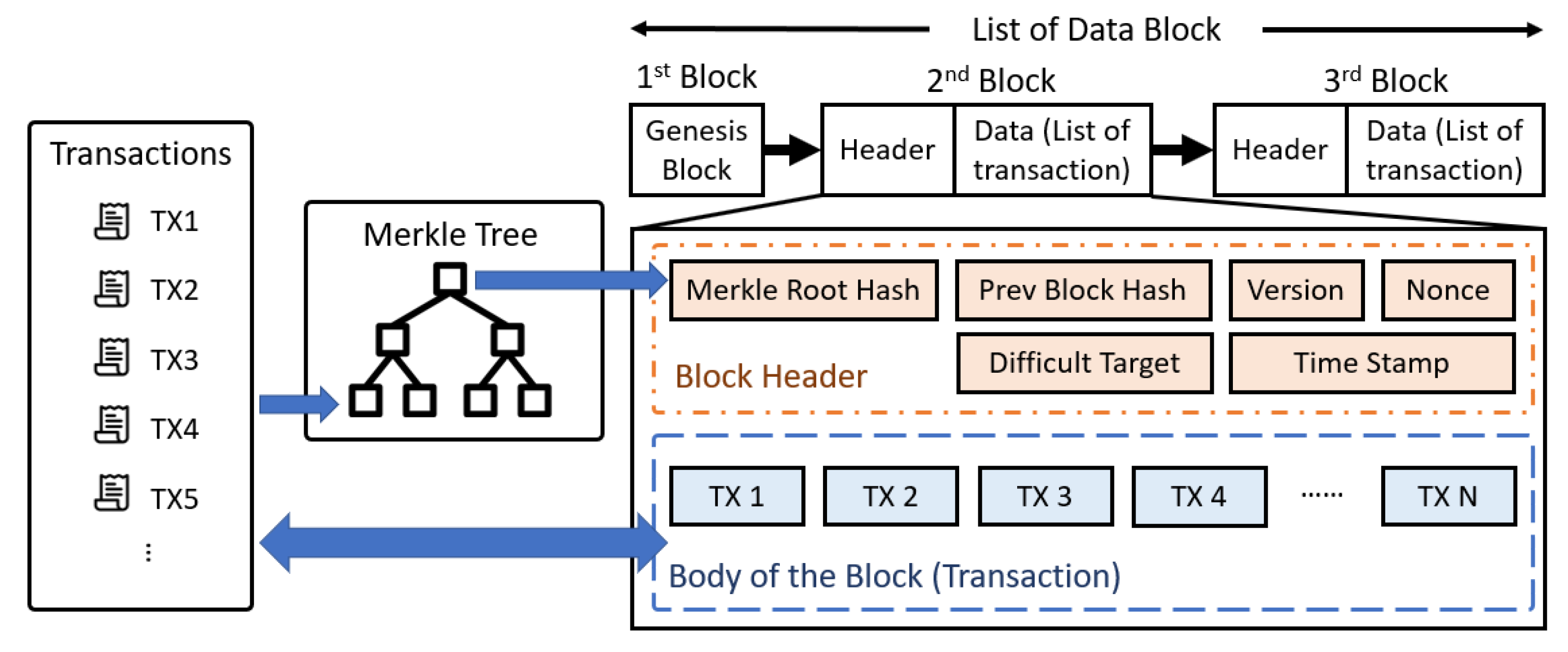
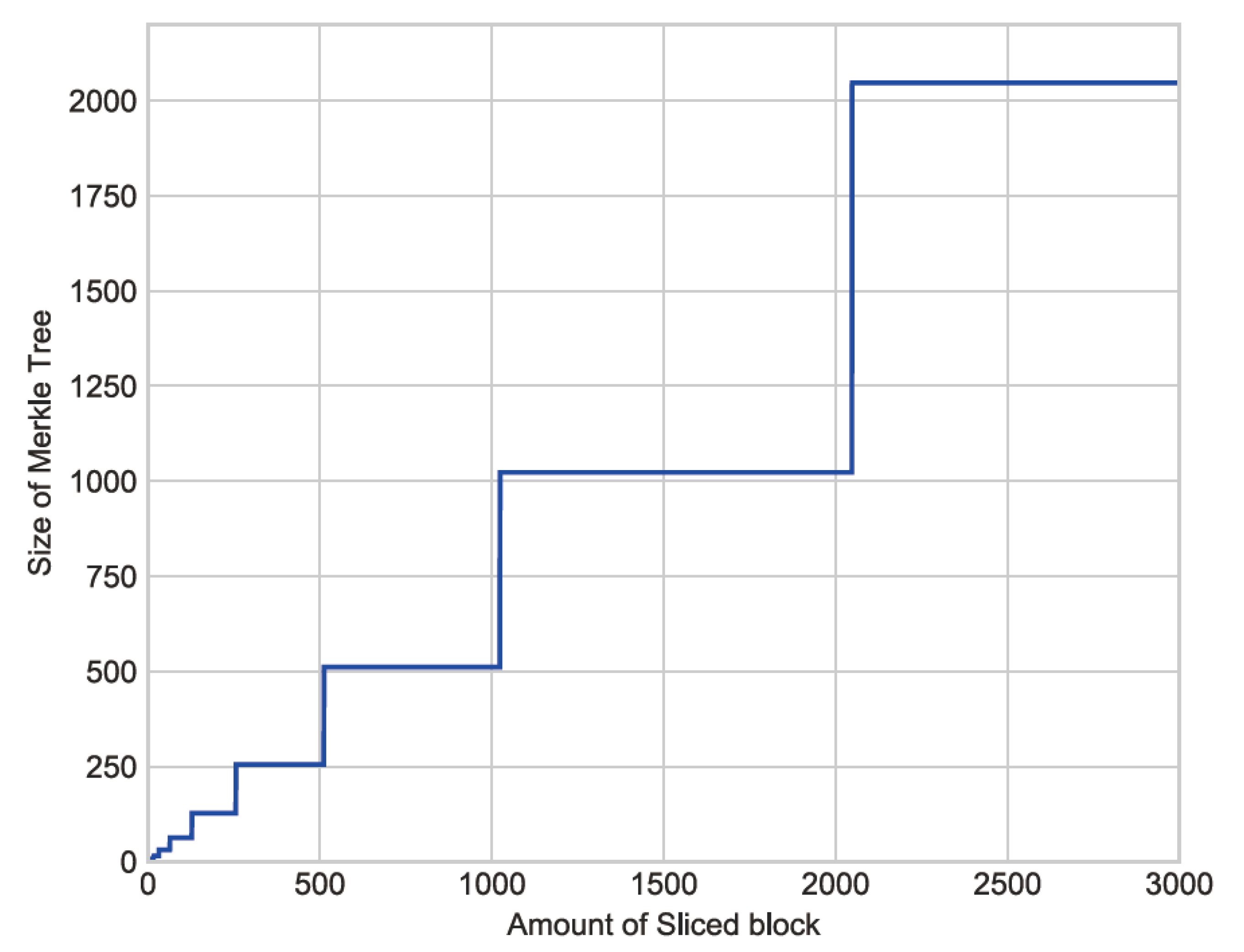
3.1. Merkle Tree Generation
| Procedure 1 Merkle Tree Generation |
Input: Original Image Output: Merkle tree M
|
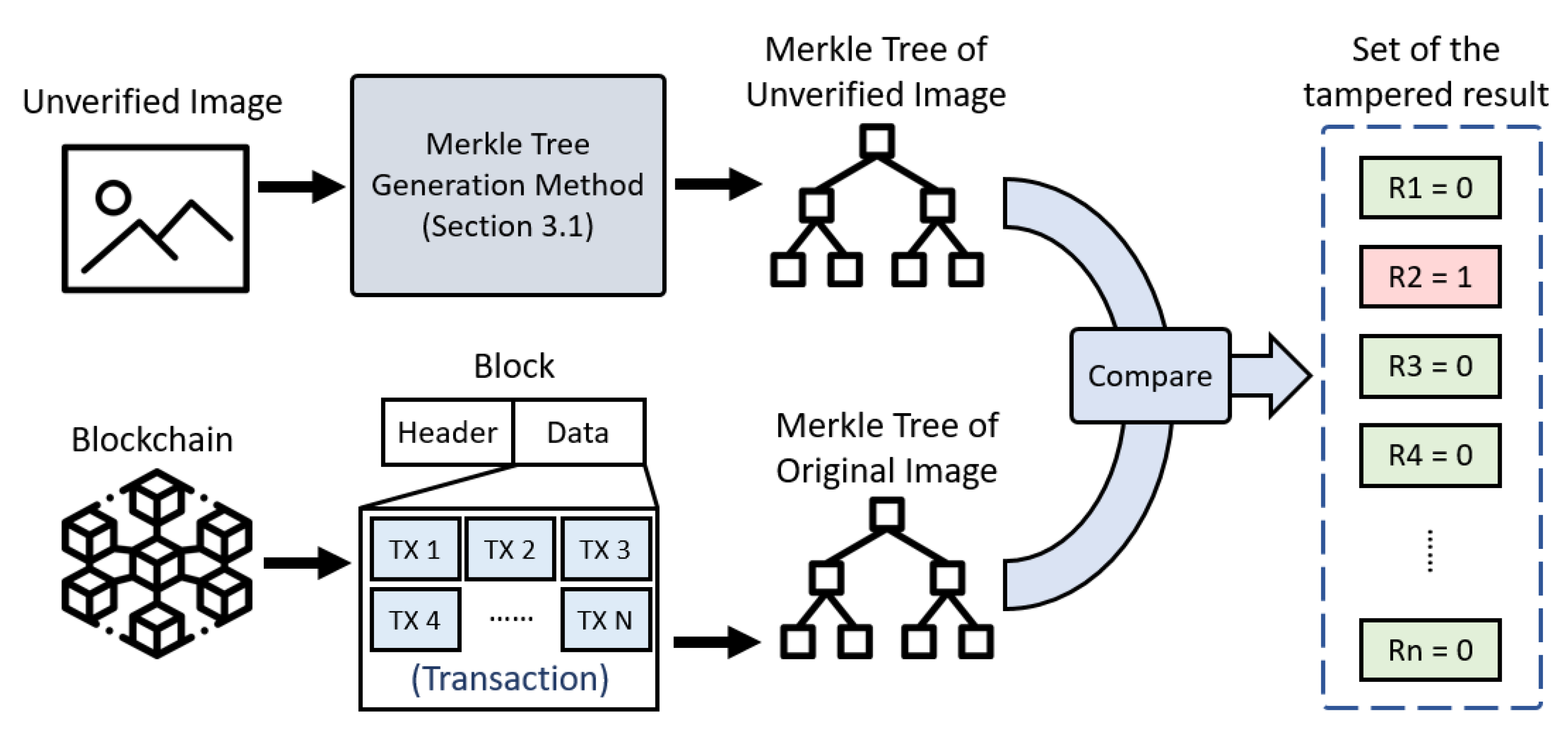
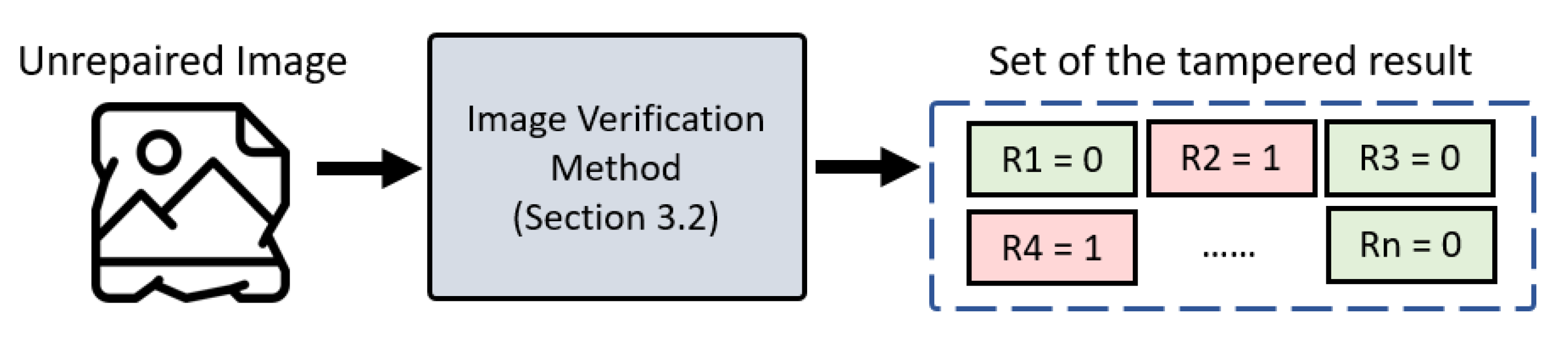
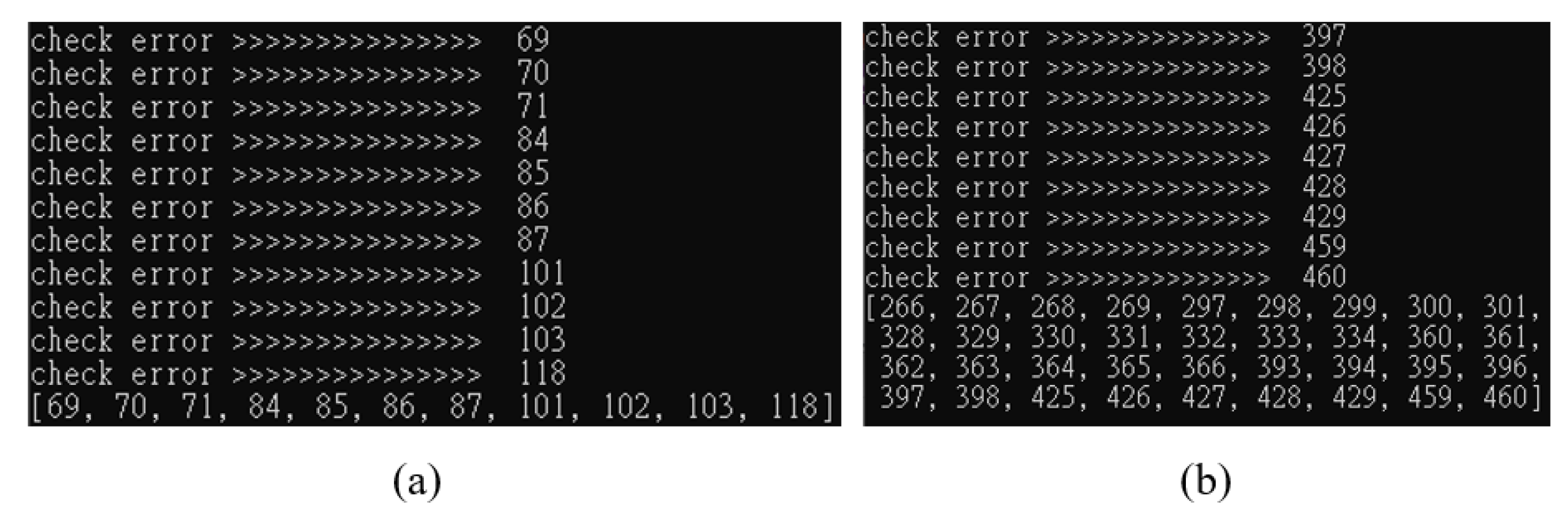
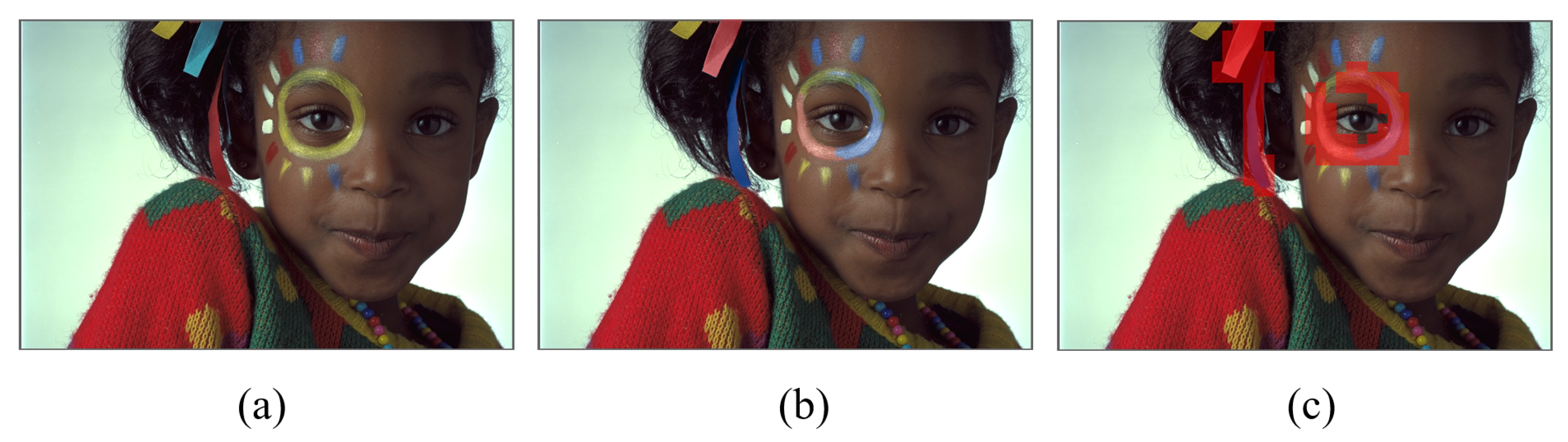
3.2. Image Verification
| Procedure 2 Image Verification |
Input: Unverified Image Output: Set of the tampered result
|
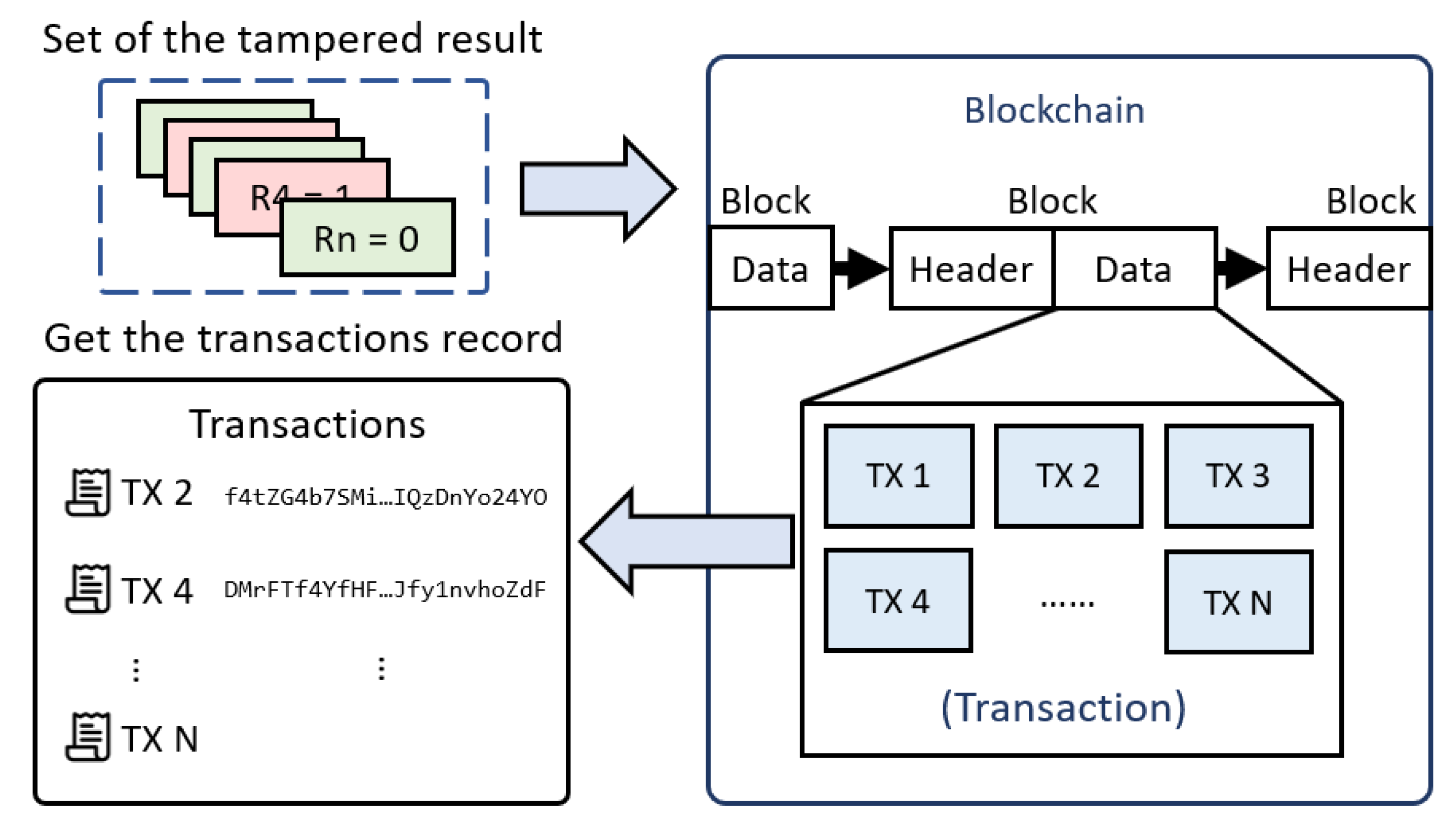
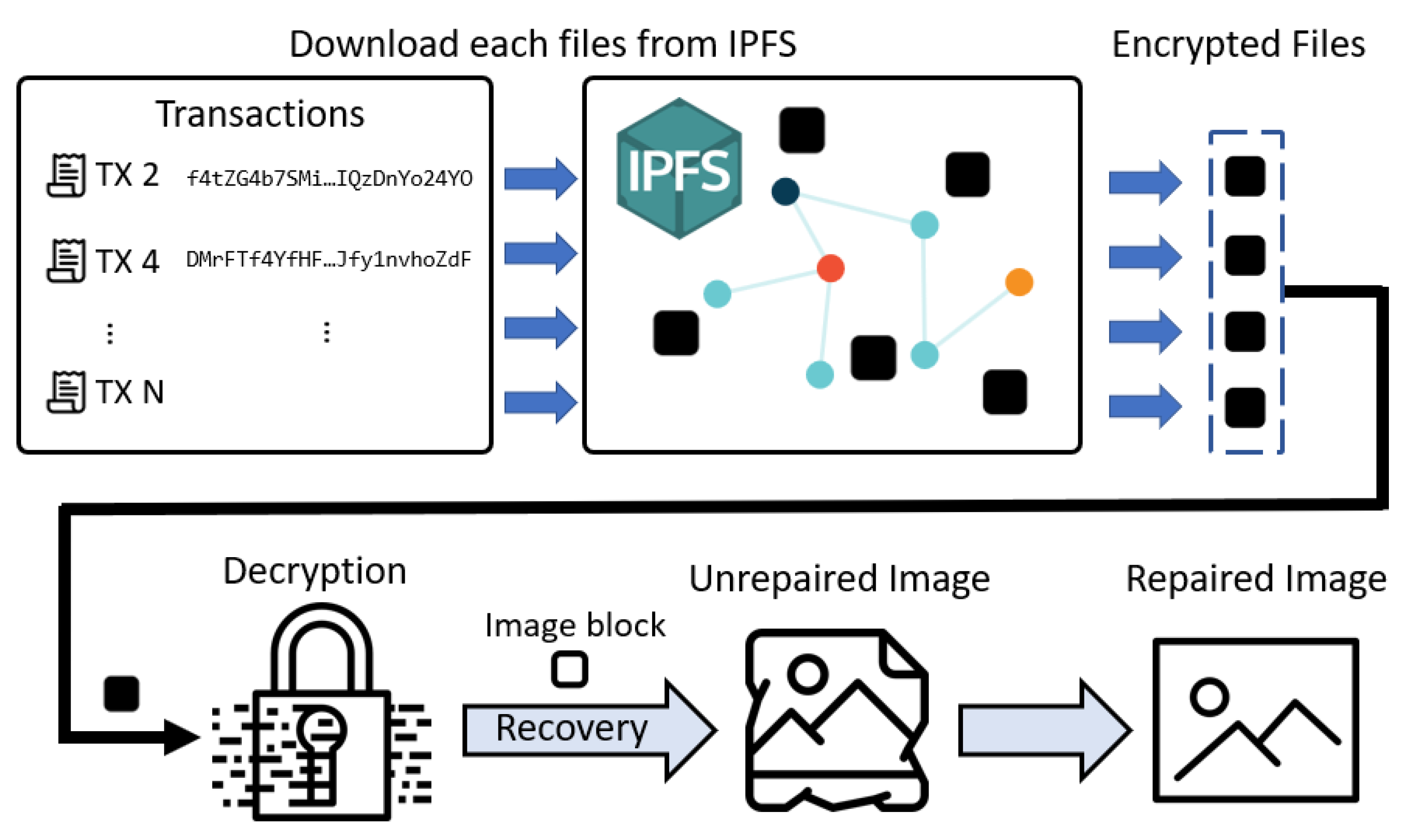
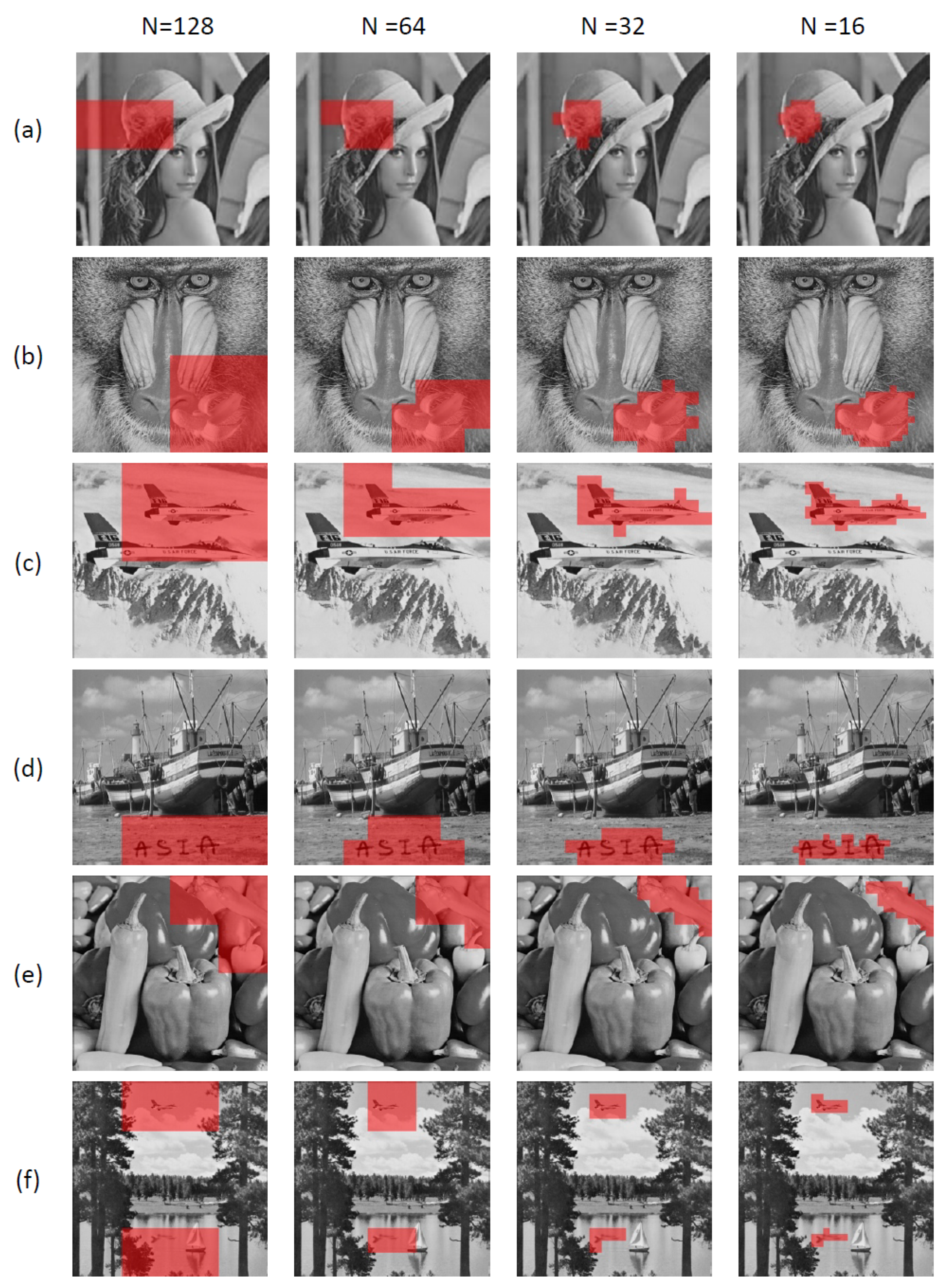
3.3. Image Recovery
| Procedure 3 Image Recovery |
Input: Unrecovered Image Output: Repaired Image
|
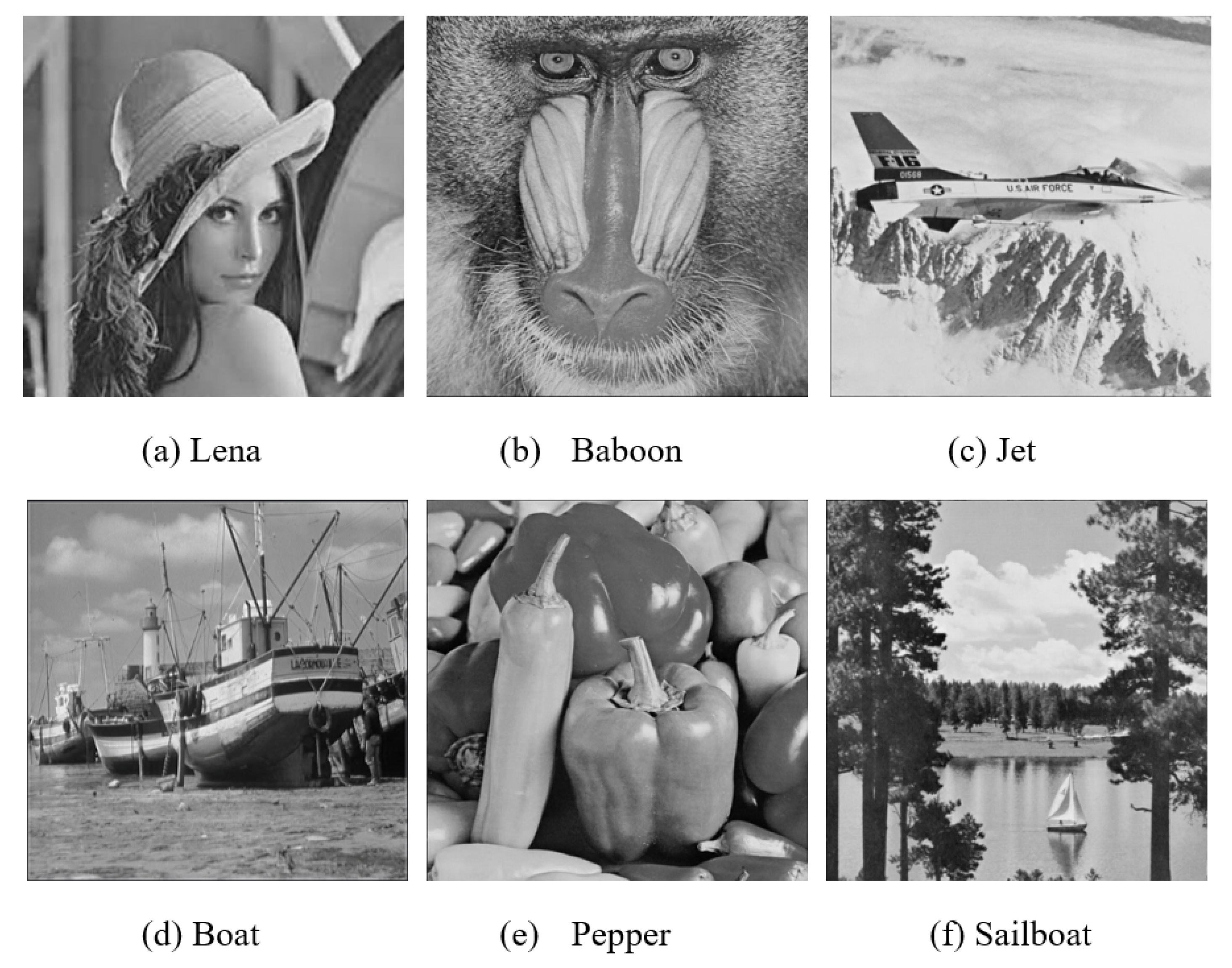
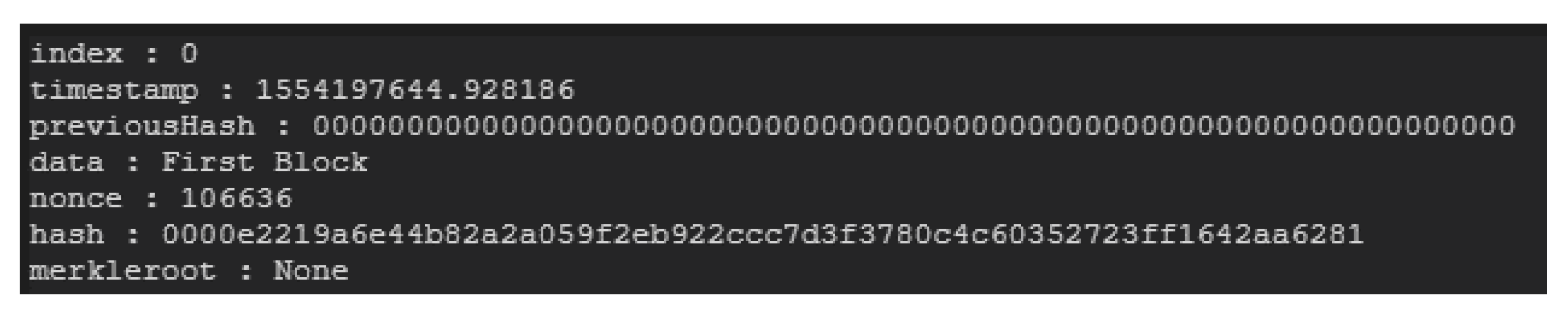
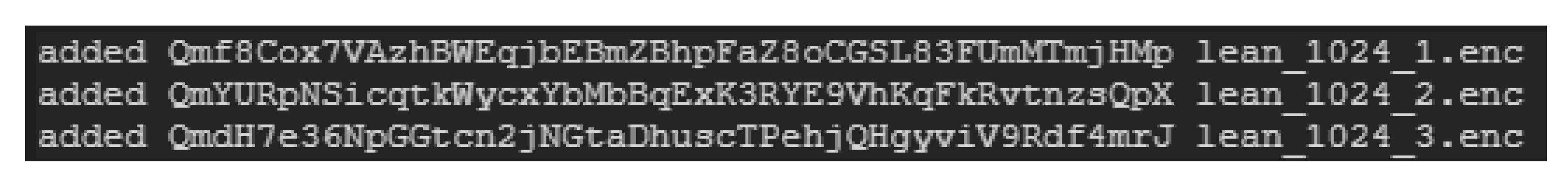
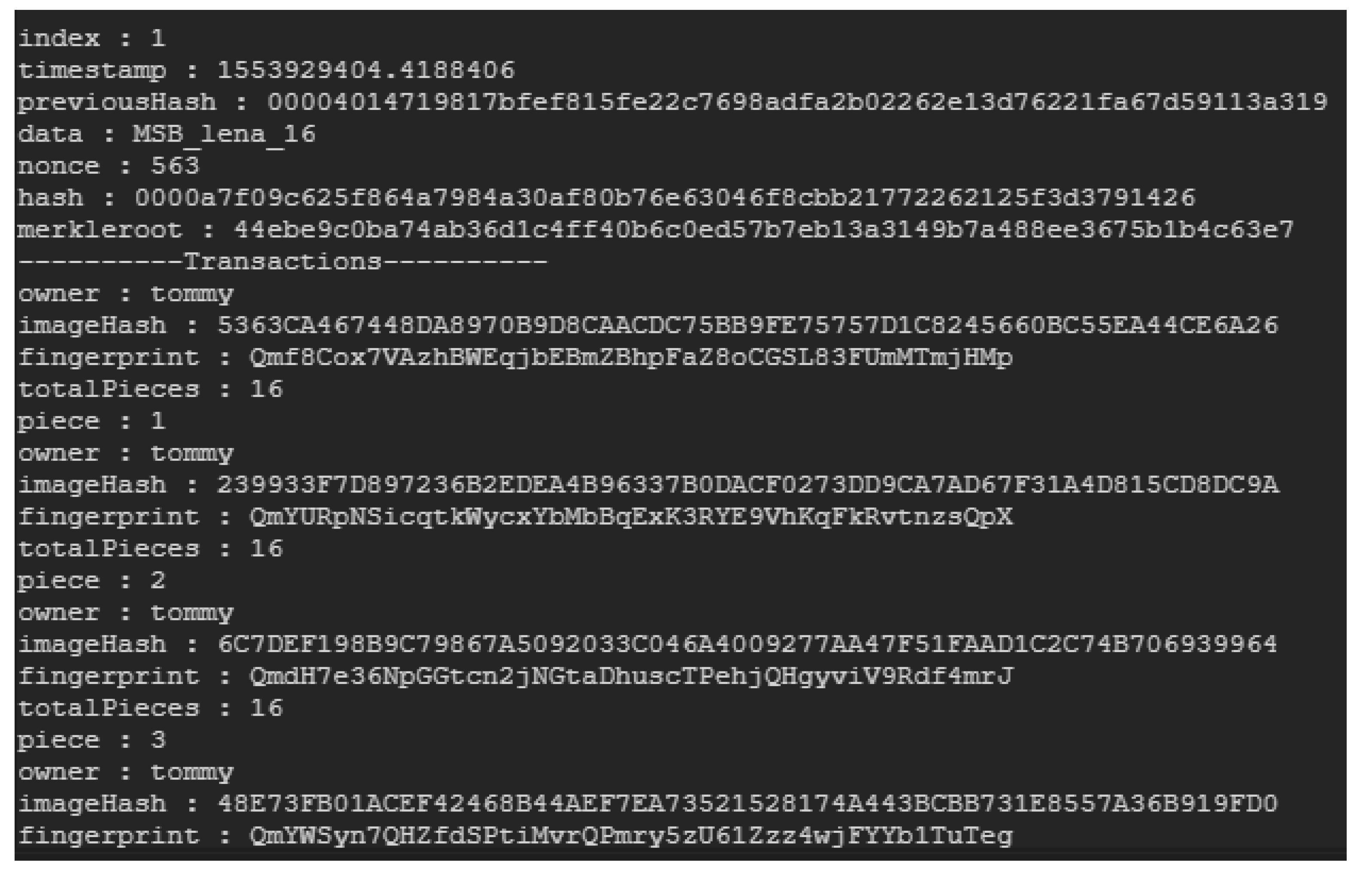
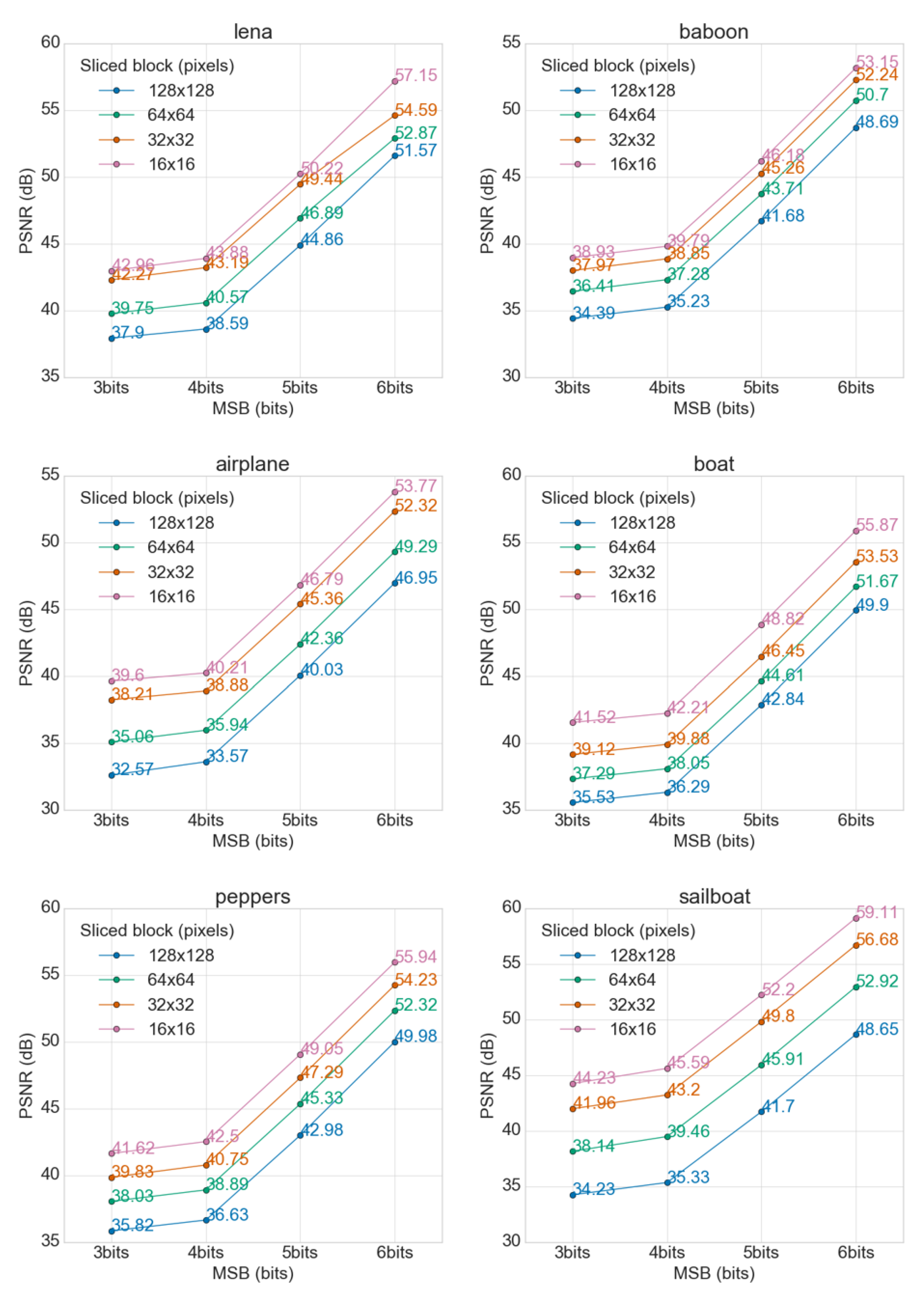
4. Simulation Results
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Hwang, M.S.; Lin, I.C. Introduction to Information and Network Security (in Chinese); Mcgraw Hill: Taipei, Taiwan, 2011. [Google Scholar]
- Kumar, C.; Singh, A.K.; Kumar, P. A recent survey on image watermarking techniques and its application in e-governance. Multimed. Tools Appl. 2018, 77, 3597–3622. [Google Scholar] [CrossRef]
- Cox, I.J.; Miller, M.L.; Bloom, J.A. Watermarking applications and their properties. In Proceedings of the International Conference on Information Technology: Coding and Computing (Cat. No. PR00540), Las Vegas, NV, USA, 27–29 March 2000; pp. 6–10. [Google Scholar]
- Joshi, M.A. Digital Image Processing: An Algorithmic Approach; PHI Learning Pvt. Ltd.: Delhi, India, 2018. [Google Scholar]
- Lin, I.C.; Liao, T.C. A Survey of Blockchain Security Issues and Challenges. IJ Netw. Secur. 2017, 19, 653–659. [Google Scholar]
- Swan, M. Blockchain: Blueprint for a New Economy; O’Reilly Media, Inc.: Sebastopol, CA, USA, 2015. [Google Scholar]
- Hughes, L.; Dwivedi, Y.K.; Misra, S.K.; Rana, N.P.; Raghavan, V.; Akella, V. Blockchain research, practice and policy: Applications, benefits, limitations, emerging research themes and research agenda. Int. J. Inf. Manag. 2019, 49, 114–129. [Google Scholar] [CrossRef]
- Benet, J. Ipfs-content addressed, versioned, p2p file system. arXiv 2014, arXiv:1407.3561. [Google Scholar]
- Mougayar, W. The Business Blockchain: Promise, Practice, and Application of the Next Internet Technology; John Wiley & Sons: Hoboken, NJ, USA, 2016. [Google Scholar]
- Zheng, Z.; Xie, S.; Dai, H.N.; Chen, X.; Wang, H. Blockchain challenges and opportunities: A survey. Int. J. Web Grid Serv. 2018, 14, 352–375. [Google Scholar] [CrossRef]
- Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System. 2008. Available online: http://bitcoin. org/bitcoin. pdf (accessed on 5th July 2019).
- Sultan, K.; Ruhi, U.; Lakhani, R. Conceptualizing Blockchains: Characteristics & Applications. In Proceedings of the 11th IADIS International Conference Information Systems, Lisbon, Portugal, 14–16 April 2018; pp. 49–57. [Google Scholar]
- Carter, J.L.; Wegman, M.N. Universal classes of hash functions. J. Comput. Syst. Sci. 1979, 18, 143–154. [Google Scholar] [CrossRef]
- Merkle, R. Secrecy, Authentication, and Public Key Systems. Ph.D. Thesis, Stanford University, Stanford, CA, USA, 1979. [Google Scholar]
- Becker, G. Merkle signature schemes, merkle trees and their cryptanalysis. Ruhr-University Bochum, Tech. Rep.. 2008. Available online: https://www.emsec.ruhr-uni-bochum.de/media/crypto/attachments/files/2011/04/becker_1.pdf (accessed on 5th July 2019).
- Merkle, R.C. Protocols for public key cryptosystems. In Proceedings of the 1980 IEEE Symposium on Security and Privacy, Oakland, CA, USA, 14–16 April 1980; p. 122. [Google Scholar]
- Haouzia, A.; Noumeir, R. Methods for image authentication: A survey. Multimed. Tools Appl. 2008, 39, 1–46. [Google Scholar] [CrossRef]
- Chang, C.C.; Chen, T.S.; Huang, K.F. Digital Image Processing Techniques; Flag Information Co. Ltd.: Taipei, Taiwan, 2003. (In Chinese) [Google Scholar]
- Bhowmik, D.; Feng, T. The multimedia blockchain: A distributed and tamper-proof media transaction framework. In Proceedings of the 2017 22nd International Conference on Digital Signal Processing (DSP), London, UK, 23–25 August 2017; pp. 1–5. [Google Scholar]
- Bhowmik, D.; Natu, A.; Ishikawa, T.; Feng, T.; Abhayaratne, C. The Jpeg-Blockchain Framework For Glam Services. In Proceedings of the 2018 IEEE International Conference on Multimedia & Expo Workshops (ICMEW), San Diego, CA, USA, 23–27 July 2018; pp. 1–6. [Google Scholar]
- Badr, B.; Horrocks, R.; Wu, X.B. Blockchain By Example: A Developer’S Guide to Creating Decentralized Applications Using Bitcoin, Ethereum, and Hyperledger; Packt Publishing Ltd.: Birmingham, UK, 2018. [Google Scholar]

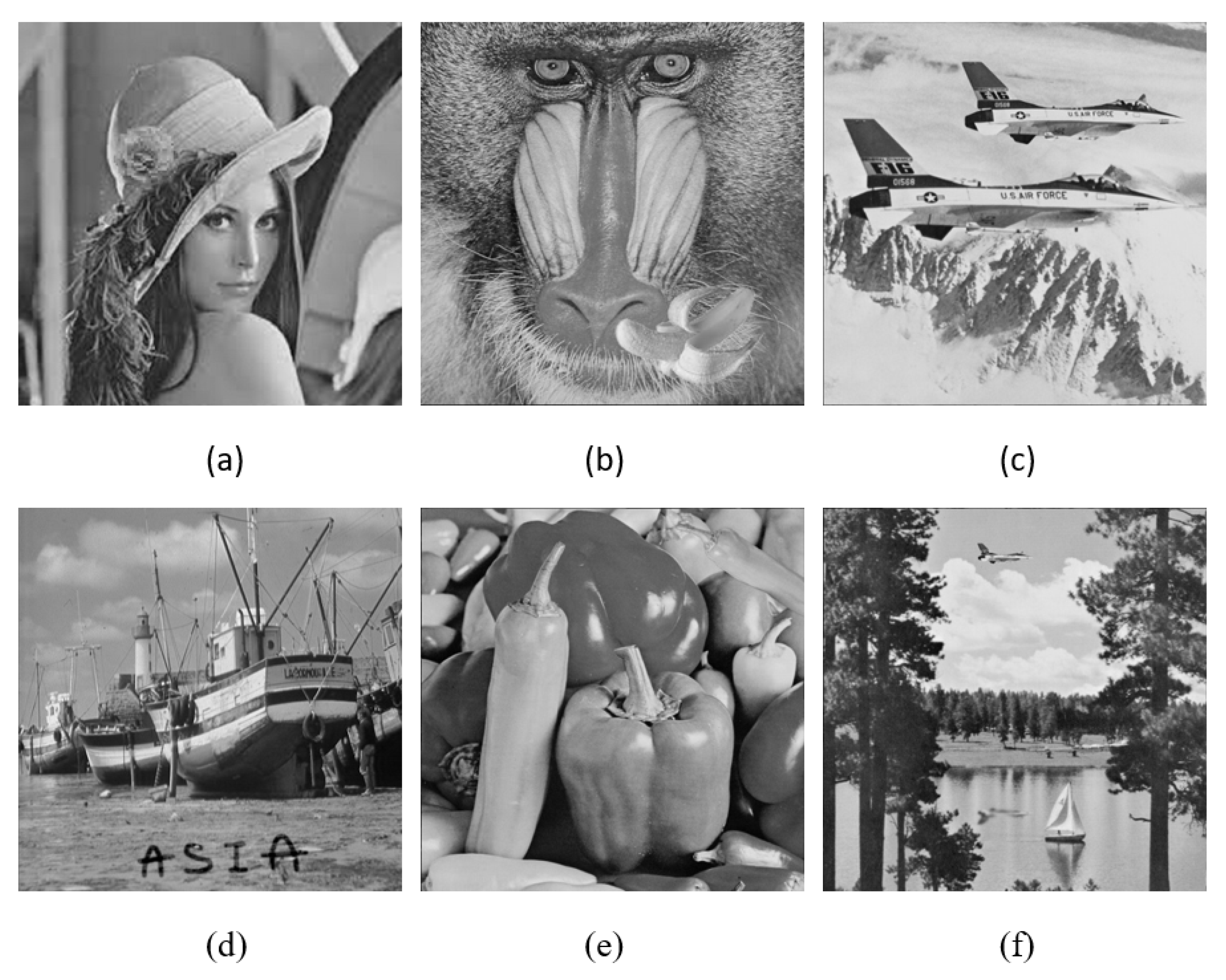
| Image | bits | 16 × 16 | 32 × 32 | 64 × 64 | 128 × 128 |
|---|---|---|---|---|---|
| lena | 3 bits | 3.29 | 3.85 | 6.88 | 10.52 |
| 4 bits | 2.66 | 3.12 | 5.70 | 8.99 | |
| 5 bits | 0.62 | 0.84 | 1.33 | 2.12 | |
| 6 bits | 0.13 | 0.23 | 0.34 | 0.45 | |
| baboon | 3 bits | 8.30 | 10.37 | 14.84 | 23.63 |
| 4 bits | 6.82 | 8.47 | 12.14 | 19.48 | |
| 5 bits | 1.57 | 1.94 | 2.77 | 4.41 | |
| 6 bits | 0.31 | 0.39 | 0.55 | 0.88 | |
| airplane | 3 bits | 7.12 | 9.80 | 20.25 | 35.92 |
| 4 bits | 6.19 | 8.41 | 16.55 | 28.52 | |
| 5 bits | 1.36 | 1.89 | 3.77 | 6.45 | |
| 6 bits | 0.27 | 0.38 | 0.77 | 1.31 | |
| boat | 3 bits | 4.57 | 7.95 | 12.11 | 18.19 |
| 4 bits | 3.90 | 6.68 | 10.17 | 15.25 | |
| 5 bits | 0.85 | 1.47 | 2.25 | 3.38 | |
| 6 bits | 0.17 | 0.29 | 0.44 | 0.66 | |
| peppers | 3 bits | 41.62 | 39.83 | 38.03 | 17.00 |
| 4 bits | 42.50 | 40.75 | 38.89 | 14.11 | |
| 5 bits | 49.05 | 47.29 | 45.33 | 3.27 | |
| 6 bits | 55.94 | 54.23 | 52.32 | 0.65 | |
| sailboat | 3 bits | 4.48 | 6.75 | 10.22 | 34.23 |
| 4 bits | 3.65 | 5.46 | 8.39 | 35.33 | |
| 5 bits | 0.81 | 1.21 | 1.90 | 41.70 | |
| 6 bits | 0.17 | 0.25 | 0.38 | 48.65 |
| Image | bits | 16 × 16 | 32 × 32 | 64 × 64 | 128 × 128 |
|---|---|---|---|---|---|
| lena | 3 bits | 42.96 | 42.27 | 39.75 | 37.90 |
| 4 bits | 43.88 | 43.19 | 40.57 | 38.59 | |
| 5 bits | 50.22 | 49.44 | 46.89 | 44.86 | |
| 6 bits | 57.15 | 54.59 | 52.87 | 51.57 | |
| baboon | 3 bits | 38.93 | 37.97 | 36.41 | 34.39 |
| 4 bits | 39.79 | 38.85 | 37.28 | 35.23 | |
| 5 bits | 46.18 | 45.26 | 43.71 | 41.68 | |
| 6 bits | 53.15 | 52.24 | 50.70 | 48.69 | |
| airplane | 3 bits | 39.60 | 38.21 | 35.06 | 32.57 |
| 4 bits | 40.21 | 38.88 | 35.94 | 33.57 | |
| 5 bits | 46.79 | 45.36 | 42.39 | 40.03 | |
| 6 bits | 53.77 | 52.32 | 49.29 | 46.95 | |
| boat | 3 bits | 41.52 | 39.12 | 37.29 | 35.53 |
| 4 bits | 42.21 | 39.88 | 38.05 | 36.29 | |
| 5 bits | 48.82 | 46.45 | 44.61 | 42.84 | |
| 6 bits | 55.87 | 53.53 | 51.67 | 49.90 | |
| peppers | 3 bits | 41.62 | 39.83 | 38.03 | 35.82 |
| 4 bits | 42.50 | 40.75 | 38.89 | 36.63 | |
| 5 bits | 49.05 | 47.29 | 45.33 | 42.98 | |
| 6 bits | 55.94 | 54.23 | 52.32 | 49.98 | |
| sailboat | 3 bits | 44.23 | 41.96 | 38.14 | 34.23 |
| 4 bits | 45.59 | 43.20 | 39.46 | 35.33 | |
| 5 bits | 52.20 | 49.80 | 45.91 | 41.70 | |
| 6 bits | 59.11 | 56.68 | 52.92 | 48.65 |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Chen, Y.-C.; Chou, Y.-P.; Chou, Y.-C. An Image Authentication Scheme Using Merkle Tree Mechanisms. Future Internet 2019, 11, 149. https://doi.org/10.3390/fi11070149
Chen Y-C, Chou Y-P, Chou Y-C. An Image Authentication Scheme Using Merkle Tree Mechanisms. Future Internet. 2019; 11(7):149. https://doi.org/10.3390/fi11070149
Chicago/Turabian StyleChen, Yi-Cheng, Yueh-Peng Chou, and Yung-Chen Chou. 2019. "An Image Authentication Scheme Using Merkle Tree Mechanisms" Future Internet 11, no. 7: 149. https://doi.org/10.3390/fi11070149
APA StyleChen, Y.-C., Chou, Y.-P., & Chou, Y.-C. (2019). An Image Authentication Scheme Using Merkle Tree Mechanisms. Future Internet, 11(7), 149. https://doi.org/10.3390/fi11070149





