Cyber-Storms Come from Clouds: Security of Cloud Computing in the IoT Era
Abstract
1. Introduction
Contribution and Outline of the Paper
- We provide a novel Cloud-centered perspective of IoT security. As already mentioned, Cloud computing has become of paramount importance for Internet of Things. Nevertheless, most of the works related to IoT security focus on the security of end devices. In this paper, we fill this gap providing an analysis of Cloud security issues and how they affect IoT security.
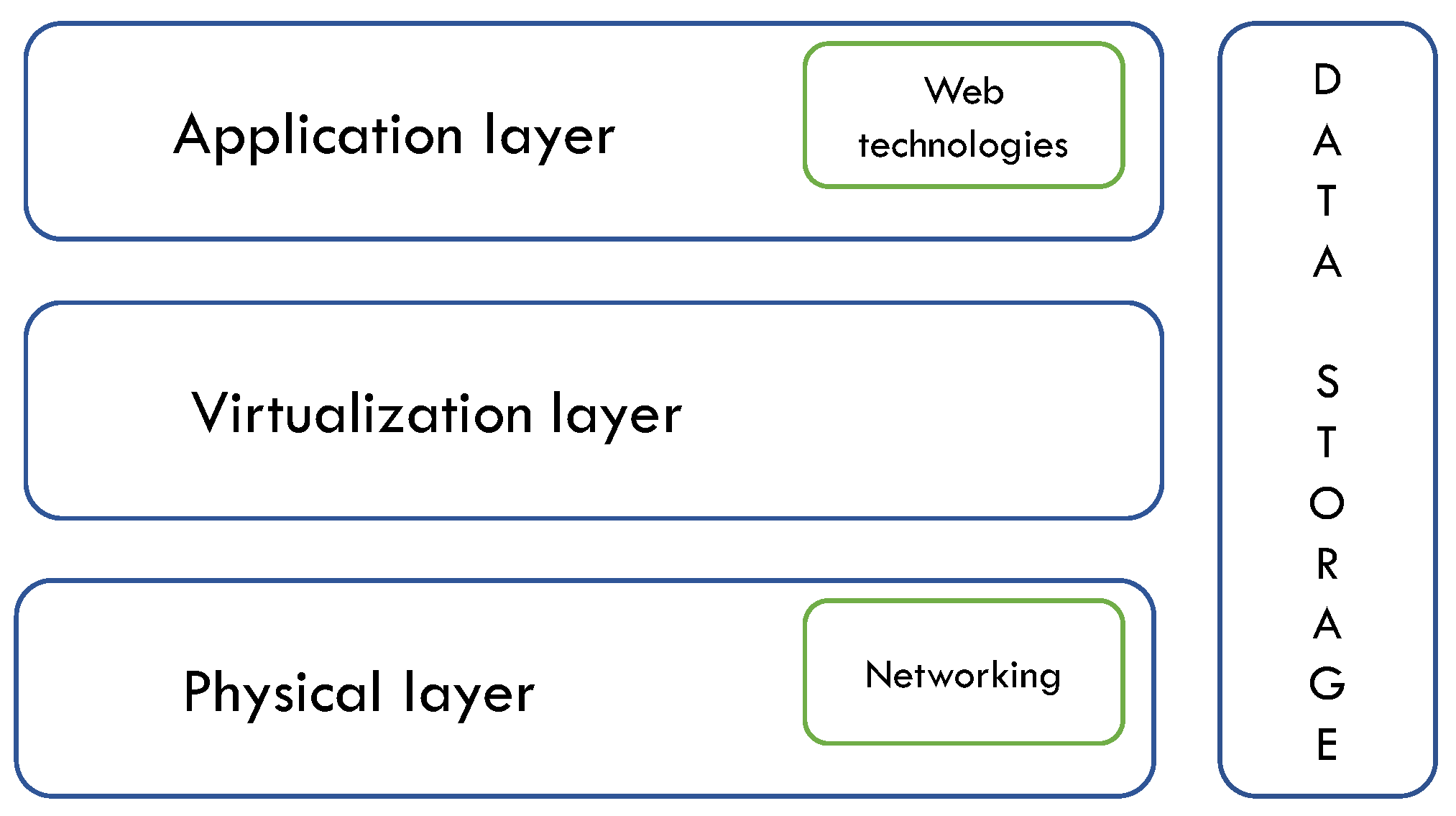
- We propose and discuss a structured classification of Cloud computing security issues: differently from other works, security issues associated with Cloud computing will be classified according to different layers. First, we distinguish between Cloud-specific security issues and other issues non strictly related to the Cloud but still important in the IoT context. Then, for each layer of the Cloud architecture, we investigate security properties affected by each issue. This contribution aims at giving a clear overall picture of all aspects of Cloud security.
2. Related Work
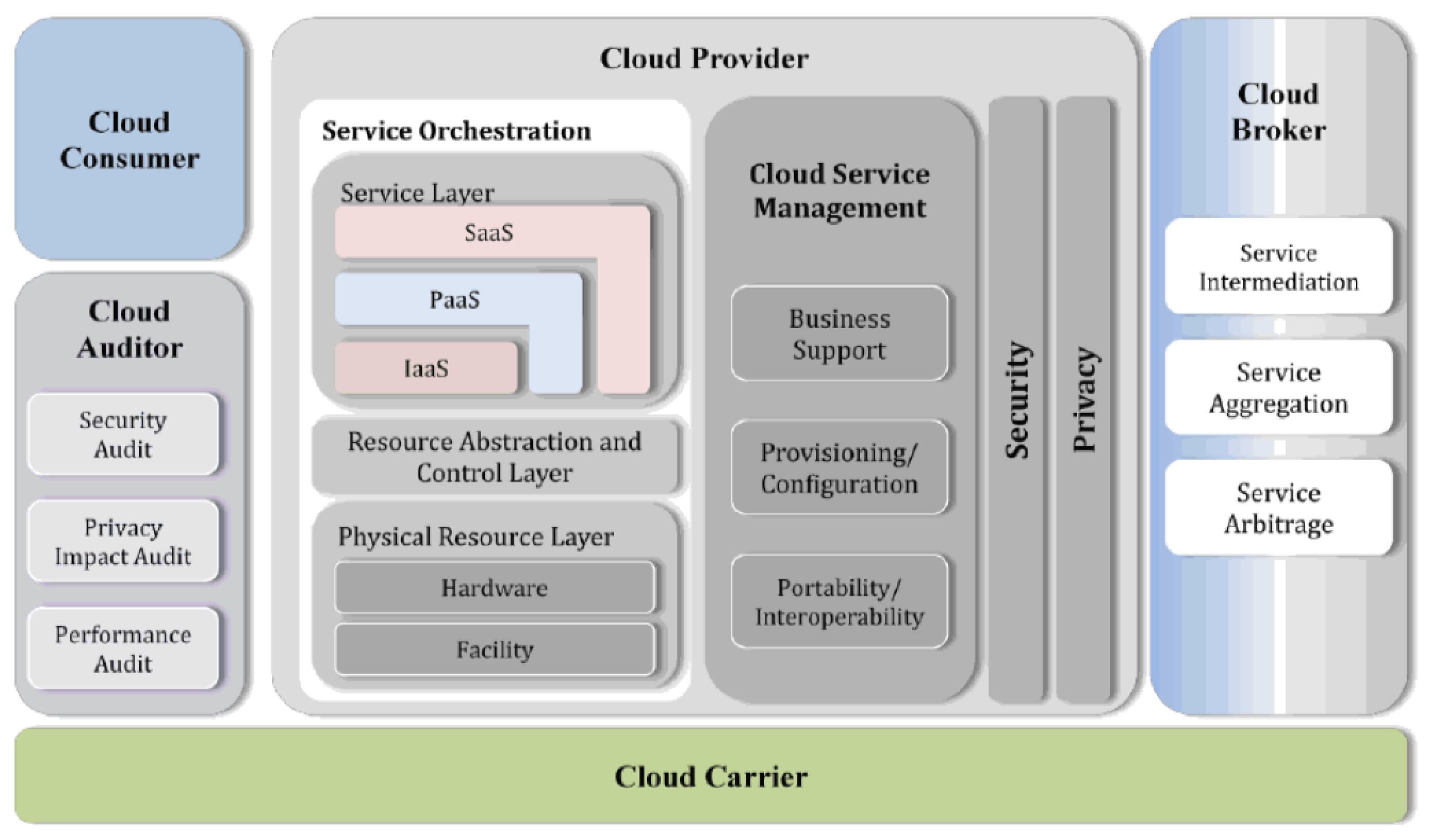
3. Background: Cloud Computing Paradigm
- Cloud Provider: an entity that provides a service to interested parties;
- Cloud Consumer: an entity that uses a service from, and has a business relationship with, one or more Cloud providers;
- Cloud Broker: an entity that mediates affairs between Cloud providers and Cloud consumers, and that manages the use, performance, and delivery of Cloud services;
- Cloud Carrier: an intermediary that supplies connectivity and delivery of Cloud services from Cloud providers to Cloud consumers;
- Cloud Auditor: a party that conducts independent assessments of the Cloud infrastructure, including services, information systems operations, performances, and security of the Cloud implementation.
3.1. Essential Characteristics
- On-demand self-service: computing capabilities can be provided automatically when needed, without requiring any human interaction between consumer and service provider;
- Broad network access: computing capabilities are available over the network and accessible through several mechanisms which are disposable for a wide range of client platforms (e.g., workstations, laptops, and mobile devices);
- Resource pooling: computing resources are pooled to accommodate multiple consumers, dynamically allocating and deallocating them according to consumer demand. In addition, the provider resources are location independent, i.e., the consumer does not have any knowledge or control of their exact location;
- Rapid elasticity: computing capabilities can flexibly be provided and released to scale in and out according to the demand. As a result, the consumer has the perception of unlimited, and always adequate, computing capabilities;
- Measured service: resource usage can be monitored and reported according to the type of service offered. This is particularly relevant in charge-per-use, or pay-per-user, services because it grants great transparency between the provider and the consumer of the service.
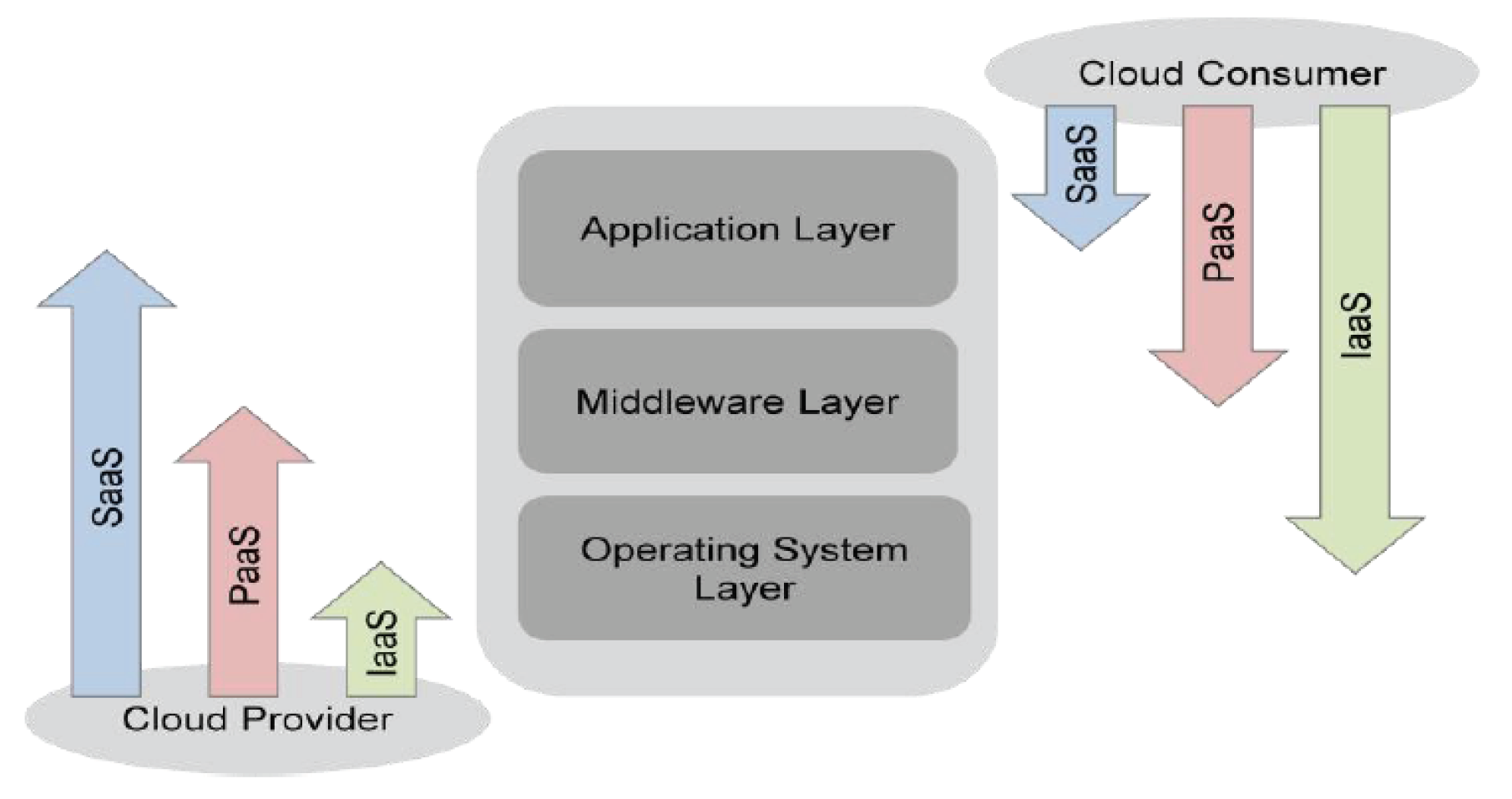
3.2. Service Models
- Infrastructure as a Service (IaaS): processing, storage, networks, and other fundamental computing resources (both software and hardware) are provided to the consumer. The consumer can run and deploy any software and can control operating systems, storage, and deployed applications. The consumer does not control or manage the underlying Cloud infrastructure;
- Platform as a Service (PaaS): the consumer is provided with a whole development stack that can be used to develop and deploy new applications. The development stack includes programming languages, libraries, services, and tools that are supported by the provider. The consumer controls both deployed applications and possible configuration settings for the applications environment. The consumer does not control or manage the underlying Cloud infrastructure, operating systems, and storage;
- Software as a Service (SaaS): the consumer can use the applications offered by the provider, running on the Cloud infrastructure. The consumer does not control or manage the underlying Cloud infrastructure, operating systems, storage, and individual applications capabilities.
3.3. Deployment Models
- Private Cloud: the Cloud infrastructure is provided for the exclusive use of a single organization. The organization can include different consumers (e.g., business units);
- Community Cloud: the Cloud infrastructure is provisioned for the exclusive use of organizations with shared concerns, such as security requirements, policy, and mission. Each organization can include multiple consumers;
- Public Cloud: the Cloud infrastructure is provided for open use by the general public over the Internet. It is ideal either for small to medium size businesses, or for single customers;
- Hybrid Cloud: the Cloud infrastructure is a combination of two or more infrastructures deployed with different models (private, community, or public). Each Cloud infrastructure remains a unique entity, but it is bound together with the others by standardized or proprietary technologies enabling portability.
4. Methodology
4.1. Reference Architecture
4.2. Structured Classification
- “✓”: it is placed if we found a literature work describing an attack affecting the corresponding security property, or if we found a literature work stating that the issue might affect the corresponding property;
- “∼”: it is placed if, although the previous condition is not verified, we believe that the given issue might allow compromising the corresponding security property;
- an empty cell, if the previous conditions do not hold.
5. Cloud-Specific Security Issues
5.1. Confidentiality
5.1.1. Virtualization Level Issues
Multi-Tenancy Issues
VM Isolation Issues
Virtual Network Issues
Virtual Machine Introspection Issues
VM Management Issues
VM Migration Issues
5.1.2. Application Level Issues
Isolation Issues
Synchronization Mechanisms Issues
5.1.3. Data Storage Level Issues
Outsourcing Issues
Data Deletion Issues
5.2. Integrity
5.2.1. Virtualization Level Issues
VM Isolation Issues
VM Management Issues
VM Migration Issues
5.2.2. Application Level Issues
Computation Cheating Issues
Insecure APIs, Management and Control Interfaces
Isolation Issues
Synchronization Mechanisms Issues
5.2.3. Data Storage Level Issues
Outsourcing Issues
5.3. Availability
5.3.1. Virtualization Level Issues
Multi-Tenancy Issues
VM Management Issues
VM Isolation
Virtual Network Issues
VM Migration Issues
5.3.2. Application Level Issues
Resource Accounting Issues
5.3.3. Network Level Issues
Network Under-Provisioning Issues
5.3.4. Multi-Level Issues
Economic Sustainability Issues
6. Generic Security Issues
6.1. Confidentiality
6.1.1. Network Level Issues
6.1.2. Application Level Issues
6.1.3. Multi-Level Issues
6.2. Integrity
6.2.1. Network Level Issues
6.2.2. Application Level Issues
6.3. Availability
6.3.1. Network Level Issues
6.3.2. Application Level Issues
7. IoT Security Issues
Discussion
8. Conclusions and Future Work
Author Contributions
Funding
Conflicts of Interest
References
- IoTdevs. Available online: https://www.statista.com/statistics/471264/iot-number-of-connected-devices-worldwide/ (accessed on 21 January 2019).
- Rehman, H.U.; Asif, M.; Ahmad, M. Future applications and research challenges of IOT. In Proceedings of the 2017 International Conference on Information and Communication Technologies (ICICT), Karachi, Pakistan, 30–31 December 2017; pp. 68–74. [Google Scholar]
- Nalin, M.; Baroni, I.; Mazzara, M. A Holistic Infrastructure to Support Elderlies’ Independent Living. In Encyclopedia of E-Health and Telemedicine; IGI Global: Hershey, PA, USA, 2016. [Google Scholar]
- Salikhov, D.; Khanda, K.; Gusmanov, K.; Mazzara, M.; Mavridis, N. Microservice-based IoT for Smart Buildings. In Proceedings of the 31st International Conference on Advanced Information Networking and Applications Workshops (WAINA), Taipei, Taiwan, 27–29 March 2017. [Google Scholar]
- Salikhov, D.; Khanda, K.; Gusmanov, K.; Mazzara, M.; Mavridis, N. Jolie Good Buildings: Internet of things for smart building infrastructure supporting concurrent apps utilizing distributed microservices. In Proceedings of the 1st International conference on Convergent Cognitive Information Technologies, Moscow, Russia, 25–26 November 2016; pp. 48–53. [Google Scholar]
- Dragoni, N.; Giaretta, A.; Mazzara, M. The Internet of Hackable Things. In Proceedings of the 5th International Conference in Software Engineering for Defense Applications (SEDA’16), Rome, Italy, 10 May 2016; Springer: Berlin/Heidelberg, Germany, 2018. [Google Scholar]
- De Donno, M.; Dragoni, N.; Giaretta, A.; Spognardi, A. DDoS-Capable IoT Malwares: Comparative Analysis and Mirai Investigation. Secur. Commun. Netw. 2018, 2018, 7178164. [Google Scholar] [CrossRef]
- Donno, M.D.; Dragoni, N.; Giaretta, A.; Mazzara, M. AntibIoTic: Protecting IoT Devices Against DDoS Attacks. In Proceedings of the 5th International Conference in Software Engineering for Defence Applications—SEDA 2016, Rome, Italy, 10 May 2016; pp. 59–72. [Google Scholar]
- Online Oxford Dictionary. Available online: https://en.oxforddictionaries.com/definition/internet_of_things (accessed on 3 December 2018).
- Yang, Y.; Wu, L.; Yin, G.; Li, L.; Zhao, H. A survey on security and privacy issues in Internet-of-Things. IEEE Internet Things J. 2017, 4, 1250–1258. [Google Scholar] [CrossRef]
- Lin, J.; Yu, W.; Zhang, N.; Yang, X.; Zhang, H.; Zhao, W. A survey on Internet of Things: Architecture, enabling technologies, security and privacy, and applications. IEEE Internet Things J. 2017, 4, 1125–1142. [Google Scholar] [CrossRef]
- Conti, M.; Dehghantanha, A.; Franke, K.; Watson, S. Internet of Things security and forensics: Challenges and opportunities. Future Gener. Comput. Syst. 2018, 78, 544–546. [Google Scholar] [CrossRef]
- Guan, Z.; Li, J.; Wu, L.; Zhang, Y.; Wu, J.; Du, X. Achieving Efficient and Secure Data Acquisition for Cloud-Supported Internet of Things in Smart Grid. IEEE Internet Things J. 2017, 4, 1934–1944. [Google Scholar] [CrossRef]
- Mihovska, A.; Sarkar, M. Smart Connectivity for Internet of Things (IoT) Applications. In New Advances in the Internet of Things; Yager, R.R., Pascual Espada, J., Eds.; Springer International Publishing: Cham, Switerland, 2018; pp. 105–118. [Google Scholar]
- Malik, A.; Om, H. Cloud Computing and Internet of Things Integration: Architecture, Applications, Issues, and Challenges. In Sustainable Cloud and Energy Services: Principles and Practice; Rivera, W., Ed.; Springer International Publishing: Cham, Switerland, 2018; pp. 1–24. [Google Scholar]
- Mahmud, R.; Kotagiri, R.; Buyya, R. Fog Computing: A Taxonomy, Survey and Future Directions. In Internet of Everything: Algorithms, Methodologies, Technologies and Perspectives; Di Martino, B., Li, K.C., Yang, L.T., Esposito, A., Eds.; Springer: Singapore, 2018; pp. 103–130. [Google Scholar]
- Botta, A.; de Donato, W.; Persico, V.; Pescapé, A. On the Integration of Cloud Computing and Internet of Things. In Proceedings of the 2014 International Conference on Future Internet of Things and Cloud, Barcelona, Spain, 27–29 August 2014; pp. 23–30. [Google Scholar] [CrossRef]
- Botta, A.; De Donato, W.; Persico, V.; Pescapé, A. Integration of cloud computing and internet of things: A survey. Future Gener. Comput. Syst. 2016, 56, 684–700. [Google Scholar] [CrossRef]
- Díaz, M.; Martín, C.; Rubio, B. State-of-the-art, challenges, and open issues in the integration of Internet of things and cloud computing. J. Netw. Comput. Appl. 2016, 67, 99–117. [Google Scholar] [CrossRef]
- Cook, A.; Robinson, M.; Ferrag, M.A.; Maglaras, L.A.; He, Y.; Jones, K.; Janicke, H. Internet of Cloud: Security and Privacy Issues. In Cloud Computing for Optimization: Foundations, Applications, and Challenges; Mishra, B.S.P., Das, H., Dehuri, S., Jagadev, A.K., Eds.; Springer International Publishing: Cham, Switerland, 2018; pp. 271–301. [Google Scholar]
- OpenFog Consortium Architecture Working Group. OpenFog Reference Architecture for Fog Computing. 2017. Available online: https://www.openfogconsortium.org/wp-content/uploads/OpenFog_Reference_Architecture_2_09_17-FINAL.pdf (accessed on 4 June 2019).
- Liu, Y.; Sun, Y.; Ryoo, J.; Rizvi, S.; Vasilakos, A.V. A survey of security and privacy challenges in cloud computing: solutions and future directions. J. Comput. Sci. Eng. 2015, 9, 119–133. [Google Scholar] [CrossRef]
- Shahzad, F. State-of-the-art survey on cloud computing security Challenges, approaches and solutions. Procedia Comput. Sci. 2014, 37, 357–362. [Google Scholar] [CrossRef]
- Ryan, M.D. Cloud computing security: The scientific challenge, and a survey of solutions. J. Syst. Softw. 2013, 86, 2263–2268. [Google Scholar] [CrossRef]
- Subashini, S.; Kavitha, V. A survey on security issues in service delivery models of cloud computing. J. Netw. Comput. Appl. 2011, 34, 1–11. [Google Scholar] [CrossRef]
- Grobauer, B.; Walloschek, T.; Stocker, E. Understanding cloud computing vulnerabilities. IEEE Secur. Priv. 2011, 9, 50–57. [Google Scholar] [CrossRef]
- Modi, C.; Patel, D.; Borisaniya, B.; Patel, A.; Rajarajan, M. A survey on security issues and solutions at different layers of Cloud computing. J. Supercomput. 2013, 63, 561–592. [Google Scholar] [CrossRef]
- Singh, S.; Jeong, Y.S.; Park, J.H. A survey on cloud computing security: Issues, threats, and solutions. J. Netw. Comput. Appl. 2016, 75, 200–222. [Google Scholar] [CrossRef]
- Fernandes, D.A.B.; Soares, L.F.B.; Gomes, J.V.; Freire, M.M.; Inácio, P.R.M. Security issues in cloud environments: A survey. Int. J. Inf. Secur. 2014, 13, 113–170. [Google Scholar] [CrossRef]
- Polash, F.; Abuhussein, A.; Shiva, S. A survey of cloud computing taxonomies: Rationale and overview. In Proceedings of the 9th International Conference for Internet Technology and Secured Transactions (ICITST-2014), London, UK, 8–10 December 2014; pp. 459–465. [Google Scholar] [CrossRef]
- Singh, A.; Chatterjee, K. Cloud security issues and challenges: A survey. J. Netw. Comput. Appl. 2017, 79, 88–115. [Google Scholar] [CrossRef]
- Xiao, Z.; Xiao, Y. Security and privacy in cloud computing. IEEE Commun. Surv. Tutor. 2013, 15, 843–859. [Google Scholar] [CrossRef]
- Ardagna, C.A.; Asal, R.; Damiani, E.; Vu, Q.H. From security to assurance in the cloud: A survey. ACM Comput. Surv. 2015, 48, 2. [Google Scholar] [CrossRef]
- Hashizume, K.; Rosado, D.G.; Fernández-Medina, E.; Fernandez, E.B. An analysis of security issues for cloud computing. J. Internet Serv. Appl. 2013, 4, 5. [Google Scholar] [CrossRef]
- Mell, P.; Grance, T. The NIST Definition of Cloud Computing; Technical Report; 2011. Available online: https://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication800-145.pdf (accessed on 4 June 2019).
- Liu, F.; Tong, J.; Mao, J.; Bohn, R.; Messina, J.; Badger, L.; Leaf, D. NIST Cloud Computing Reference Architecture; Technical Report 2011; NIST: Gaithersburg, MD, USA, 2011. [Google Scholar]
- Glossary of Terms Related to Fog Computing. Available online: https://www.openfogconsortium.org/wp-content/uploads/OpenFog-Consortium-Glossary-of-Terms-January-2018.pdf (accessed on 10 October 2018).
- Goodrich, M.; Tamassia, R. Introduction to Computer Security; Pearson Education, Inc.: Boston, MA, USA, 2011. [Google Scholar]
- Ristenpart, T.; Tromer, E.; Shacham, H.; Savage, S. Hey, You, Get off of My Cloud: Exploring Information Leakage in Third-party Compute Clouds. In Proceedings of the 16th ACM Conference on Computer and Communications Security, Chicago, IL, USA, 9–13 November 2009; ACM: New York, NY, USA, 2009; pp. 199–212. [Google Scholar] [CrossRef]
- Zhang, Y.; Juels, A.; Reiter, M.K.; Ristenpart, T. Cross-VM side channels and their use to extract private keys. In Proceedings of the 2012 ACM Conference on Computer and Communications Security, Raleigh, NC, USA, 16–18 October 2012; ACM: New York, NY, USA, 2012; pp. 305–316. [Google Scholar]
- Yarom, Y.; Falkner, K. FLUSH + RELOAD: A High Resolution, Low Noise, L3 Cache Side-Channel Attack. In Proceedings of the 23rd USENIX Security Symposium, San Diego, CA, USA, 20–22 August 2014; pp. 719–732. [Google Scholar]
- Liu, F.; Yarom, Y.; Ge, Q.; Heiser, G.; Lee, R.B. Last-level cache side-channel attacks are practical. In Proceedings of the 2015 IEEE Symposium on IEEE Security and Privacy (SP), San Jose, CA, USA, 17–21 May 2015; pp. 605–622. [Google Scholar]
- Irazoqui, G.; Inci, M.S.; Eisenbarth, T.; Sunar, B. Wait a minute! A fast, Cross-VM attack on AES. In International Workshop on Recent Advances in Intrusion Detection; Springer: Berlin/Heidelberg, Germany, 2014; pp. 299–319. [Google Scholar]
- Suzaki, K.; Iijima, K.; Yagi, T.; Artho, C. Memory Deduplication As a Threat to the Guest OS. In Proceedings of the Fourth European Workshop on System Security, Salzburg, Austria, 10 April 2011; ACM: New York, NY, USA, 2011; pp. 1:1–1:6. [Google Scholar] [CrossRef]
- Lipp, M.; Schwarz, M.; Gruss, D.; Prescher, T.; Haas, W.; Mangard, S.; Kocher, P.; Genkin, D.; Yarom, Y.; Hamburg, M. Meltdown. arXiv 2018, arXiv:1801.01207. [Google Scholar]
- Kocher, P.; Genkin, D.; Gruss, D.; Haas, W.; Hamburg, M.; Lipp, M.; Mangard, S.; Prescher, T.; Schwarz, M.; Yarom, Y. Spectre Attacks: Exploiting Speculative Execution. arXiv 2018, arXiv:1801.01203. [Google Scholar]
- Wang, Z.; Wu, C.; Grace, M.; Jiang, X. Isolating commodity hosted hypervisors with hyperlock. In Proceedings of the 7th ACM European Conference on Computer Systems, Bern, Switzerland, 10–13 April 2012; ACM: New York, NY, USA, 2012; pp. 127–140. [Google Scholar]
- Riddle, A.R.; Chung, S.M. A survey on the security of hypervisors in cloud computing. In Proceedings of the 2015 IEEE 35th International Conference on Distributed Computing Systems Workshops (ICDCSW), Columbus, OH, USA, 29 June–2 July 2015; pp. 100–104. [Google Scholar]
- Studnia, I.; Alata, E.; Deswarte, Y.; Kaâniche, M.; Nicomette, V. Survey of security problems in cloud computing virtual machines. In Proceedings of the C&ESAR 2012 Cloud and Security, Threat or Opportunity: Computer and Electronics Security Applications Rendez-vous, Rennes, France, 20–22 November 2012; pp. 61–74. [Google Scholar]
- Li, J.; Li, B.; Wo, T.; Hu, C.; Huai, J.; Liu, L.; Lam, K. CyberGuarder: A virtualization security assurance architecture for green cloud computing. Future Gener. Comput. Syst. 2012, 28, 379–390. [Google Scholar] [CrossRef]
- Almorsy, M.; Grundy, J.; Müller, I. An analysis of the cloud computing security problem. In Proceedings of the 2010 Asia Pacific Software Engineering Conference (APSEC 2010) Cloud Workshop, Sydney, Australia, 30 November–3 December 2010. [Google Scholar]
- Vaquero, L.M.; Rodero-Merino, L.; Morán, D. Locking the sky: A survey on IaaS cloud security. Computing 2011, 91, 93–118. [Google Scholar] [CrossRef]
- Wu, H.; Ding, Y.; Winer, C.; Yao, L. Network security for virtual machine in cloud computing. In Proceedings of the 2010 5th International Conference on Computer Sciences and Convergence Information Technology (ICCIT), Seoul, Korea, 30 November–2 December 2010; pp. 18–21. [Google Scholar]
- Schoo, P.; Fusenig, V.; Souza, V.; Melo, M.; Murray, P.; Debar, H.; Medhioub, H.; Zeghlache, D. Challenges for Cloud Networking Security; Pentikousis, K., Agüero, R., García-Arranz, M., Papavassiliou, S., Eds.; Mobile Networks and Management; Springer: Berlin/Heidelberg, Germany, 2011; pp. 298–313. [Google Scholar]
- Thimmaraju, K.; Shastry, B.; Fiebig, T.; Hetzelt, F.; Seifert, J.P.; Feldmann, A.; Schmid, S. The vAMP Attack: Taking Control of Cloud Systems via the Unified Packet Parser. In Proceedings of the 2017 on Cloud Computing Security Workshop, Dallas, TX, USA, 3 November 2017; ACM: New York, NY, USA, 2017; pp. 11–15. [Google Scholar] [CrossRef]
- Lombardi, F.; Di Pietro, R. Secure Virtualization for Cloud Computing. J. Netw. Comput. Appl. 2011, 34, 1113–1122. [Google Scholar] [CrossRef]
- Jiang, X.; Wang, X.; Xu, D. Stealthy Malware Detection Through Vmm-based “Out-of-the-box” Semantic View Reconstruction. In Proceedings of the 14th ACM Conference on Computer and Communications Security, Alexandria, VA, USA, 28–31 October 2007; ACM: New York, NY, USA, 2007; pp. 128–138. [Google Scholar] [CrossRef]
- Aikat, J.; Akella, A.; Chase, J.S.; Juels, A.; Reiter, M.K.; Ristenpart, T.; Sekar, V.; Swift, M. Rethinking Security in the Era of Cloud Computing. IEEE Secur. Priv. 2017, 15, 60–69. [Google Scholar] [CrossRef]
- Rocha, F.; Gross, T.; Moorsel, V.A. Defense-in-Depth Against Malicious Insiders in the Cloud. In Proceedings of the 2013 IEEE International Conference on Cloud Engineering (IC2E), Redwood City, CA, USA, 25–27 March 2013; pp. 88–97. [Google Scholar] [CrossRef]
- Bahram, S.; Jiang, X.; Wang, Z.; Grace, M.; Li, J.; Srinivasan, D.; Rhee, J.; Xu, D. DKSM: Subverting Virtual Machine Introspection for Fun and Profit. In Proceedings of the 2010 29th IEEE Symposium on Reliable Distributed Systems, New Delhi, India, 31 October–3 November 2010; pp. 82–91. [Google Scholar] [CrossRef]
- Duncan, A.J.; Creese, S.; Goldsmith, M. Insider attacks in cloud computing. In Proceedings of the 2012 IEEE 11th International Conference on Trust, Security and Privacy in Computing and Communications (TrustCom), Liverpool, UK, 25–27 June 2012; pp. 857–862. [Google Scholar]
- Wei, J.; Zhang, X.; Ammons, G.; Bala, V.; Ning, P. Managing Security of Virtual Machine Images in a Cloud Environment. In Proceedings of the 2009 ACM Workshop on Cloud Computing Security; ACM: New York, NY, USA, 2009; pp. 91–96. [Google Scholar] [CrossRef]
- Balduzzi, M.; Zaddach, J.; Balzarotti, D.; Kirda, E.; Loureiro, S. A Security Analysis of Amazon’s Elastic Compute Cloud Service. In Proceedings of the 27th Annual ACM Symposium on Applied Computing, Trento, Italy, 26–30 March 2012; ACM: New York, NY, USA, 2012; pp. 1427–1434. [Google Scholar] [CrossRef]
- Modi, C.; Patel, D.; Borisaniya, B.; Patel, H.; Patel, A.; Rajarajan, M. A survey of intrusion detection techniques in cloud. J. Netw. Comput. Appl. 2013, 36, 42–57. [Google Scholar] [CrossRef]
- Aiash, M.; Mapp, G.; Gemikonakli, O. Secure live virtual machines migration: Issues and solutions. In Proceedings of the 2014 28th International Conference on Advanced Information Networking and Applications Workshops (WAINA), Victoria, BC, Canada, 13–16 May 2014; pp. 160–165. [Google Scholar]
- Yeh, J.R.; Hsiao, H.C.; Pang, A.C. Migrant attack: A multi-resource dos attack on cloud virtual machine migration schemes. In Proceedings of the 2016 11th Asia Joint Conference on Information Security (AsiaJCIS), Fukuoka, Japan, 4–5 August 2016; pp. 92–99. [Google Scholar]
- Rakotondravony, N.; Taubmann, B.; Mandarawi, W.; Weishäupl, E.; Xu, P.; Kolosnjaji, B.; Protsenko, M.; de Meer, H.; Reiser, H.P. Classifying malware attacks in IaaS cloud environments. J. Cloud Comput. 2017, 6, 26. [Google Scholar] [CrossRef]
- Shetty, J.; Anala, M.R.; Shobha, G. A Survey on Techniques of Secure Live Migration of Virtual Machine. Int. J. Comput. Appl. 2012, 39, 34–39. [Google Scholar] [CrossRef]
- Rodero-Merino, L.; Vaquero, L.M.; Caron, E.; Muresan, A.; Desprez, F. Building safe PaaS clouds: A survey on security in multitenant software platforms. Comput. Secur. 2012, 31, 96–108. [Google Scholar] [CrossRef]
- Linthicum, D.S. PaaS Death Watch? IEEE Cloud Comput. 2017, 4, 6–9. [Google Scholar] [CrossRef]
- Favaretto, M.; Anh, T.T.; Kavaja, J.; De Donno, M.; Dragoni, N. When the Price is Your Privacy: A Security Analysis of Two Cheap IoT Devices. In Proceedings of the 6th International Conference in Software Engineering for Defense Applications, Rome, Italy, 7–8 June 2018; Springer: Berlin/Heidelberg, Germany, 2019. [Google Scholar]
- Nakouri, I.; Hamdi, M.; Kim, T.H. A new biometric-based security framework for cloud storage. In Proceedings of the 2017 13th International Wireless Communications and Mobile Computing Conference (IWCMC), Valencia, Spain, 26–30 June 2017; pp. 390–395. [Google Scholar] [CrossRef]
- Liang, X.; Shetty, S.; Zhang, L.; Kamhoua, C.; Kwiat, K. Man in the Cloud (MITC) Defender: SGX-Based User Credential Protection for Synchronization Applications in Cloud Computing Platform. In Proceedings of the 2017 IEEE 10th International Conference on Cloud Computing (CLOUD), Honolulu, CA, USA, 25–30 June 2017; pp. 302–309. [Google Scholar] [CrossRef]
- Samarati, P.; di Vimercati, S.D.C.; Murugesan, S.; Bojanova, I. Cloud security: Issues and concerns. In Encyclopedia on Cloud Computing; John Wiley & Sons: Hoboken, NJ, USA, 2016; pp. 1–14. [Google Scholar]
- Zhou, M.; Zhang, R.; Xie, W.; Qian, W.; Zhou, A. Security and privacy in cloud computing: A survey. In Proceedings of the 2010 Sixth International Conference on Semantics Knowledge and Grid (SKG), Beijing, China, 1–3 November 2010; pp. 105–112. [Google Scholar]
- Chen, D.; Zhao, H. Data security and privacy protection issues in cloud computing. In Proceedings of the 2012 International Conference on Computer Science and Electronics Engineering (ICCSEE), Hangzhou, China, 23–25 March 2012; Volume 1, pp. 647–651. [Google Scholar]
- Helland, P. Condos and Clouds. Commun. ACM 2013, 56, 50–59. [Google Scholar] [CrossRef]
- Martins, P.; Sousa, L.; Mariano, A. A survey on fully homomorphic encryption: An engineering perspective. ACM Comput. Surv. (CSUR) 2017, 50, 83. [Google Scholar] [CrossRef]
- Rong, C.; Nguyen, S.T.; Jaatun, M.G. Beyond lightning: A survey on security challenges in cloud computing. Comput. Electr. Eng. 2013, 39, 47–54. [Google Scholar] [CrossRef]
- Ren, K.; Wang, C.; Wang, Q. Security Challenges for the Public Cloud. IEEE Internet Comput. 2012, 16, 69–73. [Google Scholar] [CrossRef]
- di Vimercati, S.D.C.; Foresti, S.; Livraga, G.; Paraboschi, S.; Samarati, P. Confidentiality Protection in Large Databases. In A Comprehensive Guide Through the Italian Database Research Over the Last 25 Years; Springer: Berlin/Heidelberg, Germany, 2018; pp. 457–472. [Google Scholar]
- Tari, Z. Security and Privacy in Cloud Computing. IEEE Cloud Comput. 2014, 1, 54–57. [Google Scholar] [CrossRef]
- Islam, M.S.; Kuzu, M.; Kantarcioglu, M. Access Pattern disclosure on Searchable Encryption: Ramification, Attack and Mitigation. In Proceedings of the 19th Annual Network and Distributed System Security Symposium, NDSS 2012, San Diego, CA, USA, 5–8 February 2012; The Internet Society. Available online: https://pdfs.semanticscholar.org/9614/87973d4b33f96406fddbfcf1235dc587571f.pdf (accessed on 4 June 2019).
- Baumann, A.; Peinado, M.; Hunt, G. Shielding applications from an untrusted cloud with haven. ACM Trans. Comput. Syst. (TOCS) 2015, 33, 8. [Google Scholar] [CrossRef]
- Pearson, S. Privacy, security and trust in cloud computing. In Privacy and Security for Cloud Computing; Springer: Berlin/Heidelberg, Germany, 2013; pp. 3–42. [Google Scholar]
- Jasti, A.; Shah, P.; Nagaraj, R.; Pendse, R. Security in multi-tenancy cloud. In Proceedings of the 44th Annual 2010 IEEE International Carnahan Conference on Security Technology, San Jose, CA, USA, 5–8 October 2010; pp. 35–41. [Google Scholar] [CrossRef]
- Tsai, H.Y.; Siebenhaar, M.; Miede, A.; Huang, Y.; Steinmetz, R. Threat as a Service? Virtualization’s Impact on Cloud Security. IT Prof. 2012, 14, 32–37. [Google Scholar] [CrossRef]
- Milenkoski, A.; Payne, B.D.; Antunes, N.; Vieira, M.; Kounev, S. HInjector: Injecting hypercall attacks for evaluating VMI-based intrusion detection systems. In Proceedings of the 2013 Annual Computer Security Applications Conference (ACSAC 2013), New Orleans, LA, USA, 9–13 December 2013. [Google Scholar]
- Perez-Botero, D.; Szefer, J.; Lee, R.B. Characterizing Hypervisor Vulnerabilities in Cloud Computing Servers. In Proceedings of the 2013 International Workshop on Security in Cloud Computing, Hangzhou, China, 8 May 2013; ACM: New York, NY, USA, 2013; pp. 3–10. [Google Scholar] [CrossRef]
- Liao, X.; Alrwais, S.; Yuan, K.; Xing, L.; Wang, X.; Hao, S.; Beyah, R. Lurking Malice in the Cloud: Understanding and Detecting Cloud Repository As a Malicious Service. In Proceedings of the 2016 ACM SIGSAC Conference on Computer and Communications Security, Vienna, Austria, 24–28 October 2016; ACM: New York, NY, USA, 2016; pp. 1541–1552. [Google Scholar] [CrossRef]
- Wang, C.; Ren, K.; Wang, J. Secure and practical outsourcing of linear programming in cloud computing. In Proceedings of the 2011 Proceedings IEEE INFOCOM, Shanghai, China, 10–15 April 2011; pp. 820–828. [Google Scholar]
- Wei, L.; Zhu, H.; Cao, Z.; Dong, X.; Jia, W.; Chen, Y.; Vasilakos, A.V. Security and privacy for storage and computation in cloud computing. Inf. Sci. 2014, 258, 371–386. [Google Scholar] [CrossRef]
- Jensen, M.; Schwenk, J.; Gruschka, N.; Iacono, L.L. On technical security issues in cloud computing. In Proceedings of the IEEE International Conference on Cloud Computing, Bangalore, India, 21–25 September 2009; pp. 109–116. [Google Scholar]
- Karnwal, T.; Sivakumar, T.; Aghila, G. A comber approach to protect cloud computing against XML DDoS and HTTP DDoS attack. In Proceedings of the 2012 IEEE Students’ Conference on Electrical, Electronics and Computer Science (SCEECS), Bhopal, India, 1–2 March 2012; pp. 1–5. [Google Scholar]
- Ahuja, S.P.; Komathukattil, D. A survey of the state of cloud security. Netw. Commun. Technol. 2012, 1, 66. [Google Scholar] [CrossRef][Green Version]
- Stanislav, M.; Beardsley, T. Hacking Iot: A Case Study on Baby Monitor Exposures and Vulnerabilities. Technical Report. Available online: https://www.rapid7.com/ (accessed on 4 June 2019).
- Cachin, C.; Keidar, I.; Shraer, A. Trusting the Cloud. SIGACT News 2009, 40, 81–86. [Google Scholar] [CrossRef]
- Wang, C.; Wang, Q.; Ren, K.; Cao, N.; Lou, W. Toward secure and dependable storage services in cloud computing. IEEE Trans. Serv. Comput. 2012, 5, 220–232. [Google Scholar] [CrossRef]
- Syam Kumar, P.; Subramanian, R. An efficient and secure protocol for ensuring data storage security in Cloud Computing. IJCSI Int. J. Comput. Sci. Issues 2011, 8, 261. [Google Scholar]
- Zafar, F.; Khan, A.; Malik, S.U.R.; Ahmed, M.; Anjum, A.; Khan, M.I.; Javed, N.; Alam, M.; Jamil, F. A survey of cloud computing data integrity schemes: Design challenges, taxonomy and future trends. Comput. Secur. 2017, 65, 29–49. [Google Scholar] [CrossRef]
- Varadarajan, V.; Kooburat, T.; Farley, B.; Ristenpart, T.; Swift, M.M. Resource-freeing Attacks: Improve Your Cloud Performance (at Your Neighbor’s Expense). In Proceedings of the 2012 ACM Conference on Computer and Communications Security, Raleigh, NC, USA, 16–18 October 2012; ACM: New York, NY, USA, 2012; pp. 281–292. [Google Scholar] [CrossRef]
- Luo, S.; Lin, Z.; Chen, X.; Yang, Z.; Chen, J. Virtualization security for cloud computing service. In Proceedings of the 2011 International Conference onCloud and Service Computing (CSC), Hong Kong, China, 12–14 December 2011; pp. 174–179. [Google Scholar]
- Dabrowsk, C.; Mills, K. VM leakage and orphan control in open-source clouds. In Proceedings of the 2011 IEEE Third International Conference on Cloud Computing Technology and Science (CloudCom), Athens, Greece, 29 November–1 December 2011; pp. 554–559. [Google Scholar]
- Zhou, F.; Goel, M.; Desnoyers, P.; Sundaram, R. Scheduler Vulnerabilities and Coordinated Attacks in Cloud Computing. J. Comput. Secur. 2013, 21, 533–559. [Google Scholar] [CrossRef]
- Alarifi, S.; Wolthusen, S.D. Robust Coordination of Cloud-Internal Denial of Service Attacks. In Proceedings of the 2013 International Conference on Cloud and Green Computing, Karlsruhe, Germany, 30 September–2 October 2013; pp. 135–142. [Google Scholar] [CrossRef]
- Atya, A.O.F.; Qian, Z.; Krishnamurthy, S.V.; Porta, T.L.; McDaniel, P.; Marvel, L. Malicious co-residency on the cloud: Attacks and defense. In Proceedings of the IEEE INFOCOM 2017—IEEE Conference on Computer Communications, Atlanta, GA, USA, 1–4 May 2017; pp. 1–9. [Google Scholar] [CrossRef]
- Moon, S.J.; Sekar, V.; Reiter, M.K. Nomad: Mitigating arbitrary cloud side channels via provider-assisted migration. In Proceedings of the 22nd ACM Sigsac Conference on Computer and Communications Security, Denver, CO, USA, 12–16 October 2015; ACM: New York, NY, USA, 2015; pp. 1595–1606. [Google Scholar]
- Atya, A.; Aqil, A.; Khalil, K.; Qian, Z.; Krishnamurthy, S.V.; La Porta, T.F. Stalling Live Migrations on the Cloud. In Proceedings of the 11th USENIX Workshop on Offensive Technologies (WOOT 17), Vancouver, BC, Canada, 14–15 August 2017. [Google Scholar]
- Wang, Y.; Ma, J.; Lu, D.; Lu, X.; Zhang, L. From high-availability to collapse: Quantitative analysis of “Cloud-Droplet-Freezing” attack threats to virtual machine migration in cloud computing. Clust. Comput. 2014, 17, 1369–1381. [Google Scholar] [CrossRef]
- Liu, H. A New Form of DOS Attack in a Cloud and Its Avoidance Mechanism. In Proceedings of the 2010 ACM Workshop on Cloud Computing Security Workshop, Chicago, IL, USA, 8 October 2010; ACM: New York, NY, USA, 2010; pp. 65–76. [Google Scholar] [CrossRef]
- Somani, G.; Gaur, M.S.; Sanghi, D.; Conti, M.; Buyya, R. DDoS attacks in cloud computing: Issues, taxonomy, and future directions. Comput. Commun. 2017, 107, 30–48. [Google Scholar] [CrossRef]
- Ficco, M.; Rak, M. Economic Denial of Sustainability Mitigation in Cloud Computing. In Organizational Innovation and Change; Rossignoli, C., Gatti, M., Agrifoglio, R., Eds.; Springer International Publishing: Cham, Switerland, 2016; pp. 229–238. [Google Scholar]
- Somani, G.; Gaur, M.S.; Sanghi, D. DDoS/EDoS attack in cloud: Affecting everyone out there! In Proceedings of the 8th International Conference on Security of Information and Networks, Sochi, Russia, 8–10 September 2015; ACM: New York, NY, USA, 2015; pp. 169–176. [Google Scholar]
- Ficco, M.; Palmieri, F. Introducing fraudulent energy consumption in cloud infrastructures: A new generation of denial-of-service attacks. IEEE Syst. J. 2017, 11, 460–470. [Google Scholar] [CrossRef]
- Coppolino, L.; D’Antonio, S.; Mazzeo, G.; Romano, L. Cloud security: Emerging threats and current solutions. Comput. Electr. Eng. 2017, 59, 126–140. [Google Scholar] [CrossRef]
- Kim, D.; Vouk, M.A. A survey of common security vulnerabilities and corresponding countermeasures for SaaS. In Proceedings of the Globecom Workshops (GC Wkshps), Austin, TX, USA, 8–12 December 2014; pp. 59–63. [Google Scholar]
- Gupta, S.; Gupta, B.B. Cross-Site Scripting (XSS) attacks and defense mechanisms: classification and state-of-the-art. Int. J. Syst. Assur. Eng. Manag. 2017, 8, 512–530. [Google Scholar] [CrossRef]
- Putthacharoen, R.; Bunyatnoparat, P. Protecting cookies from cross site script attacks using dynamic cookies rewriting technique. In Proceedings of the 2011 13th International Conference on Advanced Communication Technology (ICACT), Seoul, Korea, 13–16 February 2011; pp. 1090–1094. [Google Scholar]
- Morrow, B. BYOD security challenges: Control and protect your most sensitive data. Netw. Secur. 2012, 2012, 5–8. [Google Scholar] [CrossRef]
- Sood, A.K.; Enbody, R.J. Targeted cyberattacks: A superset of advanced persistent threats. IEEE Secur. Priv. 2013, 11, 54–61. [Google Scholar]
- Chen, P.; Desmet, L.; Huygens, C. A Study on Advanced Persistent Threats. In Communications and Multimedia Security; De Decker, B., Zúquete, A., Eds.; Springer: Berlin/Heidelberg, Germany, 2014; pp. 63–72. [Google Scholar]
- Caviglione, L.; Podolski, M.; Mazurczyk, W.; Ianigro, M. Covert Channels in Personal Cloud Storage Services: The Case of Dropbox. IEEE Trans. Ind. Inform. 2017, 13, 1921–1931. [Google Scholar] [CrossRef]
- Xiao, L.; Xu, D.; Xie, C.; Mandayam, N.B.; Poor, H.V. Cloud Storage Defense Against Advanced Persistent Threats: A Prospect Theoretic Study. IEEE J. Sel. Areas Commun. 2017, 35, 534–544. [Google Scholar] [CrossRef]
- Shahriar, H.; Zulkernine, M. Client-side detection of cross-site request forgery attacks. In Proceedings of the 2010 IEEE 21st International Symposium on Software Reliability Engineering (ISSRE), San Jose, CA, USA, 1–4 November 2010; pp. 358–367. [Google Scholar]
- Siddiqui, M.S.; Verma, D. Cross site request forgery: A common web application weakness. In Proceedings of the 2011 IEEE 3rd International Conference on Communication Software and Networks (ICCSN), Xi’an, China, 27–29 May 2011; pp. 538–543. [Google Scholar]
- Livshits, V.B.; Lam, M.S. Finding Security Vulnerabilities in Java Applications with Static Analysis. In Proceedings of the 14th USENIX Security Symposium, Baltimore, MD, USA, 31 July–5 August 2005. [Google Scholar]
- You, P.; Peng, Y.; Liu, W.; Xue, S. Security issues and solutions in cloud computing. In Proceedings of the 2012 32nd International Conference on Distributed Computing Systems Workshops (ICDCSW), Macau, China, 18–21 June 2012; pp. 573–577. [Google Scholar]
- Chapade, S.; Pandey, K.; Bhade, D. Securing cloud servers against flooding based DDoS attacks. In Proceedings of the 2013 International Conference on Communication Systems and Network Technologies (CSNT), Gwalior, India, 6–8 April 2013; pp. 524–528. [Google Scholar]
- Zargar, S.T.; Joshi, J.; Tipper, D. A survey of defense mechanisms against distributed denial of service (DDoS) flooding attacks. IEEE Commun. Surv. Tutor. 2013, 15, 2046–2069. [Google Scholar] [CrossRef]
- De Donno, M.; Dragoni, N.; Giaretta, A.; Spognardi, A. Analysis of DDoS-capable IoT malwares. In Proceedings of the 2017 Federated Conference on Computer Science and Information Systems, Prague, Czech Republic, 3–6 September 2017. [Google Scholar]
- Badis, H.; Doyen, G.; Khatoun, R. Understanding botclouds from a system perspective: A principal component analysis. In Proceedings of the 2014 IEEE Network Operations and Management Symposium (NOMS), Krakow, Poland, 5–9 May 2014; pp. 1–9. [Google Scholar]
- Yan, Q.; Yu, F.R.; Gong, Q.; Li, J. Software-defined networking (SDN) and distributed denial of service (DDoS) attacks in cloud computing environments: A survey, some research issues, and challenges. IEEE Commun. Surv. Tutor. 2016, 18, 602–622. [Google Scholar] [CrossRef]
- Kolias, C.; Kambourakis, G.; Stavrou, A.; Voas, J. DDoS in the IoT: Mirai and Other Botnets. Computer 2017, 50, 80–84. [Google Scholar] [CrossRef]
- Osanaiye, O.; Choo, K.K.R.; Dlodlo, M. Distributed denial of service (DDoS) resilience in cloud: Review and conceptual cloud DDoS mitigation framework. J. Netw. Comput. Appl. 2016, 67, 147–165. [Google Scholar] [CrossRef]
- Dantas, Y.G.; Nigam, V.; Fonseca, I.E. A Selective Defense for Application Layer DDoS Attacks. In Proceedings of the 2014 IEEE Joint Intelligence and Security Informatics Conference, The Hague, The Netherlands, 24–26 September 2014; pp. 75–82. [Google Scholar] [CrossRef]
- Jensen, M.; Gruschka, N.; Herkenhöner, R. A survey of attacks on web services. Comput. Sci. Res. Dev. 2009, 24, 185. [Google Scholar] [CrossRef]
- Singh, K.; Singh, P.; Kumar, K. Application layer HTTP-GET flood DDoS attacks: Research landscape and challenges. Comput. Secur. 2017, 65, 344–372. [Google Scholar] [CrossRef]
- Choi, J.; Choi, C.; Ko, B.; Kim, P. A method of DDoS attack detection using HTTP packet pattern and rule engine in cloud computing environment. Soft Comput. 2014, 18, 1697–1703. [Google Scholar] [CrossRef]
- Zhao, Y.; Liu, Y.; Yu, Y.; Li, Y. Blockchain based Privacy-Preserving Software Updates with Proof-of-Delivery for Internet of Things. arXiv 2019, arXiv:1902.03712. [Google Scholar]
- Yu, Y.; Li, Y.; Tian, J.; Liu, J. Blockchain-Based Solutions to Security and Privacy Issues in the Internet of Things. IEEE Wirel. Commun. 2018, 25, 12–18. [Google Scholar] [CrossRef]
- Rullo, A.; Bertino, E.; Saccà, D. PAST: Protocol-Adaptable Security Tool for Heterogeneous IoT Ecosystems. In Proceedings of the IEEE Conference on Dependable and Secure Computing, DSC 2018, Kaohsiung, Taiwan, 10–13 December 2018; pp. 1–8. [Google Scholar]
- Giura, P.; Jim, T. Sapphire: Using Network Gateways for IoT Security. In Proceedings of the 8th International Conference on the Internet of Things, Santa Barbara, CA, USA, 15–18 October 2018; ACM: New York, NY, USA, 2018; pp. 5:1–5:8. [Google Scholar]
- Kong, Q.; Lu, R.; Ma, M.; Bao, H. A privacy-preserving sensory data sharing scheme in Internet of Vehicles. Future Gener. Comp. Syst. 2019, 92, 644–655. [Google Scholar] [CrossRef]
- Fazio, M.; Ranjan, R.; Girolami, M.; Taheri, J.; Dustdar, S.; Villari, M. A Note on the Convergence of IoT, Edge, and Cloud Computing in Smart Cities. IEEE Cloud Comput. 2018, 5, 22–24. [Google Scholar] [CrossRef]
- Dragoni, N.; Massacci, F.; Saidane, A. A Self-protecting and Self-healing Framework for Negotiating Services and Trust in Autonomic Communication Systems. Comput. Netw. 2009, 53, 1628–1648. [Google Scholar] [CrossRef]
- Guidi, C.; Lanese, I.; Mazzara, M.; Montesi, F. Microservices: A Language-Based Approach. In Present and Ulterior Software Engineering; Mazzara, M., Meyer, B., Eds.; Springer International Publishing: Cham, Switerland, 2017; pp. 217–225. [Google Scholar]
- Yan, Z.; Cimpian, E.; Zaremba, M.; Mazzara, M. BPMO: Semantic Business Process Modeling and WSMO Extension. In Proceedings of the 2007 IEEE International Conference on Web Services (ICWS 2007), Salt Lake City, UT, USA, 9–13 July 2007; pp. 1185–1186. [Google Scholar]
- Mazzara, M. Towards Abstractions for Web Services Composition. Ph.D. Thesis, University of Bologna, Bologna, Italy, 2006. [Google Scholar]
- Dragoni, N.; Mazzara, M. A Formal Semantics for the WS-BPEL Recovery Framework—The pi-Calculus Way; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2009; Volume 6194, pp. 92–109. [Google Scholar]

| Architectural Level | Issues | Confidentiality | Integrity | Availability | Exploited/Victim(Cloud, IoT Devices, Both) |
|---|---|---|---|---|---|
| Virtualization | Multi-tenancy | ✓ | ✓ | Cloud/IoT devices | |
| VM isolation | ✓ | ✓ | ✓ | Cloud/IoT devices | |
| Virtual network | ✓ | ∼ | ✓ | Both/Both | |
| VM introspection | ✓ | Cloud/IoT devices | |||
| VM management | ✓ | ✓ | ✓ | Cloud/Both | |
| VM migration | ✓ | ✓ | ✓ | Both/IoT devices | |
| Application | Isolation | ✓ | ✓ | ∼ | Cloud/IoT devices |
| Synchronization mechanisms | ✓ | ✓ | ∼ | Both/IoT devices | |
| Insecure APIs, management and control interfaces | ∼ | ✓ | ∼ | Both/Both | |
| Resource accounting | ✓ | IoT devices/Cloud | |||
| Network | Network under-provision | ✓ | Both/Both | ||
| Data Storage | Outsourcing | ✓ | ✓ | Cloud/IoT devices | |
| Data deletion | ✓ | Cloud/IoT devices | |||
| Multi-level | Economic sustainability | ✓ | Both/IoT devices |
| Architectural Level | Issues | Confidentiality | Integrity | Availability | Exploited/Victim(Cloud, IoT Devices, Both) |
|---|---|---|---|---|---|
| Network | Man In The Middle (MITM) attack | ✓ | ✓ | ✓ | Both/Both |
| DDoS attack | ✓ | Both/Both | |||
| Application | Cross-site scripting (XSS) attack | ✓ | ∼ | Cloud/IoT devices | |
| Injection flaws | ✓ | ✓ | ✓ | Cloud/Both | |
| Man in the Browser (MitB) attack | ✓ | ✓ | ∼ | IoT devices/Both | |
| Cross-site request forgery (CSRF) attack | ∼ | ✓ | Cloud/IoT devices | ||
| Hidden field manipulation and cookie poisoning | ∼ | ✓ | Cloud/IoT devices | ||
| XML Signature Element Wrapping | ∼ | ✓ | Cloud/Both | ||
| Metadata Spoofing attack | ∼ | ✓ | ∼ | Cloud/Both | |
| Application-bug level DoS attack | ✓ | Both/Both | |||
| Flooding DoS attack | ✓ | Both/Both | |||
| Multi-level | Advanced Persistent threats | ✓ | ∼ | ∼ | Both/Both |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
De Donno, M.; Giaretta, A.; Dragoni, N.; Bucchiarone, A.; Mazzara, M. Cyber-Storms Come from Clouds: Security of Cloud Computing in the IoT Era. Future Internet 2019, 11, 127. https://doi.org/10.3390/fi11060127
De Donno M, Giaretta A, Dragoni N, Bucchiarone A, Mazzara M. Cyber-Storms Come from Clouds: Security of Cloud Computing in the IoT Era. Future Internet. 2019; 11(6):127. https://doi.org/10.3390/fi11060127
Chicago/Turabian StyleDe Donno, Michele, Alberto Giaretta, Nicola Dragoni, Antonio Bucchiarone, and Manuel Mazzara. 2019. "Cyber-Storms Come from Clouds: Security of Cloud Computing in the IoT Era" Future Internet 11, no. 6: 127. https://doi.org/10.3390/fi11060127
APA StyleDe Donno, M., Giaretta, A., Dragoni, N., Bucchiarone, A., & Mazzara, M. (2019). Cyber-Storms Come from Clouds: Security of Cloud Computing in the IoT Era. Future Internet, 11(6), 127. https://doi.org/10.3390/fi11060127







