Wireless Mesh Networking: An IoT-Oriented Perspective Survey on Relevant Technologies
Abstract
1. Introduction
2. Preliminaries on Routing Protocols for Ad-hoc Networks
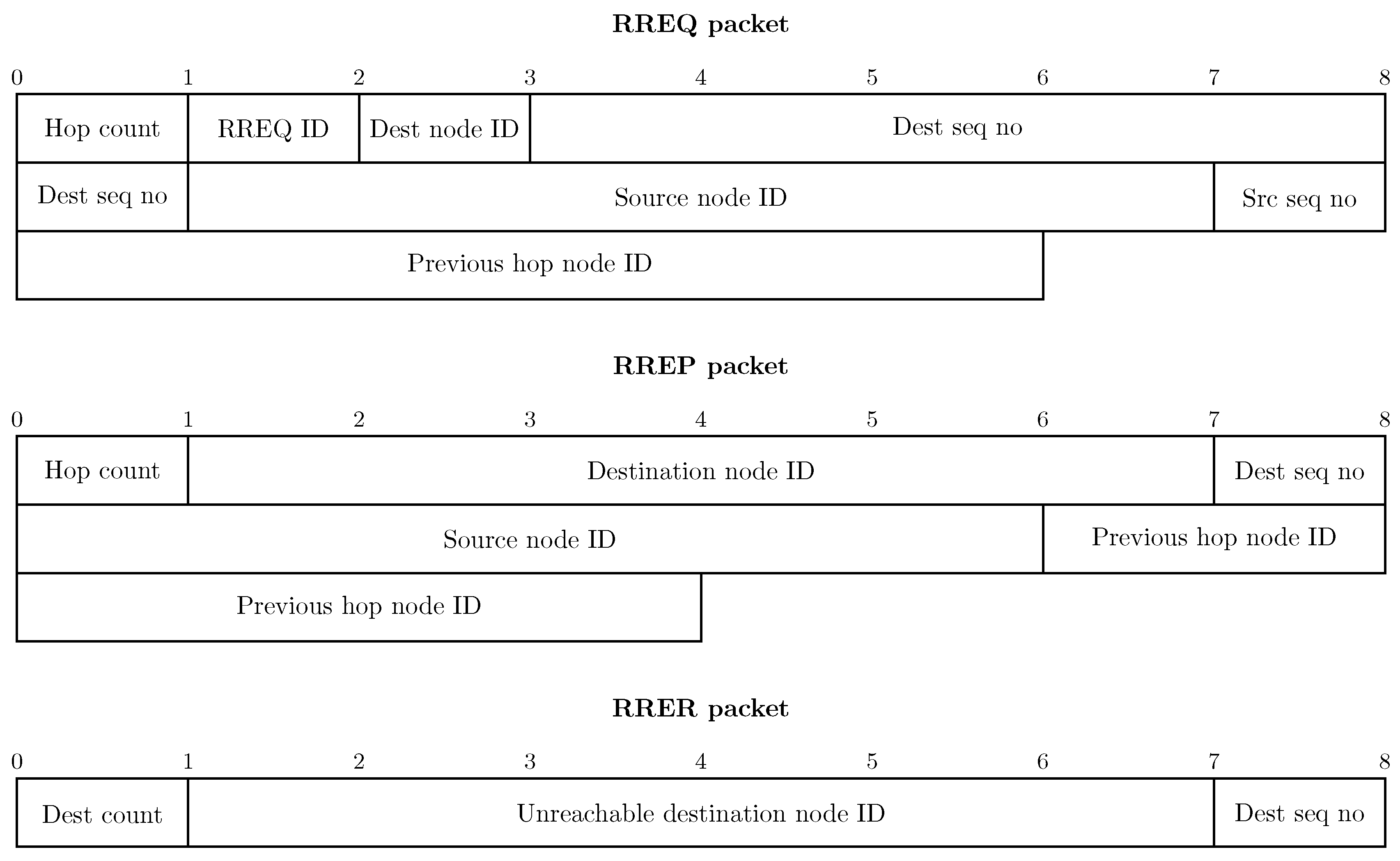
2.1. Ad hoc On-Demand Distance Vector Routing Protocol
- The source node S broadcasts a Route REQuest (RREQ) packet, whose main fields are the destination address and hop counter, to its n neighbors , , ⋯, .
- Upon reception of a RREQ packet, a node checks if the packet contains routing information related to the destination. If so, it rebroadcasts the RREQ increasing the hop counter. If the node itself is the destination of the packet, it replies to the source with a Route REPly (RREP) message.
- Finally, the source node S builds its routing table on the basis of the received RREP messages, storing the next-hop to each destination, and uses this information for following transmissions.
2.2. Optimized Link State Routing (OLSR) Protocol
2.3. Dynamic Source Routing (DSR) Protocol
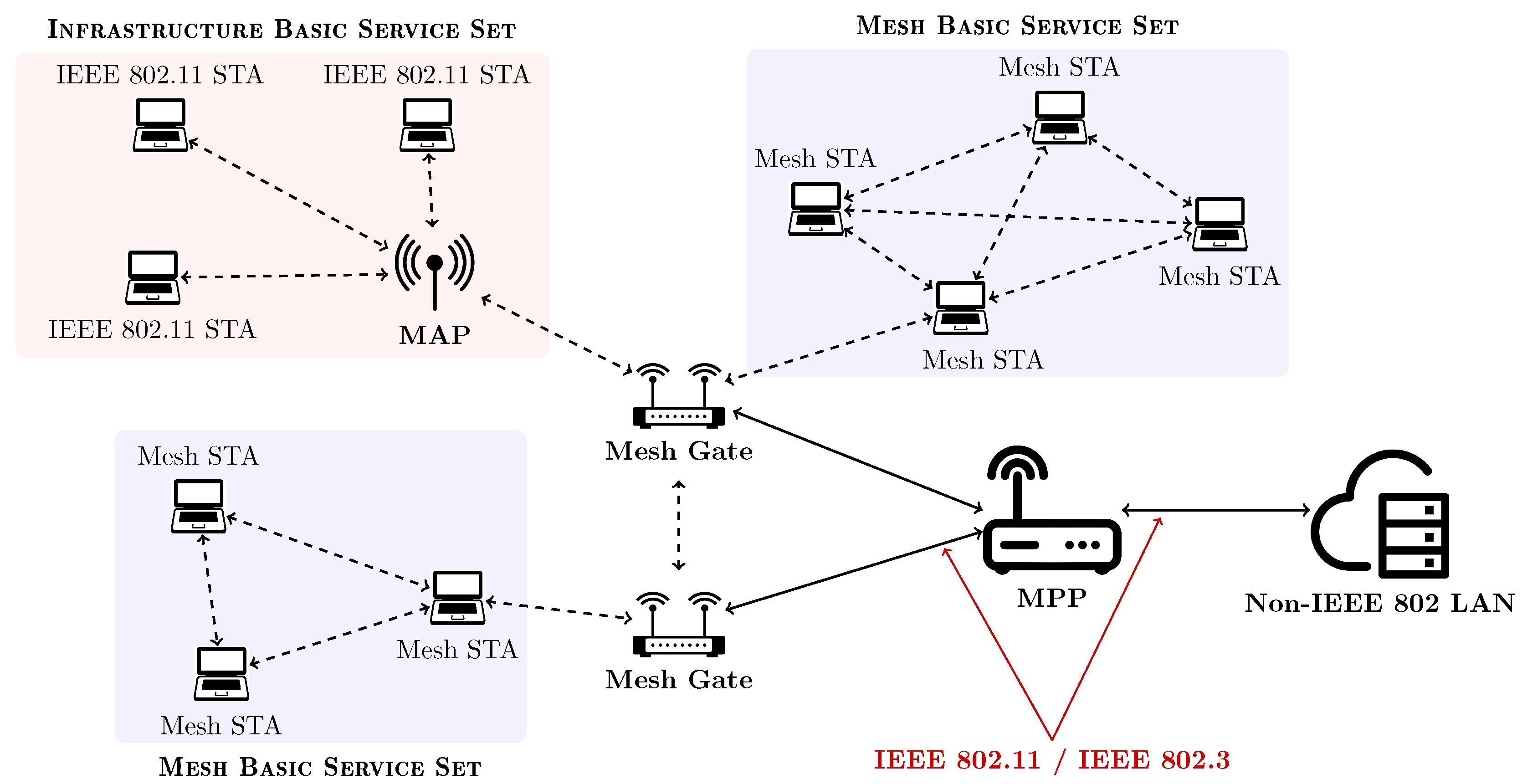
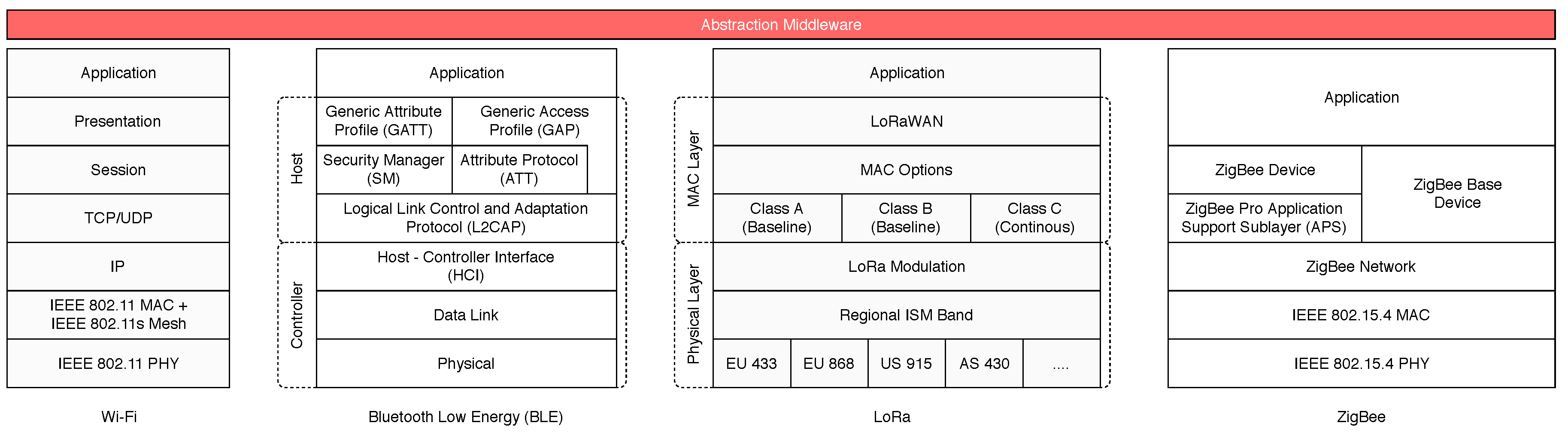
3. Mesh in IEEE 802.11 Networks
3.1. Standard: IEEE 802.11s
3.1.1. IEEE 802.11s Basics
3.1.2. IEEE 802.11s Topology Formation
3.1.3. IEEE 802.11s Routing Algorithm
3.2. Other Solutions
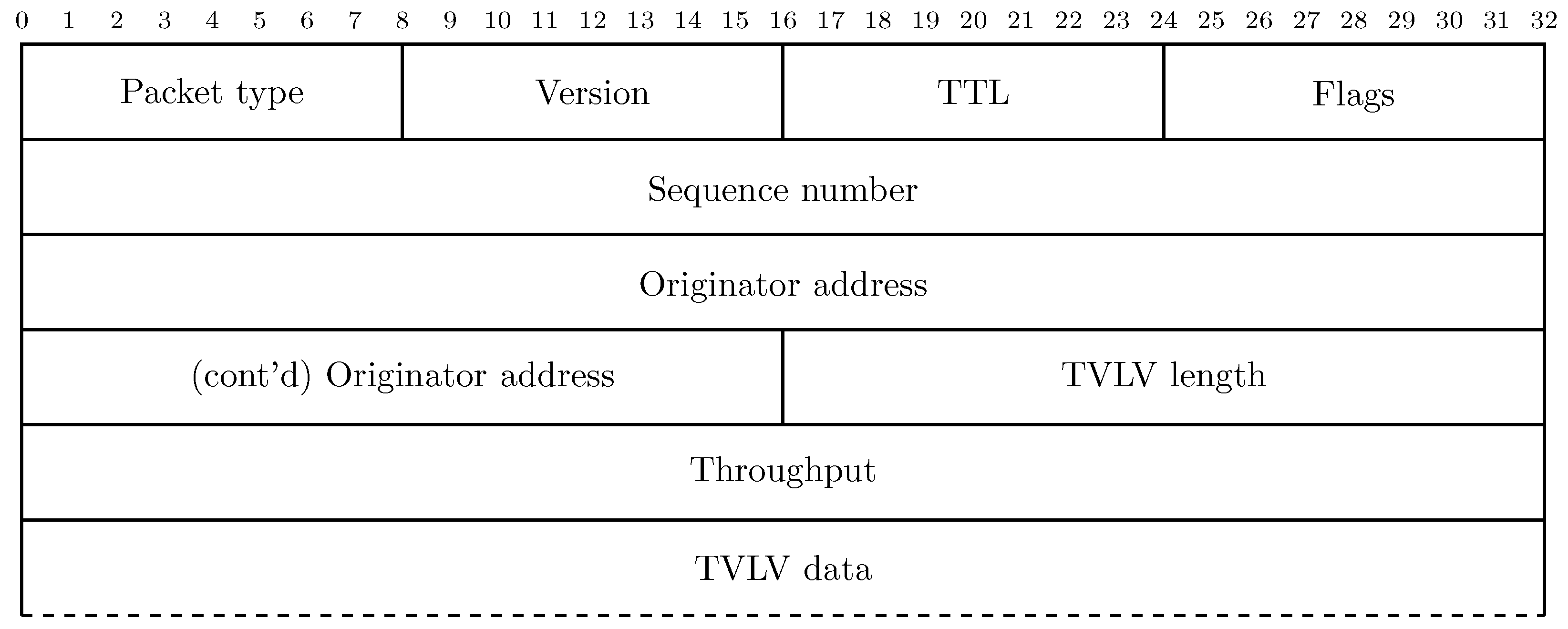
3.2.1. Better Approach To Mobile Ad-hoc Networks (B.A.T.M.A.N.)
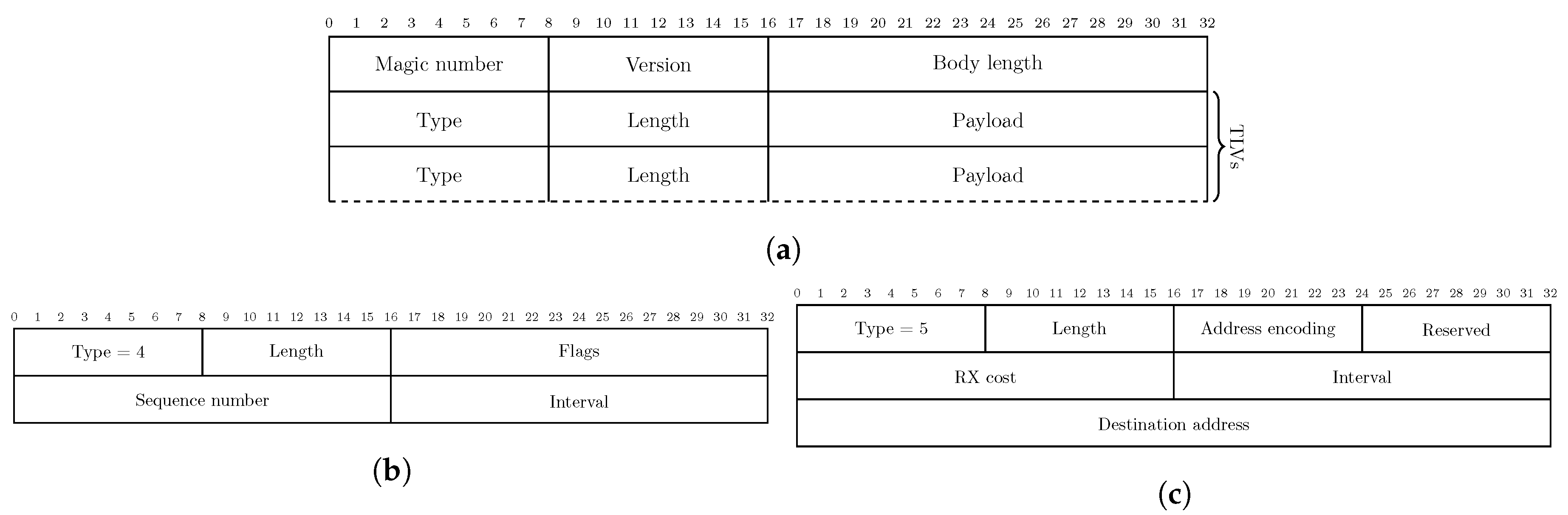
3.2.2. Babel Routing Protocol
3.3. Applications
4. Mesh in Bluetooth/BLE Networks
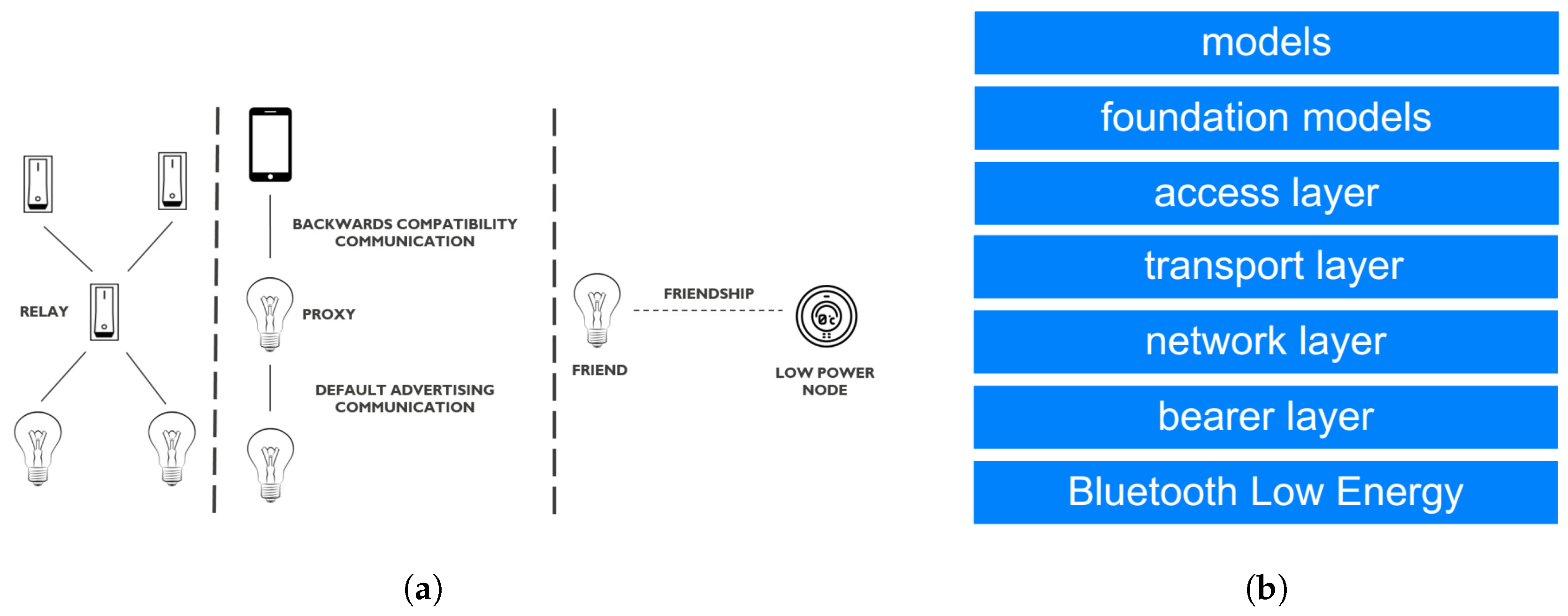
4.1. Standard
- Unicast address, identifying a single element or a node in the network in a unique way. A unicast address is assigned to a device during the provisioning process, when it becomes part of the network.
- Group address, corresponding to a multicast address able to represent either a single element or node, as well as multiple elements or nodes. Moreover, group addresses can be either assigned dynamically (i.e., established by the user via a configuration application), as well as fixed by the official SIG group (in this case, denoted as SIG Fixed Group Addresses).
- Virtual address, corresponding to a 128-bit UUID that can be assigned to either one or more elements, as well as to a single or multiple nodes.
- Relay feature: since the scalability and the robustness of the network can be reduced, if not properly managed, by the adoption of the flooding mechanism (as required by the standard), then, in order to avoid inefficiencies, the relay feature requires that only relay-enabled nodes in the network are allowed to forward received messages further in the network. Another additional features are the message cache and the Time-To-Live (TTL) field, which ensure that a a message M will be relayed by a device N only once. In fact, N only relays M if: (i) M is not already stored in the cache memory of the device N and (ii) the TTL value proper of the message M is greater than 1. Moreover, each time M is relayed further into the network, then its TTL field value is decreased by 1.
- Proxy feature: this feature has been defined aiming at maintaining compatibility with all BLE devices not supporting Bluetooth Mesh. A node N with the proxy feature enabled can perform communication in two ways: (i) employing the default BLE mesh advertising method, and (ii) using the backwards compatibility feature that is based on traditional BLE connections.
- Friendship and Low-Power feature: since the standard forces nodes to scan advertisement channels with a 100% duty cycle, this strongly affects the low-energy aspect of BLE advertising precluding the use of mesh networking in all power-constrained applications. The friendship feature has been introduced to overcome this limitation, allowing a power-limited device P to join the mesh network without the 100% duty cycle. Another, not constrained, node N can establish a friendship relationship with P becoming its friend. In the mesh network, friend nodes are in charge to store and to relay further all incoming messages. Then, the low-power node P can ask to N for new messages with a rate compatible with its reduced duty cycle, and limiting its power usage.
- Bluetooth Low Energy Core Specification layer: this bottom layer provides basic wireless communications capabilities on top of which the whole mesh architecture is built (either using connection-oriented and advertising mechanisms).
- Bearer layer: this layer defines the interfaces (also denoted as “bearers”) between the underlying core specification and the upper layers, through two interfaces: the (i) ADV bearer, managing the BLE advertisement processes, and (ii) the GATT bearer, managing BLE connections.
- Network layer: this layer implements security aspects and defines the various message address types and a network message format which is employed in the bearer layer.
- Transport layer: this layer manages both segmentation and reassembly of larger messages into the original message, thus passing them to the Application level.
- Access layer: works as an interface between the application-oriented layers above and the technology-oriented layers below. The main aim of the Access layer is to guarantee the correctness of all messages exchange between lower layers and application layer.
4.2. Other Solutions
4.3. Applications
4.4. Issues
5. Mesh Networking with IEEE 802.15.4
5.1. Reference Standard: ZigBee Pro & ZigBee 3.0
- Coordinator: each ZigBee Pro network can contain one and only one coordinator. This node is started before the other since it is responsible for network formation. The coordinator, in fact, selects the frequency channel to use and manages the operations related to the join of new child nodes in the network. After the establishment of the network, the coordinator performs routing-related activities, relaying messages among the nodes, sending and receiving messages.
- Router: is another type of node with routing capabilities. It sends and receives data, and allows other child nodes to join the mesh network. A ZigBee-based network can contain several routers which must always be available to maintain routing among nodes.
- End device: is a node which simply sends or receives data to or from its parent node, without routing functionality. Since end devices can be battery-powered, when they are not transmitting or receiving data, they can sleep in order to preserve power; hence, messages addressed to a sleeping end device E will be buffered by the parent node until E awakens. A ZigBee network can comprise many end devices, which cannot have child nodes, since they cannot relay messages or admit new nodes in the network.
- Device discovery: returns to the requesting node the addresses of a network node. If the node starting the request is the network coordinator or a router, it may supply the addresses on behalf of all the devices that are under its control, in addition to its own address [55]. In this way, all devices in a network can be discovered with a request from the coordinator to all children, in a recursive way [56].
- Route discovery: allows to know the best available route for an outgoing message from a source to the destination node. If a route already exists, the message is routed along it; otherwise, the routing node sending the message (which can be, as already mentioned, the coordinator or an intermediate router) initiates the discovery procedure that, once completed, returns the calculated route along which the outgoing message will be sent. In detail, a route discovery procedure involves the following steps: (i) the parent of the source end device () sends a broadcast discovery request with the end device’s network address; (ii) the parent of the destination end device () receives the broadcast discovery request, and sends back a reply addressed to ; and (iii) when the reply message is forwarded back through the ZigBee Pro network, the number of hops a measure of each hop signal quality are recorded. In this way, each routing node composing the path can store a routing table entry containing the best path to which generally, is the one with the smallest number of hops. Thanks to this strategy, unidirectional routes from a source to a destination end device are built. This means that the reverse routes (from to ), must be discovered starting a new route discovery round.
5.2. Other solutions
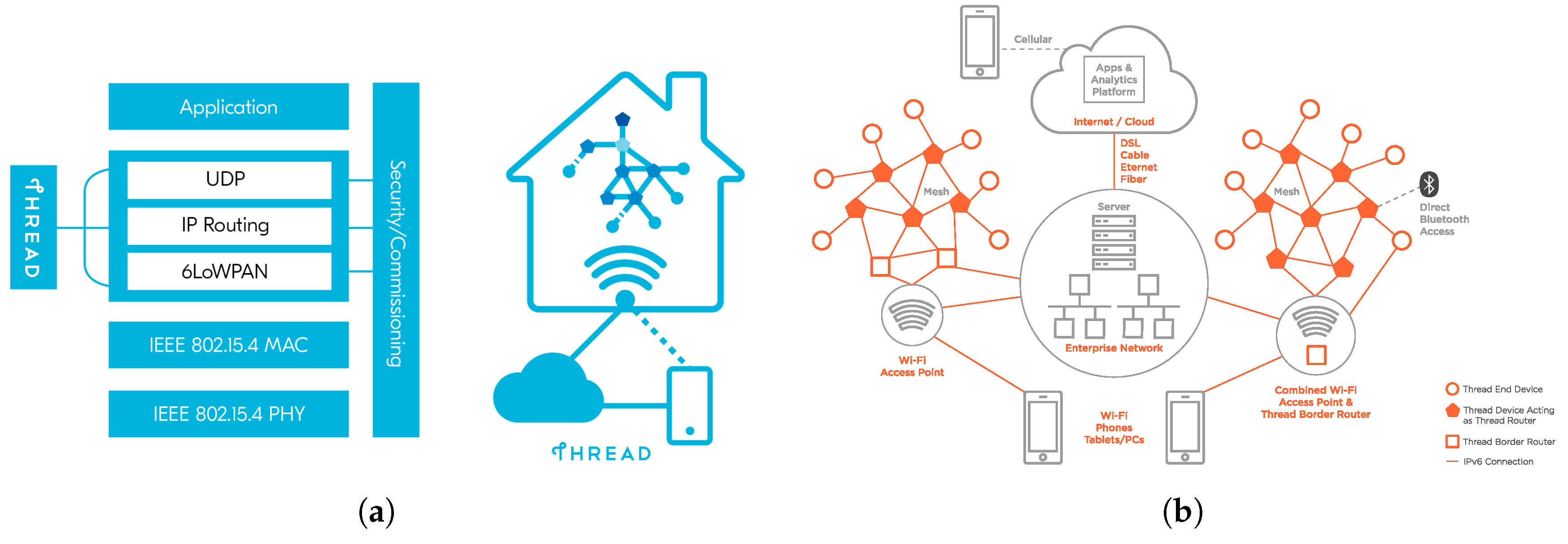
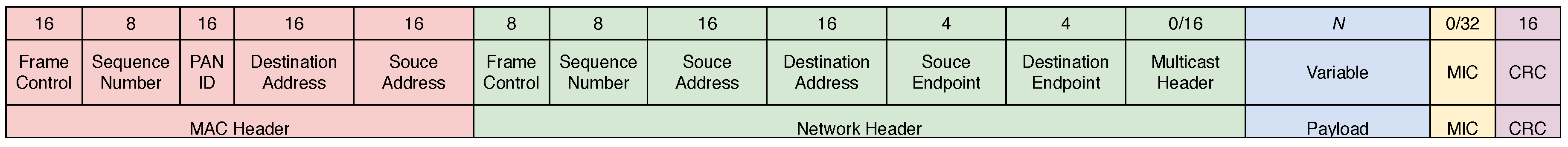
5.2.1. Thread
- Thread presents a small and low-consumption footprint, interoperable and scalable up to a huge number of devices, thus being reliable and secure, avoiding single bottlenecks and failure points.
- Thread presents a flexible intermediate layer allowing the device-to-device communication across all networks.
- Thread provides a security layer admitting to join a Thread-based network only to authenticated devices, thus encrypting the traffic flowing inside the network and including built-in link-layer authorization policies.
- Thread is able to expand its controlled network (composed by low-power nodes) to external networks (e.g., either based on IEEE 802.11 or IEEE 802.3) or to the Internet, through the adoption of border routers.
- Thread allows the inclusion of battery-powered nodes into a Thread-handled network, avoiding frequent coin-cell changes and, in this way, allowing those that people use every day—such as thermostats and lighting controls.
5.2.2. Lightweight Mesh (LWMesh)
- Native routing: since, through this mechanism, LWMesh performs route discovery without any additional structure, then the native routing algorithm is not able to guarantee the optimality of discovered routes.
- AODV routing: as introduced in Section 2.1, this is a standard routing algorithm using additional commands to perform route discovery, which might take longer time, but able to guarantee optimality in the discovered routes and to cope with groups of nodes.
Native Routing
5.3. Applications: Comparison between ZigBee Pro and LWMesh Protocols
5.3.1. Application Layer Throughput
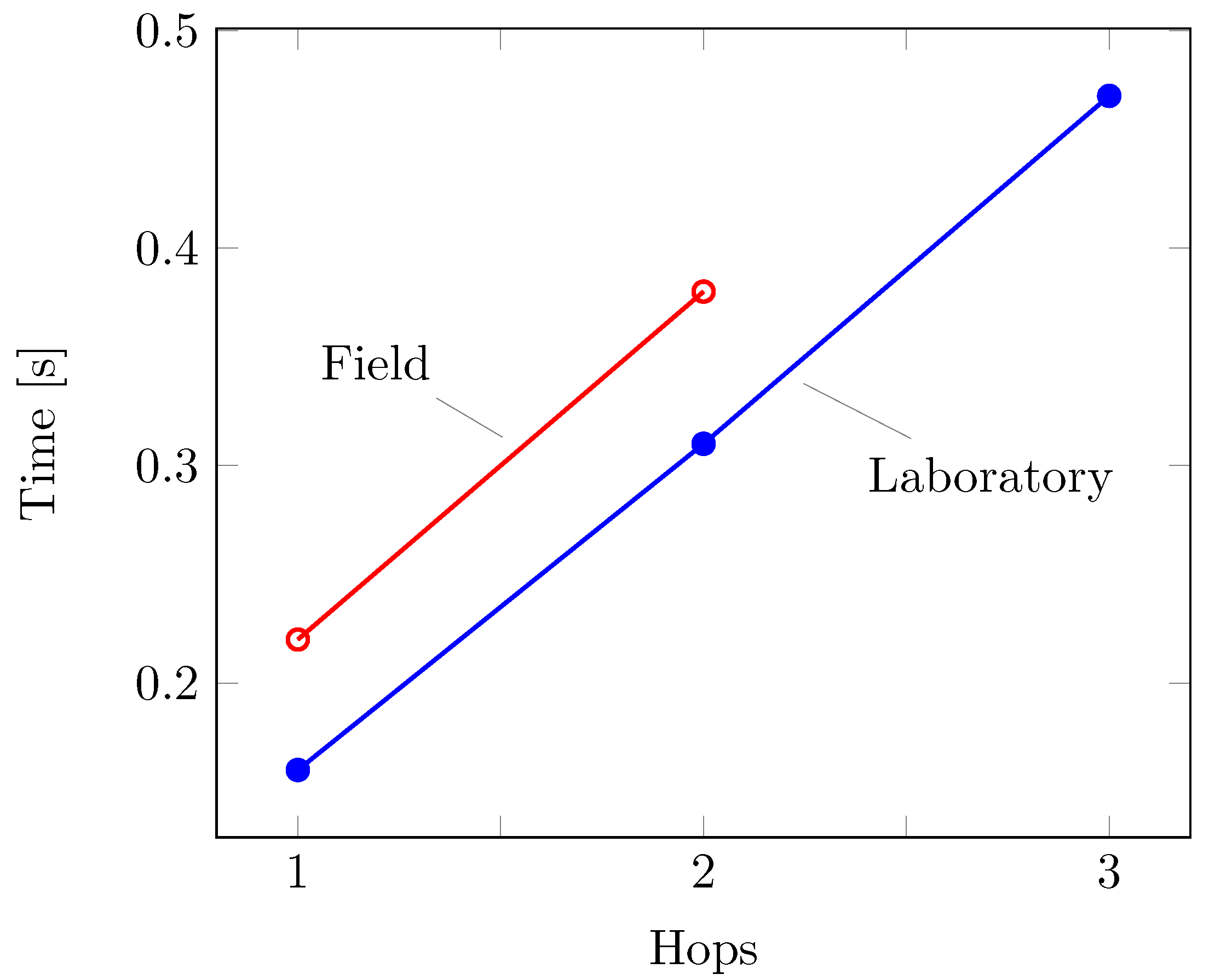
5.3.2. Routing Latency
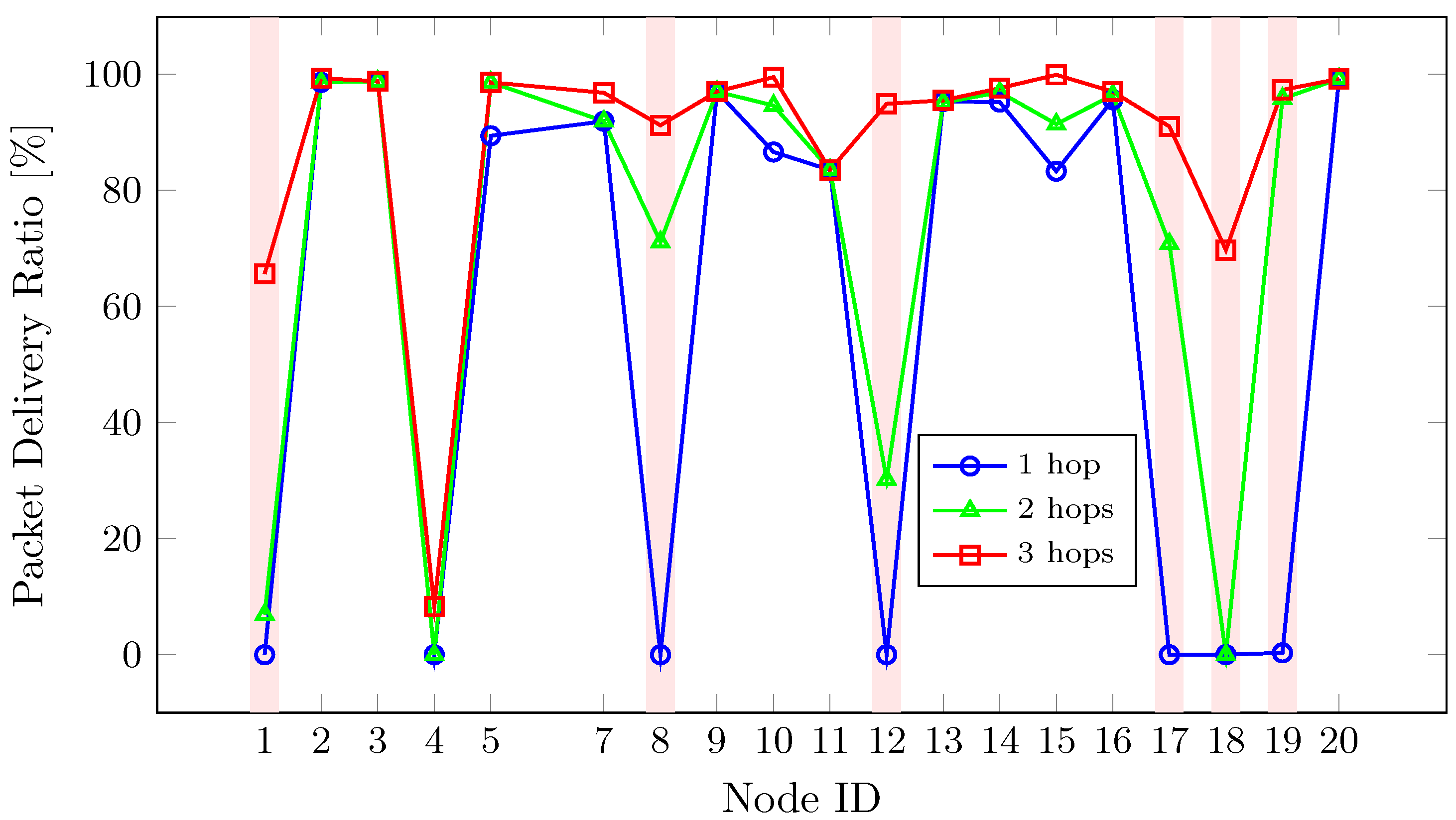
5.3.3. Self-healing Capabilities
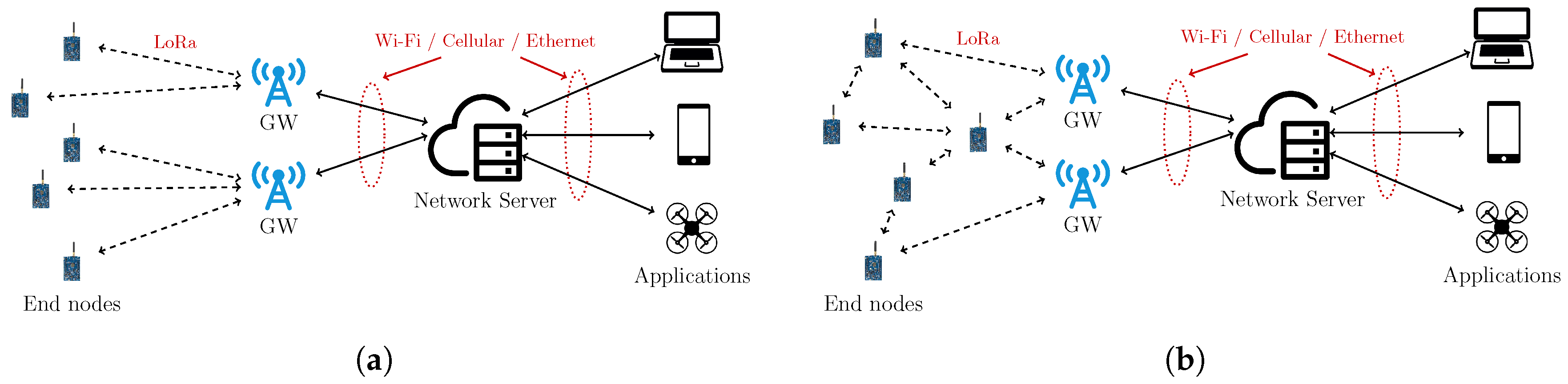
6. LoRa Mesh Networking
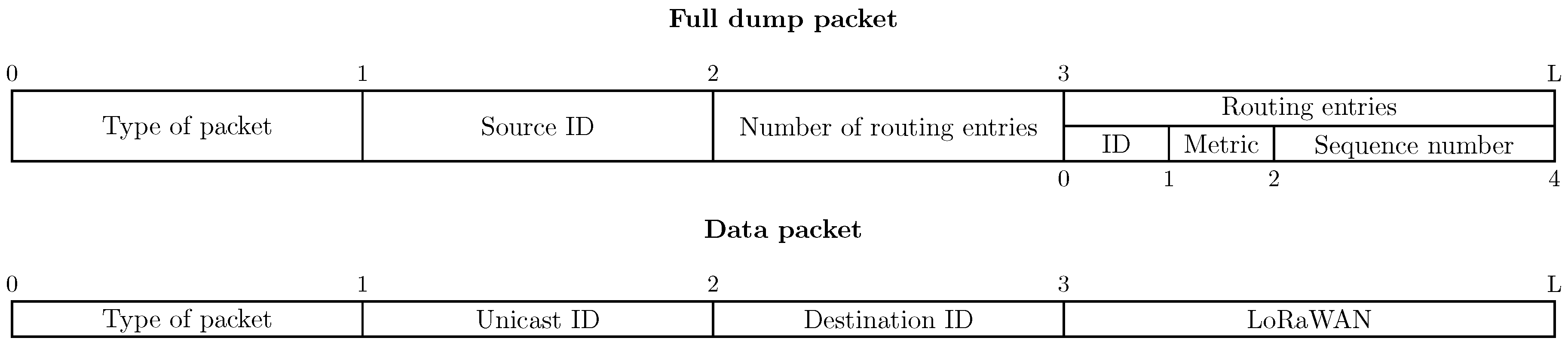
- full dumps packets, containing route informations (such as next-hop and rate/link metric)—dumps are transmitted after receiving a beacon;
- data packets, containing the actual data to be sent.
7. Ongoing and Future Developments
7.1. Smart Agriculture
7.2. Smart City
7.3. General Considerations and Future Technologies Developments
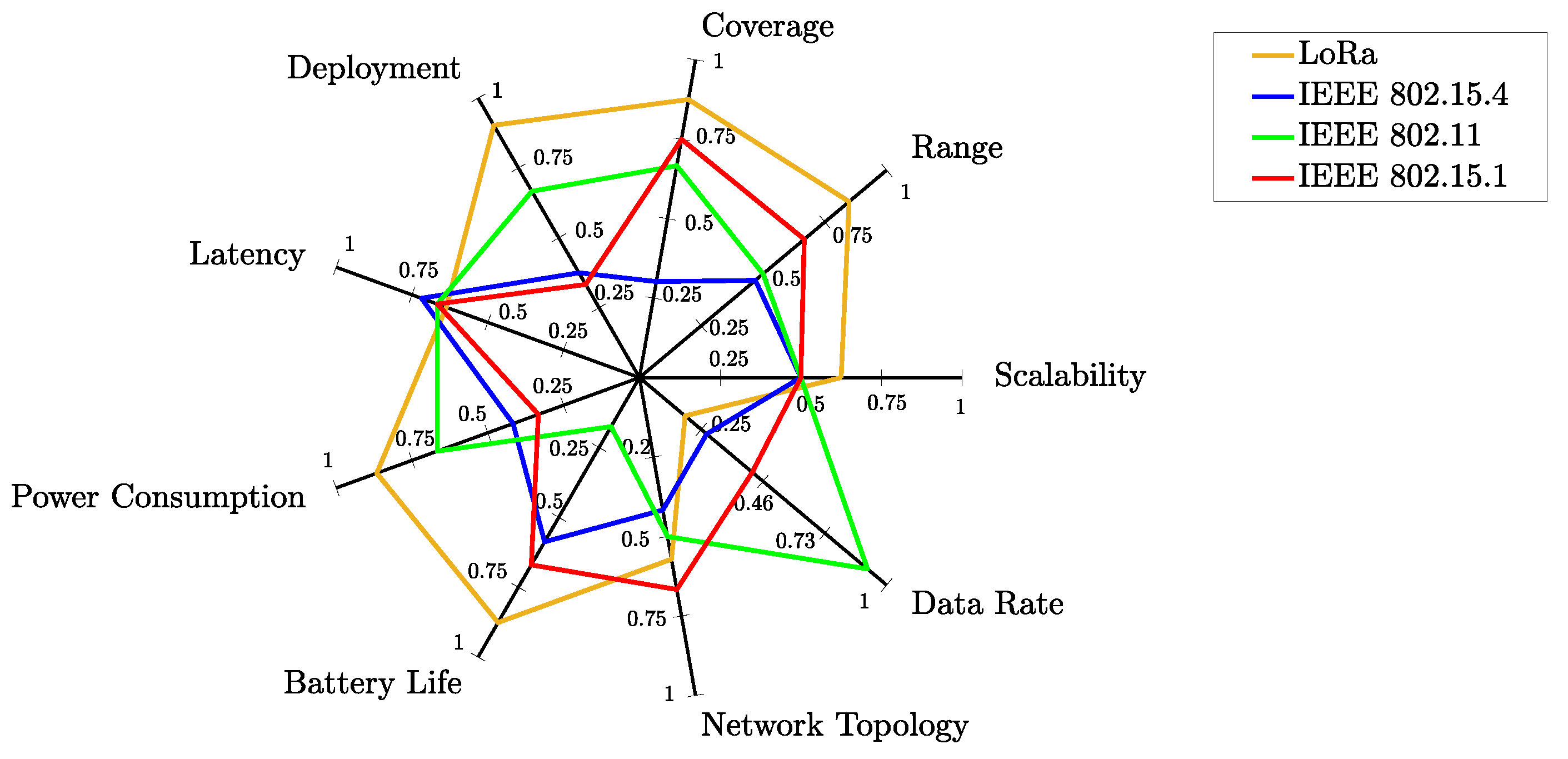
- Coverage (dimension: [m]): intended as the area which can be covered using a mesh network based on the analyzed technology.
- Range (dimension: [m]): intended as the transmission range of a single node in the mesh network.
- Scalability: intended as the capability of a mesh network, based on used wireless technology, to scale.
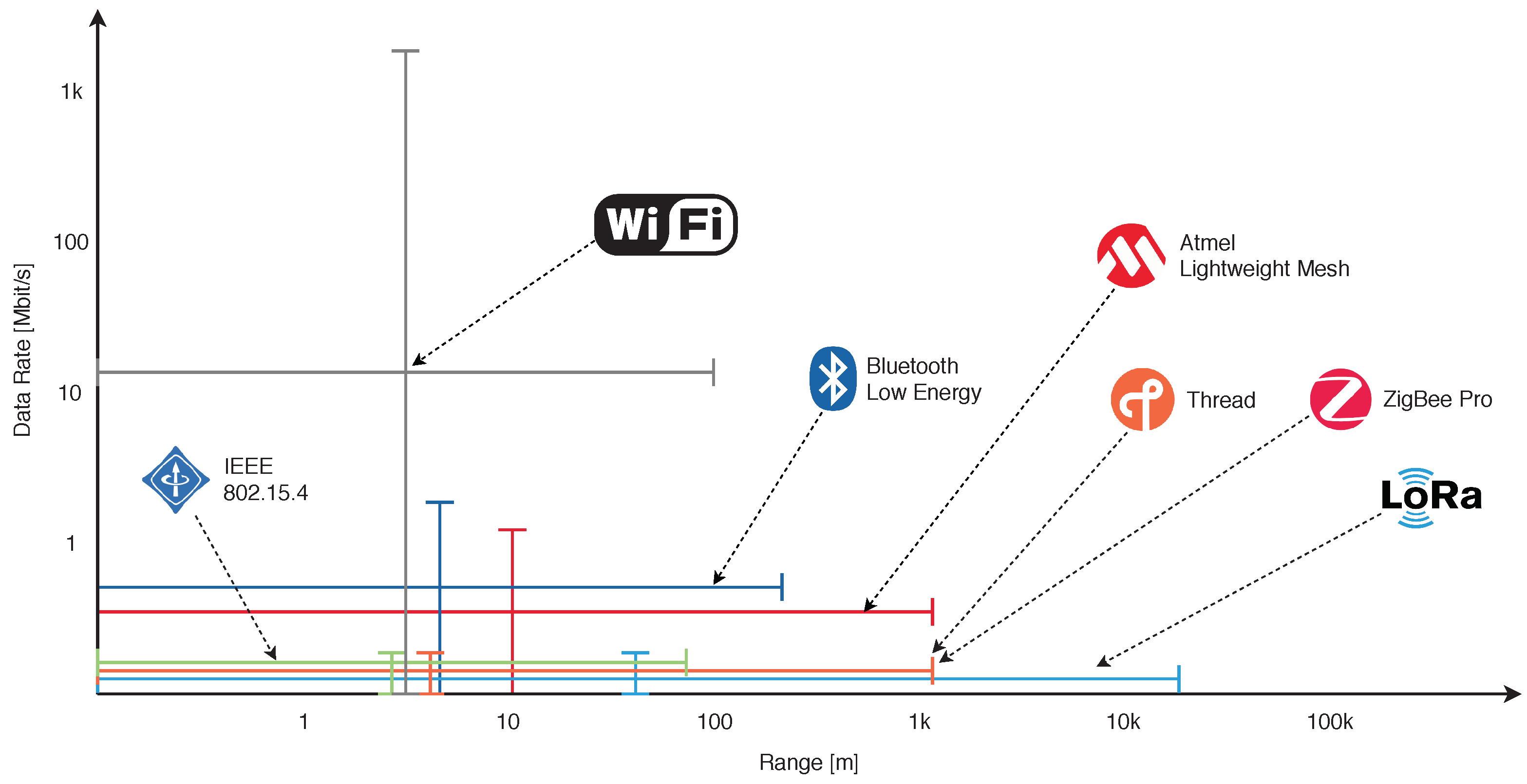
- Data Rate (dimension: [b/s]): measured on single nodes.
- Network topology: intended as the degree of complexity reachable building different network topologies.
- Battery Life (dimension: [days]): measured on single nodes.
- Power Consumption (dimension: [W]): measured on single nodes.
- Latency (dimension: [s]): intended as the capability of a technology to obtain low latencies among nodes communications.
- Deployment: intended as the complexity to deploy a mesh network based on the specific wireless technology.
8. Conclusions
Author Contributions
Funding
Conflicts of Interest
Appendix A
| LoRa | IEEE 802.15.4 | IEEE 802.11 | IEEE 802.15.1 | |||||||
|---|---|---|---|---|---|---|---|---|---|---|
| [79] | [80] | [81] | [82] | [83] | [82] | [84] | [85] | [86] | [87] | |
| Scalability | 4 | 3.5 | — | — | — | 3 | 3 | 3 | 3 | 3 |
| Range | 5.5 | 5 | 4.5 | 8 | 3.5 | — | — | 3 | 3 | 4 |
| Coverage | 5.5 | 5 | — | 7 | 1 | 3 | 3 | 4 | 4 | 4.5 |
| Deployment | 5.5 | 5.5 | — | 7 | 2 | — | — | 4 | 4 | 2 |
| Latency | 4 | 4 | 5 | 4 | 5.5 | — | — | 4 | 4 | 4 |
| Power Consumption | — | — | 6 | 7 | 4 | — | — | 4 | 4 | 2 |
| Battery Life | 5 | 5.5 | — | — | — | 3.5 | — | 1 | 1 | 4 |
| Network Topology | — | — | 4 | — | — | 2.5 | — | 3 | 3 | 4 |
| Data Rate | — | — | — | 1 | 1.5 | — | — | 5.5 | 5.5 | 2.5 |
| Max Scale () | 6 | 6 | 7 | 8 | 8 | 6 | 6 | 6 | 6 | 6 |
References
- ABI Research. The Internet of Things Will Drive Wireless Connected Devices to 40.9 Billion in 2020. Available online: https://www.abiresearch.com/press/the-internet-of-things-will-drive-wireless-connect/ (accessed on 25 March 2019).
- IHS Markit. Number of Connected IoT Devices Will Surge to 125 Billion by 2030, IHS Markit Says. Available online: https://technology.ihs.com/596542/number-of-connected-iot-devices-will-surge-to-125-billion-by-2030-ihs-markit-says (accessed on 25 March 2019).
- IDTechEx. 5G and Low-Power Wide-Area Networks 2019-2029: Global Forecasts, Technologies, Applications. Available online: https://www.idtechex.com/research/reports/5g-and-low-power-wide-area-networks-2019-2029-global-forecasts-technologies-applications-000614.asp (accessed on 25 March 2019).
- Perkins, C.E.; Bhagwat, P. Highly Dynamic Destination-Sequenced Distance-Vector Routing (DSDV) for Mobile Computers. SIGCOMM Comput. Commun. Rev. 1994, 24, 234–244. [Google Scholar] [CrossRef]
- Johnson, D.; Hu, Y.; Maltz, D. The Dynamic Source Routing Protocol (DSR) for Mobile Ad Hoc Networks for IPv4. RFC 4728, Internet Engineering Task Force. 2007. Available online: https://tools.ietf.org/html/rfc4728 (accessed on 15 April 2019).
- Perkins, C.; Belding-Royer, E.; Das, S. Ad hoc On-Demand Distance Vector (AODV) Routing. RFC 3561, Internet Engineering Task Force. 2003. Available online: https://tools.ietf.org/html/rfc3561 (accessed on 15 April 2019).
- Clausen, T.; Jacquet, P. Optimized Link State Routing Protocol (OLSR). RFC 3626, Internet Engineering Task Force, 2003. Available online: https://tools.ietf.org/html/rfc3626 (accessed on 15 April 2019).
- Institute of Electrical and Electronics Engineers (IEEE). IEEE Standard for Information Technology–Telecommunications and Information Exchange between Systems Local and Metropolitan Area Networks–Specific Requirements—Part 11: Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications; IEEE Std 802.11-2016 (Revision of IEEE Std 802.11-2012); IEEE: Piscataway, NJ, USA, 2016; pp. 1–3534. [Google Scholar] [CrossRef]
- Institute of Electrical and Electronics Engineers (IEEE). IEEE Standard for Information Technology–Telecommunications and Information Exchange between Systems–Local and Metropolitan Area Networks–Specific Requirements Part 11: Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications Amendment 10: Mesh Networking; IEEE Std 802.11s-2011; IEEE: Piscataway, NJ, USA, 2011; pp. 1–372. [Google Scholar] [CrossRef]
- Hiertz, G.R.; Denteneer, D.; Max, S.; Taori, R.; Cardona, J.; Berlemann, L.; Walke, B. IEEE 802.11s: The WLAN Mesh Standard. IEEE Wirel. Commun. 2010, 17, 104–111. [Google Scholar] [CrossRef]
- Bari, S.M.S.; Anwar, F.; Masud, M.H. Performance study of hybrid Wireless Mesh Protocol (HWMP) for IEEE 802.11s WLAN mesh networks. In Proceedings of the 2012 International Conference on Computer and Communication Engineering (ICCCE), Kuala Lumpur, Malaysia, 3–5 July 2012; pp. 712–716. [Google Scholar] [CrossRef]
- Open-Mesh. Originator Message version 2 (OGMv2). Available online: https://www.open-mesh.org/projects/batman-adv/wiki/OGMv2 (accessed on 25 March 2019).
- Chroboczek, J. The Babel Routing Protocol. RFC 6126, Internet Engineering Task Force. 2011. Available online: https://tools.ietf.org/html/rfc6126 (accessed on 15 April 2019).
- Chroboczek, J. Extension Mechanism for the Babel Routing Protocol. RFC 7557, Internet Engineering Task Force. 2015. Available online: https://tools.ietf.org/html/rfc7557 (accessed on 15 April 2019).
- Savage, D.; Ng, J.; Moore, S.; Slice, D.; Paluch, P.; White, R. Cisco’s Enhanced Interior Gateway Routing Protocol (EIGRP). RFC 7868, Internet Engineering Task Force. 2016. Available online: https://tools.ietf.org/html/rfc7868 (accessed on 15 April 2019).
- Jonglez, B.; Chroboczek, J. Delay-based Metric Extension for the Babel Routing Protocol. Internet-Draft draft-jonglez-babel-rtt-extension-02, Internet Engineering Task Force. 2019. Available online: https://tools.ietf.org/html/draft-jonglez-babel-rtt-extension-02 (accessed on 15 April 2019).
- Chouasne, G.; Chroboczek, J. TOS-Specific Routing in Babel. Internet-Draft draft-chouasne-babel-tos-specific-00, Internet Engineering Task Force. 2017. Available online: https://tools.ietf.org/html/draft-chouasne-babel-tos-specific (accessed on 15 April 2019).
- Boutier, M.; Chroboczek, J. Source-Specific Routing in Babel. Internet-Draft draft-ietf-babel-source-specific-04, Internet Engineering Task Force. 2018. Available online: https://tools.ietf.org/html/draft-ietf-babel-source-specific (accessed on 15 April 2019).
- Chroboczek, J. Applicability of the Babel Routing Protocol. Internet-Draft draft-ietf-babel-applicability-05, Internet Engineering Task Force. 2018. Available online: https://tools.ietf.org/html/draft-ietf-babel-applicability (accessed on 15 April 2019).
- Moy, J. OSPF Version 2. STD 54, Internet Engineering Task Force, 1998. Available online: https://tools.ietf.org/html/rfc2328 (accessed on 15 April 2019).
- Coltun, R.; Ferguson, D.; Moy, J.; Lindem, A. OSPF for IPv6. RFC 5340, Internet Engineering Task Force. 2008. Available online: https://tools.ietf.org/html/rfc5340 (accessed on 15 April 2019).
- Oran, D. OSI IS-IS Intra-domain Routing Protocol. RFC 1142, Internet Engineering Task Force. 1990. Available online: https://tools.ietf.org/html/rfc1142 (accessed on 15 April 2019).
- Ridolfi, M.; Van de Velde, S.; Steendam, H.; De Poorter, E. WiFi ad-hoc mesh network and MAC protocol solution for UWB indoor localization systems. In Proceedings of the 2016 Symposium on Communications and Vehicular Technologies (SCVT), Mons, Belgium, 22 November 2016; pp. 1–6. [Google Scholar] [CrossRef]
- Katila, C.J.; Di Gianni, A.; Buratti, C.; Verdone, R. Routing protocols for video surveillance drones in IEEE 802.11s Wireless Mesh Networks. In Proceedings of the 2017 European Conference on Networks and Communications (EuCNC), Oulu, Finland, 12–15 June 2017; pp. 1–5. [Google Scholar] [CrossRef]
- Zambrano, M.; Esteve, M.; Pérez, I.; Carvajal, F.; Zambrano, A.M. Situation awareness in the large forest fires response. A solution based on wireless mesh networks. In Proceedings of the 2017 IEEE 9th Latin-American Conference on Communications (LATINCOM), Guatemala City, Guatemala, 8–10 November 2017; pp. 1–6. [Google Scholar] [CrossRef]
- Muhendra, R.; Arzi, Y.H. Development of street lights controller using wifi mesh network. In Proceedings of the 2017 International Conference on Smart Cities, Automation Intelligent Computing Systems (ICON-SONICS), Yogyakarta, Indonesia, 8–10 November 2017; pp. 105–109. [Google Scholar] [CrossRef]
- Saputro, N.; Akkaya, K.; Uluagac, S. Supporting Seamless Connectivity in Drone-assisted Intelligent Transportation Systems. In Proceedings of the 2018 IEEE 43rd Conference on Local Computer Networks Workshops (LCN Workshops), Chicago, IL, USA, 1–4 October 2018; pp. 110–116. [Google Scholar] [CrossRef]
- Menouar, H.; Guvenc, I.; Akkaya, K.; Uluagac, A.S.; Kadri, A.; Tuncer, A. UAV-enabled intelligent transportation systems for the smart city: Applications and challenges. IEEE Commun. Mag. 2017, 55, 22–28. [Google Scholar] [CrossRef]
- Decristofaro, M.A.; Lansdowne, C.A.; Schlesinger, A.M. Heterogeneous Wireless Mesh Network Technology Evaluation for Space Proximity and Surface Applications. In Proceedings of the 13th SpaceOps 2014, Pasadena, CA, USA, 5–9 May 2014. [Google Scholar] [CrossRef]
- Kim, H.; Lee, J.; Jang, J.W. BLEmesh: A Wireless Mesh Network Protocol for Bluetooth Low Energy Devices. In Proceedings of the 2015 3rd International Conference on Future Internet of Things and Cloud, Rome, Italy, 24–26 August 2015; pp. 558–563. [Google Scholar] [CrossRef]
- Sirur, S.; Juturu, P.; Gupta, H.P.; Serikar, P.R.; Reddy, Y.K.; Barak, S.; Kim, B. A mesh network for mobile devices using Bluetooth low energy. In Proceedings of the 2015 IEEE SENSORS, Busan, South Korea, 1–4 November 2015; pp. 1–4. [Google Scholar] [CrossRef]
- Zenker, P.; Krug, S.; Binhack, M.; Seitz, J. Evaluation of BLE Mesh capabilities: A case study based on CSRMesh. In Proceedings of the 2016 Eighth International Conference on Ubiquitous and Future Networks (ICUFN), Vienna, Austria, 5–8 July 2016; pp. 790–795. [Google Scholar] [CrossRef]
- Prasetyo, J.A.; Yushev, A.; Sikora, A. Investigations on the performance of bluetooth enabled mesh networking. In Proceedings of the 2016 3rd International Symposium on Wireless Systems within the Conferences on Intelligent Data Acquisition and Advanced Computing Systems (IDAACS-SWS), Offenburg, Germany, 26–27 September 2016; pp. 56–61. [Google Scholar] [CrossRef]
- Bluetooth, S. Mesh Profile Specification: 1.0; Bluetooth Special Interest Group: Kirkland, WA, USA, 2017. [Google Scholar]
- Apple iBeacon. 2013. Available online: https://developer.apple.com/ibeacon/ (accessed on 15 April 2019).
- Baert, M.; Rossey, J.; Shahid, A.; Hoebeke, J. The Bluetooth mesh standard: An overview and experimental evaluation. Sensors 2018, 18, 2409. [Google Scholar] [CrossRef] [PubMed]
- Gomez, C.; Darroudi, S.; Savolainen, T.; Spoerk, M. IPv6 Mesh over BLUETOOTH(R) Low Energy using IPSP. Internet-Draft draft-ietf-6lo-blemesh-03, Internet Engineering Task Force. 2018. Available online: https://tools.ietf.org/html/draft-ietf-6lo-blemesh (accessed on 15 April 2019).
- Nieminen, J.; Savolainen, T.; Isomaki, M.; Patil, B.; Shelby, Z.; Gomez, C. IPv6 over BLUETOOTH(R) Low Energy. RFC 7668, Internet Engineering Task Force. 2015. Available online: https://tools.ietf.org/html/rfc7668 (accessed on 15 April 2019).
- Group, B.S.I. Internet Protocol Support Profile V 1.0.0; Technical Report; Bluetooth Special Interest Group: Kirkland, WA, USA, 2014. [Google Scholar]
- Silva, H.C.; Margi, C.B. Energy and performance costs evaluation for BLE mesh links. In Proceedings of the Brazilian Symposium on Computer Networks and Distributed Systems (SBRC), Campos do Jordao, Brazil, 6–10 May 2018; SBC: Porto Alegre, Brazil, 2018. [Google Scholar]
- Leonardi, L.; Patti, G.; Bello, L.L. Multi-hop Real-time Communications over Bluetooth Low Energy Industrial Wireless Mesh Networks. IEEE Access 2018, 6, 26505–26519. [Google Scholar] [CrossRef]
- Snekvik, T. nRF OpenMesh; Technical Report; Norwegian University of Science and Technology: Trondheim, Norway, 2015. [Google Scholar]
- Levis, P.; Clausen, T.; Hui, J.; Gnawali, O.; Ko, J. The Trickle Algorithm. RFC 6206, Internet Engineering Task Force. 2011. Available online: https://tools.ietf.org/html/rfc6206 (accessed on 15 April 2019).
- Murillo, Y.; Reynders, B.; Chiumento, A.; Malik, S.; Crombez, P.; Pollin, S. Bluetooth now or low energy: Should BLE mesh become a flooding or connection oriented network? In Proceedings of the 2017 IEEE 28th Annual International Symposium on Personal, Indoor, and Mobile Radio Communications (PIMRC), Montreal, QC, Canada, 8–13 October 2017; pp. 1–6. [Google Scholar] [CrossRef]
- Darroudi, S.; Gomez, C. Bluetooth low energy mesh networks: A survey. Sensors 2017, 17, 1467. [Google Scholar] [CrossRef] [PubMed]
- Trogh, J.; Plets, D.; Martens, L.; Joseph, W. Bluetooth low energy based location tracking for livestock monitoring. In Proceedings of the 8th European Conference on Precision Livestock Farming, Nantes, France, 12–14 September 2017; pp. 469–475. [Google Scholar]
- Lin, Y.W.; Lin, C.Y. An Interactive Real-Time Locating System Based on Bluetooth Low-Energy Beacon Network. Sensors 2018, 18, 1637. [Google Scholar] [CrossRef]
- Veiga, A.; Abbas, C. Proposal and Application of Bluetooth Mesh Profile for Smart Cities’ Services. Smart Cities 2019, 2, 1–19. [Google Scholar] [CrossRef]
- Zhang, B.; Wang, Y.; Wei, L.; Jin, Q.; Vasilakos, A.V. BLE mesh: A practical mesh networking development framework for public safety communications. Tsinghua Sci. Technol. 2018, 23, 333–346. [Google Scholar] [CrossRef]
- Fraga-Lamas, P.; Lopez-Iturri, P.; Celaya-Echarri, M.; Blanco-Novoa, O.; Azpilicueta, L.; Varela-Barbeito, J.; Falcone, F.; Fernández-Caramés, T.M. Design and Validation of a Bluetooth 5 Fog Computing Based Industrial CPS Architecture for Intelligent Industry 4.0 Shipyard Workshops. arXiv 2019, arXiv:1903.00713. [Google Scholar]
- Danebjer, F.; Schreiter, C. Bluetooth Mesh Interoperability Analysis; Student Paper; Lund University: Lund, Sweden, 2017. [Google Scholar]
- Zigbee PRO Mesh Protocol. Available online: https://www.zigbee.org/zigbee-for-developers/zigbee-pro/ (accessed on 22 December 2018).
- Zigbee 3.0 mesh protocol. Available online: https://www.zigbee.org/zigbee-for-developers/zigbee-3-0/ (accessed on 22 December 2018).
- ZigBee Specification—Document 053474r20. Available online: https://www.zigbee.org/download/standard-zigbee-pro-specification-2/ (accessed on 22 December 2018).
- Belli, L.; Cirani, S.; Davoli, L.; Gorrieri, A.; Mancin, M.; Picone, M.; Ferrari, G. Design and Deployment of an IoT Application-Oriented Testbed. Computer 2015, 48, 32–40. [Google Scholar] [CrossRef]
- Davoli, L.; Belli, L.; Cilfone, A.; Ferrari, G. Integration of Wi-Fi mobile nodes in a Web of Things Testbed. ICT Express 2016, 2, 95–99. [Google Scholar] [CrossRef]
- Cirani, S.; Davoli, L.; Ferrari, G.; Léone, R.; Medagliani, P.; Picone, M.; Veltri, L. A Scalable and Self-Configuring Architecture for Service Discovery in the Internet of Things. IEEE Internet Things J. 2014, 1, 508–521. [Google Scholar] [CrossRef]
- Davoli, L.; Antonini, M.; Ferrari, G. DiRPL: A RPL-Based Resource and Service Discovery Algorithm for 6LoWPANs. Appl. Sci. 2018, 9. [Google Scholar] [CrossRef]
- ZigBee PRO Stack—JN-UG-3048. Available online: https://www.nxp.com/docs/en/user-guide/JN-UG-3048.pdf (accessed on 22 December 2018).
- Salsano, S.; Veltri, L.; Davoli, L.; Ventre, P.L.; Siracusano, G. PMSR—Poor Man’s Segment Routing, a minimalistic approach to Segment Routing and a Traffic Engineering use case. In Proceedings of the NOMS 2016—2016 IEEE/IFIP Network Operations and Management Symposium, Istanbul, Turkey, 25–29 April 2016; pp. 598–604. [Google Scholar] [CrossRef]
- Thread—Official Website. Available online: https://www.threadgroup.org/BUILT-FOR-IOT/Home (accessed on 20 December 2018).
- Rzepecki, W.; Iwanecki, L.; Ryba, P. IEEE 802.15.4 Thread Mesh Network—Data Transmission in Harsh Environment. In Proceedings of the 2018 6th International Conference on Future Internet of Things and Cloud Workshops (FiCloudW), Barcelona, Spain, 6–8 August 2018; pp. 42–47. [Google Scholar] [CrossRef]
- Unwala, I.; Taqvi, Z.; Lu, J. Thread: An IoT Protocol. In Proceedings of the 2018 IEEE Green Technologies Conference (GreenTech), Austin, TX, USA, 4–6 April 2018; pp. 161–167. [Google Scholar] [CrossRef]
- OpenWeave: A Secure and Reliable Communications Backbone for the Connected Home. Available online: https://openweave.io/ (accessed on 20 December 2018).
- OMA LightweightM2M V1.0 Overview. Available online: http://www.openmobilealliance.org/wp/Overviews/lightweightm2moverview.html (accessed on 20 December 2018).
- Rao, S.; Chendanda, D.; Deshpande, C.; Lakkundi, V. Implementing LWM2M in constrained IoT devices. In Proceedings of the 2015 IEEE Conference on Wireless Sensors (ICWiSe), Melaka, Malaysia, 24–26 August 2015; pp. 52–57. [Google Scholar] [CrossRef]
- Dotdor—Official Website. Available online: https://www.zigbee.org/zigbee-for-developers/dotdot/ (accessed on 20 December 2018).
- OCF Specifications. Available online: https://openconnectivity.org/developer/specifications (accessed on 20 December 2018).
- Thread: IPv6-Based Mesh Networking for the Smart Home and Building Automation. Available online: https://www.nordicsemi.com/Products/Low-power-short-range-wireless/Thread (accessed on 22 December 2018).
- Thread: Connecting Devices Where We Live & Work. Available online: https://www.threadgroup.org/BUILT-FOR-IOT/Commercial (accessed on 22 December 2018).
- Atmel Lightweight Mesh. Available online: https://www.microchip.com/developmenttools/ProductDetails/AtmelLightweightMesh (accessed on 22 December 2018).
- Atmel Lightweight Mesh—AVR2130: Lightweight Mesh Developer Guide. Available online: https://www.microchip.com/wwwAppNotes/AppNotes.aspx?appnote=en591088 (accessed on 22 December 2018).
- Cervenka, V.; Mraz, L.; Komosny, D. Comprehensive Performance Analysis of Lightweight Mesh and Its Comparison with ZigBee Pro Technology. Wirel. Pers. Commun. 2014, 78, 1527–1538. [Google Scholar] [CrossRef]
- Bor, M.; Vidler, J.; Roedig, U. LoRa for the Internet of Things. In Proceedings of the 2016 International Conference on Embedded Wireless Systems and Networks, EWSN ’16, Graz, Austria, 15–17 February 2016; pp. 361–366. [Google Scholar]
- Lundell, D.; Hedberg, A.; Nyberg, C.; Fitzgerald, E. A Routing Protocol for LoRA Mesh Networks. In Proceedings of the 2018 IEEE 19th International Symposium on “A World of Wireless, Mobile and Multimedia Networks” (WoWMoM), Chania, Greece, 12–15 June 2018; pp. 14–19. [Google Scholar] [CrossRef]
- Lee, H.; Ke, K. Monitoring of Large-Area IoT Sensors Using a LoRa Wireless Mesh Network System: Design and Evaluation. IEEE Trans. Instrum. Meas. 2018, 67, 2177–2187. [Google Scholar] [CrossRef]
- Dias, J.; Grilo, A. LoRaWAN multi-hop uplink extension. Procedia Comput. Sci. 2018, 130, 424–431. [Google Scholar] [CrossRef]
- Davoli, L.; Belli, L.; Cilfone, A.; Ferrari, G. From Micro to Macro IoT: Challenges and Solutions in the Integration of IEEE 802.15.4/802.11 and Sub-GHz Technologies. IEEE Internet Things J. 2018, 5, 784–793. [Google Scholar] [CrossRef]
- Connectivity Now and Beyond; Exploring Cat-M1, NB-IoT, and LPWAN Connections. Available online: https://ubidots.com/blog/exploring-cat-m1-nb-iot-lpwan-connections (accessed on 27 March 2019).
- Mekki, K.; Bajic, E.; Chaxel, F.; Meyer, F. A comparative study of LPWAN technologies for large-scale IoT deployment. ICT Express 2019, 5, 1–7. [Google Scholar] [CrossRef]
- Leti Boasts of LoRa, NB-IoT-Beating LPWA-CB Tests. Available online: https://abopen.com/news/leti-boasts-of-lora-nb-iot-beating-lpwan-tests (accessed on 27 March 2019).
- Wireless Standards for IoT: WiFi, BLE, SigFox, NB-IoT and LoRa. Available online: http://wireless.ictp.it/school2017/Slides/IoTWirelessStandards.pdf (accessed on 27 March 2019).
- Diez, M. Secure Position Data Transmission for Object Tracking using LoRaWAN. Available online: https://files.ifi.uzh.ch/CSG/staff/schmitt/Extern/Theses/Matthias_Diez_MA.pdf (accessed on 27 March 2019).
- Petrosky, E.E.; Michaels, A.J.; Ridge, D.B. Network Scalability Comparison of IEEE 802.15.4 and Receiver-Assigned CDMA. IEEE Internet Things J. 2019, 1. [Google Scholar] [CrossRef]
- Casilari, E.; Florez-Lara, A.; Cano-García, J.M. Analysis of the scalability of hierarchical IEEE 802.15.4/Zigbee networks. In Proceedings of the 3rd International ICST Conference on Scalable Information Systems, INFOSCALE 2008, Vico Equense, Italy, 4–6 June 2008; p. 3. [Google Scholar] [CrossRef]
- The Role of Wi-Fi & Unlicensed Technologies in 5G. Available online: https://www.wballiance.com/the-role-of-wi-fi-unlicensed-technologies-in-5g (accessed on 27 March 2019).
- Pothuganti, K.; Chitneni, A. A Comparative Study of Wireless Protocols: Bluetooth, UWB, ZigBee, and Wi-Fi. Adv. Electron. Electr. Eng. 2014, 4, 655–662. [Google Scholar]
- MEMS and Wireless Options: User Localization in Cellular Phones. Available online: https://www.gpsworld.com/mems-and-wireless-options-user-localization-in-cellular-phones (accessed on 27 March 2019).
- Pascual, M.D.G. Indoor Location Systems Based on ZigBee Networks. Bachelor’s Thesis, Mikkeli University of Applied Sciences, Mikkeli, Finland, 2012. [Google Scholar] [CrossRef]
- Morin, E.; Maman, M.; Guizzetti, R.; Duda, A. Comparison of the Device Lifetime in Wireless Networks for the Internet of Things. IEEE Access 2017, 5, 7097–7114. [Google Scholar] [CrossRef]



© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Cilfone, A.; Davoli, L.; Belli, L.; Ferrari, G. Wireless Mesh Networking: An IoT-Oriented Perspective Survey on Relevant Technologies. Future Internet 2019, 11, 99. https://doi.org/10.3390/fi11040099
Cilfone A, Davoli L, Belli L, Ferrari G. Wireless Mesh Networking: An IoT-Oriented Perspective Survey on Relevant Technologies. Future Internet. 2019; 11(4):99. https://doi.org/10.3390/fi11040099
Chicago/Turabian StyleCilfone, Antonio, Luca Davoli, Laura Belli, and Gianluigi Ferrari. 2019. "Wireless Mesh Networking: An IoT-Oriented Perspective Survey on Relevant Technologies" Future Internet 11, no. 4: 99. https://doi.org/10.3390/fi11040099
APA StyleCilfone, A., Davoli, L., Belli, L., & Ferrari, G. (2019). Wireless Mesh Networking: An IoT-Oriented Perspective Survey on Relevant Technologies. Future Internet, 11(4), 99. https://doi.org/10.3390/fi11040099








