SLoPCloud: An Efficient Solution for Locality Problem in Peer-to-Peer Cloud Systems
Abstract
1. Introduction
- (i)
- This paper uses RTT as a metric to estimate the distance between nodes. Consequently, it proposes a locality solution referred to as SLoPCloud, to solve the mismatch problem between the overlay and physical layer. The proposed solution does not impose a serious overhead on network performance parameters, such as traffic and delay, while it could be applied to most of the well-known overlay networks.
- (ii)
- This paper suggests a flexible topology, i.e. Generalized Hypercube Connected Cycle (GHCC), to be used as an overlay layer in P2P cloud networks. GHCC is compatible with the proposed solution and could be easily converted into different well-known topologies with just a simple modification in its parameters. It is worth noting that choosing a proper graph has a considerable effect on the network performance metrics such as the bandwidth, congestion, and delay.
- (iii)
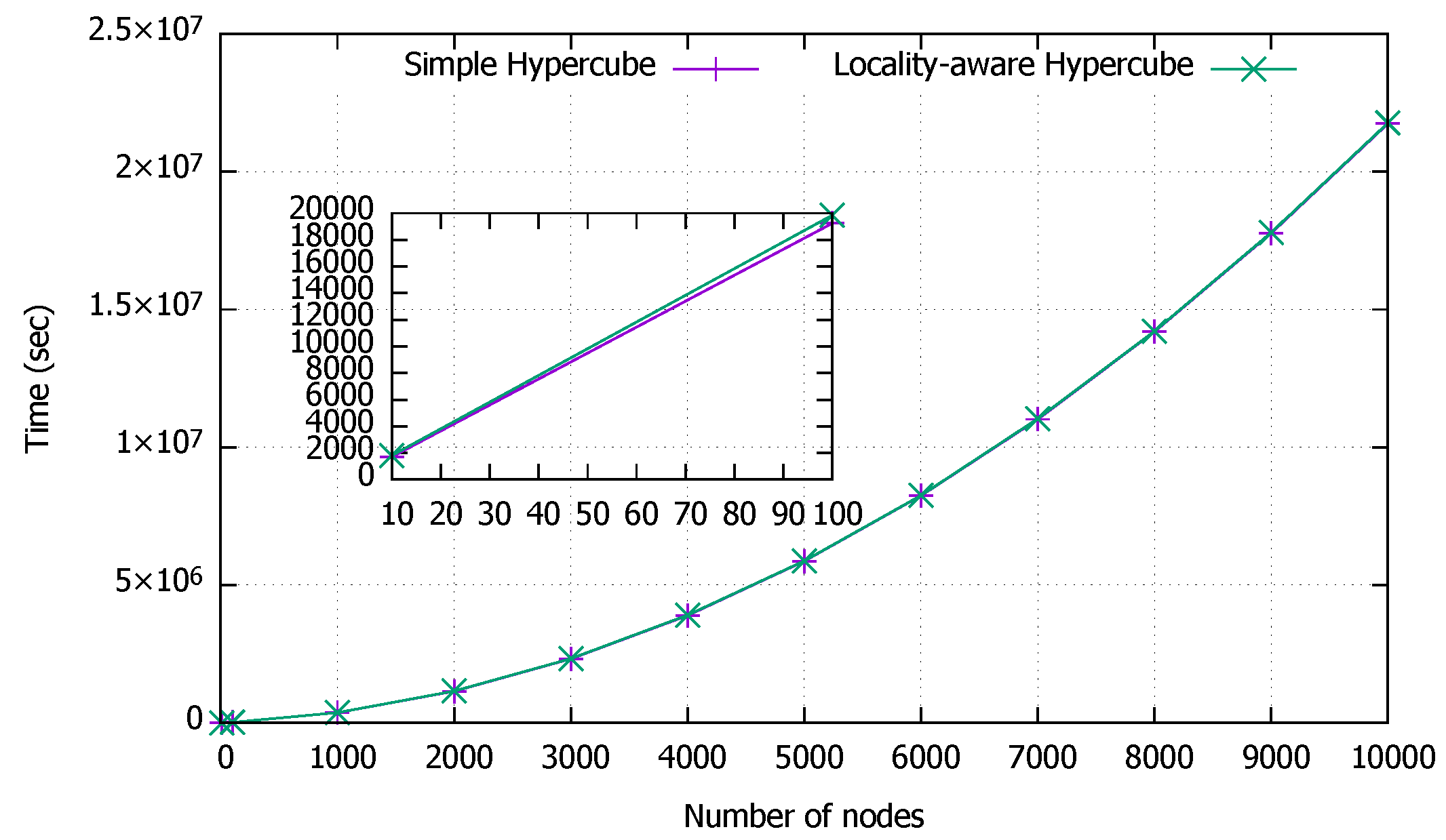
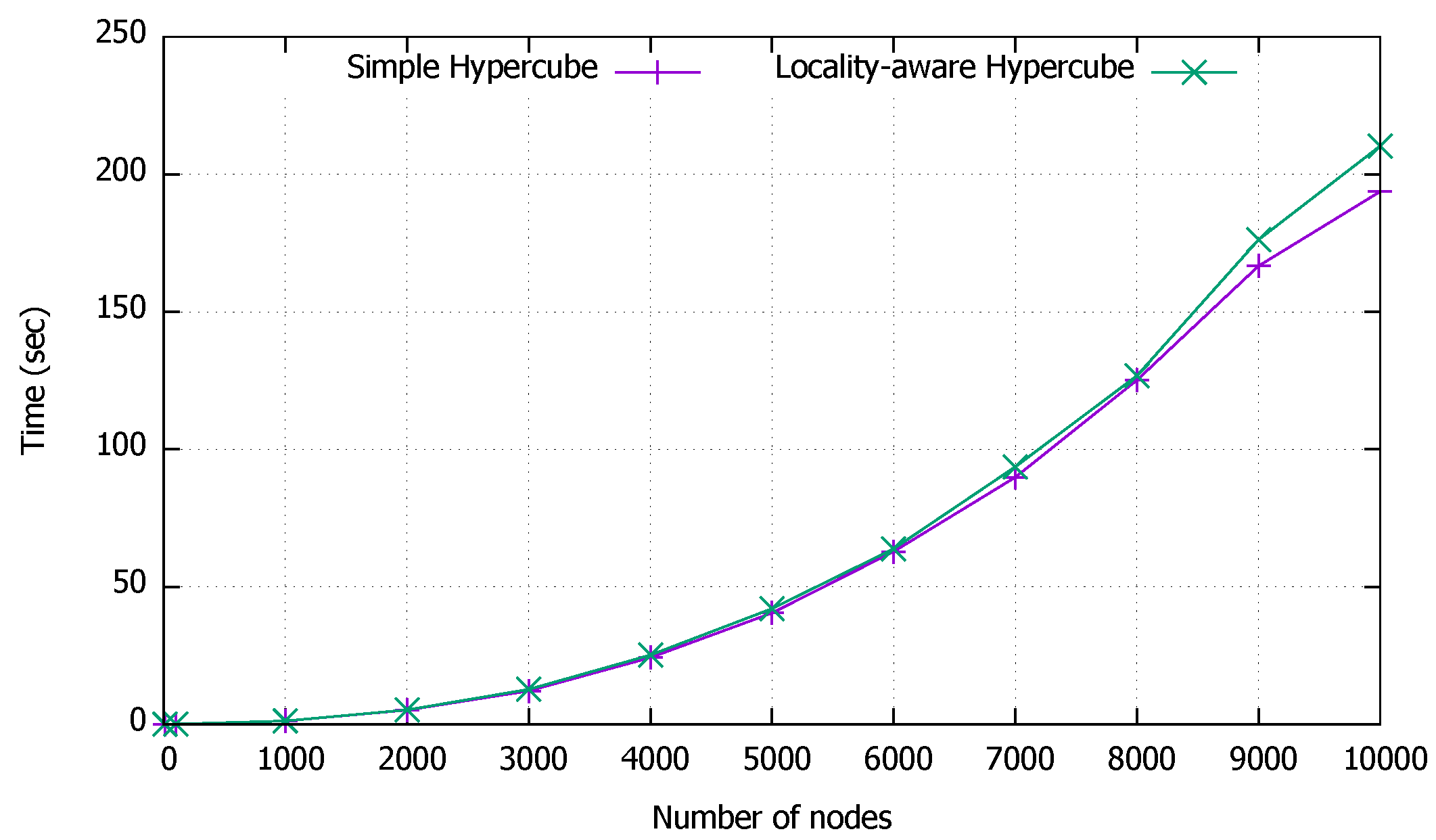
- This paper proves the performance and the scalability of the proposed solution SLoPCloud, through comprehensive simulations. Here, SLoPCloud solution has been implemented while topologies Ring, Hypercube, CCC, and GHCC are considered as the overlay network. The focus of simulation study in this paper is on the network bootstrapping time and the control traffic caused by the locality solution.
2. Related Work
2.1. P2P Networks and Locality Problem
2.2. P2P Cloud Systems
3. Background
4. Proposed Solutions for Locality Problem in P2P Cloud System
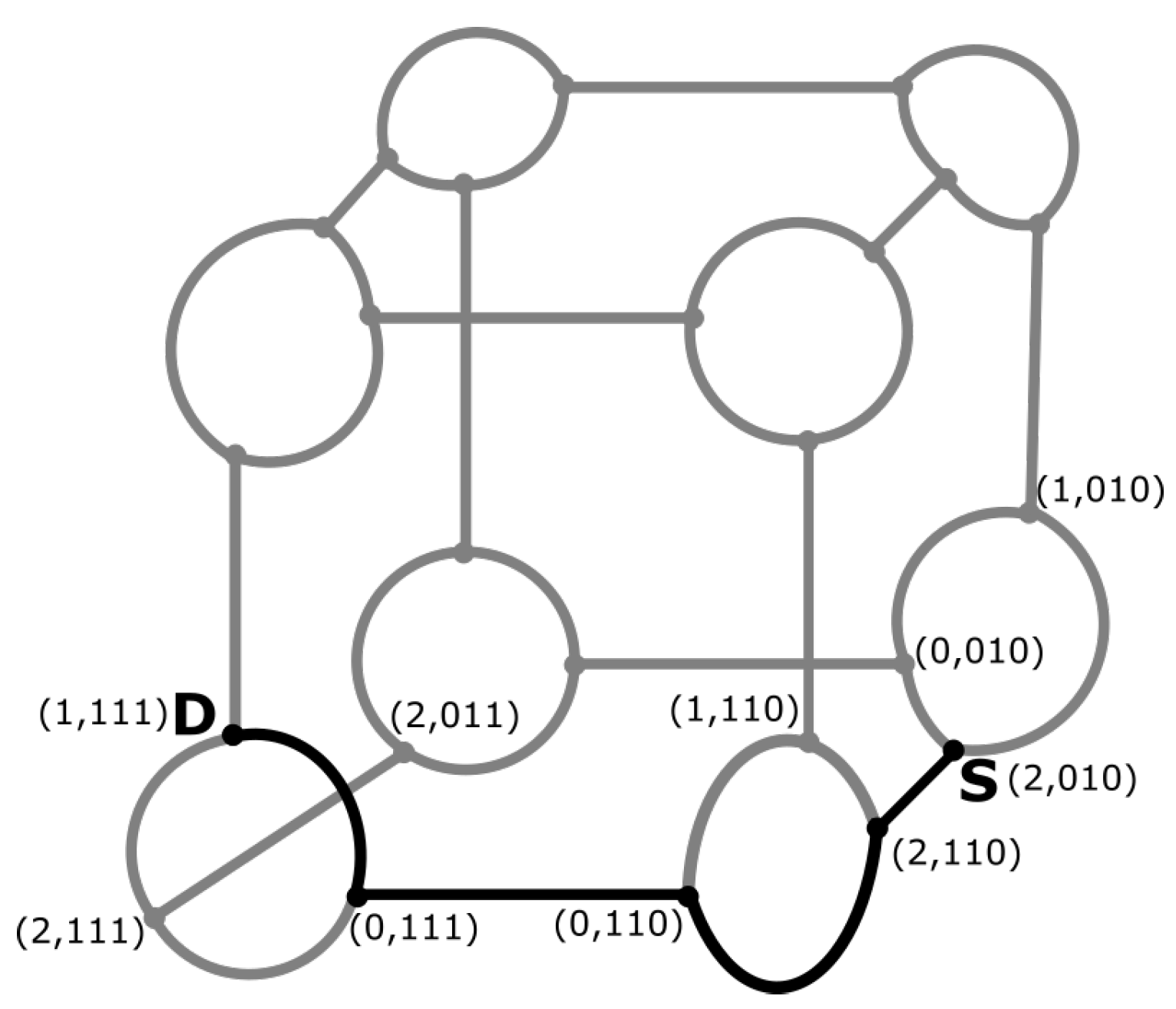
4.1. Hypercube Based Overlay Network
4.2. Cube Connected Cycle Based Overlay Network
| Algorithm 1: SLoPCloud |
|
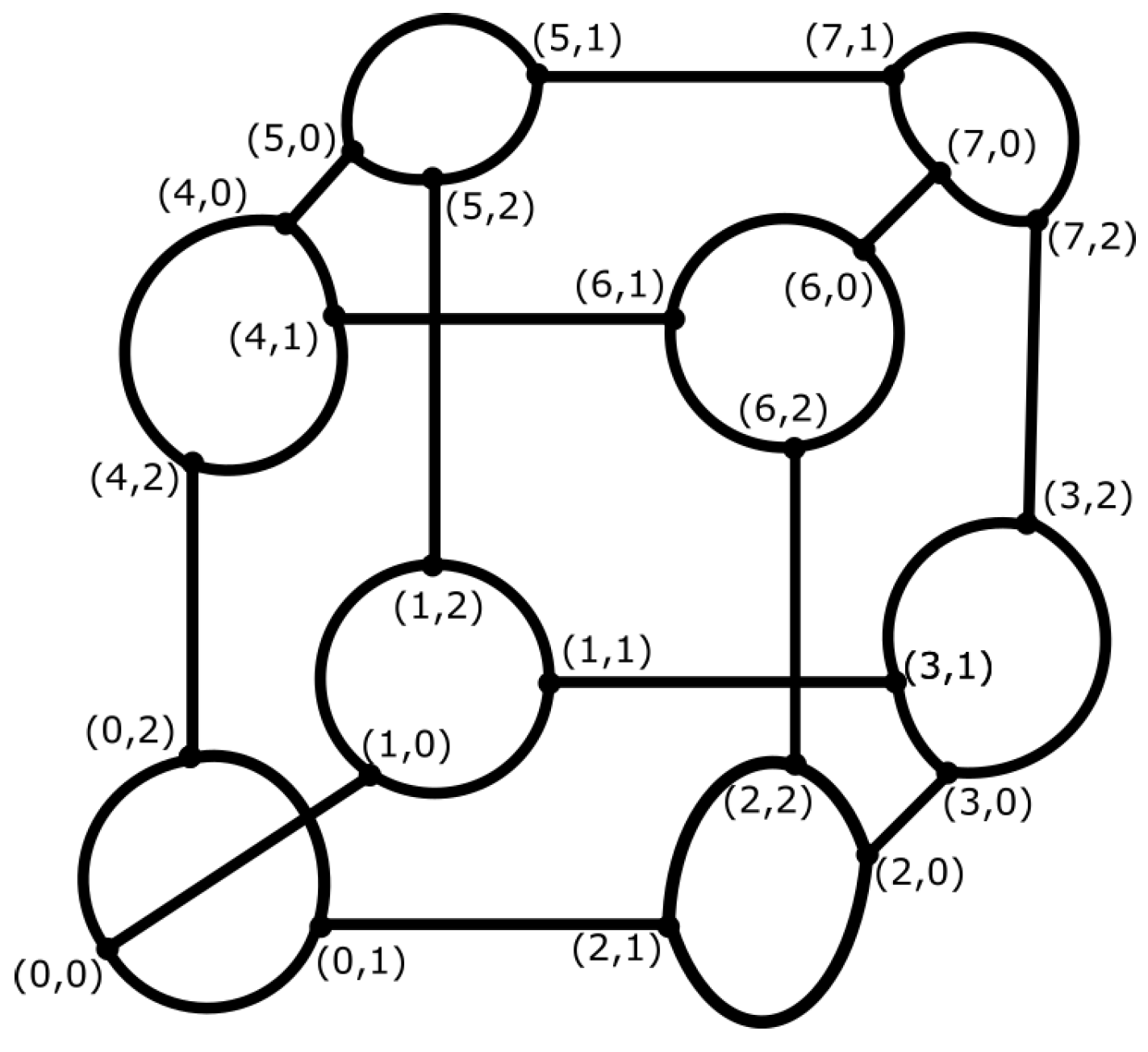
4.3. Generalized Hypercube Connected Cycle Overlay Network
- (i)
- Total number of nodes in the graph is represented by N.
- (ii)
- l and m are the parameters of the graph, where .
- (iii)
- The nodes of the graph are divided into l levels, which are numbered as , and each level consists of nodes.
- (iv)
- Specification of each node:
- (a)
- All nodes in one level are numbered by a variable in a range from 0 to . This variable is called the index of a node in the specific level. The index is displayed by a string with l literals and each literal has a value from 0 to .
- (b)
- Another literal is used to identify different levels of nodes. It is in the range of 0 to .
Here is an example of representing a node in GHCC (l,m). The ordered set of literals is used where p indicates the number of levels, , and the string represents the index of a node in level p. Thus, p is l-valued while s are m-valued. There is also another way to display a node, which is a two-tuple form, where p is the number of level and n is the index such that . - (v)
- There are two kinds of links in this topology, inter-level and intra-level links, which are defined as follows:
- (a)
- Inter-level links:l nodes with different levels and same indices are distributed in the network. These l nodes are connected in a way that forms a Ring. The links between these nodes are called inter-level links. For example, if we consider a node , it is connected to two other nodes in adjacent levels, . Consider that all additions and subtractions are in the modulus l. There are cycles in the graph which are constructed by inter-level links. Each cycle consists of l nodes.
- (b)
- Intra-level links: There are some other links which connect nodes in the same level. Node is connected to other nodes through clique edges, where signifies all values of the corresponding literal which is in the range of 0 to , excluding the value . The intra-level links form number of disjoint cliques in each level, each clique is with the size of m.
- (vi)
- Since there are inter-level links and two intra-level links emerging from each node, the degree of the graph is .
- (vii)
- As is obvious, the graph is symmetric.
5. Experimental Results
6. Conclusions
Author Contributions
Acknowledgments
Conflicts of Interest
Abbreviations
| CCC | Cube Connected Cycle |
| DHT | Distributed Hash Table |
| DOLR | Decentralized Object Location and Routing |
| GHCC | Generalized Hypercube Connected Cycle |
| KBR | Key Based Routing |
| OBAP | Optimal Bandwidth Allocation Problem |
| P2P | Peer to Peer |
| RTT | Round-Trip Time |
| TTL | Time to Live |
| VoD | Video on Demand |
References
- Foster, I.; Zhao, Y.; Raicu, I.; Lu, S. Cloud computing and grid computing 360-degree compared. In Proceedings of the Grid Computing Environments Workshop, Austin, TX, USA, 16 November 2008; pp. 1–10. [Google Scholar] [CrossRef]
- De Asís López-Fuentes, F.; García-Rodríguez, G. Collaborative cloud computing based on P2P networks. In Proceedings of the 30th International Conference on Advanced Information Networking and Applications Workshops, AINA 2016 Workshops, Crans-Montana, Switzerland, 23–25 March 2016; pp. 209–213. [Google Scholar]
- Soares, J.; Wuhib, F.; Yadhav, V.; Han, X.; Joseph, R. Re-designing Cloud platforms for massive scale using a P2P architecture. In Proceedings of the IEEE International Conference on Cloud Computing Technology and Science (CloudCom), Hongkong, China, 11–14 December 2017; pp. 57–64. [Google Scholar]
- Shen, H.; Li, Z.; Chen, K. Social-P2P: An online social network based P2P file sharing system. IEEE Trans. Parallel Distrib. Syst. 2015, 26, 2874–2889. [Google Scholar] [CrossRef]
- Liu, G.; Shen, H.; Ward, L. An efficient and trustworthy P2P and social network integrated file sharing system. IEEE Trans. Comput. 2015, 64, 54–70. [Google Scholar] [CrossRef]
- Zhou, Y.; Fu, T.Z.; Chiu, D.M. A unifying model and analysis of P2P VoD replication and scheduling. IEEE/ACM Trans. Netw. 2015, 23, 1163–1175. [Google Scholar] [CrossRef]
- Li, Z.; Huang, Y.; Liu, G.; Wang, F.; Liu, Y.; Zhang, Z.L.; Dai, Y. Challenges, designs, and performances of large-scale open-P2SP content distribution. IEEE Trans. Parallel Distrib. Syst. 2013, 24, 2181–2191. [Google Scholar] [CrossRef]
- Karagiannis, T.; Rodriguez, P.; Papagiannaki, K. Should internet service providers fear peer-assisted content distribution? In Proceedings of the 5th Internet Measurement Conference (IMC 2005), Berkeley, CA, USA, 19–21 October 2005; p. 6. [Google Scholar]
- Stoica, I.; Morris, R.; Karger, D.; Kaashoek, M.F.; Balakrishnan, H. Chord: A scalable peer-to-peer lookup service for internet applications. SIGCOMM Comput. Commun. Rev. 2001, 31, 149–160. [Google Scholar] [CrossRef]
- Rowstron, A.I.T.; Druschel, P. Pastry: Scalable, Decentralized Object Location, and Routing for Large-Scale Peer-to-Peer Systems. In Proceedings of the IFIP/ACM International Conference on Distributed Systems Platforms and Open Distributed Processing, Heidelberg, Germany, 12–16 November 2000; pp. 329–350. [Google Scholar]
- Zhao, B.Y.; Kubiatowicz, J.D.; Joseph, A.D. Tapestry: An Infrastructure for Fault-Tolerant Wide-Area Location and Outing; Technical Report; UCB/CSD: Berkeley, CA, USA, 2001. [Google Scholar]
- Teoh, S.T.; Ma, K.L.; Wu, S.F.; Massey, D.; Zhao, X.L.; Pei, D.; Wang, L.; Zhang, L.; Bush, R. Visual-based anomaly detection for BGP origin AS change (OASC) events. In Proceedings of the 14th IFIP/IEEE International Workshop on Distributed Systems: Operations and Management (DSOM 2003), Heidelberg, Germany, 20–22 October 2003; pp. 155–168. [Google Scholar]
- Gharib, M.; Barzegar, Z.; Habibi, J. A novel method for supporting locality in Peer-to-Peer overlays using hypercube topology. In Proceedings of the International Conference on Intelligent Systems, Modelling and Simulation (ISMS), Liverpool, UK, 27–29 January 2010; pp. 391–395. [Google Scholar] [CrossRef]
- Gharib, M.; Barzegar, Z.; Habibi, J. The effect of using cube connected cycle for improving locality awareness in Peer-to-Peer networks. In Proceedings of the 12th International Conference on Computer Modelling and Simulation (UKSim), Cambridge, UK, 24–26 March 2010; pp. 491–496. [Google Scholar] [CrossRef]
- Zhao, P.; Huang, T.L.; Liu, C.X.; Wang, X. Research of P2P architecture based on cloud computing. In Proceedings of the International Conference on Intelligent Computing and Integrated Systems (ICISS), Guilin, China, 22–24 October 2010; pp. 652–655. [Google Scholar]
- Napster. Available online: http://www.us.napster.com (accessed on 1 September 2018).
- Gnutella. Available online: https://web.archive.org/web/20080525005017/http://www.gnutella.com (accessed on 1 September 2018).
- Wilcox-O’Hearn, B. Experiences Deploying a Large-Scale Emergent Network. In Proceedings of the First International Workshop (IPTPS 2002), Cambridge, MA, USA, 7–8 March 2002; pp. 104–110. [Google Scholar]
- Clarke, I.; Sandberg, O.; Wiley, B.; Hong, T.W. Freenet: A distributed anonymous information storage and retrieval system. In Proceedings of the Designing Privacy Enhancing Technologies, International Workshop on Design Issues in Anonymity and Unobservability, Berkeley, CA, USA, 25–26 July 2000; pp. 46–66. [Google Scholar]
- Ratnasamy, S.; Francis, P.; Handley, M.; Karp, R.; Shenker, S. A scalable content-addressable network. SIGCOMM Comput. Commun. Rev. 2001, 31, 161–172. [Google Scholar] [CrossRef]
- Dabek, F.; Zhao, B.; Druschel, P.; Kubiatowicz, J.; Stoica, I. Towards a common API for structured peer-to-peer overlays. In Proceedings of the Peer-to-Peer Systems II, Second International Workshop (IPTPS 2003), Berkeley, CA, USA, 21–22 Februray 2003; pp. 33–44. [Google Scholar]
- Plaxton, C.G.; Rajaraman, R.; Richa, A.W. Accessing nearby copies of replicated objects in a distributed environment. In Proceedings of the Ninth Annual ACM Symposium on Parallel Algorithms and Architectures, Newport, RI, USA, 23–25 June 1997; pp. 311–320. [Google Scholar] [CrossRef]
- Awerbuch, B.; Peleg, D. Concurrent online tracking of mobile users. ACM SIGCOMM Comput. Commun. Rev. 1991, 22, 221–233. [Google Scholar] [CrossRef]
- Rajaraman, R.; Richa, A.W.; Vöcking, B.; Vuppuluri, G. A data tracking scheme for general networks. In Proceedings of the 13th ACM Symposium on Parallel Algorithms and Architectures, Crete Island, Greece, 4–6 July 2001; pp. 247–254. [Google Scholar] [CrossRef]
- Maymounkov, P.; Mazières, D. Kademlia: A peer-to-peer information system based on the xor metric. In Proceedings of the First International Workshop, IPTPS 2002, Cambridge, MA, USA, 7–8 March 2002; pp. 53–65. [Google Scholar]
- Malkhi, D.; Naor, M.; Ratajczak, D. Viceroy: A scalable and dynamic emulation of the butterfly. In Proceedings of the Twenty-first Annual Symposium on Principles of Distributed Computing, Monterey, CA, USA, 21–24 July 2002; pp. 183–192. [Google Scholar] [CrossRef]
- Harvey, N.J.A.; Jones, M.B.; Saroiu, S.; Theimer, M.; Wolman, A. Skipnet: A scalable overlay network with practical locality properties. In Proceedings of the 4th USENIX Symposium on Internet Technologies and Systems (USITS’03), Seattle, WA, USA, 26–28 March 2003. [Google Scholar]
- Freedman, M.J.; Vutukuru, M.; Feamster, N.; Balakrishnan, H. Geographic locality of IP prefixes. In Proceedings of the 5th ACM SIGCOMM conference on Internet Measurement, Berkeley, CA, USA, 19–21 October 2005; p. 13. [Google Scholar]
- Dabek, F.; Cox, R.; Kaashoek, F.; Morris, R. Vivaldi: A decentralized network coordinate system. SIGCOMM Comput. Commun. Rev. 2004, 34, 15–26. [Google Scholar] [CrossRef]
- Wang, L.; Tao, J.; Kunze, M.; Castellanos, A.; Kramer, D.; Karl, W. Scientific cloud computing: Early definition and experience. In Proceedings of the 10th IEEE International Conference on High Performance Computing and Communications (HPCC 2008), Dalian, China, 25–27 September 2008; pp. 825–830. [Google Scholar] [CrossRef]
- Jo, S.; Han, J. Convergence P2P cloud computing. Peer Peer Netw. Appl. 2018, 6, 1153–1155. [Google Scholar] [CrossRef]
- Xu, K.; Song, M.; Zhang, X.; Song, J. A cloud computing platform based on P2P. In Proceedings of the IEEE International Symposium on IT in Medicine Education, Jinan, China, 14–16 August 2009; pp. 427–432. [Google Scholar] [CrossRef]
- Xiong, N.; Liu, Y.; Wu, S.; Yang, L.; Xu, K. An efficient search algorithm without memory for peer-to-peer cloud computing networks. In Proceedings of the 25th IEEE International Symposium on Parallel and Distributed Processing (IPDPS 2011), Anchorage, AK, USA, 16–20 May 2001; pp. 1452–1457. [Google Scholar] [CrossRef]
- Yoon, J.; Hong, T.; Choi, J.; Park, C.; Kim, K.; Yu, H. Evaluation of P2P and cloud computing as platform for exhaustive key search on block ciphers. Peer Peer Netw. Appl. 2018, 11, 1206–1216. [Google Scholar] [CrossRef]
- Li, J.; Wu, J.; Chen, L. Block-secure: Blockchain based scheme for secure P2P cloud storage. Inf. Sci. 2018, 465, 219–231. [Google Scholar] [CrossRef]
- Chang, H.Y.; Shih, Y.Y.; Lin, Y.W. CloudPP: A novel cloud-based P2P live video streaming platform with SVC technology. In Proceedings of the 8th International Conference on Computing Technology and Information Management (ICCM), Jeju, South Korea, 26–28 August 2012; pp. 64–68. [Google Scholar]
- Provensi, L.; Eliassen, F.; Vitenberg, R. A cloud-assisted tree-based P2P system for low latency streaming. In Proceedings of the International Conference on Cloud and Autonomic Computing (ICCAC 2017), Tucson, AZ, USA, 18–22 September 2017; pp. 172–183. [Google Scholar]
- Zhao, W.; Liu, J.; Hara, T. Optimal replica distribution in edge-node-assisted Cloud-P2P Platforms for real-time streaming. IEEE Trans. Veh. Tech. 2018, 67, 8637–8646. [Google Scholar] [CrossRef]
- Liu, F.; Shen, S.; Li, B.; Li, B.; Yin, H.; Li, S. Novasky: Cinematic-quality VoD in a P2P storage cloud. In Proceedings of the 30th IEEE International Conference on Computer Communications, Joint Conference of the IEEE Computer and Communications Societies, Shanghai, China, April 10–15 2011; pp. 936–944. [Google Scholar] [CrossRef]
- Huang, G.; Kong, L.; Wu, K.; Chen, Z. A bandwidth allocation policy for helpers in cloud-assisted p2p video-on-demand systems. In Proceedings of the Fifth International Conference on Advanced Cloud and Big Data (CBD), Shanghai, China, 13–16 August 2017; pp. 7–12. [Google Scholar]
- Huang, G.; Gao, Y.; Kong, L.; Wu, K. An incentive scheme based on bitrate adaptation for cloud-assisted P2P video-on-demand streaming systems. In Proceedings of the 3rd International Conference on Cloud Computing and Big Data Analysis (ICCCBDA), Chengdu, China, 20–22 April 2018; pp. 404–408. [Google Scholar]
- Soudi, A.; Gharib, M. The effect of choosing proper overlay topologyon the peer to peer networks’ properties. Int. J. Comput. Sci. Inf. Secur. 2012, 10, 99–102. [Google Scholar]
- Hadighi, R.; Gharib, M. Using proximity measure to improve locality in structured p2p networks. Int. J. Comput. Appl. 2012, 45, 31–37. [Google Scholar]
- Preparata, F.P.; Vuillemin, J. The cube-connected-cycles: A versatile network for parallel computation. In Proceedings of the 20th Annual Symposium on Foundations of Computer Science, 29–31 October 1979; pp. 140–147. [Google Scholar] [CrossRef]
- Gharib, M.; Yousefi’zadeh, H.; Movaghar, A. A survey of key pre-distribution and overlay routing in unstructured wireless networks. Comput. Sci. Eng. Electr. 2016, 23, 2831–2844. [Google Scholar] [CrossRef][Green Version]
- Gupta, S.; Das, D.; Sinha, B. The generalized hypercube-connected-cycle: an efficient network topology. In Proceedings of the 3rd International Conference on High Performance Computing, Minneapolis, MN, USA, 29 September–1 October 1996; pp. 182–187. [Google Scholar] [CrossRef]
- Gharib, M.; Yousefi’zadeh, H.; Movaghar, A. Secure overlay routing using key pre-distribution: A linear distance optimization approach. IEEE Trans. Mob. Comput. 2016, 15, 2333–2344. [Google Scholar] [CrossRef]
- Gharib, M.; Yousefi’zadeh, H.; Movaghar, A. Secure overlay routing for large scale networks. IEEE Trans. Netw. Sci. Eng. 2018. [Google Scholar] [CrossRef]
- Gupta, S.; Das, D.; Sinha, B. A New Class of Network Graphs for Different Degrees and Diameters; Technical Report; Indian Statistical Institute: Calcutta, Indian, 1996. [Google Scholar]
- Planetsim. Available online: http://sourceforge.net/projects/planetsim (accessed on 2 September 2018).




| d | Number of Overlay Topology Dimensions |
|---|---|
| ℵ | The set of starting nodes |
| The timeout threshold | |
| N | Number of network nodes |
| D | Diameter of the graph |
| Degree of the graph | |
| l | GHCC parameter representing number of levels |
| m | GHCC parameter |
| Representation of a node in GHCC | |
| p | Level number of the node in GHCC |
| String node index in level p | |
| Another representation of a node in GHCC | |
| n | Decimal node index in level p |
| Overlay | Bootstrapping Time (Sec) | Bootstrapping Control Traffic (# of Packets) |
|---|---|---|
| Simple Hypercube | ||
| Locality Aware Hypercube | ||
| Locality Aware Cube connected cycle | ||
| Locality Aware Ring |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Gharib, M.; Malekimajd, M.; Movaghar, A. SLoPCloud: An Efficient Solution for Locality Problem in Peer-to-Peer Cloud Systems. Algorithms 2018, 11, 150. https://doi.org/10.3390/a11100150
Gharib M, Malekimajd M, Movaghar A. SLoPCloud: An Efficient Solution for Locality Problem in Peer-to-Peer Cloud Systems. Algorithms. 2018; 11(10):150. https://doi.org/10.3390/a11100150
Chicago/Turabian StyleGharib, Mohammed, Marzieh Malekimajd, and Ali Movaghar. 2018. "SLoPCloud: An Efficient Solution for Locality Problem in Peer-to-Peer Cloud Systems" Algorithms 11, no. 10: 150. https://doi.org/10.3390/a11100150
APA StyleGharib, M., Malekimajd, M., & Movaghar, A. (2018). SLoPCloud: An Efficient Solution for Locality Problem in Peer-to-Peer Cloud Systems. Algorithms, 11(10), 150. https://doi.org/10.3390/a11100150





