Data Privacy Preservation and Security in Smart Metering Systems
Abstract
1. Introduction
- Establishing a pivot for the interested researchers of the importance of SMs;
- Quantifying the existing problems regarding operation stability;
- Addressing the common defense mechanisms employed for protecting SMs’ data privacy;
- Proposing a comprehensive comparison of the involved trust models for SMs’ data privacy;
- Highlighting the role of SMs’ security for disaster management;
- Recommending the future directions of the SM privacy for the interested scholars.
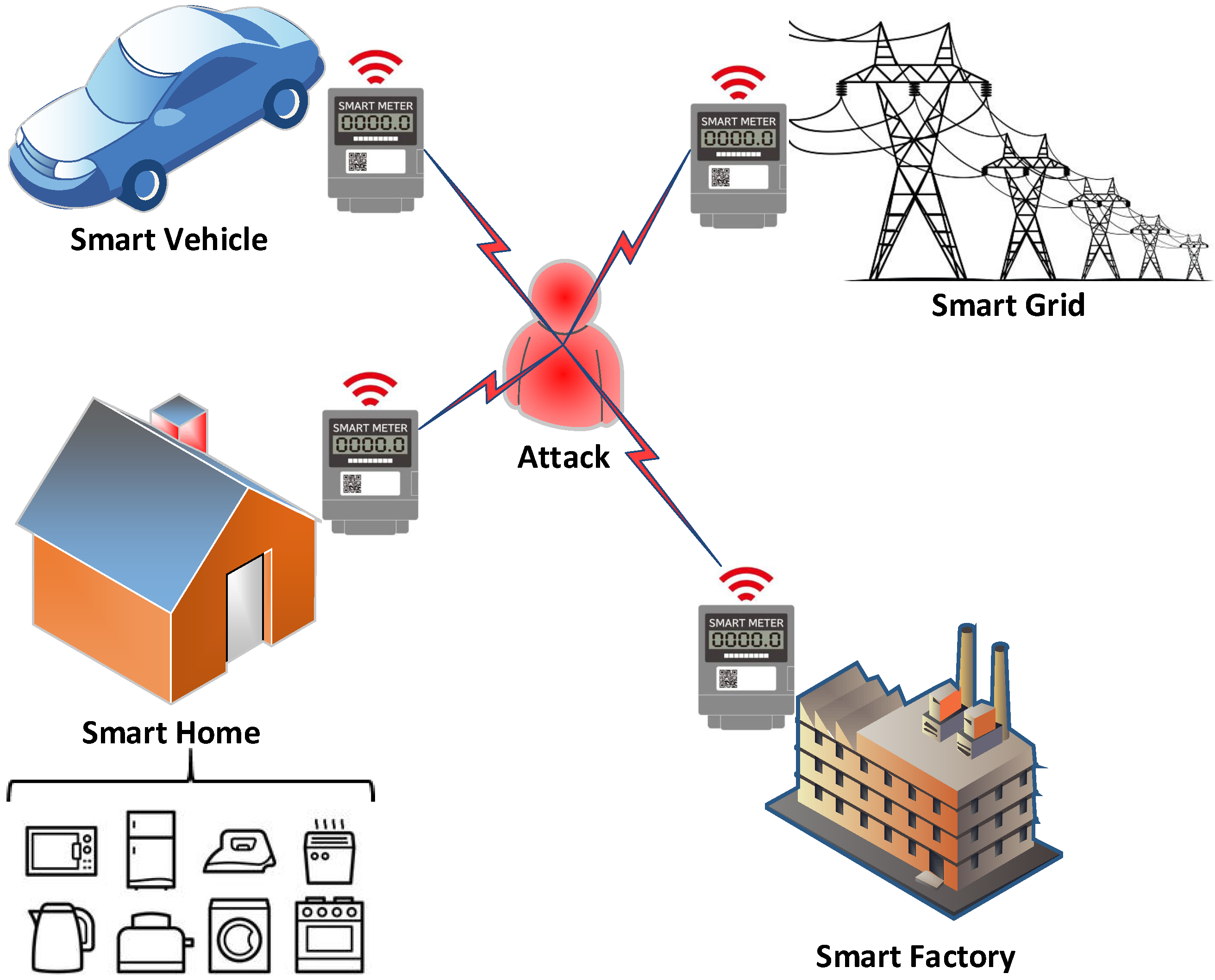
2. Existing Problems of Smart Meters
2.1. Optimal Power Flow
2.2. Privacy Problems
3. Defense Mechanisms of Smart Meters
3.1. Differential Privacy
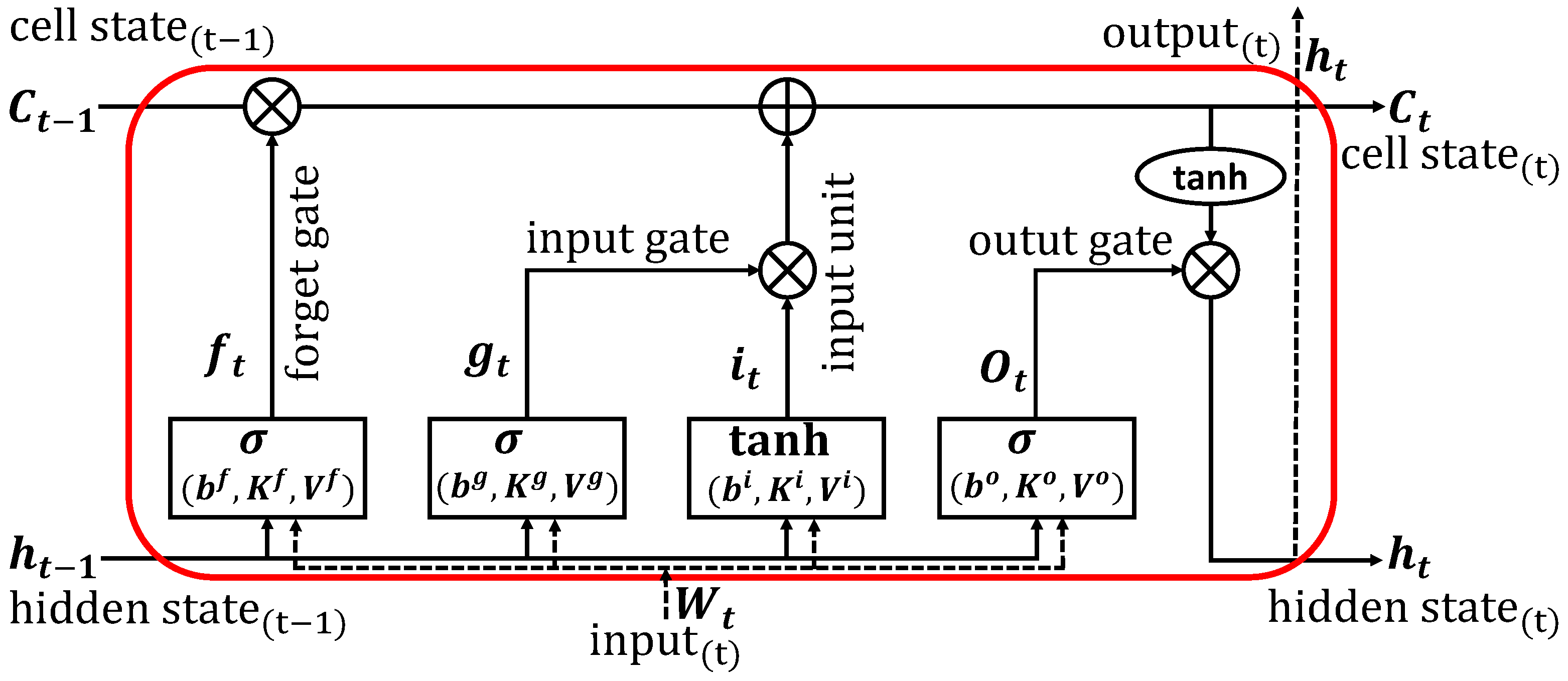
3.2. Machine Learning
3.3. Kullback–Leibler Divergence
3.4. Game Theory
- The strategic interaction between competing or cooperative interests when the limitations and compensation for actions are taken into account is referred to as a game.
- A player is a fundamental component of a game. Each player in the game, given by the number i, is responsible for acting rationally, as shown by the symbol . In a game, a player may take the place of a human, a machine, or a team of players N.
- The Utility/Payoff is expressed by the reward or punishment to a player based on a given action throughout the game given by , which calculates the output for the ith player, and pinpointed by the participating players actions , where the symbol × represents a Cartesian product.
- A strategy is defined by an action plan throughout the game in which a player can adopt a strategic game .
- NE is defined as the profile of the optimal action, , as a player is not able to gain from unilaterally changing its course and opting for a different course of action [77,80]. This process is reflected by the utility function as for all , where is the player strategy i and represents the strategies of all players except i [75].
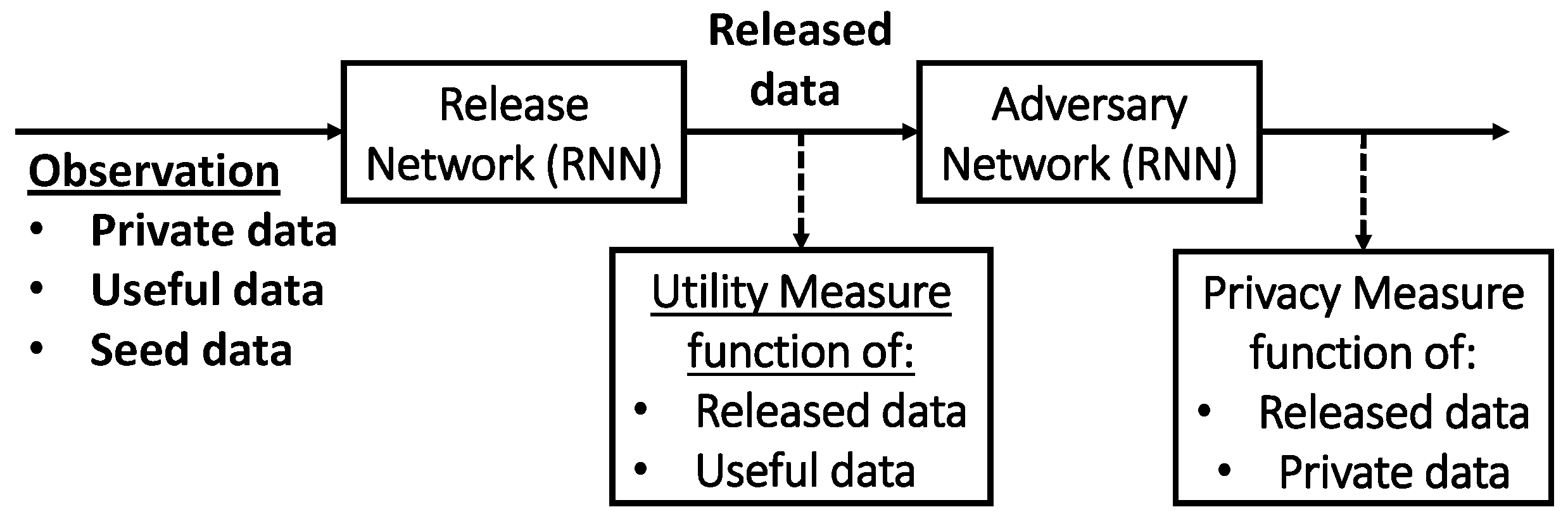
3.5. Generative Adversarial Privacy
3.6. Data Aggregation
3.7. Pseudonyms
3.8. Clustering
3.9. Entropy
3.10. Fuzzy
3.11. Bayesian
4. Existing Solutions Comparison
5. Recommendations for Future Directions
- Analyzing the impact an attacker could have on the data release framework if they have prior knowledge about their victim that was obtained without using smart meter data;
- Combining their algorithm with physical distortion methods, such as renewable energy or batteries, could further increase a consumer’s privacy by shaping their demand profile;
- Observing the privacy impact of the DP algorithms when the resolution of the model, or the data collection interval, is over a specific time threshold;
- Investigating the effects of privacy preservation against non-intrusive load monitoring techniques;
- Providing more inference privacy techniques;
- Considering the modern technologies and adaptive protocols of the Internet of Things to attain acceptable disaster management and risk mitigation.
6. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Alsharif, A.; Nabil, M.; Mahmoud, M.M.; Abdallah, M. EPDA: Efficient and privacy-preserving data collection and access control scheme for multi-recipient AMI networks. IEEE Access 2019, 7, 27829–27845. [Google Scholar] [CrossRef]
- Alsharif, A.; Nabil, M.; Tonyali, S.; Mohammed, H.; Mahmoud, M.; Akkaya, K. EPIC: Efficient privacy-preserving scheme with EtoE data integrity and authenticity for AMI networks. IEEE Internet Things J. 2018, 6, 3309–3321. [Google Scholar] [CrossRef]
- Fadlullah, Z.M.; Fouda, M.M.; Kato, N.; Takeuchi, A.; Iwasaki, N.; Nozaki, Y. Toward intelligent machine-to-machine communications in smart grid. IEEE Commun. Mag. 2011, 49, 60–65. [Google Scholar] [CrossRef]
- Fouda, M.M.; Fadlullah, Z.M.; Kato, N.; Lu, R.; Shen, X.S. A Lightweight Message Authentication Scheme for Smart Grid Communications. IEEE Trans. Smart Grid 2011, 2, 675–685. [Google Scholar] [CrossRef]
- Fadlullah, Z.M.; Fouda, M.M.; Kato, N.; Shen, X.; Nozaki, Y. An early warning system against malicious activities for smart grid communications. IEEE Netw. 2011, 25, 50–55. [Google Scholar] [CrossRef]
- Abdulaal, M.J.; Ibrahem, M.I.; Mahmoud, M.M.E.A.; Khalid, J.; Aljohani, A.J.; Milyani, A.H.; Abusorrah, A.M. Real-Time Detection of False Readings in Smart Grid AMI Using Deep and Ensemble Learning. IEEE Access 2022, 10, 47541–47556. [Google Scholar] [CrossRef]
- Ali, S.S.; Choi, B.J. State-of-the-art artificial intelligence techniques for distributed smart grids: A review. Electronics 2020, 9, 1030. [Google Scholar] [CrossRef]
- Saxena, N.; Choi, B.J. State of the art authentication, access control, and secure integration in smart grid. Energies 2015, 8, 11883–11915. [Google Scholar] [CrossRef]
- Alsharif, A.; Nabil, M.; Mahmoud, M.; Abdallah, M. Privacy-preserving collection of power consumption data for enhanced AMI networks. In Proceedings of the 2018 25th International Conference on Telecommunications (ICT), Saint-Malo, France, 26–28 June 2018; pp. 196–201. [Google Scholar]
- Sherifl, A.; Alsharif, A.; Mahmoud, M.; Abdallah, M.; Song, M. Efficient privacy-preserving aggregation scheme for data sets. In Proceedings of the 2018 25th International Conference on Telecommunications (ICT), Saint-Malo, France, 26–28 June2018; pp. 191–195. [Google Scholar]
- Aladdin, S.; El-Tantawy, S.; Fouda, M.M.; Tag Eldien, A.S. MARLA-SG: Multi-Agent Reinforcement Learning Algorithm for Efficient Demand Response in Smart Grid. IEEE Access 2020, 8, 210626–210639. [Google Scholar] [CrossRef]
- Fouda, M.M.; Fadlullah, Z.M.; Kato, N.; Takeuchi, A.; Nozaki, Y. A novel demand control policy for improving quality of power usage in smart grid. In Proceedings of the 2012 IEEE Global Communications Conference (GLOBECOM), Anaheim, CA, USA, 3–7 December 2012; pp. 5154–5159. [Google Scholar] [CrossRef]
- Badr, M.M.; Ibrahem, M.I.; Baza, M.; Mahmoud, M.; Alasmary, W. Detecting Electricity Fraud in the Net-Metering System Using Deep Learning. In Proceedings of the 2021 International Symposium on Networks, Computers and Communications (ISNCC), Dubai, United Arab Emirates, 31 October–2 November 2021; pp. 1–6. [Google Scholar] [CrossRef]
- Ilo, A. Design of the smart grid architecture according to fractal principles and the basics of corresponding market structure. Energies 2019, 12, 4153. [Google Scholar] [CrossRef]
- Junior, J.M.; da Costa, J.P.C.; Garcez, C.C.; de Oliveira Albuquerque, R.; Arancibia, A.; Weichenberger, L.; de Mendonça, F.L.L.; Galdo, G.D.; de Sousa, R.T., Jr. Data security and trading framework for smart grids in neighborhood area networks. Sensors 2020, 20, 1337. [Google Scholar] [CrossRef] [PubMed]
- Alsharif, A.; Nabil, M.; Sherif, A.; Mahmoud, M.; Song, M. MDMS: Efficient and privacy-preserving multidimension and multisubset data collection for AMI networks. IEEE Internet Things J. 2019, 6, 10363–10374. [Google Scholar] [CrossRef]
- Alsharif, A.; Tonyali, S.; Mahmoud, M.; Akkaya, K.; Ismail, M.; Serpedin, E. Performance analysis of certificate renewal scheme for ami networks. In Proceedings of the 7th International Workshop on Computer Science and Engineering, Beijing, China, 25–27 June 2017; pp. 25–27. [Google Scholar]
- Ibrahem, M.I.; Nabil, M.; Fouda, M.M.; Mahmoud, M.M.E.A.; Alasmary, W.; Alsolami, F. Efficient Privacy-Preserving Electricity Theft Detection With Dynamic Billing and Load Monitoring for AMI Networks. IEEE Internet Things J. 2021, 8, 1243–1258. [Google Scholar] [CrossRef]
- Alsharif, A.; Shafee, A.; Nabil, M.; Mahmoud, M.; Alasmary, W. A multi-authority attribute-based signcryption scheme with efficient revocation for smart grid downlink communication. In Proceedings of the 2019 International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Atlanta, GA, USA, 14–17 July 2019; pp. 1025–1032. [Google Scholar]
- Ibrahem, M.I.; Mahmoud, M.; Fouda, M.M.; Alsolami, F.; Alasmary, W.; Shen, X. Privacy Preserving and Efficient Data Collection Scheme for AMI Networks Using Deep Learning. IEEE Internet Things J. 2021, 8, 17131–17146. [Google Scholar] [CrossRef]
- Badr, M.M.; Ibrahem, M.I.; Mahmoud, M.; Fouda, M.M.; Alsolami, F.; Alasmary, W. Detection of False-Reading Attacks in Smart Grid Net-Metering System. IEEE Internet Things J. 2022, 9, 1386–1401. [Google Scholar] [CrossRef]
- Ibrahem, M.I.; Badr, M.M.; Fouda, M.M.; Mahmoud, M.; Alasmary, W.; Fadlullah, Z.M. PMBFE: Efficient and Privacy-Preserving Monitoring and Billing Using Functional Encryption for AMI Networks. In Proceedings of the 2020 International Symposium on Networks, Computers and Communications (ISNCC), Montreal, QC, Canada, 16–18 June 2020; pp. 1–7. [Google Scholar] [CrossRef]
- Ibrahem, M.I.; Badr, M.M.; Mahmoud, M.; Fouda, M.M.; Alasmary, W. Countering Presence Privacy Attack in Efficient AMI Networks Using Interactive Deep-Learning. In Proceedings of the 2021 International Symposium on Networks, Computers and Communications (ISNCC), Dubai, United Arab Emirates, 31 October–2 November 2021; pp. 1–7. [Google Scholar] [CrossRef]
- Badr, M.M.; Ibrahem, M.I.; Mahmoud, M.; Alasmary, W.; Fouda, M.M.; Almotairi, K.H.; Fadlullah, Z.M. Privacy-Preserving Federated-Learning-Based Net-Energy Forecasting. In Proceedings of the SoutheastCon 2022, Mobile, AL, USA, 26 March–3 April 2022; pp. 133–139. [Google Scholar] [CrossRef]
- Shateri, M.; Messina, F.; Piantanida, P.; Labeau, F. Real-time privacy-preserving data release for smart meters. IEEE Trans. Smart Grid 2020, 11, 5174–5183. [Google Scholar] [CrossRef]
- Gough, M.B.; Santos, S.F.; AlSkaif, T.; Javadi, M.S.; Castro, R.; Catalão, J.P. Preserving privacy of smart meter data in a smart grid environment. IEEE Trans. Ind. Inform. 2021, 18, 707–718. [Google Scholar] [CrossRef]
- Mashima, D. Authenticated down-sampling for privacy-preserving energy usage data sharing. In Proceedings of the 2015 IEEE International Conference on Smart Grid Communications (SmartGridComm), Miami, FL, USA, 2–5 November 2015; pp. 605–610. [Google Scholar]
- Azizi, E.; Shotorbani, A.M.; Hamidi-Beheshti, M.T.; Mohammadi-Ivatloo, B.; Bolouki, S. Residential household non-intrusive load monitoring via smart event-based optimization. IEEE Trans. Consum. Electron. 2020, 66, 233–241. [Google Scholar] [CrossRef]
- Shateri, M.; Messina, F.; Piantanida, P.; Labeau, F. Learning Sparse Privacy-Preserving Representations for Smart Meters Data. In Proceedings of the 2021 IEEE International Conference on Communications, Control, and Computing Technologies for Smart Grids (SmartGridComm), Aachen, Germany, 25–28 October 2021; pp. 333–338. [Google Scholar]
- Reinhardt, A.; Pereira, L. Energy Data Analytics for Smart Meter Data. Energies 2021, 14, 5376. [Google Scholar] [CrossRef]
- Stadler, M.; Pecenak, Z.; Mathiesen, P.; Fahy, K.; Kleissl, J. Performance comparison between two established microgrid planning MILP methodologies tested on 13 microgrid projects. Energies 2020, 13, 4460. [Google Scholar] [CrossRef]
- Athanasiadis, C.; Doukas, D.; Papadopoulos, T.; Chrysopoulos, A. A scalable real-time non-intrusive load monitoring system for the estimation of household appliance power consumption. Energies 2021, 14, 767. [Google Scholar] [CrossRef]
- Farokhi, F. Review of results on smart-meter privacy by data manipulation, demand shaping, and load scheduling. IET Smart Grid 2020, 3, 605–613. [Google Scholar] [CrossRef]
- Zhang, X.Y.; Kuenzel, S.; Córdoba-Pachón, J.R.; Watkins, C. Privacy-Functionality Trade-Off: A privacy-preserving multi-channel smart metering system. Energies 2020, 13, 3221. [Google Scholar] [CrossRef]
- Abdalzaher, M.S.; Muta, O. A Game-Theoretic Approach for Enhancing Security and Data Trustworthiness in IoT Applications. IEEE Internet Things J. 2020, 7, 11250–11261. [Google Scholar] [CrossRef]
- Hamdy, O.; Gaber, H.; Abdalzaher, M.S.; Elhadidy, M. Identifying Exposure of Urban Area to Certain Seismic Hazard Using Machine Learning and GIS: A Case Study of Greater Cairo. Sustainability 2022, 14, 10722. [Google Scholar] [CrossRef]
- Abdalzaher, M.S.; Soliman, M.S.; El-Hady, S.M.; Benslimane, A.; Elwekeil, M. A deep learning model for earthquake parameters observation in IoT system-based earthquake early warning. IEEE Internet Things J. 2021, 9, 8412–8424. [Google Scholar] [CrossRef]
- Abdalzaher, M.S.; Elwekeil, M.; Wang, T.; Zhang, S. A deep autoencoder trust model for mitigating jamming attack in IoT assisted by cognitive radio. IEEE Syst. J. 2021, 16, 3635–3645. [Google Scholar] [CrossRef]
- Abdalzaher, M.S.; Moustafa, S.S.; Abd-Elnaby, M.; Elwekeil, M. Comparative performance assessments of machine-learning methods for artificial seismic sources discrimination. IEEE Access 2021, 9, 65524–65535. [Google Scholar] [CrossRef]
- Moustafa, S.S.; Abdalzaher, M.S.; Yassien, M.H.; Wang, T.; Elwekeil, M.; Hafiez, H.E.A. Development of an optimized regression model to predict blast-driven ground vibrations. IEEE Access 2021, 9, 31826–31841. [Google Scholar] [CrossRef]
- Ibrahem, M.I.; Mahmoud, M.; Alsolami, F.; Alasmary, W.; AL-Ghamdi, A.; Shen, X. Electricity Theft Detection for Change-and-Transmit Advanced Metering Infrastructure. IEEE Internet Things J. 2022. [Google Scholar] [CrossRef]
- Abdulaal, M.J.; Ibrahem, M.I.; Mahmoud, M.; Bello, S.A.; Aljohani, A.J.; Milyani, A.H.; Abusorrah, A.M. DRFD: Deep Learning-Based Real-time and Fast Detection of False Readings in AMI. In Proceedings of the SoutheastCon 2022, Mobile, AL, USA, 26 March–3 April 2022; pp. 682–689. [Google Scholar] [CrossRef]
- Ibrahem, M.I.; Abdelfattah, S.; Mahmoud, M.; Alasmary, W. Detecting Electricity Theft Cyber-attacks in CAT AMI System Using Machine Learning. In Proceedings of the 2021 International Symposium on Networks, Computers and Communications (ISNCC), Dubai, United Arab Emirates, 31 October–2 November 2021; pp. 1–6. [Google Scholar] [CrossRef]
- Abdalzaher, M.S.; Moustafa, S.S.; Abdelhafiez, H.; Farid, W. An Optimized Learning Model Augment Analyst Decisions for Seismic Source Discrimination. IEEE Trans. Geosci. Remote Sens. 2022, 60. [Google Scholar] [CrossRef]
- Roth, J.; Chadalawada, J.; Jain, R.K.; Miller, C. Uncertainty matters: Bayesian probabilistic forecasting for residential smart meter prediction, segmentation, and behavioral measurement and verification. Energies 2021, 14, 1481. [Google Scholar] [CrossRef]
- Aslam, Z.; Javaid, N.; Ahmad, A.; Ahmed, A.; Gulfam, S.M. A combined deep learning and ensemble learning methodology to avoid electricity theft in smart grids. Energies 2020, 13, 5599. [Google Scholar] [CrossRef]
- Qiu, Y.L.; Wang, Y.D.; Xing, B. Grid impact of non-residential distributed solar energy and reduced air emissions: Empirical evidence from individual-consumer-level smart meter data. Appl. Energy 2021, 290, 116804. [Google Scholar] [CrossRef]
- Brown, J.; Abate, A.; Rogers, A. Disaggregation of household solar energy generation using censored smart meter data. Energy Build. 2021, 231, 110617. [Google Scholar] [CrossRef]
- Hussain, S.S.; Tak, A.; Ustun, T.S.; Ali, I. Communication modeling of solar home system and smart meter in smart grids. IEEE Access 2018, 6, 16985–16996. [Google Scholar] [CrossRef]
- Donaldson, D.L.; Jayaweera, D. Effective solar prosumer identification using net smart meter data. Int. J. Electr. Power Energy Syst. 2020, 118, 105823. [Google Scholar] [CrossRef]
- Chatterji, E.; Bazilian, M.D. Smart meter data to optimize combined roof-top solar and battery systems using a stochastic mixed integer programming model. IEEE Access 2020, 8, 133843–133853. [Google Scholar] [CrossRef]
- Abdalzaher, M.S.; Elsayed, H.A. Employing data communication networks for managing safer evacuation during earthquake disaster. Simul. Model. Pract. Theory 2019, 94, 379–394. [Google Scholar] [CrossRef]
- Ghamry, E.; Mohamed, E.K.; Abdalzaher, M.S.; Elwekeil, M.; Marchetti, D.; De Santis, A.; Hegy, M.; Yoshikawa, A.; Fathy, A. Integrating pre-earthquake signatures from different precursor tools. IEEE Access 2021, 9, 33268–33283. [Google Scholar] [CrossRef]
- Moustafa, S.S.; Abdalzaher, M.S.; Khan, F.; Metwaly, M.; Elawadi, E.A.; Al-Arifi, N.S. A Quantitative Site-Specific Classification Approach Based on Affinity Propagation Clustering. IEEE Access 2021, 9, 155297–155313. [Google Scholar] [CrossRef]
- Elhadidy, M.; Abdalzaher, M.S.; Gaber, H. Up-to-date PSHA along the Gulf of Aqaba-Dead Sea transform fault. Soil Dyn. Earthq. Eng. 2021, 148, 106835. [Google Scholar] [CrossRef]
- Abdalzaher, M.S.; El-Hadidy, M.; Gaber, H.; Badawy, A. Seismic hazard maps of Egypt based on spatially smoothed seismicity model and recent seismotectonic models. J. Afr. Earth Sci. 2020, 170, 103894. [Google Scholar] [CrossRef]
- Hegazy, H.I.; Tag Eldien, A.S.; Tantawy, M.M.; Fouda, M.M.; TagElDien, H.A. Real-Time Locational Detection of Stealthy False Data Injection Attack in Smart Grid: Using Multivariate-Based Multi-Label Classification Approach. Energies 2022, 15, 5312. [Google Scholar] [CrossRef]
- Elwekeil, M.; Abdalzaher, M.S.; Seddik, K. Prolonging smart grid network lifetime through optimising number of sensor nodes and packet length. IET Commun. 2019, 13, 2478–2484. [Google Scholar] [CrossRef]
- Vallent, T.F.; Hanyurwimfura, D.; Mikeka, C. Efficient certificate-less aggregate signature scheme with conditional privacy-preservation for vehicular ad hoc networks enhanced smart grid system. Sensors 2021, 21, 2900. [Google Scholar] [CrossRef]
- Farao, A.; Veroni, E.; Ntantogian, C.; Xenakis, C. P4G2Go: A Privacy-Preserving Scheme for Roaming Energy Consumers of the Smart Grid-to-Go. Sensors 2021, 21, 2686. [Google Scholar] [CrossRef]
- Llaria, A.; Dos Santos, J.; Terrasson, G.; Boussaada, Z.; Merlo, C.; Curea, O. Intelligent Buildings in Smart Grids: A Survey on Security and Privacy Issues Related to Energy Management. Energies 2021, 14, 2733. [Google Scholar] [CrossRef]
- Son, Y.B.; Im, J.H.; Kwon, H.Y.; Jeon, S.Y.; Lee, M.K. Privacy-preserving peer-to-peer energy trading in blockchain-enabled smart grids using functional encryption. Energies 2020, 13, 1321. [Google Scholar] [CrossRef]
- Syed, D.; Refaat, S.S.; Bouhali, O. Privacy preservation of data-driven models in smart grids using homomorphic encryption. Information 2020, 11, 357. [Google Scholar] [CrossRef]
- Dwork, C.; Roth, A. The algorithmic foundations of differential privacy. Found. Trends® Theor. Comput. Sci. 2014, 9, 211–407. [Google Scholar] [CrossRef]
- Manivannan, M.; Najafi, B.; Rinaldi, F. Machine learning-based short-term prediction of air-conditioning load through smart meter analytics. Energies 2017, 10, 1905. [Google Scholar] [CrossRef]
- Hochreiter, S.; Schmidhuber, J. Long Short-Term Memory. Neural Comput. 1997, 9, 1735–1780. [Google Scholar] [CrossRef] [PubMed]
- Gers, F.; Schmidhuber, J.; Cummins, F. Learning to forget: Continual prediction with LSTM. In Proceedings of the 1999 Ninth International Conference on Artificial Neural Networks ICANN 99, (Conf. Publ. No. 470), Bristol, UK, 6–9 September 1999; Volume 2, pp. 850–855. [Google Scholar] [CrossRef]
- Werbos, P.J. Backpropagation through time: What it does and how to do it. Proc. IEEE 1990, 78, 1550–1560. [Google Scholar] [CrossRef]
- Bengio, Y.; Simard, P.; Frasconi, P. Learning long-term dependencies with gradient descent is difficult. IEEE Trans. Neural Netw. 1994, 5, 157–166. [Google Scholar] [CrossRef]
- Gers, F.A.; Schmidhuber, J.; Cummins, F. Learning to forget: Continual prediction with LSTM. Neural Comput. 2000, 12, 2451–2471. [Google Scholar] [CrossRef]
- Ozay, M.; Esnaola, I.; Yarman Vural, F.T.; Kulkarni, S.R.; Poor, H.V. Machine Learning Methods for Attack Detection in the Smart Grid. IEEE Trans. Neural Netw. Learn. Syst. 2016, 27, 1773–1786. [Google Scholar] [CrossRef]
- Parvez, I.; Sarwat, A.I.; Wei, L.; Sundararajan, A. Securing metering infrastructure of smart grid: A machine learning and localization based key management approach. Energies 2016, 9, 691. [Google Scholar] [CrossRef]
- Babar, M.; Tariq, M.U.; Jan, M.A. Secure and resilient demand side management engine using machine learning for IoT-enabled smart grid. Sustain. Cities Soc. 2020, 62, 102370. [Google Scholar] [CrossRef]
- Esmalifalak, M.; Liu, L.; Nguyen, N.; Zheng, R.; Han, Z. Detecting stealthy false data injection using machine learning in smart grid. IEEE Syst. J. 2014, 11, 1644–1652. [Google Scholar] [CrossRef]
- Wang, B.; Wu, Y.; Liu, K.R. Game theory for cognitive radio networks: An overview. Comput. Netw. 2010, 54, 2537–2561. [Google Scholar] [CrossRef]
- Roy, S.; Ellis, C.; Shiva, S.; Dasgupta, D.; Shandilya, V.; Wu, Q. A survey of game theory as applied to network security. In Proceedings of the System Sciences (HICSS), 2010 43rd Hawaii International Conference, Honolulu, HI, USA, 5–8 January 2010; pp. 1–10. [Google Scholar]
- Han, Z. Game Theory in Wireless and Communication Networks: Theory, Models, and Applications; Cambridge University Press: Cambridge, UK, 2012. [Google Scholar]
- Shi, H.Y.; Wang, W.L.; Kwok, N.M.; Chen, S.Y. Game theory for wireless sensor networks: A survey. Sensors 2012, 12, 9055–9097. [Google Scholar] [CrossRef] [PubMed]
- Zhang, Y.; Guizani, M. Game Theory for Wireless Communications and Networking; CRC Press: Boca Raton, FL, USA, 2011. [Google Scholar]
- Yang, F.; Zhou, X.; Jia, G.; Zhang, Q. A Non-cooperative Game Approach for Intrusion Detection in Smartphone Systems. In Proceedings of the Communication Networks and Services Research Conference (CNSR), 2010 Eighth Annual, Montreal, QC, Canad, 11–14 May 2010; pp. 146–151. [Google Scholar]
- Abdalzaher, M.S.; Seddik, K.; Elsabrouty, M.; Muta, O.; Furukawa, H.; Abdel-Rahman, A. Game theory meets wireless sensor networks security requirements and threats mitigation: A survey. Sensors 2016, 16, 1003. [Google Scholar] [CrossRef] [PubMed]
- Abdalzaher, M.S.; Muta, O.; Seddik, K.; Abdel-Rahman, A.; Furukawa, H. B-18-40 A Simplified Stackelberg Game Approach for Securing Data Trustworthiness in Wireless Sensor Networks. In Proceedings of the 2016 IEICE General Conference (IEICE), Fukuoka, Japan, 17 March 2016; p. 538. [Google Scholar]
- Abdalzaher, M.S.; Muta, O. Employing game theory and TDMA protocol to enhance security and manage power consumption in WSNs-based cognitive radio. IEEE Access 2019, 7, 132923–132936. [Google Scholar] [CrossRef]
- Abdalzaher, M.S.; Seddik, K.; Muta, O. Using Stackelberg game to enhance cognitive radio sensor networks security. IET Commun. 2017, 11, 1503–1511. [Google Scholar] [CrossRef]
- Abdalzaher, M.S.; Seddik, K.; Muta, O. An effective Stackelberg game for high-assurance of data trustworthiness in WSNs. In Proceedings of the 2017 IEEE Symposium on Computers and Communications (ISCC), Heraklion, Greece, 3–6 July 2017; pp. 1257–1262. [Google Scholar]
- Abdalzaher, M.S.; Seddik, K.; Muta, O. Using repeated game for maximizing high priority data trustworthiness in wireless sensor networks. In Proceedings of the 2017 IEEE Symposium on Computers and Communications (ISCC), Heraklion, Greece, 3–6 July 2017; pp. 552–557. [Google Scholar]
- Abdalzaher, M.S.; Samy, L.; Muta, O. Non-zero-sum game-based trust model to enhance wireless sensor networks security for IoT applications. IET Wirel. Sens. Syst. 2019, 9, 218–226. [Google Scholar] [CrossRef]
- Li, F.; Luo, B.; Liu, P. Secure information aggregation for smart grids using homomorphic encryption. In Proceedings of the 2010 First IEEE International Conference on Smart Grid Communications, Gaithersburg, MD, USA, 4–6 October 2010; pp. 327–332. [Google Scholar]
- Bagaa, M.; Younis, M.; Balasingham, I. Optimal strategies for data aggregation scheduling in wireless sensor networks. In Proceedings of the 2015 IEEE Global Communications Conference (GLOBECOM), San Diego, CA, USA, 6–10 December 2015; pp. 1–6. [Google Scholar]
- Efthymiou, C.; Kalogridis, G. Smart grid privacy via anonymization of smart metering data. In Proceedings of the 2010 first IEEE international conference on smart grid communications, Gaithersburg, MD, USA, 4–6 October 2010; pp. 238–243. [Google Scholar]
- Rottondi, C.; Verticale, G.; Krauss, C. Distributed privacy-preserving aggregation of metering data in smart grids. IEEE J. Sel. Areas Commun. 2013, 31, 1342–1354. [Google Scholar] [CrossRef]
- Wang, Y.; Raval, N.; Ishwar, P.; Hattori, M.; Hirano, T.; Matsuda, N.; Shimizu, R. On methods for privacy-preserving energy disaggregation. In Proceedings of the 2017 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP), New Orleans, LA, USA, 5–9 March 2017; pp. 6404–6408. [Google Scholar]
- Barbosa, P.; Brito, A.; Almeida, H. A technique to provide differential privacy for appliance usage in smart metering. Inf. Sci. 2016, 370, 355–367. [Google Scholar] [CrossRef]
- Ford, V.; Siraj, A. Clustering of smart meter data for disaggregation. In Proceedings of the 2013 IEEE Global Conference on Signal and Information Processing, Austin, TX, USA, 3–5 December 2013; pp. 507–510. [Google Scholar]
- Ford, V.; Siraj, A. Applications of machine learning in cyber security. In Proceedings of the 27th International Conference on Computer Applications in Industry and Engineering, Kota Kinabalu, Malaysia, 28 September–1 October 2014; Volume 118. [Google Scholar]
- Zhuang, W.; Ye, Y.; Chen, Y.; Li, T. Ensemble clustering for internet security applications. IEEE Trans. Syst. Man Cybern. Part C (Appl. Rev.) 2012, 42, 1784–1796. [Google Scholar] [CrossRef]
- Sedjelmaci, H.; Feham, M. Novel hybrid intrusion detection system for clustered wireless sensor network. arXiv 2011, arXiv:1108.2656. [Google Scholar] [CrossRef]
- Ren, S.; Chen, D.; Tao, Y.; Xu, S.; Wang, G.; Yang, Z. Intelligent terminal security technology of power grid sensing layer based upon information entropy data mining. J. Intell. Syst. 2022, 31, 817–834. [Google Scholar] [CrossRef]
- Hock, D.; Kappes, M.; Ghita, B. Using multiple data sources to detect manipulated electricity meter by an entropy-inspired metric. Sustain. Energy Grids Netw. 2020, 21, 100290. [Google Scholar] [CrossRef]
- Singh, S.K.; Bose, R.; Joshi, A. Entropy-based electricity theft detection in AMI network. IET Cyber-Phys. Syst. Theory Appl. 2018, 3, 99–105. [Google Scholar] [CrossRef]
- Alnasser, A.; Sun, H. A fuzzy logic trust model for secure routing in smart grid networks. IEEE Access 2017, 5, 17896–17903. [Google Scholar] [CrossRef]
- Batista, E.A.; de Brito, M.A.; Siqueira, J.C.; Dias, J.C.; Gomez, R.C.; Catharino, M.F.; Gomes, M.B. A Multifunctional Smart Meter Using ANN-PSO Flux Estimation and Harmonic Active Compensation with Fuzzy Voltage Regulation. Sensors 2021, 21, 4154. [Google Scholar] [CrossRef]
- Zhou, W.; Ardakanian, O.; Zhang, H.T.; Yuan, Y. Bayesian learning-based harmonic state estimation in distribution systems with smart meter and DPMU data. IEEE Trans. Smart Grid 2019, 11, 832–845. [Google Scholar] [CrossRef]
- Velusamy, D.; Pugalendhi, G.K. Fuzzy integrated Bayesian Dempster–Shafer theory to defend cross-layer heterogeneity attacks in communication network of Smart Grid. Inf. Sci. 2019, 479, 542–566. [Google Scholar] [CrossRef]
| Abbreviation | Description |
|---|---|
| SMs | Smart Meters |
| PG | Power Grid |
| KL | Kullback–Leibler |
| ANN | Artificial Neural Network |
| RNN | Recurrent Neural Network |
| LSTM | Long Short-Term Memory |
| DNN | Deep Neural Network |
| ML | Machine Learning |
| DL | Deep Learning |
| DP | Differential Privacy |
| ETD | Electrical Theft Detection |
| Adaboost | Adaptive Boost |
| AC | Alternative Current |
| PGN | Power Grid Network |
| HPPs | High-Priority Packets |
| HPT | High-Priority Data Trustworthiness |
| GAP | Generative Adversarial Privacy |
| NE | Nash Equilibrium |
| HC | Hierarchical Clustering |
| KM | K-Medoids |
| FPGA | Field Programmable Gate Array |
| VHDL | VHSIC Hardware Description Language |
| DPMDs | Distribution-level Phasor Measurement Devices |
| MAC | Medium Access Control |
| BDST | Dempster–Shafer theory |
| Notation | Description |
|---|---|
| Releaser loss function | |
| Attacker loss function | |
| The releaser parameter | |
| The attacker parameter | |
| A parameter that controls the privacy-utility trade-off | |
| The released data | |
| The useful data | |
| The private data | |
| Cell state | |
| Hidden state | |
| Forget gate | |
| and | Input gates |
| Output gate | |
| b | The biases |
| K | Input weights |
| V | Recurrent weights |
| T | Total period |
| The utility of the player | |
| The action of the player | |
| A | The actions of all players |
| N | The number of players |
| The optimal action | |
| The strategies of all players except i |
| Security Model | Advantages | Disadvantages | Recommendation |
|---|---|---|---|
| Game theory | The utility of the nodes is calculated when the association between nodes is analyzed as a cooperative and non-cooperative game. The game model addresses the logical issue involving the rational participants. | Complexity of implementation. | Medium |
| Clustering | The cluster’s node rearrangement and network scalability. Easy to put into action. | Very significant overheads for control. Certain protocols have a long transmission latency. Sophisticated algorithms. | Low |
| Bayesian | The degree of confidence is taken into account while making decisions. | Scalable network design cannot be taken into account since assessment is solely focused on the node’s QoS. | High |
| Entropy | Inspired by the theory of thermodynamics that deals with the degree of uncertainty in a signal or random occurrence, employed for ad hoc. | Handles attacks individually. | Low |
| Fuzzy | To address a control issue, it inserts a number of if–then rules. | Memory overflow results from adding more if–else statements. | Medium |
| Differential privacy | Can interactively support machine learning models. | Expensive computation, does not support sufficient performance with high complexity problems. | High |
| Machine learning | Easy to pinpoint patterns, supports full automation, supports several applications. | Long training time, high probability of error, big datasets are needed. | High |
| Kullback-Leibler Divergence | It depicts the information loss between expected and ground truth distribution. | Some samples produced by the model may not fit the data distribution. | Meduim |
| Generative Adversarial Privacy | Easy to combine with machine learning, easy to interpret its generated data. | Oscillation of model’s parameters leads to non-convergence, the generator can collapse. | Low |
| Data Aggregation | Data aggregation aids in condensing information from various, dissimilar, and many sources. | If data are not gathered and organized meaningfully, they are difficult to identify and analyze. | Low |
| Pseudonyms | Anonymity. | Twice the identities. | Low |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Abdalzaher, M.S.; Fouda, M.M.; Ibrahem, M.I. Data Privacy Preservation and Security in Smart Metering Systems. Energies 2022, 15, 7419. https://doi.org/10.3390/en15197419
Abdalzaher MS, Fouda MM, Ibrahem MI. Data Privacy Preservation and Security in Smart Metering Systems. Energies. 2022; 15(19):7419. https://doi.org/10.3390/en15197419
Chicago/Turabian StyleAbdalzaher, Mohamed S., Mostafa M. Fouda, and Mohamed I. Ibrahem. 2022. "Data Privacy Preservation and Security in Smart Metering Systems" Energies 15, no. 19: 7419. https://doi.org/10.3390/en15197419
APA StyleAbdalzaher, M. S., Fouda, M. M., & Ibrahem, M. I. (2022). Data Privacy Preservation and Security in Smart Metering Systems. Energies, 15(19), 7419. https://doi.org/10.3390/en15197419








