A Survey of Protocol-Level Challenges and Solutions for Distributed Energy Resource Cyber-Physical Security
Abstract
1. Introduction
- Most DERs communicate using Modbus or DNP3. Specifically, DERs such as smart inverters use Modbus, which is highly insecure since it employs no encryption. Communications from substation to the control center is typically on DNP3 which also has severe security deficiencies;
- Vendors have access to utility OT networks for software/firmware updates, error reporting, performance monitoring, etc. This is highly insecure because a vendor (or an impostor) could successfully access other critical devices on the same network;
- Manufacturers typically install Raspberry Pi-powered protection modules, and configure them to the Dynamic Host Configuration Protocol (DHCP) mode using which they communicate with the utility network;
- Utilities also do not include cybersecurity requirements in their procurement language for DER equipment purchases because they assume the products come with adequate security mechanisms;
- There is no mechanism today where patches or firmware get downloaded to an isolated system outside the OT network of concern, get inspected for data integrity and vulnerabilities, and only then be uploaded to the devices which need patching in the OT network;
- Considering the minimal DER penetration into distribution networks currently, security is not given much importance, but with the increasing rate of integration of DERs, security at the device and protocol levels would be of utmost significance;
- Regulatory guidelines such as the North American Electric Reliability Corporation (NERC) Critical Infrastructure Protection (CIP) have defined cybersecurity requirements but only for the transmission grid systems. Moreover, co-operatives pay greatest attention just to NERC CIP, but in this new scenario, they must explore their security requirements beyond what is specified in the guidelines.
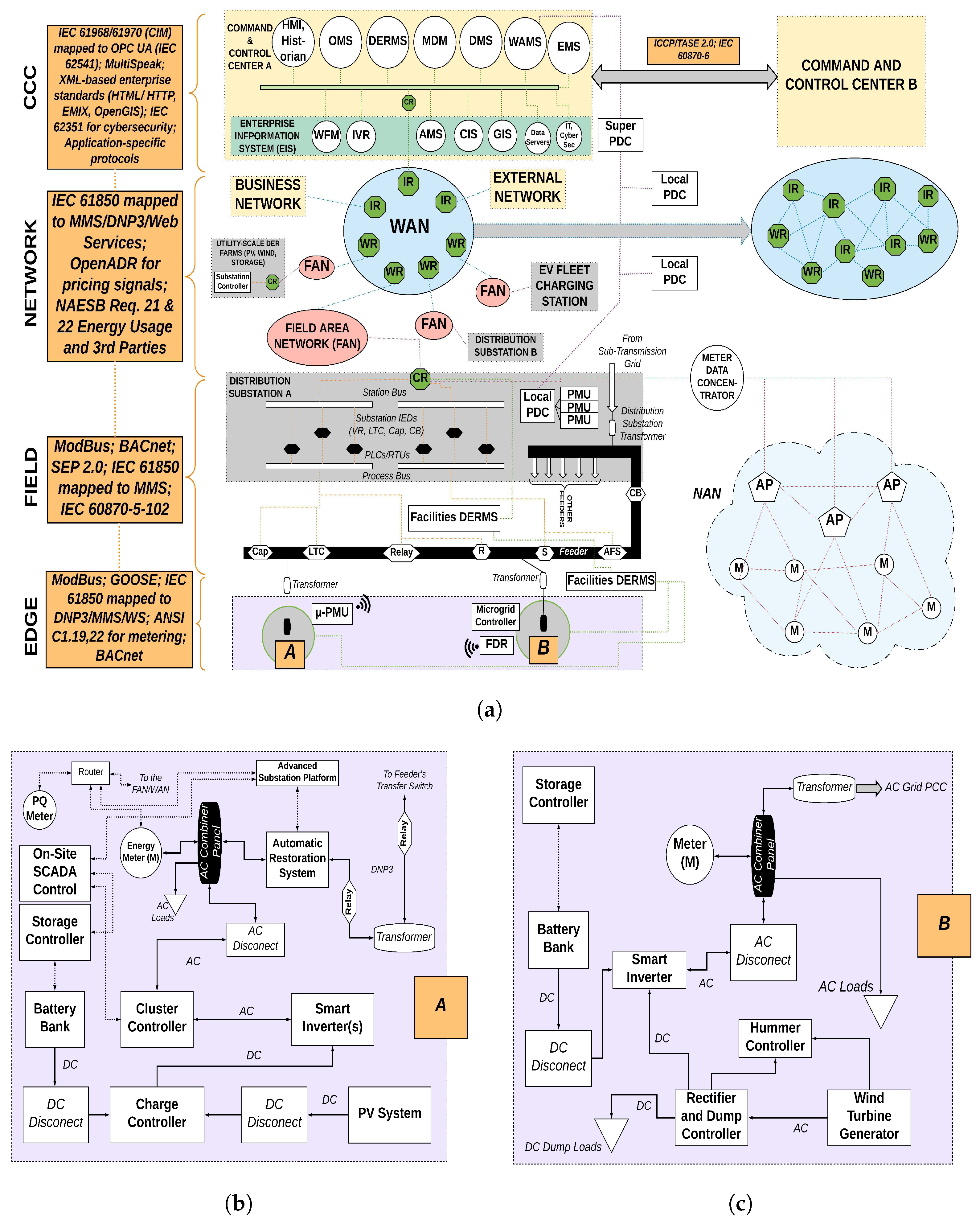
2. DER Communications Architecture
2.1. Protocol Mapping
2.2. Architecture
2.2.1. Edge and Field
2.2.2. Network
2.2.3. CCC
3. DER Communication Vulnerabilities
3.1. Physical (Layer 1)
3.2. Data Link (Layer 2)
3.3. Network (Layer 3)
3.4. Transport (Layer 4)
4. Potential Cyberattacks and Corresponding Solutions to Secure DER Communications
4.1. Physical (Layer 1)
4.2. Data Link (Layer 2)
4.3. Network (Layer 3)
4.4. Transport (Layer 4)
4.5. Key Observations
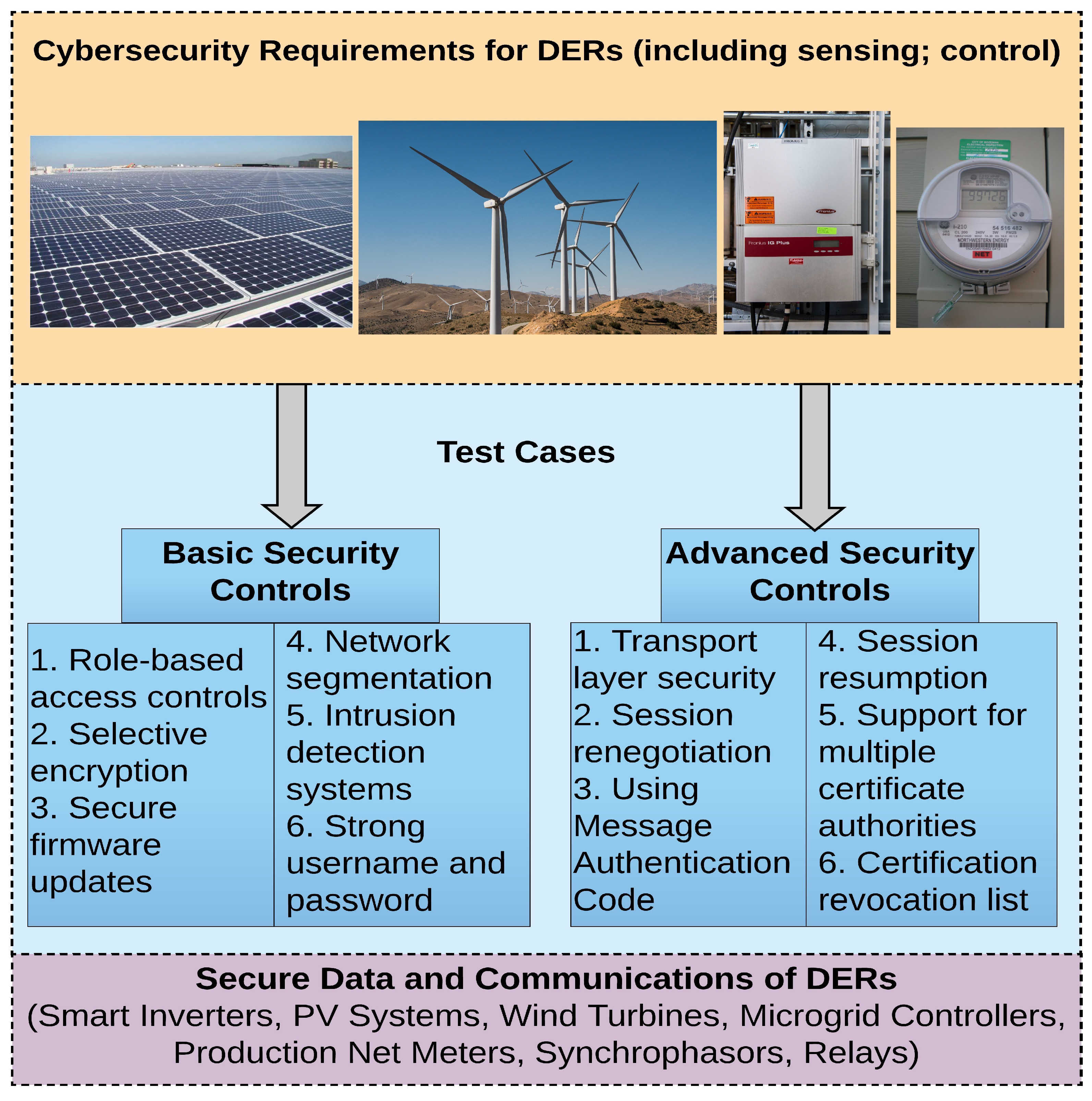
5. Future Work
5.1. Surveying Layers 5 through 7, GWAC Interoperability Stack
5.2. Introducing the Significance of NREL’s Layered Defense Model for DER Security
- Strictly implementing role-based access controls on the DER devices and network components;
- Employing sound network segmentation principles to create different VLANs for information technology, operational technology and business networks;
- Conducting regular upgrades of patches to the application software or DER firmware and ensuring that an effective patch management process is in place;
- Using strong passwords that are immune to dictionary attacks and password cracking, including modifying the default passwords that the DER devices are assigned at the time of manufacturing/installation;
- Employing selective encryption to reduce the processing overhead incurred in the encryption and decryption steps, considering that the DER devices are located at remote fields and are resource-constrained;
- Padding the DER devices with network front-ends such as inline blocking and protocol-level filtering tools that validate the integrity of incoming and outgoing messages before being passed onto the actual devices;
- Practicing strong port-hardening techniques such as disabling unused ports and closely monitoring the active ports available for connection to different client application requests.
- Employing TLS versions 1.2 or 1.3 and recommended cipher suites to comply with the NIST guidelines;
- Supporting session resumption that uses a secret session key for scenarios where the session stays disconnected for a time less than the TLS session resumption time;
- Supporting session renegotiation that uses a secret session key for scenarios where the session stays disconnected for a time more than the TLS session renegotiation time;
- Supporting the use of message authentication codes and multiple certificate authorities when communicating across DER domains;
- Maintaining an active certificate revocation list to bar connection requests coming from entities with expired or blacklisted certificates.
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- INL. Cyber Threat and Vulnerability Analysis of the U.S. Electric Sector; Idaho National Laboratory (INL) Mission Support Center Analysis Report; Idaho National Laboratory: Idaho Falls, ID, USA, 2016.
- Otuoze, A.O.; Mustafa, M.W.; Larik, R.M. Smart grids security challenges: Classification by sources of threats. J. Electr. Syst. Inf. Technol. 2018. [Google Scholar] [CrossRef]
- Ozgur, U.; Nair, H.T.; Sundararajan, A.; Akkaya, K.; Sarwat, A.I. An Efficient MQTT Framework for Control and Protection of Networked Cyber-Physical Systems. In Proceedings of the 2017 IEEE Conference on Communications and Network Security (CNS), Las Vegas, NV, USA, 9–11 October 2017. [Google Scholar]
- Eder-Neuhauser, P.; Zseby, T.; Fabini, J.; Vormayr, G. Cyber attack models for smart grid environments. Sustain. Energy Grids Netw. 2017, 12, 10–29. [Google Scholar] [CrossRef]
- NIST. NISTIR Guidelines for Smart Grid Cybersecurity Revision 1; NIST: Gaithersburg, MD, USA, 2014.
- D.O.E. Cybersecurity Capability Maturity Model Version 1.1.; U.S. DOE Technical Report; U.S. Department of Energy: Washington, DC, USA, 2014.
- NERC. Improving Human Performance: From Individual to Organization and Sustaining the Results; North American Electric Reliability Corporation (NERC) Technical Presentation; NERC: Atlanta, GA, USA, 2012. [Google Scholar]
- Benoit, J. Making Sense Out of Smart Grid Cyber Security Standards; White Paper by Cooper Power Systems; Eaton: Cleveland, OH, USA, 2013. [Google Scholar]
- Lee, R.M.; Assante, M.J.; Conway, T. CrashOverride: Analysis of the Threat to Electric Grid Operations; Dragos Technical Report; Dragos Inc.: Hanover, MD, USA, 2016. [Google Scholar]
- SANS. The Impact of Dragonfly Malware on Industrial Control Systems; SANS Institute InfoSec Reading Room Technical Report; SANS Institute: Singapore, 2016. [Google Scholar]
- US-CERT. Russian Government Cyber Activity Targeting Energy and Other Critical Infrastructure Sectors; US Computer Emergency Readiness Team (CERT) Alert (TA18-074A); US-CERT: Washington, DC, USA, 2018.
- Dragos. Analysis of the Cyber Attack on the Ukrainian Power Grid; SANS Industrial Control Systems Electricity Information Sharing and Analysis Center Technical Report; Dragos Inc.: Hanover, MD, USA, 2017. [Google Scholar]
- Hernandez, J.C.; Bueno, P.G.; Rus-Casas, C. Enhanced utility-scale photovoltaic units with frequency support functions and dynamic grid support for transmission systems. IET Renew. Power Gener. 2017, 11, 361–372. [Google Scholar] [CrossRef]
- Hernandez, J.C.; Sanchez-Sutil, F.; Vidal, P.G.; Rus-Casas, C. Primary frequency control and dynamic grid support for vehicle-to-grid intransmission systems. J. Electr. Power Energy Syst. 2018, 100, 152–166. [Google Scholar] [CrossRef]
- Anzalchi, A.; Sundararajan, A.; Wei, L.; Moghadasi, A.; Pour, M.M.; Sarwat, A.I. Future Directions to the Application of Distributed Fog Computing in Smart Grid Systems. Smart Grid Anal. Sustain. Urban 2018. [Google Scholar] [CrossRef]
- Zimmerman, H. OSI Reference Model-The IS0 Model of Architecture for Open Systems Interconnection. IEEE Trans. Commun. 1980, 28, 425–432. [Google Scholar] [CrossRef]
- Surman, G. Understanding Security Using the OSI Model; SANS Institute InfoSec Reading Room Technical Report; SANS Institute: Singapore, 2002. [Google Scholar]
- Buffenoir, T. A Layered Security Model: OSI and Information Security. Comput. Stand. Interfaces 1988, 145–150. [Google Scholar] [CrossRef]
- Holl, K. OSI Defense in Depth to Increase Application Security; SANS Security Essentials GSEC Practical Assignment Version 1.4b; SANS Institute: Singapore, 2003. [Google Scholar]
- Pace, K. A Layered Security Model: OSI and Information Security; SANS Institute Global Information Assurance Certification Paper; SANS Institute: Singapore, 2004. [Google Scholar]
- Bellovin, S. Security Problems in the TCP/IP Protocol Suite. Comput. Commun. Rev. 1989, 19, 32–48. [Google Scholar] [CrossRef]
- Mateti, P. Security Issues in the TCP/IP Suite. In Security in Distributed and Networking Systems; World Scientific Review Volume: Singapore, 2006. [Google Scholar]
- Dominguez, J. An Overview of Defense in Depth at Each Layer of the TCP/IP Model; SANS Institute Global Information Assurance Certification Paper; SANS Institute: Singapore, 2002. [Google Scholar]
- Kumar, M.; Karthikeyan, S. An Enhanced Security for TCP/IP Protocol Suite. Int. J. Comput. Sci. Mob. Comput. 2013, 2, 331–338. [Google Scholar]
- Idaho National Laboratory (INL). Control Systems Cyber Security: Defense in Depth Strategies; Idaho National Laboratory (INL) Control Systems Security Center Technical Report; Idaho National Laboratory: Idaho Falls, ID, USA, 2006.
- Small, P. Defense in Depth: An Impractical Strategy for Cyber World; SANS Institute InfoSec Reading Room Report; SANS Institute: Singapore, 2011. [Google Scholar]
- SANS Institute. Defense in Depth; SANS Institute InfoSec Reading Room Report; SANS Institute: Singapore, 2001. [Google Scholar]
- Shamim, A.; Fayyaz, B.; Balakrishnan, V. Layered Defense in Depth Model for IT Organizations. In Proceedings of the 2nd International Conference on Innovations in Engineering and Technology, Bengaluru, India, 21–23 August 2014. [Google Scholar]
- Sundararajan, A.; Khan, T.; Aburub, H.; Sarwat, A.I.; Rahman, S. A Tri-Modular Human-on-the-Loop Framework for Intelligent Smart Grid Cyber-Attack Visualization. In Proceedings of the IEEE Southeast Conference, St. Petersburg, FL, USA, 19–22 April 2018. [Google Scholar]
- Intergraph. Smart Grid Operations Command-and-Control Center: Bringing a Common Operating Picture to the Control Room; Intergraph Technical Report: Solution Sheet; Intergraph: Madison, AL, USA, 2010. [Google Scholar]
- Anzalchi, A.; Sarwat, A. A survey on security assessment of metering infrastructure in Smart Grid systems. In Proceedings of the SoutheastCon 2015, Ft. Lauderdale, FL, USA, 9–12 April 2015; pp. 1–4. [Google Scholar] [CrossRef]
- Kott, A.; Wang, C.; Erbacher, R. Advances in Information Security. Cyber Defense and Situation Awareness; Springer: Berlin, Germany, 2014. [Google Scholar]
- Wei, L.; Moghadasi, A.H.; Sundararajan, A.; Sarwat, A.I. Defending mechanisms for protecting power systems against intelligent attacks. In Proceedings of the 2015 10th System of Engineering Conference (SoSE 2015), San Antonio, TX, USA, 17–20 May 2015; pp. 12–17. [Google Scholar] [CrossRef]
- Kott, A.; Lange, M.; Ludwig, J. Approaches to Modeling the Impact of Cyber Attacks on a Mission. arXiv, 2017; arXiv:1710.04148. [Google Scholar]
- Ibrahim, E. A Layered Solution to Cybersecurity; National Renewable Energy Laboratory (NREL) Technical Paper; National Renewable Energy Laboratory (NREL): Golden, CO, USA, 2017.
- Ibrahim, E. Disruptive Ideas for Power Grid Security and Resilience with DER. In Proceedings of the National Renewable Energy Laboratory Annual Cybersecurity and Resilience Workshop, Golden, CO, USA, 9–10 October 2017. [Google Scholar]
- Cisco. Unified Field Area Network Architecture for Distribution Automation; Cisco Technologies White Paper; Cisco: San Jose, CA, USA, 2014. [Google Scholar]
- SEP. Communication Network Challenges and Solutions in the Utility Industry; Sierra Energy Group’s Research & Analysis Division of Energy Central Technical White Paper Report; Sierra Energy: Davis, CA, USA, 2011. [Google Scholar]
- Rodine, C. The Field Area Network (FAN); Electric Power Research Institute (EPRI) Technical Presentation at Stanford University; Electric Power Research Institute (EPRI): Palo Alto, CA, USA, 2011. [Google Scholar]
- Al-Sarawi, S.; Anbar, M.; Alieyan, K.; Alzubaidi, M. Internet of Things (IoT) communication protocols: Review. In Proceedings of the 8th International Conference on Information Technology (ICIT), Bhubaneswar, India, 21–23 December 2017. [Google Scholar] [CrossRef]
- Elyengui, S.; Bouhouchi, R.; Ezzedine, T. The Enhancement of Communication Technologies and Networks for Smart Grid Applications. Int. J. Emerg. Trends Technol. Comput. Sci. 2013, arXiv:1403.0530v1. [Google Scholar]
- Mendes, T.D.P.; Godina, R.; Rodrigues, E.M.G.; Matias, J.C.O.; Catalão, J.P.S. Smart Home Communication Technologies and Applications: Wireless Protocol Assessment for Home Area Network Resources. Energies 2015, 8, 7279–7311. [Google Scholar] [CrossRef]
- Sarwat, A.I.; Sundararajan, A.; Parvez, I. Trends and Future Directions of Research for Smart Grid IoT Sensor Networks. In International Symposium on Sensor Networks, Systems and Security; Springer: Cham, Germany, 2017; pp. 45–61. [Google Scholar]
- SunilKumar, K.N.; Shivashankar. A review on security and privacy issues in wireless sensor networks. In Proceedings of the 2nd IEEE International Conference on Recent Trends in Electronics, Information & Communication Technology (RTEICT), Piscataway, NJ, USA, 19–20 May 2017. [Google Scholar] [CrossRef]
- Robertson, P.; Gordon, C.; Loo, S. Implementing Security for Critical Infrastructure Wide-Area Networks. In Proceedings of the Power and Energy Automation Conference, Spokane, WA, USA, 26–28 March 2013. [Google Scholar]
- ESRI. Enterprise GIS and the Smart Electric Grid; ESRI Technical White Paper; ESRI: Redlands, CA, USA, 2009. [Google Scholar]
- Parra, I.; Rodriguez, A.; Arroyo-Figueroa, G. Electric utility enterprise architecture to support the Smart Grid-Enterprise architecture for the Smart Grid. In Proceedings of the 11th International Conference on Informatics in Control, Automation and Robotics (ICINCO), Vienna, Austria, 2–4 September 2014. [Google Scholar] [CrossRef]
- Parekh, K.; Zhou, J.; McNair, K.; Robinson, G. Utility Enterprise Information Management Strategies. In Proceedings of the Grid-Interop Forum, Albuquerque, NM, USA, 7–9 November 2007. [Google Scholar]
- Modbus Application Protocol Specification V 1.1b3. Available online: http://www.modbus.org/docs/Modbus_Application_Protocol_V1_1b3.pdf (accessed on 2 September 2018).
- ASHRAE. BACnet—A Data Communication Protocol for Building Automation and Control Networks; ANSI ASHRAE Standard Specification; ASHRAE: New York, NY, USA, 2008. [Google Scholar]
- OASIS. Energy Market Information Exchange (EMIX) Version 1.0.; OASIS Committee Specification 02; OASIS: Burlington, MA, USA, 2012. [Google Scholar]
- ABB. DNP3 Communication Protocol Manual; ABB Technical Report Version 1.1.; ABB: Zurich, Switzerland, 2011. [Google Scholar]
- IEEE. 1815.1-2015—IEEE Standard for Exchanging Information between Networks Implementing IEC 61850 and IEEE Std 1815(TM) [Distributed Network Protocol (DNP3)]; IEEE Standards Document; IEEE Power & Energy Society: Piscataway, NJ, USA, 2016. [Google Scholar]
- IEEE. P2030.5—IEEE Approved Draft Standard for Smart Energy Profile Application Protocol; Revision of IEEE Standard 2030.5-2013; IEEE: Piscataway, NJ, USA, 2018. [Google Scholar]
- East, S.; Butts, J.; Papa, M.; Shenoi, S. A Taxonomy of Attacks on the DNP3 Protocol. In Proceedings of the International Conference on Critical Infrastructure Protection, Hanover, NH, USA, 23–25 March 2009. [Google Scholar] [CrossRef]
- Ramaswamy, R. Traffic flow confidentiality security service in OSI computer network architecture. In Proceedings of the IEEE TENCON’90: 1990 IEEE Region 10 Conference on Computer and Communication Systems, Hong Kong, China, 24–27 September 1990. [Google Scholar] [CrossRef]
- Childers, M.; Borrielli, M. IEC61850 substation experiences DPSP 2012. In Proceedings of the 11th IET International Conference on Developments in Power Systems Protection (DPSP), Birmingham, UK, 23–26 April 2012. [Google Scholar] [CrossRef]
- Alzari, A.S. Telecommunication traffic through submarine cables: Security and vulnerabilities. In Proceedings of the 11th International Conference for Internet Technology and Secured Transactions (ICITST), Barcelona, Spain, 5–7 December 2016. [Google Scholar] [CrossRef]
- Luo, G. Wireless transmission of RS232 interface signal based on ZigBee. In Proceedings of the International Conference on Anti-Counterfeiting, Security and Identification, Chengdu, China, 18–20 July 2010. [Google Scholar] [CrossRef]
- Hu, S.; Sun, J. Research on the network security based on radiated virus. In Proceedings of the 2010 International Conference on Information, Networking and Automation (ICINA), Kunming, China, 18–19 October 2010. [Google Scholar] [CrossRef]
- Oberle, A.; Larbig, P.; Kuntze, N.; Rudolph, C. Integrity based relationships and trustworthy communication between network participants. In Proceedings of the IEEE International Conference on Communications (ICC), Sydney, NSW, Australia, 10–14 June 2014. [Google Scholar] [CrossRef]
- Lee, Y.W.; Lee, Y.G. FTTH network survivability security based on massive fiber optic mechanical switch in consolidated central office. In Proceedings of the Digest of the 9th International Conference on Optical Internet (COIN), Jeju, Korea, 11–14 July 2010. [Google Scholar] [CrossRef]
- Conti, M.; Dragoni, N.; Lesyk, V. A Survey of Man in the Middle Attacks. IEEE Commun. Surv. Tutor. 2016, 18. [Google Scholar] [CrossRef]
- Karakoc, E.; Dikbiyik, F. Rapid migration of VMs on a datacenter under cyber attack over optical infrastructure. In Proceedings of the 2016 HONET-ICT, Nicosia, Cyprus, 13–14 October 2016. [Google Scholar] [CrossRef]
- Heo, Y.; Na, J. Development of unidirectional security gateway appliance using intel 82580EB NIC interface. In Proceedings of the International Conference on Information and Communication Technology Convergence (ICTC), Jeju, Korea, 19–21 October 2016. [Google Scholar] [CrossRef]
- Reddi, R.M.; Srivastava, A.K. Real time test bed development for power system operation, control and cyber security. In Proceedings of the North American Power Symposium, Arlington, TX, USA, 26–28 September 2010. [Google Scholar] [CrossRef]
- Stefanov, A.; Liu, C. Cyber-power system security in a smart grid environment. In Proceedings of the IEEE PES Innovative Smart Grid Technologies (ISGT), Washington, DC, USA, 16–20 January 2012. [Google Scholar] [CrossRef]
- Hadbah, A.; Kalam, A.; Zayegh, Z. Powerful IEDs, ethernet networks and their effects on IEC 61850-based electric power utilities security. In Proceedings of the Australasian Universities Power Engineering Conference (AUPEC), Melbourne, VIC, Australia, 19–22 November 2017. [Google Scholar] [CrossRef]
- Al-Salloum, Z.S.; Wolthusen, S.D. A link-layer-based self-replicating vulnerability discovery agent. In Proceedings of the IEEE symposium on Computers and Communications, Riccione, Italy, 22–25 June 2010. [Google Scholar] [CrossRef]
- Sharma, G.; Pandey, N.; Hussain, I.; Kathri, S.K. Design of framework and analysis of Internet of things at data link layer. In Proceedings of the 2nd International Conference on Telecommunication and Networks (TEL-NET), Noida, India, 10–11 August 2017. [Google Scholar] [CrossRef]
- Cioraca, A.; Voloh, I.; Adamiak, M. What protection engineers need to know about networking. In Proceedings of the 68th Annual Conference for Protective Relay Engineers, College Station, TX, USA, 30 March–2 April 2015. [Google Scholar] [CrossRef]
- Tu, K. Communications Link Layer Security. In Proceedings of the International Conference on Communication Technology, Guilin, China, 27–30 November 2006. [Google Scholar] [CrossRef]
- Lu, Z.; Shakeri, A.; Razo, M.; Tacca, M.; Fumagalli, A.; Galimberti, G.M.; Martinelli, G.; Swallow, G. Orchestration of reliable three-layer networks. In Proceedings of the 19th International Conference on Transparent Optical Networks (ICTON), Girona, Spain, 2–6 July 2017. [Google Scholar] [CrossRef]
- Gerisch, A.; Lawniczak, A.T.; Di-Stefano, B. Building blocks of a simulation environment of the OSI network layer of packet-switching networks. In Proceedings of the CCECE 2003–Canadian Conference on Electrical and Computer Engineering. Toward a Caring and Humane Technology, Montreal, QC, Canada, 4–7 May 2003. [Google Scholar] [CrossRef]
- Embry, J.; Manson, P.; Milham, D. An open network management architecture: OSI/NM Forum architecture and concepts. IEEE Netw. 1990, 4, 14–22. [Google Scholar] [CrossRef]
- Li, Y.; Li, D.; Cui, W.; Zhang, R. Research based on OSI model. In Proceedings of the IEEE 3rd International Conference on Communication Software and Networks, Xi’an, China, 27–29 May 2011. [Google Scholar] [CrossRef]
- Wilder, R. Fairness issues for mixed TCP/OSI internets. In Proceedings of the MILCOM 91—Conference Record, McLean, VA, USA, 4–7 November 1991. [Google Scholar] [CrossRef]
- Wang, Y.; Xiang, C. IP network-based trust management system. In Proceedings of the Eighth International Conference on Fuzzy Systems and Knowledge Discovery (FSKD), Shanghai, China, 26–28 July 2011. [Google Scholar] [CrossRef]
- Zdrnja, B. Malicious JavaScript Insertion through ARP Poisoning Attacks. IEEE Secur. Priv. 2009, 7. [Google Scholar] [CrossRef]
- Mirkovic, J.; Kissel, E. Comparative Evaluation of Spoofing Defenses. IEEE Trans. Dependable Secur. Comput. 2009, 8. [Google Scholar] [CrossRef]
- Gupta, N.; Jain, A.; Saini, P.; Gupta, V. DDoS attack algorithm using ICMP flood. In Proceedings of the 3rd International Conference on Computing for Sustainable Global Development (INDIACom), New Delhi, India, 16–18 March 2016. [Google Scholar]
- Raman, L.G. OSI upper layer protocol requirements for TMN operations. In Proceedings of the IEEE INFOCOM’88, Seventh Annual Joint Conference of the IEEE Computer and Communcations Societies. Networks: Evolution or Revolution? New Orleans, LA, USA, 27–31 March 1988. [Google Scholar] [CrossRef]
- Silva, S.D. Transport Level Address for application level communication. In Proceedings of the 2nd IEEE International Conference on Computer Science and Information Technology, Beijing, China, 8–11 August 2009. [Google Scholar] [CrossRef]
- Malhotra, A.; Sharma, V.; Gandhi, P.; Purohit, N. UDP based chat application. In Proceedings of the 2nd International Conference on Computer Engineering and Technology, Chengdu, China, 16–18 April 2010. [Google Scholar] [CrossRef]
- Cai, L.; Pan, Y.; Guo, Y. Research on the effects of transport protocols on the application performance based on OPNET. In Proceedings of the IEEE/ACIS 15th International Conference on Computer and Information Science (ICIS), Okayama, Japan, 26–29 June 2016. [Google Scholar] [CrossRef]
- Pakanati, C.; Padmavathamma, M.; Reddy, N.R. Performance Comparison of TCP, UDP, and TFRC in Wired Networks. In Proceedings of the IEEE International Conference on Computational Intelligence & Communication Technology, Ghaziabad, India, 13–14 February 2015. [Google Scholar] [CrossRef]
- Wang, S.; Xu, D.; Yan, S. Analysis and application of Wireshark in TCP/IP protocol teaching. In Proceedings of the International Conference on E-Health Networking Digital Ecosystems and Technologies (EDT), Shenzhen, China, 17–18 April 2010. [Google Scholar] [CrossRef]
- Xiao, S.; Deng, L.; Li, S.; Wang, X. Integrated TCP/IP protocol software testing for vulnerability detection. In Proceedings of the International Conference on Computer Networks and Mobile Computing, Shanghai, China, 20–23 October 2003. [Google Scholar] [CrossRef]
- Weerathunga, P.E.; Cioraca, A. The importance of testing Smart Grid IEDs against security vulnerabilities. In Proceedings of the 69th Annual Conference for Protective Relay Engineers (CPRE), College Station, TX, USA, 4–7 April 2016. [Google Scholar] [CrossRef]
- Jiwen, C.; Shanmei, L. Cyber security vulnerability assessment for Smart substations. In Proceedings of the IEEE PES Asia-Pacific Power and Energy Engineering Conference (APPEEC), Xi’an, China, 25–28 October 2016. [Google Scholar] [CrossRef]
- Wang, Y.; Gamage, T.T.; Hauser, C.H. Security Implications of Transport Layer Protocols in Power Grid Synchrophasor Data Communication. IEEE Trans. Smart Grid 2016, 7. [Google Scholar] [CrossRef]
- Hung, T.C.; Khanh, T.P. Analyze and Evaluate the performance of SCTP at transport layer. In Proceedings of the 12th International Conference on Advanced Communication Technology (ICACT), Phoenix Park, Korea, 7–10 February 2010. [Google Scholar]
- Ramnath, D.; Deepak, T.; Krishnakumar, K.; Vijayaraghavan, S.; Ramanathan, R. An improved secret key update for multiple intersymbol obfuscation in physical layer security. In Proceedings of the International Conference on Advances in Computing, Communications and Informatics (ICACCI), Udupi, India, 13–16 September 2017. [Google Scholar] [CrossRef]
- Yan, J.; Liu, C.; Govindarasu, M. Cyber intrusion of wind farm SCADA system and its impact analysis. In Proceedings of the IEEE/PES Power Systems Conference and Exposition, Phoenix, AZ, USA, 20–23 March 2011. [Google Scholar] [CrossRef]
- Aryai, S.; Binu, G.S. Cross layer approach for detection and prevention of Sinkhole Attack using a mobile agent. In Proceedings of the 2nd International Conference on Communication and Electronics Systems (ICCES), Coimbatore, India, 19–20 October 2017. [Google Scholar] [CrossRef]
- Kartalopoulos, S.V. Quantum Cryptography For Secure Optical Networks. In Proceedings of the IEEE International Conference on Communications, Glasgow, Scotland, 24–28 June 2007. [Google Scholar] [CrossRef]
- Guruprasad, A.; Pandey, P.; Prashant, B. Security features in Ethernet switches for access networks. In Proceedings of the TENCON 2003 Conference on Convergent Technologies for Asia-Pacific Region, Bangalore, India, 15–17 October 2003. [Google Scholar] [CrossRef]
- IEEE. 802.1AEcg-2017—IEEE Standard for Local and Metropolitan Area Networks—Media Access Control (MAC) Security—Amendment 3: Ethernet Data Encryption Devices; IEEE Standards Document; IEEE: Piscataway, NJ, USA, 2017. [Google Scholar] [CrossRef]
- Witzke, E.L.; Gossage, S.; Wiener, D.J. An Architecture for Multi-Security Level Network Traffic. In Proceedings of the 40th Annual 2006 International Carnahan Conference on Security Technology, Lexington, KY, USA, 16–19 October 2006. [Google Scholar] [CrossRef]
- Wahid, K.F. Maximizing Ethernet Security by Switch-Based Single Secure Domain. In Proceedings of the Seventh International Conference on Information Technology: New Generations, Las Vegas, NV, USA, 12–14 April 2010. [Google Scholar] [CrossRef]
- Su, S.; Duan, X.; Zeng, X.; Chan, W.L.; Li, K.K. Context Information based Cyber Security Defense of Protection System. In Proceedings of the IEEE Power Engineering Society General Meeting, Tampa, FL, USA, 24–28 June 2007. [Google Scholar] [CrossRef]
- Penera, E.; Chasaki, D. Packet scheduling attacks on shipboard networked control systems. In Proceedings of the 2015 Resilience Week, Philadelphia, PA, USA, 18–20 August 2015. [Google Scholar] [CrossRef]
- Kirkpatrick, M.E. A security standard for LANs. In Proceedings of the Fifth Annual Computer Security Applications Conference, Tucson, AZ, USA, 4–8 December 1989. [Google Scholar] [CrossRef]
- Kiravuo, T.; Sarela, M.; Manner, J. A Survey of Ethernet LAN Security. IEEE Commun. Surv. Tutor. 2013, 15. [Google Scholar] [CrossRef]
- Hadjina, N.; Thompson, P. Data security on Ethernet LANs. In Proceedings of the 10th Mediterranean Electrotechnical Conference. Information Technology and Electrotechnology for the Mediterranean Countries. Proceedings. MeleCon, 2000 (Cat. No.00CH37099), Lemesos, Cyprus, 29–31 May 2000. [Google Scholar] [CrossRef]
- Yeung, K.H.; Yan, F.; Leung, C. Improving Network Infrastructure Security by Partitioning Networks Running Spanning Tree Protocol. In Proceedings of the International Conference on Internet Surveillance and Protection, Cote d’Azur, France, 26–29 August 2006. [Google Scholar] [CrossRef]
- Scott, B.; Xu, J.; Zhang, J.; Brown, A.; Clark, E.; Yuan, X. An interactive visualization tool for teaching ARP spoofing attack. In Proceedings of the IEEE Frontiers in Education Conference (FIE), Indianapolis, IN, USA, 18–21 October 2017. [Google Scholar] [CrossRef]
- Meghana, J.S.; Subashri, T.; Vimal, K.R. A survey on ARP cache poisoning and techniques for detection and mitigation. In Proceedings of the Fourth International Conference on Signal Processing, Communication and Networking (ICSCN), Chennai, India, 16–18 March 2017. [Google Scholar] [CrossRef]
- Bhirud, S.G.; Katkar, V. Light weight approach for IP-ARP spoofing detection and prevention. In Proceedings of the Second Asian Himalayas International Conference on Internet (AH-ICI), Kathmandu, Nepal, 4–6 November 2011. [Google Scholar] [CrossRef]
- Nelson, R. End-to-end encryption at the network layer. In Proceedings of the Fifth Annual Computer Security Applications Conference, Tucson, AZ, USA, 4–8 December 1989. [Google Scholar] [CrossRef]
- Sanaiye, O.A. Short Paper: IP spoofing detection for preventing DDoS attack in Cloud Computing. In Proceedings of the 18th International Conference on Intelligence in Next Generation Networks, Paris, France, 17–19 February 2015. [Google Scholar] [CrossRef]
- Duan, Z.; Yuan, X.; Chandrashekar, J. Controlling IP Spoofing through Interdomain Packet Filters. IEEE Trans. Dependable Secur. Comput. 2007, 5. [Google Scholar] [CrossRef]
- Chuiyi, X.; Yizhi, Z.; Yuan, B.; Shuoshan, L.; Qin, X. A Distributed Intrusion Detection System against flooding Denial of Services attacks. In Proceedings of the 13th International Conference on Advanced Communication Technology (ICACT2011), Seoul, Korea, 13–16 February 2011. [Google Scholar]
- Udhayan, J.; Anitha, R. Demystifying and Rate Limiting ICMP hosted DoS/DDoS Flooding Attacks with Attack Productivity Analysis. In Proceedings of the IEEE International Advance Computing Conference, Patiala, India, 6–7 March 2009. [Google Scholar] [CrossRef]
- Blackridge. BlackRidge TAC Gateways: Quick Start Guide. In BlackRidge Technology User Guide; BlackRidge Technology Inc.: Reno, NV, USA, 2016. [Google Scholar]
- Logeshwari, K.; Lakshmanan, L. Authenticated anonymous secure on demand routing protocol in VANET (Vehicular adhoc network). In Proceedings of the International Conference on Information Communication and Embedded Systems (ICICES), Chennai, India, 23–24 February 2017. [Google Scholar] [CrossRef]
- Sirohi, P.; Agarwal, A.; Tyagi, S. A comprehensive study on security attacks on SSL/TLS protocol. In Proceedings of the 2nd International Conference on Next Generation Computing Technologies (NGCT), Dehradun, India, 14–16 October 2016. [Google Scholar] [CrossRef]
- Dong, K.; Yang, S.; Wang, S. Analysis of low-rate TCP DoS attack against FAST TCP. In Proceedings of the Sixth International Conference on Intelligent Systems Design and Applications, Jinan, China, 16–18 October 2006. [Google Scholar] [CrossRef]
- Kolahi, S.S.; Treseangrat, K.; Sarrafpour, B. Analysis of UDP DDoS flood cyber attack and defense mechanisms on Web Server with Linux Ubuntu 13. In Proceedings of the International Conference on Communications, Signal Processing, and their Applications (ICCSPA’15), Sharjah, UAE, 17–19 February 2015. [Google Scholar] [CrossRef]
- Chen, Z.; Wen, W.; Yu, D. Detecting SIP flooding attacks on IP Multimedia Subsystem (IMS). In Proceedings of the International Conference on Computing, Networking and Communications (ICNC), Maui, HI, USA, 30 January–2 February 2012. [Google Scholar] [CrossRef]
- Narayan, S.; Gupta, R.; Kumar, A.; Ishrar, S.; Khan, Z. Cyber security attacks on network with transition mechanisms. In Proceedings of the International Conference on Computing and Network Communications (CoCoNet), Trivandrum, India, 16–19 December 2015. [Google Scholar] [CrossRef]
- Wang, H.-Y.; Cao, H.-Z.; Zhu, X.; Ji, C.-J.; Ji, X.-J. The Security and Promotion Method of Transport Layer of TCP/IP Agreement. In Proceedings of the Second International Conference on Information Technology and Computer Science, Kiev, Ukraine, 24–25 July 2010. [Google Scholar] [CrossRef]
- Al-Jarrah, M.; Tamimi, A.R. A Thin Security Layer Protocol over IP Protocol on TCP/IP Suite for Security Enhancement. In Proceedings of the Innovations in Information Technology, Dubai, UAE, 19–21 November 2006. [Google Scholar] [CrossRef]
- Chang, R.K.C.; Fung, K.P. Transport layer proxy for stateful UDP packet filtering. In Proceedings of the ISCC 2002 Seventh International Symposium on Computers and Communications, Taormina-Giardini Naxos, Italy, 1–4 July 2002. [Google Scholar] [CrossRef]
- Chang, B.; Liang, Y.; Jin, J. Adaptive cross-layer-based TCP congestion control for 4G wireless mobile cloud access. In Proceedings of the IEEE International Conference on Consumer Electronics-Taiwan (ICCE-TW), Nantou, Taiwan, 27–29 May 2016. [Google Scholar] [CrossRef]
- Carter, C.; Onunkwo, I.; Cordeiro, P.; Johnson, J. Cyber Security Assessment of Distributed Energy Resources. In Proceedings of the IEEE Photovoltaic Specialists Conference (PVSC), Washington, DC, USA, 25–30 June 2017. [Google Scholar]
- Castiglione, A.; D’Arco, P.; Santis, A.D.; Russo, R. Secure group communication schemes for dynamic heterogeneous distributed computing. Future Gener. Comput. Syst. 2017, 74, 313–324. [Google Scholar] [CrossRef]
- GWAC. GridWise Interoperability Context-Setting Framework; GridWise Architecture Council (GWAC) Technical Report; GridWise Architecture Council (GWAC): Richland, WA, USA, 2008.
- NIST. NIST Framework and Roadmap for Smart Grid Interoperability Standards Release 1.0.; National Institute of Standards & Technology Technical Report; NIST: Gaithersburg, MD, USA, 2010.

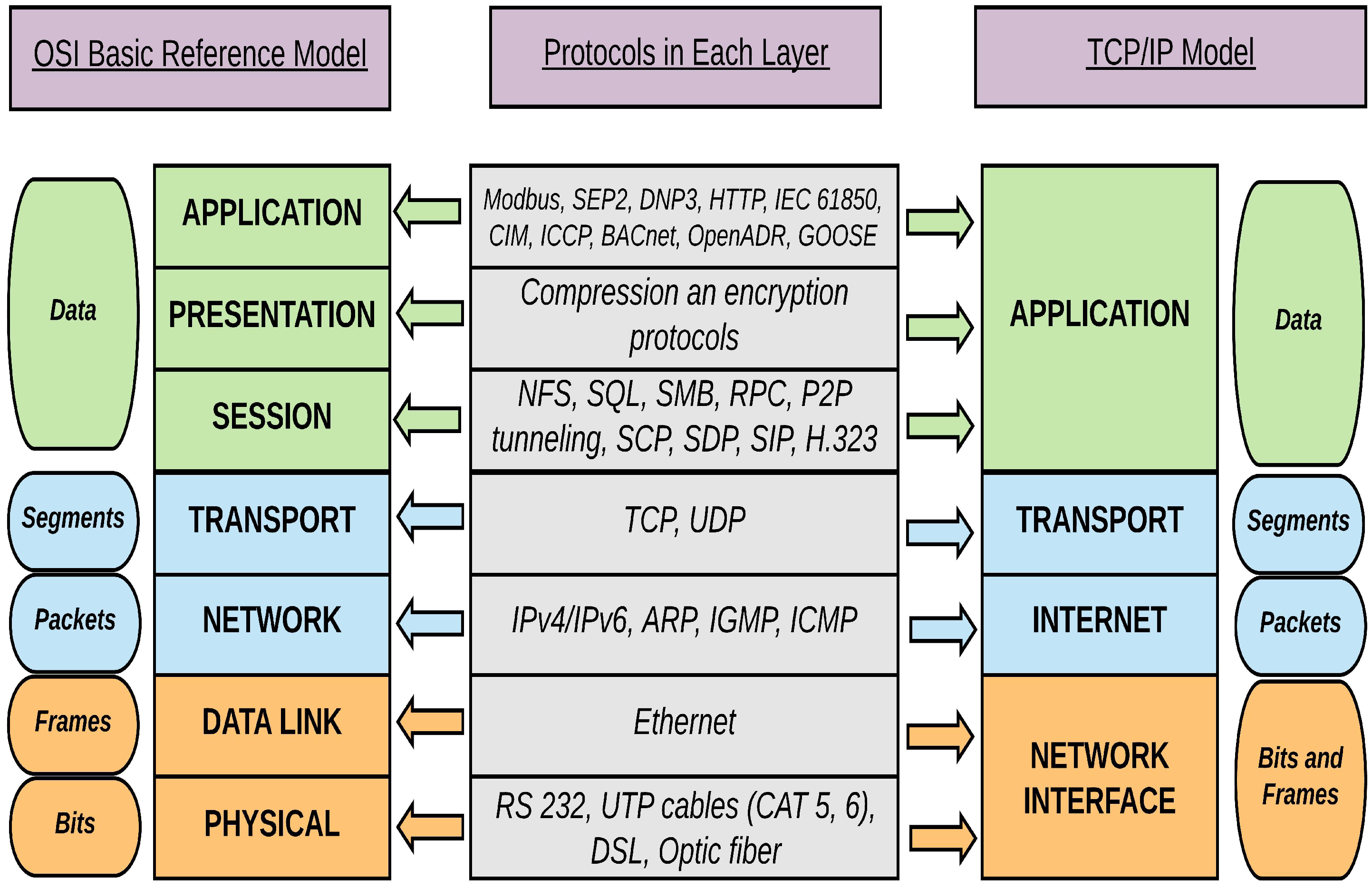
| Layer | Layer Number | Protocols/ Connections | Smart Grid Layer(s) | Standard/ Body | Vulnerabilities |
|---|---|---|---|---|---|
| Physical [58,59,60,61,62,63,64,65] | Layer 1 | RS 232, UTP cables (CAT 5, 6), DSL, optic fiber | Edge, Field, Network | IEEE 802.3 | Data/hardware thefts, unauthorized changes to functional environment, undetectable data interception, wiretaps, and reconnaissance, open authentication, rogue employees and access points |
| Data Link [66,67,68,69,70,71,72] | Layer 2 | Ethernet | Edge, Field | IEEE 802.1, IEEE 802.3 | Unauthorized joins and expansion of the network, VLAN join, tagging and hopping, remote access of LAN, topology and vulnerability discovery, break-ins, switch control |
| Network [73,74,75,76,77,78,79,80,81,82] | Layer 3 | IPv4/IPv6 | Edge, Field | IETF | Guessing TCP sequence numbers, stealing existing session, no cryptography |
| ARP | No authentication, works in broadcast | ||||
| IGMP, ICMP | Unauthorized access | ||||
| Transport [83,84,85,86,87,88,89,90,91,92] | Layer 4 | TCP, UDP | All | IETF, DARPA | Three-way handshake flaws, TCP sequence number prediction, port scan |
| Layer | Layer Number | Protocols/ Connections | Potential Attacks | Existing Solutions |
|---|---|---|---|---|
| Physical [57,62,93,94,95,96] | Layer 1 | RS 232, UTP cables (CAT5/6), DSL, optic fiber cables | Stealing data, data slurping, wiretapping, Bluejacking and Bluesnarfing, physical destruction, obstruction, manipulation of physical assets | Block the USB port, data storage cryptography, accountability and auditing to track and control physical assets [57,62,96] |
| Data Link [71,97,98,99,100,101,102,103,104,105,106] | Layer 2 | Ethernet | ARP poisoning, MAC flooding and spoofing, spanning-tree, multicast brute force, identity theft, attacks on VLAN trunking protocol and VLAN hopping, double-encapsulated 802.1Q/nested VLAN attacks | Physical protection, network segmentation, role-based access control, ACLs, control and management plane overload protection, centrally managed LAN security, encryption and integrity verification, Ethernet firewall and deep packet inspection, IDPS, port security, packet storm protection [103,104,105,106] |
| Network [107,108,109,110,111,112,113,114,115] | Layer 3 | IPV4/IPv6 | Spoofing, teardrop, replay, wormhole, routing, network manipulation and consumption, MITM, DoS | Use: firewalls, packet filters, application/circuit-level gateways, proxy servers, net/IPFilters, two-way authentication, network/protocol/host-IDS [111,112,113,116] |
| ARP | Spoofing, also known as cache poisoning | Authenticated IP addresses, modifying ARP using cryptographic techniques, manual configuration of static ARP entries [115] | ||
| IGMP, ICMP | ICMP flooding, Smurf attack | Rate-limit traffic, turnoff ping [114] | ||
| Transport [117,118,119,120,121,122,123,124,125] | Layer 4 | TCP, UDP | TCP hijacking, TCP SYN flooding, UDP flooding | Use: SSL/TLS, secure cookie flags, HTTP strict transport security, public key pinning, strong keys, efficient key management, certificates with required domain names and fully qualified names; do not use: sensitive data in URLs or caches, wildcard certificates [122,123,124,125] |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Sundararajan, A.; Chavan, A.; Saleem, D.; Sarwat, A.I. A Survey of Protocol-Level Challenges and Solutions for Distributed Energy Resource Cyber-Physical Security. Energies 2018, 11, 2360. https://doi.org/10.3390/en11092360
Sundararajan A, Chavan A, Saleem D, Sarwat AI. A Survey of Protocol-Level Challenges and Solutions for Distributed Energy Resource Cyber-Physical Security. Energies. 2018; 11(9):2360. https://doi.org/10.3390/en11092360
Chicago/Turabian StyleSundararajan, Aditya, Aniket Chavan, Danish Saleem, and Arif I. Sarwat. 2018. "A Survey of Protocol-Level Challenges and Solutions for Distributed Energy Resource Cyber-Physical Security" Energies 11, no. 9: 2360. https://doi.org/10.3390/en11092360
APA StyleSundararajan, A., Chavan, A., Saleem, D., & Sarwat, A. I. (2018). A Survey of Protocol-Level Challenges and Solutions for Distributed Energy Resource Cyber-Physical Security. Energies, 11(9), 2360. https://doi.org/10.3390/en11092360






