The Wolf and the Caribou: Coexistence of Decentralized Economies and Competitive Markets
Abstract
:1. Introduction
Methodology
2. The Rise of Decentralized Socioeconomic Models
3. Decentralized Socioeconomic vs. Competitive Markets
3.1. Decentralized Socioeconomic Markets Definition and Description
- Entrepreneurial Common (EC): An EC is the commercial interface with external ecosystems and gives funds it raised from selling goods and services or other activities such as investments in other ecosystems in the form of tokens to the For-Benefit Common (FBC) and receives goods & services to market and sell from the Production Common (PC) in return. This requires exchange between an EC token and Fiat and a PC token that is governed by the FBC. Tokens generally represent a unit of value as defined by the participants of a DAO, and there may be many tokens within a DAO. In addition, the EC is responsible for financial and monetary policy in the DAO since issuing a token is effectively creating a currency with all the accompanying complexities. We will discuss this in more detail when we discuss our proposals for the coexistence of decentralized economies and competitive markets;
- Production Common (PC): A p2p group that produces goods and services collaboratively based on the purpose of the ecosystem as established in the FBC. A participant’s contributions are valued in PC tokens which can be exchanged to EC tokens or other tokens through an exchange utility, as detailed out in one of our four proposals below. Assets created in this common are held in common by the FBC with claims rights by the contributors based on their value contribution to the asset in order to enable a fair sharing of value generated both commercially and through reputation;
- For-Benefit Common (FBC): The FBC is the governance common that is responsible for setting the DAO vision and impact goals, sets consensus rules and incentives for the DAO commons, sets the exchange rules for the EC and PC Tokens within the commons and externally to other ecosystem tokens and fiat, sets the ownership/membership and sharing rules for the DAO commons, defines and enforces reputation also in relation to non-DAO reputation measurement and management models, sets collaboration and giving rules with internal and external entities, and acts as the interface to not-for-benefit entities etc.
- Insulate the economically vulnerable FBC and PC from extractive external markets through the EC commons by limiting token exchanges between the common markets that have direct interfaces to competitive markets.
- Enable social impact results through the FBC without a strong dependency on market results. The FBC decides the use of funds coming from the EC. As a result it is independent of “shareholder value” as defined by external and extractive markets; therefore it is accountable to the PC and EC participants.
- Allows the EC to focus on raising funds for both the FBC and PC either through selling products and services or raising funds for future products and services and social impact efforts.
- Enables the PC to focus on core competencies to create new products and services aligned with the overall DAO values independent of the EC.
- Open Value Accounting: An accounting system that allows one to record not only tangible assets and assess their value in a unit of value measure, but also to record tangible and intangible value contributions from participants to an asset and subsequent value translation into a unit of value measure such as a token in a decentralized socioeconomic model;
- Decentralized Commons Market: A decentralized marketplace for the free exchange of assets and services governed by business rules established by a governing commons through participant consensus. The decentralized marketplace is transparent and has verifiable and marketplace transactions. In order to motivate participation in a decentralized commons market (DCM), a DCM has an incentive model for both tangible and intangible value contributions and open asset ownership representation through a set of defined unit of value measures such as tokens. The rules for DAO membership and voting are normally based on consensus processes;
- DCM Reciprocity: Reciprocity in this context means that the return on investment beyond a certain value7 is capped but not frozen by requiring reciprocity contributions to the DCM in the form of tangible or intangible value contributions that equal or exceed returns. Example: For a return of a 100 token investment in a DCM asset beyond say 10 tokens, an actor needs to make a value contribution after applying an exchange rate of token to utility token quantifiably equivalent to 1 utility or 1 reputation token for every token earned beyond 10 tokens.
- Cong et al. (Cong and He 2018) argues that Blockchains enlarge the competitive contracting space while at the same time the process of reaching decentralized consensus changes the information environment enabling “higher social welfare and consumer surplus through enhanced entry and competition, yet it may also lead to greater collusion.” Because “Blockchain and smart contracts can sustain market equilibria with a larger range of economic outcomes.” This aligns with our above discussion on open value accounting and DCMs with reciprocity and the related discussion in (Freund 2018).
- Yermack points out in (Yermack 2016) that the lack of clear governance principles and rules for decentralized economies such as Bitcoin and Ethereum lead to either inaction in the case of the Bitcoin scaling debate or to ecosystem hard forks in the case of Ethereum. We will discuss in the last section that choosing a hard fork at the protocol i.e., the Blockchain level—is actually a preferable option if consensus cannot be reached or an ecosystem is attacked by a majority collusion attack.
- Cong et al. formally show and provide empirical evidence in (Cong et al. 2018) that mining pools have a natural tendency to centralize because of risk-sharing advantages. They also provide a new explanation for why Bitcoin mining may be adequately decentralized over time due to the higher fee structure of large pools. The paper does not consider collusion scenarios of mining pools to manipulate markets, which is currently a possibility given the concentration of mining power in a few large mining pools. Note that this discussion is only applicable to a competitive decentralized market that is the nature of Proof-of-Work (PoW) or simplistic Proof-of-Stake (PoS). In more sophisticated versions of Proof-of-Stake such as Casper FFG (Buterin and Griffith 2017), rewards are shared, the market is less competitive and decentralization is encouraged through dynamic ROI based on the number and stake of participants changing the underlying market dynamics.
- Easley et al. show in (Easley et al. 2017) that in the absence of transaction fees, over time the Bitcoin Blockchain, in fact any Blockchain, is not viable. However, even with transactions fees, the authors show that there is an upper bound on the size of the Blockchain imposed by the waiting time confronting users in the transaction pool. Users exit the Blockchain if the waiting time gets too long and the costs of waiting significantly diminish the expected gains from a transaction in much the way that miners exit the Blockchain when their revenues no longer generate profits. Hence, the equilibrium in the bitcoin Blockchain is a complex balancing of user and miner participation. Albeit very important, the analysis is only pertinent for PoW Blockchains, because the queueing problem is significantly less in PoS Blockchains, especially when scaling improvements are taken into account. However, unless transaction ordering and transaction censoring are addressed, as we will discuss below in Proposal #1, the queueing problem may arise again in front running scenarios such as decentralized exchanges. We will touch upon this in Proposal #4.
- Huberman et al. show in (Huberman et al. 2017) a relationship between congestion and transaction fees in the Bitcoin Blockchain system, which matches network data. It is also demonstrated that, as block rewards are reduced, congestion is essential for raising revenue from users to fund miners’ provision of infrastructure. The authors correctly highlight key economic challenges in the design of the markets that underlie these distributed systems though they leave out some key considerations such as non-homogenous distribution of mining power, which makes it more likely for users or their intermediaries to send transactions to large mining pools irrespective of fees. What the paper highlights well is the fact that relying on transaction fees alone is not a viable strategy because today’s users expect fast response times and low fees of computer systems. This means that new protocols need not only have a dynamic fee schedule but also a dynamic reward and economic stake function that balances validator/miner ROI against the level of decentralization providing system security as is done in Casper FFG (Buterin and Griffith 2017). In addition, adoption is important since higher usage together with available higher capacity in non-PoW systems will allow significant revenue to be created from transaction fees alone, even if they are small.
- Dupont discusses the failed DAO experiment in 2017 (DuPont 2017) and found three key themes of governance related to the DAO experiment that are in line with the discussions on governance in (Freund 2018) and are reflected in our proposals in Section 6, where applicable:
- shift of legal authority from existing, judicial authority to algorithmic authority;
- the difficulty of designing and governing algorithmic systems, and especially immutable and decentralized ones;
- the challenging ethical questions of experimentation with forms of distributed action through autonomous, decentralized systems.
- What are the legal forms that DAOs can take?
- Do DAOs have to be incorporated?
- How do you establish legal recourse?
- How is ownership established, if at all?
- When are tokens securities vs. currencies vs. commodities vs. …?
- How can DAOs account for different legal and regulatory boundary conditions in different jurisdictions while maintaining, potentially global rules and processes?
- Legal Forms and Incorporation: Entity to entity business relationships are governed by jurisdictional specific laws and regulations. Generally speaking, a DAO that wishes to interact or do business with a traditional company will require a legal, non-person entity9 to be established in the jurisdiction in question, otherwise the traditional business will not do business with the DAO, at least for higher value or higher risk business transactions. The legal entity might take the form of a non-profit or for-profit entity and it might or might not exploit particulars of applicable jurisdictional law as for example cleverly done so in (Sundell 2017). The same holds true for intra DAO value exchanges and transactions if legal, non-person entities are DAO members. However, value exchanges within a DAO or between DAOs (excluding any of their legal entities) do not require legal, non-person entities and are perfectly in line with jurisdictional law as long as those transactions are done between legal persons and adhere to the jurisdictional laws governing legal persons;
- Legal Recourse: Legal recourse is one of the most important tenets in the current centralized economic model with the current, centralized legal system taking on the role as final arbiter. However, with decentralized economic models, there is typically a priori no centralized arbiter function, but rather a decentralized one based on consensus. In fact, this is not too dissimilar to a jury system except that the legal constructs wrapped around a jury are centralized structures. Therefore, legal recourse in a decentralized economic model takes on an even larger role given that there might not be a legal entity to sue or if there is, they might not hold any liabilities to a product or service in certain cases as opens source software under the Apache 2.0 license. That means, if an event occurs that causes a socioeconomic imbalance in the DAO, there have to be well defined rights of DAO participants to the DAO’s underlying assets in all three of its components. Note, that a participant might have recourse rights against one, two, or all three of the DAO structures. Those are rights that should be enforceable programmatically, if certain predefined conditions are verifiably met. This is important since the exact expression of legal recourse varies by jurisdiction, yielding sole reliance on court systems too slow, inefficient, and open to manipulation to be useful for a DAO. The exact details of such an internal legal recourse as well as of external legal recourse are based on the jurisdictions a DAO operates in, and are determined by the governance common, the FBC, through consensus processes. Consensus proposals need to be agreed to by the PC and EC through commons specific consensus processes, as there cannot be unilateral action in this construct. Given the potential scale of a DAO, consensus and incentives take on great importance given the legal recourse requirements. Therefore, a careful definition of the rights and warrants of participants to the underlying tokens representing asset rights for each of the three commons of the DAO becomes imperative and independent if these assets are digital or analog. In addition, there needs to be a careful definition of cascading rights. To make this very important point more concrete, let us consider the following situation: Actor A holds EC tokens that were acquired through an exchange functionality in an environment for fiat currency as discussed in Proposal #4 below in detail. These EC tokens are subsequently exchanged with the PC for PC tokens through an exchange functionality in order for the PC to create a new good or service. The PC token represents an ownership right. The important question that needs to be answered is what type of ownership this token represents. It could be ownership of the underlying asset or the cash flow associated with that asset. If assets are to be freely used and shared throughout the PC, then the natural answer would be cash flow. If that is not the case, the answer probably would be an asset. Whatever the case, each product and service requires such a determination of ownership rights for contributors both financially and from an asset contribution point of view. This means that the DAO needs to create programmatic business logic representing the ownership rights decisions such that Actor A knows exactly what will happen to his contribution to the PC for a service or product, if a socioeconomic imbalance or dispute occurs. This example is relatively simple, however, for each contributor relationship within the ecosystem that the DAO spans, it is important to have this clarity of cascading legal recourse. A complex but very important task to define, agree upon by participants, and subsequently transform into computer code.
- Ownership & Control:
- ○
- Ownership: When analyzed through the lens of a decentralized socioeconomic context we find two forms of ownership in decentralized economies:
- ▪
- Self-Sovereign Ownership where ownership rights over an asset are entirely self-sovereign; i.e., “even if shared with others I can do with my ownership share as I please”;
- ▪
- Non-dominium ownership where assets are held in common within a DAO as a custodian and the rights governed by asset rules established by the DAO through consensus.
An interesting question in this regard is revoking ownership rights. In a decentralized economy revoking ownership rights should not even be possible. The question then is how can DAO entities that abuse ownership rights be effectively censured in order to ensure continued trust into the long term viability of a DAO? A possible answer is to not allow an entity to exercise their ownership rights. For example, leveraging publicly available lists, DAOs disallow interacting with blacklisted assets of DAO participants or the participants themselves. Other DAO participants ignoring such blacklisting can be equally censured since the asset can be tracked through functionality, provided transparency is established by using Blockchain technology. Of course, this discussion depends on courts recognizing Blockchain secured ownership of assets, at least if these assets are utilized outside a DAO. - ○
- Control: In contrast to ownership, control of an asset or an actor (guardianship) can be revoked (transparently on a Blockchain) through the owners of an asset or an actor him or herself at any point. Again, the legal discussion reduces to the question of legal sustainability of verifiable claims on a Blockchain in a court of law.
- Tokens: Generally speaking there are three types of tokens:
- ○
- Native (Utility) Tokens: Tokens representing transferable ecosystem value but do not confer any counterparty rights such as title except what the token holds itself. An example is Bitcoin or any other cryptocurrency10 or access tokens to a service;
- ○
- Counterparty Tokens: Confer a 3rd party counterparty right. For example, tokenized debt to a lender or the right to shares and shareholder rights aka an equity;
- ○
- Ownership Tokens: Describes the rights of owners towards an asset such as title. There are no direct or indirect counterparty claim rights associated to such a token.
3.2. Competitive Markets Definition and Description
3.3. Framework for Market Comparison
- Number and size of producing organizations with respect to the market size.
- Barriers to entry of new firms, informed by the ratio of fixed to total cost and network effects.
- Product differentiation and degree of information symmetry12.
3.4. Decentralized Socioeconomic Markets
- Number and size of producing organizations with respect to the market size:
- In decentralized markets, there are a large number of producing organizations as the notion of a firm dissolves into project groups within a decentralized network of entities (people, organizations and, in the future, things). This can be viewed as similar to a chemical reactor. The entire model has a mixture of entities and assets interacting with one another governed by adjustable rules. To achieve the model’s goal, entities and assets combine in projects, the “producing organizations,” to deliver an outcome. Over time, the same entities may frequently work together, but they would not legally constitute a firm, but are rather a commonly occurring set of entities within many projects;
- The market size is the number of participants potentially impacted by the decentralized model’s purpose. We will explain in Proposal #2 below, the concept of open value accounting, but we can assume that the larger the impact of a decentralized model’s purpose, the more members it will have. This is because participants in a decentralized model are compensated in proportion to their contributions when an asset is monetized or has proven impact. Therefore, the larger the purpose, the higher the chance of earning from an asset considering that the network effects of a large decentralized community increases the chance of innovation success and value generated (Torrance and Tomlinson 2009);
- Since we assume that there is generally a constant optimal project size (Blenko et al. 2010), the ratio of the number of producing organizations per market opportunity is likely to be larger in a decentralized market comprised of short-term project teams than it would be in a competitive market where firms are the producing organization, almost always including more than one project group.13
- Barriers to entry of new producing organizations with respect to market size:
- The barriers to entry for organizations providing commodities and services are low in these markets because assets are open and free for any member to use and build upon. For products that rely on network effects, like social media platforms or sharing economy services, the barrier to entry will be higher than commodity or service providers, but lower than the barriers to entry of competitive markets where network effects are built on top of proprietary platforms. Because the products that rely on network effects are open, incremental innovation can be implemented as an update, and come from any member of the decentralized model rather than just the platform founder as in the competitive market scenario with platforms like Facebook and Google;
- Product differentiation and degree of information symmetry:
- Decentralized markets operate with globally differentiated products, but locally homogeneous products because of the commons model. This model incents efficient use of existing assets and rewards participants more for added-value rather than recreating existing value. Because members are incented to produce added, rather than recreated value, when an effective solution is in place at the local level, innovators will work to solve new problems related to the decentralized model’s purpose. On the global level, however, innovations for the same problem will look different because of contextual innovations that took place at the local level.
- Because assets are open and transparent from Blockchain-mediation, information symmetry is approached, but not reached due to bounded rationality14.
3.5. Competitive Markets
- Number and size of producing organizations with respect to the market size:
- The number of firms is large. This develops competitiveness as each firm works to develop a preferred offering.
- Barriers to entry of new firms:
- Competitive markets are characterized by easy entry into and exit from the market. Without this being the case, the market would become a monopoly.
- Product differentiation and degree of information symmetry:
- Products are differentiated, and information asymmetry is a factor that can drive prices since information and assets within a firm are generally closed, and all actions are not Blockchain or technology-mediated exchanges.16 Competitive firms can further their purpose of profit maximization by taking advantage of information asymmetry to set higher than market prices that a customer will normally accept in a more information/asset symmetric market; i.e., a high degree of competition.
3.6. Comparison of the Outcomes of These Different Organizational and Market Structures
4. Value Extraction vs. Reciprocity: How Competitive Markets and Centralization Endanger Decentralized Economies
4.1. Number of Producing Organizations
4.2. Barriers to Entry & Product Differentiation
4.3. Information Asymmetry
4.4. Other Value Extraction Opportunities
5. The Role of Market Interfaces in the Proliferation of Decentralized Socioeconomic Models
Case Studies in How Decentralized Economies Interact with Competitive Markets
- Introduce the market’s purpose.
- Define value flow at the edge, aka: market interactions and accounting within the system.
- Note any important outcomes of the interface design.
- The three zones of our proposed decentralized socioeconomic model design encompass functions of existing organizations, even if they currently are not delineated into three zones. We will discuss the strength, weakness, or absence of the functions of the three commons (EC, FBC, PC) within each case study, and any resulting vulnerabilities to illustrate the importance of well-developed zones.
- Sensorica is a network of people who self-govern to innovate and design sensors (Bauwens and Niaros 2016).
- Members of the network, and any other party, have open access to all contributions of other members, allowing them to mix and match, repurpose, and build upon each other’s contributions. Innovation happens in two ways. One is in the context of intrinsically motivated innovation, and the other is market-funded projects that they rely on their commons to deliver. Their accounting system, called open value accounting, tracks all members’ contributions, allows them to be valued through a value equation that was previously agreed upon and rewards members proportional to those contributions when a product or service is externally monetized. In addition to project contributions, members earn reputation based on quality of work and in recognition of actions aligned to the network’s collective interest. This value is used to assign roles in future projects and provides an assessment of the fairness of activities happening across the network to build trust between members.
- The market interface is their ability to sell products, services and be sponsored by corporations on open source projects. This flows money into their network while giving them independence from external shareholders. This insulates their value sovereignty from extractive forces by avoiding the need for investors and only accepting funding through grants as needed.
- Up to this point, Sensorica has been able to protect their network from extractive forces when competitive organizations follow initial agreements. However, they have interacted with corporations who do not uphold their initial agreement, and forfeit payment to the network. This highlights a key vulnerability of their server-based infrastructure. They are not able to enforce agreements easily without legal recourse. A Blockchain infrastructure with programmatically executed contracts could automate payment based on defined metrics or milestones, potentially alleviating this weakness. However, Sensorica has developed one of the most successful operating incentive structures that organizes the efforts of decentralized members around the FBC’s purposes. Their model was key to informing Proposal #2.
- The FBC of Sensorica is relatively strong. They have defined governance, and a clear, defined purpose with matching incentives through open value accounting. The EC is relatively weak because fundraising is carried out spontaneously by members, or on an urgent basis to fund specific network needs. Projects and products are sold similar to in a small business, but their network’s small size and equitable distribution of revenue to contributors means that there are no large stores of value in the network available to fight legal battles when larger corporations violate their contract. The PC is relatively strong, with the assets produced by the members held in a not-for-profit called a custodian and open for all members of the PC to access. In addition, open value accounting creates a defined set of rules and reward expectations that all members agree and operate on, aligning incentives of contributors with the values of openness held in the FBC. The vulnerabilities mainly come from the EC, where funding is weak, limiting the level of mobilization of PC participants to carry out the FBC’s goals. The lack of a well-defined EC with reasonably enforceable contracts means that the network is prone to net value loss to external organizations as they take advantage of open assets without reciprocating value.
- Enspiral is a supportive coalition of and for social entrepreneurs.
- As SEs, the members of Enspiral operate like competitive businesses but with a social mission. They use fiat currency and traditional accounting to offer products and services. Enspiral LLC acts as the central node of the SE network. Members can contribute to this node’s budget, which is democratically governed by participating members to determine how funds are allocated.
- Enspiral interacts with the competitive market by issuing shares to investors and capping returns to a specified rate in a model referred to as “capped-returns” transvestment. Once a specified return rate is reached, the SE buys back the investor shares and is able to reinvest all future profits into its mission.
- This model avoids perpetual extractive shareholder interests by raising initial capital from the capitalistic economy, then buying back all shares to become an autonomous business free to act in the interest of their mission, not shareholders.
- The FBC is strong, and structured as a central node comprised of members who vote on changes using a centralized software tool called Loomio. The limitation of using a centralized decision making tool for all governance and decisions is the nothing at stake problem, opening the network up to human-engineering type attacks like discouragement, extortion, or collusion whose mitigation are chiefly discussed in Proposal #1. The central node also accepts donations from member organizations and individuals, acting as the EC, which distributes the funds democratically through member vote to projects that serve its purposes. The other component of the EC is the capped returns policy for raising external funds from investors by strictly limiting the amount of return on investment that can be earned and extracted from the network, and prohibits funds (except for wages and covering operational type costs) from being withdrawn from the network so that the maximum amount is reinvested into its purpose (Financial Agreement Enspiral Handbook n.d.). Enspiral’s PC is relatively weak, and is simply the combination of SEs that are incented to work together by intrinsic motivation, rather than by design. The control mechanism for selecting members who will be intrinsically aligned is through invite and nomination-only membership from existing members. The weak PC introduces a possibility that members will not maximally contribute to Enspiral’s overall benefit because each member organization must succeed on its own. Without strong extrinsic incentives to contribute or formal requirements of open assets, the strength of collaboration within the network relies on intrinsic alignment of contributors (Venture Agreement Enspiral Handbook n.d.).
- FairCoop/FairCoin is a group of coops founded on the values of cooperation, ethics, solidarity and north-south redistribution and justice in economic relations (Faircoin—P2P Foundation n.d.). The FairCoin has been developed to become an alternative currency for exchange and a store of value within the FairCoop network.
- FairCoins are designed to be an alternative currency to fiat. Members can participate in FairCoop market exchanges with them. Once coins gain enough value in the market, they can be used to fund cooperative projects that FairCoop members care about. There is a static coin supply that cannot be changed, even through consensus (König 2016).
- The market interface is the exchange mechanism between fiat and the coin. This is their means of transvestment, and bootstraps value into the cooperative network. To establish value sovereignty, they developed an incentive mechanism so members are able to use FairCoins as an exchange mechanism and store of value. This is done by rewarding members who hold a minimum number of tokens for a specified time period. This reduces volatility from extractive investors who buy large amounts of tokens, hold them until the price increases, and then exchange them back to fiat without reciprocating any value into the ecosystem.
- An important distinction here is that value sovereignty is not enforced, but rather encouraged. Since its launch in 2014, its value has increased along with many other cryptocurrencies, and has been successfully used as an exchange mechanism with the FairCoop ecosystem (FairCoop 2017). We consider the permanently static coin supply to be undesirable, although it was done intentionally to increase the coin’s ability to store value (König 2016). FairCoin is therefore designed with fewer ways to address value fluctuations from internal market activities, external factors like speculation, or arbitration attacks. The long term stability and success of FairCoin as a means for exchange over time will provide evidence for or against our Proposal #3.
- The FairCoin is only a tool of the FairCoop organization, so the discussion around the three zones will focus on FairCoop. The FBC has started with founding, unalterable values, but strategies and other things can be changed (FairCoop Principles n.d.). Changes are made through four councils that propose changes, and must reach 75% majority vote from participants. The EC is governed by FairFunds, an organization within FairCoop that holds FairCoins from the initial token distribution, and also accepts donations to support new projects that contribute to FairCoop’s values. The new projects are governed by a democratic council and only receive funds after milestones are met (FairFunds n.d., FairCoop—P2P Foundation n.d.). Otherwise, the EC also includes policies that FairCoins can be purchased in exchange for fiat at will. The main vulnerabilities are that the FBC defines unalterable values, which may become ineffective in the future, and the inability to alter them may cause misalignment with members and abandoning the ecosystem. The EC is also dependent on the value of the FairCoin to increase and remain stable, as it is the main funding mechanism for network growth. This highlights the need for Proposal #4, decentralized exchanges, to support the stability and reduce the probability of attacks on the token, which is central to FairCoop’s operations. The PC is supported by an ecosystem of common resources like FairCoin and FairFunds. Local nodes are expected to contribute knowledge to the global knowledge commons of the FairCoop, and global knowledge is also expected to flow to local nodes, although it is unclear how this norm is enforced (FairCoop—P2P Foundation n.d.).
- The Ecuador FLOK (free/libre, open knowledge) Society was a project initiated when Rafael Correa came into power, rewrote Ecuador’s constitution, and was determined to link “economic and social life to the values of personal well-being and protection of the environment” (Bauwens and Restakis 2015). Research, planning, and policy proposals were developed to implement a FLOK based economy that could give Ecuador independence from extractive western nations that were buying Ecuador’s low-value raw materials, and selling Ecuador high-value refined products. This commons model would realign Ecuador’s economy to an infinite resource—knowledge, and away from finite natural resources.
- People contribute to the commons, paid or unpaid. In the transition period before the commons economy becomes dominant, the state will pay commoners for the investment period when a livelihood cannot be made by contributing to the commons. Those people are taxpayers as well, and generate the knowledge, code, and resources that go into the open commons. The commons are managed by non-profit foundations. These foundations ensure the open licenses on commons assets are not breached, and raise money for infrastructure. Their work also gets contributed to the commons. People who contribute to entrepreneurial projects, and who contributed to the production of the assets held in common that were used, are compensated in a commons-measure of value. This is the internal value regime, independent of the existing competitive market. Because these “ethical companies” will be opening their IP, they will be less attractive to investors looking for profit maximization. To support these mission-oriented organizations, alternative economic systems for them to operate on must be developed and politically supported.
- Businesses and entrepreneurs are able to access the resources in the commons, employ people to help add value to the common assets, and provide funding for commons infrastructure. The surplus social value accrues back to the commons because a business that privatizes knowledge from the commons is required to pay for that asset used, as stipulated by the peer production license of commons-based knowledge.
- This model was developed and several policy recommendations were made, but the Ecuadorian government did not implement all of the policies. To date, the implementation of these proposals includes the mandate for all academic texts to be made open, and the beginning of a transition of government software to free and open versions (Brown 2017). Because of this partial transition to a commons based economy, we cannot determine the framework’s success.
- The fact that this case was never fully implemented is the major consideration. The FBC is government controlled, and never was implemented. If it had been, this centralized control would subject the community to unilateral changes in the market, introducing unpredictability, and therefore lack of trust as a long term, viable market to base livelihoods on. The instability of central control is another motivation for Proposal #1.
6. Protection & Coexistence: A Working Proposal to Protect Decentralized Economies
- Collusion Resistant and Tamper Proof Consensus Governance to avoid the illustrated value extraction attacks at both the platform and application layer. This proposal is also foundational for the other proposals to be really secure;
- Programmatic Value Recourse: Equitable Asset Participation that establishes built-in value reciprocity limiting value extraction either unintentionally or maliciously through collusion attacks;
- Semi-Programmatic Monetary and Fiscal Token Policy to avoid liquidity value extractions attacks and enable to enhance network effects as a secondary benefit when certain fiscal and/or monetary conditions in the DAO are met;
- Decentralized Exchanges to prevent value extraction through arbitrage stemming from information asymmetry and access restrictions to trading facilities and other means by requiring trading collateral and trading stakes.
6.1. Proposal 1: Collusion Resistant and Tamper Proof Consensus Governance
- All consensus processes should utilize a proof-of-(resource)-stake algorithm24 utilizing Blockchain tokens defined at both the protocol layer, such as Bitcoin, and at the application layer, such as an ICO token. Proof-of-(resource)-stake is recommended to avoid the energy waste of PoW and making consensus processes more easily implementable and scalable across a large participant group without significant compute requirements;
- Tokens are earned through rewards (new tokens) and fees charged by participants that provide utility services to a DAO. Minimal fees should be defined in a schedule per utility service. The fee schedule is governed by consensus of all actors participating in utility services and should be dynamic. A Utility Service is a consensus governed service such as Block validation provided by a set of staked ecosystem participants running a consensus algorithm either at the protocol or application layer;
- Participants can pool tokens to become a staked validator in a consensus protocol: One validation node with multiple pooled stakeholders is, therefore, possible;
- Proof-of-(Resource)-Stake consensus algorithms should have a mathematical proof of security;
- The nominal token value of the reward for a unit of a utility service, such as a Block, is determined through consensus of the ecosystem initiating actors and is recorded within a Blockchain. Subsequent changes require a p-majority agreement of ecosystem participants where p > 50%. The reward should be dynamic such that it maintains a rate of return as has been agreed upon by the utility service participants through consensus, irrespective of the number of participants in a given consensus round;
- Non-utility services including governance processes requiring external validation should follow a simplified model of staked validators etc., as described in Model Assumption 16 in (Freund 2018).
6.1.1 Attack Vectors & Mitigations
- Collusion Attacks: A 50%+ stake majority of consensus participants collude to alter Blockchain history. Mitigations: Stake is not equivalent to voting power but rather gives a participant a higher chance to be part of the voting committee, otherwise it is one member one vote, making collusion more difficult, especially in larger committees. Furthermore, the consensus algorithms we propose are probabilistic, meaning that at any given point in time there are several active chains but only one of those will turn out to be the longest chain. This means that if a collusion attack is detected, the minority can abandon the corrupted chain and continue with a chain that they trust. If economic finalization of an epoch is colluded against, the same approach of chain switching can be taken. In addition, committee membership can change and/or be different on another chain and that committee can gain enough votes for finalization. At that point, the colluding participants need to switch to the new longest chain with the now finalized checkpoints or risk losing all their stake due to a violation of protocol rules that disallow conflicting checkpoints with a majority of votes;
- Long Range (Revision) Attacks (Nothing-at-Stake): A 50%+ majority of Committee members who voted on a checkpoint in the past but have now since unbonded their stake could vote on finalizing a conflicting check point after the one they last voted on, creating an alternate chain. Mitigations: Long unbonding periods in the protocol make these attacks more difficult because the other participants will have seen a lot of other checkpoints finalized and will not accept a conflicting checkpoint at a lower height. There is the issue of a large number of participants having been offline for a longer period of time. This would be a potential problem, however, the protocol’s liveness slashing condition26 mitigates this type of attack;
- Discouragement Attacks: Examples of such attacks are censoring transactions or not participating in consensus in order to prevent checkpoints from being finalized. Mitigations: The latter type of attack is mitigated by the protocol’s liveness stake, slashing conditions, and the former attack can be mitigated through the staked consensus of the trusted hardware overlay networks (Bakshi and Freund 2018);
- Extortion Attacks: These type of attacks are a variant of censorship attacks where the attackers either refuse to process transactions or vote on check points unless participants pay an extra fee or collude with them in one of the above three other attacks. Mitigations: As discussed under Discouragement Attacks, censoring actions can be mitigated by trusted hardware overlay networks and the former type of extortion attack can be submitted as a malicious action transaction and can lead, if approved by a majority of the committee;
- Committee Manipulation Attacks: This is a very complex subject matter dealing with the selection algorithm, its inherent entropy etc., and potentially quite dangerous since it allows the manipulation of the chain by a malicious committee (see collusion attacks). Mitigations: We refer the reader to the details of the Snow White and Casper papers we cite. The bottom line is that given the chosen constructs, manipulation of committee selection is becoming extremely difficult;
- Participants synching to a malicious chain after being offline for a long time: Again, this is a very complex subject matter dealing with different types of sophisticated attackers and quite dangerous since it allows a malicious chain to persist unbeknownst to honest participants. Mitigations: We refer to the details of the Snow White and Casper. The bottom line is that given the chosen constructs, manipulating synching participants is becoming extremely difficult.
- Collusion Attacks: Mitigations: Stake is not equivalent to voting power but rather gives a participant a higher chance to be part of the voting committee, otherwise it is one member one vote, making collusion more difficult, especially in larger committees. If vote finalization within a voting period is colluded against, non-voters lose their stake and a new committee is selected. Furthermore, if there is a suspicion of collusion, anyone can request a revote if the request is staked (skin-in-the-game) with a new committee further reducing the possibility of a successful collusion attack;
- Long Range (Revision) Attacks (Nothing-at-Stake): Mitigations: Not required since the underlying consensus algorithm protects against this type of attack;
- Discouragement Attacks: Mitigations: Censoring a vote is not possible if submitted to multiple Blockchain nodes at the same time and non-voting leads to a loss of stake as discussed before;
- Extortion Attacks: Mitigations in this case are the same as for discouragement attacks;
- Committee Manipulation Attacks: Mitigations: Given that committee selection is done in the blind, possibly even with trusted hardware, such attacks are virtually impossible;
- Participants synching to a malicious chain after being offline for a long time: Mitigation to this attack is provided by the underlying consensus algorithm of the protocol.
6.2. Proposal 2: Programmatic Value Recourse: Equitable Asset Participation
- A Contributions Log to record actor contributions
- An Asset & Resource Registry to create visibility of existing assets and resources to DAO actors
- A Value Aggregation framework consisting of
- A value equation and associated processes that describes how contributions are evaluated and associated with assets
- Solidarity Mechanisms to ensure compassion and distribution of risk
- A project marketplace where available projects are marketed and teams can be formed
- An identity for the combined asset is created with the actors who have contributed to the asset as co-owners with ownership token amounts equivalent to the agreed upon value of their contributions;
- The assets used to create the new asset are also made co-owners with ownership token amounts equivalent to the agreed upon value of the assets contribution. There are three options for assessing the value of the contribution. All three need to be functionally available in the three DAO commons:
- The actors who have created the new asset assess the value of the parent assets without involvement of owners of the used assets. This is the most efficient solution. However, it is fraught with risk of one or more of the used asset owners, aka: claim rights holders filing a malicious action claim that could result in any number of adverse outcomes, such as loss of DAO stake, expulsion from the DAO, blacklisting, legal action etc.;
- The actors who have created the new asset assess the value of the contribution as under (a) and then submit the value assessment within the PC to a vote of the owners of the used asset. The used asset owners can accept or reject the valuation. If it is rejected, the value assessment is referred to an arbitration function in the FBC containing the rejected value assessment and a proposed new value assessment. This arbitration function will be described in more detail below. Both parties are bound by the arbitration outcome;
- The actors who have created the new asset assess the value of the used asset and submit it to the arbitration function of the FBC and the owners of the used asset. The process then follows the description under (b).
- A claim holder can recursively call all assets where his or her asset is used and, therefore, construct a cryptographically verifiable claim structure that we are calling an identity graph. It should be noted here that in order to avoid payments to claims right holders in perpetuity as assets get fully commoditized, there should be a decay function over time in the number of claims rights held by an ecosystem participant in the form of tokens. This avoids the scenario of everyone still having to pay a small portion to the ancestors of the inventor of the wheel every time a wheel of any sort is sold;
- The claims can be quantified and used to programmatically identify who needs to be compensated and how much in either Fiat or tokens through a Smart Contract payment system situated within the FBC.
6.2.1 Attack Vectors & Mitigations
6.3. Proposal 3: Semi-Programmatic Monetary and Fiscal Token Policy
- Policy Setting Mechanisms
- Token Definitions and Policies
6.3.1. Policy Setting Mechanisms
- At the beginning of each ecosystem time period, a participant signals through a token stake, if they want to be an outcome or state validator;
- Outcome/state specific rules are agreed upon by the affected counterparties. Ecosystem outcomes or states that require validation are assigned a random set of an uneven number of validators from the set of signaling validators. Signaling validators determine how many outcomes or states they want to validate. Validators need to stake each outcome/state they want to validate equally;
- The assigned validators vote on the assigned ecosystem outcome/state during the voting period, which is determined ahead of time by the counterparties to the ecosystem outcome or state.
- For an outcome or state to be validated, the validators in the consensus majority receive equal parts of the stake from the validators that were in the minority;
- If the validators agree with the proposed outcome or state, the stake of the participant who wanted an outcome or state validated is returned. If not, then the stake is distributed in equal parts to the majority validators;
- Any participant can raise an objection to the validator consensus in the ecosystem time period during, E, or immediately after, E + 1, the validator consensus was reached by requesting a 2nd round of validation by another set of randomly selected validators during the ecosystem time period, E + 1. In order to raise an objection, a participant needs to provide a stake for the objection in order to avoid spurious objections spamming the system. The size of the required stake is determined as a percentage of the value at stake; e.g., reputation tokens;
- If the new set of validators agree with the objection, then the actor raising the objection receives the stake plus a percentage reward from the stake of the original giver and receiver as well as the stake of the initial set of validators. The new set of validators receives the remaining stake of the initial validators who were contradicted by the second set of validators. The exact percentages need to be specified either on the protocol level for utility services employing this approach or on a case-by-case basis at the application layer. In both instances, the consensus process parameters are determined by consensus of the participating actors;
- If the new set of validators disagree with the objection, then the objecting actor loses its stake. The stake is distributed in equal parts amongst the validators that confirmed the conclusion of the original validator set.
6.3.2. Token Definitions and Policies
- Through consensus controlled changes by ecosystem participants, it should be possible to add additional token types to an ecosystem, including at the protocol level. The type of tokens should be unconstrained. This allows the necessary flexibility to create new token types required as the ecosystem evolves, such as reputation;
- The initial types of tokens at the protocol level cannot be retired, in other words being taken fully out of circulation. This ensures security against economic extortion or discouragement attacks at a platform level. Any additional protocol token types created in addition to the initial base tokens can be retired and taken out of circulation, as long as a majority consensus of token holders agrees on a retirement proposal. The exact consensus criteria for token retirement or any token utility changes have to be implemented at the token protocol level, as part of the overall ecosystem protocol, and should not be changeable after initiation to avoid extortion and discouragement attacks on a token economy. Therefore, the consensus rules have to be carefully crafted at the beginning to allow for sufficient fiscal and monetary token flexibility. For example, voting rights based strictly on the size of stake will lead to power concentration in the token economy, which is to be avoided at all cost as this leads to self-optimization rather than ecosystem-optimization;
- A token should allow a participant to participate in any ecosystem actions; e.g., buying and selling of goods and services;
- A protocol token does not represent an ownership right. It represents a unit of ecosystem economic value, at minimum for utility services. Ownership of assets should be managed through tokens defined at the application layer. Assets themselves are to be defined at the application and not the protocol layer;
- One or more tokens can be earned through actions in an ecosystem; e.g., services for tokens that are governed by a set of rules agreed upon by the counterparties of the action;
- Except for reputation tokens, tokens should be freely transferable amongst ecosystem participants;
- Except for reputation tokens, tokens are freely exchangeable for any other token and any other non-ecosystem token (cross ecosystem token transfer e.g., Token to Ether or USD);
- There should be a fixed number of tokens at ecosystem creation (ecosystem specific and agreed upon by ecosystem instantiating actors) with the number allowed to increase or decrease over time as mentioned before;
- New tokens at the protocol level are created only through utility services such as running a Blockchain node. The number of new tokens per service; e.g., the size of a Block reward—and what constitutes a utility service is agreed upon by the participants defining a utility service for an ecosystem through consensus;
- New tokens are distributed to one or more participants providing an ecosystem utility service. The manner of distribution is specific to an ecosystem and is agreed upon by the participants in utility services through consensus; e.g., based on the size of their stake in a PoS consensus model powering a Blockchain;
- The growth of a token quantity over one or more fixed time periods should be limited to Y%. The growth rate Y, the number of time periods, and the definition of length of a time period is governed by consensus of the ecosystem participants;
- Tokens can be destroyed through the actions of participants either voluntarily or involuntarily. The rules governing the destruction of tokens require:
- Consensus of ecosystem participants if the rules can affect the token balance of any actor in an ecosystem, such as ecosystem utility services.
- One or more ecosystem participants if the destruction rules affect only the token balances of ecosystem participants making the token destruction rules. A token contract governing a token will have to contain a method that allows a participant holding tokens to destroy them. In order to avoid malicious behavior in case a participant is compromised, there should be an escrow function as part of the token contract that either prevents or makes malicious behavior very difficult.
6.3.3. Attack Vectors & Mitigations
6.4. Proposal 4: Decentralized Exchanges
- where there are no information and trading capability asymmetries due to full exchange market transparency and standard trading capabilities provided to everyone.
- so the exchange governance itself is being administered through a DAO/Common with built-in programmatic consensus mechanisms.
- where liquidity cannot be artificially concentrated since non-ecosystem assets used in the exchange facility are required to be escrowed, increasing the opportunity cost of external assets if only used for extractive purposes (short term horizon).
- where token values of a decentralized economy are, at least partially, tied to underlying digital assets rather than just based on the trust external actors place in the DAO governing the decentralized economy/commons.
6.4.1 Attack Vectors & Mitigations
- Front Running/Transaction Ordering Attacks: This is a quite simple, yet effective attack. A Blockchain node can observe all bid/ask spreads in the exchange as well as all incoming exchange transactions. With this information, an attacker controlling a Blockchain node can exploit the information asymmetry between what the node can see and the other market participants and create arbitrage by placing its own exchange transaction before all others and, therefore, capitalize on small price imbalances. Mitigation: As discussed in Proposal #1 and detailed in (Bakshi and Freund 2018), these type of attacks can be mitigated using consensus driven overlay networks using trusted hardware;
- Transaction Censoring Attacks: Besides inserting their own transaction ahead of any other exchange transaction, a malicious node can simply ignore transactions and never execute them. We have discussed this extensively before in Proposal #1. Mitigation: The mitigation strategy is the same as for Front Running/Transaction Ordering Attacks;
- Value Extraction Attacks: Such attacks can take many forms, such as hording tokens, short selling tokens in secondary markets not controlled by the decentralized exchange, or otherwise trying to manipulate prices through collusion and/or extortion attacks unrelated to consensus. Mitigation: To avoid such value extraction attacks the DAO regulating the decentralized exchange facility can increase capital requirements to be escrowed, increasing the opportunity costs of attackers significantly. The DAOs that have issued tokens that are traded can use Proposal #3 and increase token supply when for example hording is detected, which will bring down token prices. Short selling of tokens is also not possible since one has to lock up capital to do so. This capital could be totally lost if a malicious action proposal, see (Freund 2018) for more details, is submitted and accepted to the DAO overseeing the decentralized exchange functionality. Again, the full transparency of the ledger prevents malicious actors to leverage information asymmetry for gains.
7. Conclusions
Author Contributions
Acknowledgments
Conflicts of Interest
References
- Akerlof, George A. 1995. The Market for ‘Lemons’: Quality Uncertainty and the Market Mechanism. In Essential Readings in Economics. Edited by Saul Estrin and Alan Marin. London: Macmillan Education UK, pp. 175–88. [Google Scholar]
- Arnold, Malcolm F. 2008. Non-financial performance metrics for corporate responsibility reporting revisited. A Doughty Centre for Corporate Responsibility. Working paper, 40. Available online: https://dspace.lib.cranfield.ac.uk/handle/1826/3222 (accessed on 4 May 2018).
- Our Product—B3i. n.d. Available online: https://b31tech/our-product.html (accessed on 7 May 2018).
- Backfeed | Spreading Consensus. n.d. Available online: http://backfeed.cc/ (accessed on 4 May 2018).
- Bakshi, Sanjay, and Andreas Freund. 2018. Increasing Blockchain Security, Scalability, Privacy and Decentralization through Trusted Compute Resources. Preprint in preparation. [Google Scholar]
- Bano, Shehar, Alberto Sonnino, Mustafa Al-Bassam, Sarah Azouvi, Patrick McCorry, Sarah Meiklejohn, and George Danezis. 2017. SoK: Consensus in the Age of Blockchains. Available online: https://arxiv.org/pdf/1711.03936 (accessed on 7 May 2018).
- Bauwens, Michel, and Vasilis Niaros. 2016. Value in the Commons Economy: Developments in Open and Contributory Value Accounting. Available online: http://confrontations.org/wp-content/uploads/2016/12/1.Value-in-the-Commons-Economy_M.-Bauwens.pdf (accessed on 15 March 2018).
- Bauwens, Michel, and John Restakis. 2015. Commons Transition: Policy Proposals for an Open Knowledge Commons Society. Available online: https://commonstransition.org/wp-content/uploads/2014/11/Commons-Transition_-Policy-Proposals-for-a-P2P-Foundation.pdf (accessed on 1 March 2018).
- Beck, Don Edward, Teddy Hebo Larsen, Sergey Solonin, Rica Viljoen, Rica Viljoen, and Thomas Johns. 2018. Spiral Dynamics in Action: Humanity’s Master Code. Hoboken: Wiley, Available online: https://books.telegraph.co.uk/Product/Don-Edward-Beck/Spiral-Dynamics-in-Action--Humanitys-Master-Code/20666740 (accessed on 9 May 2018).
- Bissonnette, Zac. 2015. The Great Beanie Baby Bubble by Zac Bissonnette. Portfolio/Penguin. Available online: https:www.penguinrandomhouse.combooks313121the-great-beanie-baby-bubble-by-zac-bissonnette9781591848004 (accessed on 9 May 2018).
- Blenko, Marcia, Michael C. Mankins, and Paul Rogers. 2010. Decide & Deliver: 5 Steps to Breakthrough Performance in Your Organization. Boston: Harvard Business Review Press. [Google Scholar]
- Boldrin, Michele, and David K. Levine. 2005. Intellectual Property and the Efficient Allocation of Social Surplus from Creation. Review of the Economic Research on Copyright Issues 2: 45–66. [Google Scholar]
- Bollier, David. 2017. Re-Imagining Value: Insights from the Care Economy, Commons, Cyberspace and Nature. Commons Strategies Group in cooperation with the Heinrich Böll Foundation and David Graeber. Available online: https://www.boell.de/en/2017/03/07/re-imagining-value-insights-care-economy-commons-cyberspace-and-nature (accessed on 22 March 2018).
- Boschee, Jerr. 2010. Merging the Profit Motive and Moral Imperatives: The Rise of Social Enterprise in the United States. Geneva: The Institute for Social Entrepreneurs. [Google Scholar]
- Brown, Dana. 2017. Ecuador’s ‘Citizen Revolution.’ Latin America’s “Pink Tide” and the Challenge of Systemic Change (Blog). Available online: https://thenextsystem.org/learn/stories/ecuadors-citizen-revolution (accessed on 7 August 2017).
- Buterin, Vitalik, and Virgil Griffith. 2017. Casper the Friendly Finality Gadget. ArXiv, arXiv:1710.09437. [Google Scholar]
- Coindesk. 2018. Available online: https://www.coindesk.com/vietnam-investigates-ico-fraud-660-million-losses-reported/ (accessed on 11 April 2018).
- Colony: A Platform for Open Organizations. n.d. Available online: https://colony.io (accessed on 7 May 2018).
- Commons Transition Primer. 2018. Case Studies. Available online: http://primer.commonstransition.org/4-more/5-elements/case-studies (accessed on 15 March 2018).
- Commons-Based Peer Production Directory. 2018. Welcome to the P2Pvalue Directory of Commons Based Peer Production. Available online: http://directory.p2pvalue.eu/ (accessed on 15 March 2018).
- Cong, Lin William, and Zhiguo He. 2018. Blockchain Disruption and Smart Contracts. Available online: https://www.ssrn.com/abstract=2985764 (accessed on 9 May 2018).
- Cong, Lin William, Zhiguo He, and Jiasun Li. 2018. Decentralized Mining in Centralized Pools. Available online: https://www.ssrn.com/abstract=3143724 (accessed on 9 May 2018).
- Dave Grace & Associates. 2014. Measuring the Size and Scope of the Cooperative Economy: Results of the 2014 Global Census on Co-Operatives. For the United Nation’s Secretariat Department of Economic and Social Affairs Division for Social Policy and Development. Available online: http://www.un.org/esa/socdev/documents/2014/coopsegm/grace.pdf (accessed on 22 March 2018).
- Dees, Gregory, and Beth Battle Anderson. 2007. Enterprising Social Innovation: Focusing Research on the Most Intriguing Form of Social Entrepreneurship. Social Enterprise Reporter 302–3: 1–14. [Google Scholar]
- Digital Library of the Commons. n.d. Available online: http://dlc.dlib.indiana.edu/dlc/contentguidelines (accessed on 22 March 2018).
- District0x. n.d. Available online: https://district0x.io/ (accessed on 7 May 2018).
- Dunbar, Robin I. M. 1992. Neocortex Size as a Constraint on Group Size in Primates. Journal of Human Evolution 22: 469–93. [Google Scholar] [CrossRef]
- Dunn, Cheryl, Gregory Gerard, and Severin Grabski. 2016. Resources-Events-Agents Design Theory: A Revolutionary Approach to Enterprise System Design. Communications of the Association for Information Systems 38. [Google Scholar] [CrossRef]
- DuPont, Quinn. 2017. Experiments in Algorithmic Governance: A History and Ethnography of “The DAO,” a Failed Decentralized Autonomous Organization. Chapter 8, Bitcoin and Beyond. Abingdon: Routledge, Available online: https://www.researchgate.net/publication/319529311_Experiments_in_Algorithmic_Governance_A_history_and_ethnography_of_The_DAO_a_failed_Decentralized_Autonomous_Organization (accessed on 9 May 2018).
- Easley, David, Maureen O’Hara, and Soumya Basu. 2017. From Mining to Markets: The Evolution of Bitcoin Transaction Fees. Available online: https://www.ssrn.com/abstract=3055380 (accessed on 9 May 2018).
- Faircoin—P2P Foundation. n.d. Available online: http://wiki.p2pfoundation.net/Faircoin#Details (accessed on 22 March 2018).
- FairCoop. 2017. What Can We Do with Our FairCoin? Available online: https://fair-coin.org/en/what-can-we-do-our-faircoin (accessed on 22 March 2018).
- FairCoop principles. n.d. Available online: https://2017.fair.coop/principles/ (accessed on 9 May 2018).
- FairFunds. n.d. Available online: https://2017.fair.coop/fairfunds/ (accessed on 9 May 2018).
- Filippi, Primavera De, Benjamin Loveluck, Vasilis Niaros, Alekos Pantazis, and Mayo Fuster Morell. n.d. Best Practices for CBPP Communities & Policy Recommendations. Available online: https://p2pvalue.eu/wp-content/uploads/2013/07/Deliverable_2.3-updated.pdf (accessed on 22 March 2018).
- Financial Agreement Enspiral Handbook. n.d. Available online: https://handbook.enspiral.com/agreements/financial.html (accessed on 9 May 2018).
- Freund, Andreas. 2018. Model for Consensus Controlled, Socioeconomic Incentivized and Platform Driven Decentralized Economies and Businesses. Available online: https://docs.google.com/document/d/1vlOoXhHIS2hSNysH7eP44X3yP990F0zHMV_rSztQGZs/edit (accessed on 9 May 2018).
- Giotitsas, Chris, and Jose Ramos. 2017. A New Model of Production for a New Economy. The New Economics Foundation. Available online: https://p2pfoundation.net/wp-content/uploads/2017/09/A-New-Model-of-Production-for-a-New-Economy-FINAL.pdf (accessed on 22 March 2018).
- Goldgar, Anne. 2007. Tulipmania: Money, Honor, and Knowledge in the Dutch Golden Age. Available online: http://www.press.uchicago.edu/ucp/books/book/chicago/T/bo5414939.html (accessed on 22 March 2018).
- Graves, Clare W. 2005. The Never Ending Quest: Dr. Clare W. Graves Explores Human Nature: A Treatise on an Emergent Cyclical Conception of Adult Behavioral Systems and Their Development. ECLET Publishing. Available online: https://www.alibris.com/The-Never-Ending-Quest-Dr-Clare-W-Graves-Explores-Human-Nature-a-Treatise-on-an-Emergent-Cyclical-Conception-of-Adult-Behavioral-Systems-and-Their-Development/book/-97247421 (accessed on 22 March 2018).
- Harriman, Alyssa. 2015. The Making of a Movement: The Rise of the B Corp on the Global Stage. Ph.D. thesis, Copenhagen Business School, Frederiksberg, Denmark; p. 103. [Google Scholar]
- Haugen, Bob, and Lynn Foster. 2017. ValueFlows. Available online: https://www.valueflo.ws/ (accessed on 22 March 2018).
- Huberman, Gur, Jacob D. Leshno, and Ciamac C. Moallemi. 2017. Monopoly without a Monopolist: An Economic Analysis of the Bitcoin Payment System. Available online: https://www.ssrn.com/abstract=3025604 (accessed on 22 March 2018).
- ICOdata.io. 2018. Available online: icodata.io/stats/ (accessed on 9 May 2018).
- Kish, David. n.d. Ecosystem of You Presentation. The Next Evolution (Blog). Available online: http://www.thenextevolution.com/presentations-2/ecosystem-of-you-presentation/ (accessed on 22 March 2018).
- König, Thomas. 2016. FairCoin V2 White Paper. Available online: https://chain.fair-coin.org/download/FairCoin2-white-paper-V1.1.pdf (accessed on 9 May 2018).
- Kurzweil, Ray. 2005. Singularity Is Near. Penguin Random House. Available online: https:www.penguinrandomhouse.combooks291221pp-singularity-is-near-by-ray-kurzweil (accessed on 22 March 2018).
- Lewis, Michael. 2014. The New New Thing: A Silicon Valley Story. New York: W. W. Norton & Company. [Google Scholar]
- Li, Jiasun, and William Mann. 2018. Initial Coin Offering and Platform Building. Available online: https://papers.ssrn.com/sol3/papers.cfm?abstract_id=3088726 (accessed on 9 May 2018).
- Manzanedo, Ana, and Alícia Trepat. 2017. Designing Positive Platforms: A Guide for a Governance-Based Approach. Palo Alto: Institute for the Future Research on Positive Platforms, p. 16. [Google Scholar]
- Mueller, Lukas. 2018. Conceptual Framework for Legal and Risk Assessment of Crypto Tokens. Available online: https:// www.mme.ch/fileadmin/files/documents/180501_BCP_Framework_for_Assessment_of_Crypto_Tokens_-_Block_2.pdf (accessed on 9 May 2018).
- National Association of Housing Cooperatives. n.d. Significant Dates in Cooperative History. Available online: https://coophousing.org/resources/general-cooperative-information/significant-dates-in-cooperative-history/ (accessed on 22 March 2018).
- Ortmann, Gerald F., and Rober P. King. 2007. Agricultural Cooperatives I: History, Theory and Problems. Agrekon 46: 18–46. [Google Scholar] [CrossRef]
- Pass, Rafael, and Elaine Shi. 2016a. Snow White: Provably Secure Proofs of Stake. Available online: https://ia.cr/2016/919 (accessed on 9 May 2018).
- Pass, Rafael, and Elaine Shi. 2016b. The Sleepy Model of Consensus. Available online: https://ia.cr/2016/918 (accessed on 9 May 2018).
- Peer Production License—P2P Foundation. n.d. Available online: http://wiki.p2pfoundation.net/Peer_Production_License#Simple_Definition_and_the_PPL_as_a_Transvestment_Stategy (accessed on 22 March 2018).
- Peerism: The Skill Token Economy for Post-Capitalism. n.d. Available online: http://peerism.org/ (accessed on 7 May 2018).
- Poon, Daryl. 2011. The Emergence and Development of Social Enterprise Sectors. Available online: https://repository.upenn.edu/cgi/viewcontent.cgi?referer=https://www.google.com/&httpsredir=1&article=1010&context=sire (accessed on 9 May 2018).
- R3.Com Technology. n.d. Available online: https://www.r3.com/technology/ (accessed on 7 May 2018).
- Saleh, Fahad. 2017. Blockchain without Waste: Proof-of-Stake. Available online: https://pdfs.semanticscholar.org/cd35/131e29c6122dbacdb95d569be5b391da083a.pdf (accessed on 9 may 2018).
- Sensorica. n.d. Sensorica—Commons Transition Wiki. Available online: http://wiki.commonstransition.org/wiki/Sensorica#Value_Accounting_in_Sensorica (accessed on 22 March 2018).
- Smith, H. Jeff. 2003. The Shareholders vs. Stakeholders Debate. Magazine. MIT Sloan Management Review (Blog). Available online: https://sloanreview.mit.edu/article/the-shareholders-vs-stakeholders-debate/ (accessed on 22 March 2018).
- Startup Tracker. 2018. Outlier Ventures (Blog). Available online: https://outlierventures.io/startup-tracker/ (accessed on 16 February 2018).
- Sundell, Ville. 2017. “Etherpriseses LLC, set up your own company on Ethereum”. Available online: https://www.linkedin.com/pulse/etherprises-llc-set-up-your-own-company-ethereum-ville-sundell (accessed on 9 May 2018).
- Torrance, Andrew W., and Bill Tomlinson. 2009. Patents and the Regress of Useful Arts. The Columbia Science and Technology Law Review 10: 130–68. [Google Scholar]
- Venture Agreement Enspiral Handbook. n.d. Available online: https://handbook.enspiral.com/agreements/venture.html (accessed on 9 May 2018).
- Yermack, David. 2016. Corporate Governance and Blockchain. Available online: www.nber.org/papers/w21802 (accessed on 9 May 2018).
| 1 | Meaning non-members profit, but at a net loss to the decentralized market. |
| 2 | Blockchain projects related to supply chain & logistics, provenance & notary, payments, legal, audit & tax, Internet of Things, infrastructure, identity & reputation, compliance & security, data analytics, financial services, and governance & transparency were considered to be “global well-being purposes,” which comprised 50% of the 1352 Blockchain startups listed (Startup Tracker 2018). |
| 3 | With decentralization we refer to governance, ownership and control as well as infrastructure. |
| 4 | Without a Nothing-at-Stake problem and without either federation or lack of imperative mandate. |
| 5 | Non-competitive in this context means that participants are not competing against one another or other external entities per se but are aligned to create value around a purpose that is addressing a set of societal or common individual challenges or opportunities. |
| 6 | The Digital Library of the Commons defines “commons” as “a general term for shared resources in which each stakeholder has an equal interest” (Digital Library of the Commons n.d.). |
| 7 | As defined by a DCM governing DAO through participant consensus. |
| 8 | The comments below were informed by multiple discussions with regulators, and several securities attorneys having done multiple ICOs each and the reading of 60+ ICO whitepapers. |
| 9 | Note that the legal definition of a legal, person or legal, non-person entity can vary wildly by jurisdiction. We are discussing the most common form that treats legally registered businesses different from individual people. |
| 10 | Based on private discussions of the authors with several regulators, a cryptocurrency may be classified as a security, if a predetermined set of people received a set of tokens in exchange for either fiat currency or other crypto currencies/platform tokens with the purpose of financing the building of the cryptocurrency platform before the new cryptocurrency or token platform was launched and/or the issuance was accompanied with an either direct or indirect promise of cryptocurrency/platform token value gain. |
| 11 | Management of competitive organizations commonly subscribe to the shareholder theory, where their ethical role is to maximize profits for shareholders. In competitive markets today, another management theory is emerging. The stakeholder theory, coined in the mid-1900s and generating more interest by the early 2000s (Arnold 2008), expands the corporation’s purpose to serve all entities that contributed to the wealth of the business (Smith 2003). The stakeholder theory, closely related to corporate social responsibility (CSR), expands performance metrics beyond revenue and into the realm of social impact. These impacts are often still competitive in nature, however, and are often only valued by the corporation because the CSR activities actually feed back into a revenue stream (Arnold 2008). A simple example would be an IT company focusing CSR efforts on STEM education programs. No matter which management theory the organization subscribes to, the corporation still remains competitive in nature as it assumes that it will best serve either its stakeholders, or shareholders, by improving its position in the market. |
| 12 | Information symmetry is achieved when all market participants have the same information available to them at all times. |
| 13 | More explicitly, (the number of producing organizations (project teams)/market opportunity) in a decentralized market is greater than (the number of producing organizations (firms)/market opportunity) in a competitive market by virtue of project teams having fewer people than firms because there is no bureaucracy. This is a theory based on logic, not observation. |
| 14 | Bounded rationality means actors make imperfect decisions because of a lack of understanding, time, or access to information. |
| 15 | Here we assume imperfect competition to consider real-world, rather than theoretical markets, although we will continue to refer to them simply as competitive markets. |
| 16 | Information asymmetry has been reduced by the internet and ecommerce. Easy access to competitors’ pricing and quality has reduced this information asymmetry. |
| 17 | Asset sharing arguably happens within a firm, so the distinction of closed and open IP is the organizational boundary. The competitive corporation’s boundaries are limited to employees. The decentralized socioeconomic model’s boundaries are members, but unlike a company with limited resources and a limited number of employees, decentralized socioeconomic models can accept an unlimited number of members and scale their protection of the commons with the EC on Blockchain without incurring additional costs. |
| 18 | A reputation token represents the appreciation of any justified and finalized giving action without any economic compensation through ecosystem tokens or other ecosystem external assets; e.g., you cannot build a barn and get paid in bread and expect to gain social reputation (Freund 2018). |
| 19 | Non-exchangeable value refers to efforts that benefit humankind, but do not produce a product or service that a single person would rationally buy. One example is reducing your personal carbon footprint. |
| 20 | Global markets refers to both decentralized and competitive markets. |
| 21 | Number of producing organizations, barriers to entry, product differentiation, and information symmetry/asymmetry. |
| 22 | The feeling of value being disproportionately earned by an actor is subjective to the producing unit members, but solidified in objective measures through the consensus process. Therefore value earned can only be disproportionate if other producing members feel it is. |
| 23 | Value sovereignty is “the capacity to self-regulate its relations with the market and to assure that significant aspects of its common wealth and social relationships remain inalienable—not for sale via market exchange.” Put another way, “... a commons must be able to develop “semi-permeable boundaries” that enable it to safely interact with markets on its own terms. For example, a coastal fishery functioning as a commons may sell some of its fish to markets, but the goals of earning money and maximizing profit cannot be allowed to become so foundational that it crowds out commons governance and respect for ecological limits.” (Peer Production License—P2P Foundation n.d.). |
| 24 | Proof-of-Stake = An Algorithm that requires participants to provide an economically meaningful stake of some type that allows them to participate as a network validator in a consensus protocol and earn money through rewards. The economic stake can be lost if a validator violates specific rules of a consensus protocol. Therefore, the economic stake acts as a deterrent to malicious validator behavior. |
| 25 | One fork that is k blocks longer than any other fork, where k is either dynamically determined or static, and is determined to have achieved consensus. |
| 26 | If validators do not participate in voting for a certain period of time they lose all of their stake over time. |
| 27 | See the discussion in Section 3.1 on token types and how they might or might not be treated from a regulatory point of view. |
| 28 | A giving transaction is a cryptographic proof of a social good action that has not been done in exchange for any monetary value or other economically relevant advantage and is verifiable by a set of validators. See detailed definition of a giving transaction in (Freund 2018). |
| 29 | Economic Finality: A state H1 is economically finalized if enough validators sign a message attesting to H1, with the property that if both H1 and a conflicting H2 are finalized, then there is evidence that can be used to prove that at least x% of validators were malicious and therefore destroy their entire deposits where x = 1 – p with p > 50% being the consensus majority parameter see Casper FFG (Buterin and Griffith 2017) as an example. |
| 30 | See (Freund 2018) for a detailed description and discussion of such a decentralized exchange facility and its processes. |
| 31 | See (Freund 2018) for a detailed description and discussion of such a decentralized exchange facility and its processes. |
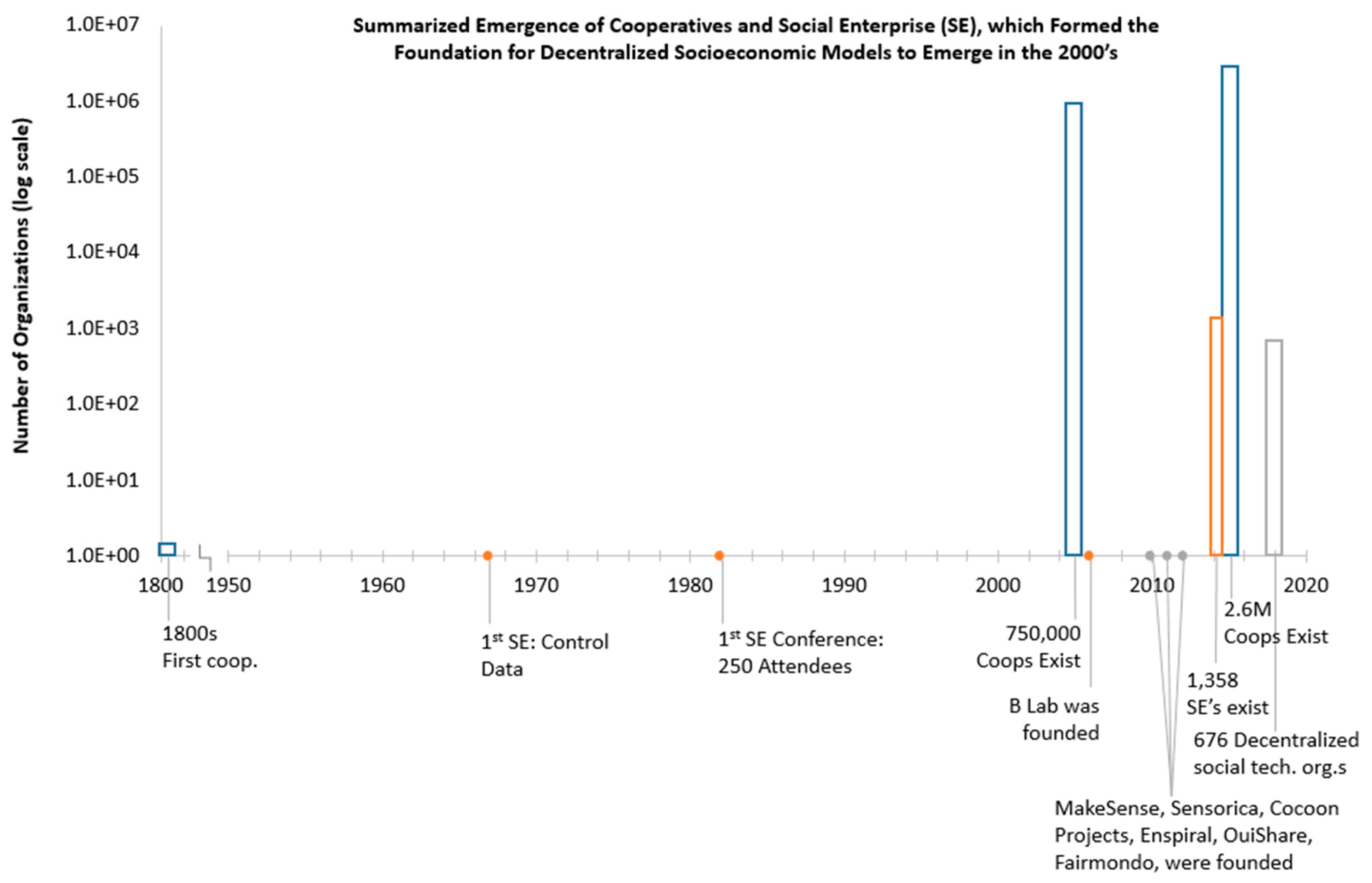
| Token/Type | Purpose | Usage | Underlying Value | Model Layer |
|---|---|---|---|---|
| Entrepreneurial Common Tokens (EC Tokens)/Native Utility Token | Exchangeable for Protocol Tokens, other DAO tokens, Fiat | Currency | Fiat, Protocol Tokens or Assets held in common by DAO | Decentralized Economies Applications Layer |
| Production Common Token (PC Tokens)/Ownership Token | Governed by FBC Values member contributions Exchangeable for EC Tokens | Claim Right | Asset backed | Decentralized Economies Applications Layer |
| Production Common Token (PC Tokens)/Native Utility Token | Governed by FBC Values member contributions Exchangeable for EC Tokens | Access Right to Asset | Asset backed | Decentralized Economies Applications Layer |
| Platform Token/Native Utility Token | Participate in platform and DAO actions. Confers voting rights for platform utility services | Currency | Platform Services | Protocol Layer |
| Primary Market Characteristics | Decentralized Socioeconomic | Competitive |
|---|---|---|
| Number of producing organizations | Many. The producing organization (project team) is the size of an effective project team | Many, but fewer because the producing organization (firm) is usually comprised of many project teams |
| Barriers to Entry | Almost nonexistent because all assets are held in common | Low because fixed costs are assumed to be low |
| Product Differentiation | Homogenous locally Differentiated globally | Differentiated |
| Information Symmetry | Approaches symmetric | Asymmetric |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Freund, A.; Stanko, D. The Wolf and the Caribou: Coexistence of Decentralized Economies and Competitive Markets. J. Risk Financial Manag. 2018, 11, 26. https://doi.org/10.3390/jrfm11020026
Freund A, Stanko D. The Wolf and the Caribou: Coexistence of Decentralized Economies and Competitive Markets. Journal of Risk and Financial Management. 2018; 11(2):26. https://doi.org/10.3390/jrfm11020026
Chicago/Turabian StyleFreund, Andreas, and Danielle Stanko. 2018. "The Wolf and the Caribou: Coexistence of Decentralized Economies and Competitive Markets" Journal of Risk and Financial Management 11, no. 2: 26. https://doi.org/10.3390/jrfm11020026
APA StyleFreund, A., & Stanko, D. (2018). The Wolf and the Caribou: Coexistence of Decentralized Economies and Competitive Markets. Journal of Risk and Financial Management, 11(2), 26. https://doi.org/10.3390/jrfm11020026