A Risk Management Approach for a Sustainable Cloud Migration
Abstract
:1. Introduction
2. Related Work
2.1. Sustainable Information System (IS) and Cloud
2.2. Risks Management in Cloud Computing
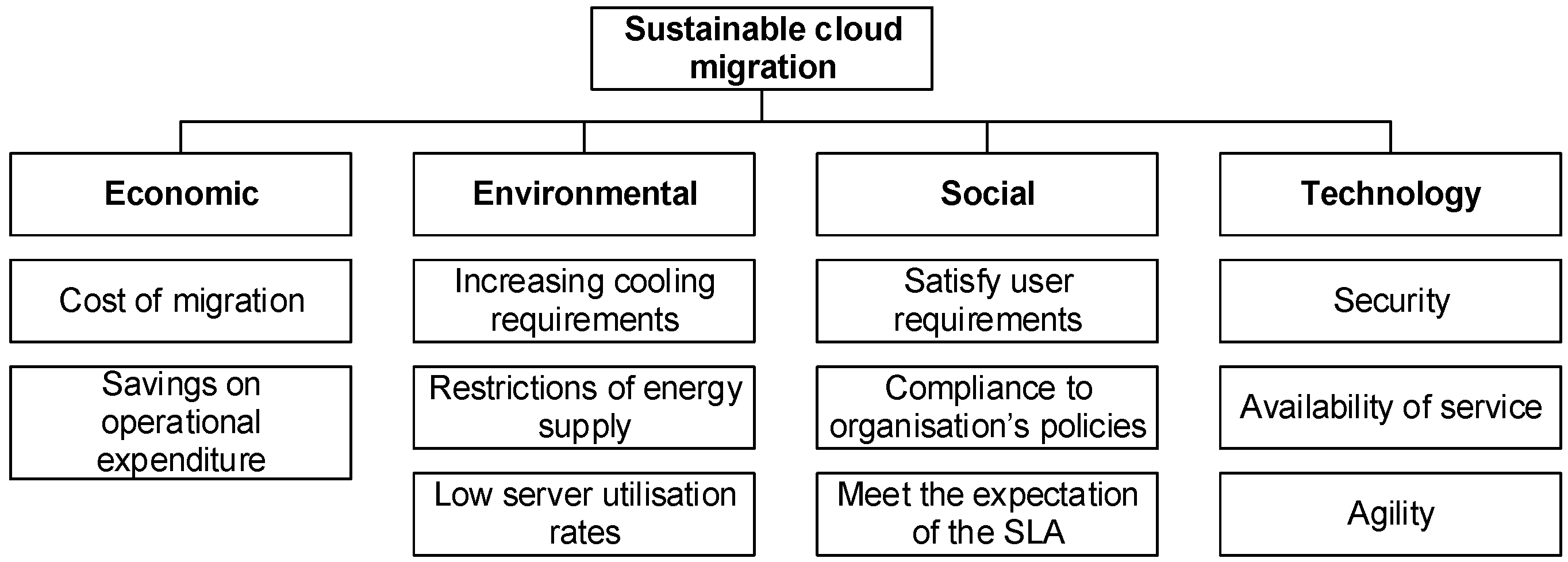
3. Sustainable Cloud Migration
The ability of cloud services to satisfy internal and external users’ value, economic value, business continuity, flexibility and agility of the system and environmental value.
3.1. Sustainable Dimensions
3.1.1. Economic Dimension
3.1.2. Environmental Dimension
3.1.3. Social Dimension
3.1.4. Technology Dimension
3.2. Principles and Characteristics for a Sustainable Cloud Migration
4. Demspter Shafer Theory (D-S Theory) of Evidence
4.1. Basic Probability Assignment (bpa) or m-Values
4.2. Belief Functions
- Control 1:
- mC1 (a), mC1 (~a), mC1 ({a,~a})
- Control 2:
- mC2 (a), mC2 (~a), mC2 ({a,~a})
- Control n:
- mCn (a), m Cn (~a), mCn ({a,~a})
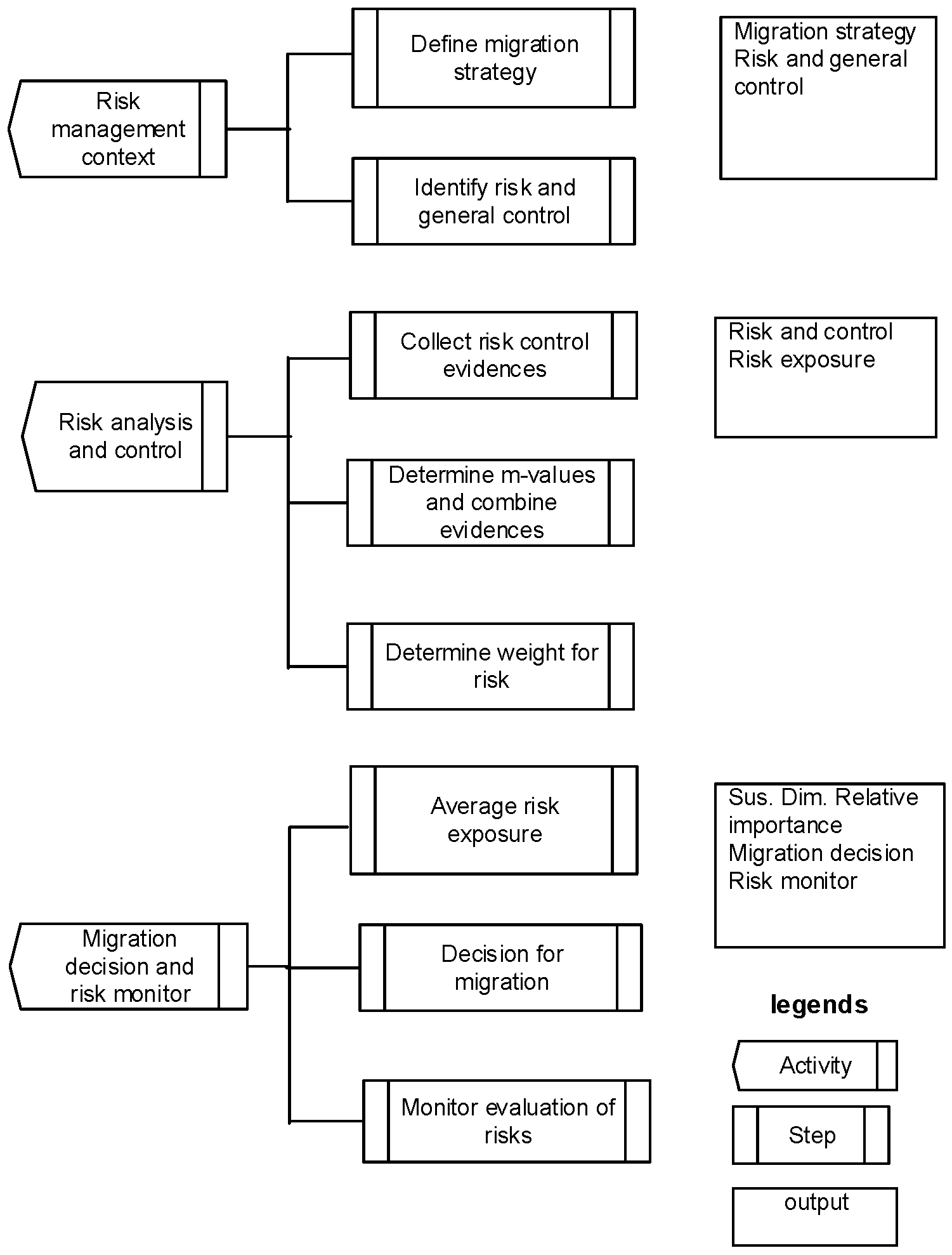
5. Risk Management Approach
5.1. Activity 1: Risk Management Context
- Migration type: Type I: Replace, Type II: Partially migrate, Type III: Migrate the whole software stack Type IV: Cloudify.
- Service model: suitable service model, i.e., IaaS, SaaS, PaaS.
- Deployment model: suitable deployment model, i.e., public, private, community and hybrid
- Security assessment: include access controls, data governance, change management, business continuity, incident handling, third party management, compliance to rules and regulations, auditability of virtual records, data retention policies and physical security.
- Migration size: migration size depends on the relevant application and data properties. The application properties include inherent application components, storage, integration point, business logic. Data include type, registry, size, format, sources, and dependency with the application. Furthermore, it is also necessary to identify the sensitivity of the migrated data so that appropriate protection requirements can be identified. User data migrates into the cloud can be different categories, i.e., Personal Identifying Information (PII), depersonalized information and anonymised information.
- Financial assessment: evaluation on cost savings or return on investment includes cloud deployment, timing of the migration, application and data requirements, and platform storage. The bigger the migration, the higher expected migration costs and complexity.
5.2. Activity 2: Risks Analysis and Control
- Adequate (A): Control is adequate to mitigate a risk
- Not adequate (N): Control is not adequate to mitigate a risk
- Partial adequate (P): Control is either adequate or inadequate to mitigate a risk
- ri: Individual risk of any category, i.e., economic, environmental, social and technology
- i = 1 ... n
- RE: Exposure of risk ri
- P: Probability of risk ri
- I: Impact of risk ri
5.3. Activity 3: Migration Decision and Risk Monitor
- Rsustainable (Economic) = Total sustainable risk exposure for economic
- Ren = n number of risk exposure for economic.
- (a)
- The number of sustainability dimensions that linked to a high risk exposure should be less than three.
- (b)
- Risk exposure is insignificant and can be mitigated by the existing controls.
- (c)
- The controls are adequate and have been designed in accordance with relevant legislations, regulations or best practices for the sustainability dimension which is deemed to be important.
- (d)
- There is adequate justification and documentation relevant to the cloud migration procedures and practised.
- (e)
- The cloud migration is for noncomplex application systems or the migration size is small.
- (a)
- The number of sustainability dimensions that linked to a high risk exposure should be less than two.
- (b)
- There are evidence that threats or risk are manageable.
- (c)
- There is adequate justification and documentation relevant to the cloud migration procedures and practised.
- (d)
- The migration is intended for core systems of the organisation and the existing controls are effective and efficient to mitigate risks. Appropriate control measures are designed to minimise risk for each sustainability dimensions.
- (a)
- The controls are not adequate to mitigate risks.
- (b)
- The controls have not been designed in accordance with relevant legislations, regulations or best practises.
6. Evaluation
- Identify risk and possible control for making a viable sustainable decision;
- Examine the applicability of using sustainable dimension and risk for the cloud migration decision.
6.1. Migration Use Case
6.2. Introduction of Risk Management Process
6.2.1. Activity 1: Risk Management Context
- Migration type: Type II: Partially migrate due to not considering the whole MoH.
- Service model: SaaS
- Deployment model: public
- Security assessment: access controls, data governance, change management, business continuity, incident handling, third party management, compliance to rules and regulations, auditability of virtual records, data retention policies and physical security.
- Migration size: The application and data requirements are identified. The application requirements include components, storage, integration point, business logic. Data requirements include files, registry information, size of data, sources and storage. The category of data and its sensitivity are also taken into consideration.
6.2.2. Activity 2: Risks Analysis and Control
- m(A) = 0.9259
- m(P) = 0.0740
- m (N) = 0.00000
6.2.3. Activity 3. Migration Decision and Risk Monitor
6.3. Discussion
6.3.1. Applicability of the Sustainable Cloud Migration Approach
6.3.2. Sustainability Risk Driven Approach for Sustainable Cloud Migration
6.3.3. Evaluation Inherent Risks for Cloud Migration
6.3.4. Risk Management Process and Artefacts
6.3.5. Limitations of the Framework and Study Validity
7. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Accenture. 2010. Cloud Computing and Sustainability: The Environmental Benefits of Moving to the Cloud. Hong Kong: Accenture, pp. 1–11. [Google Scholar]
- Asif, Muhammad, Cory Searcy, Ambika Zutshi, and Olaf A. M. Fisscher. 2013. An integrated management systems approach to corporate social responsibility. Journal of Cleaner Production 56: 7–17. [Google Scholar] [CrossRef]
- Awasthi, Anjali, and Satyaveer S. Chauhan. 2011. Using AHP and Dempster–Shafer theory for evaluating sustainable transport solutions. Environmental Modelling & Software 26: 787–96. [Google Scholar]
- Bash, Cullen, Tahir Cader, Yuan Chen, Daniel Gmach, Richard Kaufman, Dejan Milojicic, and Puneet Sharma Shah. 2011. Cloud Sustainability Dashboard, Dynamically Assessing Sustainability of Data Centers and Clouds. Palo Alto: HP Laboratories, HPL-2011-148. [Google Scholar]
- Behrend, Tara S., Eric N. Wiebe, Jennifer E. London, and Emily C. Johnson. 2011. Cloud computing adoption and usage in community colleges. Behaviour & Information Technology 30: 231–40. [Google Scholar]
- Beynon, Malcom, Darren Cosker, and David Marshall. 2011. An expert system for multi-criteria decision making using Dempster Shafer theory. Expert Systems with Applications 20: 336–57. [Google Scholar] [CrossRef]
- Brender, Nathalie, and Iliya Markov. 2013. Risk perception and risk management in cloud computing: Results from a case study of Swiss companies. International Journal of Information Management 33: 726–33. [Google Scholar] [CrossRef]
- Chang, Victor, David De Roure, Gary Wills, and Robert Walters. 2011. Case studies and organisational sustainability modelling presented by cloud computing business framework. International Journal of Web Services Research 8: 26–53. [Google Scholar] [CrossRef]
- Dempster, Arthur P. 1967. Upper and lower probabilities induced by a multivalued mappings. The Annals of Mathematical Statistics 38: 325–39. [Google Scholar] [CrossRef]
- Dempster, Arthur P. 1968. A generalization of Bayesian inference. Journal of the Royal Statistical Society 30: 205–47. [Google Scholar]
- ENISA. 2009. Cloud Computing Benefits, Risks and Recommendations for Information Security. Available online: https://resilience.enisa.europa.eu/cloud-security-and-resilience/publications (accessed on 2 June 2017).
- Gruschka, Nils, and Luigi Lo Iacono. 2009. Vulnerable Cloud: SOAP Message Security Validation Revisited. Paper presented at IEEE International Conference on Web Services, Los Angeles, CA, USA, July 5–10; pp. 625–31. [Google Scholar]
- Harmon, Rober, and Haluk Demirkan. 2011. The Next Wave of Sustainable IT. IEEE IT Professional 13: 19–25. [Google Scholar] [CrossRef]
- Harmon, Rober R., Tugrl Daim, and David Raffo. 2010. Roadmapping the Future of Sustainable IT. Paper presented at IEEE Conference on Technology Management for Global Economic Growth, Phuket, Thailand, July 18–22; pp. 1–10. [Google Scholar]
- Hessami, Ali G., Feng Hsu, and Hamid Jahankhani. 2009. A Systems Framework for Sustainability. Berlin and Heidelberg: Springer, pp. 76–94. [Google Scholar]
- Islam, Shareeful, Stefan Fenz, Edgar Weippl, and Christos Kalloniatis. 2016. Migration Goals and Risk Management in Cloud Computing: A Review of State of the Art and Survey Results on Practitioners. International Journal of Secure Software Engineering 7: 44–73. [Google Scholar] [CrossRef]
- Islam, Sahreeful, Stefen Fenz, Edgar Weippl, and Haris Mouratidis. 2017. A Risk Management Framework for Cloud Migration Decision Support. Journal of Risk and Financial Management 10: 10. [Google Scholar] [CrossRef]
- Kalloniatis, Christos, Haris Mouratidis, and Shareeful Islam. 2013. Evaluating Cloud Deployment Scenarios Based on Security and Privacy Requirements. Requirements Engineering 18: 299–319. [Google Scholar] [CrossRef]
- Khajeh-Hosseini, Ali, Ian Sommerville, Jurgen Bogaerts, and Pradeep Teregowda. 2011. Decision Support Tools for Cloud Migration in the Enterprise. Paper presented at IEEE 4th International Conference on Cloud Computing, Hangzhou, China, October 11–14; pp. 542–48. [Google Scholar]
- Madria, Sanjay, and Amartya Sen. 2015. Off-Line Risk Assessment of Cloud Service Provider. Paper presented at IEEE Cloud Computing Conference, Anchorage, AK, USA, June 27–July 2; vol. 2, No. 3. pp. 50–57. [Google Scholar]
- Mastroeni, Loretta, and Maurizio Naldi. 2011. Long-range Evaluation of Risk in the Migration to Cloud Storage. Paper presented at IEEE Conference on Commerce and Enterprise Computing, Luxembourg, September 5–7; pp. 260–66. [Google Scholar]
- Morin, Jean-Henry, Jocelyn Aubert, and Benjamin Gateau. 2012. Towards Cloud Computing SLA Risk Management: Issues and Challenges. Paper presented at 45th Hawaii International Conference on System Science, Maui, HI, USA, January 4–7. [Google Scholar]
- Müller, Gunter, Noboru Sonehara, Isao Echizen, and Sven Wohlgemuth. 2011. Sustainable Cloud Computing. Business & Information Systems Engineering 3: 129–31. [Google Scholar]
- Perrini, Francesco, and Antonio Tencati. 2006. Sustainability and stakeholder management: The need for corporate performance evaluation and reporting systems. Business Strategy and Environment 15: 296–308. [Google Scholar] [CrossRef]
- Puthal, Deepak, B. P. S. Sahoo, Sambit Mishra, and Satyabrata Swain. 2015. Cloud Computing Features, Issues, and Challenges: A Big Picture. Paper presented at Conference on Computational Intelligence & Networks, Bhubaneshwar, India, January 12–13. [Google Scholar]
- Rahman, Alifah Aida Lope Abdul, and Shareeful Islam. 2015. Sustainability Forecast for Cloud Migration. Paper presented at IEEE International Symposium on the Maintenance and Evolution of Service-Oriented and Cloud-Based Environments, Bremen, Germany, October 2. [Google Scholar]
- Rana, Omer. 2014. The Costs of Cloud Migration. IEEE Cloud Computing 1: 62–65. [Google Scholar] [CrossRef]
- Ristenpart, Thomas, Eran Tromer, Hovav Shacham, and Stefan Savage. 2009. Hey, you, get off of my cloud: Exploring information leakage in third-party compute clouds. Paper presented at 16th ACM Conference on Computer and Communications Security, New York, NY, USA, November 9–13; pp. 199–212. [Google Scholar]
- Schmidt, Nils-Holger, Koray Erek, Lutz M Kolbe, and Rüdiger Zarnekow. 2009. Sustainable Information Systems Management. Business & Information Systems Engineering 5: 400–2. [Google Scholar]
- Shafer, G. 1976. A Mathematical Theory of Evidence, a Mathematical Theory of Evidence. Princeton: Princeton University Press. [Google Scholar]
- Silvius, A. J. Gilber, Jasper Van Den Brink, and Jacobus Smit. 2009. Sustainability in Information and Communications Technology (ICT) Projects. Communications of the IIMA 9: 33–44. [Google Scholar]
- Sunyaev, Ali, and Stephen Schneider. 2013. Cloud services certificate. Communications of the ACM 56: 33–36. [Google Scholar] [CrossRef]
- Theoharidou, Marianthi, Nick Papanikolaou, Siani Pearson, and Dimitris Gritzalis. 2013. Privacy Risk, Security, Accountability in the Cloud. Paper presented at IEEE Cloud Computing Technology and Science (CloudCom), Bristol, UK, December 2–5. [Google Scholar]
- Wang, Chengen, Zhuming Bi, and Li Da Xu. 2014. IoT and Cloud Computing in Automation of Assembly Modeling Systems. IEEE Transactions on Industrial Informatics 10: 1426–34. [Google Scholar] [CrossRef]
- Yi, Sangho, Artur Andrzejak, and Derrick Kondo. 2012. Monetary cost aware checkpointing and migration on Amazon cloud spot intances. IEEE Transactions on Services Computing 5: 512–24. [Google Scholar] [CrossRef]
- Zhang, Xuan, Nattapong Wuwong, Hao Li, and Xuejie Zhang. 2010. Information Security Risk Management Framework for the Cloud Computing Environments. Paper presented at IEEE Computer and Information Technology, Bradford, UK, June 29–July 1. [Google Scholar]
| Process Level of Cloud Migration | Objective | Economic Controls | Environmental Controls | Social Controls | Technological Controls |
|---|---|---|---|---|---|
| Planning stage | No hidden cost, Timely Service and maintenance at expected level, Comply with organisation’s rules and policies. | Cost benefit analysis Measure cost effectiveness of each related cost to cloud migration. | Check for certification Check for Eco labels | Suppliers audit, Reliable clause of SLA, User requirements, Examine ethical policy, compare economic costs and benefits related to social activities and policies). | Software and hardware selection, Check user requirements. |
| Execution stage | Lower energy cost, Data center efficiency, Effectively outsourcing, Shared IS infrastructures, Shared application systems | Cost effectiveness | Increase cooling, Energy savings Low server utilization rates, Use dynamic provisioning, shared infrastructure, operate servers at higher utilisation rates, use advanced data centre infrastructure, power conditioning. | Business continuity, Satisfy user requirements, Check user’s competency, Compliance to data privacy and security. | Ease of use Flexibility of the systems, Agility of the systems. |
| Follow up | Effectively and timely maintain | Cost effective | Green IS compliance | Meet user’s objective | Availability of service |
| Criteria | Sub-Criteria | Indicator |
|---|---|---|
| ECONOMIC | Cost benefit analysis Procurement process effectiveness | Satisfaction assessment on compliance with financial rules and regulations |
| ENVIRONMENT | Green IT configuration Paperless Energy savings | Percentage savings for paperless environment, recycling, energy savings, reduction of general waste No of IT equipment shared Availability of green oriented disposal policy |
| SOCIAL | Compliance to rules and regulation Outsourcing Key performance indicator IS strategic plan Knowledge transfer User’s satisfaction Continuous monitoring | Satisfaction assessment on compliance with rules and regulation, control policies and procedure for application/third party provider, (percentage of objective attained) Percentage of employees who know the system’s functions(responsiveness, user friendly) Percentage of employees who can perform system maintenance procedures Satisfaction assessment for KPI achievement |
| TECHNOLOGY | Availability of service, service delivery flexibility Security | No of system incident reported Average time for system failure Percentage of accurate and reliable information/output produced by IS average time for generated output, application processing No of interaction for continuity of operation (availability of backup plan, storage facility) Satisfaction assessment of system flexibility Average time for network connectivity No of report produced by audit trails Average recovery time after service is down Average time to restore the data Ability to add, modify and remove any software , hardware or data components from IS infrastructure Availability of destruction procedure |
| Risk | General Controls |
|---|---|
Economic
|
|
Environmental
|
|
Social
|
|
Technology
|
|
| Score | Likelihood | Likelihood of Occurrence |
|---|---|---|
| 5 | Expected | More than 90% chance of occurrence |
| 4 | High | 64–89% chance of occurrence |
| 3 | Moderate | 35–63% chance of occurrence |
| 2 | Low | 10–34% chance of occurrence |
| 1 | Not likely | Less than 10% chance of occurrence |
| Risk Exposure Level | Score | Risk Exposure Description |
|---|---|---|
| Extreme | 0.81–1.0 | Economic: Budget deficit, cloud migration is suspended. Environmental: Unable to comply with green IS strategy and cost optimisation. Social: Incapable to monitor service performance from the supplier and managing change. Technological: Incompetent to handle IS incidents, to accomplish IS control objectives or to provide security for IS or for cloud migration. |
| High | 0.61–0.8 | Economic: Budget deficit, cloud migration is reschedule at a later date. Environmental: Able to comply with green IS strategy but incur additional cost. Social: Incapable of monitoring service performance from the supplier and managing change. Technological: Business continuity, crisis management plan and IS strategic plan are not established. |
| Medium | 0.41–0.6 | Economic: Limited budget estimate, cloud migration is possible. Environmental: Only some equipment is green IS compliant due to limited budget. Social: Capable of defining service level and managing change. Technological: Business continuity, crisis management plan and IS strategic plan are established and but not tested. |
| Low | 0.21–0.4 | Economic: Reasonable budget estimate, adequate resource for cloud migration. Environmental: Equipment is green IS compliant. Social: Capable of defining service level and managing change. Technology: Business continuity plan, crisis management plan and disaster recovery plan are available and tested. |
| Very Low | 0.0–0.2 | Economic: Moderate budget estimate, adequate resource for cloud migration. Environmental: Equipment is green IS compliant. Social: Capable of defining service level, provides adequate IS controls, storage and managing change. Technology: Business continuity plan, crisis management plan and disaster recovery plan are available, tested and sufficient. |
| Sustainable Dimensions | m-Values | Weight Factor (Impact ) | Probability Value | Risk Exposure | ||
|---|---|---|---|---|---|---|
| Mitigate | Inbetween | Not Mitigate | ||||
| Economic | ||||||
| R1 | 0.9259 | 0.07404 | 0 | 0.673 | 0.0741 | 0.0498693 |
| R2 | 0.6666 | 0.25 | 0 | 0.256 | 0.3334 | 0.053504 |
| R3 | 0.9795 | 0.0204 | 0 | 0.07 | 0.0205 | 0.001435 |
| Total 0.1366547 | ||||||
| Environment | ||||||
| R4 | 0.7222 | 0.2222 | 0.0555 | 0.6333 | 0.2778 | 0.1759307 |
| R5 | 0.8378 | 0.1351 | 0.027 | 0.2667 | 0.1622 | 0.0432587 |
| Total 0.2191895 | ||||||
| Social | ||||||
| R6 | 0.8974 | 0.0769 | 0.0256 | 0.2179 | 0.1026 | 0.0223565 |
| R7 | 0.8591 | 0.1126 | 0.0281 | 0.4676 | 0.1409 | 0.0658848 |
| R8 | 0.9523 | 0.0357 | 0.0119 | 0.3143 | 0.0477 | 0.0149921 |
| Total 0.1032335 | ||||||
| Technology | ||||||
| R9 | 0.9692 | 0.0307 | 0 | 0.2554 | 0.0308 | 0.0078663 |
| R10 | 0.875 | 0.1111 | 0.138 | 0.1129 | 0.125 | 0.0141125 |
| R11 | 0.918 | 0.0819 | 0 | 0.5861 | 0.082 | 0.0480602 |
| R12 | 0.922 | 0.0649 | 0.0129 | 0.454 | 0.078 | 0.355412 |
| Total 0.105451 | ||||||
| Overall 0.1411322 | ||||||
© 2017 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Abdul Rahman, A.A.L.; Islam, S.; Kalloniatis, C.; Gritzalis, S. A Risk Management Approach for a Sustainable Cloud Migration. J. Risk Financial Manag. 2017, 10, 20. https://doi.org/10.3390/jrfm10040020
Abdul Rahman AAL, Islam S, Kalloniatis C, Gritzalis S. A Risk Management Approach for a Sustainable Cloud Migration. Journal of Risk and Financial Management. 2017; 10(4):20. https://doi.org/10.3390/jrfm10040020
Chicago/Turabian StyleAbdul Rahman, Alifah Aida Lope, Shareeful Islam, Christos Kalloniatis, and Stefanos Gritzalis. 2017. "A Risk Management Approach for a Sustainable Cloud Migration" Journal of Risk and Financial Management 10, no. 4: 20. https://doi.org/10.3390/jrfm10040020
APA StyleAbdul Rahman, A. A. L., Islam, S., Kalloniatis, C., & Gritzalis, S. (2017). A Risk Management Approach for a Sustainable Cloud Migration. Journal of Risk and Financial Management, 10(4), 20. https://doi.org/10.3390/jrfm10040020







