A Risk Management Framework for Cloud Migration Decision Support
Abstract
:1. Introduction
2. Related Work
2.1. Risk Management Framework and Migration Decision Support in the Cloud
2.2. Risks in the Cloud
3. Risk Management Framework
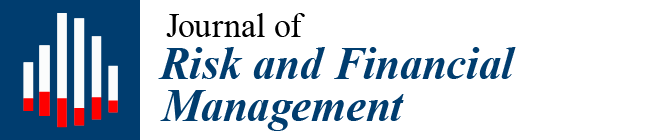
3.1. Conceptual View
3.2. Risk Management Process
Activity 1: Initialize Risk Management
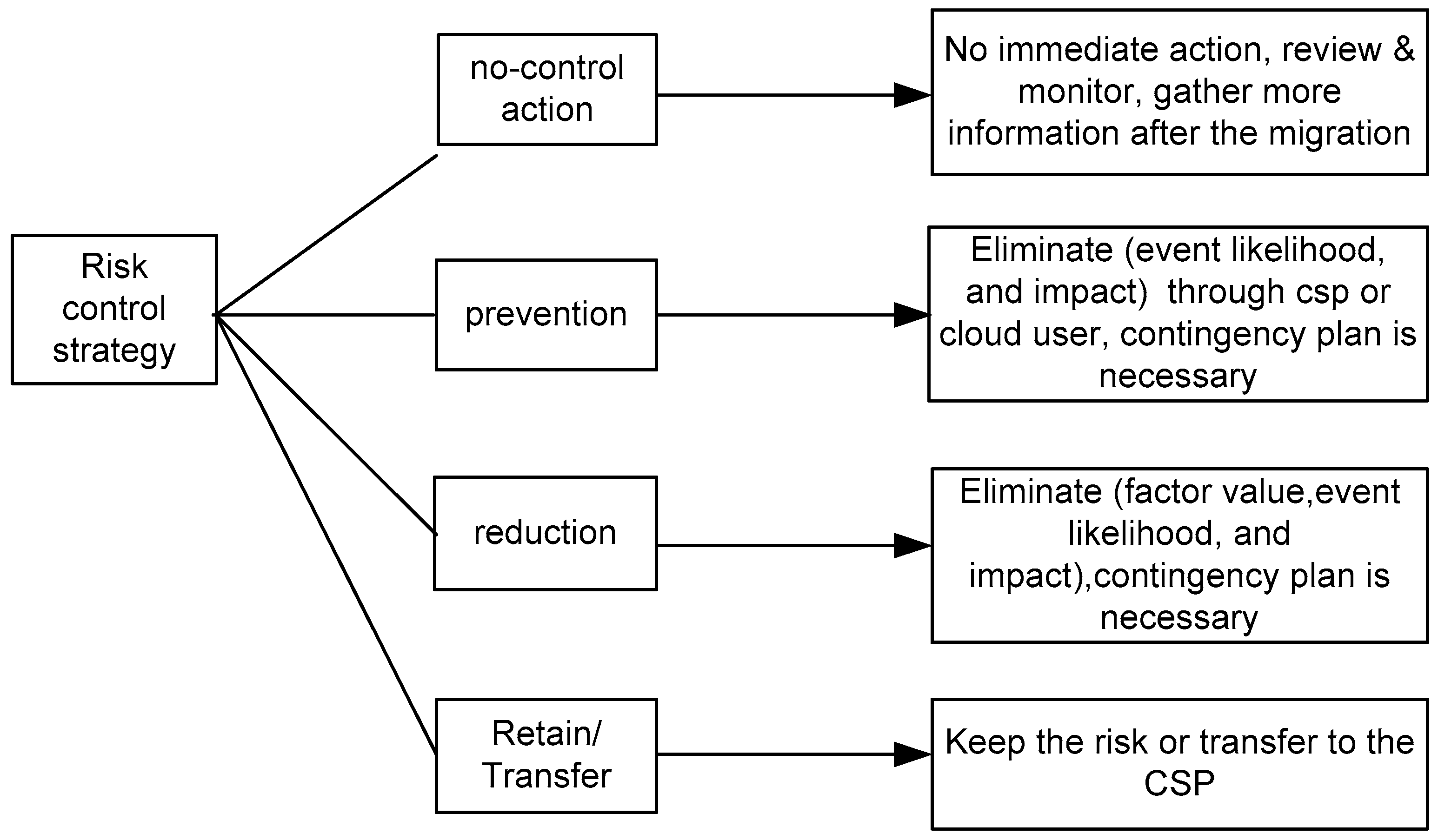
Task 1A: Define Migration Profile
- Business Value (BV): This goal includes the main business gain in terms of financial profit, maintenance benefits, service delivery, business growth—specifically in new markets—and competitive advantages due to cloud migration.
- Organization Function (OF): The organization function goal considers key operations for successfully running the business, including internal process improvement, customer services, human resources, collaboration with internal units and business partners, business continuity and disaster recovery, and efficient IT usage and IT availability.
- Confidentiality (C): This goal deals with not disclosing data to unauthorized users, including cloud users, CSP-internal users, and malicious attackers. The goal also includes secure deletion and transfer of data between authorized parties to prevent the data leakage.
- Integrity (I): Integrity refers to the trustworthiness of the migrated resources. In particular, the data migrated into the cloud must only be modifiable by authorized users.
- Availability (A): Availability refers to the migrated resources, such as data or applications, being accessible when needed and the cloud service being available as per the agreement.
- Transparency (T): Transparency refers to the dissemination of information about access to and usage of user data, security incidents and audit reports by the cloud service provider. It also considers real-time monitoring of virtual machines and SLAs. Transparency is critical for the mutual trust between the user and the CSP.
Task 1B: Plan Risk Management
Activity 2: Identify and Categorize Risks
Task 2A: Identify Risks
Task 2B: Categorize Risks
- Business risks: These risks directly obstruct the achieving of the user’s main business goals. Business risks reduce the financial benefits and brand value and incur financial loss for the overall business continuity.
- Organizational risks: Such risks mainly focus on issues relating to the user’s and cloud provider’s overall organizational operational context. For instance, a cloud user organization’s employee’s inadequate experience with cloud technology and maintenance difficulties could lead to a severe business disruption while migrating and operating in the cloud. It is hard to predict and control human factors relating to human error and behaviors that pose a risk in the cloud context.
- Technical risks: These risks include underlying technical issues such as the cloud platform being affected by malicious code, hypervisor-level attacks, data leakage due to the multi-tenancy architecture, system malfunctions, or unauthorized transmission, which are more probable in a cloud-based context. Security and privacy issues play a critical role for the technical risks. In particular, the loss of confidentiality, integrity and availability as well as lack of transparency would certainly disrupt the business mission.
Activity 3: Analyze and Control Risks
Task 3A: Assess Risks
Step 1: Relative Importance of Migration Goals
- CR: Consistency ratio
- CI: Consistency index
- RI: Random consistency index
- CM = Comparison matrix value
- BV = Business Value, OF = Organization Function, C = Confidentiality,
- I = Integrity, A = availability, T = Transparency
| BV | OF | C | I | A | T | ||
| Bv | CMi,j | - | - | - | - | CMi,6 | |
| OF | CMi+1,j | - | - | - | - | CMi+1,6 | |
| CMij= | C | CMi+2,j | - | - | - | - | CMi+2,6 |
| I | CMi+3,j | - | - | - | - | CMi+3,6 | |
| A | CMi+4,j | - | - | - | - | CMi+4,6 | |
| T | CM6,j | - | - | - | - | CM6,6 |
Step 2: Net Risk Calculation
- Rule 1: Risk impact depends on the affected migration goals. If a risk affects important migration goals, impact is certainly high.
- Rule 2: If the risk factors may be, at least partially, beyond the control of a user’s organization and mainly posed by the CSP, the overall risk impact can be higher.
- Rule 3: Individual judgment is always useful for net risk calculation. However, individual perception should be closely mapped with reality, otherwise we may overestimate or underestimate risk value.
- ri: Individual risk factor value
- ri1........rin: n influential risk factors of a risk Ri
- P(ri): Probability of a risk factor ri
- Probability scales = unlikely (less than 0.30), likely (0.30–0.59), certain/expected (above 0.60).
- I: Impact of overall risk Ri
- Impact scales = low (less than 0.30), medium (0.30–0.59), high (above 0.60)
- Ri: Value of a risk Ri
- Rnet: Net risk of Ri
- We: Relative weight of the affected migration goal [BV, OF, C, I, A, T] by Ri
Risk levels
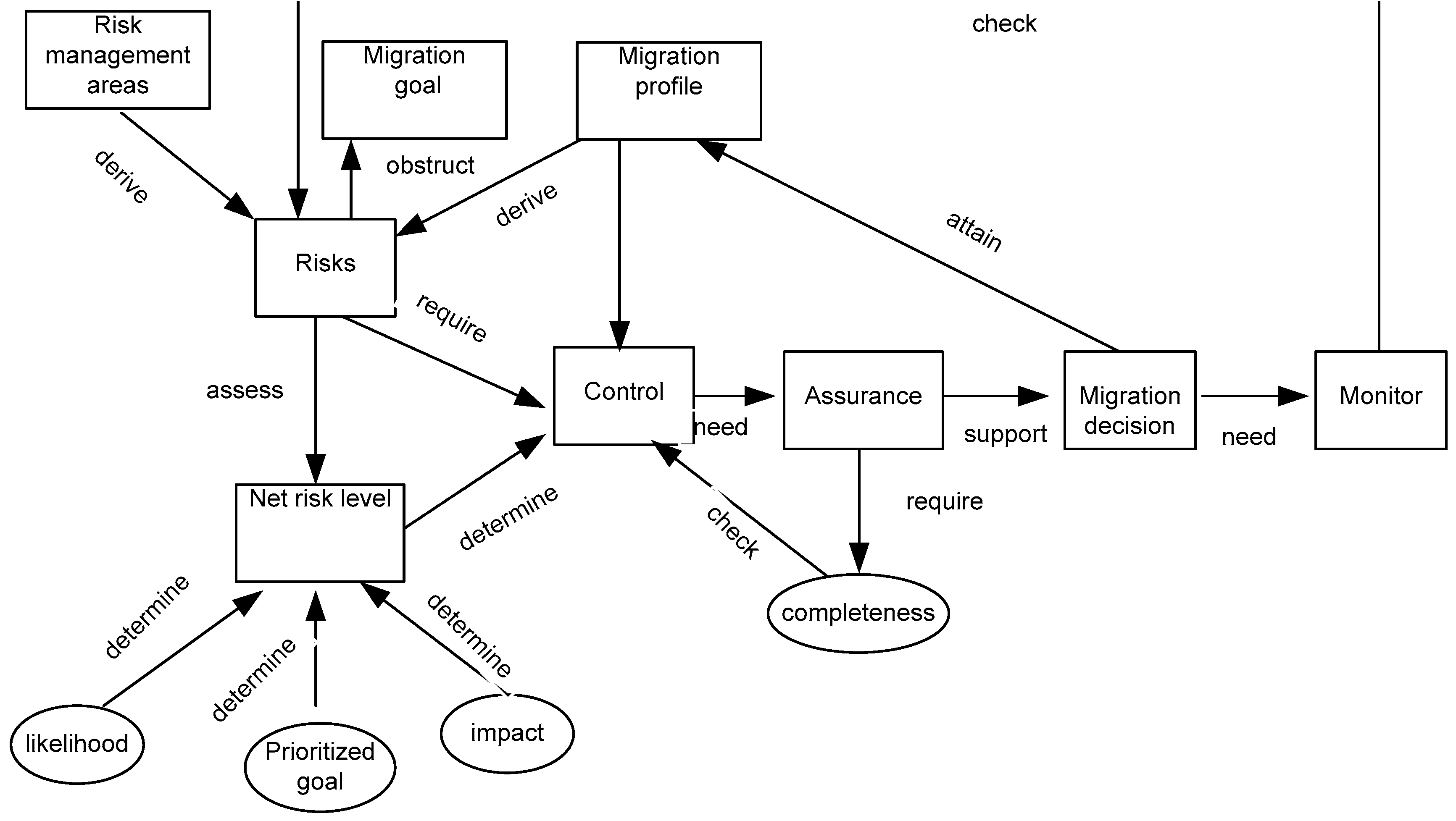
- Low risk (less than 0.30) implies that it is recommended to develop a corrective measure and contingency plan.
- Critical risk (between 0.30 and 0.59) implies the risk has an adverse affect on the organization and corrective actions are needed and a contingency plan should be developed if necessary. A plan should be developed for the execution of the control measure within a specific period of time.
- Highly critical risk (above 0.60) implies the identified control measures for the risk mitigation need to be implemented immediately within a short time frame with a plan. The risk level is highly critical if both the probability of the risk event and its impact are high or one is medium and another high.
Task 3B: Identify Potential Risk Control Measures
Activity 4: Migration Decision and Risk Monitoring
Task 4A: Assurance of Control Measures
- Level 1 No completion: There is zero or minimum evidence for the assurance of control measure attributes for managing the risks.
- Level 2 Partial completion: There is some evidence for the assurance of control measure attributes for managing the risks.
- Level 3 Full completion: There is adequate evidence for the assurance of control measure attributes for managing the risks.
Task 4B: Migration Decision
Task 4C: Monitor Risks in Operation
- Ri = the identified risks
- ri1 = risk factor
- Rnetm = monitored risk net value
- For each identified risk Ri to be monitored Rim
- Monitor the occurrence of related risk factors ri1,ri2,..........rin
- For each ri,
- P(ri) = no of occurrence/monitored time,
- If (Rnetm ≥ Rnet) then
- Revise the existing control strategy with immediate action
- If (Rnetm Rnet) then no immediate action is required
4. The Risk Management Tool
4.1. Application Design
4.2. User Interface
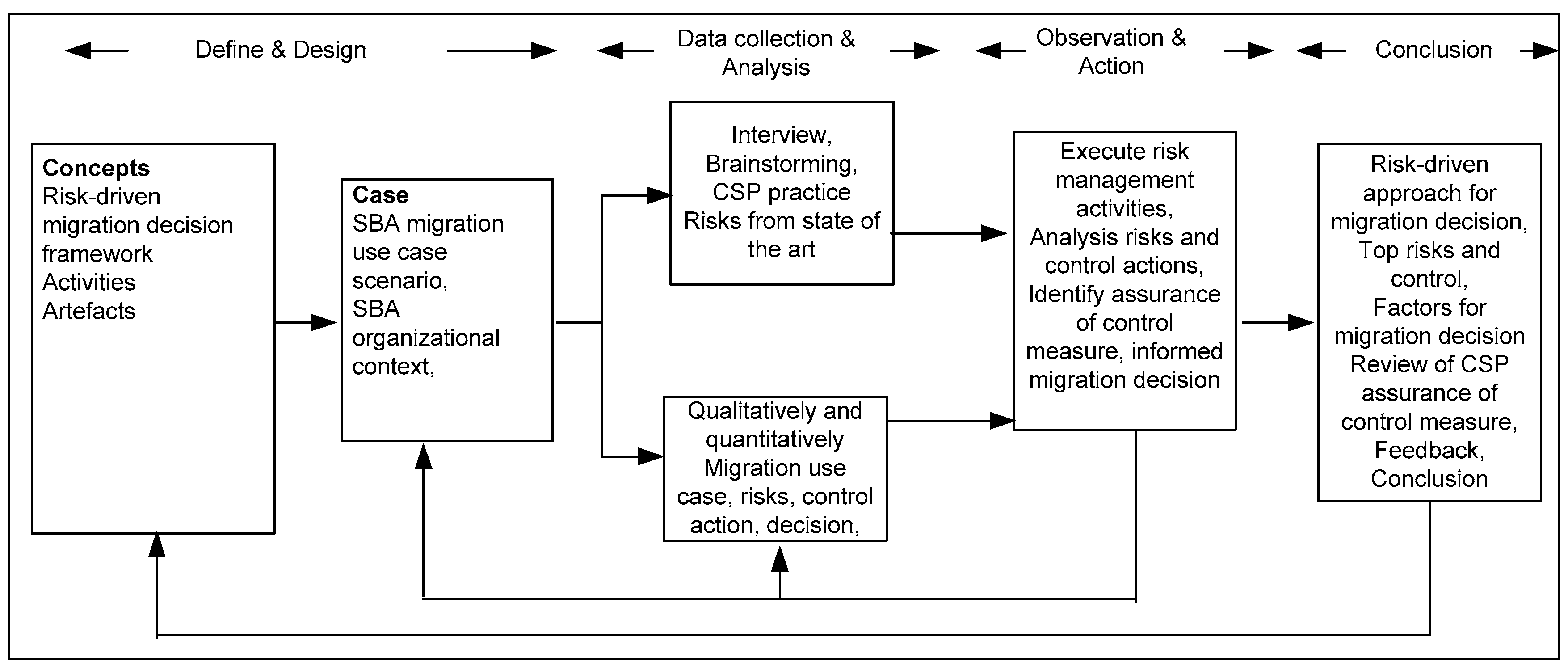
5. Evaluation
5.1. Study Design
Study Construct and Data Collection
- understand the usefulness of the risk management framework in supporting SBA in the migration decision;
- understand the risks associated with migrating the use-case scenario into the cloud;
- identify suitable CSPs that could address the risks and support the user in making the migration decision.
Data Collection and Analysis
Migration Use Case for the Study Context
Migration Use Case
5.2. Introduction of Risk Management Process
Activity 1: Initialize Risk Management
- There is no major amendment of applications involved in the migration profile;
- SBA staff has sound technical expertise; most have adequate security knowledge, and adequate in-house security controls are already implemented;
- Medium-sensitive organization data such as research data and research proposals are considered for the migration profile;
- Cost reduction, accessibility and secrecy of data are the most prioritized areas if the migration decision is taken.
Activity 2: Analyze and Control Risks
- Relative Weight of BV = = 0.32
- Relative Weight of OF = = 0.22
- Relative Weight of C = = 0.25
- Relative Weight of I = = 0.06
- Relative Weight of A = = 0.09
- Relative Weight of T = = 0.06
Activity 3: Identify and Categorize Risks
- Net Risk R1 (Leakage of Research Data) Calculation
- P(r1 = long-standing access by CSP-internal employee) = 0.8
- P(r2 = malicious attack by impersonating to misuse and modify service instance) = 0.7
- P(r3 = VM vulnerabilities) = 0.2
- P(r4 = misuse by SBA-internal user) = 0.1
- Impact of R1 = 0.8
- Affected migration goals = BV, OF, C, I, T
- r1 = 0.8 × 0.8 = 0.64
- r2 = 0.7 × 0.8 = 0.56
- r3 =.2 × 0.8 = 0.16
- r4 = 0.1 × 0.8 = 0.08
- R1 = (0.64 + 0.56 + 0.16 + 0.08) = (1.44) = 0.36
- Net risk R1 = 0.32 × 0.36 + 0.22 × 0.36 + 0.25 × 0.36 + 0.06 × 0.36 + 0.06 × 0.36 = 0.327
Identify Potential Risk Controls
- C1 (Data leakage prevention): encryption of data at rest and in transit, restricted standing access, monitor privileged data access; CSP
- C2 (Physical security): physical security of CSP’s data center; CSP
- C3 (Data loss prevention): data loss prevention mechanism; CSP
- C4 (Data transparency): appropriate dissemination of information about data access specifically by the CSP’s internal staff; CSP
- C5 (Stable CSP): cloud vendor should not go out of business; CSP
- C6 (Audit program and report): appropriate governance and audit management program, CSP audit report; CSP
- C7 (Security incident report): CSP security incident report; CSP
- C8 (Policy): access control with privileged access, disaster recovery and business continuity plan by CSP; CSP
- C9 (Customer service): real-time customer support service; CSP
- C10 (Penetration testing): SBA should perform penetration testing with the knowledge of the CSP; SBA
- C11 (Policy amendment): extend SBA’s existing access control, disaster recovery and business continuity to adjust to cloud-based dependencies; SBA
- C12 (Usage estimation): accurate usage estimation based on the existing and future need of SBA; SBA
- C13 (Usage monitor): tools to monitor usage; SBA
- C14 (Testing): necessary testing to confirm that the service, control process, and VM are functioning and protected from risks; SBA
Activity 4: Migration Decision and Risk Monitor
Assurance of Control Measures
Migration Decision
Risk Monitoring
6. Discussion
6.1. Applicability of the Framework
6.2. Comparison with Other Study Results
6.3. Limitations of the Framework
6.4. Study Validity
7. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Kalloniatis Christos, Haralambos Mouratidis, Manousakis Vassilisc, Shareeful Islam, Stefanos Gritzalis, and Evangelia Kavaklif. “Towards the design of secure and privacy-oriented Information Systems in the Cloud: Identifying the major concepts.” In Computer Standards & Interfaces. Amsterdam, Netherlands: Elsevier, 2014. [Google Scholar]
- Mouratidis Haralambos, Shareeful Islam, Christos Kalloniatis, and Stefanos Gritzalis. “A framework to support selection of cloud providers based on security and privacy requirements.” Journal of Systems and Software 86 (2013): 2276–93. [Google Scholar]
- Gruschka Nils, and Luigi Lo Iacono. “Vulnerable Cloud: SOAP Message Security Validation Revisited.” In Paper presented at the IEEE International Conference on Web Services, Los Angeles, CA, USA, 6–10 July 2009. [Google Scholar]
- Shareeful Islam, Haralambos Mouratidis, and Edgar Weippl. “A Goal-driven Risk Management Approach to Support Security and Privacy Analyzes of Cloud-based System.” In Security Engineering for Cloud Computing: Approaches and Tools. Hershey, PA, USA: IGI Global Publication, 2012. [Google Scholar]
- Kalloniatis Christos, Haralambos Mouratidis, and Shareeful Islam. “Evaluating Cloud Deployment Scenarios Based on Security and Privacy Requirements.” In Requirements Engineering Journal (REJ). Berlin, Germany: Springer-Verlag, 2013, vol. 18, pp. 299–319. [Google Scholar]
- Ristenpart Thomas, Eran Tromer, Hovav Shacham, and Stefan Savage. “Hey, you, get off of my cloud: Exploring information leakage in third-party compute clouds.” In Paper presented at the 16th ACM Conference on Computer and Communications Security, Chicago, IL, USA, 9–13 November 2009. [Google Scholar]
- Saripalli Prasad, and Ben Walters. “Quirc: A quantitative impact and risk assessment framework for cloud security.” In Paper presented at the IEEE 3rd International Conference on Cloud Computing, Miami, FL, USA, 5–10 July 2010. [Google Scholar]
- Samad Javeria, Seng W. Loke, and Karl Reed. “Quantitative Risk Analysis for Mobile Cloud Computing: A Preliminary Approach and a Health Application Case Study.” In Paper presented at the 12th IEEE International Conference on Trust, Security and Privacy in Computing and Communications (TrustCom), Melbourne, Australia, 16–18 July 2013. [Google Scholar]
- Xuan Zhang, Nattapong Wuwong, Hao Li, and Xuejie Zhang. “Information security risk management framework for the cloud computing environments.” In Paper presented at the 10th IEEE International Conference on Computer and Information Technology (CIT), Cork, Ireland, 29 June–1 July 2010. [Google Scholar]
- ISO 31000:2009 Risk Management Principles and Guidelines. Geneva, Switzerland: International Organization for Standardization (ISO)/International Electrotechnical Commission (IEC), 2009.
- J. Oriol Fitó, Mario Macías, and Jordi Guitart. “Toward Business-driven Risk Management for Cloud Computing.” In Paper presented at the IEEE international conference on Network and Service Management (CNSM), Niagara Falls, ON, Canada, 25–29 October 2012. [Google Scholar]
- J. Oriol Fitó, Mario Macías, Ferran Julia, and Jordi Guitart. “Business-Driven IT Management for Cloud Computing Providers.” In Paper presented at the IEEE 4th International Conference on Cloud Computing Technology and Science, Taipei, Taiwan, 3–6 December 2012. [Google Scholar]
- Sailesh Gadia. “Cloud Computing Risk Assessment a Case Study.” ISACA Journal 4 (2011): 2011. [Google Scholar]
- ENISA_Survey. “A SME Perspective on Cloud Computing Survey, The European Network and Information Security Agency. 2009.” Available online: https:/www.enisa.europa.eu/activities/risk-management/files/deliverables/cloud-computing-sme-survey (accessed on 24 March 2016).
- Umar Ismail, Shareeful Islam, Moussa Ouedraogo, and Edgar Weippl. “A Framework for Security Transparency in Cloud Computing.” Journal of Future Internet 8, 1 (2016). [Google Scholar] [CrossRef]
- Greg Stone, and Pierrre Noel. “Cloud Risk Decision Framework, Microsoft.” Available online: download.microsoft.com/documents/australia/.../smic1545_pdf_v7_pdf (accessed on 01 April 2016).
- Warren Chan, Eugene Leung, and Heidi Pili. Enterprise Risk Management for Cloud Computing. Available online: https://www.coso.org/Documents/Cloud-Computing-Thought-Paper.pdf, 2012 (accessed on 1 April 2016).
- Robert Lemos. “5 Lessons from Dark Side of Cloud Computing. CIO. 2009.” Available online: http://www.cio.com.au/article/314110/5_lessons_from_dark_side_clo ud_computing?eid=-156 (accessed on 26 February 2016).
- Catteddu Daniele. “Cloud15 Computing: Benefits, Risks and Recommendations for Information Security. 2009.” Available online: http//www.enisa.europa.eu/act/rm/files/deliverables/cloud.../at.../fullReport (accessed on 24 January 2016).
- Michael Gregg. “10 Security Concerns for Cloud Computing, Global Knowledge Training LLC. 2010.” Available online: http://viewer.media.bitpipe.com/1078177630_947/1268847180_5/WP_VI_10SecurityConcernsCloudComputing.pdf (accessed on 23 March 2016).
- Shareeful Islam, Stefan Fenz, Edgar Weippl, and Christos Kalloniatis. “Migration Goals and Risk Management in Cloud Computing: A Review of State of the Art and Survey Results on Practitioners.” International Journal of Secure Software Engineering (IJSSE) 7 (2016): 44–73. [Google Scholar] [CrossRef]
- Marianthi Theoharidou, Nick Papanikolaou, Siani Pearson, and Dimitris Gritzalis. “Privacy Risk, Security, Accountability in the Cloud.” In Paper presented at the IEEE 5th International Conference on Cloud Computing Technology and Science (CloudCom), Bristol, UK, 2–5 December 2013. [Google Scholar]
- Sabrina De Capitani di Vimercati, Sara Foresti, Sushil Jajodia, Stefano Paraboschi, and Pierangela Samarati. “Over-encryption: Management of access control evolution on outsourced data.” In Paper presented at the 33rd international conference on Very large databases, Vienna, Austria, 23–27 September 2007. [Google Scholar]
- Siani Pearson. “Taking account of privacy when designing cloud computing services.” In Paper presented at the ICSE Workshop on Software Engineering Challenges of Cloud Computing, Vancouver, BC, Canada, 23 May 2009. [Google Scholar]
- Amir Khosravani, Brian Nicholson, and Trevor Wood-Harper. “A case study analysis of risk, trust and control in cloud computing.” In Paper presented at the IEEE Science and Information Conference, London, UK, 7–9 October 2013. [Google Scholar]
- Ali Khajeh-Hosseini, David Greenwood, and Ian Sommerville. “Cloud Migration: A Case Study of Migrating an Enterprise IT System to IaaS.” In Paper presented at the IEEE 3rd International Conference on Cloud Computing, Miami, FL, USA, 5–10 July 2010. [Google Scholar]
- ISO 27001:2013 Information Technology—Security Techniques—Information Security Management Systems—Requirements. Geneva, Switzerland: International Organization for Standardization (ISO)/International Electrotechnical Commission (IEC), 2013.
- Thomas L. Saaty. “Decision making with the analytic hierarchy process.” International Journal of Services Sciences (IJSSCI) 1 (2008): 83–98. [Google Scholar] [CrossRef]
- Robert K. Yin. Case Study Research: Design and Methods. Oaks, CA, USA: SAGE Publications Inc., 2003. [Google Scholar]
- R.M. Davison, M.G. Martinsons, and N. Kock. “Principles of canonical action research.” Information Systems Journal 14 (2004): 65–86. [Google Scholar] [CrossRef]
- SBA. “Secure Business Austria. 2015.” Available online: http://www.sba-research.org/research/ (accessed on 1 April 2016).


| Importance Level | Definition |
|---|---|
| 1 | Equal importance of two compared goals |
| 3 | Moderate importance/one goal slightly favored over the other |
| 5 | Strong importance/one goal strongly favored over the other |
| 7 | Very importance/one goal very strongly favored over to the other |
| 9 | Extreme importance/one goal extremely favored over the other |
| 2,4,6,8 | Intermediate values |
| BV | OF | C | I | A | T | |
|---|---|---|---|---|---|---|
| BV | 1 | 3 | 1 | 5 | 3 | 5 |
| OF | 1 | 1 | 3 | 3 | 5 | |
| C | 1 | 1 | 1 | 3 | 3 | 3 |
| I | 1 | 1 | ||||
| A | 3 | 1 | 1 | |||
| T | 1 | 1 | 1 | |||
| Sum | 3.06 | 5.9 | 4 | 16 | 11.3 | 16 |
| Risk Factors | Risk | Category | Affected Goals | Net Risk |
|---|---|---|---|---|
| Long-standing access by CSP-internal employee, malicious attack by impersonating to misuse and modify service instance, VM vulnerabilities, misuse by SBA-internal users | R1 = Leakage of research data (research output/research proposals) | Organization, Technical | BV, OF, C, I,T | 0.33 (Critical risk) |
| Inaccurate usage estimation, uncertainty of cloud billing due to price change, poor SBA reputation due to cloud migration | R2 = Financial loss | Business | BV,OF | 0.32 (Critical risk) |
| CSP instability and lack of customer support, unavailability of data, lack of disaster recovery and business continuity plan by SBA/CSP, inconsistencies between SBA and CSP policies | R3 = Interruption of organizational functionalities | Organization | BV,OF,A,T | 0.60 (Highly critical risk) |
| Lack of audit support by CSP, poor transparency of SBA data access, unclear SBA policies for controlling data in the CSP infrastructure, attacker gains control over the SBA’s service instance | R4 = Loss of control /CSP dependency for the business continuity | Organization | BV,OF,C,I,A,T | 0.287 (Low risk) |
| Poor flexibility of data access, resource exhaustion, availability reduction. | R5 = Data unavailability | Organization,Technical | BV,OF,A | 0.30 (Critical risk) |
| Control Measure | CSP A | CSP B |
|---|---|---|
| C1 | Data encryption at rest and in transit using BitLocker and SSL/TLS encryption; CSP partner could access the data only by obtaining consent from the user; Admin access is strictly controlled Standing access is strictly checked before authentication. | Users have complete control of the instance and virtual networking environment; Encrypted IPsec VPN connectivity besides HTTPs using secure socket layer through API end points; Protection against traditional network security issues such as DDoS, MITM, spoofing; Encrypted data storage using Advanced Encryption Standard (AES) 256, a secure symmetric-key encryption standard using 256-bit encryption keys. There are several security flaws relating to data leakage identified by different research |
| C2 | Physical access control is in place but no details available | Physical access control is strictly implemented at the perimeter; security staff utilizing video surveillance, intrusion detection systems, and other electronic means; Authorized staff must pass two-factor authentication a minimum of two times to access data center floors. |
| C3 | DLP prevention features are included while users are sending sensitive data; Data encryption at rest and in transit using BitLocker and SSL/TLS encryption; CSP partner could access the data only by obtaining consent from the user; Admin access is strictly controlled; Isolation between tenants; But no clear evidences on what technologies are really used for leakage prevention. | Users have complete control of the instance and virtual networking environment; Encrypted IPsec VPN connectivity besides HTTPs using secure socket layer through API end points; Protection against traditional network security issues such as DDoS, MITM, spoofing; Encrypted data storage using Advanced Encryption Standard (AES) 256, a secure symmetric-key encryption standard using 256-bit encryption keys. |
| C4 | Discloses the location of data and who is accessing the data | AWS audit trial provides log of user activities |
| C5 | CSP B is a reputable institution | CSP A is a reputable institution |
| C6 | Third-party audit is performed to comply with ISO27001 certification, NIST 800-53, HIPAA BAA and SSAE16 SOC1 Type II | CSP A compliance program provides evidence of robust security and complies with ISO 27001 certification, SOC 1/SSAE 16/ISAE 3402 (formerly SAS 70 Type II), PCI DSS Level 1, FIPS 140-2; Users can also deploy solutions that comply with HIPAA or Cloud Security Alliance (CSA) |
| C7 | No evidence | No evidence but CSP B claims that it will notify publically if applicable |
| C8 | Strong access control using RBAC and lockbox and physical security, several back up of users’ data in different locations; No evidence of disaster recovery and business continuity plan | High-level availability of data in various global locations; industry-standard diagnostic procedures to drive resolution of incidents |
| C9 | Dedicated real-time customer support service | Dedicated real-time customer support service |
| C10 | No evidence | Permits users to perform penetration testing of its resource through an official procedure |
© 2017 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license ( http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Islam, S.; Fenz, S.; Weippl, E.; Mouratidis, H. A Risk Management Framework for Cloud Migration Decision Support. J. Risk Financial Manag. 2017, 10, 10. https://doi.org/10.3390/jrfm10020010
Islam S, Fenz S, Weippl E, Mouratidis H. A Risk Management Framework for Cloud Migration Decision Support. Journal of Risk and Financial Management. 2017; 10(2):10. https://doi.org/10.3390/jrfm10020010
Chicago/Turabian StyleIslam, Shareeful, Stefan Fenz, Edgar Weippl, and Haralambos Mouratidis. 2017. "A Risk Management Framework for Cloud Migration Decision Support" Journal of Risk and Financial Management 10, no. 2: 10. https://doi.org/10.3390/jrfm10020010
APA StyleIslam, S., Fenz, S., Weippl, E., & Mouratidis, H. (2017). A Risk Management Framework for Cloud Migration Decision Support. Journal of Risk and Financial Management, 10(2), 10. https://doi.org/10.3390/jrfm10020010