Transnational Child Sexual Abuse: Outcomes from a Roundtable Discussion
Abstract
1. Introduction
1.1. Offender Characteristics
1.2. Types of Networks
1.3. The Role of Cyberspace as an Enabler and Mode of Child Sexual Exploitation
1.4. National and International Policy—Current Response Frameworks
2. Method
2.1. Study Design
2.2. Participants/Discussants
2.3. Procedure and Materials
2.4. Data Analysis
3. Results
3.1. Roundtable Discussion
3.1.1. TCSA Definition
“I think there’s a more fundamental question to be asked—what do we mean by location and distribution channels? What is being distributed via what channel? (…) It can be online or offline, it can be abroad, or being streamed.”“There’s a burning question about motivation there, isn’t there? Because there will be people that will have a sort of prima facie motivation to go to a different country or location—regardless of whether its online/offline—to abuse a child. And so will therefore proactively seek out information that will allow them to do this. But then (…) you have situational offenders who may just be, for example, engaging with CSEM [Child Sexual Exploitation Material] in a network (…) where there’s some on-going conversations, and then all of a sudden, the opportunity presented itself.”
“[We need to consider] economic discrepancies or poverty in the countries where this happens and the cultural acceptability of the exploitation happening. It’s not just a question of demand—but children coming round hotels offering services … so that parameter of wealth, poverty and social inequality in these locations seemed to be a key factor in our discussions.”
3.1.2. Criminal Justice Issues
Management of Travelling Offenders
“If we’re concerned about UK offenders travelling abroad, there’s places like Kenya, Philippines, and older countries like Thailand and Cambodia that continue to be areas of concern.”
Investigative Methods
“One of the issues we raised was prevention. In the UK, we haven’t got a bottomless pit of resources of money. Let’s deal with our offenders going abroad and deal with them at source. They may be men, and they may be coming from here, but let’s deal with our own offenders first and see what works, and then spread that. Deal with the root cause.”
Enhancing Knowledge about the Offending
“We were recognising that CSEM is all over, but why do people travel to do it? There are various hypotheses—high-risk sex offenders who carefully monitor might choose to do that. Respected individuals who might not do it in this country would go abroad—a process of normalisation might reinforce that. We were looking at could we understand the pathways by which people ended up doing that. Part of that would be what would come out of investigations leading to convictions, but part of it might come from interviewing people about how their pathways developed. It could be that it’s through sharing exploitative material, networking—building up to it from that. Or it might be that there’s knowledge of certain places to go to—how do people get that knowledge? From an intervention viewpoint, those processes might have points that could be disrupted.”
Maintaining a Victim-Centric Stance
“It is very difficult when you’ve got different levels of victim support and training—what exactly are we looking to prevent? Because a lot of these problems on the ground are not exactly preventable.”
3.1.3. Geographical Issues
“We were saying corruption is a real problem—it leads on from poverty. The reverse is: the offenders are rich, they can buy people off. They can buy the family off, they can groom the family. They can pay police officers off. Families will take any amount of money for a child. So poverty, corruption and richness together is the perfect triangle of abuse, isn’t it?”
“Maybe it’s not just people travelling abroad … maybe they are more sexualised here? Is this a cultural phenomenon? Is [TCSA] actually a specific issue or is it just sexual abuse in general happening in different fora with new technology?”“We had a presentation at a hotel recently, there was a person from serious crime office talking about CSE [child sexual exploitation]—1.3 million children were abused in this country [UK]. (…) Why don’t we talk about this country? We have 10,000 refugee children missing in Europe. It’s much easier to talk about what’s happening in Vietnam—it makes us feel more comfortable, but that’s the way it is.”
“It depends on the level of sophistication of the offender you see. The newbies will go in social media—which are controlled by the police. We’re talking now about the dark social (not necessarily dark web), but those that can’t be encrypted such as Snapchat, where there’s no potential of looking. So if I’m an offender and I start a network with others who bring other people, then I can organise my own network.”
3.1.4. Tourism/Hospitality Issues
3.2. Priority Ranking
4. Discussion
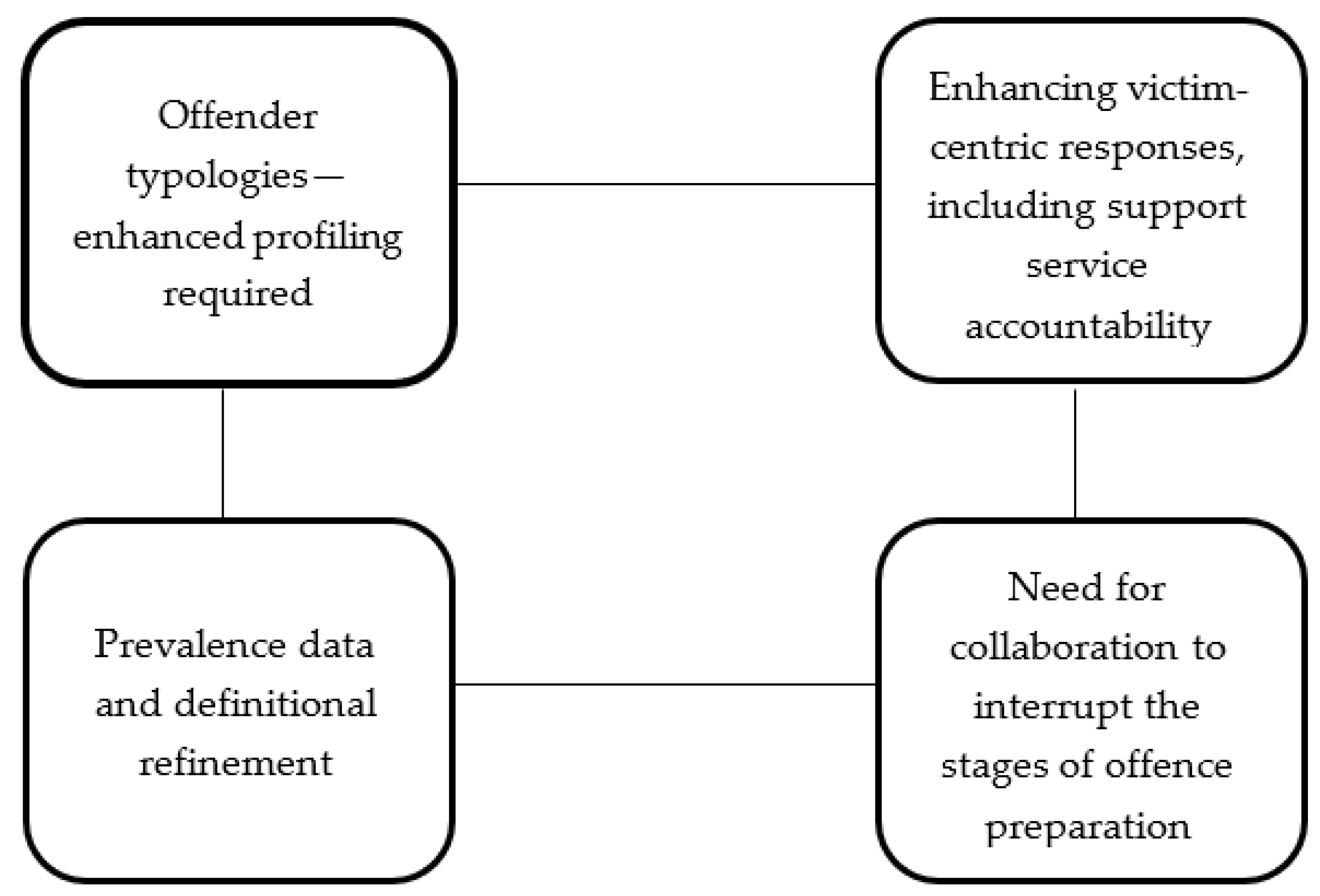
4.1. Key Theme 1: Offender Typologies
4.2. Key Theme 2: Victim-Centric Investigative Practice
4.3. Key Theme 3: Prevalence and Definitions
4.4. Key Theme 4: Collaboration
4.5. Limitations
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Harkins, L.; Dixon, L. Sexual offending in groups: An evaluation. Aggress. Violent Behav. 2010, 15, 87–99. [Google Scholar] [CrossRef]
- Thomas, T. International travel for purposes of child sexual exploitation: Policies and responses. Crime Prev. Community Saf. 2011, 13, 134–147. [Google Scholar] [CrossRef]
- Association of Chief Police Officers. Memorandum on the Policing and Crime Bill 2009: Part 2 Clauses 21–24. Parliament UK Website, 2009. Available online: https://publications.parliament.uk/pa/cm200809/cmpublic/policing/memos/ucm6802.htm (accessed on 5 December 2017).
- Child Exploitation and Online Protection Centre. Threat Assessment of Child Sexual Exploitation and Abuse. Norfolk Safeguarding Children Board Website, 2013. Available online: https://www.norfolklscb.org/wp-content/uploads/2015/03/CEOP_Threat-Assessment_CSE_JUN2013.pdf (accessed on 5 December 2017).
- Davies, H.; Beddoe, C.; McCourt, S.; McIntyre, J.; Geden, J.; Morgan, A. Civil Prevention Orders Sexual Offences Act 2003: ACPO Commissioned Review of the Existing Statutory Scheme and Recommendations for Reform. ECPAT UK Website, 2013. Available online: https://www.ecpat.org.uk/Handlers/Download.ashx?IDMF=cc782ae4-fd99-429c-84e4-43c1f1e62b5d (accessed on 5 December 2017).
- Blackburn, A.G.; Taylor, R.W.; Davis, J.E. Understanding the complexities of human trafficking and child sexual exploitation: The case of Southeast Asia. Women Crim. Justice 2010, 20, 105–126. [Google Scholar] [CrossRef]
- Davy, D. Understanding the motivations and activities of transnational advocacy networks against child sex trafficking in the Mekong Subregion: The value of cosmopolitan globalisation theory. Cosmopol. Civ. Soc. Interdiscip. J. 2013, 5, 39–68. [Google Scholar] [CrossRef]
- Panko, T.R.; George, B.P. Child sex tourism: Exploring the issues. Crim. Justice Stud. 2012, 25, 67–81. [Google Scholar] [CrossRef]
- Rafferty, Y. Child trafficking and commercial sexual exploitation: A review of promising prevention policies and programs. Am. J. Orthopsychiatry 2013, 83, 559–575. [Google Scholar] [CrossRef] [PubMed]
- Cockbain, E.; Brayley, H.; Laycock, G. Exploring internal child sex trafficking networks using social network analysis. Policy J. Policy Pract. 2011, 5, 144–157. [Google Scholar] [CrossRef]
- Johnson, B.C. Aftercare for survivors of human trafficking. Soc. Work Christ. 2012, 39, 370–389. [Google Scholar]
- Newman, W.J.; Holt, B.W.; Rabun, J.S.; Phillips, G.; Scott, C.L. Child sex tourism: Extending the borders of sexual offender legislation. Int. J. Law Psychiatry 2011, 34, 116–121. [Google Scholar] [CrossRef]
- Reid, J.A.; Jones, S. Exploited vulnerability: Legal and psychological perspectives on child sex trafficking victims. Vict. Offenders 2011, 16, 207–231. [Google Scholar] [CrossRef]
- Warria, A.; Nel, H.; Triegaardt, J. Challenges in identification of child victims of transnational trafficking. Soc. Work Action 2015, 27, 315–333. [Google Scholar] [CrossRef]
- Wolak, J.; Mitchell, K.; Finkelhor, D. Unwanted and wanted exposure to online pornography in a national sample of youth internet users. Paediatrics 2007, 119, 247–257. [Google Scholar] [CrossRef] [PubMed]
- Kloess, J.A.; Beech, A.R.; Harkins, L. Online child sexual exploitation: Prevalence, process and offender characteristics. Trauma Violence Abuse 2014, 15, 126–139. [Google Scholar] [CrossRef] [PubMed]
- Kloess, J.A.; Hamilton-Giachritsis, C.E.; Long, M.L.; Shipley, D.; Beech, A.R. Offense processes of online sexual grooming and abuse of children via Internet communication platforms. Sex. Abuse J. Res. Treat. 2017. [CrossRef] [PubMed]
- Mitchell, K.J.; Finkelhor, D.; Wolak, J.; Ybarra, M.L.; Turner, H. Youth internet victimization in a broader victimization context. J. Adolesc. Health 2011, 48, 128–134. [Google Scholar] [CrossRef] [PubMed]
- Martellozzo, E. Online Child Sexual Abuse: Grooming, Policing and Child Protection in a Multi-Media World, 1st ed.; Routledge: London, UK, 2012; ISBN 978-0415618212. [Google Scholar]
- Schulz, A.; Bergen, E.; Schuhmann, P.; Hoyer, J.; Santtila, P. Online sexual solicitation of minors: How often and between whom does it occur? J. Res. Crime Delinq. 2016, 53, 165–188. [Google Scholar] [CrossRef]
- Bergen, E.; Ahto, A.; Schulz, A.; Imhoff, R.; Antfolk, J.; Schuhmann, P.; Alanko, K.; Santtila, P.; Jern, P. Adult-adult and adult-child/adolescent online sexual interactions: An exploratory self-report study on the role of situational factors. J. Sex Res. 2015, 52, 1006–1016. [Google Scholar] [CrossRef]
- Bergen, E.; Davidson, J.; Schulz, A.; Schuhmann, P.; Johansson, A.; Santtila, P.; Jern, P. The effects of using identity deception and suggesting secrecy on the outcomes of adult-adult and adult-child or-adolescent online sexual interactions. Vict. Offenders 2014, 9, 276–298. [Google Scholar] [CrossRef]
- Davidson, J.; Gottschalk, P. Characteristics of the Internet for criminal child sexual abuse by online groomers. Crim. Justice Stud. 2011, 24, 23–36. [Google Scholar] [CrossRef]
- Webster, S.; Davidson, J.; Bifulco, A.; Gottschalk, P.; Caretti, V.; Pham, T.H.; Grove-Hills, J.; Turley, C.; Tompkins, C.N.E.; Ciulla, S.; et al. European Online Grooming Project—Final Report. NatCen Website, 2012. Available online: http://natcen.ac.uk/media/22514/european-online-grooming-projectfinalreport.pdf (accessed on 5 December 2017).
- Durkin, K.F.; Bryant, C.D. Propagandizing pederasty: A thematic analysis of the online exculpatory accounts of unrepentant pedophiles. Deviant Behav. Interdiscip. J. 1999, 20, 103–127. [Google Scholar] [CrossRef]
- Holt, T.J.; Blevins, K.R.; Burkert, N. Considering the Pedophile Subculture Online. Sex. Abuse J. Res. Treat. 2010, 22, 3–24. [Google Scholar] [CrossRef] [PubMed]
- O’Halloran, E.; Quayle, E. A content analysis of a ‘Boy Love’ support forum: Revisiting Durkin and Bryant. J. Sex. Aggress. 2010, 16, 71–85. [Google Scholar] [CrossRef]
- Azaola, E. The sexual exploitation of children in Mexico. Police Pract. Res. 2006, 7, 97–110. [Google Scholar] [CrossRef]
- McLain, N.M.; Garrity, S.E. Sex trafficking and the exploitation of adolescents. J. Obstet. Gynecol. Neonatal Nurs. 2011, 40, 243–252. [Google Scholar] [CrossRef]
- Briggs, P.; Simon, W.T.; Simonsen, S. An exploratory study of Internet-initiated sexual offences and the chat room sex offender: Has the Internet enabled a new typology of sex offender. Sex. Abuse J. Res. Treat. 2011, 23, 72–91. [Google Scholar] [CrossRef] [PubMed]
- Europol. Online Sexual Coercion and Extortion as a Form of Crime Affecting Children: Law Enforcement Perspective. Europol Website, 2017. Available online: https://www.europol.europa.eu/publications-documents/online-sexual-coercion-and-extortion-form-of-crime-affecting-children-law-enforcement-perspective (accessed on 5 December 2017).
- Quayle, E.; Taylor, M. Child pornography and the Internet: Perpetuating a cycle of abuse. Deviant Behav. 2002, 23, 331–361. [Google Scholar] [CrossRef]
- Malesky, L.A.; Ennis, L. Supportive distortions: Analysis of posts on a pedophile internet message board. J. Addict. Offender Couns. 2004, 24, 94–100. [Google Scholar] [CrossRef]
- Beech, A.R.; Elliot, I.A.; Birgden, A.; Findlater, D. The internet and child sexual offending: A criminological review. Aggress. Violent Behav. 2008, 13, 216–228. [Google Scholar] [CrossRef]
- Tate, T. Child Pornography: An Investigation, 1st ed.; Methuen Publishing: London, UK, 1990; ISBN 9780413615404. [Google Scholar]
- De Young, M. The indignant page: Techniques of neutralization in the publications of pedophile organisations. Child Abuse Negl. 1988, 12, 583–591. [Google Scholar] [CrossRef]
- La Fontaine, J.S. Defining organised sexual abuse. Child Abuse Rev. 1993, 2, 223–231. [Google Scholar] [CrossRef]
- Green, L. Analysing the sexual abuse of children by workers in residential care homes: Characteristics, dynamics and contributory factors. J. Sex. Aggress. 2001, 7, 5–25. [Google Scholar] [CrossRef]
- George, B.P.; Panko, T.R. Child sex tourism: Facilitating conditions, legal remedies, and other interventions. Vulnerable Child. Youth Stud. 2011, 6, 134–143. [Google Scholar] [CrossRef]
- Burgess, A.W. Child Pornography and Sex Rings, 1st ed.; Lexington Books: Toronto, CA, USA, 1984; ISBN 978-0669067415. [Google Scholar]
- Baron, R.S.; Kerr, N.L. Group Processes, Group Decision, Group Action, 2nd ed.; Open University Press: Berkshire, UK, 2003; ISBN 978-0335206971. [Google Scholar]
- ECPAT International. The Use of Information and Communication Technologies in Connection with Cases of Child-Sex Tourism in East and South East Asia. Business & Human Rights Resource Centre, 2010. Available online: https://business-humanrights.org/en/the-use-of-information-and-communication-technologies-in-connection-with-cases-of-child-sex-tourism-in-east-and-south-east-asia (accessed on 5 December 2017).
- Davidson, J.; Gottschalk, P. Internet Child Abuse: Current Research and Policy, 1st ed.; Routledge: London, UK, 2010; ISBN 978-0415559805. [Google Scholar]
- Whittle, H.; Hamilton-Giachritsis, C.E.; Beech, A.R.; Collings, G. A review of online grooming: Characteristics and concerns. Aggress. Violent Behav. 2013, 18, 62–70. [Google Scholar] [CrossRef]
- Quayle, E. Over the Internet, under the Radar: Online Child Sexual Abuse and Exploitation—A Brief. Centre for Youth & Criminal Justice Website, 2017. Available online: http://www.cycj.org.uk/wp-content/uploads/2017/02/Over-the-Internet-literature-review.pdf (accessed on 5 December 2017).
- National Institute for Health and Care Excellence. Harmful Sexual Behaviour among Children and Young People. NICE Website, 2016. Available online: https://www.nice.org.uk/guidance/ng55 (accessed on 5 December 2017).
- Livingstone, S.; Haddon, L.; Görzig, A.; Ólafsson, K. Risks and Safety on the Internet: The Perspective of European Children. Full Findings and Policy Implications from the EU Kids Online Survey of 9–16 Year Olds and Their Parents in 25 Countries. LSE Research Online Website, 2011. Available online: http://eprints.lse.ac.uk/33731/ (accessed on 5 December 2017).
- Kingston, S.; Thomas, T. The sexual risk order and the sexual harm prevention order: The first two years. Probat. J. 2018, 65, 77–88. [Google Scholar] [CrossRef]
- Scherrer, A.; van Ballegooij, W. Combating Sexual Abuse of Children: Directive 2011/93/EU. European Implementation Assessment. European Parliament Website, 2017. Available online: http://www.europarl.europa.eu/RegData/etudes/STUD/2017/598614/EPRS_STU%282017%29598614_EN.pdf (accessed on 5 December 2017).
- Montgomery, H. Buying innocence: Child-sex tourists in Thailand. Third World Q. 2008, 29, 903–917. [Google Scholar] [CrossRef]
- ECPAT UK. British Child Sex Offenders Abroad: Discussion Paper. ECPAT UK Website. 2012. Available online: http://new.ecpat.org.uk/sites/default/files/briefings/ecpat_uk_discussion_paper_-_british_child_sex_offenders_abroad_-_dec_2012.pdf (accessed on 5 December 2017).
- Berardi, G. Engaging the Travel and Tourism Sector in Protecting Children from Sexual Exploitation. Council of Europe Website, 2011. Available online: https://www.coe.int/t/dg3/children/1in5/Source/PublicationSexualViolence/Berardi.pdf (accessed on 5 December 2017).
- WePROTECT Global Alliance. Preventing and Tackling Child Sexual Exploitation and Abuse (CSEA): A Model National Response. WePROTECT Global Alliance Website, 2016. Available online: http://www.weprotect.org/the-model-national-response/ (accessed on 5 December 2017).
- Hawke, A.; Raphael, A. Offenders on the Move: Global Study on Sexual Exploitation of Children in Travel and Tourism 2016. ECPAT UK Website, 2016. Available online: https://www.ecpat.org.uk/Handlers/Download.ashx?IDMF=2ead9526-6b4f-402a-aa23-821c0274ddfe (accessed on 5 December 2017).
- McCartan, K.F.; Merdian, H.L.; Perkins, D.E.; Kettleborough, D. Ethics and issues of secondary prevention efforts in child sexual abuse. Int. J. Offender Therapy Comp. Criminol. 2018, 62, 2548–2566. [Google Scholar] [CrossRef] [PubMed]
- Robson, C.; McCartan, K. Real World Research, 1st ed.; John Wiley & Sons: Chichester, UK, 2016; ISBN 978-1-118-74523-6. [Google Scholar]
- Braun, V.; Clarke, V. Using thematic analysis in psychology. Qual. Res. Psychol. 2006, 3, 77–101. [Google Scholar] [CrossRef]
- Guttentag, D. Airbnb: Disruptive innovation and rise of an informal tourism accommodation sector. Curr. Issues Tour. 2013, 18, 1192–1217. [Google Scholar] [CrossRef]
- ECPAT UK. Trafficked Children and Missing—Briefing Sheet. ECPAT UK Website, 2017. Available online: https://www.ecpat.org.uk/Handlers/Download.ashx?IDMF=4890c963-8292-4c16-bedd-03ae81fcf51a (accessed on 5 December 2017).
- World Congress: Child Dignity in the Digital World. The Declaration of Rome. The Catholic Church in England and Wales Website, 2017. Available online: http://www.catholicnews.org.uk/content/download/75195/548271/file/declaration-child-dignity-congress-2017.pdf (accessed on 5 December 2017).
- Livingstone, S.; Hasebrink, U.; Görzig, A. Towards a General Model of Determinants of Risk and Safety. LSE Research Online Website, 2012. Available online: http://eprints.lse.ac.uk/55467/ (accessed on 5 December 2017).
- Seto, M.C. Internet Sex Offenders, 1st ed.; American Psychological Association: Washington, DC, USA, 2013; ISBN 9781433843641. [Google Scholar]
- Smallbone, S.; Rayment-McHugh, S. Preventing youth sexual violence and abuse: Problems and solutions in the Australian context. Aust. Psychol. 2013, 48, 3–13. [Google Scholar] [CrossRef]
| Theme | Research Question | Priority Ranking |
|---|---|---|
| Offending Behaviour | How do offenders know to go to certain locations/distribution channels? | 7 |
| Victim Safeguarding | What support is available to children/victims in affected countries (e.g., safe housing, psychological support, compensation)? | 6 |
| Victim Safeguarding | In cases of compensation, how can we ensure there is no meta-abuse of the victim, and how can policy ensure such accountability? | 5 |
| Victim Safeguarding | In some countries, victims of child sexual abuse may be seen as criminally liable (differences in legislation between countries); issue of victim blaming/stigma surrounding victimisation, and power | 5 |
| Offending Behaviour | What types of transnational child sexual abuse exists? | 5 |
| Offending Behaviour | What are the profiles of perpetrators in-country vs. foreign visitors (travelling sex offenders)? How do live-streaming offences fit in? | 5 |
| Culturally-Sensitive Responding | Western way of thinking in a non-Western problem—how can we think/act globally? | 4 |
| Offending Behaviour | What is the impact of online child sexual abuse, networking, and travelling on contact sex offending? | 4 |
| Victim Safeguarding | Can you do research with the child victim? What are the consequences to the child? What are their perceptions of the help provided? | 3 |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Merdian, H.L.; Perkins, D.E.; Webster, S.D.; McCashin, D. Transnational Child Sexual Abuse: Outcomes from a Roundtable Discussion. Int. J. Environ. Res. Public Health 2019, 16, 243. https://doi.org/10.3390/ijerph16020243
Merdian HL, Perkins DE, Webster SD, McCashin D. Transnational Child Sexual Abuse: Outcomes from a Roundtable Discussion. International Journal of Environmental Research and Public Health. 2019; 16(2):243. https://doi.org/10.3390/ijerph16020243
Chicago/Turabian StyleMerdian, Hannah L., Derek E. Perkins, Stephen D. Webster, and Darragh McCashin. 2019. "Transnational Child Sexual Abuse: Outcomes from a Roundtable Discussion" International Journal of Environmental Research and Public Health 16, no. 2: 243. https://doi.org/10.3390/ijerph16020243
APA StyleMerdian, H. L., Perkins, D. E., Webster, S. D., & McCashin, D. (2019). Transnational Child Sexual Abuse: Outcomes from a Roundtable Discussion. International Journal of Environmental Research and Public Health, 16(2), 243. https://doi.org/10.3390/ijerph16020243





