A Secure IoT-Based Irrigation System for Precision Agriculture Using the Expeditious Cipher
Abstract
1. Introduction
- The main contribution of this article is the integration of a lightweight cryptography layer to the IoT ecosystem for smart agriculture that meets the requirements of constrained devices used in smart agriculture in general and specifically, in our proposed IoT-based irrigation system.
- The article investigates the deployment of a lightweight encryption protocol (Expeditious Cipher (X-cipher)) to create a secure channel between the sensing layer and the broker in the MQTT protocol as well as a secure channel between the broker and its subscribers in smart irrigation systems (our case study).
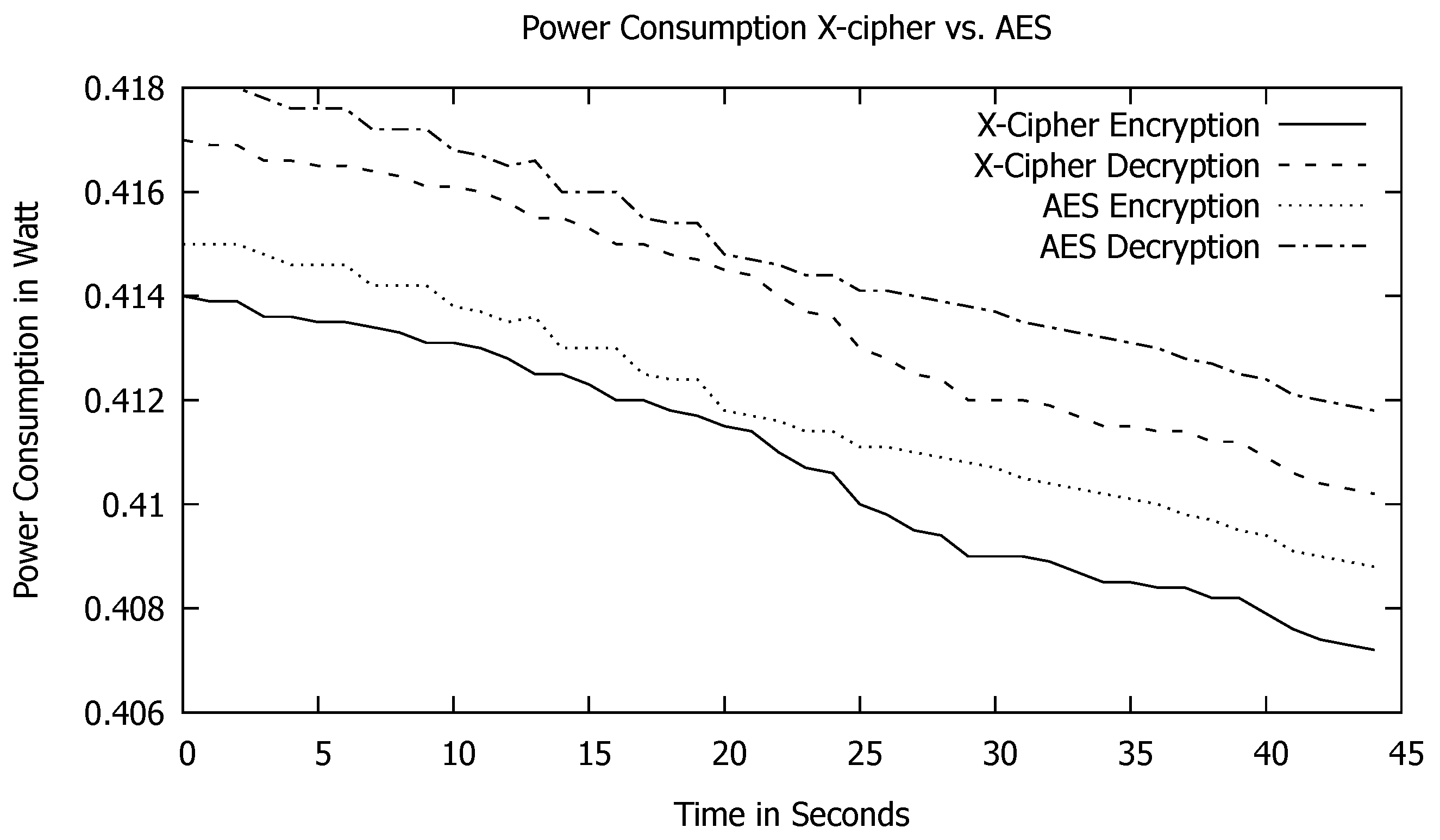
- The proposed model is evaluated through simulation to validate the lightweight property of the chosen encryption protocol in terms of power consumption, execution time, and memory usage. Moreover, a performance comparison is carried out between the Expeditious Cipher (X-cipher), AES, and PRESENT cipher (lightweight standard protocol) in terms of power consumption, execution time, memory usage, and average throughput.
- The security requirements of IoT-based agriculture systems and the potential attacks against them are discussed.
- A state-of-the-art lightweight security architectures proposed for securing MQTT protocol is reviewed after highlighting the concept of lightweight cryptography.
2. Materials and Methods
2.1. MQTT Security Challenges and Solutions
2.2. Proposed IoT System Architecture
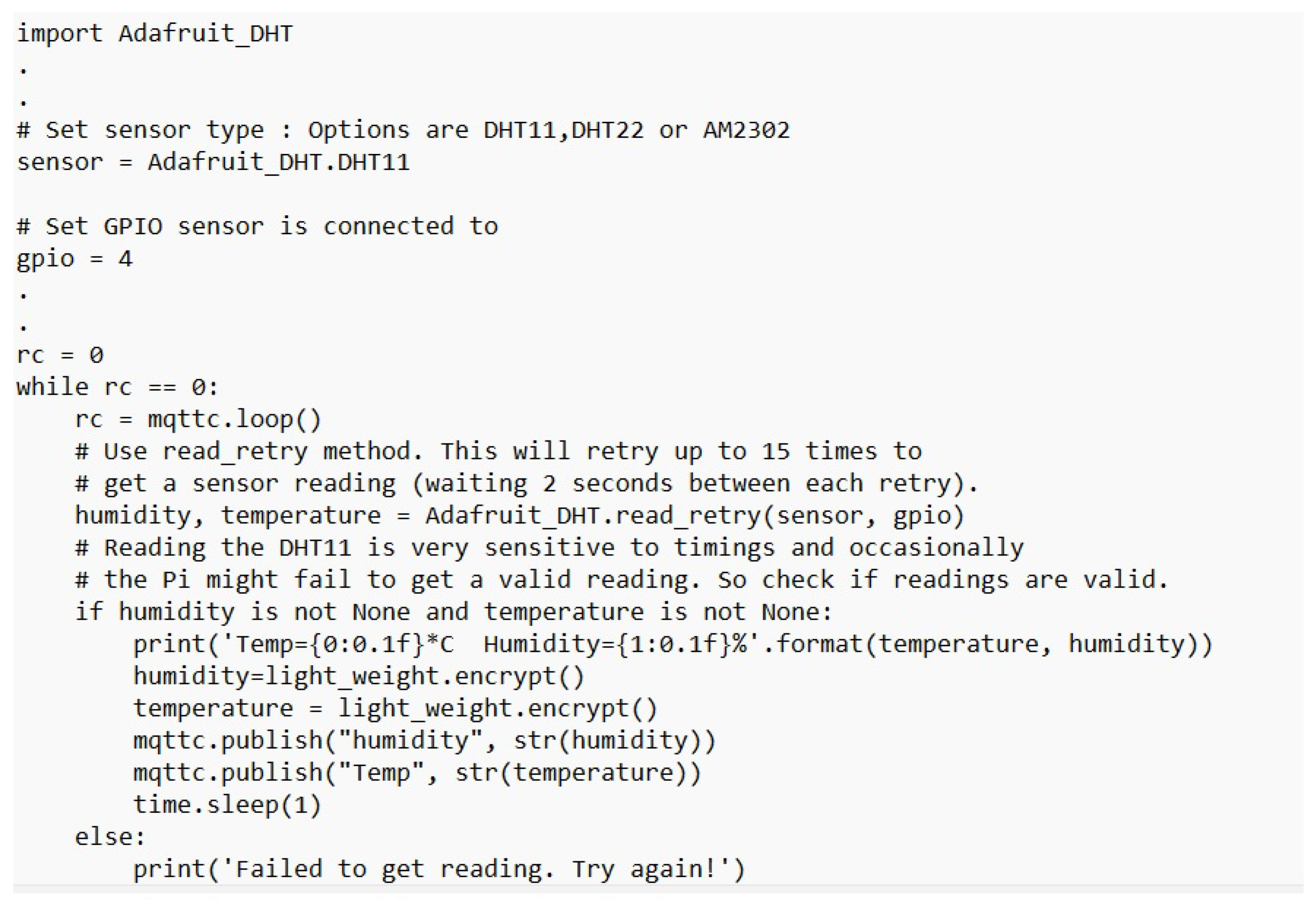
2.2.1. The Sensing Layer
2.2.2. Lightweight Cryptography Layer
2.2.3. Communication Layer
3. Results
3.1. Simulation Scenario
3.2. Comparison with Related Work
4. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Abbreviations
| AEAD | Authenticated Encryption with Associated Data |
| AES | Advanced Encryption System |
| AI | Artificial Intelligence |
| ANNs | Artificial Neural Networks |
| DA | Data Analytics |
| DOS | Denial Of Service |
| DODAG | Destination-Oriented Directed Acyclic Graph |
| DOS | Denial Of Service |
| ECDHE | Elliptic Curve Diffie Hellman Ephemeral |
| FFNN | Feed-Forward Neural Network |
| GSM | Global System for Mobile Communications |
| IoT | Internet of Things |
| IETF | Internet Engineering Task Force |
| PSK | Pre-Shared Key |
| LPWA | Low Power Wide Area |
| M2M | Machine to Machine |
| MITM | Man-In-The-Middle |
| MQTT | Message Queue Telemetry Transport |
| MQTT-SN | MQTT for Sensor Network |
| NFC | Near-Field Communications |
| NIST | National Institute of Standards and Technology |
| OASIS | Organization for the Advancement of Structured Information Standards |
| OF | Objective Function |
| RF | Radio Frequency |
| RFID | Radio Frequency Identification |
| RPL | Routing Protocol for Low-Power and Lossy Networks |
| SDN | Software-Defined Networking |
| SSL | Secure Socket Layer |
| TLS | Transport Layer Security |
| UN | United Nations |
| WSNs | Wireless Sensor Networks |
References
- Yang, X.; Shu, L.; Chen, J.; Ferrag, M.A.; Wu, J.; Nurellari, E.; Huang, K. A Survey on Smart Agriculture: Development Modes, Technologies, and Security and Privacy Challenges. IEEE/CAA J. Autom. Sin. 2021, 8, 273–302. [Google Scholar] [CrossRef]
- Elijah, O.; Rahman, T.A.; Orikumhi, I.; Leow, C.Y.; Hindia, M.N. An Overview of Internet of Things (IoT) and Data Analytics in Agriculture: Benefits and Challenges. IEEE Internet Things J. 2018, 5, 3758–3773. [Google Scholar] [CrossRef]
- Quy, V.K.; Hau, N.V.; Anh, D.V.; Quy, N.M.; Ban, N.T.; Lanza, S.; Randazzo, G.; Muzirafuti, A. IoT-Enabled Smart Agriculture: Architecture, Applications, and Challenges. Appl. Sci. 2022, 12, 3396. [Google Scholar] [CrossRef]
- Raza, U.; Kulkarni, P.; Sooriyabandara, M. Low Power Wide Area Networks: An Overview. IEEE Commun. Surv. Tutor. 2017, 19, 855–873. [Google Scholar] [CrossRef]
- Winter, T.; Thubert, P.; Brandt, A.; Hui, J.; Kelsey, R.; Levis, P.; Pister, K.; Struik, R.; Vasseur, J.; Alexander, R. Rfc6550: Rpl. Internet Engineering Task Force (IETF), Request for Comments: 6550. 2012, pp. 1–157. Available online: https://www.rfc-editor.org/rfc/pdfrfc/rfc6550.txt.pdf (accessed on 30 December 2022).
- Zier, A.; Abouaissa, A.; Lorenz, P. E-RPL: A Routing Protocol for IoT Networks. In Proceedings of the 2018 IEEE Global Communications Conference, GLOBECOM 2018—Proceedings, Abu Dhabi, United Arab Emirates, 9–13 December 2018. [Google Scholar] [CrossRef]
- Marjani, M.; Nasaruddin, F.; Gani, A.; Karim, A.; Hashem, I.A.T.; Siddiqa, A.; Yaqoob, I. Big IoT Data Analytics: Architecture, Opportunities, and Open Research Challenges. IEEE Access 2017, 5, 5247–5261. [Google Scholar] [CrossRef]
- Farooq, M.S.; Riaz, S.; Abid, A.; Abid, K.; Naeem, M.A. A Survey on the Role of IoT in Agriculture for the Implementation of Smart Farming. IEEE Access 2019, 7, 156237–156271. [Google Scholar] [CrossRef]
- Chang, Y.C.; Huang, T.W.; Huang, N.F. A Machine Learning Based Smart Irrigation System with LoRa P2P Networks. In Proceedings of the 2019 20th Asia-Pacific Network Operations and Management Symposium: Management in a Cyber-Physical World, APNOMS 2019, Matsue, Japan, 18–20 September 2019; pp. 31–34. [Google Scholar] [CrossRef]
- Boursianis, A.D.; Papadopoulou, M.S.; Gotsis, A.; Wan, S.; Sarigiannidis, P.; Nikolaidis, S.; Goudos, S.K. Smart Irrigation System for Precision Agriculture—The AREThOU5A IoT Platform. IEEE Sens. J. 2021, 21, 17539–17547. [Google Scholar] [CrossRef]
- Kashyap, P.K.; Kumar, S.; Jaiswal, A.; Prasad, M.; Gandomi, A.H. Towards Precision Agriculture: IoT-Enabled Intelligent Irrigation Systems Using Deep Learning Neural Network. IEEE Sens. J. 2021, 21, 17479–17491. [Google Scholar] [CrossRef]
- Hassan, N.; Hasib Cheragee, S.; Ahammed, S.; Touhidul Islam, A.Z. Sensor based Smart Irrigation System with Monitoring and Controlling using Internet of Things. Int. J. Ambient Syst. Appl. 2021, 9, 17–26. [Google Scholar] [CrossRef]
- Samawi, V.W. Smcsis: An iot based secure multi-crop irrigation system for smart farming. Int. J. Innov. Comput. Inf. Control 2021, 17, 1225–1241. [Google Scholar] [CrossRef]
- Singh, D.K.; Sobti, R.; Kumar Malik, P.; Shrestha, S.; Singh, P.K.; Ghafoor, K.Z. IoT-Driven Model for Weather and Soil Conditions Based on Precision Irrigation Using Machine Learning. Secur. Commun. Netw. 2022, 2022, 7283975. [Google Scholar] [CrossRef]
- Prasanna Lakshmi, G.S.; Asha, P.N.; Sandhya, G.; Vivek Sharma, S.; Shilpashree, S.; Subramanya, S.G. An intelligent IOT sensor coupled precision irrigation model for agriculture. Meas. Sens. 2023, 25, 100608. [Google Scholar] [CrossRef]
- Yazdinejad, A.; Zolfaghari, B.; Azmoodeh, A.; Dehghantanha, A.; Karimipour, H.; Fraser, E.; Green, A.G.; Russell, C.; Duncan, E. A review on security of smart farming and precision agriculture: Security aspects, attacks, threats and countermeasures. Appl. Sci. 2021, 11, 7518. [Google Scholar] [CrossRef]
- Basharat, A.; Mohamad, M.M.B. Security Challenges and Solutions for Internet of Things based Smart Agriculture: A Review. In Proceedings of the 4th International Conference on Smart Sensors and Application: Digitalization for Societal Well-Being, ICSSA 2022, Kuala Lumpur, Indonesia, 26–28 July 2022; pp. 102–107. [Google Scholar] [CrossRef]
- Grgic, K.; Pejkovic, A.; Zrnic, M.; Spisic, J. An Overview of Security Aspects of IoT Communication Technologies for Smart Agriculture. In Proceedings of the 16th International Conference on Telecommunications, ConTEL 2021, Zagreb, Croatia, 30 June–2 July 2021; pp. 146–151. [Google Scholar] [CrossRef]
- Butun, I.; Österberg, P.; Song, H. Security of the Internet of Things: Vulnerabilities, Attacks, and Countermeasures. IEEE Commun. Surv. Tutor. 2020, 22, 616–644. [Google Scholar] [CrossRef]
- Sadio, O.; Ngom, I.; Lishou, C. Lightweight Security Scheme for MQTT/MQTT-SN Protocol. In Proceedings of the 2019 6th International Conference on Internet of Things: Systems, Management and Security, IOTSMS 2019, Granada, Spain, 22–25 October 2019; pp. 119–123. [Google Scholar] [CrossRef]
- Hameed, S.; Khan, F.I.; Hameed, B. Understanding Security Requirements and Challenges in Internet of Things (IoT): A Review. J. Comput. Netw. Commun. 2019, 2019, 9629381. [Google Scholar] [CrossRef]
- Buchanan, W.J.; Li, S.; Asif, R. Lightweight cryptography methods. J. Cyber Secur. Technol. 2017, 1, 187–201. [Google Scholar] [CrossRef]
- Wu, X.W.; Yang, E.H.; Wang, J. Lightweight security protocols for the Internet of Things. In Proceedings of the 2017 IEEE 28th Annual International Symposium on Personal, Indoor, and Mobile Radio Communications (PIMRC), Montreal, QC, Canada, 8–13 October 2018; pp. 1–7. [Google Scholar] [CrossRef]
- Lara-Nino, C.A.; Morales-Sandoval, M.; Diaz-Perez, A. An evaluation of AES and present ciphers for lightweight cryptography on smartphones. In Proceedings of the 2016 International Conference on Electronics, Communications and Computers, CONIELECOMP 2016, Cholula, Mexico, 24–26 February 2016; pp. 87–93. [Google Scholar] [CrossRef]
- Mishra, B.; Kertesz, A. The use of MQTT in M2M and IoT systems: A survey. IEEE Access 2020, 8, 201071–201086. [Google Scholar] [CrossRef]
- Park, C.S.; Nam, H.M. Security Architecture and Protocols for Secure MQTT-SN. IEEE Access 2020, 8, 226422–226436. [Google Scholar] [CrossRef]
- Hintaw, A.J.; Manickam, S.; Karuppayah, S.; Aboalmaaly, M.F. A brief review on MQTT’s security issues within the internet of things (IoT). J. Commun. 2019, 14, 463–469. [Google Scholar] [CrossRef]
- Chen, F.; Huo, Y.; Zhu, J.; Fan, D. A Review on the Study on MQTT Security Challenge. In Proceedings of the 2020 IEEE International Conference on Smart Cloud (SmartCloud), Washington, DC, USA, 6–8 November 2020; pp. 128–133. [Google Scholar] [CrossRef]
- RFC.6574 Report from the Smart Object Workshop. 2012, pp. 1–32. Available online: https://www.iab.org/2012/04/12/rfc-6574-report-from-the-smart-object-workshop/ (accessed on 30 December 2022).
- Amnalou, S.; Bakar, K.A.A. Lightweight security mechanism over MQTT protocol for IoT devices. Int. J. Adv. Comput. Sci. Appl. 2020, 11, 202–207. [Google Scholar] [CrossRef]
- Saeb, M. The Expeditious Cipher (X-cipher): A High Throughput Lightweight Cipher. Int. J. Comput. Sci. Commun. Secur. 2014, 1, 57–62. [Google Scholar]
- Dworkin, M.; Barker, E.; Nechvatal, J.; Foti, J.; Bassham, L.; Roback, E.; Dray, J. Advanced Encryption Standard (AES); NIST: Washington, DC, USA, 2001. [CrossRef]
- Bogdanov, A.; Knudsen, L.R.; Leander, G.; Paar, C.; Poschmann, A.; Robshaw, M.J.B.; Seurin, Y.; Vikkelsoe, C. PRESENT: An Ultra-Lightweight Block Cipher. In Cryptographic Hardware and Embedded Systems—CHES 2007, Proceedings of the International Workshop on Cryptographic Hardware and Embedded Systems, Vienna, Austria, 10–13 September 2007; Paillier, P., Verbauwhede, I., Eds.; Springer: Berlin/Heidelberg, Germany, 2007; pp. 450–466. [Google Scholar]








| Proposed Model | Security Techniques Used? | Communication Technology Deployed | Data Analytics (DA) Techniques Used ? | Challenge |
|---|---|---|---|---|
| Machine Learning-based Irrigation System (2019) [9] | Not used | LoRa P2P | Multiple linear regression algorithm used to calculate the amount of water required for each irrigation | Lack of security techniques |
| The AREThOU5A IoT Platform (2021) [10] | Yes, TCP/IP SSL for encryption | LoRaWAN | Not used | The research lacks evaluation of the proposed security techniques and does not apply lightweight security algorithms as TLS techniques add overhead in terms of memory and energy on constrained nodes |
| Deep Learning Intelligent Irrigation System for Agriculture (DLISA) (2021) [11] | Not used | Wireless communication but not specified | LSTM RNN model is proposed to predict the volumetric soil moisture of the next day to schedule irrigation | Lack of security techniques |
| Sensor-based Smart Irrigation System (2021) [12] | Not used | WiFi | ThingsSpeak displays graphs of collected soil parameters, irrigation decision is made by farmers to activate/deactivate the irrigation | Lack of security techniques |
| Secure Multi-Crop Smart Irrigation System (SMCSIS) (2021) [13] | Yes, access control techniques & Blockchain technology for privacy and data integrity | Not specified | A supervised feed-forward neural network (FFNN) to estimate evaporation for estimated soil moisture (ESM) calculation to specify the next irrigation time. | The research lacks evaluation of the proposed security techniques |
| Machine learning-based Irrigation System (2022) [14] | Not used | Lora | Support vector machine (SVM) and k-nearest neighbor (KNN) algorithms used for prediction of irrigation scheduling | Lack of security techniques |
| Intelligent Sensor-based Smart Irrigation System (2023) [15] | Not used | Lora | Recurrent neural network to forecast the soil moisture level | Lack of security techniques |
| Our proposed model Secure IoT-based Irrigation System (2023) | Yes, The Expeditious Cipher (X-cipher) | WiFi and LoRAWAN or GSM | ThingsSpeak displays graphs of collected soil parameters | The proposed model integrates lightweight cryptography to the IoT ecosystem of smart irrigation systems |
| Protocol | Type | Key | Throughput | Number of Rounds | Comment |
|---|---|---|---|---|---|
| AES [32] | Symmetric block cipher | Different key for each round | 128 bits per round | 10 | Security depends on bit permutation and S-box |
| X-cipher [31] | Symmetric block cipher | Different key for each round | 512 bits per round | 8 | Security depends on cascaded hashed functions (SHA-512 and Whirlpool-512) to generate cipher sub- keys |
| PRESENT [33] | Symmetric block cipher | Different key for each round | 64 bits per round | 31 | Security depends on bit permutation and S-box |
| Lightweight encryption [23] | Symmetric block cipher | Different key for each file | Not specified | Not specified | Security depends on secure key management protocol |
| Software | Description |
|---|---|
| Python 2.7.18 | Programming language |
| Raspberry Pi emulator 4.19.0-13-amd64 | Raspberry Pi emulator |
| Ubuntu 20.1 | Virtual machine |
| Windows 10 | Virtual machine |
| Mosquito | Open source MQTT broker |
| Raspberry Pi OS with desktop Debian version: 11 (bullseye) | Raspberry Pi operating systems |
| Protocol-Process | Throughtput KBps |
|---|---|
| X-cipher-encryption | 164 KBps |
| X-cipher-decryption | 172 KBps |
| PRESENT-encryption | 140 KBps |
| PRESENT-decryption | 140 KBps |
| AES-encryption | 200 KBps |
| AES-decryption | 210 KBps |
| Protocol-Process | Memory Usage (MB) |
|---|---|
| X-cipher-encryption | 20.04 MB |
| X-cipher-decryption | 22.38 MB |
| PRESENT-encryption | 90 MB |
| PRESENT-decryption | 105 MB |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Fathy, C.; Ali, H.M. A Secure IoT-Based Irrigation System for Precision Agriculture Using the Expeditious Cipher. Sensors 2023, 23, 2091. https://doi.org/10.3390/s23042091
Fathy C, Ali HM. A Secure IoT-Based Irrigation System for Precision Agriculture Using the Expeditious Cipher. Sensors. 2023; 23(4):2091. https://doi.org/10.3390/s23042091
Chicago/Turabian StyleFathy, Cherine, and Hassan M. Ali. 2023. "A Secure IoT-Based Irrigation System for Precision Agriculture Using the Expeditious Cipher" Sensors 23, no. 4: 2091. https://doi.org/10.3390/s23042091
APA StyleFathy, C., & Ali, H. M. (2023). A Secure IoT-Based Irrigation System for Precision Agriculture Using the Expeditious Cipher. Sensors, 23(4), 2091. https://doi.org/10.3390/s23042091








