Enhancing Time-Frequency Analysis with Zero-Mean Preprocessing
Abstract
:1. Introduction
2. Preliminaries
2.1. Correlation Power Analysis
2.2. Masking Countermeasure
| Algorithm 1: First-order masked AES-128 |
| Input: Plaintext , Master key , AES S-box Output: Ciphertext Initialization 1: Choose masking values , , , , , uniformly at random from 2: Initialize 3: for up to do 4: 5: end for 6: 7: 8: Encryption 9: 10: for up to 9 do 11: 12: 13: 14: 15: 16: end for 17: 18: 19: 20: Return |
2.3. Hiding Countermeasure
2.4. Second-Order Correlation Power Analysis
2.5. Time-Frequency Analysis for Second-Order Side-Channel Analysis
3. Mathematical Analysis on Time-Frequency Analysis with Zero-Mean Preprocessing
3.1. Mathematical Analysis
3.2. Zero-Mean Preprocessing
4. Experimental Results
- TFA represents Belgarric et al.’s time-frequency analysis without any zero-mean preprocessing.
- TFAwPS represents a time-frequency analysis with standardization.
- TFAwPN represents a time-frequency analysis with min-max normalization.
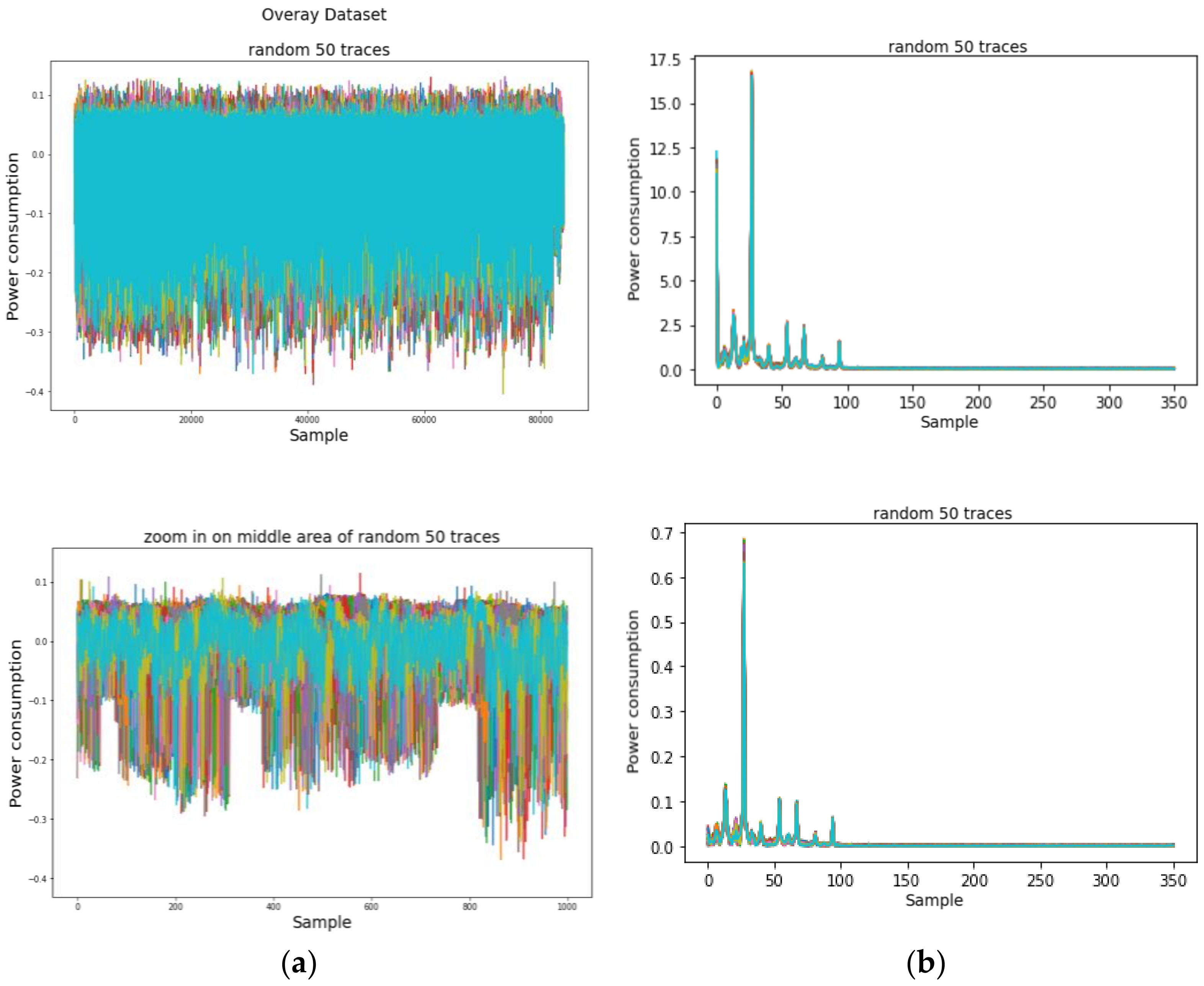
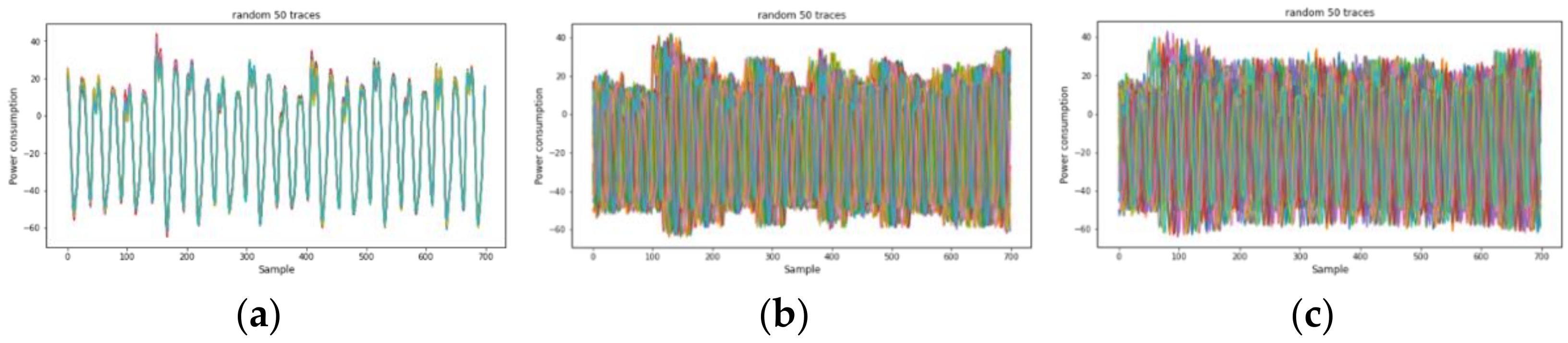
4.1. Introduction to the AES-M Datasets
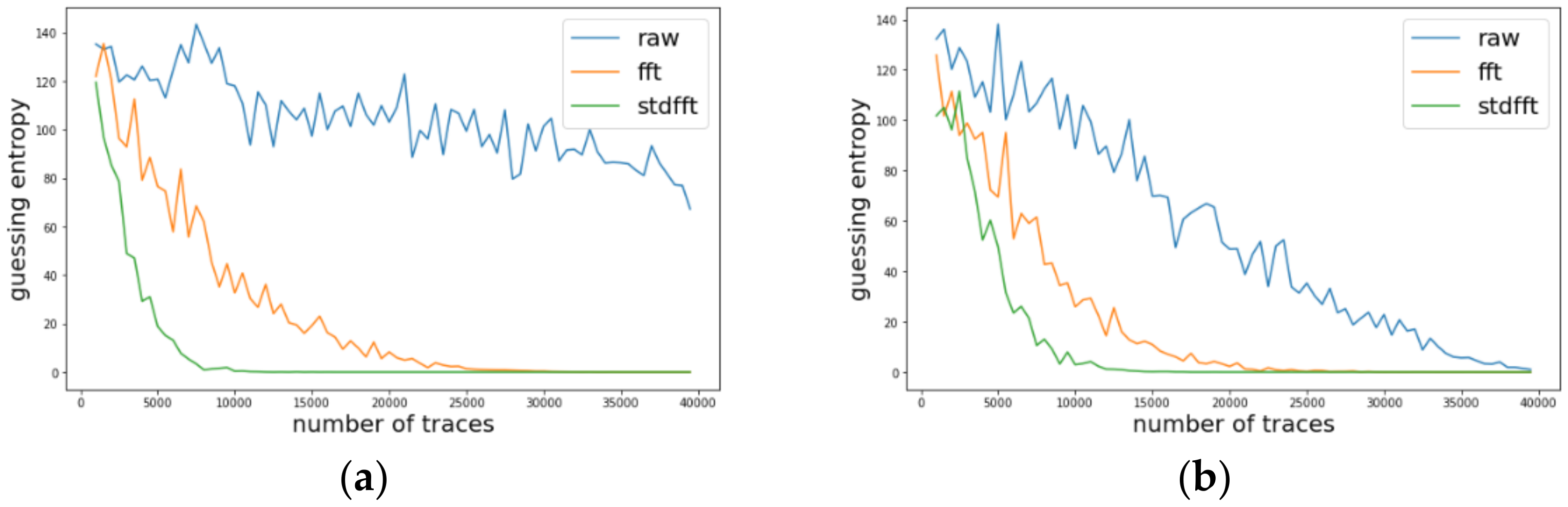
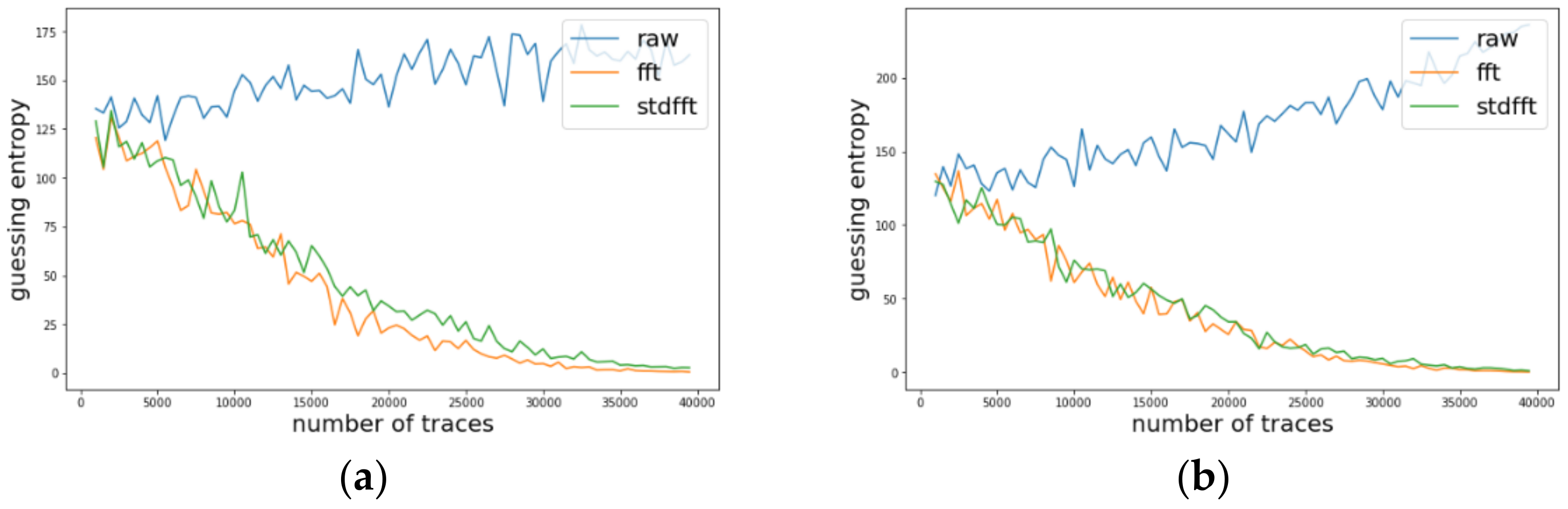
4.2. Experimental Results on AES-M-Sync
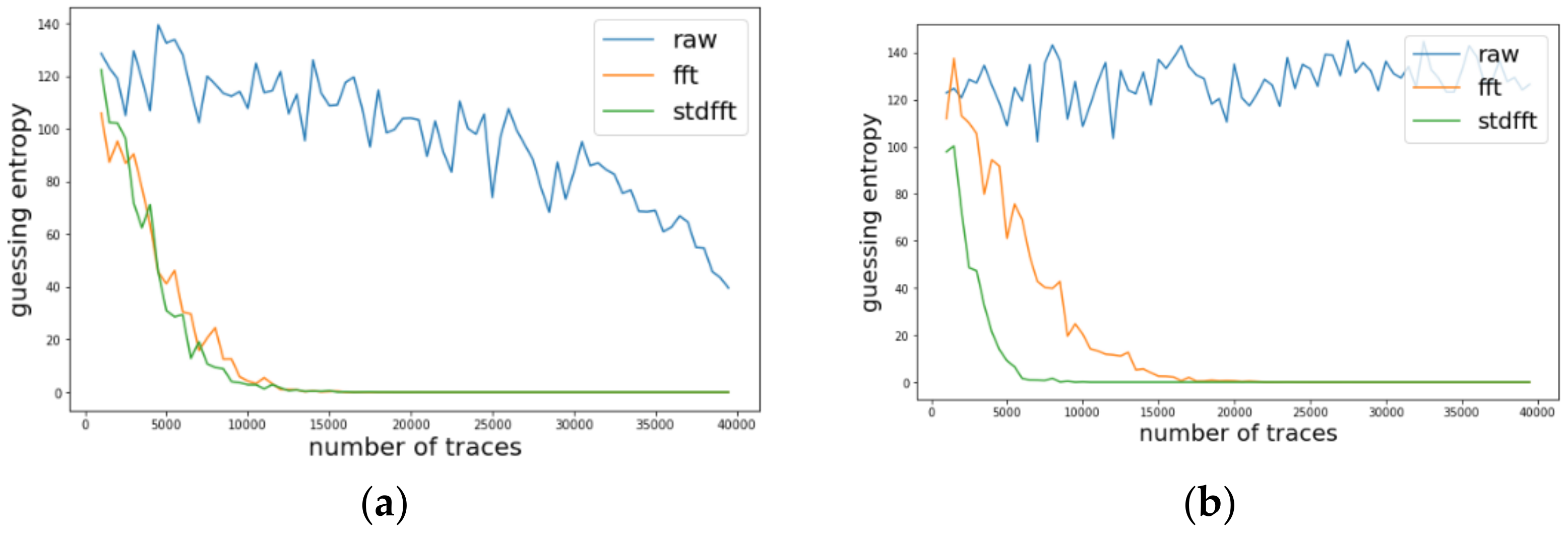
4.3. Experimental Results on AES-M-Desync50
4.4. Experimental Results on AES-M-Desync100
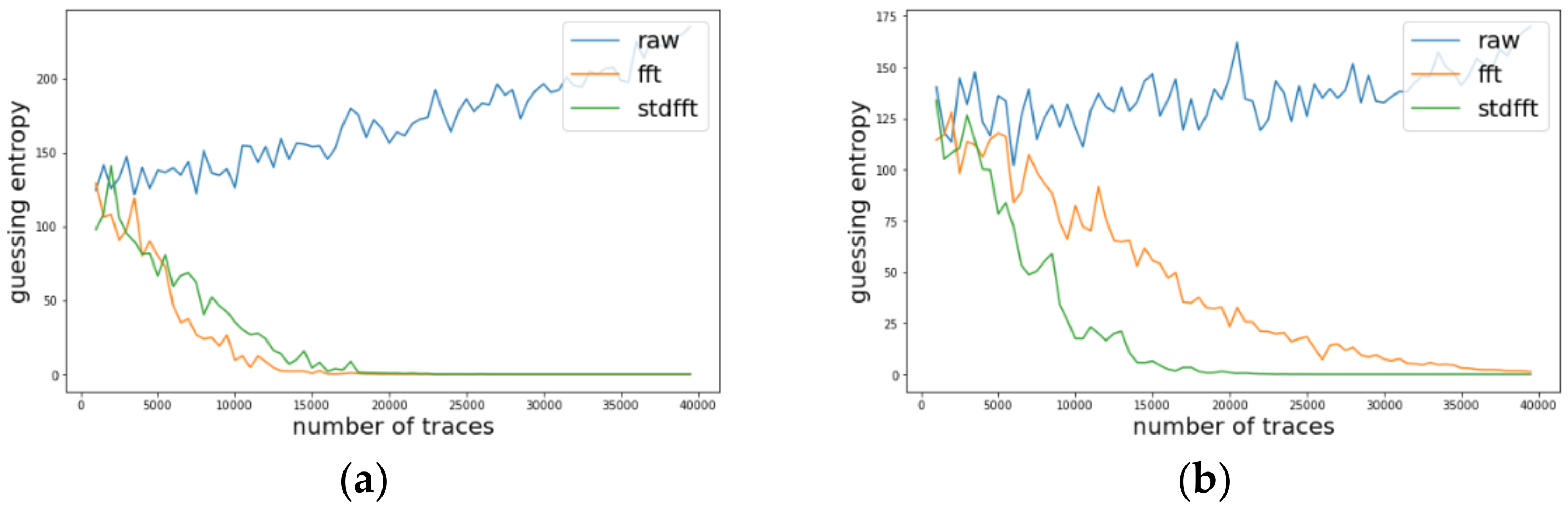
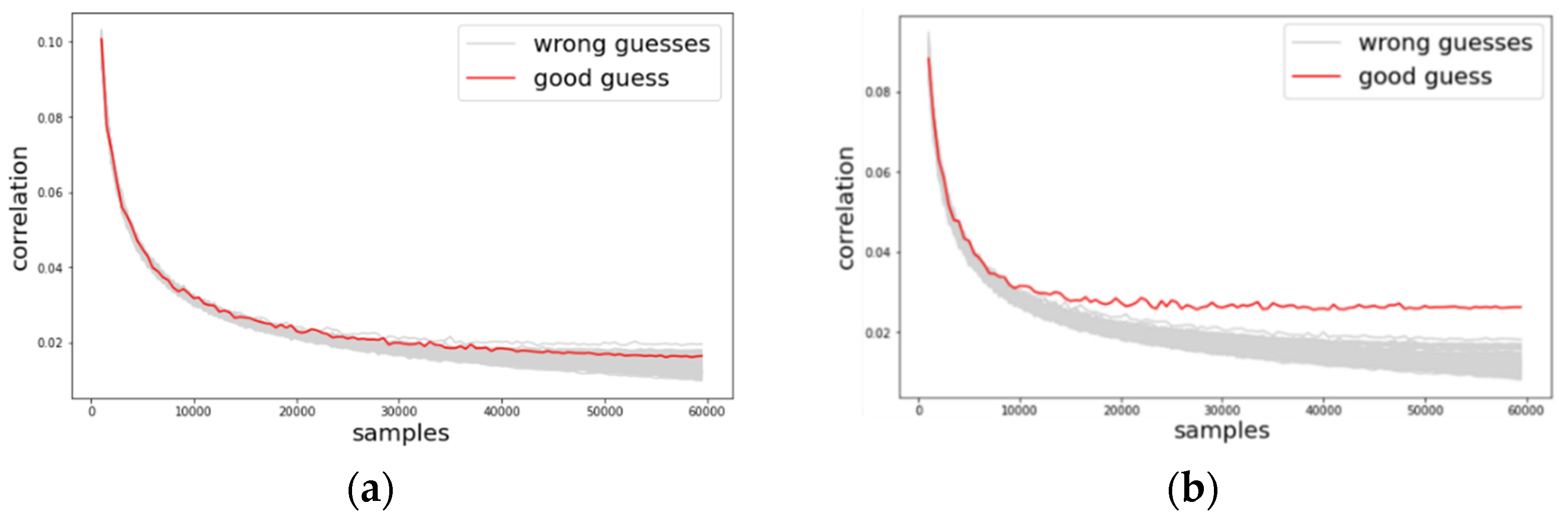
4.5. Experimental Results on ASCAD Dataset
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Appendix A
| AES-M-sync | ||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Byte | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | 10 | 11 | 12 | 13 | 14 | 15 | 16 |
| No preprocessing | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X |
| TFA | O | O | O | O | O | O | O | O | O | O | O | O | O | O | O | O |
| TFAwPS | O | O | O | O | O | O | O | O | O | O | O | O | O | O | O | O |
| TFAwPN | O | O | O | O | O | O | O | O | O | O | O | O | O | O | O | O |
| AES-M-desync30 | ||||||||||||||||
| Byte | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | 10 | 11 | 12 | 13 | 14 | 15 | 16 |
| No preprocessing | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X |
| TFA | O | O | O | O | O | O | O | O | X | O | O | O | O | O | O | O |
| TFAwPS | O | O | O | O | O | O | O | O | O | O | O | O | O | O | O | O |
| TFAwPN | O | X | X | X | X | X | X | X | X | X | X | X | O | X | X | X |
| AES-M-desync50 | ||||||||||||||||
| Byte | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | 10 | 11 | 12 | 13 | 14 | 15 | 16 |
| No preprocessing | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X |
| TFA | X | X | X | O | O | O | O | O | X | O | O | O | O | O | O | O |
| TFAwPS | O | O | O | O | X | O | X | O | X | O | O | O | O | O | O | O |
| TFAwPN | O | X | X | O | O | X | X | X | O | X | X | X | X | X | X | X |
| AES-M-desync100 | ||||||||||||||||
| Byte | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | 10 | 11 | 12 | 13 | 14 | 15 | 16 |
| No preprocessing | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X |
| TFA | X | X | X | X | O | X | X | X | X | X | O | O | O | X | X | X |
| TFAwPS | X | X | X | O | X | X | X | X | X | X | O | O | O | X | X | X |
| TFAwPN | O | X | O | X | X | X | X | O | X | X | X | O | X | X | X | X |
| AES-RD 1 | ||||||||||||||||
| Byte | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | 10 | 11 | 12 | 13 | 14 | 15 | 16 |
| No preprocessing | X | X | X | X | X | O | X | X | X | X | X | X | X | X | X | X |
| TFA | O | X | X | X | O | O | X | O | O | O | X | X | O | O | X | O |
| TFAwPS | O | X | X | O | O | O | O | O | O | O | X | O | O | O | X | O |
| TFAwPN | O | O | X | O | O | O | X | O | O | O | X | X | O | O | X | X |
| ASCAD-sync | ASCAD-desync50 | ASCAD-desync100 | |
|---|---|---|---|
| No preprocessing | X | X | X |
| TFA | X | X | O |
| TFAwPS | O | O | O |
| TFAwPN | O | X | X |
References
- Kocher, P.C. Timing Attacks on Implementations of Diffie-Hellman, RSA, DSS, and Other Systems. In Advances in Cryptology—CRYPTO ’96, Proceedings of the 16th Annual International Cryptology Conference, Santa Barbara, CA, USA, 18–22 August 1996; Koblitz, N., Ed.; Springer: Berlin/Heidelberg, Germany, 1996; Volume 1109, pp. 104–113. [Google Scholar]
- Kocher, P.C.; Jaffe, J.; Jun, B. Differential Power Analysis. In Advances in Cryptology—CRYPTO ’99, Proceedings of the 19th Annual International Cryptology Conference, Santa Barbara, CA, USA, 15–19 August 1999; Wiener, M.J., Ed.; Springer: Berlin/Heidelberg, Germany, 1999; Volume 1666, pp. 388–397. [Google Scholar]
- Gandolfi, K.; Mourtel, C.; Olivier, F. Electromagnetic Analysis: Concrete Results. In Cryptographic Hardware and Embedded Systems—CHES 2001, Proceedings of the Third International Workshop, Paris, France, 14–16 May 2001; Koç, Ç.K., Naccache, D., Paar, C., Eds.; Springer: Berlin/Heidelberg, Germany, 2001; Volume 2162, pp. 251–261. [Google Scholar]
- Quisquater, J.-J.; Samyde, D. ElectroMagnetic Analysis (EMA): Measures and Counter-Measures for Smart Cards. In Proceedings of the International Conference on Research in Smart Cards: Smart Card Programming and Security, E-Smart 2001, Cannes, France, 19–21 September 2001; Attali, I., Jensen, T.P., Eds.; Springer: Berlin/Heidelberg, Germany, 2001; Volume 2140, pp. 200–210. [Google Scholar]
- Genkin, D.; Shamir, A.; Tromer, E. RSA Key Extraction via Low-Bandwidth Acoustic Cryptanalysis. In Advances in Cryptology—CRYPTO 2014, Proceedings of the 34th Annual Cryptology Conference, Santa Barbara, CA, USA, 17–21 August 2014; Part I; Garay, J.A., Gennaro, R., Eds.; Springer: Berlin/Heidelberg, Germany, 2014; Volume 8616, pp. 444–461. [Google Scholar]
- Hutter, M.; Schmidt, J.-M. The Temperature Side Channel and Heating Fault Attacks. In Smart Card Research and Advanced Applications, Proceedings of the 12th International Conference, CARDIS 2013, Berlin, Germany, 27–29 November 2013; Revised Selected Papers; Francillon, A., Rohatgi, P., Eds.; Springer: Berlin/Heidelberg, Germany, 2013; Volume 8419, pp. 219–235. [Google Scholar]
- Shepherd, C.; Markantonakis, K.; van Heijningen, N.; Aboulkassimi, D.; Gaine, C.; Heckmann, T.; Naccache, D. Physical Fault Injection and Side-Channel Attacks on Mobile Devices: A Comprehensive Analysis. Comput. Secur. 2021, 111, 102471. [Google Scholar] [CrossRef]
- Mangard, S.; Oswald, E.; Popp, T. Power Analysis Attacks—Revealing the Secrets of Smart Cards; Springer: Boston, MA, USA, 2007; ISBN 978-0-387-30857-9. [Google Scholar]
- Randolph, M.; Diehl, W. Power Side-Channel Attack Analysis: A Review of 20 Years of Study for the Layman. Cryptography 2020, 4, 15. [Google Scholar] [CrossRef]
- Chari, S.; Rao, J.R.; Rohatgi, P. Template Attacks. In Cryptographic Hardware and Embedded Systems—CHES 2002, Proceedings of the 4th International Workshop, Redwood Shores, CA, USA, 13–15 August 2002; Revised Papers; Kaliski, B.S., Koç, K., Paar, C., Eds.; Springer: Berlin/Heidelberg, Germany, 2003; Volume 2523, pp. 13–28. [Google Scholar]
- Batina, L.; Djukanovic, M.; Heuser, A.; Picek, S. It Started with Templates: The Future of Profiling in Side-Channel Analysis. In Security of Ubiquitous Computing Systems: Selected Topics; Avoine, G., Hernandez-Castro, J., Eds.; Springer International Publishing: Cham, Switzerland, 2021; pp. 133–145. ISBN 978-3-030-10591-4. [Google Scholar]
- Maghrebi, H.; Portigliatti, T.; Prouff, E. Breaking Cryptographic Implementations Using Deep Learning Techniques. In Security, Privacy, and Applied Cryptography Engineering, Proceedings of the 6th International Conference, SPACE 2016, Hyderabad, India, 14–18 December 2016; Carlet, C., Hasan, M.A., Saraswat, V., Eds.; Springer: Berlin/Heidelberg, Germany, 2016; Volume 10076, pp. 3–26. [Google Scholar]
- Cagli, E.; Dumas, C.; Prouff, E. Convolutional Neural Networks with Data Augmentation Against Jitter-Based Countermeasures—Profiling Attacks without Pre-Processing. In Cryptographic Hardware and Embedded Systems—CHES 2017, Proceedings of the 19th International Conference, Taipei, Taiwan, 25–28 September 2017; Fischer, W., Homma, N., Eds.; Springer: Berlin/Heidelberg, Germany, 2017; Volume 10529, pp. 45–68. [Google Scholar]
- Carbone, M.; Conin, V.; Cornelie, M.-A.; Dassance, F.; Dufresne, G.; Dumas, C.; Prouff, E.; Venelli, A. Deep Learning to Evaluate Secure RSA Implementations. IACR Trans. Cryptogr. Hardw. Embed. Syst. 2019, 2019, 132–161. [Google Scholar] [CrossRef]
- Brier, E.; Clavier, C.; Olivier, F. Correlation Power Analysis with a Leakage Model. In Cryptographic Hardware and Embedded Systems—CHES 2004, Proceedings of the 6th International Workshop Cambridge, MA, USA, 11–13 August 2004; Joye, M., Quisquater, J.-J., Eds.; Springer: Berlin/Heidelberg, Germany, 2004; Volume 3156, pp. 16–29. [Google Scholar]
- Le, T.-H.; Clédière, J.; Canovas, C.; Robisson, B.; Servière, C.; Lacoume, J.-L. A Proposition for Correlation Power Analysis Enhancement. In Cryptographic Hardware and Embedded Systems—CHES 2006, Proceedings of the 8th International Workshop, Yokohama, Japan, 10–13 October 2006; Goubin, L., Matsui, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2006; Volume 4249, pp. 174–186. [Google Scholar]
- Chari, S.; Jutla, C.S.; Rao, J.R.; Rohatgi, P. Towards Sound Approaches to Counteract Power-Analysis Attacks. In Advances in Cryptology—CRYPTO ’99, Proceedings of the 19th Annual International Cryptology Conference, Santa Barbara, CA, USA, 15–19 August 1999; Wiener, M.J., Ed.; Springer: Berlin/Heidelberg, Germany, 1999; Volume 1666, pp. 398–412. [Google Scholar]
- Herbst, C.; Oswald, E.; Mangard, S. An AES Smart Card Implementation Resistant to Power Analysis Attacks. In Applied Cryptography and Network Security, Proceedings of the 4th International Conference, ACNS 2006, Singapore, 6–9 June 2006; Zhou, J., Yung, M., Bao, F., Eds.; Springer: Berlin/Heidelberg, Germany, 2006; Volume 3989, pp. 239–252. [Google Scholar]
- Coron, J.-S.; Goubin, L. On Boolean and Arithmetic Masking against Differential Power Analysis. In Cryptographic Hardware and Embedded Systems—CHES 2000, Proceedings of the Second International Workshop, Worcester, MA, USA, 17–18 August 2000; Koç, Ç.K., Paar, C., Eds.; Springer: Berlin/Heidelberg. Germany, 2000; Volume 1965, pp. 231–237. [Google Scholar]
- Goubin, L.; Patarin, J. DES and Differential Power Analysis the “Duplication” Method. In Proceedings of the CHES 1999: Cryptographic Hardware and Embedded Systems, Worcester, MA, USA, 12–13 August 1999; Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); Springer: Berlin/Heidelberg, Germany, 1999. [Google Scholar]
- Fumaroli, G.; Martinelli, A.; Prouff, E.; Rivain, M. Affine Masking against Higher-Order Side Channel Analysis. In Proceedings of the Selected Areas in Cryptography—Proceedings of the 17th International Workshop, SAC 2010, Waterloo, ON, Canada, 12–13 August 2010; Revised Selected Papers; Biryukov, A., Gong, G., Stinson, D.R., Eds.; Springer: Berlin/Heidelberg, Germany, 2010; Volume 6544, pp. 262–280. [Google Scholar]
- Tiri, K.; Akmal, M.; Verbauwhede, I. A Dynamic and Differential CMOS Logic with Signal Independent Power Consumption to Withstand Differential Power Analysis on Smart Cards. In Proceedings of the 28th European Solid-State Circuits Conference, Florence, Italy, 24–26 September 2002; pp. 403–406. [Google Scholar]
- Popp, T.; Mangard, S. Masked Dual-Rail Pre-Charge Logic: DPA-Resistance without Routing Constraints. In Cryptographic Hardware and Embedded Systems—CHES 2005, Proceedings of the 7th International Workshop, Edinburgh, UK, 29 August—1 September 2005; Rao, J.R., Sunar, B., Eds.; Springer: Berlin/Heidelberg, Germany, 2005; Volume 3659, pp. 172–186. [Google Scholar]
- Chen, C.; Eisenbarth, T.; Shahverdi, A.; Ye, X. Balanced Encoding to Mitigate Power Analysis: A Case Study. In Smart Card Research and Advanced Applications, Proceedings of the 13th International Conference, CARDIS 2014, Paris, France, 5–7 November 2014; Revised Selected Papers; Joye, M., Moradi, A., Eds.; Springer: Berlin/Heidelberg, Germany, 2014; Volume 8968, pp. 49–63. [Google Scholar]
- Maghrebi, H.; Servant, V.; Bringer, J. There Is Wisdom in Harnessing the Strengths of Your Enemy: Customized Encoding to Thwart Side-Channel Attacks. In Fast Software Encryption, Proceedings of the 23rd International Conference, FSE 2016, Bochum, Germany, 20–23 March 2016; Revised Selected Papers; Peyrin, T., Ed.; Springer: Berlin/Heidelberg, Germany, 2016; Volume 9783, pp. 223–243. [Google Scholar]
- Coron, J.-S.; Kizhvatov, I. An Efficient Method for Random Delay Generation in Embedded Software. In Cryptographic Hardware and Embedded Systems—CHES 2009, Proceedings of the 11th International Workshop, Lausanne, Switzerland, 6–9 September 2009; Clavier, C., Gaj, K., Eds.; Springer: Berlin/Heidelberg, Germany, 2009; Volume 5747, pp. 156–170. [Google Scholar]
- Coron, J.S.; Kizhvatov, I. Analysis and Improvement of the Random Delay Countermeasure of CHES 2009. In Proceedings of the 12th International Conference on Cryptographic Hardware and Embedded Systems, Santa Barbara, CA, USA, 17–20 August 2010; Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); Springer: Berlin/Heidelberg, Germany, 2010. [Google Scholar]
- Veyrat-Charvillon, N.; Medwed, M.; Kerckhof, S.; Standaert, F.-X. Shuffling against Side-Channel Attacks: A Comprehensive Study with Cautionary Note. In Advances in Cryptology—ASIACRYPT 2012, Proceedings of the 18th International Conference on the Theory and Application of Cryptology and Information Security, Beijing, China, 2–6 December 2012; Wang, X., Sako, K., Eds.; Springer: Berlin/Heidelberg, Germany, 2012; Volume 7658, pp. 740–757. [Google Scholar]
- Woudenberg, J.G.J.V.; Witteman, M.F.; Bakker, B. Improving Differential Power Analysis by Elastic Alignment. In Proceedings of the Topics in Cryptology—CT-RSA 2011—The Cryptographers’ Track at the RSA Conference 2011, San Francisco, CA, USA, 14–18 February 2011; Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); Springer: Berlin/Heidelberg, Germany, 2011. [Google Scholar]
- Muijrers, R.A.; Woudenberg, J.G.J.V.; Batina, L. RAM: Rapid Alignment Method. In Proceedings of the CARDIS 2011: Smart Card Research and Advanced Applications, Leuven, Belgium, 14–16 September 2011; Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); Springer: Berlin/Heidelberg, Germany, 2011. [Google Scholar]
- Clavier, C.; Coron, J.-S.; Dabbous, N. Differential Power Analysis in the Presence of Hardware Countermeasures. In Cryptographic Hardware and Embedded Systems—CHES 2000, Proceedings of the Second International Workshop, Worcester, MA, USA, 17–18 August 2000; Koç, Ç.K., Paar, C., Eds.; Springer: Berlin/Heidelberg, Germany, 2000; Volume 1965, pp. 252–263. [Google Scholar]
- Le, T.-H.; Clédière, J.; Servière, C.; Lacoume, J.-L. Noise Reduction in Side Channel Attack Using Fourth-Order Cumulant. IEEE Trans. Inf. Forensics Secur. 2007, 2, 710–720. [Google Scholar] [CrossRef]
- Nagashima, S.; Homma, N.; Imai, Y.; Aoki, T.; Satoh, A. DPA Using Phase-Based Waveform Matching against Random-Delay Countermeasure. In Proceedings of the International Symposium on Circuits and Systems (ISCAS 2007), New Orleans, LA, USA, 27–20 May 2007; IEEE: Piscataway, NJ, USA, 2007; pp. 1807–1810. [Google Scholar]
- Durvaux, F.; Renauld, M.; Standaert, F.-X.; tot Oldenzeel, L.v.O.; Veyrat-Charvillon, N. Efficient Removal of Random Delays from Embedded Software Implementations Using Hidden Markov Models. In Smart Card Research and Advanced Applications, Proceedings of the 11th International Conference, CARDIS 2012, Graz, Austria, 28–30 November 2012; Revised Selected Papers; Mangard, S., Ed.; Springer: Berlin/Heidelberg, Germany, 2012; Volume 7771, pp. 123–140. [Google Scholar]
- Pozo, S.M.D.; Standaert, F.-X. Blind Source Separation from Single Measurements Using Singular Spectrum Analysis. In Cryptographic Hardware and Embedded Systems—CHES 2015, Proceedings of the 17th International Workshop, Saint-Malo, France, 13–16 September 2015; Güneysu, T., Handschuh, H., Eds.; Springer: Berlin/Heidelberg, Germany, 2015; Volume 9293, pp. 42–59. [Google Scholar]
- Batina, L.; Hogenboom, J.; van Woudenberg, J.G.J. Getting More from PCA: First Results of Using Principal Component Analysis for Extensive Power Analysis. In Proceedings of the Topics in Cryptology—CT-RSA 2012—The Cryptographers’ Track at the RSA Conference 2012, San Francisco, CA, USA, 27 February–2 March 2012; Dunkelman, O., Ed.; Springer: Berlin/Heidelberg, Germany, 2012; Volume 7178, pp. 383–397. [Google Scholar]
- Souissi, Y.; Guilley, S.; Danger, J.-L.; Mekki, S.; Duc, G. Improvement of Power Analysis Attacks Using Kalman Filter. In Proceedings of the Proceedings of the IEEE International Conference on Acoustics, Speech, and Signal Processing, ICASSP 2010, Dallas, TX, USA, 14–19 March 2010; IEEE: Piscataway, NJ, USA, 2010; pp. 1778–1781. [Google Scholar]
- Charvet, X.; Pelletier, H. Improving the DPA Attack Using Wavelet Transform. 2005. Available online: https://csrc.nist.rip/groups/STM/cmvp/documents/fips140-3/physec/papers/physecpaper14.pdf (accessed on 3 February 2022).
- Maghrebi, H.; Prouff, E. On the Use of Independent Component Analysis to Denoise Side-Channel Measurements. In Constructive Side-Channel Analysis and Secure Design, Proceedings of the 9th International Workshop, COSADE 2018, Singapore, 23–24 April 2018; Fan, J., Gierlichs, B., Eds.; Springer: Berlin/Heidelberg, Germany, 2018; Volume 10815, pp. 61–81. [Google Scholar]
- Debande, N.; Souissi, Y.; Elaabid, M.A.; Guilley, S.; Danger, J.-L. Wavelet Transform Based Pre-Processing for Side Channel Analysis. In Proceedings of the 45th Annual IEEE/ACM International Symposium on Microarchitecture, MICRO 2012, Workshops Proceedings, Vancouver, BC, Canada, 1–5 December 2012; IEEE Computer Society: Washington, DC, USA, 2012; pp. 32–38. [Google Scholar]
- Kwon, D.; Kim, H.; Hong, S. Non-Profiled Deep Learning-Based Side-Channel Preprocessing with Autoencoders. IEEE Access 2021, 9, 57692–57703. [Google Scholar] [CrossRef]
- Dworkin, M.J.; Barker, E.B.; Nechvatal, J.R.; Foti, J.; Bassham, L.E.; Roback, E.; Dray, J.F., Jr. Advanced Encryption Standard (AES). 2001. Available online: https://nvlpubs.nist.gov/nistpubs/fips/nist.fips.197.pdf (accessed on 3 February 2022).
- Benadjila, R.; Prouff, E.; Strullu, R.; Cagli, E.; Dumas, C. Deep Learning for Side-Channel Analysis and Introduction to ASCAD Database. J. Cryptogr. Eng. 2020, 10, 163–188. [Google Scholar] [CrossRef]
- Messerges, T.S. Using Second-Order Power Analysis to Attack DPA Resistant Software. In Proceedings of the Cryptographic Hardware and Embedded Systems—CHES, Worcester, MA, USA, 17–18 August 2000; Koç, Ç.K., Paar, C., Eds.; Springer: Berlin/Heidelberg, Germany, 2000; pp. 238–251. [Google Scholar]
- Prouff, E.; Rivain, M.; Bevan, R. Statistical Analysis of Second Order Differential Power Analysis. IEEE Trans. Comput. 2009, 58, 799–811. [Google Scholar] [CrossRef]
- Waddle, J.; Wagner, D.A. Towards Efficient Second-Order Power Analysis. In Cryptographic Hardware and Embedded Systems—CHES 2004, Proceedings of the 6th International Workshop, Cambridge, MA, USA, 11–13 August 2004; Proceedings; Joye, M., Quisquater, J.-J., Eds.; Springer: Berlin/Heidelberg, Germany, 2004; Volume 3156, pp. 1–15. [Google Scholar]
- Timon, B. Non-Profiled Deep Learning-Based Side-Channel Attacks with Sensitivity Analysis. IACR Trans. Cryptogr. Hardw. Embed. Syst. 2019, 2019, 107–131. [Google Scholar] [CrossRef]
- Durvaux, F.; Standaert, F.-X.; Veyrat-Charvillon, N.; Mairy, J.-B.; Deville, Y. Efficient Selection of Time Samples for Higher-Order DPA with Projection Pursuits. In Constructive Side-Channel Analysis and Secure Design, Proceedings of the 6th International Workshop, COSADE 2015, Berlin, Germany, 13–14 April 2015; Revised Selected Papers; Mangard, S., Poschmann, A.Y., Eds.; Springer: Berlin/Heidelberg, Germany, 2015; Volume 9064, pp. 34–50. [Google Scholar]
- Belgarric, P.; Bhasin, S.; Bruneau, N.; Danger, J.-L.; Debande, N.; Guilley, S.; Heuser, A.; Najm, Z.; Rioul, O. Time-Frequency Analysis for Second-Order Attacks. In Smart Card Research and Advanced Applications, Proceedings of the 12th International Conference, CARDIS 2013, Berlin, Germany, 27–29 November 2013; Revised Selected Papers; Francillon, A., Rohatgi, P., Eds.; Springer: Berlin/Heidelberg, Germany, 2013; Volume 8419, pp. 108–122. [Google Scholar]
- Gebotys, C.H.; Ho, S.; Tiu, C.C. EM Analysis of Rijndael and ECC on a Wireless Java-Based PDA. In Cryptographic Hardware and Embedded Systems—CHES 2005, Proceedings of the 7th International Workshop, Edinburgh, UK, 29 August—1 September 2005; Rao, J.R., Sunar, B., Eds.; Springer: Berlin/Heidelberg, Germany, 2005; Volume 3659, pp. 250–264. [Google Scholar]
- Chen, J.; Ng, J.-S.; Chong, K.-S.; Lin, Z.; Gwee, B.-H. A Novel Normalized Variance-Based Differential Power Analysis against Masking Countermeasures. IEEE Trans. Inf. Forensics Secur. 2021, 16, 3767–3779. [Google Scholar] [CrossRef]
- NewAE Technology. CW308T-STM32F. Available online: https://rtfm.newae.com/Targets/UFO%20Targets/CW308T-STM32F/ (accessed on 3 February 2022).
- NewAE Technology. CW1173 ChipWhisperer-Lite. Available online: https://rtfm.newae.com/Capture/ChipWhisperer-Lite/ (accessed on 3 February 2022).








| TFA | TFAwPS | |
|---|---|---|
| Average max peak of absolute correlation coefficients | 0.036785 | 0.042720 |
| Average confidence (1st max peak/2nd max peak) | 1.591291 | 1.840527 |
| The number of found key bytes | 16 | 16 |
| TFA | TFAwPS | |
|---|---|---|
| Average max peak of absolute correlation coefficients | 0.028241 | 0.027701 |
| Average confidence (1st max peak/2nd max peak) | 1.234980 | 1.200778 |
| The number of found key bytes | 12 | 13 |
| TFA | TFAwPS | |
|---|---|---|
| Average max peak of absolute correlation coefficients | 0.024567 | 0.025794 |
| Average confidence (1st max peak/2nd max peak) | 1.083455 | 1.123166 |
| The number of found key bytes | 4 | 4 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Jin, S.; Johansson, P.; Kim, H.; Hong, S. Enhancing Time-Frequency Analysis with Zero-Mean Preprocessing. Sensors 2022, 22, 2477. https://doi.org/10.3390/s22072477
Jin S, Johansson P, Kim H, Hong S. Enhancing Time-Frequency Analysis with Zero-Mean Preprocessing. Sensors. 2022; 22(7):2477. https://doi.org/10.3390/s22072477
Chicago/Turabian StyleJin, Sunghyun, Philip Johansson, HeeSeok Kim, and Seokhie Hong. 2022. "Enhancing Time-Frequency Analysis with Zero-Mean Preprocessing" Sensors 22, no. 7: 2477. https://doi.org/10.3390/s22072477
APA StyleJin, S., Johansson, P., Kim, H., & Hong, S. (2022). Enhancing Time-Frequency Analysis with Zero-Mean Preprocessing. Sensors, 22(7), 2477. https://doi.org/10.3390/s22072477







