LoRaWAN Behaviour Analysis through Dataset Traffic Investigation
Abstract
:1. Introduction
- We aim at defining and using some performance metrics useful to evaluate LoRaWAN, as a network. As far as we know the contribution is new since few works have provided a way to process real LoRaWAN datasets to derive performance indicators. The most of the proposals in the literature are based on simulations while we have developed software tools to apply the metrics on any dataset;
- We designed and presented the procedures implemented in our software tool that can be used to analyse real-world LoRaWAN data;
- We tested these procedures on a large and heterogeneous dataset that contain data collected from a big LoRaWAN ecosystem with 9 gateways and used for several distinct IoT applications.
2. LoRaWAN in a Nutshell
2.1. LoRa
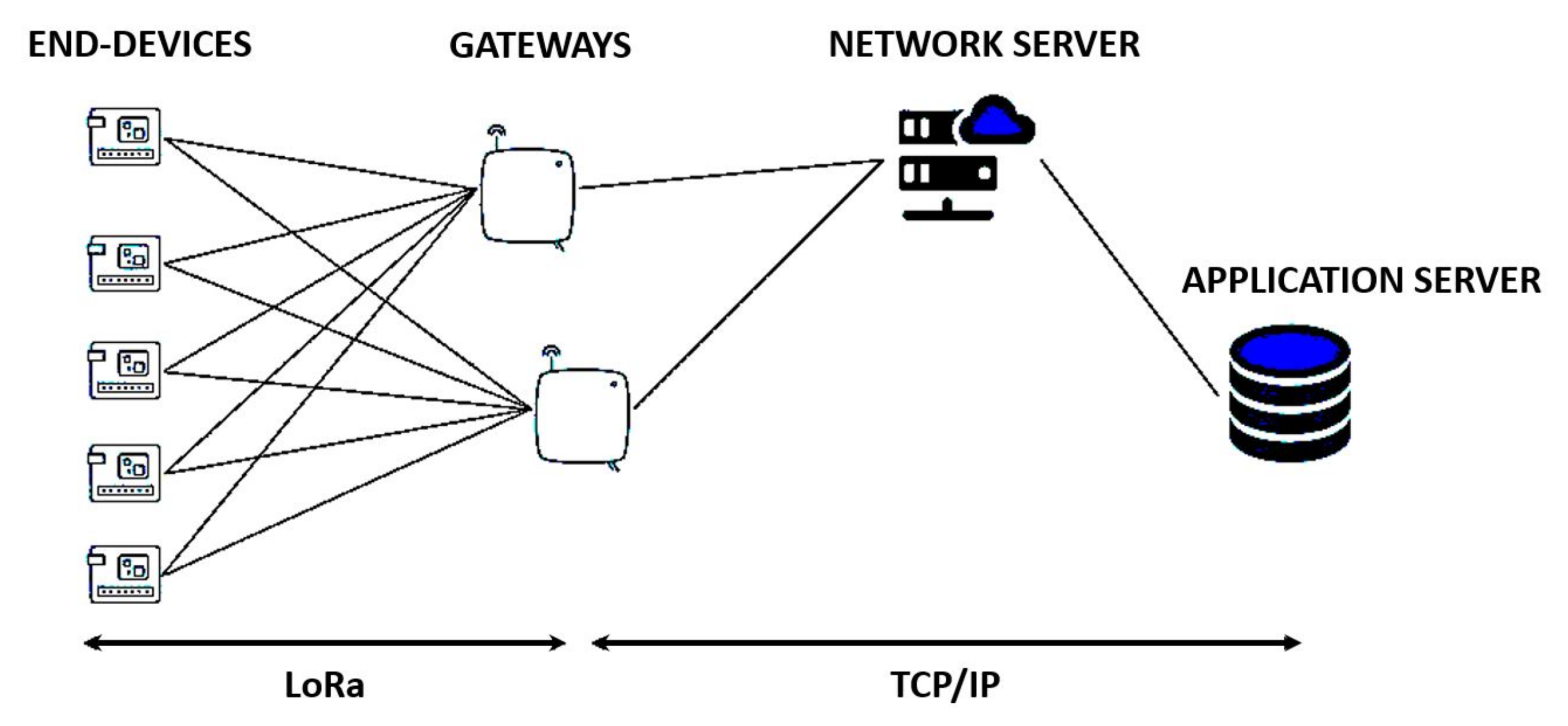
2.2. LoRaWAN
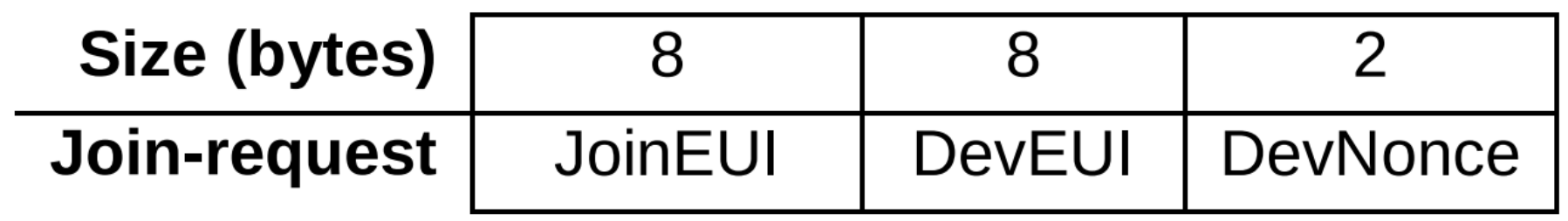
- DevEUI: It is a global end-device ID in IEEE EUI64 address space that uniquely identifies the ED. DevEUI is the recommended unique device identifier by Network Servers, whatever activation procedure is used, to identify a device roaming across networks;
- JoinEUI: The JoinEUI is a global application ID in IEEE EUI64 address space that uniquely identifies the Join Server that is able to assist in the processing of the Join procedure and the session keys derivation;
- NwkKey and AppKey: They are AES-128 root keys specific to the end-device that are assigned to the ED during fabrication.
2.3. LoRa Physical Packet Structure
2.4. LoRa Applications and Related Research
3. LoED: LoRaWAN Dataset
- time: Time at which the packet was received by the gateway;
- physical payload: Raw payload contained in the received packet;
- gateway: Identifier of the gateway that has received the packet;
- crc status: Physical layer CRC;
- frequency: Transmission frequency;
- Spreading Factor: Transmission SF of the packet;
- bandwidth: Bandwidth used by the received packet;
- code-rate: LoRa coding-rate of the packet;
- RSSI: Sampled RSSI value of packet reception;
- SNR: Sampled SNR value of packet reception;
- device-address: Device-address of the device that has sent the packet;
- mtype: mtype bit fields of the packet;
- fcnt: Counter value of the packet;
- fport: Port of the packet.
4. LoRaWAN Analysis
- Gateway radio indicators;
- Packets loss;
- Device–Gateway interaction;
- End-Device addressing and activation;
- Duty-Cycle enforcement;
- Performance of De-duplication procedure.
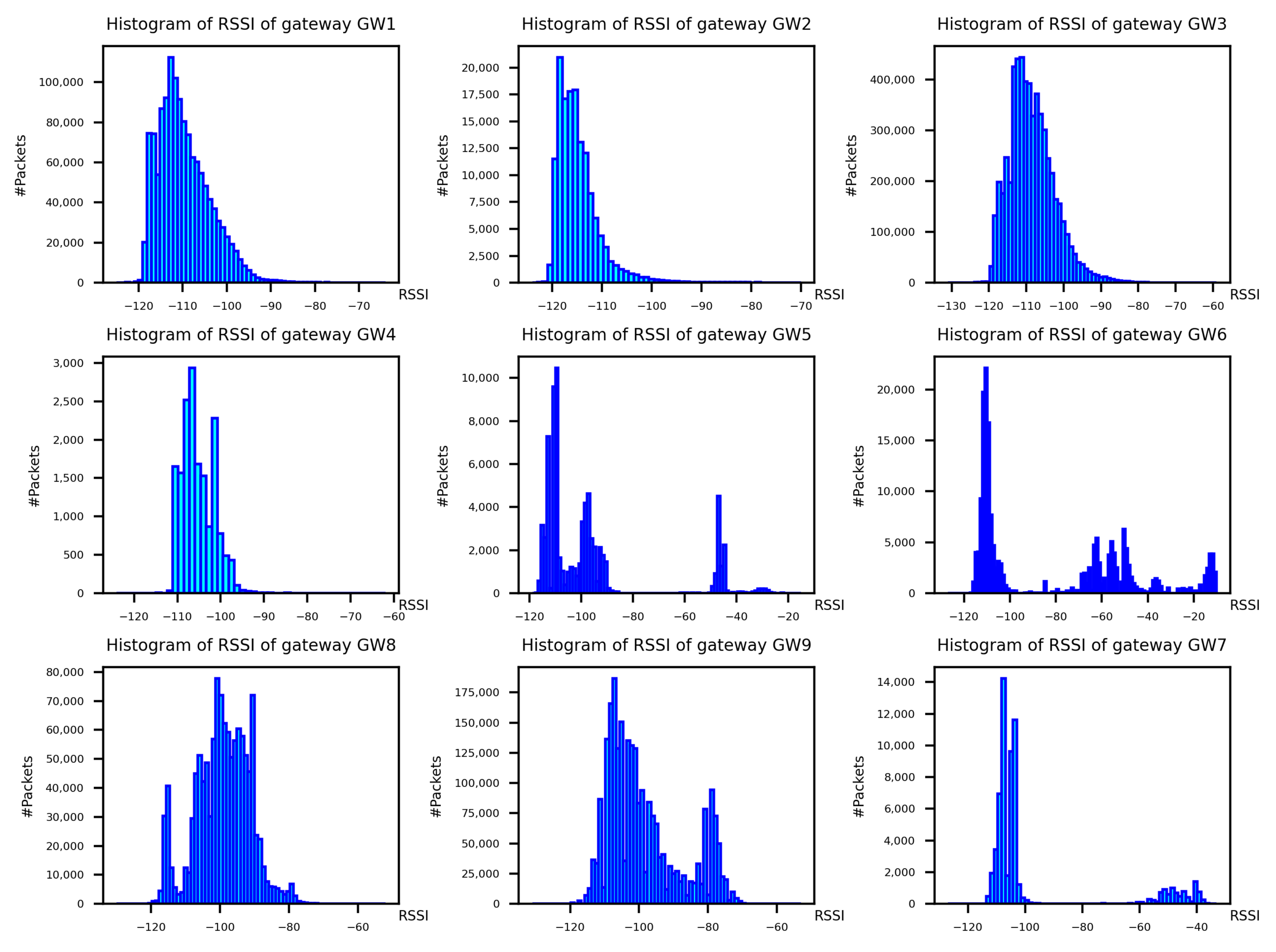
4.1. Gateway Radio Indicators
4.2. Packets Loss
4.3. Device-Gateway Interaction
4.4. End-Device Addressing and Activation
- Number of join request: ;
- Rejoin request: ;
- Join accept: .
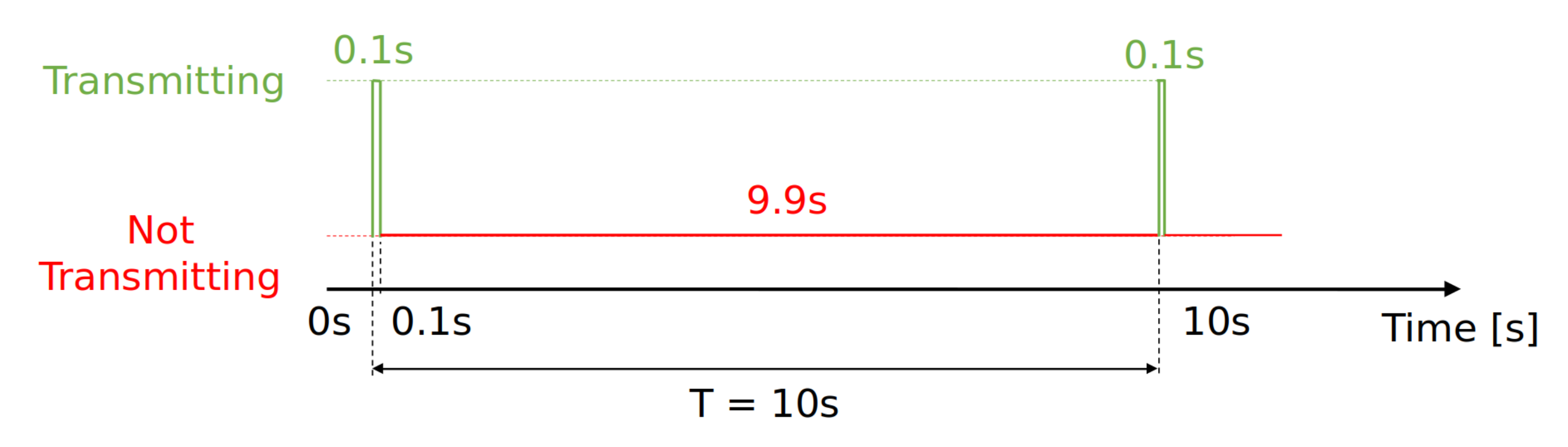
4.5. Duty-Cycle Enforcement
- Find the period of time of connection of the device to the network, computed as where is the first time in which the device is seen in the network and is the last time in which the device is seen in the network;
- Compute the amount of time in which the device was active, we find this amount time by sum all the ToA of the packets sent by the device;
- Compute the duty-cycle percentage as
- Preamble ;
- ;
- Spreading factor of the packet ;
- Length of the payload P of the packet;
- Bandwidth used to transmit the packet expressed in Hz.
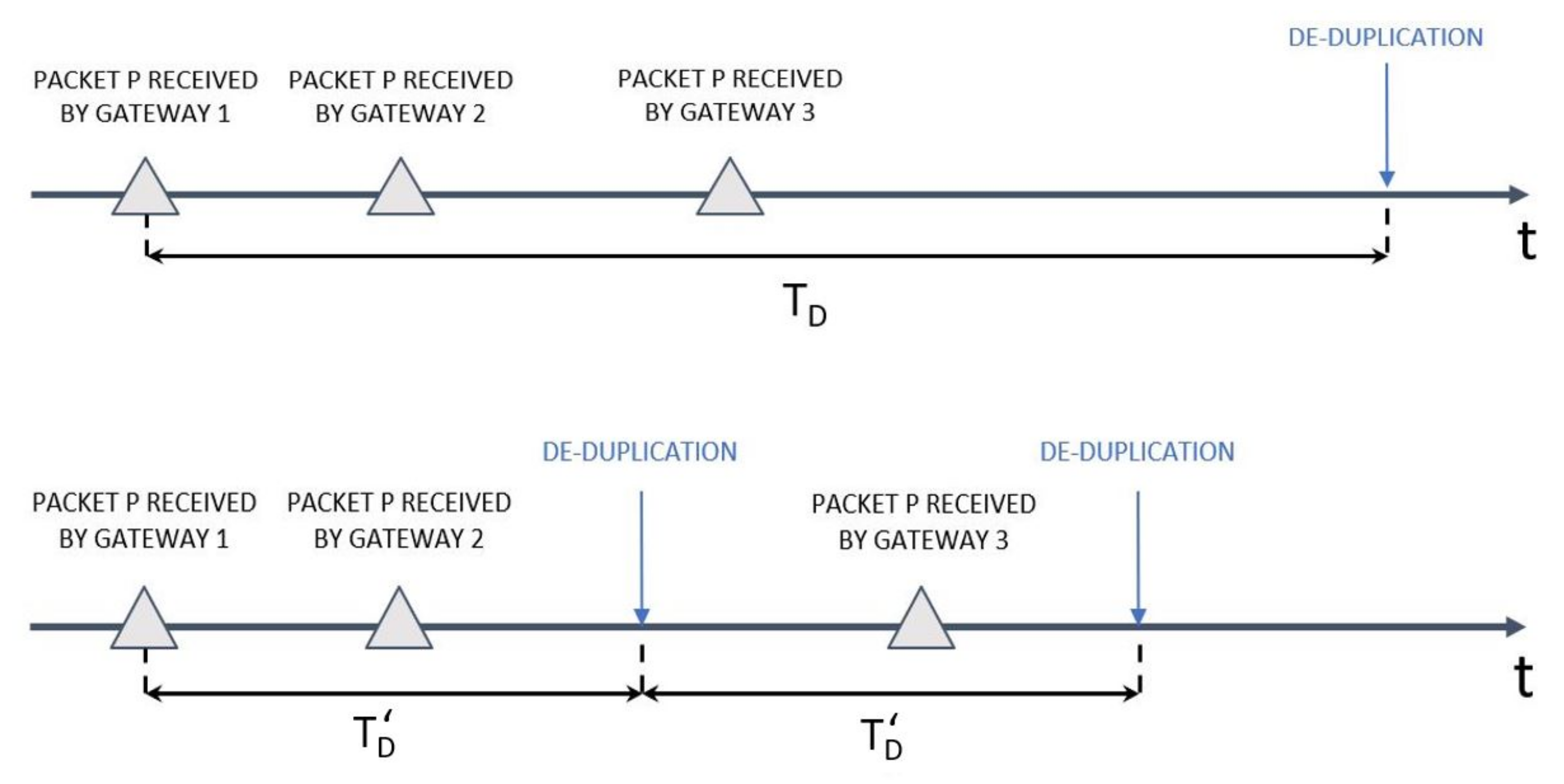
4.6. Performance of De-Duplication Procedure
5. Discussion
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Abbreviations
| ABP | Activation By Personalization |
| ADR | Adaptive Data Rate |
| BW | Bandwidth |
| CR | Coding Rate |
| CSS | Chirp Spread Spectrum |
| DevAddr | Device Address |
| DevEUI | Device Extended Unique Identifier |
| DevNonce | Device Nonce |
| ED | End Device |
| FCnt | Frame Counter |
| FCntDown | Frame Counter Downlink |
| FCntUp | Frame Counter Uplink |
| FCtrl | Frame Control |
| FHDR | Frame Header |
| FOpts | Frame Options |
| ISM | Industrial Scientific and Medical |
| LoED | LoRaWAN at the Edge Dataset |
| LPWAN | Low-Power Wide-Area-Network |
| MHDR | MAC header |
| MIC | Message Integrity Code |
| NS | Network Server |
| OTAA | Over-The-Air Activation |
| PHDR | Physical Header |
| RSSI | Received Signal Strength Indicator |
| SF | Spreading Factor |
References
- Sinha, S. State of IoT 2021: Number of Connected IoT Devices Growing 9% to 12.3 Billion Globally, Cellular IoT Now Surpassing 2 Billion. 2021. Available online: https://iot-analytics.com/number-connected-iot-devices (accessed on 30 January 2022).
- Bhatia, L.; Breza, M.; Marfievici, R.; McCann, J.A. 2020 Dataset LoED the LoRaWAN at the Edge Dataset. In Proceedings of the 3rd International SenSys+BuildSys Workshop on Data Acquisition to Analysis (DATA 2020), Yokohama, Japan, 16 November 2020; ACM: New York, NY, USA, 2020; p. 2. [Google Scholar]
- Semtech LoRa Overwiev. Available online: https://www.semtech.com/lora (accessed on 30 January 2022).
- Semtech Corporation. LoRa and LoRaWAN: A Technical Overview, Semtech Corporation 200 Flynn Road, Camarillo, CA 93012. 2020. Available online: https://lora-developers.semtech.com/uploads/documents/files/LoRa_and_LoRaWAN-A_Tech_Overview-Downloadable.pdf (accessed on 30 January 2022).
- LoRa® Alliance Technical Marketing Workgroup. LoRaWAN™, What is it? A technical overview of LoRa® and LoRaWAN™. LoRa Alliance®. 2020. Available online: https://lora-alliance.org/wp-content/uploads/2020/11/what-is-lorawan.pdf (accessed on 30 January 2022).
- Sornin, N.; Yegin, A. LoRaWAN™ 1.1 Specification; LoRa Alliance, Inc.: Beaverton, OR, USA, 2017; p. 97003. [Google Scholar]
- LoRa Technology Is Connecting Our Smart Planet, Semtech Corporation. 2022. Available online: https://www.semtech.com/lora/lora-applications (accessed on 30 January 2022).
- UseCase-EBook-SmartCitiesoftheFuture. Semtech Corporation. 2021. Available online: https://info.semtech.com/lora-smart-cities-ebook (accessed on 30 January 2022).
- LoRa Edge™, Semtech Corporation. Available online: https://www.semtech.com/products/wireless-rf/lora-edge (accessed on 30 January 2022).
- Monitoring of Covid-19 Vaccines storage And Transportation. OrionM2M®. 2021. Available online: https://lora-alliance.org/member-press-release/monitoring-of-covid-19-vaccines-storage-and-transportation (accessed on 30 January 2022).
- Magrin, D.; Capuzzo, M.; Zanella, A. A Thorough Study of LoRaWAN Performance Under Different Parameter Settings. IEEE Internet Things J. 2020, 7, 116–127. [Google Scholar] [CrossRef] [Green Version]
- Garlisi, D.; Martino, A.; Zouwayhed, J. Exploratory approach for network behavior clustering in LoRaWAN. J. Ambient. Intell. Hum. Comput. 2021, 1–15. [Google Scholar] [CrossRef]
- The Things Stack. Available online: https://www.thethingsindustries.com/stack (accessed on 30 January 2022).
- Toro-Betancur, V.; Premsankar, G.; Slabicki, M.; Di Francesco, M. Modeling Communication Reliability in LoRa Networks with Device-level Accuracy. In Proceedings of the IEEE INFOCOM 2021—IEEE Conference on Computer Communications, Vancouver, BC, Canada, 10–13 May 2021. [Google Scholar]
- Ferre, G. Collision and packet loss analysis in a LoRaWAN network. In Proceedings of the 2017 25th European Signal Processing Conference (EUSIPCO), Kos, Greece, 28 August–2 September 2017. [Google Scholar]
- Spadaccino, P.; Garlisi, D.; Cuomo, F.; Pillon, G.; Pisani, P. Discovery privacy threats via device de-anonymization in LoRaWAN. Comput. Commun. 2022, 189, 1–10. [Google Scholar] [CrossRef]
- Di Vincenzo, V. Improving Downlink Scalability in LoRaWAN, Rel. Paolo Giaccone, Politecnico di Torino, Corso di Laurea Magistrale in Ingegneria Informatica (Computer Engineering). 2020. Available online: https://webthesis.biblio.polito.it/14451/1/tesi.pdf (accessed on 30 January 2022).
- ChirpStack Open-Source LoRaWAN Network Server Stack, Orne Brocaar. Available online: https://www.chirpstack.io (accessed on 30 January 2022).











| Gateway Number | Gateway ID |
|---|---|
| 00000f0c210281c4 | GW1 |
| 00000f0c22433141 | GW2 |
| 00000f0c210721f2 | GW3 |
| 00000f0c224331c4 | GW4 |
| 00800000a0001914 | GW5 |
| 00800000a0001793 | GW6 |
| 00800000a0001794 | GW7 |
| 7276ff002e062804 | GW8 |
| 0000024b0b031c97 | GW9 |
| mtype | Message Type |
|---|---|
| 000 | Join request |
| 001 | Join accept |
| 110 | Rejoin request |
| 010 | Unconfirmed data-up |
| 100 | Confirmed data-up |
| 011 | Unconfirmed data-down |
| 101 | Confirmed data-down |
| 111 | Proprietary |
| Message Type | Total Number of Packets | Number of Distinct Packets |
|---|---|---|
| Join request | 246,272 | 170,476 |
| Rejoin request | 27,576 | 26,561 |
| Join-Accept | 20,971 | 20,660 |
| Confirmed data-up | 664,474 | 441,742 |
| Unconfirmed data-up | 7,441,505 | 4,776,723 |
| Confirmed data-down | 63,216 | 32,537 |
| Unconfirmed data-down | 24,140 | 23,989 |
| Proprietary | 30,206 | 29,539 |
| Unknown | 2,744,641 | 2,744,641 |
| Total | 11,263,001 | 8,266,868 |
| Spreading Factor | Bit Rate [bps] |
|---|---|
| SF12 | 150 |
| SF11 | 260 |
| SF10 | 580 |
| SF9 | 1360 |
| SF8 | 2740 |
| SF7 | 4840 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Spadaccino, P.; Crinó, F.G.; Cuomo, F. LoRaWAN Behaviour Analysis through Dataset Traffic Investigation. Sensors 2022, 22, 2470. https://doi.org/10.3390/s22072470
Spadaccino P, Crinó FG, Cuomo F. LoRaWAN Behaviour Analysis through Dataset Traffic Investigation. Sensors. 2022; 22(7):2470. https://doi.org/10.3390/s22072470
Chicago/Turabian StyleSpadaccino, Pietro, Francesco Giuseppe Crinó, and Francesca Cuomo. 2022. "LoRaWAN Behaviour Analysis through Dataset Traffic Investigation" Sensors 22, no. 7: 2470. https://doi.org/10.3390/s22072470
APA StyleSpadaccino, P., Crinó, F. G., & Cuomo, F. (2022). LoRaWAN Behaviour Analysis through Dataset Traffic Investigation. Sensors, 22(7), 2470. https://doi.org/10.3390/s22072470







