A Survey on Wireless Wearable Body Area Networks: A Perspective of Technology and Economy
Abstract
1. Introduction
1.1. Research/Survey Methodology
1.2. What Questions Does This Survey Answer?
- 1.
- What is a wireless wearable body area network and its communication architecture?
- 2.
- What sensors are used in Wearable Wireless BANs, and what end products and solutions are available in the market?
- 3.
- What are the potential wireless technologies used to develop WWBANs, and what security threats and control measures are available?
- 4.
- What does the future hold, and what major challenges do the wireless wearable body area devices have to face?
- 5.
- What are the major projects and research directions in this area?
1.3. Contributions
- 1.
- During our study on WBANs, we found that a majority of the reports focus on only a particular set of viewers as discussed above.
- 2.
- The present article addresses maximum perspectives of wireless wearable body area networks such as architecture, components, sensors, devices, health systems, wireless technologies, security concerns, projects, regulations, and most important, and Compound Annual Growth Rate (CAGR).
- 3.
- A special section is added in this survey that focuses on the emerging WBAN technologies, such as energy harvesting, human body communication, quantum computing, graph neural networks (GNN), artificial intelligence (machine and deep learning), blockchain, and digital twins. Such a section is rarely seen in surveys or review articles.
- 4.
- Since the article is interdisciplinary, technical terms of a particular field are briefly explained on the spot so that a specialist of one field may understand the concepts of another without repetitive switching from this article to another.
2. WBAN Technical Issues
2.1. WBAN Architecture
Components
2.2. Types of Sensors
2.2.1. Type-I Implantable
2.2.2. Type-II Ingestibles
2.2.3. Type-III Injectables
2.2.4. Type-IV Patchable: Body Surfaced/Patched
2.2.5. Type-V Proximity-Based Devices
2.2.6. Type-VI Textile Structured Devices
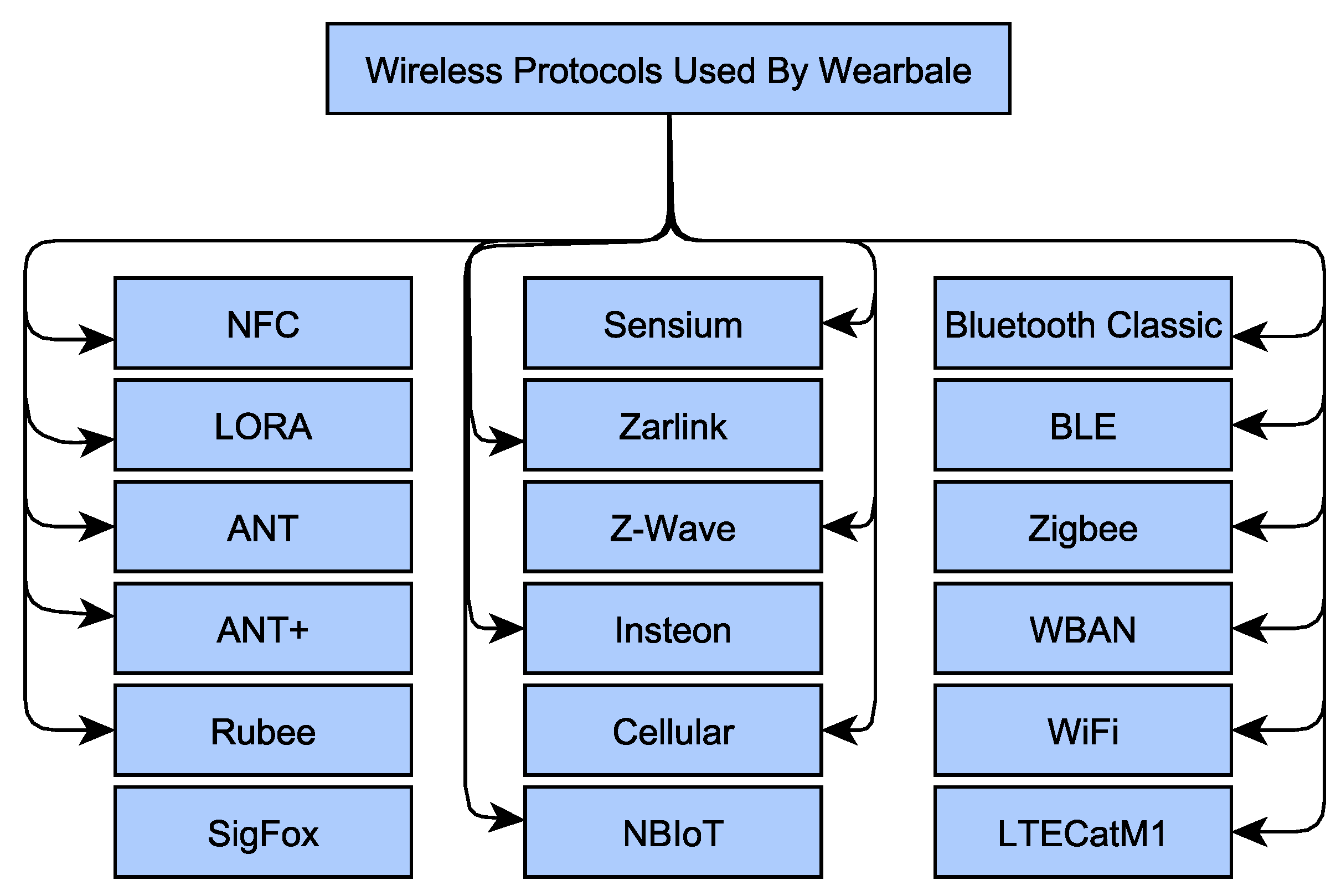
2.3. Wireless Technologies
2.3.1. NFC
2.3.2. ANT
2.3.3. RuBee IEEE 1902.1
2.3.4. Sensium
2.3.5. Zarlink
2.3.6. Z-Wave and Insteon
2.3.7. Bluetooth Classic
2.3.8. Bluetooth Low Energy (BLE)
2.3.9. Zigbee
2.3.10. Ultra-Wideband (UWB)
2.3.11. LORA
2.3.12. WBAN IEEE 802.15.6
2.3.13. WiFi
2.3.14. Cellular
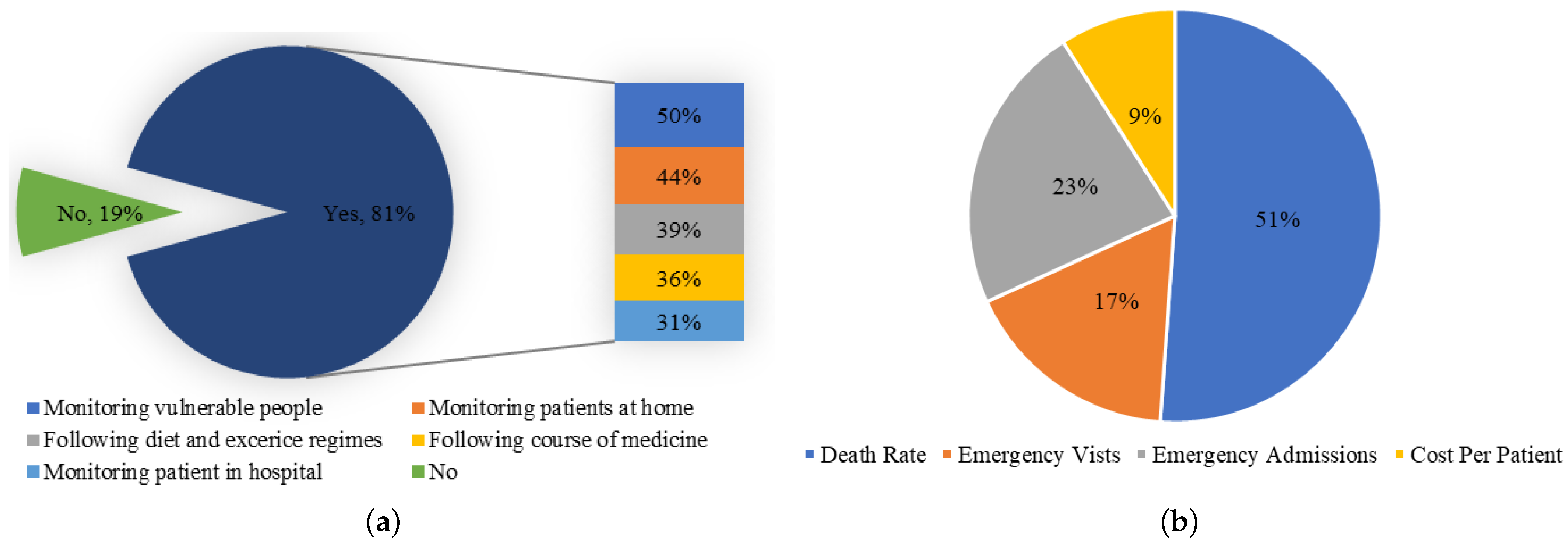
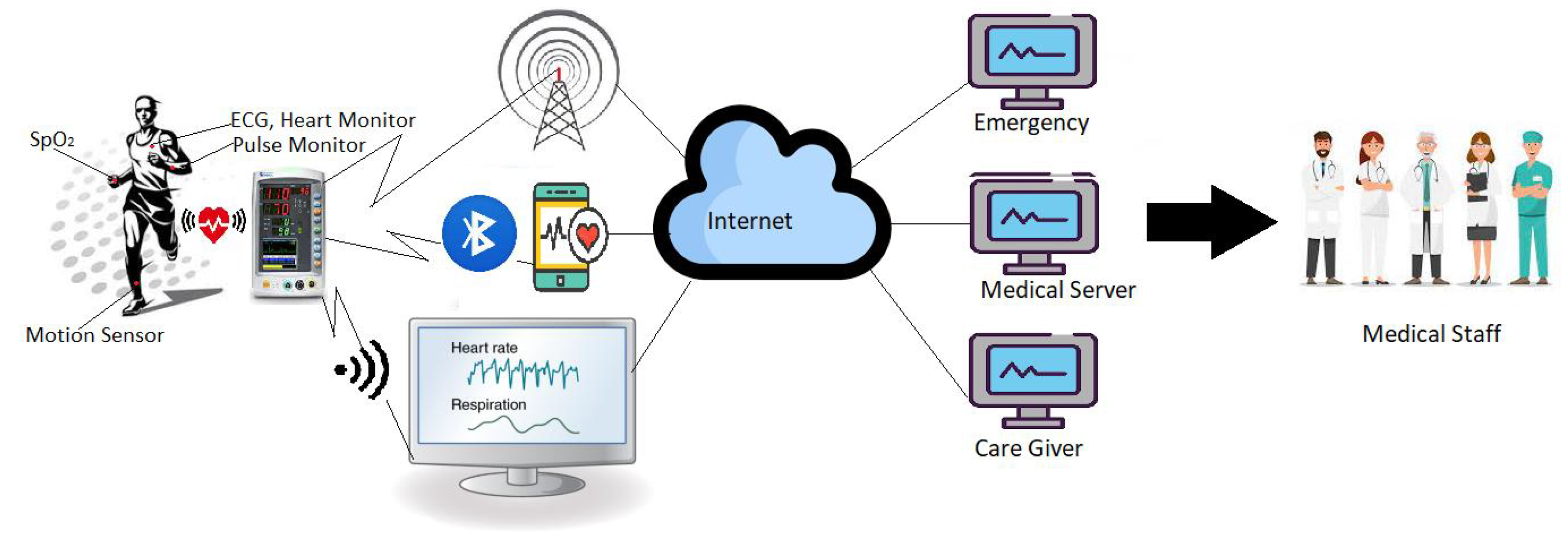
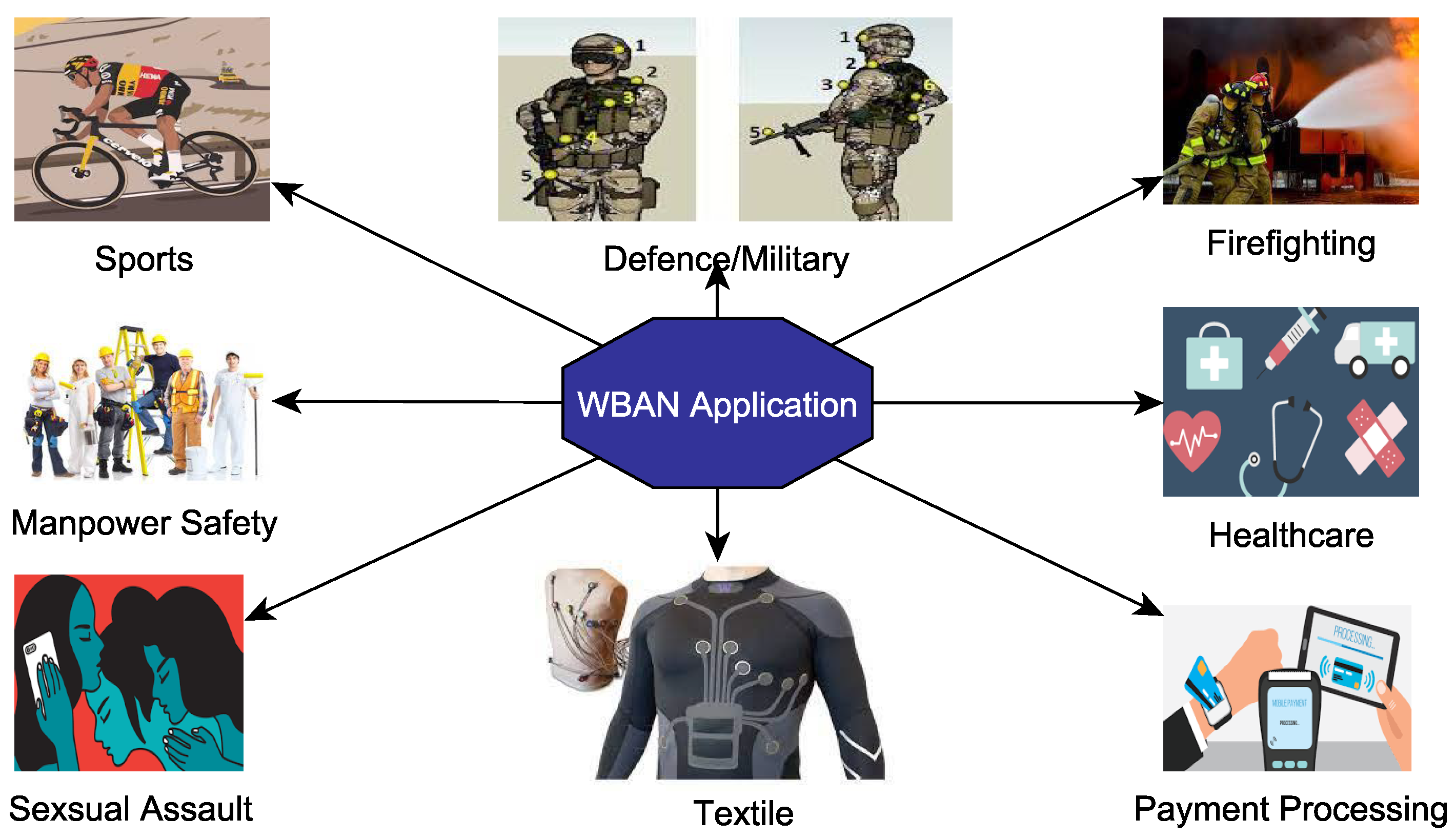
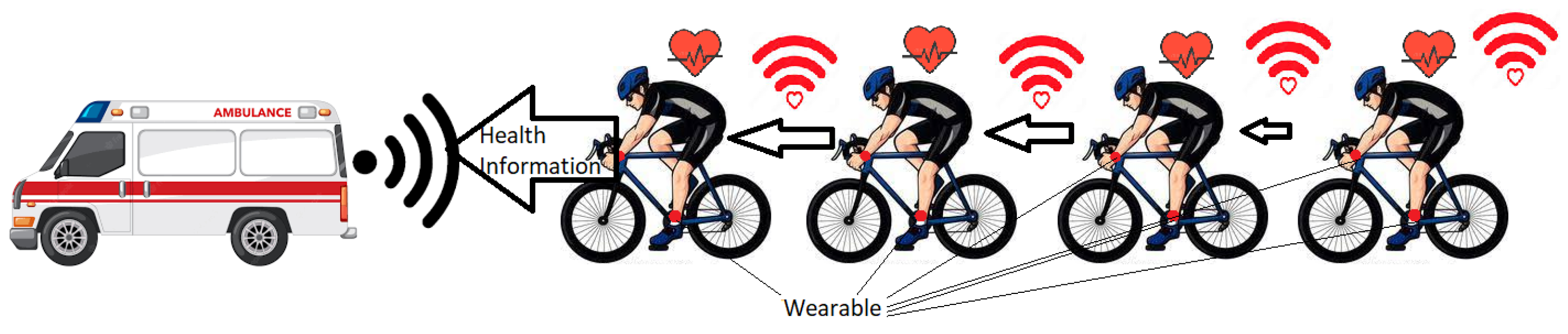
2.4. Application of Wearable WBANS
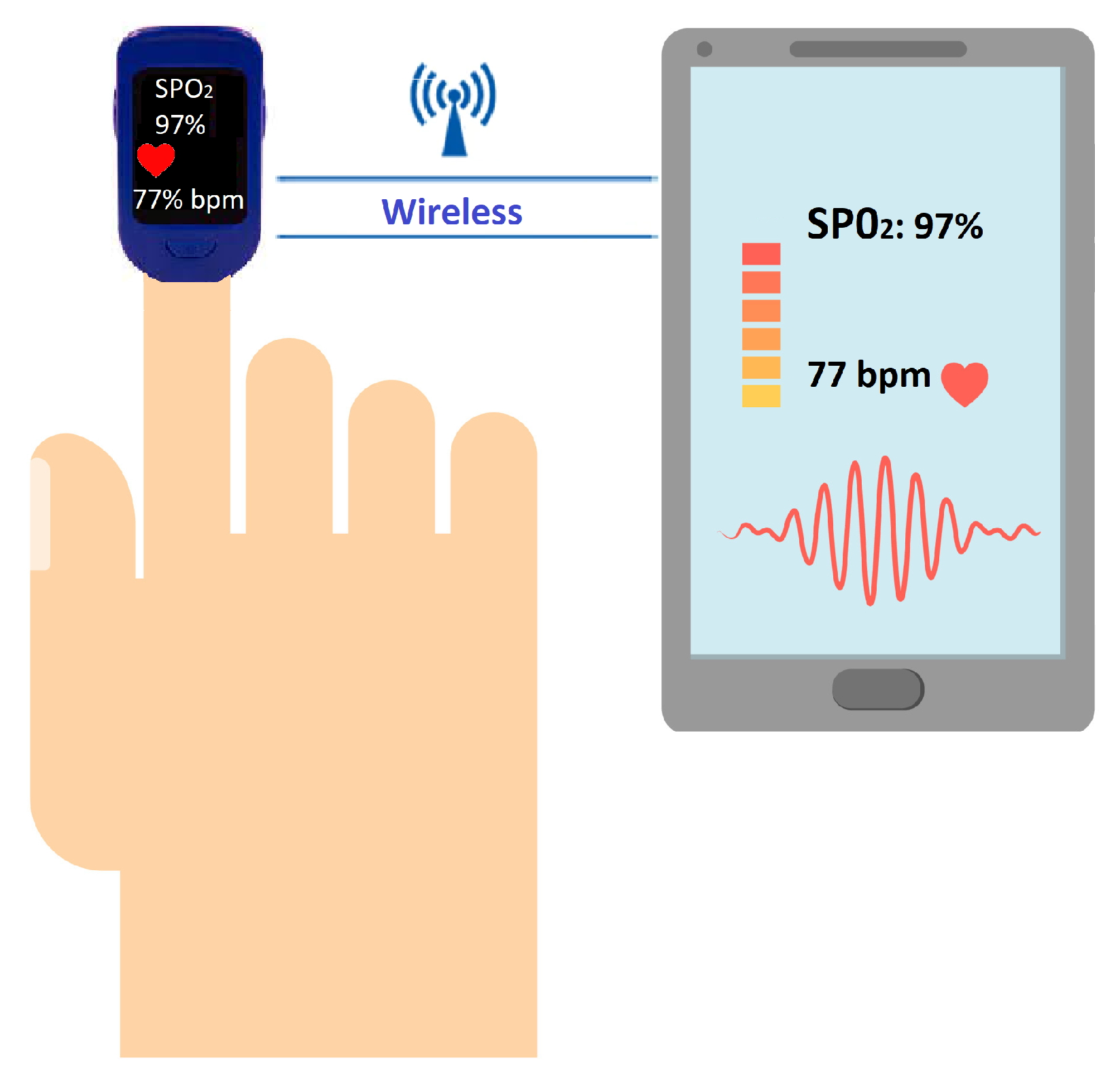
Vital Sign Monitoring
- 1.
- They use sensors to determine heart beat rate, walking or running steps and number of calories burned.
- 2.
- These devices can be connected to a computer, laptop, or mobile to communicate the results wirelessly.
2.5. WBAN Security Issues
2.5.1. Major Security Requirements
- 1.
- Device Authenticity: This is a very critical issue. Adversaries can implant a malevolent node in a non-line-of-sight (NLOS) location that can inject fake data and even receive legal data while acting as a legal device [128]. Thus, it is very important to validate the authenticity of the BAN devices that they claim to be [129].
- 2.
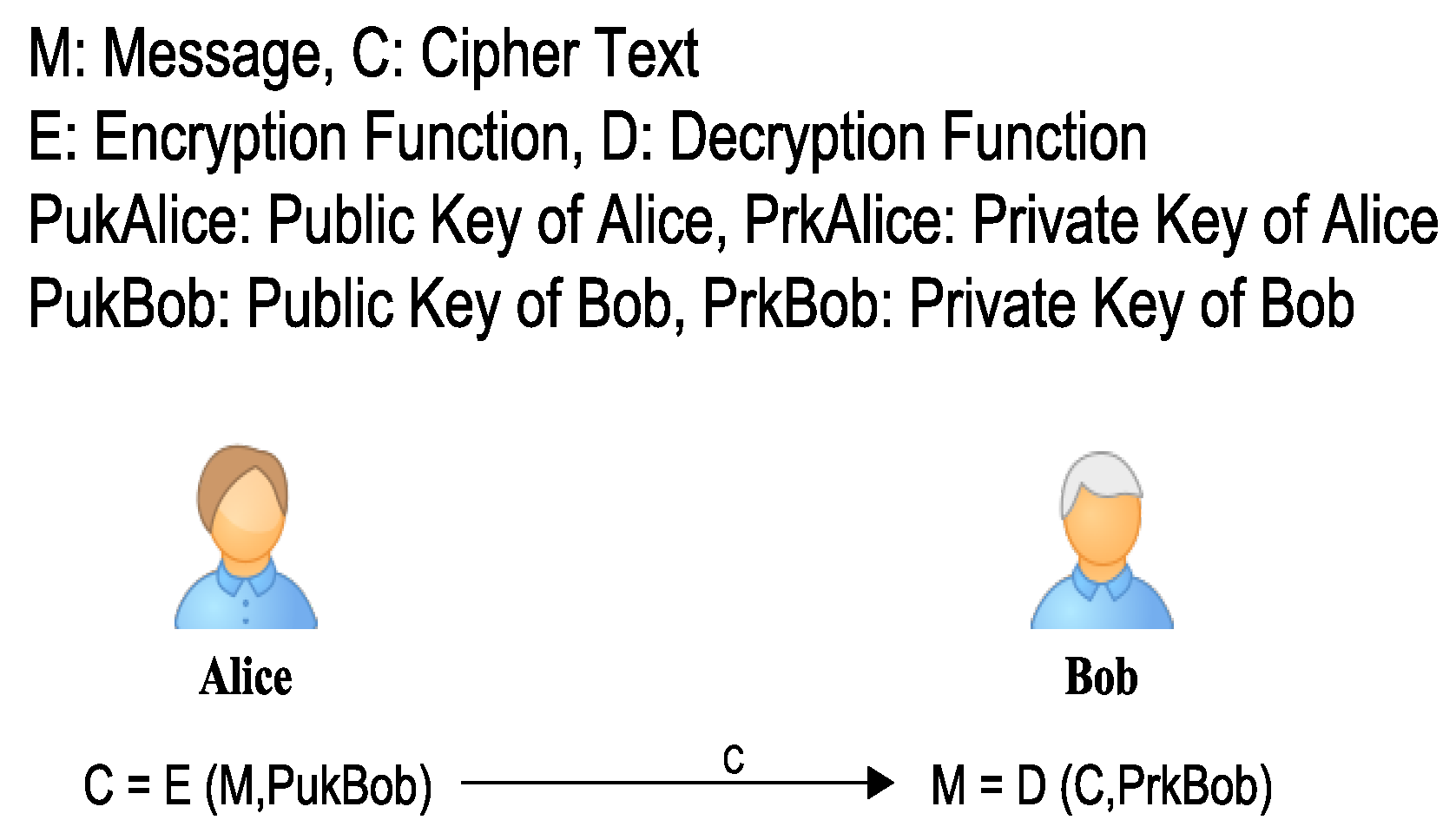
- Confidentiality: Confidentiality ensures that the information should not be disclosed to unauthorized entities while moving from wearable WBAN source to destination [130]. However, due to the open and broadcast nature of WBAN transmission, the data can be eavesdropped and disclosed to an unauthorized party. Therefore, it is always advised to encrypt data before transmission [128].
- 3.
- Integrity: It claims that information must reach the destination in its original form as was sent by the body-worn or wearable WBAN source; it must not be altered during its transfer. Due to the free-flying of wireless BAN frames, they can be intercepted and tampered with by the attacker, which may harm the health system or even the patient’s life [128,130]. That is why it is required to ensure the integrity of data using some message authentication techniques such as hashing or CRC. They ensure the data are not modified during the transition from one BAN device to another.
- 4.
- Availability: One of the most disturbing attacks is DOS (Denial of Service), which is launched against a body controller unit, cloud server, or medical server. Thus, the attack can even cause a shutdown of medical services, which may impose serious life threats on patients [128,130]. For ensuring life safety and timely treatment of the patient, health network communication systems must be available whenever a WBAN source is required to send data.
- 5.
- User Authentication/Authorization: In remotely controlled healthcare WBAN systems, only the authentic and authorized medical staff members must be able to access the data of a particular patient. User authentication can be established using well-informed mechanisms, such as username/password, PINs, fingerprints, etc. Similarly, a proper access control mechanism (e.g., Access Control Lists) must be devised to ensure authorized access to data [129].
2.5.2. Importance of Security
2.5.3. Technical Approaches
TinySec Security Solution
ECC
Biometric-Based Security Solution
Encryption
2.5.4. Wireless Security Fixes
ANT/ANT+/ANT+S
RuBee IEEE 1902.1
Sensium
Z-Wave
Zarlink
Insteon
LR-WPANs IEEE 802.15.4 Security Services
WBAN IEEE 802.15.6 Security
ZigBee Security Services
BLE Security
Bluetooth Security Protocols
- 1.
- Non-secure: No security.
- 2.
- Service-level enforced security mode A non-secure ACL (Asynchronous Connection Link) can be established using this mode. Security functions run only after the L2CAP connection-oriented or connection-less channel request is placed.
- 3.
- Link-level enforced security mode Security primitives are started before making any request for a channel is initiated and the ACL link is established.
- 4.
- Service-level enforced security mode (SSP) This is similar to service-level enforced security mode; the only difference is that only the Bluetooth devices that use secure simple pairing (SSP) can be set in this mode.
802.11 Security
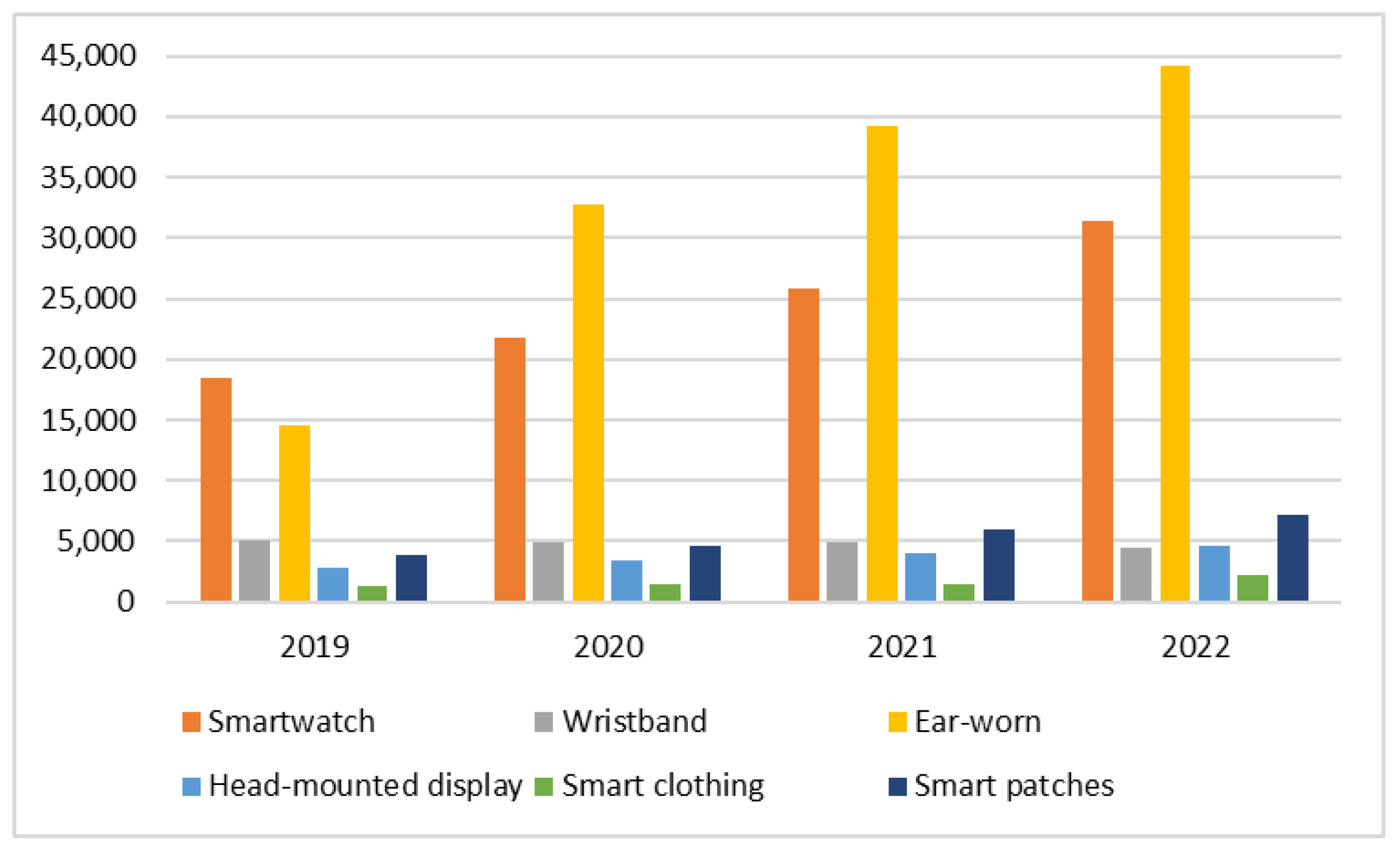
3. WBAN Economical Issues
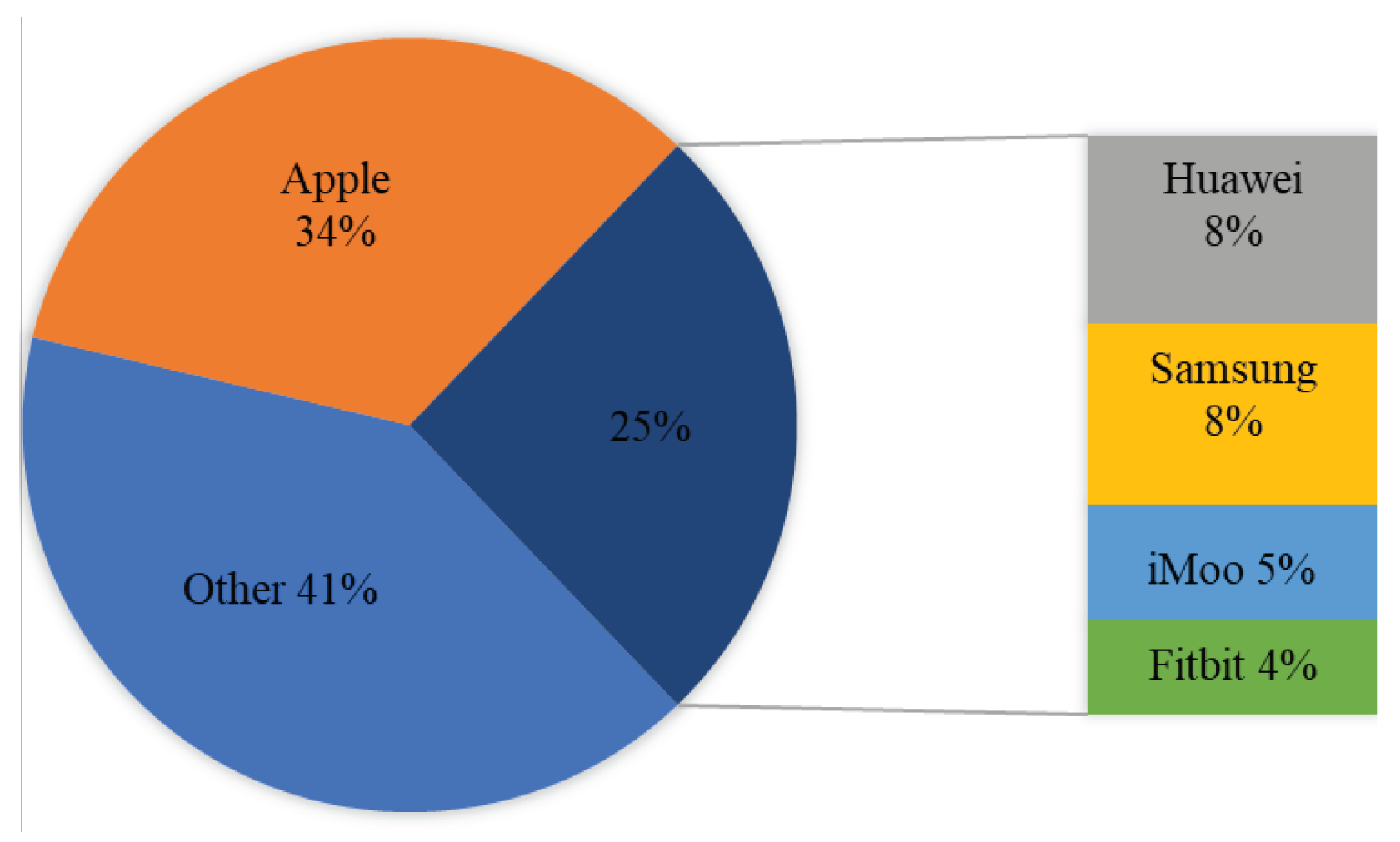
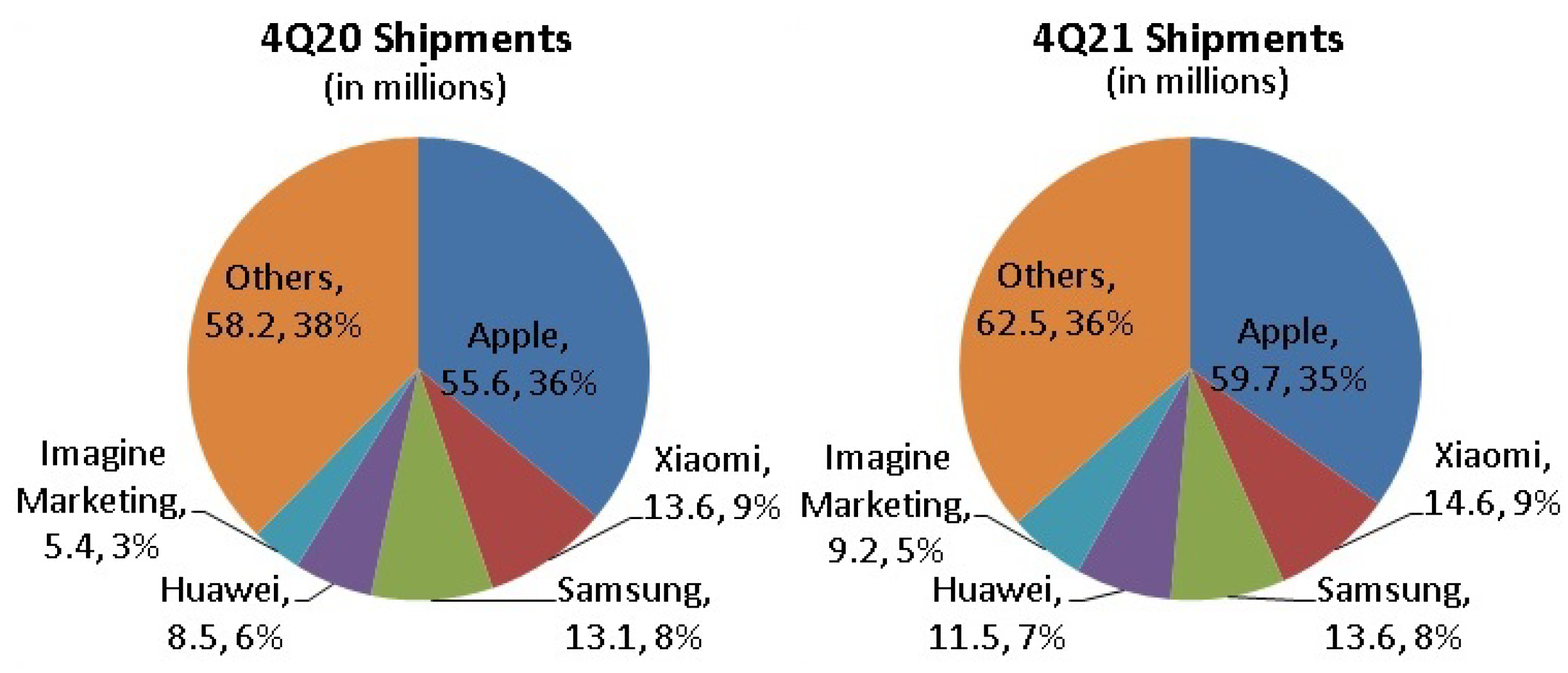
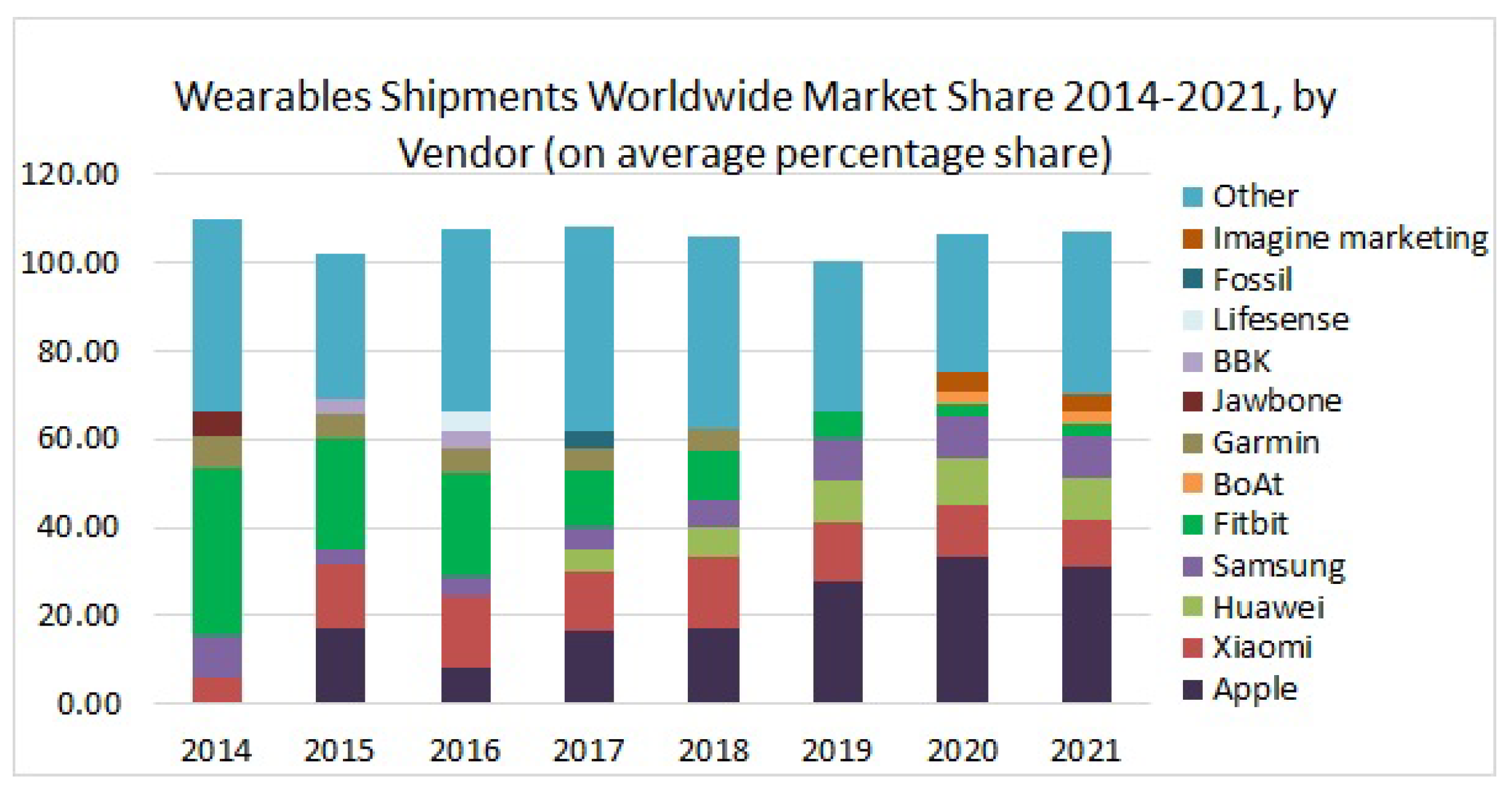
3.1. WBAN/Wearable Compound Annual Growth Rate
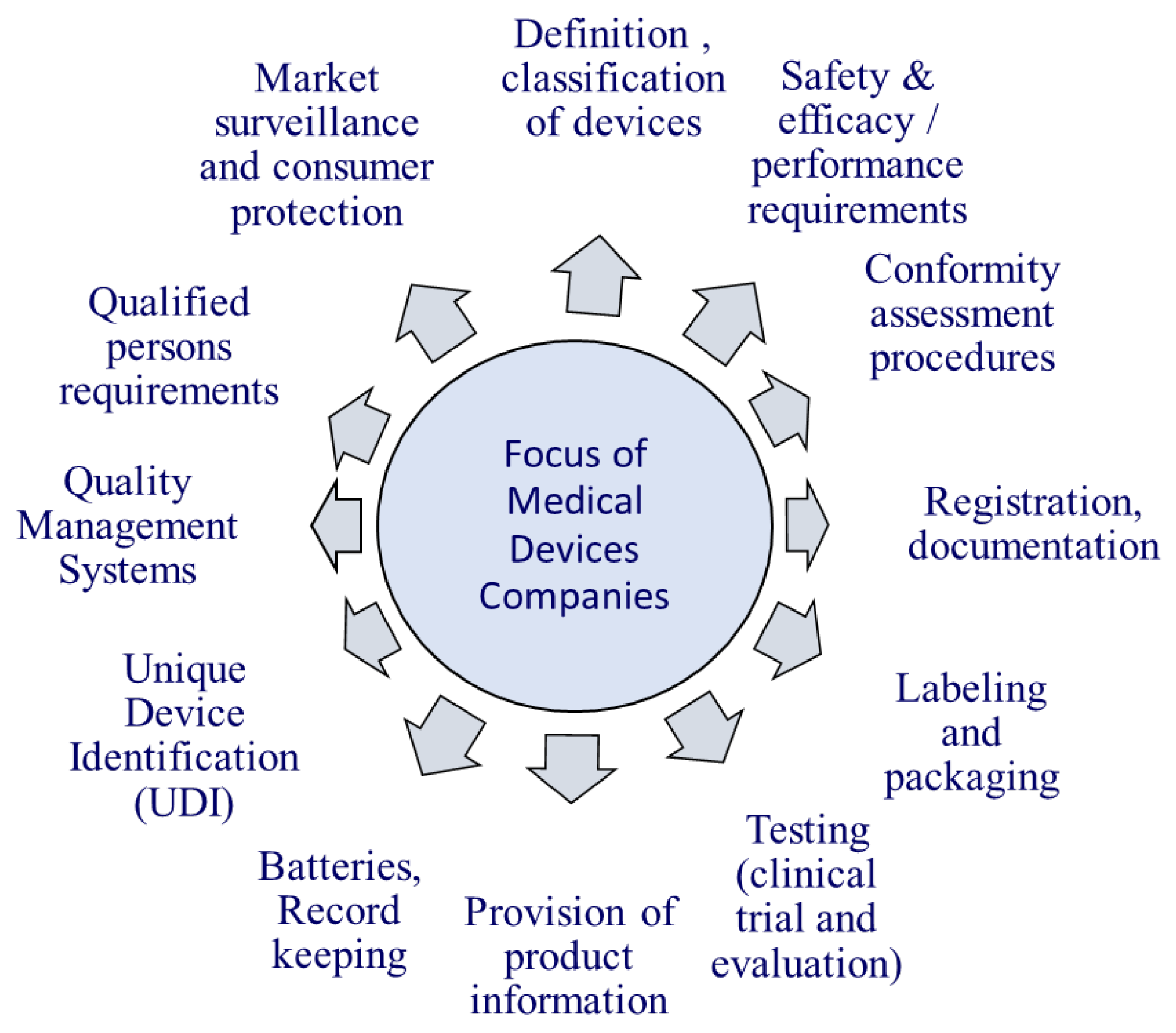
3.2. WEARABLE/WBAN Regulatory for Body
3.3. WEARABLE/WBAN Feasible Projects
4. Open Issues
4.1. Research Challenges
4.1.1. Security vs. Efficiency
4.1.2. Security vs. Safety
4.1.3. Security vs. Usability
4.1.4. Device Interoperability
4.1.5. Device Authentication
4.1.6. Secret Key Acquisition
4.1.7. Strict Regulations
4.2. Research Directions
- 1.
- Global RF Design: The Radio Frequency of the Wireless Wearable BAN must be such that the devices can operate in any part of the world because it is observed that some wireless channels are allowed to operate in the USA but not in other parts of the world or some channels are used in one part of the world but not in other. Thus, RF design must be able to cope with heterogeneous wearable BAN devices [38].
- 2.
- Performance: Other high-power ISM wireless devices operating in the surrounding may degrade the performance of low-power wearable and WBAN devices making them less attractive and appealing for high-quality medical and healthcare applications. For instance, Wireless Medical Telemetry Service (WMTS) frequency bands are extensively being used, but unfortunately, their use is limited to healthcare applications in the USA. Moreover, UWB is a good candidate technology for wireless wearable devices, but at the same time, it is badly affected by the interference of the co-existence of high data rate applications such as wireless multi-media.
- 3.
- 2360–2400 MHz Band: Federal Communication Commission (FCC) has opened the 2360–2400 MHz band for medical WBAN. It is believed that the band will be used to devise an artificial nervous system to reinstate sensation and mobility and regain the functionality of paralyzed limbs and organs. However, the devices based on this medical WBAN frequency band are required to test and validate against the FCC health-related rules and regulations [231]. Therefore, designing devices that exactly meet the FCC regulations is also one of the great challenges.
- 4.
- Channel Model Design: Another research challenge is the designing of the RF channel model because it plays an important part in the designing of PHY (Physical Layer) technologies. PHY is an abbreviation of the Physical Layer of TCP/IP or OSI Model. PHY is implemented to connect the MAC layer with the physical medium; in this, it is a wireless Radio Frequency (RF). PHY consists of RF, Transceiver, DSP (Digital Signal Processor), communication protocol, and channel codes. PHY is integrated with MAC in SOC (System on a Chip) technology. Examples of wireless PHY are 3G, 4G, LTE, WiMAX, and UWB.
- 5.
- Radio Antenna Design: Designing an antenna for wireless wearable BAN devices is also very critical due to restrictions on size, shape and choice of material [232,233]. Since the devices are wearable, patched on the body or implanted inside the body, the size of these antennae must be miniaturized. Designers do not have too many choices for the shape of antennae; it is the organ that puts restrictions on the shape. The material that can be used to design antennae should be harmless for the human body such as titanium or platinum. However, antennae made of such material result in low performance when compared with the antennae made up of copper.
- 6.
- Physical Layer Protocols: Physical layer protocols of wearable and BAN devices must assure low power consumption without compromising reliability, connectivity, throughput and turnaround time [5,38]. Fast wake-up from sleep mode and speedy turnaround time can significantly save the power of wearable/WBAN devices. Presently, energy efficiency is being achieved through duty cycling, but researchers are endeavoring to find new ways of energy saving such as low-power listening harvesting [234].
- 7.
- MAC Design: It is always required to have a wearable BAN MAC (Medium Access Control) layer that should be resilient to interference experienced due to the co-existence of multiple WBANs in crowded areas such as hospitals. MAC layer protocols should be adaptable to frequent topology changes. Moreover, MAC protocol of the WBAN should be able to switch to a silent channel in the case of severe interference due to the co-existence of similar networks operating in the surrounding using the same frequency band [38].
4.3. Emerging Techniques in WBAN
4.3.1. Human Body Communication (HBC)
4.3.2. Energy Harvesting
4.3.3. Quantum Computing
4.3.4. Graph Neural Networks (GNN)
4.4. Artificial Intelligence: Machine and Deep Learning
4.4.1. Blockchain
4.4.2. Digital Twins
5. Conclusions and Future Work
- 1.
- Wireless wearable BAN devices are one of the marvelous inventions in human history that improves the apex quality of human life.
- 2.
- There is great investment potential in the global industry of wireless body area networks that have also been observed from the different CAGR values reported in many global market analysis reports.
- 3.
- On the other hand, a lot of work is still required to make those devices whose manufacturing ingredients involve radio or electromagnetic waves and frequencies safe for the living body cells and tissues.
- 4.
- Wireless body area networks consist of very low-resource devices, which is why it is demanded that communication and security protocols must be light in computation, storage, and transmission because these factors are directly linked with the lifetime of BAN nodes as they are battery powered.
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Xiao, Y.; Pan, Y. Emerging Wireless LANs, Wireless PANs, and Wireless MANs: IEEE 802.11, IEEE 802.15, 802.16 Wireless Standard Family; Wiley: Hoboken, NJ, USA, 2009. [Google Scholar]
- AlShourbaji, I. An Overview of Wireless Local Area Network (WLAN). arXiv 2013, arXiv:1303.1882. [Google Scholar]
- Catherwood, P.A.; Steele, D.; Little, M.; Mccomb, S.; Mclaughlin, J. A Community-Based IOT Personalized Wireless Healthcare Solution Trial. IEEE J. Transl. Eng. Health Med. 2018, 6, 372–380. [Google Scholar] [CrossRef]
- Tufail, F.; Islam, M.H. Wearable Wireless Body Area Networks. In Proceedings of the 2009 International Conference on Information Management and Engineering, Kuala Lumpur, Malaysia, 3–5 April 2009; pp. 656–660. [Google Scholar] [CrossRef]
- Ometov, A.; Shubina, V.; Klus, L.; Skibińska, J.; Saafi, S.; Pascacio, P.; Flueratoru, L.; Gaibor, D.Q.; Chukhno, N.; Chukhno, O.; et al. A Survey on Wearable Technology: History, State-of-the-Art and Current Challenges. Comput. Netw. 2021, 193, 108074. [Google Scholar] [CrossRef]
- Latré, B.; Braem, B.; Moerman, I.; Blondia, C.; Demeester, P. A Survey on Wireless Body Area Networks. Wirel. Netw. 2011, 17, 1–18. [Google Scholar] [CrossRef]
- Ullah, S.; Higgins, H.; Braem, B.; Latre, B.; Blondia, C.; Moerman, I.; Saleem, S.; Rahman, Z.; Kwak, K.S. A Comprehensive Survey of Wireless Body Area Networks. J. Med. Syst. 2012, 36, 1065–1094. [Google Scholar] [CrossRef] [PubMed]
- Revadigar, G.; Javali, C.; Asghar, H.J.; Rasmussen, K.B.; Jha, S. Mobility Independent Secret Key Generation for Wearable Health-care Devices. In Proceedings of the 10th EAI International Conference on Body Area Networks, Oulu, Finland, 2–3 October 2018; ICST (Institute for Computer Sciences, Social-Informatics and Telecommunications Engineering): Brussels, Belgium, 2015. BodyNets ’15. pp. 294–300. [Google Scholar] [CrossRef]
- Revadigar, G.; Javali, C.; Asghar, H.J.; Rasmussen, K.B.; Jha, S. Secret Key Generation for Body-worn Devices by Inducing Artificial Randomness in the Channel. Tech. Rep. 2015. [Google Scholar]
- Al-Eidan, R.M.; Al-Khalifa, H.; Al-Salman, A.M. A Review of Wrist-Worn Wearable: Sensors, Models, and Challenges. J. Sens. 2018, 2018, 1–20. [Google Scholar] [CrossRef]
- Kwak, K.S.; Ameen, M.A.; Kwak, D.; Lee, C.; Lee, H. A study on proposed IEEE 802.15 WBAN MAC protocols. In Proceedings of the 2009 9th International Symposium on Communications and Information Technology, Icheon, Korea, 28–30 September 2009; pp. 834–840. [Google Scholar] [CrossRef]
- is Promo, J. Samsung Health In-depth Tutorial (Previously S Health). 2019. Available online: https://www.youtube.com/watch?v=0UQ6xz0_wPA (accessed on 28 October 2021).
- Miller, K. Got a Cold? Your Smartwatch Can Detect It before You Do. 2021. Available online: https://www.verywellhealth.com/wearable-health-technology-detect-illness-5204814 (accessed on 26 January 2022).
- Lambert, V. Empowering Patients to Track Their Health through Wearable Tech. Ph.D. Dissertation. 2016. Available online: https://www.raconteur.net/empowering-patients-to-track-their-health-through-wearable-tech/ (accessed on 17 November 2021).
- Research; Markets. Global Wearables Market Anticipated to Reach US $116.88 Billion by 2025, Growing at a CAGR of 17% between 2021 and 2025. 2021. Available online: https://www.businesswire.com/news/home/20210930005681/en/Global-Wearables-Market-Anticipated-to-Reach-US116.88-Billion-by-2025-Growing-at-a-CAGR-of-17-Between-2021-and-2025—ResearchAndMarkets.com (accessed on 18 November 2021).
- Siddiqi, M. Securing the Provenance of Wearable Healthcare Sensing Data. Ph.D. Dissertation, University of New South Wales, Sydney, Australia, 2019. [Google Scholar]
- Vijayan, V.; Connolly, J.P.; Condell, J.; McKelvey, N.; Gardiner, P. Review of Wearable Devices and Data Collection Considerations for Connected Health. Sensors 2021, 21, 5589. [Google Scholar] [CrossRef]
- Hajar, M.S.; Al-Kadri, M.O.; Kalutarage, H.K. A survey on wireless body area networks: Architecture, security challenges and research opportunities. Comput. Secur. 2021, 104, 102211. [Google Scholar] [CrossRef]
- Kim, B.S.; Shah, B.; He, T.; Kim, K.I. A survey on analytical models for dynamic resource management in wireless body area networks. Ad Hoc Netw. 2022, 135, 102936. [Google Scholar] [CrossRef]
- Kim, B.S.; Shah, B.; Kim, K.I. Resource Allocation in Wireless Body Area Networks: A Smart City Perspective. In Emerging Trends in Wireless Sensor Networks; IntechOpen: London, UK, 2022. [Google Scholar] [CrossRef]
- Bouani, A.; Maissa, Y.; Rachid, S.; Hammouch, A.; Tamtaoui, A. A Comprehensive Survey of Medium Access Control Protocols for Wireless Body Area Networks. Wirel. Commun. Mob. Comput. 2021, 2021. [Google Scholar] [CrossRef]
- Celik, A.; Salama, K.N.; Eltawil, A.M. The Internet of Bodies: A Systematic Survey on Propagation Characterization and Channel Modeling. IEEE Internet Things J. 2022, 9, 321–345. [Google Scholar] [CrossRef]
- Zhong, L.; He, S.; Lin, J.; Wu, J.; Li, X.; Pang, Y.; Li, Z. Technological Requirements and Challenges in Wireless Body Area Networks for Health Monitoring: A Comprehensive Survey. Sensors 2022, 22, 3539. [Google Scholar] [CrossRef]
- Dias, D.; Cunha, J.P. Wearable Health Devices? Vital Sign Monitoring, Systems and Technologies. Sensors 2018, 18, 2414. [Google Scholar] [CrossRef] [PubMed]
- Pramanik, P.K.D.; Nayyar, A.; Pareek, G. Chapter 7—WBAN: Driving e-healthcare Beyond Telemedicine to Remote Health Monitoring: Architecture and Protocols. In Telemedicine Technologies; Jude, H.D., Balas, V.E., Eds.; Academic Press: Cambridge, MA, USA, 2019; pp. 89–119. [Google Scholar] [CrossRef]
- Singh, R.; Gaonkar, M.V.; Sharma, S.; Grover, P.; Khatri, A. Introduction To Body Sensor Networks. In Proceedings of the 2019 International Conference on Machine Learning, Big Data, Cloud and Parallel Computing (COMITCon), Faridabad, India, 14–16 February 2019; pp. 437–440. [Google Scholar] [CrossRef]
- Patel, B.C.; Sinha, G.R.; Goel, N. Introduction to sensors. In Advances in Modern Sensors; IOP Publishing: Philadelphia, PA, USA, 2020; pp. 1–21. [Google Scholar] [CrossRef]
- Gambhir, S.; Kathuria, M. DWBAN: Dynamic priority based WBAN architecture for healthcare system. In Proceedings of the 2016 3rd International Conference on Computing for Sustainable Global Development (INDIACom), New Delhi, India, 16–18 March 2016; pp. 3380–3386. [Google Scholar]
- Karthikeyan, S.; Gopal, Y.; Kumar, V. Design and Analysis of Wearable Antenna for Wireless Body Area Network. IOP Conf. Ser. Mater. Sci. Eng. 2019, 590, 012022. [Google Scholar] [CrossRef]
- Yazdandoost, K.Y.; Kohno, R. UWB antenna for wireless body area network. In Proceedings of the 2006 Asia-Pacific Microwave Conference, November 2006; pp. 1647–1652. [Google Scholar] [CrossRef]
- Zhang, K.; Soh, P.J.; Yan, S. Meta-Wearable Antennas—A Review of Metamaterial Based Antennas in Wireless Body Area Networks. Materials 2021, 14, 149. [Google Scholar] [CrossRef]
- Sudha, M.; Benitta, S. Design of antenna in Wireless Body Area Network (WBAN) for biotelemetry applications. Intell. Decis. Technol. 2016, 10, 1–7. [Google Scholar] [CrossRef]
- Van, D.D.; Ai, Q.; Liu, Q. Vertical Handover Algorithm for WBANs in Ubiquitous Healthcare with Quality of Service Guarantees. Information 2017, 8, 34. [Google Scholar] [CrossRef]
- Elhadj, H.; Elias, J.; Fourati, L.; Kamoun, L. Multi Attribute Decision Making Handover Algorithm for Wireless Body Area Networks. Comput. Commun. 2016, 81. [Google Scholar] [CrossRef]
- Park, J.T.; Nah, J.W.; Kim, S.W.; Chun, S.M.; Wang, S.; Seo, S.H. Context-Aware Handover with Power Efficiency for u-Healthcare Service in WLAN. In Proceedings of the 2009 International Conference on New Trends in Information and Service Science, Beijing, China, 30 June–2 July 2009; pp. 1279–1283. [Google Scholar] [CrossRef]
- Dahal, S.; Shin, S. A Review on Vertical Handover Schemes to Integrate WBAN with Other Heterogeneous Networks. Korean Inst. Next Gener. Comput. 2015, 11, 29–40. [Google Scholar]
- Lav Gupta, R.J. Security in Low Energy Body Area Networks for Healthcare. A Paper Written under the Guidance of Prof. Raj Jain. Washington University of St. Louis. 2014. Available online: https://www.cse.wustl.edu/~jain/cse571-14/ftp/ban.pdf (accessed on 4 March 2022).
- Salayma, M.; Al-Dubai, A.; Romdhani, I.; Nasser, Y. Wireless Body Area Network (WBAN): A Survey on Reliability, Fault Tolerance, and Technologies Coexistence. ACM Comput. Surv. 2017, 50, 3041956. [Google Scholar] [CrossRef]
- Kiourti, A.; Nikita, K.S. A Review of In-Body Biotelemetry Devices: Implantables, Ingestibles, and Injectables. IEEE Trans. Biomed. Eng. 2017, 64, 1422–1430. [Google Scholar] [CrossRef]
- Ullah, S.; Higgin, H.; Siddiqui, M.A.; Kwak, K.S. A Study of Implanted and Wearable Body Sensor Networks. In Agent and Multi-Agent Systems: Technologies and Applications; Nguyen, N.T., Jo, G.S., Howlett, R.J., Jain, L.C., Eds.; Springer: Berlin/Heidelberg, Germany, 2008; pp. 464–473. [Google Scholar]
- Khan, P.; Hussain, A.; Kwak, K. Medical Applications of Wireless Body Area Networks. JDCTA 2009, 3, 185–193. [Google Scholar] [CrossRef]
- Darwish, A.; Hassanien, A.E. Wearable and implantable wireless sensor network solutions for healthcare monitoring. Sensors 2011, 11, 5561–5595. [Google Scholar] [CrossRef] [PubMed]
- Machiele, R.; Motlagh, M.; Patel, B.C. Intraocular Pressure. In StatPearls; StatPearls Publishing: Treasure Island, FL, USA, 2021. [Google Scholar]
- Tran, L.G.; Cha, H.K.; Park, W.T. RF power harvesting: A review on designing methodologies and applications. Micro Nano Syst. Lett. 2017, 5, 14. [Google Scholar] [CrossRef]
- Xiang, W.; Xie, Y.; Han, Y.; Long, Z.; Zhang, W.; Zhong, T.; Liang, S.; Xing, L.; Xue, X.; Zhan, Y. A self-powered wearable brain–machine-interface system for ceasing action. Nanoscale 2022, 14, 4671–4678. [Google Scholar] [CrossRef]
- Johnston, L.; Wang, G.; Hu, K.; Qian, C.; Liu, G. Advances in Biosensors for Continuous Glucose Monitoring Towards Wearables. Front. Bioeng. Biotechnol. 2021, 9, 733810. [Google Scholar] [CrossRef]
- Sanchez, P.; Ghosh-Dastidar, S.; Tweden, K.S.; Kaufman, F.R. Real-World Data from the First U.S. Commercial Users of an Implantable Continuous Glucose Sensor. Diabetes Technol. Ther. 2019, 21, 677–681. [Google Scholar] [CrossRef]
- Renard. Implantable glucose sensors for diabetes monitoring. Minim. Invasive Ther. Allied. Technol. 2004, 13, 78–86. [Google Scholar] [CrossRef]
- Veeramuthu, L.; Cho, C.J.; Venkatesan, M.; Kumar, G.R.; Hsu, H.Y.; Zhuo, B.X.; Kau, L.J.; Chung, M.A.; Lee, W.Y.; Kuo, C.C. Muscle fibers inspired electrospun nanostructures reinforced conductive fibers for smart wearable optoelectronics and energy generators. Nano Energy 2022, 101, 107592. [Google Scholar] [CrossRef]
- New Orleans Profusa Inc. Injectable Body Sensors Take Personal Chemistry to a Cell Phone Closer to Reality. Tech Report. 2018. Available online: https://profusa.com/injectable-body-sensors-take-personal-chemistry-to-a-cell-phone-closer-to-reality/ (accessed on 28 March 2022).
- Somers, R.C.; Lanning, R.M.; Snee, P.T.; Greytak, A.B.; Jain, R.K.; Bawendi, M.G.; Nocera, D.G. A nanocrystal-based ratiometric pH sensor for natural pH ranges. Chem. Sci. 2012, 3, 2980–2985. [Google Scholar] [CrossRef] [PubMed]
- Bai, W.; Kuang, T.; Chitrakar, C.; Yang, R.; Li, S.; Zhu, D.; Chang, L. Patchable micro/nanodevices interacting with skin. Biosens. Bioelectron. 2018, 122, 189–204. [Google Scholar] [CrossRef] [PubMed]
- Shetti, N.P.; Mishra, A.; Basu, S.; Mascarenhas, R.J.; Kakarla, R.R.; Aminabhavi, T.M. Skin-Patchable Electrodes for Biosensor Applications: A Review. ACS Biomater. Sci. Eng. 2020, 6, 1823–1835. [Google Scholar] [CrossRef] [PubMed]
- Manasa, G.; Mascarenhas, R.J.; Shetti, N.P.; Malode, S.J.; Mishra, A.; Basu, S.; Aminabhavi, T.M. Skin Patchable Sensor Surveillance for Continuous Glucose Monitoring. ACS Appl. Bio. Mater. 2022, 5, 945–970. [Google Scholar] [CrossRef]
- Baek, D.; Lee, H.G.; Chang, N. SmartPatch: A Self-Powered and Patchable Cumulative UV Irradiance Meter. IEEE Des. Test 2019, 36, 57–64. [Google Scholar] [CrossRef]
- Wang, X.; Zhou, X.; Liu, Z.; Fan, X. A Survey on Patchable Sensors. In Proceedings of the 2020 IEEE 4th International Conference on Frontiers of Sensors Technologies (ICFST), Shanghai, China, 6–9 November 2020; pp. 39–43. [Google Scholar] [CrossRef]
- Joshi, M.; Archer, S.; Morbi, A.; Arora, S.; Kwasnicki, R.; Ashrafian, H.; Khan, S.; Cooke, G.; Darzi, A. Short-Term Wearable Sensors for In-Hospital Medical and Surgical Patients: Mixed Methods Analysis of Patient Perspectives. JMIR Perioper Med. 2021, 4, e18836. [Google Scholar] [CrossRef]
- Hartel, M.C.; Lee, D.; Weiss, P.S.; Wang, J.; Kim, J. Resettable sweat-powered wearable electrochromic biosensor. Biosens. Bioelectron. 2022, 215, 114565. [Google Scholar] [CrossRef]
- Taleb, H.; Nasser, A.; Andrieux, G.; Charara, N.; Motta Cruz, E. Wireless technologies, medical applications and future challenges in WBAN: A survey. Wirel. Netw. 2021, 27, 5271–5295. [Google Scholar] [CrossRef]
- WHO. Pulse Oximetry Training Manual. WHO Library Cataloguing-in-Publication Data. 2011. Available online: https://www.who.int/patientsafety/safesurgery/pulse_oximetry/who_ps_pulse_oxymetry_training_manual_en.pdf (accessed on 8 November 2021).
- WHO. Using Pulse Oximeters. 2011. Available online: https://www.who.int/patientsafety/safesurgery/pulse_oximetry/who_ps_pulse_oxymetry_tutorial1_the_basics_en.pdf (accessed on 8 November 2021).
- Chan, E.D.; Chan, M.M.; Chan, M.M. Pulse oximetry: Understanding its basic principles facilitates appreciation of its limitations. Respir. Med. 2013, 107, 789–799. [Google Scholar] [CrossRef]
- Wellue. Wellue® O2TM Ring Continuous Ring Oxygen Monitor. Available online: https://getwellue.com/products/o2ring-wearable-pulse-oximeter (accessed on 26 January 2022).
- Zhou, Z.; Chen, N.; Zhong, H.; Zhang, W.; Zhang, Y.; Yin, X.; He, B. Textile-Based Mechanical Sensors: A Review. Materials 2021, 14, 6074. [Google Scholar] [CrossRef]
- Gulzar, U.; De angelis, F.; Zaccaria, R.; Capiglia, C. Recent Advances in Textile Based Energy Storage Devices. World J. Eng. Technol. 2016, 2, 6–15. [Google Scholar]
- Shak Sadi, M.; Kumpikaitė, E. Advances in the Robustness of Wearable Electronic Textiles: Strategies, Stability, Washability and Perspective. Nanomaterials 2022, 12, 2039. [Google Scholar] [CrossRef] [PubMed]
- Kota, A.; Gogia, A.; Neidhard-Doll, A.T.; Chodavarapu, V.P. Printed Textile-Based Ag2O–Zn Battery for Body Conformal Wearable Sensors. Sensors 2021, 21, 2178. [Google Scholar] [CrossRef]
- Mohanty, S.P. Biosensors: A Survey Report. 2001. Available online: https://www.researchgate.net/publication/2531450_Biosensors_A_Survey_Report (accessed on 8 November 2021).
- Naresh, V.; Lee, N. A Review on Biosensors and Recent Development of Nanostructured Materials-Enabled Biosensors. Sensors 2021, 21, 1109. [Google Scholar] [CrossRef] [PubMed]
- Hayajneh, T.; Almashaqbeh, G.; Ullah, S.; Vasilakos, A.V. A Survey of Wireless Technologies Coexistence in WBAN: Analysis and Open Research Issues. Wirel. Netw. 2014, 20, 2165–2199. [Google Scholar] [CrossRef]
- Fan Wu, T.W.; Yuce, M.R. An Internet-of-Things (IOT) Network System for Connected Safety and Health Monitoring Applications. Sensors 2019, 19, 21. [Google Scholar]
- Seneviratne, S.; Hu, Y.; Nguyen, T.; Lan, G.; Khalifa, S.; Thilakarathna, K.; Hassan, M.; Seneviratne, A. A Survey of Wearable Devices and Challenges. IEEE Commun. Surv. Tutor. 2017, 19, 2573–2620. [Google Scholar] [CrossRef]
- Sarangi, M.; Debabrata Singh, M.K. A Challenging Solution for Man-in-Middle Security Issues through Near Field Communication (NFC). Int. J. Eng. Adv. Technol. (IJEAT) 2019, 8, 963–983. [Google Scholar]
- Khan, R.A.; Pathan, A.S.K. The state-of-the-art wireless body area sensor networks: A survey. Int. J. Distrib. Sens. Netw. 2018, 14, 1550147718768994. [Google Scholar] [CrossRef]
- Wong, A.W.; McDonagh, D.; Omeni, O.; Nunn, C.; Hernandez-Silveira, M.; Burdett, A.J. Sensium: An ultra-low-power wireless body sensor network platform: Design & application challenges. Annu. Int. Conf. IEEE Eng. Med. Biol. Soc. 2009, 2009, 6576–6579. [Google Scholar]
- Kołodziej, J.; Gonzalez-Velez, H.; Karatza, H. High-performance modelling and simulation for big data applications. Simul. Model. Pract. Theory 2017, 76. [Google Scholar] [CrossRef]
- Victor, C.M.L.; Huasong Cao, C.C.H.C. Enabling Technologies for Wireless Body Area Networks: A Survey and Outlook. IEEE Commun. Mag. 2009, 47, 84–93. [Google Scholar] [CrossRef]
- Arefin, M.T.; Ali, M.H.; Haque, A.K.M.F. Wireless Body Area Network: An Overview and Various Applications. J. Comput. Commun. 2017, 5, 53–64. [Google Scholar] [CrossRef]
- Negra, R.; Jemili, I.; Belghith, A. Wireless body area networks: Applications and technologies. Procedia Comput. Sci. 2016, 83, 1274–1281. [Google Scholar] [CrossRef]
- Dementyev, A.; Hodges, S.; Taylor, S.; Smith, J. Power consumption analysis of Bluetooth Low Energy, ZigBee and ANT sensor nodes in a cyclic sleep scenario. In Proceedings of the 2013 IEEE International Wireless Symposium (IWS), Beijing, China, 14–18 April 2013; pp. 1–4. [Google Scholar] [CrossRef]
- Kshetrimayum, R.S. An introduction to UWB communication systems. IEEE Potentials 2009, 28, 9–13. [Google Scholar] [CrossRef]
- Batra, A.; Balakrishnan, J.; Dabak, A. Multi-band OFDM: A new approach for UWB. In Proceedings of the 2004 IEEE International Symposium on Circuits and Systems, Vancouver, BC, Canada, 23–26 May 2004. [Google Scholar] [CrossRef]
- Fernandes, J.R.; Wentzloff, D. Recent advances in IR-UWB transceivers: An overview. In Proceedings of the 2010 IEEE International Symposium on Circuits and Systems, Paris, France, 30 May–2 June 2010; pp. 3284–3287. [Google Scholar] [CrossRef]
- Sundaram, J.P.S.; Du, W.; Zhao, Z. A Survey on LoRa Networking: Research Problems, Current Solutions and Open Issues. arXiv 2019, arXiv:1908.10195. [Google Scholar] [CrossRef]
- You, I.; Kwon, S.; Choudhary, G.; Sharma, V.; Seo, J. An Enhanced LoRaWAN Security Protocol for Privacy Preservation in IOT with a Case Study on a Smart Factory-Enabled Parking System. Sensors 2018, 18, 1888. [Google Scholar] [CrossRef] [PubMed]
- Movassaghi, S.; Ara, P.; Abolhasan, M. Wireless technologies for Body Area Networks: Characteristics and challenges. In Proceedings of the 2012 International Symposium on Communications and Information Technologies (ISCIT), Gold Coast, QLD, Australia, 2–5 October 2012. [Google Scholar] [CrossRef]
- Sun, H.; Zhang, Z.; Hu, R.Q.; Qian, Y. Wearable Communications in 5G: Challenges and Enabling Technologies. IEEE Veh. Technol. Mag. 2018, 13, 100–109. [Google Scholar] [CrossRef]
- Lin, J.; Shen, Z.; Miao, C. Using Blockchain Technology to Build Trust in Sharing LoRaWAN IoT. In Proceedings of the 2nd International Conference on Crowd Science and Engineering, Beijing, China, 6–9 July 2017; pp. 38–43. [Google Scholar] [CrossRef]
- Tavera, C.A.; Ortiz, J.H.; Khalaf, O.I.; Saavedra, D.F.; Aldhyani, T.H.H. Wearable Wireless Body Area Networks for Medical Applications. Comput. Math. Methods Med. 2021, 2021, 5574376. [Google Scholar] [CrossRef]
- Cavallari, R.; Martelli, F.; Rosini, R.; Buratti, C.; Verdone, R. A Survey on Wireless Body Area Networks: Technologies and Design Challenges. IEEE Commun. Surv. Tutor. 2014, 16, 1635–1657. [Google Scholar] [CrossRef]
- Meharouech, A.; Elias, J.; Mehaoua, A. Moving Towards Body-to-Body Sensor Networks for Ubiquitous Applications: A Survey. J. Sens. Actuator Netw. 2019, 8, 27. [Google Scholar] [CrossRef]
- Alam, M.M.; Hamida, E.B. Review Surveying Wearable Human Assistive Technology for Life and Safety Critical Applications: Standards, Challenges and Opportunities. Sensors 2014, 14, 9153–9209. [Google Scholar] [CrossRef] [PubMed]
- Christensen, B. Army Wrist Display Uses 4.3 Inch OLED, US Department of Defence. 2010. Available online: http://www.technovelgy.com/ct/Science-Fiction-News.asp?NewsNum=3052 (accessed on 28 October 2021).
- Shi, H.; Zhao, H.; Liu, Y.; Gao, W.; Dou, S.C. Systematic Analysis of a Military Wearable Device Based on a Multi-Level Fusion Framework: Research Directions. Sensors 2019, 19, 2651. [Google Scholar] [CrossRef]
- Liu, W.; Long, Z.; Yang, G.; Xing, L. A Self-Powered Wearable Motion Sensor for Monitoring Volleyball Skill and Building Big Sports Data. Biosensors 2022, 12, 60. [Google Scholar] [CrossRef] [PubMed]
- Chatterjee, A.; Aceves, A.; Dungca, R.; Flores, H.; Giddens, K. Classification of wearable computing: A survey of electronic assistive technology and future design. In Proceedings of the 2016 Second International Conference on Research in Computational Intelligence and Communication Networks (ICRCICN), Kolkata, India, 23–25 September 2016; pp. 22–27. [Google Scholar]
- Iqbal, M.H.; Aydin, A.; Brunckhorst, O.; Dasgupta, P.; Ahmed, K. A review of wearable technology in medicine. J. R. Soc. Med. 2016, 109, 372–380. [Google Scholar] [CrossRef]
- Sotera Wireless, Inc. Continuous Monitoring of Key Bodily Functions Improves Patient Safety 32% Fewer Unplanned ICU Admissions Thanks to Wrist Monitor. 2022. Available online: https://www.soterawireless.com/news/continuous-monitoring-of-key-bodily-functions-improves-patient-safety-32-fewer-unplanned-icu-admissions-thanks-to-wrist-monitor (accessed on 25 April 2022).
- Phillips, BioTel Heart. Mobile Cardiac Telemetry: Beat-by-Beat Analysis and Automatic Event Detection, with Wireless Transmission. Available online: https://www.myheartmonitor.com/ (accessed on 20 January 2019).
- Medic, G.; Kotsopoulos, N.; Connolly, M.P.; Lavelle, J.; Norlock, V.; Wadhwa, M.; Mohr, B.A.; Derkac, W.M. Mobile Cardiac Outpatient Telemetry Patch vs Implantable Loop Recorder in Cryptogenic Stroke Patients in the US—Cost-Minimization Model. Med. Devices (Auckl) 2021, 14, 445–458. [Google Scholar] [CrossRef] [PubMed]
- Ambio Health, Inc. Starter Kit Single Devices. Available online: https://ambiohealth.com/products (accessed on 20 January 2019).
- INC, A.G. Providing Caregivers Better Patient Assessment. Available online: https://athenagtx.com/products/ (accessed on 20 January 2019).
- Caretaker. Healthcare Benefits: Caretaker Helps Modernize Healthcare. Available online: https://www.caretakermedical.net/ (accessed on 20 January 2019).
- Scientific, C. Wireless Vital Signs Monitoring. 2017. Available online: https://cadi.com.sg/2016/11/12/wireless-vital-signs-monitoring/ (accessed on 20 January 2019).
- Connect, V. Vital Patch RTM. Available online: https://vitalconnect.com (accessed on 20 January 2019).
- Westenberg, J. Fitbit Premium Review: Is It Worth It? 2022. Available online: https://www.androidauthority.com/fitbit-premium-review-1097663/ (accessed on 10 February 2022).
- Garmin. Fitness at Your Fingertips. Available online: https://connect.garmin.com/#:~:text=On%20mobile%20or%20web%2C%20Garmin,activities%20from%20your%20Garmin%20device. (accessed on 10 November 2021).
- SamSung. Enhance Your Life with Samsung Health. Available online: https://www.samsung.com/global/galaxy/apps/samsung-health/ (accessed on 28 October 2021).
- Apple. Apple Health Kit. Available online: https://developer.apple.com/documentation/healthkit (accessed on 28 November 2021).
- Radiofrequency Wireless ICD, Heart Failure Devices FDA Approved. 2014. Available online: https://www.dicardiology.com/product/radiofrequency-wireless-icd-heart-failure-devices-fda-approved-0 (accessed on 10 November 2021).
- Katwal, A.B.; McCotter, C.J. Use of a Wireless Implantable Cardioverter Defibrillator in a Patient with a Preexisting Neurostimulator. Pacing Clin. Electrophysiol. 2009, 32, 822–824. [Google Scholar] [CrossRef] [PubMed]
- Burri, H.; Senouf, D. Remote Monitoring and Follow-Up of Pacemakers and Implantable Cardioverter Defibrillators. EP Eur. 2009, 11, 701–709. [Google Scholar] [CrossRef]
- Scientific, B. Boston Scientific Electromagnetic (EMI) Compatibility Table for Pacemakers, Transvenous ICDs, S-ICDs and Heart Failure Devices. Tech Guide. 2017. Available online: https://www.bostonscientific.com/content/dam/lifebeat-online/en/documents/BSC_Electromagnetic_Compatibility_Guide.pdf (accessed on 14 April 2022).
- BIOTRONIK. Electromagnetic Compatibility of BIOTRONIK Cardiac Pacemakers, ICDs and CRT Devices. 2017. Available online: https://biotronik.cdn.mediamid.com/cdn_bio_doc/bio23016/8207/bio23016.pdf (accessed on 10 November 2021).
- Medtronic. Implantable Cardioverter Defibrillator (ICD) Devices for Tachycardia. Available online: https://europe.medtronic.com/xd-en/healthcare-professionals/products/cardiac-rhythm/icd-systems.html (accessed on 10 November 2021).
- Merlin.net. Merlin.netTM Patient Care Network (PCN) Version 5.0. Available online: http://www.cardion.cz/file/253/merlin.net-specsheet.pdf (accessed on 10 November 2021).
- Alforidi, A.; Aslam, D. Fabric-Embedded EEG/ECG/EMG Micro-Systems Monitoring Smart-Horne-Occupants’ Health/Disease by Smartphones. In Proceedings of the 2018 IEEE International Conference on Electro/Information Technology (EIT), Rochester, MI, USA, 3–5 May 2018; pp. 856–859. [Google Scholar] [CrossRef]
- BIOPAC Systems Inc. Mobita Wearable Biopotentials: 32CH EEG, ECG, EMG, EOG, EGG. Tech Report. Available online: https://www.biopac.com/product-category/research/mobita-wearable-biopotentials/ (accessed on 11 November 2021).
- Corporation, B. Bittium Faros™—Waterproof ECG Devices for Cardiac Monitoring. Available online: https://www.bittium.com/medical/bittium-faros?gclid=Cj0KCQiA-K2MBhC-ARIsAMtLKRuf1Hh9PZTYtSt05rN_5Suh_igew7qEAIIHOjcSjv22GaVR4eY_m44aAlaREALw_wcB (accessed on 11 November 2021).
- Technology, L.M. Types of ECG. Available online: https://en.lepumedical.com/products/ecg/ (accessed on 11 November 2021).
- Systems, T. Stellar Telemetry-Wireless Monitoring. Available online: https://www.tse-systems.com/product-details/stellar-telemetry/ (accessed on 11 November 2021).
- Gubbi, J.; Buyya, R.; Marusic, S.; Palaniswami, M. Internet of Things (IoT): A vision, architectural elements, and future directions. Future Gener. Comput. Syst. 2013, 29, 1645–1660. [Google Scholar] [CrossRef]
- Sakovich, N. Wearable Technology in Healthcare: How Devices Will Influence Our Health. 2018. Available online: https://www.sam-solutions.com/blog/wearable-technology-in-healthcare-how-devices-will-influence-our-health/ (accessed on 3 October 2018).
- Garmin. Wearables Activity Tracking. Available online: https://www.garmin.com.my/products/wearables/?cat=activity_tracking. (accessed on 10 January 2019).
- Rushambwa, M.C.; Gezimati, M.; Jeeva, J.B. Development of a wearable wireless body area network for health monitoring of the elderly and disabled. IOP Conf. Ser. Mater. Sci. Eng. 2017, 263, 052052. [Google Scholar] [CrossRef]
- Sikaris, K.A. Physiology and its importance for reference intervals. Clin. Biochem. Rev. 2014, 35, 3–14. [Google Scholar]
- Greger, R.; Bleich, M. Normal Values for Physiological Parameters. In Comprehensive Human Physiology: From Cellular Mechanisms to Integration; Greger, R., Windhorst, U., Eds.; Springer: Berlin/Heidelberg, Germany, 1996; pp. 2427–2449. [Google Scholar] [CrossRef]
- Zou, S.; Xu, Y.; Wang, H.; Li, Z.; Chen, S.; Hu, B. A Survey on Secure Wireless Body Area Networks. Secur. Commun. Netw. 2017, 2017, 3721234. [Google Scholar] [CrossRef]
- Ananthi, J.; Jose, P. A Perspective Review of Security Challenges in Body Area Networks for Healthcare Applications. Int. J. Wirel. Inf. Netw. 2021, 28, 1–16. [Google Scholar] [CrossRef] [PubMed]
- Asam, M.; Jamal, T.; Ajaz, A.; Haider, Z.; Butt, S.A. Security Issues in WBANs. arXiv 2019, arXiv:1911.04330. [Google Scholar]
- Saleem, S.; Ullah, S.; Kwak, K.S. A study of IEEE 802.15.4 security framework for wireless body area networks. Sensors 2011, 11, 1383–1395. [Google Scholar] [CrossRef] [PubMed]
- Al-Janabi, S.; Al-Shourbaji, I.; Shojafar, M.; Shamshirband, S. Survey of main challenges (security and privacy) in wireless body area networks for healthcare applications. Egypt. Inform. J. 2017, 18, 113–122. [Google Scholar] [CrossRef]
- Bengag, A.; Bengag, A.; Moussaoui, O. Attacks Classification and a Novel IDS for Detecting Jamming Attack in WBAN. Adv. Sci. Technol. Eng. Syst. J. 2020, 5, 80–86. [Google Scholar] [CrossRef]
- Saifuzzaman, M.; Ananna, T.N.; Chowdhury, M.J.M.; Ferdous, M.S.; Chowdhury, F. A Systematic Literature Review on Wearable Health Data Publishing under Differential Privacy. Int. J. Inf. Secur. 2022, 21, 847–872. [Google Scholar] [CrossRef]
- Ullah, F.; Zahid Khan, M.; Faisal, M.; Rehman, H.U.; Abbas, S.; Mubarek, F.S. An Energy Efficient and Reliable Routing Scheme to enhance the stability period in Wireless Body Area Networks. Comput. Commun. 2021, 165, 20–32. [Google Scholar] [CrossRef]
- Sangwan, A.; Bhattacharya, P. A Study on Various Issues in Different Layers of WBAN. Int. J. Comput. Appl. 2015, 129, 24–28. [Google Scholar] [CrossRef]
- Lucas Camelo, S.; Amy Greene, J.L.U.O. The Internet Of Insecure Things: Analyzing a Low-Energy Protocol and Cryptographic Solutions. 2015. Available online: https://courses.csail.mit.edu/6.857/2015/files/camelosa-greene-loving-otgonbaatar.pdf (accessed on 21 November 2021).
- Dynastream Innovations Inc. ANT Message Protocol and Usage. D00000652 Rev 5.1. 2014. Available online: https://www.thisisant.com/resources/ant-message-protocol-and-usage (accessed on 21 November 2021).
- Assets, V. U.S. Department of Defense Certifies RuBee (IEEE 1902.1) Wireless Has a HERO, Zero Safe Separation Distance (SSD) from Fused Ordnance. 2012. Available online: https://www.prnewswire.com/news-releases/us-department-of-defense-certifies-rubee-ieee-19021-wireless-has-a-hero-zero-safe-separation-distance-ssd-from-fused-ordnance-163527736.html (accessed on 14 November 2021).
- Ali, S.T. Security mechanisms for body sensor networks. Ph.D. Thesis, University of New South Wales, Sydney, Australia, 2011. [Google Scholar]
- Singelee, D. Study and Design of a Security Architecture for Wireless Personal Area Networks. Ph.D. Thesis, Katholieke Universiteit Leuven, Leuven, Belgium, 2008. [Google Scholar]
- Panwar, N.; Sharma, S.; Mehrotra, S.; Krzywiecki, L.; Venkatasubramanian, N. Smart Home Survey on Security and Privacy. arXiv 2019, arXiv:1904.05476. [Google Scholar]
- Olawumi, O.; Haataja, K.; Asikainen, M.; Vidgren, N.; Toivanen, P. Three practical attacks against ZigBee security: Attack scenario definitions, practical experiments, countermeasures, and lessons learned. In Proceedings of the 2014 14th International Conference on Hybrid Intelligent Systems, Kuwait, Kuwait, 14–16 December 2014; pp. 199–206. [Google Scholar] [CrossRef]
- Research.; Markets. Security in ZigBee Communications. 2016. Available online: https://www.incibe-cert.es/en/blog/security-zigbee-communications (accessed on 18 November 2021).
- Iqbal, W.; Kausar, F.; Arif, M. Attacks on Bluetooth Security Architecture and Its Countermeasures. In International Conference on Information Security and Assurance; Springer: Berlin/Heidelberg, Germany, 2010; pp. 190–197. [Google Scholar] [CrossRef]
- Be-Nazir, N.; Ibn Minar, N.; Tarique, M. Bluetooth Security Threats And Solutions: A Survey. Int. J. Distrib. Parallel Syst. 2012, 3, 3110. [Google Scholar] [CrossRef]
- Lakshmi, M.S.; Kumar, S.P.; Ashok, S. A review on wireless network attacks. Int. J. Comput. Sci. Inf. Technol. (IJCSIT) 2014, 5, 2540–2542. [Google Scholar]
- Meng, K. Wi-fi Attack Mitigation: Analysis, Design, and Implementation. Ph.D. Thesis, The University of Alabama, Tuscaloosa, AL, USA, 2011. [Google Scholar]
- Aras, E.; Ramachandran, G.S.; Lawrence, P.; Hughes, D. Exploring the Security Vulnerabilities of LoRa. In Proceedings of the 2017 3rd IEEE International Conference on Cybernetics (CYBCONF), Exeter, UK, 21–23 June 2017; pp. 1–6. [Google Scholar] [CrossRef]
- Noura, H.; Hatoum, T.; Salman, O.; Yaacoub, J.P.; Chehab, A. LoRaWAN security survey: Issues, threats and possible mitigation techniques. Internet Things 2020, 12, 100303. [Google Scholar] [CrossRef]
- Tomasin, S.; Zulian, S.; Vangelista, L. Security Analysis of LoRaWAN Join Procedure for Internet of Things Networks. In Proceedings of the 2017 IEEE Wireless Communications and Networking Conference Workshops (WCNCW), San Francisco, CA, USA, 19–22 March 2017; pp. 1–6. [Google Scholar] [CrossRef]
- Gupta, P. Mitigating Risks From A to Z-Wave. 2019. Available online: https://www.securityindustry.org/2019/04/23/mitigating-risks-from-a-to-z-wave/ (accessed on 21 November 2021).
- Toorani, M. On Vulnerabilities of the Security Association in the IEEE 802.15.6 Standard. arXiv 2015, arXiv:1501.02601. [Google Scholar]
- Diffie, W.; Hellman, M. New Directions in Cryptography. IEEE Trans. Inf. Theor. 2006, 22, 644–654. [Google Scholar] [CrossRef]
- Rivest, R.L.; Shamir, A.; Adleman, L. A Method for Obtaining Digital Signatures and Public-key Cryptosystems. Commun. ACM 1978, 21, 120–126. [Google Scholar] [CrossRef]
- Karlof, C.; Sastry, N.; Wagner, D. TinySec: A link layer security architecture for wireless sensor networks. In Proceedings of the 2nd International Conference on Embedded Networked Sensor Systems, Baltimore, MD, USA, 3–5 November 2004; pp. 162–175. [Google Scholar] [CrossRef]
- Zhao, Z. An Efficient Anonymous Authentication Scheme for Wireless Body Area Networks Using Elliptic Curve Cryptosystem. J. Med. Syst. 2014, 38, 13. [Google Scholar] [CrossRef]
- Barua, M.; Liang, X.; Lu, R.; Shen, X. PEACE: An efficient and secure patient-centric access control scheme for eHealth care system. In Proceedings of the 2011 IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Shanghai, China, 10–15 April 2011; pp. 970–975. [Google Scholar] [CrossRef]
- Guan, T.; Han, J.; Zeng, X. Exploration for energy-efficient ECC decoder of WBAN. In Proceedings of the 2015 IEEE 11th International Conference on ASIC (ASICON), Chengdu, China, 3–6 November 2015; pp. 1–4. [Google Scholar] [CrossRef]
- Tian, Y.; Peng, Y.; Peng, X.; Li, H. An Attribute-Based Encryption Scheme with Revocation for Fine-Grained Access Control in Wireless Body Area Networks. Int. J. Distrib. Sens. Netw. 2014, 10, 259798. [Google Scholar] [CrossRef]
- Chu, C.K.; Liu, J.; Zhou, J.; Bao, F.; Deng, R. Practical ID-based Encryption for Wireless Sensor Network. IACR Cryptol. Eprint Arch. 2010, 2010, 2. [Google Scholar] [CrossRef]
- Sammoud, A.; Chalouf, M.A.; Hamdi, O.; Montavont, N.; Bouallegue, A. A new biometrics-based key establishment protocol in WBAN: Energy efficiency and security robustness analysis. Comput. Secur. 2020, 96, 101838. [Google Scholar] [CrossRef]
- Ramli, S.N.; Ahmad, R.; Abdollah, M.F.; Dutkiewicz, E. A biometric-based security for data authentication in Wireless Body Area Network (WBAN). In Proceedings of the 2013 15th International Conference on Advanced Communications Technology (ICACT), PyeongChang, Korea, 27–30 January 2013; pp. 998–1001. [Google Scholar]
- Zhang, G.H.; Poon, C.C.Y.; Li, Y.; Zhang, Y.T. A biometric method to secure telemedicine systems. In Proceedings of the 2009 Annual International Conference of the IEEE Engineering in Medicine and Biology Society, Minneapolis, MN, USA, 3–6 September 2009; pp. 701–704. [Google Scholar] [CrossRef]
- Mehmood, N.Q.; Culmone, R.; Mostarda, L. A Flexible and Scalable Architecture for Real-Time ANT+ Sensor Data Acquisition and NoSQL Storage. Int. J. Distrib. Sens. Netw. 2016, 12, 3651591. [Google Scholar] [CrossRef]
- Lehpamer, H. Rfid Design Principles, 2nd ed.; Artech House: Norwood, MA, USA, 2012. [Google Scholar]
- Stevens, J.; Weich, C. Rubee (IEEE 1902.1)—The physics behind, real-time, high security wireless asset visibility networks in harsh environments. In Proceedings of the International IEEE Security Conference 2010, Vancouver, BC, Canada, 23–26 May 2010; Available online: https://www.ru-bee.com/Academy/Sec/SecPaper/ (accessed on 24 November 2021).
- Sensium. Sensium Communication Protocol. Available online: https://www.sensium.co.uk/_assets/media/documents/brochures/Radio-White-paper.pdf (accessed on 26 October 2021).
- Ghamari, M.; Janko, B.; Sherratt, R.S.; Harwin, W.; Piechockic, R.; Soltanpur, C. A Survey on Wireless Body Area Networks for eHealthcare Systems in Residential Environments. Sensors 2016, 16, 831. [Google Scholar] [CrossRef]
- Kambourakis, G.; Kolias, C.; Geneiatakis, D.; Karopoulos, G.; Makrakis, G.M.; Kounelis, I. A State-of-the-Art Review on the Security of Mainstream IoT Wireless PAN Protocol Stacks. Symmetry 2020, 12, 579. [Google Scholar] [CrossRef]
- World, R.W. Advantages of Insteon Technology Disadvantages of Insteon Technology. 2021. Available online: https://www.rfwireless-world.com/Terminology/Advantages-and-Disadvantages-of-Insteon-technology.html (accessed on 26 October 2021).
- Amin, Y.M.; Abdel-Hamid, A.T. A Comprehensive Taxonomy and Analysis of IEEE 802.15.4 Attacks. J. Electr. Comput. Eng. 2016, 2016, 7165952. [Google Scholar] [CrossRef]
- Ullah, S.; Mohaisen, M.; Alnuem, M.A. A Review of IEEE 802.15.6 MAC, PHY, and Security Specifications. Int. J. Distrib. Sens. Netw. 2013. [Google Scholar] [CrossRef]
- Kwak, K.S.; Ullah, S.; Ullah, N. An Overview of IEEE 802.15.6 Standard. arXiv 2011, arXiv:1102.4106. [Google Scholar]
- Toorani, M. Security analysis of the IEEE 802.15.6 standard. Int. J. Commun. Syst. 2016, 29, 2471–2489. [Google Scholar] [CrossRef]
- Fan, X.; Susan, F.; Long, W.J.; Li, S. Security Analysis of Zigbee. In Massachusetts Institute of Technology (MIT); 2017; Available online: https://courses.csail.mit.edu/6.857/2017/project/17.pdf (accessed on 14 April 2022).
- Razouk, W.; Crosby, G.; Sekkaki, A. New Security Approach for ZigBee Weaknesses. Procedia Comput. Sci. 2014, 37, 56. [Google Scholar] [CrossRef]
- Coskun, V.; Ozdenizci Kose, B.; Ok, K. A survey on Near Field Communication (NFC) technology. Wirel. Pers. Commun. 2013, 71. [Google Scholar] [CrossRef]
- Zhang, Y.; Weng, J.; Dey, R.; Fu, X. Bluetooth Low Energy (BLE) Security and Privacy. In Encyclopedia of Wireless Networks; Shen, X.S., Lin, X., Zhang, K., Eds.; Springer International Publishing: Cham, Switzerland, 2019; pp. 1–12. [Google Scholar] [CrossRef]
- Kacherovska, D. How Secure Is the BLE Communication Standard? Learn How to Make BLE More Secure. 2019. Available online: https://dzone.com/articles/how-secure-is-the-ble-communication-standard (accessed on 3 January 2021).
- Zheng, J.; Lee, M.; Anshel, M. Toward Secure Low Rate Wireless Personal Area Networks. IEEE Trans. Mob. Comput. 2006, 5, 1361–1373. [Google Scholar] [CrossRef]
- Malgaonkar, S.; Patil, R.; Rai, A.; Singh, A. Research on Wi-Fi Security Protocols. Int. J. Comput. Appl. 2017, 164, 30–36. [Google Scholar] [CrossRef]
- Alliance, W.F. Discover Wi-Fi Security. 2021. Available online: https://www.wi-fi.org/discover-wi-fi/security (accessed on 19 November 2021).
- Fernando, J. Compound Annual Growth Rate (CAGR). 2021. Available online: https://www.investopedia.com/terms/c/cagr.asp (accessed on 2 November 2021).
- Research, T.M. Global Body Area Network Market to Reach Us $62,120.9 Million by 2025—Transparency Market Research, 2018. News Provided by PRNewswire, Source = Transparency Market Research. Available online: https://www.prnewswire.com/news-releases/global-body-area-network-market-to-reach-us-621209-million-by-2025—Transparency-market-research-669364253.html (accessed on 5 November 2021).
- Hayward, J. Wearable Technology Forecasts 2021–2031. 2021. Available online: https://www.idtechex.com/en/research-report/wearable-technology-forecasts-2021-2031/839 (accessed on 5 November 2021).
- Perez, A.J.; Zeadally, S. Recent Advances in Wearable Sensing Technologies. Sensors 2021, 21, 6828. [Google Scholar] [CrossRef] [PubMed]
- Li, Y.; Chen, Y.; Chen, C.S.; Wang, Z.; Zhu, Y.h. Charging While Moving: Deploying Wireless Chargers for Powering Wearable Devices. IEEE Trans. Veh. Technol. 2018, 67, 11575–11586. [Google Scholar] [CrossRef]
- 360 Research Reports. Global Body Area Network Market Report, History And Forecast 2016–2027, Breakdown Data By Companies, Key Regions, Types And Application. 2021. Available online: https://www.360researchreports.com/enquiry/request-sample/18429198 (accessed on 5 November 2021).
- Future, M.R. Body Area Network Market to Touch USD 21 Billion at 13% CAGR by 2025—Report by Market Research Future (MRFR). Market Research Future. 2021. Available online: https://www.globenewswire.com/news-release/2021/08/12/2279692/0/en/Body-Area-Network-Market-to-Touch-USD-21-Billion-at-13-CAGR-by-2025-Report-by-Market-Research-Future-MRFR.html (accessed on 6 November 2021).
- Future, M.R. Body Area Network Market Research Report: By Device (Wearable Devices (Smart Bands, Smartwatches, Smart Earphones) Implantable), by Technology (Bluetooth Low Energy, Zigbee, Wi-Fi, Others) by Application (Medical and Fitness, Sports, Security, Military, Others) and by Region (North America, Europe, Asia-Pacific, Middle East and Africa, Central and South America)—Forecast till 2027. 2021. Available online: https://www.marketresearchfuture.com/sample_request/8516 (accessed on 5 November 2021).
- Gartner. Gartner Forecasts Global Spending on Wearable Devices to Total Dollar 81.5 Billion in 2021. 2021. Available online: https://www.gartner.com/en/newsroom/press-releases/2021-01-11-gartner-forecasts-global-spending-on-wearable-devices-to-total-81-5-billion-in-2021 (accessed on 28 October 2021).
- Intelligence, M. Smart Wearable Market—Growth, Trends, COVID-19 Impact, and Forecasts (2021–2026). 2021. Available online: https://www.mordorintelligence.com/industry-reports/smart-wearables-market (accessed on 28 October 2021).
- NEEDHAM, M. Wearable Devices Market Share, 2022. Online, Business Report. Available online: https://www.idc.com/promo/wearablevendor (accessed on 26 April 2022).
- Laricchia, F. Wearables Shipments Worldwide Market Share 2014–2021, by Vendor, 2022. Online, Business Report. Available online: https://www.statista.com/statistics/435944/quarterly-wearables-shipments-worldwide-market-share-by-vendor/ (accessed on 26 April 2022).
- Compliance & Risks. Compliance & Risks Launches Global Medical Device Regulatory Coverage. Regulation/Compliance Guide. 2021. Available online: https://blog.complianceandrisks.com/news-resources/compliance-risks-launches-global-medical-device-regulatory-coverage (accessed on 6 November 2021).
- Lamph, S. Regulation of medical devices outside the European Union. J. R. Soc. Med. 2012, 105 Suppl 1, S12–S21. [Google Scholar] [CrossRef]
- Medical Devices Regulations (MDR). Medical Devices Regulations SOR/98-282. 2021. Available online: https://laws-lois.justice.gc.ca/PDF/SOR-98-282.pdf (accessed on 5 November 2021).
- WHO. Word Health Organization (WHO). Available online: https://www.who.int/ (accessed on 8 November 2021).
- IMDRF. International Medical Device Regulators Forum. 2021. Available online: http://www.imdrf.org/ (accessed on 8 November 2021).
- ISO. International Organization for Standardization (ISO). Available online: https://www.iso.org/home.html (accessed on 8 November 2021).
- ECRI. Emergency Care Research Institute (ECRI). Available online: https://www.ecri.org/ (accessed on 8 November 2021).
- APEC. Asia-Pacific Economic Cooperation (APEC). Available online: https://www.apec.org/ (accessed on 8 November 2021).
- AHWP. Asian Harmonisation Working Party (AHWP). Available online: http://www.ahwp.info/ (accessed on 8 November 2021).
- ASEAN. Association of Southeast Asian Nations (ASEAN). Available online: https://asean.org/ (accessed on 8 November 2021).
- The National Institute for Health and Care Excellence (NICE). Available online: https://www.nice.org.uk/ (accessed on 8 November 2021).
- ETSI. European Telecommunications Standards Institute (ETSI). Available online: https://www.etsi.org/ (accessed on 8 November 2021).
- FCC. Federal Communications Commission(FCC). Available online: https://www.fcc.gov/ (accessed on 8 November 2021).
- HIPPA. Health Insurance Portability and Accountability Act (HIPPA). Available online: https://www.hipaa.com/ (accessed on 8 November 2021).
- FDA. Food and Drug Administration (FDA). Available online: https://www.fda.gov (accessed on 8 November 2021).
- IMED. Ministry of Health and Medical Education (IMED)—Food & Drug Administration, National Medical Device Directorate. Available online: http://imed.ir/ (accessed on 8 November 2021).
- State of Israel Ministry of Health. Medical Device Division. Available online: https://www.health.gov.il/English/MinistryUnits/HealthDivision/MedicalTechnologies/MLD/Pages/default.aspx (accessed on 8 November 2021).
- JFDA. Jordan Food and Drug Administration (JFDA). Available online: http://www.jfda.jo/ (accessed on 8 November 2021).
- SFDA. The Saudi Food and Drug Authority (SFDA). Available online: https://www.sfda.gov.sa/en/ (accessed on 8 November 2021).
- Health, M.; Mohap, P. Registration of a Medical Equipment. Available online: https:/https://mohap.gov.ae/en/services (accessed on 8 November 2021).
- Faith, A.E.; Afjn, N.J. National Medicine Regulatory Authorities in Africa: Key to Access to Safe and Effective Medical Products. 2021. Available online: http://aefjn.org/en/national-medicine-regulatory-authorities-in-africa-key-to-access-to-safe-and-effective-medical-products/ (accessed on 9 November 2021).
- WHO. Regulatory Harmonization-Updating medicines regulatory systems in sub-Saharan African countries. WHO Drug Inf. 2010, 24. Available online: https://www.who.int/medicines/technical_briefing/tbs/regulatory_harmonization_DrugInfo2010_Vol24_1.pdf?ua=1 (accessed on 9 November 2021).
- ARSO. African Organisation for Standardisation—ARSO. Available online: https://www.arso-oran.org/ (accessed on 9 November 2021).
- UNECA. African Union (AU) and United Nations Economic Commission for Africa (UNECA). Available online: https://www.uneca.org/ (accessed on 9 November 2021).
- Mboya-Okeyo, T.; Ridley, R.; Nwaka, S. The African Network for Drugs and Diagnostic Innovation. Lancet 2009, 373, 1507–1508. [Google Scholar] [CrossRef]
- Saidi, T.; Douglas, T. Medical Device Regulation in Africa. In Biomedical Engineering for Africa; University of Cape Town: Cape Town, South Africa, 2019; pp. 175–185. [Google Scholar]
- Rugera, S.P.; McNerney, R.; Poon, A.K.; Akimana, G.; Mariki, R.F.; Kajumbula, H.; Kamau, E.; Mpawenimana, S.; Said, S.Y.; Toroitich, A.; et al. Regulation of medical diagnostics and medical devices in the East African community partner states. BMC Health Serv. Res. 2014, 14, 524. [Google Scholar] [CrossRef]
- PAHO. Pan American Health Organization (PAHO). Available online: https://www.paho.org/en (accessed on 9 November 2021).
- Mercosur. What is MERCOSUR? Available online: https://www.mercosur.int/en/ (accessed on 9 November 2021).
- Emergo. COFEPRIS—Mexico Ministry of Health. 2021. Available online: https://www.emergobyul.com/resources/mexico/cofepris#:~:text=COFEPRIS%20or%20the%20Federal%20Committee,advertising%20permits%20for%20these%20products. (accessed on 9 November 2021).
- Center for the State Control of Medicines, Equipment and Medical Devices (CEMED). RESOLUTION CECMED 1. 2011. Available online: https://www-cecmed-cu.translate.goog/reglamentacion/aprobadas/resolucion-cecmed-1?_x_tr_sl=auto&_x_tr_tl=en&_x_tr_hl=en&_x_tr_pto=wapp (accessed on 9 November 2021).
- Min Wu, J.L. Wearable technology applications in healthcare: A literature review. Online J. Nurs. Inform. (OJNI) 2019, 23. [Google Scholar]
- Rodgers, M.M.; Alon, G.; Pai, V.M.; Conroy, R.S. Wearable technologies for active living and rehabilitation: Current research challenges and future opportunities. J. Rehabil. Assist. Technol. Eng. 2019, 6, 2055668319839607. [Google Scholar] [CrossRef]
- Filipe, L.; Fdez-Riverola, F.; Costa, N.; Pereira, A. Wireless Body Area Networks for Healthcare Applications: Protocol Stack Review. Int. J. Distrib. Sens. Netw. 2015, 11, 213705. [Google Scholar] [CrossRef]
- Nhx, T.; Tech Times. How to Connect Your Samsung Galaxy Watch to an Iphone. 2020. Available online: https://www.techtimes.com/articles/250619/20200626/how-to-connect-your-samsung-galaxy-watch-to-an-iphone.htm (accessed on 28 October 2021).
- Buckiewicz, B. Medical Body Area Networks: Rules and Regulations. 2019. Available online: https://www.lairdconnect.com/resources/white-papers/fcc-requirements-for-medical-body-area-networks (accessed on 28 October 2021).
- Mahmood, S.N.; Ishak, A.J.; Saeidi, T.; Soh, A.C.; Jalal, A.; Imran, M.A.; Abbasi, Q.H. Full Ground Ultra-Wideband Wearable Textile Antenna for Breast Cancer and Wireless Body Area Network Applications. Micromachines 2021, 12, 322. [Google Scholar] [CrossRef] [PubMed]
- Kumar, P.; Ali, T.; Sharma, A. Flexible Substrate based Printed Wearable Antennas for Wireless Body Area Networks Medical Applications (Review). Radioelectron. Commun. Syst. 2021, 64, 337–350. [Google Scholar] [CrossRef]
- Wang, N.; Daniels, R.; Connelly, L.; Sotzing, M.; Wu, C.; Gerhard, R.; Sotzing, G.A.; Cao, Y. All-Organic Flexible Ferroelectret Nanogenerator with Fabric-Based Electrodes for Self-Powered Body Area Networks. Small 2021, 17, 2103161. [Google Scholar] [CrossRef]
- Cornet, B.; Fang, H.; Ngo, H.; Boyer, E.W.; Wang, H. An Overview of Wireless Body Area Networks for Mobile Health Applications. IEEE Network 2022, 36, 76–82. [Google Scholar] [CrossRef]
- Khan, M.D.; Ullah, Z.; Ahmad, A.; Hayat, B.; Almogren, A.; Kim, K.H.; Ilyas, M.; Ali, M. Energy Harvested and Cooperative Enabled Efficient Routing Protocol (EHCRP) for IoT-WBAN. Sensors 2020, 20, 6267. [Google Scholar] [CrossRef] [PubMed]
- Feng, M.; Meunier, J. Skeleton Graph-Neural-Network-Based Human Action Recognition: A Survey. Sensors 2022, 22, 2091. [Google Scholar] [CrossRef]
- Yan, Y.; Liao, T.; Zhao, J.; Wang, J.; Ma, L.; Lv, W.; Xiong, J.; Wang, L. Deep Transfer Learning with Graph Neural Network for Sensor-Based Human Activity Recognition. arXiv 2022, arXiv:2203.07910. [Google Scholar]
- Negra, R. Leveraging Machine Learning for WBANs. In Distributed Computing for Emerging Smart Networks; Jemili, I., Mosbah, M., Eds.; Springer International Publishing: Cham, Switzerland, 2022; pp. 38–59. [Google Scholar]
- Kumar, P.; Chauhan, S. RETRACTED ARTICLE: Human activity recognition with deep learning: Overview, challenges and possibilities. CCF Trans. Pervasive Comput. Interact. 2021, 3, 339. [Google Scholar] [CrossRef]
- Jiang, W. Graph-based Deep Learning for Communication Networks: A Survey. Comput. Commun. 2022, 185, 40–54. [Google Scholar] [CrossRef]
- Ren, Y.; Leng, Y.; Zhu, F.; Wang, J.; Kim, H.J. Data Storage Mechanism Based on Blockchain with Privacy Protection in Wireless Body Area Network. Sensors 2019, 19, 2395. [Google Scholar] [CrossRef] [PubMed]
- Kumari, R.; Nand, P.; Astya, R. Integration of Blockchain in WBAN. In Proceedings of the 2019 International Conference on Computing, Communication, and Intelligent Systems (ICCCIS), Coimbatore, India, 6–8 December 2019; pp. 144–149. [Google Scholar] [CrossRef]
- Zeadally, S.; Bou abdo, J. Blockchain: Trends and Future Opportunities. Internet Technol. Lett. 2019, 2, 130. [Google Scholar] [CrossRef]
- Singh, M.; Fuenmayor, E.; Hinchy, E.P.; Qiao, Y.; Murray, N.; Devine, D. Digital Twin: Origin to Future. Appl. Syst. Innov. 2021, 4, 36. [Google Scholar] [CrossRef]
- Khan, S.; Arslan, T.; Ratnarajah, T. Digital Twin Perspective of Fourth Industrial and Healthcare Revolution. IEEE Access 2022, 10, 25732–25754. [Google Scholar] [CrossRef]





| Sensor | Implantation | Observation |
|---|---|---|
| Guardian Real-time | inside the body | Sugar |
| MiniMed 530G with Enlite | wearable, injectable | Sugar |
| FreeStyle | inside the body | Sugar |
| Eyeglasses biosensor | body-worn | Sugar |
| Eyeglasses biosensor | body-surface | Sugar |
| Guardian Real-time | inside the body | Sugar |
| IFever | body-worn | Temperature |
| ISense | body-worn | Temperature |
| Ran’s Night | body-worn | Temperature |
| FeverFrida thermometer | body-surfaced | Temperature |
| STEMP sensor | body-surfaced | Temperature |
| Aranet medical thermometer | body-worn | Temperature |
| Propeller | body-worn | Asthma |
| AirSonea | body-worn | Asthma |
| Wing | body-worn | Asthma |
| BH1790GLC | body-worn | HR |
| TCRT 1000 | body-worn | HR |
| Smart QHeart Rate Sensor | body-worn | HR |
| Polar H10 | body-worn | HR |
| Pulse sensor | body-worn | HR |
| MPU-9250 Invensense | body-worn | Motion |
| MMA 8451Q, accelerometer | body-worn | Motion |
| LSM 303 DLHC | body-worn | Motion |
| BNO055 | body-worn | Motion |
| MPU-9250 Invensense | body-worn | BP |
| Biosignals plux | body-worn | BP |
| Proven BPM-337BT | body-worn | BP |
| Omron M7 Intelli IT | body-worn | BP |
| Scheme | Standard LoRaWAN | Improved DO-SEO [85] |
|---|---|---|
| Mutual Authentication | ✓ | ✓ |
| Secure Key Exchange | ✓ | ✓ |
| Perfect Forward Secrecy | ✓ | |
| End-to-End Security | ✓ | |
| Thwart Replay Attack | ✓ |
| Protocol | Distance Range | Data Rate | Power Consumption | Frequency Band | Suitability |
|---|---|---|---|---|---|
| ANT (from Garmins) | 100 m outer door | 1 Mbps | 15 mA Tx 17 mA Rx | 2.40–2.483 GHz | used in sports, fitness and health devices |
| RuBee (IEEE 1902.1) | 30 m | 9.6 k | emits energy in nanoWatts, battery lasts for many years | operates below 450 kHz | considered to be a strong contestant for WBAN application |
| Insteon | 30 m | 9.6 k | Battery life is 10+ years | operates below 450 kHz | considers being a good protocol for WBAN applications |
| Sensium | home area | 13 k | 5 days | 131.65 KHz, 902–924 MH | extensively used in health care and diagnostic application, worthy of medical implanting cases, gastrointestinal [74]. |
| Bluetooth Classic (IEEE 802.15.1) | 100 m | 1–3 Mbps | 2.5–100 mW | 2400–2483.5 MHz range within the ISM 2.4 GHz frequency band | used in different area of tele-medicine and e-health systems, but unfit for WBANs [70]. |
| BLE (Bluetooth 4.2) | 50–150 m | 1 Mbps | 10 mW | 2.4 GHz | But, not suitable for frequent and steady reporting of health parameters [70]. At the |
| IEEE 802.11 | 150–200 m | 54 Mbps | 1 W | 2.4 GHz (WiFi), 5 GHz | encouraging wireless technology for WBANs [70] |
| Zigbee 3.0, 802.15.4 | 10–100 m | 250 kbps | 35 mW | 2.4 GHz mostly; though some devices use 784 MHz (China), 868 MHz (Europe), 915 MHz (USA, Australia) | unsuitable for critical WBAN application which are required to carry urgent data without delays [70]. |
| LoRa (LoRa Alliance) | urban 2–5, suburban 15, rural 45 | 0.3–50 kbps | (customizable), battery life more than 10 Years | 169 MHz, 433 MHz, 868 MHz (Europe) and 915 MHz (North America) | used as LPWAN [88] |
| NFC (ISO/IEC 18000-3) | 10 cm | 106, 100–420 kbps | 15 mA or less | 13.56 MHz | smart suits, jackets, jewelry, wrist worns, e-skin, [49] |
| Z-wave | 30 cm | 106, 212 or 424 kbps | it uses 23 mA in transmission mode, battery lasts for decades even | 900 MHz (ISM), (Z-Wave Alliance ZAD12837/ITU-T G.9959) | considered to be a good protocol for WBAN applications [74]. |
| SigFox | 2–5 (urban), 15 (suburban), 45 (rural) | 10–100 kbps | battery life more that 10 years | 433/868/780/915 MHz | used as LPWAN, no mobility and location support [88] |
| NBIoT | 2.5–5 km | more than 250 kbps | battery life more than 10 years | Cellular (Licensed Band) | used as LPWAN, needs GPS for location support, mobility [88] |
| LTECatM1 | 2.5–5 km | 1 Mbps | battery life more than 10 years | Cellular (Licensed Band) | used as LPWAN, needs GPS for location support, supports mobility [88] |
| WBAN (802.15.6) | suitable for short-range human body communication | MICS (75–455, 75–187, 101–607), (101–607) Mbps, (121–971) | 0.1 W | MICS (402–405, 420–450, 863–870), ISM1 (902–928, 950–958), ISM2 (2360–2400, 2400–2483.5) | Most of the medical, non-medical, and on-body WBAN devices have adopted this standard for communication, support for location and mobility |
| Product | Project | Product Type | Features |
|---|---|---|---|
| Life- BEAM | LifeBEAM | Helmet | Monitors beating heartrate using optical sensor |
| Combat- Connect | The Army’s Program Executive Office | Wearable electronics system | disseminate information to/from WBAN using smart hub fixed with military vest/jacket |
| Black Hornet | 3 FLIR SYSTEM | Automatic Pocket-sized helicopter | camera that can be fixed with armor/vest; works as elevated binocular |
| Ground Warfare Acoustical Combat System | Gwacs Defense | A wearable tactical system | Identifies and locates hostile fire; detects and tracks Small UAVs |
| Exo- Atlet | ExoAtlet | Lower body powered exoskeletons | Mobility assistant, reduce troop’s movement cost |
| SPaRK | Spring Active | Energy-scavenging exoskeletons | Performs energy harvesting to recharge devices |
| Monitoring Device/System | Vital Signs | Provider | Ref. |
|---|---|---|---|
| Visi Mobile System | It is (Continuous Beat-by-Beat Blood Pressure) CNiBP, Non-Invasive Blood Pressure (NiBP), ECGs, Respirations, HR, PR, SPO2, Motions and Postures. Visi Mobile System continuously leveraging on hospital’s existing WiFi infrastructure Sotera Wireless | Sotera Wireless, Inc. | [98] |
| Mobile Cardiac Outpatient Telemetry (MCOT) Patch System | MCOT collects medical information using Bluetooth from sensors, transmits ECG wirelessly to BioTel Heart all the time | Bio-Tel Heart | [99,100] |
| MCT 3 Lead (MCT 3L) Cardiac Telemetry | LifeWatch MCT 3 is very smart in nature, giving a distinct picture of the heart in addition to the rhythms of a heartbeat. | Bio-Tel Heart | [99] |
| ePatch Extended Holter Monitoring | Records and stores heartbeats | Bio-Tel heart | [99] |
| wEvent | Wireless Cardiac Event Monitor, wEvent supports arrhythmia detection with high precision | BIO-Tel Heart | [99] |
| Wireless Connector for BPA-060 | Wireless Blood Pressure Monitor | Ambio Health | [101] |
| Wireless Connector for Presto | Blood Glucose Monitor | Ambio Health | [101] |
| WiCap | Capnography device, monitors expired (EtCO2), inspired (FiCO2) breath, respiration rate (RR), SpO2, and pulse rate (PR) | Athena GTX | [102] |
| Tac Pac | Measures NIBP, HR, SpO2, and ECG | Athena GTX | [102] |
| Athena Device Management Suite (ADMS) | ADMS connects different wireless vital-sign monitoring devices and is also adaptable to mobiles and smartphones, alarming, awareness, etc. | Athena GTX | [102] |
| Wireless Vital Signs Monitor | Wirelessly monitors Sp02, HR, NIBP, and ECG within a range of 200 yards, ADMS compatible | Athena GTX | [102] |
| Caretaker | measure CNiBP, Heart Rate, and other vital signs, android compatible | Caretaker Medical | [103] |
| SmartSense | Temperature, blood pressure, pulse, SpO2, respiration, pain level, SMD, etc., via any mobile PC, draw plots of vital signs | Cadi Scientific Pte Ltd. | [104] |
| HealthPatch/Vital Patch, Vista Solutions | Health monitoring system, which can measure HR, RR, temperature, posture, activity, and fall detection | Vital Connect | [105] |
| Fitbit Premium+Health | It is a personalized health monitoring system that helps a person manage stress, have a sound sleep, and stay active. It provides a daily score of these signs. Users can download their data at any time | Fitbit LLC. | [106] |
| Garmin Connect | Garmin Connect can track, analyze and share your health data on mobile or web | Garmin Ltd. | [107] |
| Samsung Health | Galaxy smartwatch-based health solution that scores sleep and blood oxygen during sleep. It can also detect snoring and monitor running performance | Samsung Ltd. | [108] |
| Apple Health Kit | It assesses the steadiness of walking, falling probability, and goodness of sleep that help helps to assess changes in health. The health data can be shared with concerned people | Apple | [109] |
| Wireless Implantable Cardioverter and Defibrillators | Cardioverter and defibrillators give weak and strong electrical shocks to the heart to maintain rhythm and beating. FD approved such devices a long time ago [110,111]. Each manufacturer has introduced its remote monitoring system, pacemakers and ICDs, such as Home MonitoringTM, CareLink NetworkTM, Latitude Patient Management systemTM, and Merlin.netTM (St Jude Medical, Sylmar, USA). [112] | Biotronik, Medtronic, Boston Scientific, Merlin.net | [113,114,115,116] |
| EEG, ECG, EMG, EOG, EGG monitoring devices such as Bittium FarosTM—Cardiac Monitoring | These devices can measure ECG, EMG, EEG, etc., TSE Systems, Lepu Medical Technology, Bittium Corporation, BIOPAC Systems, Inc. are major providers. Stellar Implants, NEO ECG, and Mobita are also good monitoring systems | Fabric-embedded devices available at [117] | [118,119,120,121] |
| Parameters | Normal Range |
|---|---|
| Body Temperature | 37–37 Degrees Celsius |
| Hear Beat | Rate 60–100 beats per minute |
| Breathing Rate | 12–20 breaths per minute |
| Oxygen Saturation | 94–99% |
| Blood Sugar | 4–6 mmol/dL (72–108 mmol/dL) |
| Blood Pressure | 120/80 |
| Hydration level | 90–100% |
| Fall Detection | 0–20 cm |
| Security Issues | Secure System Requirements | Potential Security Measures |
|---|---|---|
| Illegitimate access to information | Dynamic secure key agreement and trust establishment | Random ephemeral key generation and distribution, use of public key cryptography |
| Information Disclosure | Confidentiality and privacy | Link/network layer encryption and access control |
| Data Modification | Integrity and authenticity | Keyed secure hash function and Digital signature |
| Denial of Service | Availability | Intrusion detection systems and redundancy |
| Compromised/Hijacked Node | Cryptosystem must be resilient to node-compromise | Anomaly detection, comprising nodes isolation |
| Routing vulnerabilities | Protection of routing information | Use of secure routing algorithms |
| Intrusions/Unauthorized Access to Network System | Intrusion detection and prevention, secure data aggregation, group communication and management | Intrusion detection and prevention systems |
| Protocol | Security Risks | Proposed Control Measures |
|---|---|---|
| ANT | by default ANT+ is not encrypted, AES128 support in special cases, provided in single channel communication only, lack of authentication, MITM [137]. | network key along with network number provides different options for access control and security level [137,138] |
| Rubee | no eavesdropping, high packet security due to date and time stamp [139]. | eavesdropping range is similar to that of tag range; such a close eavesdropper can be detected easily, it meets a high standard of security also being used in many US Govt. owned departments [139] of USA |
| Sensium | Sensium is vulnerable to all those attacks, launched on body sensor networks, such as insider attacks, DOS, wormhole, replay, jamming, etc. [140] | per hop encryption can reduce the chances of attacks, also reduces overload over the network as well [140] |
| Zigbee | insufficient integrity protection due to sending unencrypted key; location privacy, an initialization vector (or Nonce), and key management are susceptible to high-security risks; improper support of group keying [141]. Due to default weak password, misconfiguration of the Zigbee IP network, and the gateway or lack of security an attacker can bypass Zigbee authentication check [142]; replay attack, device identification attack, and packet interception are a few of the other ones [143] | time stamping, AES, and Message Integrity Codes (MIC) can be used to mitigate the risks [143]. In addition to this, since the security keys are stored in memory, adversaries can directly steal them. Therefore, it is advised to use a microcontroller for secure authentication and to eliminate the threat of physical corruption of security keys [144]. |
| Bluetooth | intrusion in pico-net, MITM (Man-in-the-Middle)/Impersonation, DOS attacks, Bluejacking [142,145]. A few other reported attacks are MAC-spoofing, PIN cracking, BlueSnarfing, BlueBugging, BluePrinting, Blue over, off-line PIN recovery attack, brute-force, reflection, backdoor, Cabir worm, Skulls worm, and Lasco worm [146]. | use long PIN Codes, do not pair in public areas, and turn on non-discoverable mode after use, at the corporate level proper policies and guidelines be devised for Bluetooth pairing [145] |
| WiFi | cipher attack is used to attain the encryption key through processing information exchanged between sender and receiver. WEP, WPA-PSK Dictionary, WPA/TKIP, and LEAP are a few of the cipher attacks. WiFi also faces, jamming, flooding, evil-twin threats [142,147] | separating the guest network from actual, encrypting traffic with WPA2 or WPA3, updating firmware timely, creating secure SSID, restricting WiFi to business hours only, all these measures can mitigate the attacks on WiFi [148]. |
| LORA | attacker can obtain access to physical LORA device, jamming-communication channel can block with the high power radio signal, replay, beacon synchronization, traffic analysis, MITM are a few threats to LORA [84]. DOS, Bit-flipping, ACK spoofing. LoRa vulnerability survey can be viewed from [149,150]. | dynamic or ephemeral key generation, DevNonce of large size can prevent join attacks [151], Block-chain is also good for powered limited devices [88]. Use Over-The-Air-Activation (OTAA) [150] |
| NFC | eavesdropping, cloning of ticket, spoofing, a man in the middle attack, corruption of data, insertion of malicious data, relay, ghost and leech, DOS, phishing, a threat to ID, PIN, credentials of credit card, etc. | shared secret keys, certificate-based authentication WEP based security can be used to reduce the probability of these attacks [73] |
| Z-Wave | Z-Wave device pairing process with the controller can run many times, which attracts “key reset attack” [142,152] | vulnerability has not been fixed, more than one million devices are in the market with this vulnerability [152] |
| WBAN | Key-Compromise Impersonation (KCI), Impersonation, WBAN security protocols do not forward secrecy as well [153] | using certified keys KCI can be avoided, but it is not recommended in standards due low resources of WBAN devices [153] |
| Regulatory Body | Year and Location | Members | Comments |
|---|---|---|---|
| WHO [199] | 1948, Geneva (Switzerland) | Globe is a member of the Word Health Organization (WHO) | Looks into global health concerns. https://www.who.int/, Accessed on: 14 April 2022 |
| Global Harmonization Task Force (GHTF), its website is ceased, visit [200] | 1992, USA | USA, European Union (EU), Japan, Australia and Canada, AHWP, International Organization for Standardization (ISO), and the International Electrotechnical Commission (IEC) | Volunteer, the original group of people from MDR formed it for the regulation of medical. GHTF was replaced by International Medical Device Regulators Forum (IMDRF) in 2012 with the aim build a strong foundation of GHTF. https://iris.paho.org/bitstream/handle/10665.2/51549/PAHOHSS19003_eng.pdf, Accessed on: 14 April 2022, https://www.adb.org/sites/default/files/publication/184392/better-regulation-medicine.pdf, Accessed on: 14 April 2022, https://pdf.usaid.gov/pdf_docs/PA00TPBN.pdf, Accessed on: 14 April 2022 |
| IMDRF [200] | 1911, NA | Australia, Brazil, Canada, China, Europe, Japan, Russia, Singapore, South Korea, USA | Successor of GHTF |
| ISO [201] | 1947, Geneva Switzerland | 163 countries are members International Organization for Standardization (ISO) | largest organization in the world for formulating standards https://www.iso.org/home.html, Accessed on: 14 April 2022 |
| Emergency Care Research Institute (ECRI) [202] | 1968, Pennsylvania USA | USA, European Free Trade Association (EFTA), But USA and Canada mutually developed Universal Medical Device Nomenclature System (UMDNS) | ECRI maintained UMDNS, the development of Asian Medical Device Nomenclature System (AMDNS) is also based UMDNS https://www.ecri.org/, Accessed on: 14 April 2022 |
| APEC [203] | 1989, Singapore | Australia, Brunei Darussalam, Canada, Indonesia, Japan, Korea, Malaysia, New Zealand, the Philippines, Singapore, Thailand, USA, China, Hong Kong, Chinese Taipei (Taiwan), Mexico, Papua New Guinea, Chile, Peru, Russia and Vietnam | Asia-Pacific Economic Cooperation (APEC) provides forum for free trade among member countries https://www.apec.org/, Accessed on: 14 April 2022 |
| Asian Harmonisation Working Party (AHWP) [204] | 1996–97, Hong Kong (Asia) | Abu Dhabi (UEA), Brunei Darussalam, Cambodia, Chile, China, Chinese Taipei (Taiwan), Hong Kong SAR, India, Indonesia, Jordan, Saudi Arabia, Korea, Laos, Malaysia, Myanmar, Pakistan, Philippines, Singapore, South Africa, Thailand, and Vietnam | It ensures the regulation of medical devices in Asia, now working on Safety Alert Dissemination System. http://www.ahwp.info/, Accessed on: 14 April 2022 |
| Association of Southeast Asian Nations (ASEAN) [205] | 1967, Jakarta (South Asia) | Bangkok, Indonesia, Malaysia, Philippines, Singapore, Thailand, Brunei Darussalam, Vietnam, Laos, Myanmar and Cambodia. Within ASEAN The Medical Device Product Working Group (MDPWG) is responsible for the regulations of medical devices. | The ASEAN Medical Device Directive (AMDD) formulate basic requirements for the safety, performance and efficiency of medical devices that include a device classification and post-marketing alert system that should be circulated throughout the ASEAN. https://asean.org/, Accessed on: 14 April 2022 |
| NICE [206] | 1999, UK. | European Union. UK is a member of The National Institute for Health and Care Excellence (NICE) | regulates the use health technologies and clinical practices in the UK. Also provides guidance on health care services and promotion. https://www.nice.org.uk/, Accessed on: 14 April 2022 |
| ETSI [207] | 1988, Sophia Antipolis, France | European Union | ETSI regulates technical standards of ICT (Information and Communications Technologies) enabled devices, systems and services https://www.etsi.org/, Accessed on: 14 April 2022 |
| FCC [208] | 1934, USA | US States comply with Federal Communications Commission (FCC) | FCC regulates radio, TV, satellite and cable communication in USA. FCC and other regulatory bodies look into the issues such as how much radio frequency/ energy absorption is harmful for humans https://www.fcc.gov/, Accessed on: 14 April 2022 |
| HIPPA [209] | Act of 1936, USA | US States follows Health Insurance Portability and Accountability Act (HIPPA) | In the USA, HIPPA is responsible for ensuring that the privacy, integrity and access controls are meeting defined standards, rules and regulation. https://www.hipaa.com/, Accessed on: 14 April 2022 |
| Country | Regulatory Body | Year | Purpose |
|---|---|---|---|
| USA | The Food and Drug Administration [210] | 1906, Maryland (USA) | oversees radio and non-radio based medical devices, medicines and drugs, cosmetics, and biologics in the USA |
| Russia | Roszdravnadzor (Federal Service on Surveillance in Healthcare and Social Development | 2004, Moscow (Russia) | it handles registration, clinical safety and efficiency of medical devices. It also oversees post-market surveillance of these devices |
| Russia | Gosstandart (Federal Agency for Technical Regulation and Meteorology) | 2004, Moscow (Russia) | ensures that imported devices meet all Russian standards. Its parent body is Ministry of Industry and Trade |
| Russia | Rospotrebnadoz (Federal Service for Supervision in the Area of Consumer Rights and Welfare Protection) | 1922, Moscow | ensures that BAN devices meet hygienic and epidemiological regulations |
| China | State Food and Drug Administration (SFDA), China Food and Drug Administration (CFDA) in 2013 China: Also a member of AHWP and APEC | CFDA (2013), NMPA (2018), Beijing (China) | accountable for the regulation of locally manufactured and imported BAN medical devices. CFDA was renamed as National Medical Products Administration in 2018 |
| Hong Kong | Device Administrative Control System (MDACS), Hong Kong is also also a member of AHWP and APEC | 2004, Hong Kong | The Medical Device Division (MDD) is accountable for implementing MDACS and developing a long-term statutory regulatory framework for local and imported medical devices. The old name of MDD was Medical Device Control Office (MDCO) formed in 2004. |
| India | Central Drug Standards Control Organization (CDSCO) India: Also a member of AHWP, Based on The Drugs and Cosmetics Act 1940 and Rules 1945, India | NA | works under Ministry of Health and Family Welfare. Carries regulation of medical devices, imported implantable, diagnostic kits and sterile devices require registration under the current system, registration will follow the GHTF, Central Licensing Approval Authority (CLAA) |
| Iran | Ministry of Health and Medical Education—Food and Drug Administration, National Medical Device Directorate [211] | NA, NA | device classification follows GHTF, registration is similar to FDA or EU. |
| Israel | Medical Device Division of the Ministry of Health (AMAR) [212] | NA, NA | devices regulation strictly follows US FDA and EU CE. |
| Jordan | The Jordan Food and Drug Administration (JFDA) [213], Jordan is also a member of AHWP | 2003, Amman (Jordan) | enforces laws and regulation for medical device, if the device is approved from USA FDA and EU CE it does need clearance in Jordan |
| Saudi Arabia | The Saudi Food and Drug Authority (SFDA) [214], Saudi Arabia is also a member of AHWP | 2003 | only those devices are permitted that have approval from any one of the GHTF member |
| UAE | UAE Ministry of Health Drug Registration and Control Department [215], United Arab Emirates (UAE) is also a member of AHWP | NA, NA | UAE adopts guidelines of GHTF, EU, Australian TGA and USA FDA in addition to UAE Pharmacy Law No4 for 1983 |
| Africa | National Medicines Regulatory Authorities (NMRA) [216,217], African Organization for Standardization (ARSO) [218], The African Network for Drugs and Diagnostic Innovation (ANDI), African Union (AU) and United Nations Economic Commission for Africa (UNECA) [219] | ARSO (1970, Kenya), UNECA (1958) | Only 7% of African countries have NMRA, 63% have minute regulations, and 31% are without regulations. ANDI was developed in phases by WHO in collaboration with TDR, AFRO and EMRO, African Development Bank, etc. [220]. More on regulatory authorities in African and East African countries can be seen from [221,222]. |
| Caribbean | Pan American Health Organization (PAHO) [223], also operates in Central and South America | 1902, Washington DC | PAHO has assigned a task to ECRI to develop and coordinate programs for medical device safety and regulation |
| South America | Mercado Común del Sur (MERCOSÚR) [224], Argentina, Brazil, Paraguay, Uruguay, Venezuela Chile, Bolivia, Colombia, Ecuador and Peru | 1991, Montevideo (Uruguay) | regulation for medical devices, single approval scheme similar to EU, Products with FDA/EU marks having Free Sale Certificate (FSC) or a Certificate to Foreign Government (CFG) affirm they can be sold |
| Mexico | Federal Commission for the Protection against Sanitary Risk (COFEPRIS) [225] | 2001, Mexico | regulation of medical devices and IVDs. Mexico is also a member of APEC and HAFTA |
| Cuba | left for the State Control of Medicines, Equipment and Medical Devices (CEMED) [226], Cuba is also a member of GHTF | NA, La Habana | regulation of medical devices based on GHTF. CCEEM is in La Habana (Cuba) |
| Project | Application | Communication |
|---|---|---|
| Body Inertial Sensing | Meant for hospitals, where it provides information to measure three degrees of freedom | Body Sensor Networks (BSN) ZigBee/Bluetooth |
| Code Blue | Targets medical care to provide pulse rate, BP, and motion information | Intra-BAN (Wired), Inter-BAN (Zigbee, Mesh), Beyond-BAN (N/A) |
| LOBIN | Measures HR, BP, Temperature | Wireless Sensor Networks (IEEE 802.15.4) |
| MEDISN | Used in hospitals for emergency detection | WSN for monitoring patient physiological data and multi-hop wireless backbone for carrying these data |
| Unobstructive BAN | Applied in hospital and disaster events to generate alarms based on identified movements and postures | Intra-BAN is Low-power and short-range WBAN, Inter-BAN is Bluetooth, and or Beyond BAN is GSM |
| WPWS | Measures temperature, humidity, and velocity of air flow | RFID like system |
| BASUMA | Targeted application area is health monitoring for measuring ECG, Respirate/Breath Rate SpO2 | Intra-BAN (UWB), Inter-BAN (N/A), Beyond-BAN (N/A) |
| MobileHealth | Monitoring of patients ECG in ambulance | Intra-BAN (Manual), Inter-BAN (Zigbee, Bluetooth), Beyond-BAN (GPRS, UMTS) |
| AID-N | Reply BP, ECG, Pulse Rate in emergency systems | Intra-BAN (Wired), Inter-BAN (Zigbee, Bluetooth), Beyond-BAN (WiFi, Internet, Cellular Networks) |
| MAHS | Targets health application to provide information about breathing and pulse rate, body motion, temperature, pressure and SpO2. | Intra-BAN (Bluetooth), Inter-BAN (Zigbee), Beyond-BAN (Internet) |
| LifeMinder | Targets self-care applications. Used to report pulse rate, ECG, SpO2, temperature, body movement, emotional state intensity | Intra-BAN (Bluetooth), Inter-BAN (Bluetooth), Beyond-BAN (Internet) |
| SMART | Monitor patients ECG, SpO2 while sitting in waiting room | Intra-BAN (Wired), Inter-BAN (Bluetooth), Beyond-BAN (N/A) |
| CareNet | Targets remote healthcare applications to report BP, temperature and body inertial (posture and movement) information | Intra-BAN (N/A), Inter-BAN (Zigbee), Beyond-BAN (Internet, Multi-hop 802.11) |
| ASNET | Targets remote healthcare applications for providing patient BP, temperature information | Intra-BAN (Wired, WiFi), Inter-BAN (Wired, WiFi), Beyond-BAN (Internet, GSM,) |
| WHMS | Used in health for monitoring ECG/EKG | Intra-BAN (Wired), Inter-BAN (Wired, WiFi), Beyond-BAN (N/A) |
| Human++ | Provides entertaino-medical living standard with ECG, EMG, EEG facility | Intra-BAN (UWB), Inter- BAN (N/A), Beyond-BAN (N/A) |
| WiMoCA | Provides gesture detection in sports | Intra-BAN, Inter-BAN (Bluetooth), Beyond-BAN (WiFi, Cellular Networks) |
| Ayushman | Used in health monitoring and provides information about EKG, BP, SpO2 and body gesture | Intra-BAN (Zigbee), Inter-BAN (WiFi), Beyond-BAN (Internet) |
| Lifeguard | Applied in space and terrestrial applications to monitor ECG, respiration and pulse rate, SpO2 and body motion | Intra-BAN (Wired), Inter-BAN (Bluetooth, Internet), Beyond-BAN (Bluetooth/Internet) |
| IBBT IM3 | Used in Telemedicine and Telecare application and measures patient ECG, respiration and heart rate | Intra-BAN (N/A), Inter-BAN (N/A), Beyond-BAN (Internet) |
| MITHrl | Used in healthcare applications and measures patient ECG and EKG | Intra-BAN (Wired), Inter-BAN (WiFi), Beyond-BAN (N/A) |
| UbiMon | Used in healthcare application and measures patient ECG and EKG, SpO2 | Intra-BAN (Zigbee), Inter-BAN (WiFi/GPRS), Beyond-BAN (WiFi/GPRS) |
| H2020 MCSA ITN/EJD A-WEAR | Used in healthcare application and measures patient ECG and EKG, SpO2 | Intra-BAN (Zigbee), Inter-BAN (WiFi/GPRS), Beyond-BAN (WiFi/GPRS) |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Bhatti, D.S.; Saleem, S.; Imran, A.; Iqbal, Z.; Alzahrani, A.; Kim, H.; Kim, K.-I. A Survey on Wireless Wearable Body Area Networks: A Perspective of Technology and Economy. Sensors 2022, 22, 7722. https://doi.org/10.3390/s22207722
Bhatti DS, Saleem S, Imran A, Iqbal Z, Alzahrani A, Kim H, Kim K-I. A Survey on Wireless Wearable Body Area Networks: A Perspective of Technology and Economy. Sensors. 2022; 22(20):7722. https://doi.org/10.3390/s22207722
Chicago/Turabian StyleBhatti, David Samuel, Shahzad Saleem, Azhar Imran, Zafar Iqbal, Abdulkareem Alzahrani, HyunJung Kim, and Ki-Il Kim. 2022. "A Survey on Wireless Wearable Body Area Networks: A Perspective of Technology and Economy" Sensors 22, no. 20: 7722. https://doi.org/10.3390/s22207722
APA StyleBhatti, D. S., Saleem, S., Imran, A., Iqbal, Z., Alzahrani, A., Kim, H., & Kim, K.-I. (2022). A Survey on Wireless Wearable Body Area Networks: A Perspective of Technology and Economy. Sensors, 22(20), 7722. https://doi.org/10.3390/s22207722






