Localization of a Power-Modulated Jammer
Abstract
:1. Introduction
2. Related Work
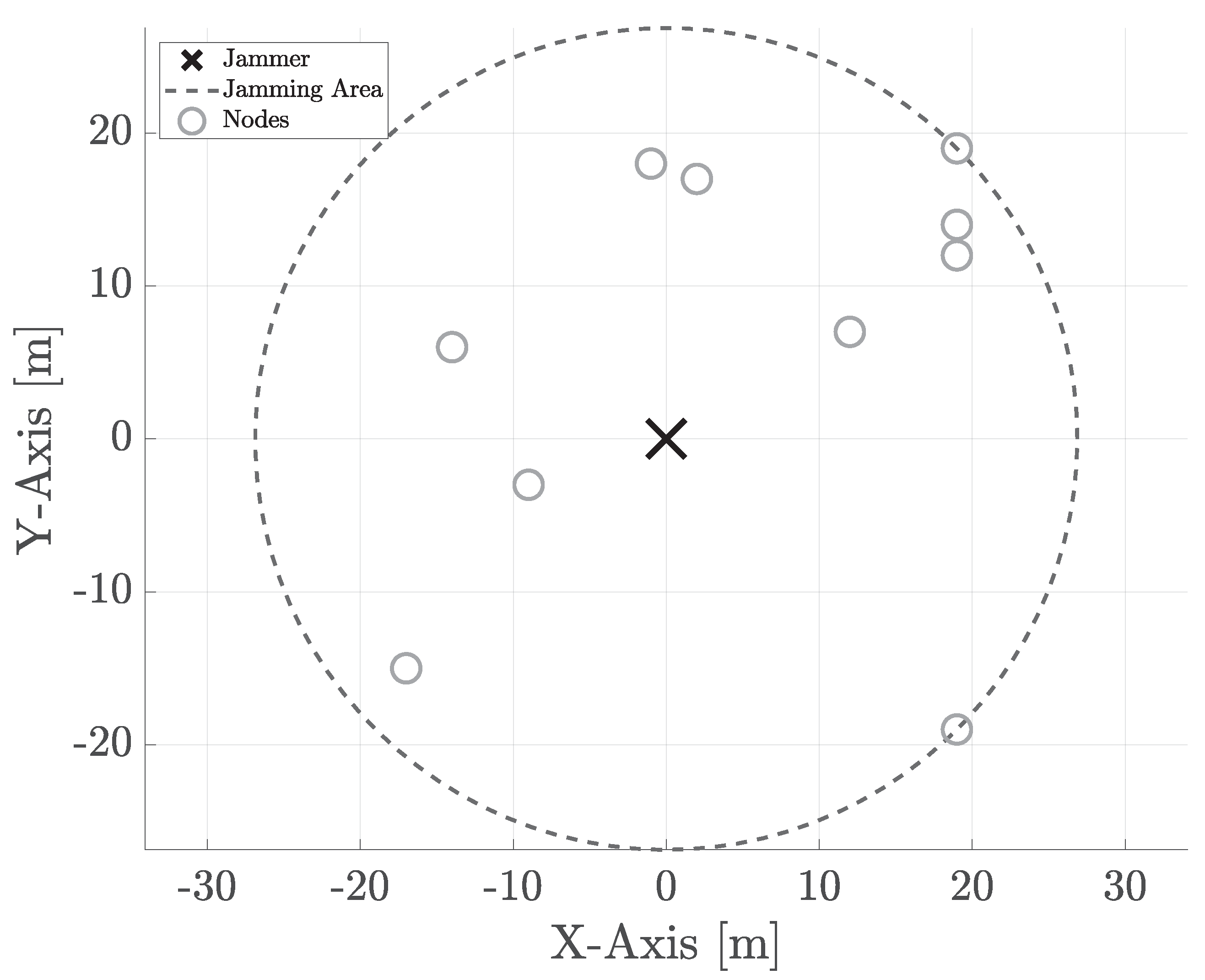
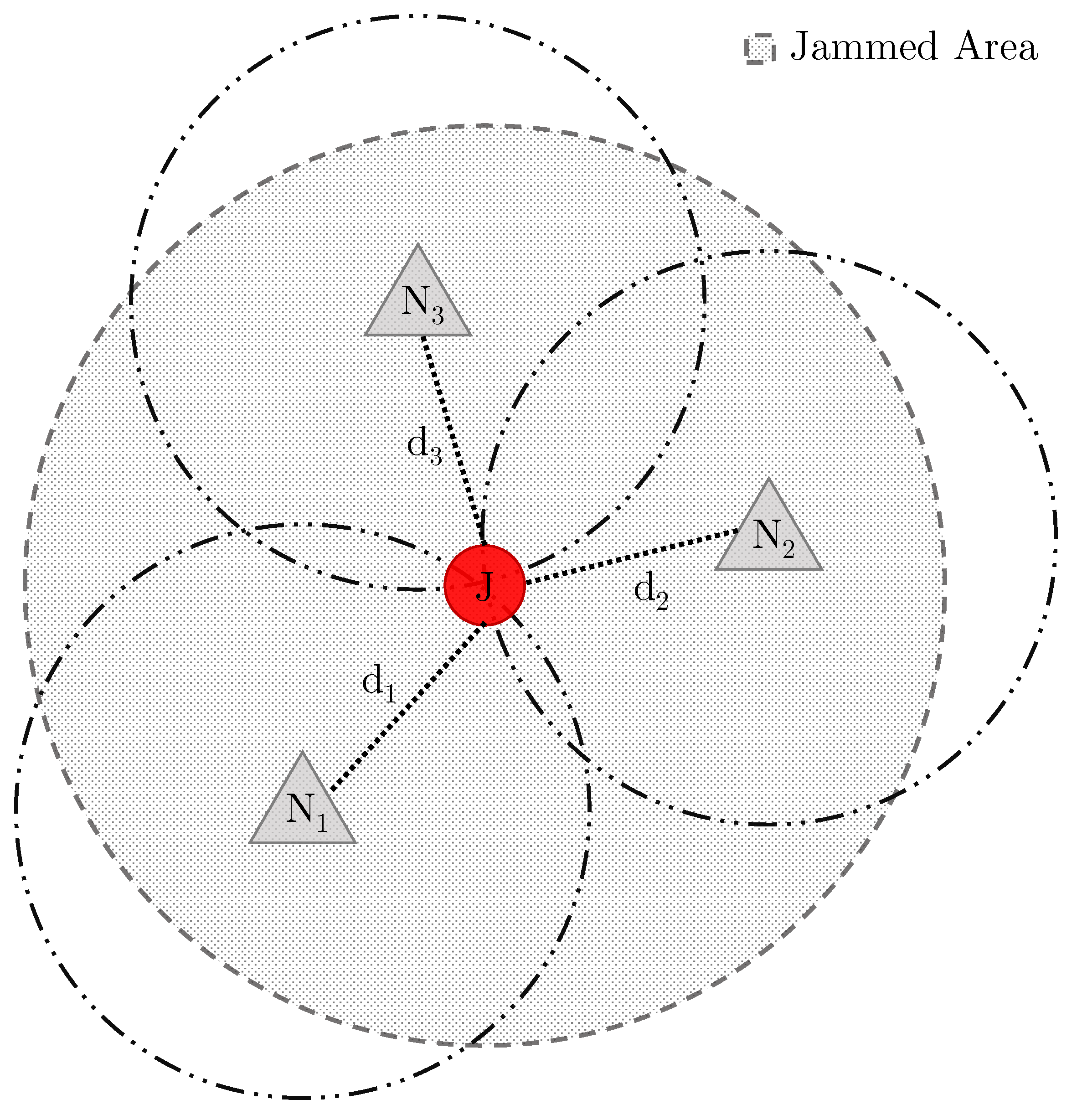
3. Scenario and Assumptions
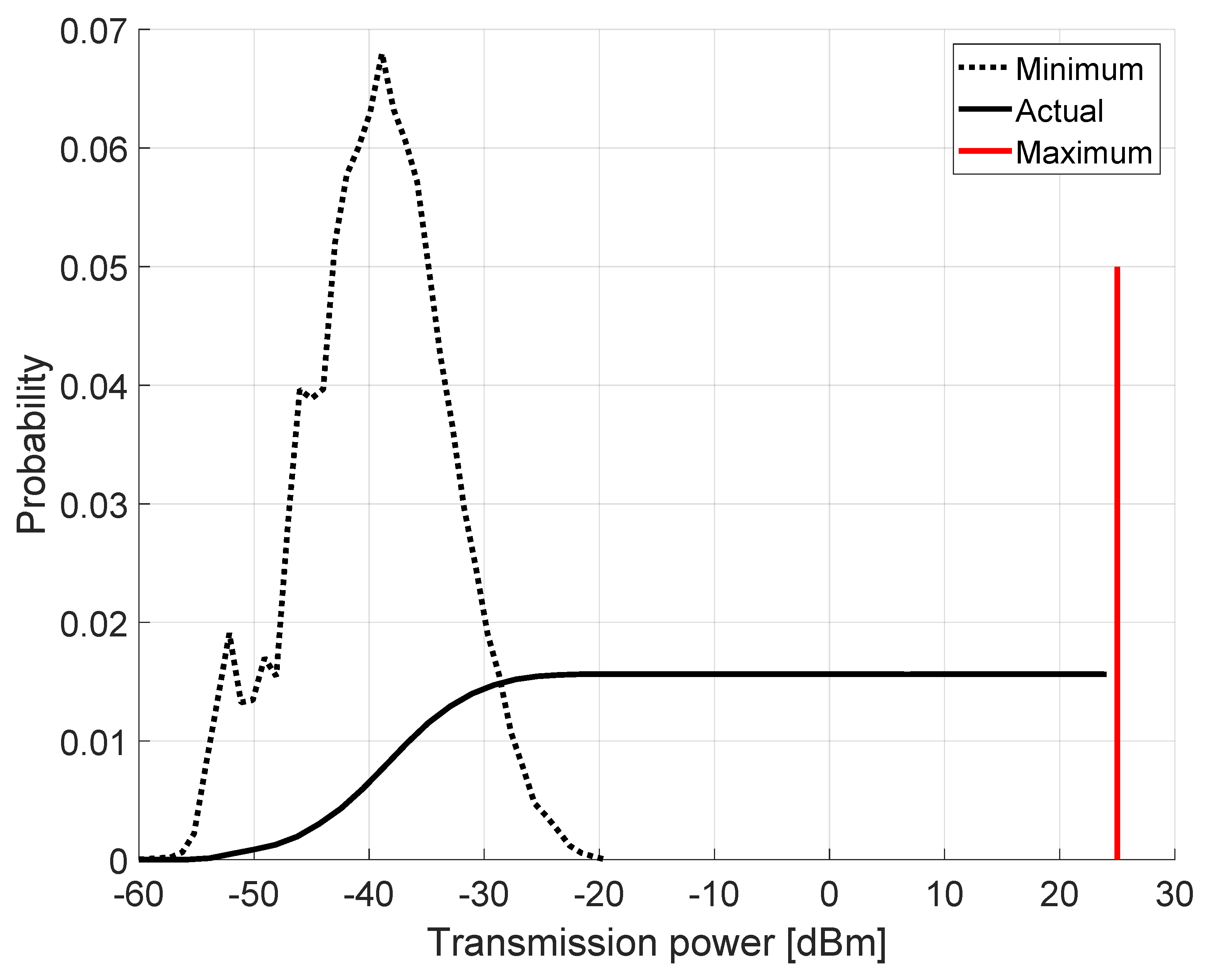
Constant and Power-Modulated Jammer
4. Jammer Localization
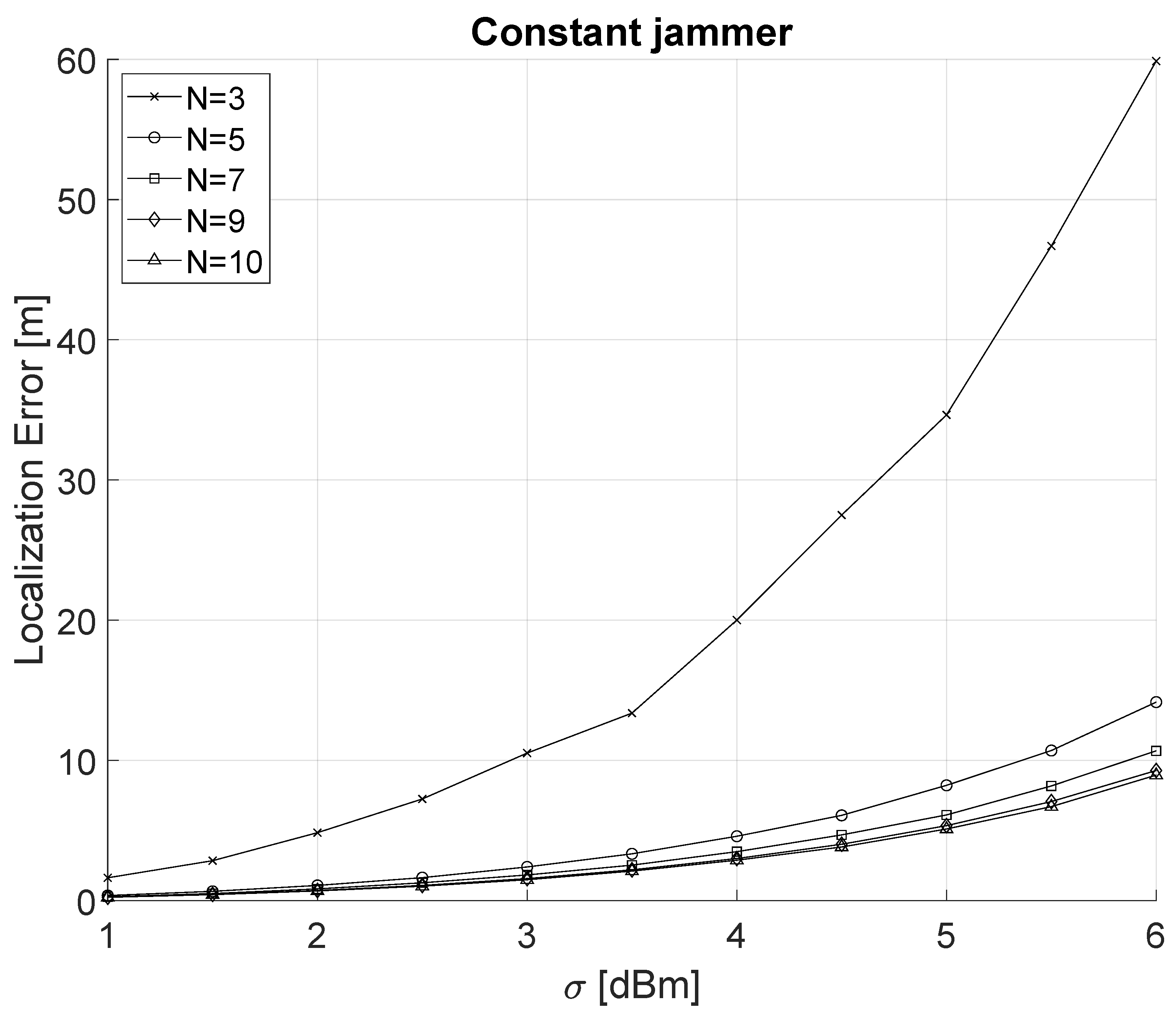
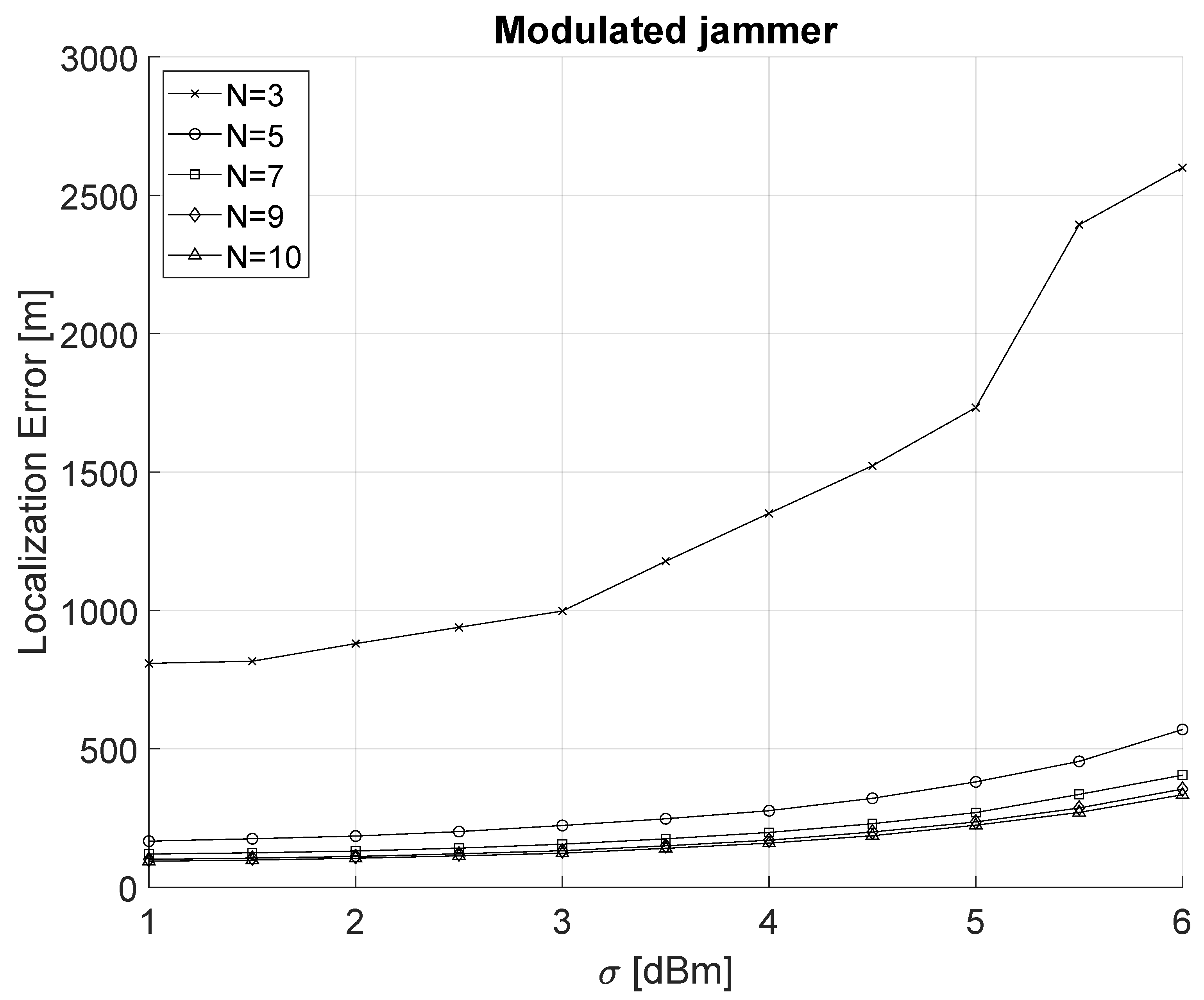
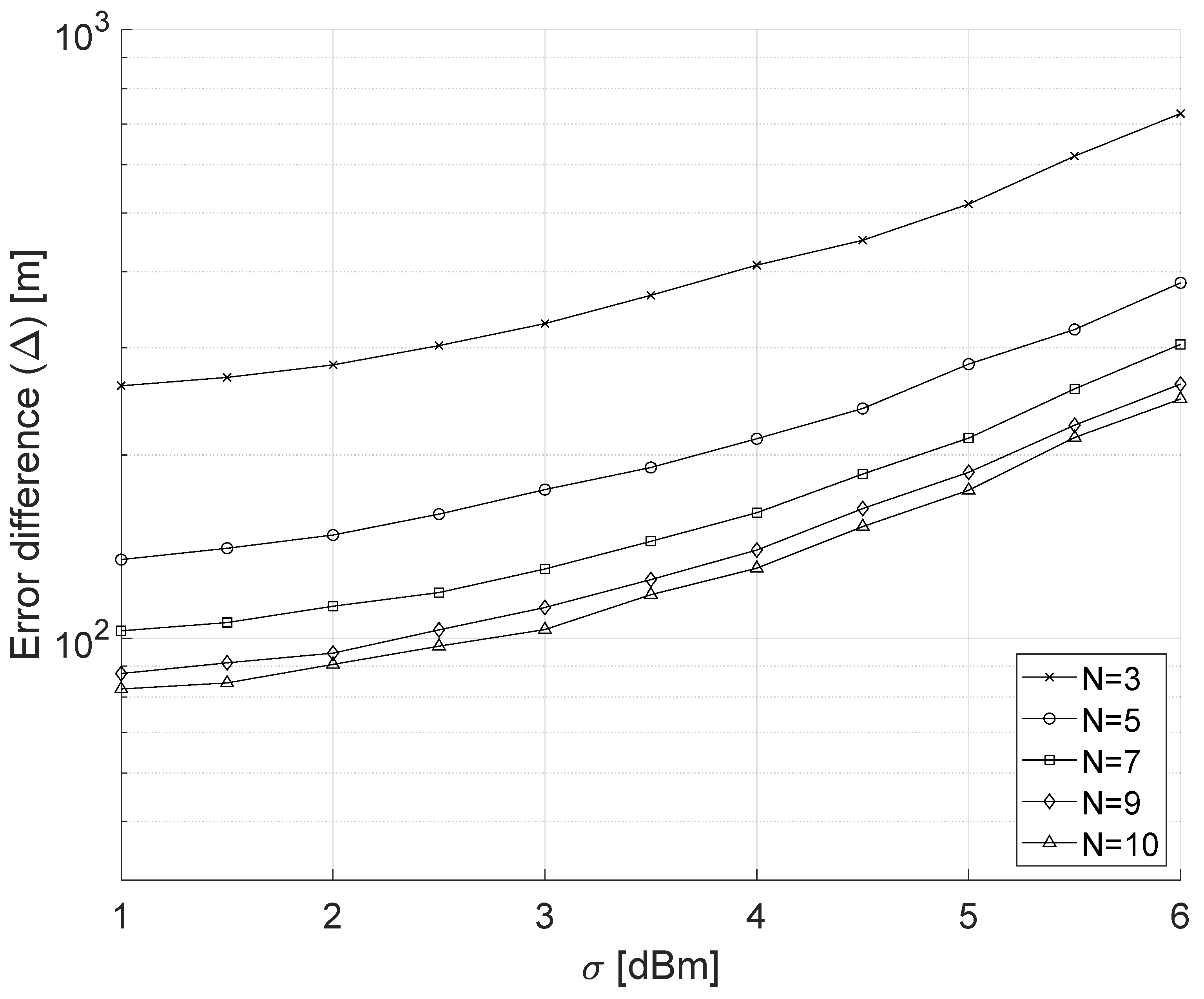
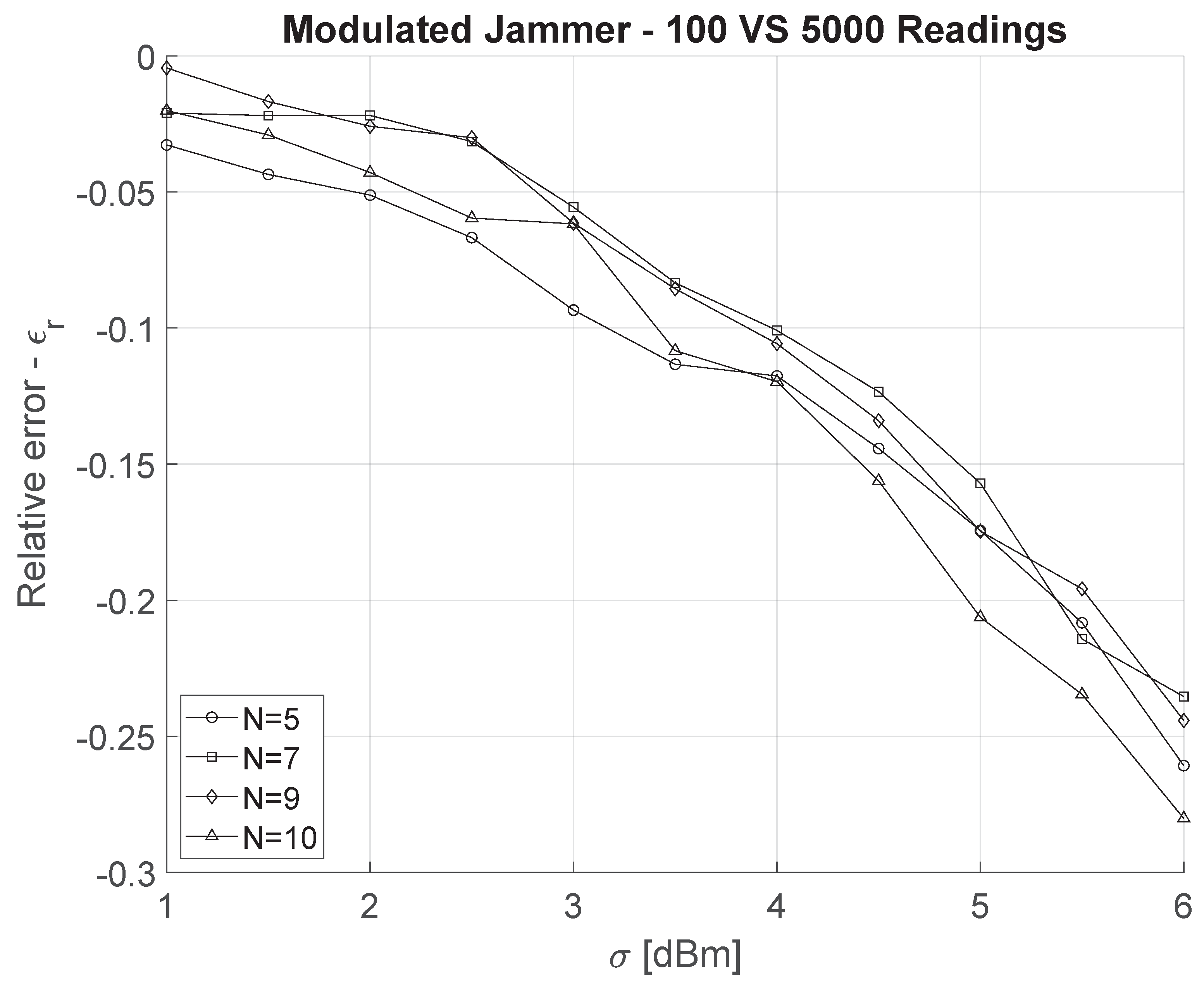
5. Discussion
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Zhang, L.; Ren, J.; Li, T. Time-Varying Jamming Modeling and Classification. IEEE Trans. Signal Process. 2012, 60, 3902–3907. [Google Scholar] [CrossRef]
- Sciancalepore, S.; Di Pietro, R. Bittransfer: Mitigating Reactive Jamming in Electronic Warfare Scenarios. IEEE Access 2019, 7, 156175–156190. [Google Scholar] [CrossRef]
- Di Pietro, R.; Oligeri, G. GopJam: Key-less jamming mitigation via gossiping. J. Netw. Comput. Appl. 2018, 123, 57–68. [Google Scholar] [CrossRef]
- Di Pietro, R.; Oligeri, G. Enabling broadcast communications in presence of jamming via probabilistic pairing. Comput. Netw. 2017, 116, 33–46. [Google Scholar] [CrossRef]
- Di Pietro, R.; Oligeri, G. Freedom of speech: Thwarting jammers via a probabilistic approach. In Proceedings of the 8th ACM Conference on Security & Privacy in Wireless and Mobile Networks, New York, NY, USA, 22–26 June 2015; pp. 1–6. [Google Scholar]
- Di Pietro, R.; Oligeri, G. Silence is golden: Exploiting jamming and radio silence to communicate. ACM Trans. Inf. Syst. Secur. (TISSEC) 2015, 17, 1–24. [Google Scholar] [CrossRef]
- Jameel, F.; Wyne, S.; Kaddoum, G.; Duong, T.Q. A Comprehensive Survey on Cooperative Relaying and Jamming Strategies for Physical Layer Security. IEEE Commun. Surv. Tutor. 2018, 21, 2734–2771. [Google Scholar] [CrossRef] [Green Version]
- Wei, X.; Wang, Q.; Wang, T.; Fan, J. Jammer Localization in Multi-Hop Wireless Network: A Comprehensive Survey. IEEE Commun. Surv. Tutorials 2017, 19, 765–799. [Google Scholar] [CrossRef]
- Pelechrinis, K.; Koutsopoulos, I.; Broustis, I.; Krishnamurthy, S.V. Lightweight Jammer Localization in Wireless Networks: System Design and Implementation. In Proceedings of the GLOBECOM 2009—2009 IEEE Global Telecommunications Conference, Honolulu, HI, USA, 30 November–4 December 2009; pp. 1–6. [Google Scholar]
- Wang, Q.; Wei, X.; Fan, J.; Wang, T.; Sun, Q. A step further of PDR-based jammer localization through dynamic power adaptation. In Proceedings of the 11th International Conference on Wireless Communications, Networking and Mobile Computing (WiCOM 2015), Shanghai, China, 21–23 September 2015; pp. 1–6. [Google Scholar]
- Kim, Y.S.; Mokaya, F.; Chen, E.; Tague, P. All your jammers belong to us—Localization of wireless sensors under jamming attack. In Proceedings of the 2012 IEEE International Conference on Communications (ICC), Ottawa, ON, Canada, 10–15 June 2012; pp. 949–954. [Google Scholar]
- Liu, Z.; Liu, H.; Xu, W.; Chen, Y. Exploiting Jamming-Caused Neighbor Changes for Jammer Localization. IEEE Trans. Parallel Distrib. Syst. 2012, 23, 547–555. [Google Scholar] [CrossRef]
- Liu, H.; Wenyuan, X.; Chen, Y.; Liu, Z. Localizing jammers in wireless networks. In Proceedings of the 2009 IEEE International Conference on Pervasive Computing and Communications, Galveston, TX, USA, 9–13 March 2009; pp. 1–6. [Google Scholar]
- Liu, H.; Liu, Z.; Chen, Y.; Xu, W. Localizing Multiple Jamming Attackers in Wireless Networks. In Proceedings of the 2011 31st International Conference on Distributed Computing Systems, Minneapolis, MN, USA, 20–24 June 2011; pp. 517–528. [Google Scholar]
- Sun, Y.; Molva, R.; Önen, M.; Wang, X.; Zhou, X. Catch the Jammer in Wireless Sensor Network. In Proceedings of the 2011 IEEE 22nd International Symposium on Personal, Indoor and Mobile Radio Communications, Toronto, ON, Canada, 11–14 September 2011; pp. 1156–1160. [Google Scholar]
- Tedeschi, P.; Oligeri, G.; Di Pietro, R. Leveraging jamming to help drones complete their mission. IEEE Access 2019, 8, 5049–5064. [Google Scholar] [CrossRef]
- Cheng, T.; Li, P.; Zhu, S. An Algorithm for Jammer Localization in Wireless Sensor Networks. In Proceedings of the 2012 IEEE 26th International Conference on Advanced Information Networking and Applications, Fukuoka, Japan, 26–29 March 2012; pp. 724–731. [Google Scholar]
- Cheng, T.; Li, P.; Zhu, S.; Torrieri, D. M-cluster and X-ray: Two methods for multi-jammer localization in wireless sensor networks. Integr. Comput.-Aided Eng. 2014, 21, 19–34. [Google Scholar] [CrossRef] [Green Version]
- Bhamidipati, S.; Gao, G.X. Locating Multiple GPS Jammers Using Networked UAVs. IEEE Internet Things J. 2019, 6, 1816–1828. [Google Scholar] [CrossRef]
- Liu, Z.; Liu, H.; Xu, W.; Chen, Y. Wireless Jamming Localization by Exploiting Nodes’ Hearing Ranges. In Distributed Computing in Sensor Systems; Rajaraman, R., Moscibroda, T., Dunkels, A., Scaglione, A., Eds.; Springer: Berlin/Heidelberg, Germany, 2010; pp. 348–361. [Google Scholar]
- CRI-LAB. Open-source code of the implementation of Power Modulated Jammer. Available online: https://github.com/pietrotedeschi/power-modulated-jammer/ (accessed on 2 January 2022).
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Tedeschi, P.; Oligeri, G.; Di Pietro, R. Localization of a Power-Modulated Jammer. Sensors 2022, 22, 646. https://doi.org/10.3390/s22020646
Tedeschi P, Oligeri G, Di Pietro R. Localization of a Power-Modulated Jammer. Sensors. 2022; 22(2):646. https://doi.org/10.3390/s22020646
Chicago/Turabian StyleTedeschi, Pietro, Gabriele Oligeri, and Roberto Di Pietro. 2022. "Localization of a Power-Modulated Jammer" Sensors 22, no. 2: 646. https://doi.org/10.3390/s22020646
APA StyleTedeschi, P., Oligeri, G., & Di Pietro, R. (2022). Localization of a Power-Modulated Jammer. Sensors, 22(2), 646. https://doi.org/10.3390/s22020646





