Identification of IoT Actors
Abstract
1. Introduction
2. The Data Protection and Privacy Legislative Landscape in the EU
2.1. GDPR and Implementation Guidelines
2.2. Draft ePrivacy Regulation
3. IoT Components
3.1. Thing
3.2. Device
- Devices with no processing capabilities (a low-cost device with no microcontrollers and without processing capabilities);
- Devices with low processing capabilities (a low-cost device with very limited microcontrollers and processing capabilities, used only for reading or writing data from/to sensors/actuators and sending or receiving those data);
- Devices with high processing capabilities (devices with processing capabilities for making decisions, running algorithms, and directly coordinating with other devices).
- Device with low processing and low connectivity (LPLC);
- Device with low processing and high connectivity (LPHC);
- Device with high processing and high connectivity (HPHC).
3.3. Gateway
3.4. Connectivity Network
- High range, high power consumption, and high bandwidth (Cellular, Satellite);
- High range, low power consumption, and low bandwidth (LPWANs);
- Low range, low power consumption, and high bandwidth (Ethernet, Bluetooth, Wi-Fi).
3.5. IoT Platforms
- Connectivity platforms;
- Device management platforms;
- Cloud platforms;
- Application enablement platforms;
- Advanced analytics platforms.
3.6. IoT Application Server
3.7. IoT Application
3.8. IoT Service
3.9. IoT User
3.10. End User
3.11. IoT Data Protection and Privacy
3.12. IoT Security
- Regulatory certification (FCC, EC);
- Industry Certification;
- Telecoms: the two main Telecoms Industry certification schemes are the Global Certification Forum (GCF) and the PCS Type Certification Review Board (PTCRB);
- Operator Certification (Deutsche Telecom, Verizon, AT&T).
4. Computing in the IoT Ecosystem
- Packet loss and higher latency;
- Unreliability of short-range radio communications in the IoT area network;
- Network overload due to large amount of traffic to be processed.
4.1. Computing Models
- The edge layer, where data management takes place within the sensors themselves;
- The fog layer, where data management takes place within the gateways and transit network;
- The cloud layer, where data management takes place within the cloud data centre.
4.2. Fog, Edge, Mist, and Dew Hardware Computing Locations
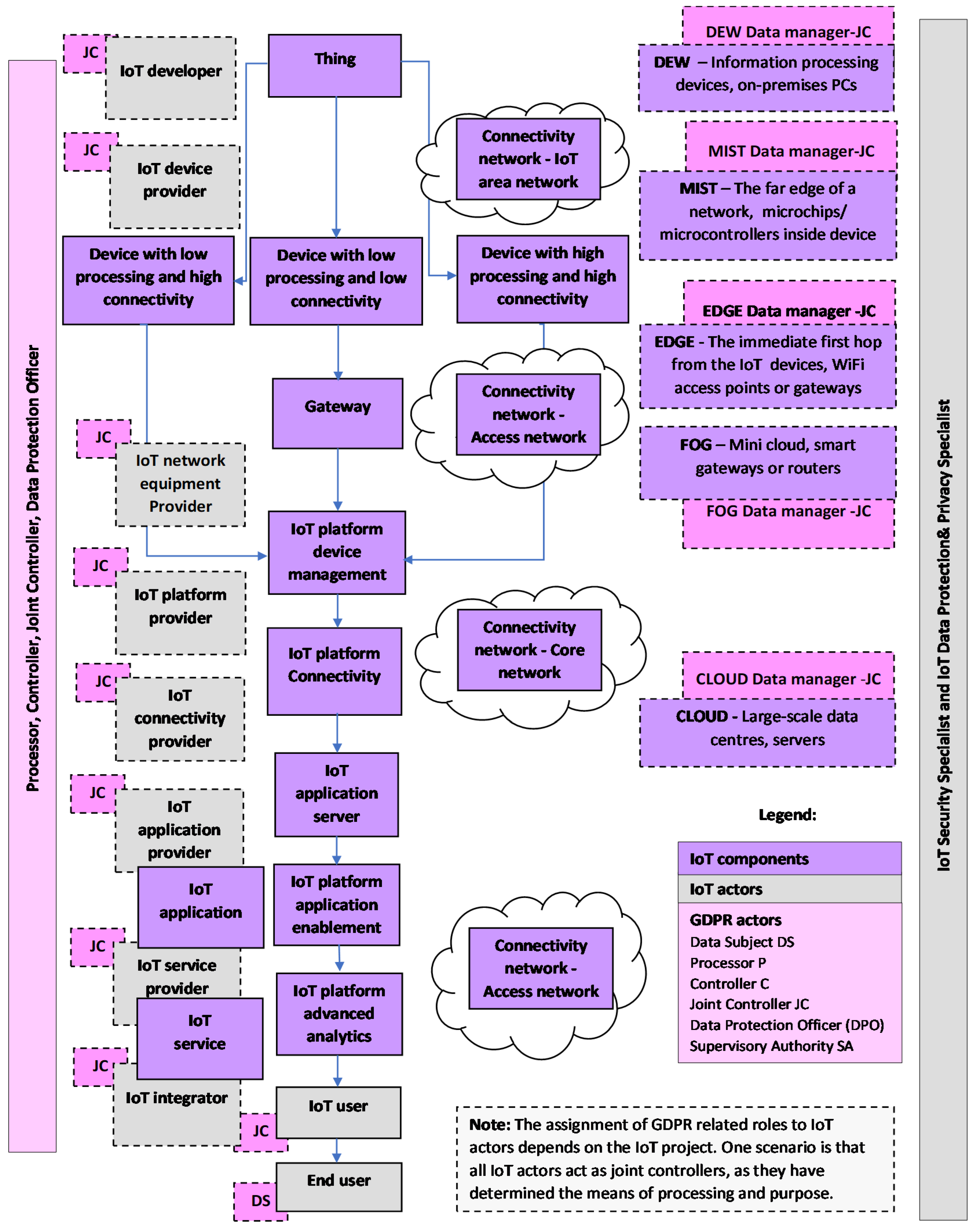
5. IoT Actors
- The device provider provides devices to the network provider and application provider;
- The network provider performs access and integration of other provider resources, provides IoT capabilities and their support and management of their infrastructure, and provides network capabilities and resources to different providers;
- The platform provider provides capabilities to application providers, such as data storage, data processing, device management, integration capabilities, and open interfaces;
- The application provider provides IoT applications to application customers while using capabilities or resources of the network provider, device provider, and platform provider;
- The application customer is the user of the IoT applications provided by the applications provider.
6. IoT Model
6.1. Methodology for Identifying IoT Components and IoT Actors
6.2. Methodology for Identifying Relevant GDPR Actors
7. Current Status and Collaborative Regulatory Approach
8. Data Brokers, Gatekeepers, and Other Actors
- Data providers;
- Multiple data brokers who collect raw data from various source and sells big data;
- The data service provider who utilize big data from the data brokers;
- Service consumer.
9. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Cisco Annual Internet Report (2018–2023) White Paper. Available online: https://www.cisco.com/c/en/us/solutions/collateral/executive-perspectives/annual-internet-report/white-paper-c11-741490.html (accessed on 1 March 2021).
- Ibarra-Esquer, J.E.; González-Navarro, F.F.; Flores-Rios, B.L.; Burtseva, L.; Astorga-Vargas, M.A. Tracking the Evolution of the Internet of Things Concept Across Different Application Domains. Sensors 2017, 17, 1379. [Google Scholar] [CrossRef] [PubMed]
- IEEE Internet of Things: Contribute to the Ever-Changing Definition of IoT. Available online: https://iot.ieee.org/definition.html (accessed on 1 March 2021).
- Jakobs, K. Standardizing the IoT and its Applications—Learning from the Past?! In Internet of Things–Concepts, Technologies, Applications, and Implementations; John Wiley & Sons: Hoboken, NJ, USA, 2018; pp. 191–218. [Google Scholar]
- Y.4000: Overview of the Internet of Things. Available online: https://www.itu.int/rec/T-REC-Y.4000/en (accessed on 1 March 2021).
- Y.4100: Common Requirements of the Internet of Things. Available online: https://www.itu.int/rec/T-REC-Y.4100/en (accessed on 1 March 2021).
- Y.4114: Specific Requirements and Capabilities of the Internet of Things for Big Data. Available online: https://www.itu.int/rec/T-REC-Y.4114-201707-I (accessed on 1 March 2021).
- Global ICT Regulatory Outlook 2020—Pointing the Way forward to Collaborative Regulation. Available online: https://www.itu.int/pub/D-PREF-BB.REG_OUT01 (accessed on 1 March 2021).
- Regulation (EU) 2016/679 of the European Parliament and of the Council of 27 April 2016 on the Protection of Natural Persons with Regard to the Processing of Personal Data and on the Free Movement of Such Data, and Repealing Directive 95/46/EC (General Data Protection Regulation) (Text with EEA Relevance) OJ L 119, 4.5.2016. pp. 1–88. Available online: https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A02016R0679-20160504 (accessed on 1 March 2021).
- European Commission (2017). Proposal for a Regulation of the European Parliament and of the Council Concerning the Respect for Private Life and the Protection of Personal Data in Electronic Communications and Repealing Directive 2002/58/EC (Regulation on Privacy and Electronic Communications) COM/2017/010 Final-2017/03 (COD). Available online: https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A52017PC0010 (accessed on 1 March 2021).
- Alshohoumi, F.; Sarrab, M.; Alhamadani, A.; Al-Abri, D. Systematic Review of Existing IoT Architectures Security and Privacy Issues and Concerns. Int. J. Adv. Comput. Sci. Appl. 2019, 10. [Google Scholar] [CrossRef]
- Lynn, T.; Endo, P.T.; Ribeiro, A.M.N.C.; Barbosa, G.B.N.; Rosati, P. The Internet of Things: Definitions, Key Concepts, and Reference Architectures. In The Cloud-to-Thing Continuum; Lynn, T., Mooney, J., Lee, B., Endo, P.T., Eds.; Palgrave Macmillan: London, UK, 2020. [Google Scholar] [CrossRef]
- Y.4113: Requirements of the Network for the Internet of Things. Available online: https://www.itu.int/rec/T-REC-Y.4113/en (accessed on 1 March 2021).
- Hanes, D.; Salgueiro, G.; Grossetete, P.; Barton, R.; Henry, J. IoT Fundamentals: Networking Technologies, Protocols, and Use Cases for the Internet of Things; Cisco Press: Indianapolis, IN, USA, 2017. [Google Scholar]
- Iorgam, M.L.; Feldman, R.; Barton, M.J.; Martin, N.; Goren, C. Mahmoudi. Fog ComputingConceptual Model— Recommendations of the National Institute of Standards and Technology. Available online: https://www.nist.gov/publications/fog-computing-conceptual-model (accessed on 1 March 2021).
- Y.4460: Architectural Reference Models of Devices for Internet of Things Applications. Available online: https://www.itu.int/rec/T-REC-Y.4460/en (accessed on 1 March 2021).
- Weber, M.; Žarko, I.P. A Regulatory View on Smart City Services. Sensors 2019, 19, 415. [Google Scholar] [CrossRef] [PubMed]
- Yousefpour, A.; Fung, C.; Nguyen, T.; Kadiyala, K.; Jalali, F.; Niakanlahiji, A.; Kong, J.; Jue, J.P. All one needs to know about fog computing and related edge computing paradigms: A complete survey. J. Syst. Arch. 2019, 98, 289–330. [Google Scholar] [CrossRef]
- Ray, P.P. An Introduction to Dew Computing: Definition, Concept and Implications. IEEE Access 2018, 6, 723–737. [Google Scholar] [CrossRef]
- Šojat, Z.; Skala, K. Views on the role and importance of dew computing in the service and control technology. In Proceedings of the 2016 39th International Convention on Information and Communication Technology, Electronics and Microelectronics (MIPRO), Opatija, Croatia, 30 May–3 June 2016; pp. 164–168. [Google Scholar]
- Technical Specification D2.1—Data Processing and Management Framework for IoT and Smart Cities and Communities. Available online: http://handle.itu.int/11.1002/pub/813b0846-en (accessed on 1 March 2021).
- European Data Protection Supervisor Guidelines on the Concepts of Controller, Processor and Joint Controllership under Regulation (EU) 2018/1725, 7 November 2019. Available online: https://edps.europa.eu/data-protection/our-work/our-work-by-type/guidelines_en (accessed on 1 March 2021).
- European Data Protection Board Guidelines 07/2020 on the Concepts of Controller and Processor in the GDPR. Available online: https://edpb.europa.eu/our-work-tools/public-consultations-art-704/2020/guidelines-072020-concepts-controller-and-processor_en (accessed on 1 March 2021).
- ETSI TR 103 591 V1.1.1 82019-10 SmartM2M; Privacy Study Report; Standards Landscape and Best Practices. Available online: https://www.etsi.org/deliver/etsi_tr/103500_103599/103591/01.01.01_60/tr_103591v010101p.pdf (accessed on 1 March 2021).
- Information Commissioner’s Office: What Needs to be Included in the Contract? Available online: https://ico.org.uk/for-organisations/guide-to-data-protection/guide-to-the-general-data-protection-regulation-gdpr/contracts-and-liabilities-between-controllers-and-processors-multi/what-needs-to-be-included-in-the-contract/#11 (accessed on 25 November 2020).
- European Commission Communications (2020), Data Protection as a Pillar of Citizens’ Empowerment and the EU’s Approach to the Digital Transition—Two Years of Application of the General Data Protection Regulation COM/2020/264 Final. Available online: https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A52020DC0264 (accessed on 1 March 2021).
- BEREC Report on the Data Economy. Available online: https://berec.europa.eu/eng/document_register/subject_matter/berec/reports/8599-berec-report-on-the-data-economy (accessed on 1 March 2021).
- Zantalis, F.; Koulouras, G.; Karabetsos, S.; Kandris, D. A Review of Machine Learning and IoT in Smart Transportation. Futur. Internet 2019, 11, 94. [Google Scholar] [CrossRef]
- Mackenzie, M.; Rebbeck, T. What Is the IoT Value Chain and Why Is It Important? Available online: https://www.analysysmason.com/research/content/comments/iot-value-chain-rdme0/ (accessed on 1 March 2021).
- Synergy Consulting Group. Enabling the IoT Ecosystem with Policy and Regulation How Policymakers and Regulators Can Encourage Sustainable Market Growth. Available online: https://www.synergyconsulting.ae/insights/enabling-iot-ecosystem-policy-regulation/ (accessed on 1 March 2021).
- Paradis, I. International Carriers’ Path to the IoT Gold Mine, The Mobile Century. Available online: http://themobilecentury.com/international-carriers-path-to-the-iot-gold-mine/ (accessed on 1 March 2021).
- Cicciari, M. The internet of word-things. IEEE Spectr. 2016, 53, 25. [Google Scholar] [CrossRef]
- Y.2222: Sensor Control Networks and Related Applications in a Next Generation Network Environment. Available online: https://www.itu.int/rec/T-REC-Y.2222-201304-I/en (accessed on 1 March 2021).
- IoT Device Certification Landscape. Available online: https://www.gsma.com/iot/resources/iot-device-certification-landscape/ (accessed on 1 March 2021).
- Elizalde, D. How Does an IoT Device Work? Available online: https://danielelizalde.com/iot-hw-blocks/ (accessed on 1 March 2021).
- Y.4101: Common Requirements and Capabilities of a Gateway for Internet of Things Applications. Available online: https://www.itu.int/rec/T-REC-Y.4101-201710-I/en (accessed on 1 March 2021).
- IoT 101: An Introduction to the Internet of Things, First Edition. Available online: https://www.leverege.com/ebooks/iot-intro-ebook (accessed on 1 March 2021).
- IoT Analytics: IoT Platforms Company Landscape 2020. Available online: https://iot-analytics.com/product/iot-platforms-landscape-database-2020/ (accessed on 1 March 2021).
- JT Solutions IoT Blog—The 5 Types of IoT Platforms. Available online: https://blog.jtiot.com/the-5-types-of-iot-platforms (accessed on 1 March 2021).
- Lucero, S. IoT Platforms: Enabling the Internet of Things, White Paper, IHS Technology. Available online: https://cdn.ihs.com/www/pdf/enabling-IOT.pdf (accessed on 1 March 2021).
- Y.4208: Internet of Things Requirements for Support of Edge Computing. Available online: https://www.itu.int/rec/T-REC-Y.4208/en (accessed on 1 March 2021).
- Y.101: Global Information Infrastructure Terminology: Terms and Definitions. Available online: https://www.itu.int/rec/T-REC-Y.101-200003-I/en (accessed on 1 March 2021).
- BEREC Report on Enabling the Internet of Things. Available online: https://berec.europa.eu/eng/document_register/subject_matter/berec/reports/5755-berec-report-on-enabling-the-internet-of-things (accessed on 1 March 2021).
- M.3050.1: Enhanced Telecom Operations Map (eTOM)—The Business Process Framework. Available online: https://www.itu.int/rec/T-REC-M.3050.1/en (accessed on 1 March 2021).
- Internet of Things Security is More Challenging Than Cybersecurity, White Paper, Wind River Systems, Inc. Rev. Available online: https://www.windriver.com/whitepapers/security/iot-security-is-more-challenging-than-cybersecurity (accessed on 1 March 2021).
- Fagan, M.; Fagan, M.; Megas, K.N.; Scarfone, K.; Smith, M. Foundational Cybersecurity Activities for IoT Device Manufacturers—The National Institute of Standards and Technology (NIST) U.S. Department of Commerce. Available online: https://csrc.nist.gov/publications/detail/nistir/8259/final (accessed on 1 March 2021).
- Fagan, M.; Megas, K.N.; Scarfone, K.; Smith, M. IoT Device Cybersecurity Capability Core Baseline—The National Institute of Standards and Technology (NIST). Available online: https://csrc.nist.gov/publications/detail/nistir/8259a/final (accessed on 1 March 2021).
- EUROSMART. The Voice of The Digital Security Industry. Available online: https://www.eurosmart.com/who-we-are/#members (accessed on 1 March 2021).
- CYBER—Cyber Security for Consumer Internet of Things: Baseline Requirements. Available online: https://www.etsi.org/deliver/etsi_en/303600_303699/303645/02.01.00_30/en_303645v020100v.pdf (accessed on 1 March 2021).
- ENISA Advisory Group—Opinion Consumers and IoT Security. Available online: https://www.enisa.europa.eu/about-enisa/structure-organization/advisory-group/ag-publications/final-opinion-enisa-ag-consumer-iot-perspective-09.2019 (accessed on 1 March 2021).
- Silva, R.; Silva, J.S.; Boavida, F. Opportunistic fog computing: Feasibility assessment and architectural proposal. In Proceedings of the 2017 IFIP/IEEE Symposium on Integrated Network and Service Management (IM), Lisbon, Portugal, 8–12 May 2017; pp. 510–516. [Google Scholar] [CrossRef]
- Jiang, J.; Li, Z.; Tian, Y.; Al-Nabhan, N. A Review of Techniques and Methods for IoT Applications in Collaborative Cloud-Fog Environment. Secur. Commun. Networks 2020, 2020, 1–15. [Google Scholar] [CrossRef]
- Li, Z.; Wang, Y. An Introduction and Comparison of the Application of Cloud and Fog in IoT. In Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering; Springer Nature: Cham, Switzerland, 2020; pp. 63–75. [Google Scholar]
- Bonomi, F.; Milito, R.; Zhu, J.; Addepalli, S. Fog computing and its role in the Internet of Things. In Proceedings of the first edition of the MCC workshop on Mobile cloud computing, Helsinki, Finland, 13–17 August 2012; pp. 13–16. [Google Scholar]
- Cisco—What is Edge Computing. Available online: https://www.cisco.com/c/en/us/solutions/computing/what-is-edge-computing.html (accessed on 25 November 2020).
- Yingwei, W.; Skala, K.; Rindos, A.; Gusev, M.; Shuhui, Y.; Yi, P. Dew Computing and Transition of Internet Computing Paradigms, ZTE Communications, No.4 2017, No.59. Available online: https://www.zte.com.cn/global/about/magazine/zte-communications/2017/4/en_222/466311.html (accessed on 1 March 2021).
- Naveen, J. Fog vs Edge vs Mist Computing: Which One Is the Most Suitable for Your Business? Available online: https://www.allerin.com/blog/fog-vs-edge-vs-mist-computing-which-one-is-the-most-suitable-for-your-business (accessed on 1 March 2021).
- Rahman, A.U.; Afsana, F.; Mahmud, M.; Kaiser, M.S.; Ahmed, M.R.; Kaiwartya, O.; James-Taylor, A. Toward a Heterogeneous Mist, Fog, and Cloud-Based Framework for the Internet of Healthcare Things. IEEE Internet Things J. 2019, 6, 4049–4062. [Google Scholar] [CrossRef]
- Dolui, K.; Datta, S.K. Comparison of edge computing implementations: Fog computing, cloudlet and mobile edge computing. 2017 Global Internet of Things Summit (GIoTS) 2017, 1–6. [Google Scholar] [CrossRef]
- Varghese, B.; Wang, N.; Nikolopoulos, D.S.; Buyya, R. Feasibility of Fog Computing. Available online: https://www.academia.edu/31011430/Feasibility_of_Fog_Computing (accessed on 1 March 2021).
- Jagannath, U.R.; Saravanan, S.; Suguna, S.K. Applications of the Internet of Things with the Cloud Computing Technologies: A Review. In Edge Computing. EAI/Springer Innovations in Communication and Computing; Al-Turjman, F., Ed.; Springer Nature: Cham, Switzerland, 2018. [Google Scholar] [CrossRef]
- Mahesa, R. How Cloud, Fog, and Mist Computing Can Work Together. Available online: https://ibmcode-staging.us-east.containers.mybluemix.net/articles/how-cloud-fog-and-mist-computing-can-work-together/ (accessed on 1 March 2021).
- Roberts, P. IBM and Samsung Bet on Bitcoin Tech to Save the Internet of Things, The Security Ledger. Available online: https://securityledger.com/2015/01/ibm-and-samsung-bet-on-bitcoin-to-save-iot/ (accessed on 1 March 2021).
- Document, No. 1: A Mapping of Arcep and Its Partners’ Understanding of the Issues Pertaining to the Internet of Things. Available online: https://en.arcep.fr/news/press-releases/p/n/arcep-and-its-partners-publish-a-white-paper-to-prepare-for-the-internet-of-things-revolution-to-en.html (accessed on 1 March 2021).
- Kar, S.; Chakravorty, B.; Sinha, S.; Gupta, M.P. Analysis of stakeholders within IoT ecosystem. In Digital India. Advances in Theory and Practice of Emerging Markets; Kar, A., Sinha, S., Gupta, M., Eds.; Springer Nature: Cham, Switzerland; ISBN 978-3-319-78377-2.
- GSMA—What’s Unique about the IoT? Available online: https://www.gsma.com/iot/whats-unique-iot/ (accessed on 1 March 2021).
- OECD—IoT Measurement and Applications. OECD Digital Economy Papers 2018. Available online: https://www.oecd-ilibrary.org/science-and-technology/iot-measurement-and-applications_35209dbf-en (accessed on 1 March 2021).
- Winchcomb, T.; Massey, S.; Beastall, P. Review of Latest Developments in the Internet of Things, A Report for Ofcom by Cambridge. Available online: https://www.ofcom.org.uk/research-and-data/telecoms-research/general/review-of-latest-developments-in-the-internet-of-things (accessed on 1 March 2021).
- Asia-Pacific Telecommunity, SATRC Report on ICT Regulatory Framework for M2M Communications and IOT for the SATRC Countries. Available online: https://www.apt.int/sites/default/files/SATRC-SAPVI-02_M2M_Report.docx (accessed on 1 March 2021).
- Moss, J.; Barnett, G. OVUM—The Internet of Things: Understanding the Evolving Value Chain. Available online: https://silo.tips/download/the-internet-of-things-understanding-the-evolving-value-chain (accessed on 1 March 2021).
- Ericsson—Exploring IoT Strategies Insights on IoT Value Chain Positioning from Leading Telecom Service Providers. Available online: https://www.ericsson.com/en/press-releases/2018/4/exploring-iot-strategies-telecom-service-providers-pursue-multiple-paths-to-iot-revenue (accessed on 1 March 2021).
- Article 29 Data Protection Working Party (2014). Opinion 8/2014 on the Recent Developments on the Internet of Things. Available online: https://www.pdpjournals.com/docs/88440.pdf (accessed on 1 March 2021).
- Advisera, Expert Advice Community. Available online: https://community.advisera.com/topic/joint-controllers-share-of-responsibilities-in-iot/#comment-15806 (accessed on 1 March 2021).
- GSR—Global Symposium for Regulators (GSR) 2020 Best Practice Guidelines The Gold Standard for Digital Regulation. Available online: https://www.itu.int/en/ITU-D/Conferences/GSR/2020/Pages/default.aspx (accessed on 1 March 2021).
- IoT Analytics—5 Things to Know about the LPWAN Market in 2020, Internet Analytics Market Insights for the Internet of Things. Available online: https://iot-analytics.com/5-things-to-know-about-the-lpwan-market-in-2020/ (accessed on 1 March 2021).
- ITU—ICT Regulatory Tracker 2019. Available online: https://www.itu.int/net4/itu-d/irt/#/tracker-by-country/regulatory-tracker/2019 (accessed on 1 March 2021).
- IESE Cities in Motion IESE Business School, University of Navarra. Available online: https://blog.iese.edu/cities-challenges-and-management/2019/05/10/iese-cities-in-motion-index-2019/ (accessed on 1 March 2021).
- STATISTA—Data Volume of Internet of Things (IoT) Connections Worldwide in 2019 and 2025. Available online: https://www.statista.com/statistics/1017863/worldwide-iot-connected-devices-data-size/ (accessed on 1 March 2021).
- FTC—Data Brokers A Call for Transparency and Accountability, May 2014, Federal Trade Commission. Available online: https://www.ftc.gov/system/files/documents/reports/data-brokers-call-transparency-accountability-report-federal-trade-commission-may-2014/140527databrokerreport.pdf (accessed on 1 March 2021).
- Oh, H.; Park, S.; Lee, G.M.; Heo, H.; Choi, J.K. Personal Data Trading Scheme for Data Brokers in IoT Data Marketplaces. IEEE Access 2019, 7, 40120–40132. [Google Scholar] [CrossRef]
- Oh, H.; Park, S.; Lee, G.M.; Choi, J.K.; Noh, S. Competitive Data Trading Model with Privacy Valuation for Multiple Stakeholders in IoT Data Markets. IEEE Internet Things J. 2020, 7, 3623–3639. [Google Scholar] [CrossRef]
- Wolfie, C. Corporate Surveillance in Everyday Life—How Companies Collect, Combine, Analyze, Trade, and Use Personal Data on Billions. A Report by Cracked Labs. Available online: https://crackedlabs.org/dl/CrackedLabs_Christl_CorporateSurveillance.pdf (accessed on 1 March 2021).
- MacMillan, D. Data Brokers Are Selling Your Secrets. How States Are Trying to Stop Them, Washington Post. Available online: https://www.washingtonpost.com/business/2019/06/24/data-brokers-are-getting-rich-by-selling-your-secrets-how-states-are-trying-stop-them/ (accessed on 1 March 2021).
- European Commission—The Digital Services Act Package. Available online: https://ec.europa.eu/digital-single-market/en/digital-services-act-package (accessed on 1 March 2021).
| GDPR Actor | Description by the GDPR [9] |
|---|---|
| Controller | Article 4 point (7) ‘’controller means the natural or legal person, public authority, agency or other body which, alone or jointly with others, determines the purposes and means of the processing of personal data’’. Article 35 paragraph 1. ‘’Where a type of processing in particular using new technologies, and taking into account the nature, scope, context and purposes of the processing, is likely to result in a high risk to the rights and freedoms of natural persons, the controller shall, prior to the processing, carry out an assessment of the impact of the envisaged processing operations on the protection of personal data.’’ |
| Joint Controller | Article paragraph 26 ‘’Where two or more controllers jointly determine the purposes and means of processing, they shall be joint controllers’’. |
| Processor | Article 4 point (8) ‘’processor means a natural or legal person, public authority, agency, or other body which processes personal data on behalf of the controller’’. |
| Third Party | Article 4 point (10) ‘’third party means a natural or legal person, public authority, agency or body other than the data subject, controller, processor and persons who, under the direct authority of the controller or processor, are authorised to process personal data’’. |
| Data Protection Officer (DPO) | Article 37 paragraph 1. ‘’The controller and the processor shall designate a data protection officer in any case where:’’…b) ‘’the core activities of the controller or the processor consist of processing operations which, by virtue of their nature, their scope and/or their purposes, require regular and systematic monitoring of data subjects on a large scale;’’ Article 37 6. ‘’The data protection officer may be a staff member of the controller or processor, or fulfil the tasks on the basis of a service contract’’ |
| Supervisory Authority | Article 51 paragraph 1 ‘’Each Member State shall provide for one or more independent public authorities to be responsible for monitoring the application of this Regulation, …’’ |
| Lead Supervisory Authority | Article 56 paragraph 1 ‘’… the supervisory authority of the main establishment or of the single establishment of the controller or processor shall be competent to act as lead supervisory authority for the cross-border processing carried out by that controller or processor…’’ Article 56 paragraph 6 ‘’The lead supervisory authority shall be the sole interlocutor of the controller or processor for the cross-border processing carried out by that controller or processor. ‘’ |
| Cloud Computing | Fog Computing | Edge Computing | Mist Computing | Dew Computing | |
|---|---|---|---|---|---|
| Computing hardware location | Large Cloud, Data centres | Mini Cloud smart gateways or routers. | The first hop from the IoT device Wi-Fi access points, switches, or gateways | The far edge of the IoT network It usually has microchips or microcontrollers built into the device | Server located inside the user’s PC and Information processing devices |
| IoT actor | Cloud Data Manager Cloud Service Provider | Fog Data Manager Network equipment provider Network providers or other business | Edge Data Manager Network equipment provider Network providers or other business | Mist Data Manager Device provider Network providers or other business | Dew Data Manager Device provider Users Self-organized, local, or other business |
| IoT Actors Identified in ITU Recommendations ITU-T Y.4100 [6] and ITU-T Y.4114 [7] | Business Roles in Informative Appendix I of Recommendation ITU-T Y.4000 [5] |
|---|---|
| Data Manager is responsible for managing the capture, processing, storage, and transfer of IoT data to meet the IoT service provision requirements [6]. Data manager actor can be a human Data manager or a machine Data manager actor | Application provider Device provider |
| Service Provider provides services related to things, such as location tracking, monitoring, and service discovery [6]. | Application provider, Platform provider, Network provider. |
| IoT User uses services related to things, such as location tracking, monitoring, and service discovery [6]. | Application customer |
| IoT Data Provider collects data from things and injects the data processed within the IoT system as well as data from external sources and provides them via the IoT data carrier to the IoT data consumer [7]. | Device provider, Network provider, Platform provider, Application provider |
| IoT Data Consumer consumes IoT data. Usage of the consumed data depends on application purposes [7]. | Device provider, Network provider, Platform provider, Application provider, Application customer. |
| IoT Data Framework Provider provides general IoT data processing capabilities and related infrastructure (e.g., storage and computing resources, data processing run time environment) as required by the IoT data provider, IoT data carrier, IoT data application provider, and IoT data consumer for the support of data operations execution [7]. | Network provider, Platform provider. |
| IoT Data Application Provider provides applications related to the execution of IoT data operations (e.g., applications for data analysis, data pre-processing, data visualization, and data query) [7]. | Device provider, Network provider, Application provider. |
| IoT Data Carrier carries data among the IoT data provider, the IoT data framework provider, the IoT data application provider, and the IoT data consumer [7]. | Network provider. |
| IoT Actors | IoT Actors Identified from Various Perspectives |
|---|---|
| IoT Developer | IoT service developer [17] IoT application developer [17] |
| IoT Security Specialist | Security specialists [64] |
| IoT Data Protection and Privacy Specialist | Data protection officer [6] |
| IoT Data Manager | Data manager [6] Application provider + data management [5] Device provider + data management [5] |
| IoT Device Provider | Device provider [5,17,65] Device manufacturers, module manufacturers [66] Designers and producers of connected devices [67] IoT module providers [67] The designers and manufacturers of the objects [64] The manufacturers of the module components [64] Device, component, and chipset manufacturers [68] Device manufacturer/provider [69] Device manufacturers, component manufacturers [70] |
| IoT Network equipment Provider | Suppliers of the middleware [64] Network equipment providers [67] Infrastructure manufacturers [70] Network equipment manufacturers [64] Connectivity equipment developers and vendors [68] |
| IoT Platform Provider | Connectivity platforms [39] Device management platforms [39] Cloud platforms [39] Application enablement platforms [39] Advanced analytics platforms [39] IoT platform provider [67], [17] Platform vendors [70] Platform provider [65], [5] |
| IoT Connectivity Provider | Network provider [5,57,64] Infrastructure provider [17] Operators [65] Connectivity service provider [43] Connectivity provider (network developer) [71] Connectivity provider [17,66,67] Connectivity/network provider [69] Connectivity/mobile network operators [68] Middleware/analytics vendors (connectivity providers, service provider) [70] |
| IoT Service Provider | Service provider [6,66,69]. (application provider, platform provider, network provider) [5] IoT service provider [43] Service providers and data aggregators [64] Service (cloud service providers, IoT platforms) [68] Service enabler and service creator [71] Cloud computing companies [64], IoT cloud provider [67] |
| IoT Application Provider | Application provider [5,65,69] |
| IoT Integrator | IoT service integrator [17] Integrators [64], System integrator [65,66] |
| IoT User | IoT user [17,43] Application customer [5] |
| End User | End user [17,43,69] Markets-payers (consumer, end user, company, public sector) [68] |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Hadzovic, S.; Mrdovic, S.; Radonjic, M. Identification of IoT Actors. Sensors 2021, 21, 2093. https://doi.org/10.3390/s21062093
Hadzovic S, Mrdovic S, Radonjic M. Identification of IoT Actors. Sensors. 2021; 21(6):2093. https://doi.org/10.3390/s21062093
Chicago/Turabian StyleHadzovic, Suada, Sasa Mrdovic, and Milutin Radonjic. 2021. "Identification of IoT Actors" Sensors 21, no. 6: 2093. https://doi.org/10.3390/s21062093
APA StyleHadzovic, S., Mrdovic, S., & Radonjic, M. (2021). Identification of IoT Actors. Sensors, 21(6), 2093. https://doi.org/10.3390/s21062093







