2. Related Works
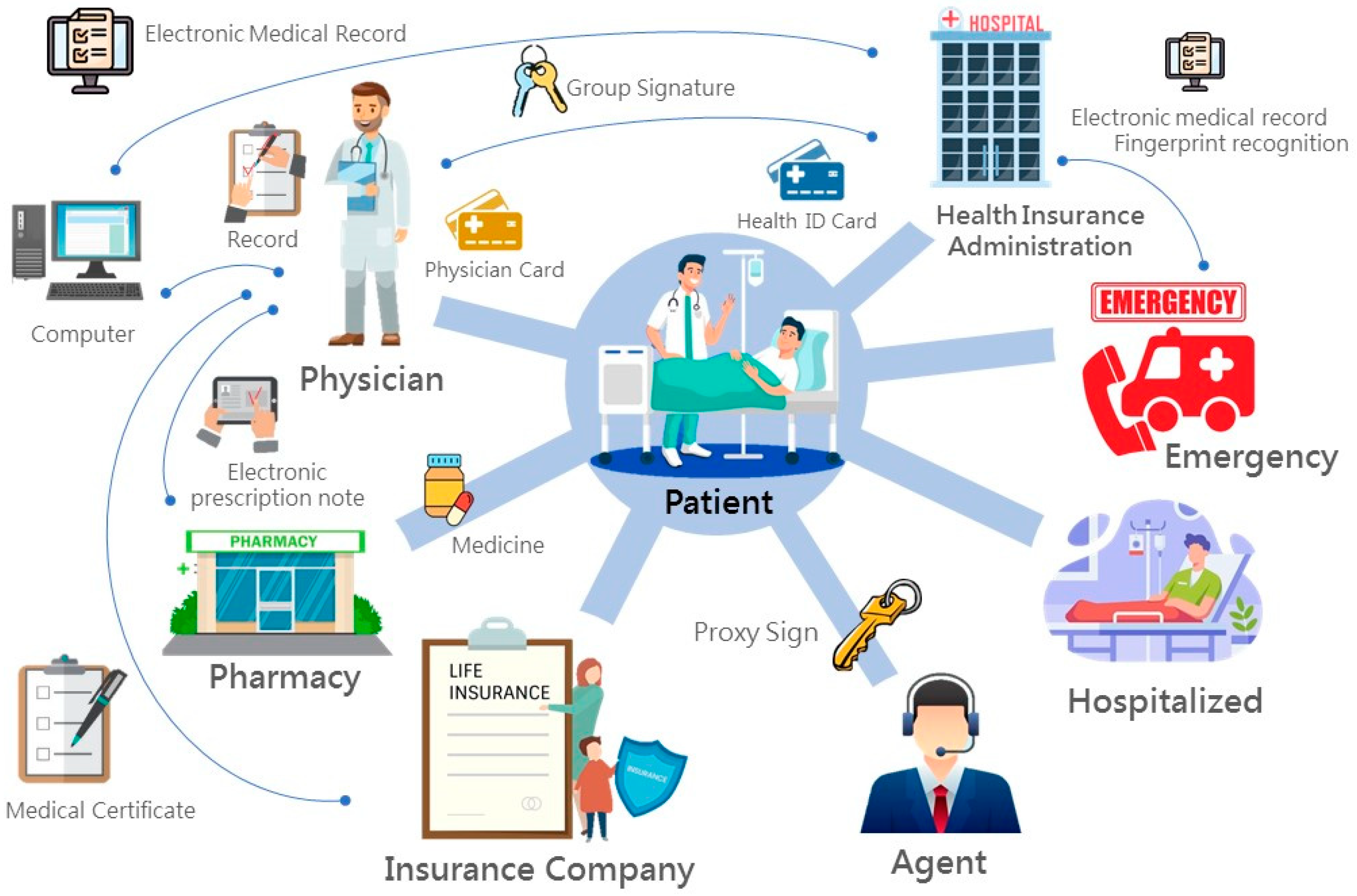
An integrated medical information system combines various computer science technologies, e.g., smart cards, electronic medical records, public-key cryptosystems, digital signature. The digital signature could be extended into a group signature or proxy signature and applied to different research fields.
2.1. Smart Cards
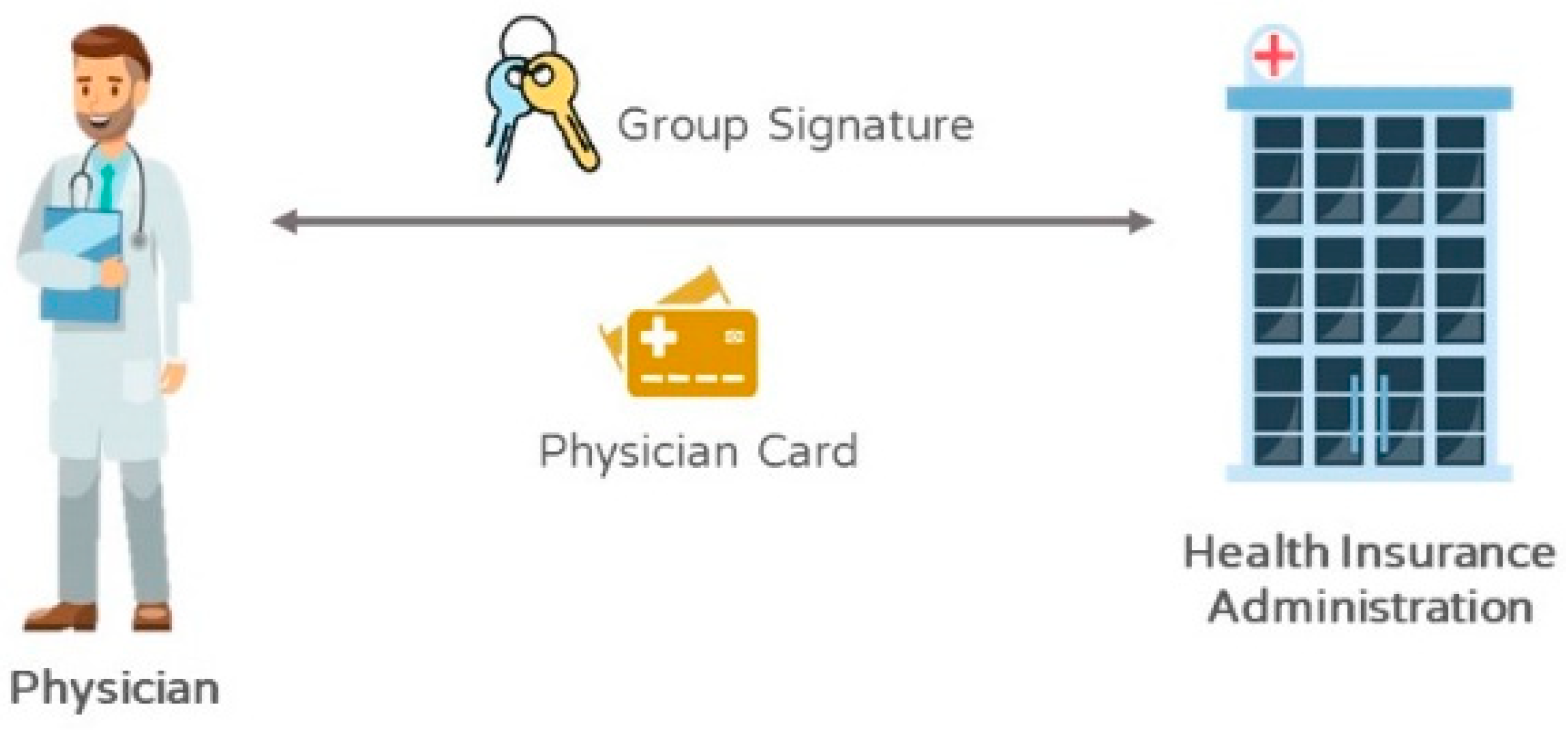
Smart cards were a plastic card with ISO standards and embedded an IC chip. By reading the data on the chip, it presented various functions of memory, identification, encryption/decryption, and transmission. Since a smart card provides a simple computation function of a computer, the card could be used for storing personal data, e.g., medicine, identity information, key, public certificate, electronic medical records, and prescriptions, and various personal diagnostic records. The transmission and encryption of data are processed through the central processing unit to become safer. The data record could be stored with the memory and eventually transmitted with an import/export interface through a reader. In the medical information system proposed in this study, healthcare certification IC cards and health insurance IC cards derived from smart cards are applied. A healthcare certification IC card, also named a doctor card, used in current medical institutions contains a medical personnel card, doctor card, and the additional card of the medical institution. These three cards allow doctors or medical personnel in a medical institution to develop the functions. Each card presents distinct functions. Ones with medical personnel cards could view medical data, but not patients’ personal data. Those with doctor cards, on the other hand, could view patients’ data and medical records [
8,
9].
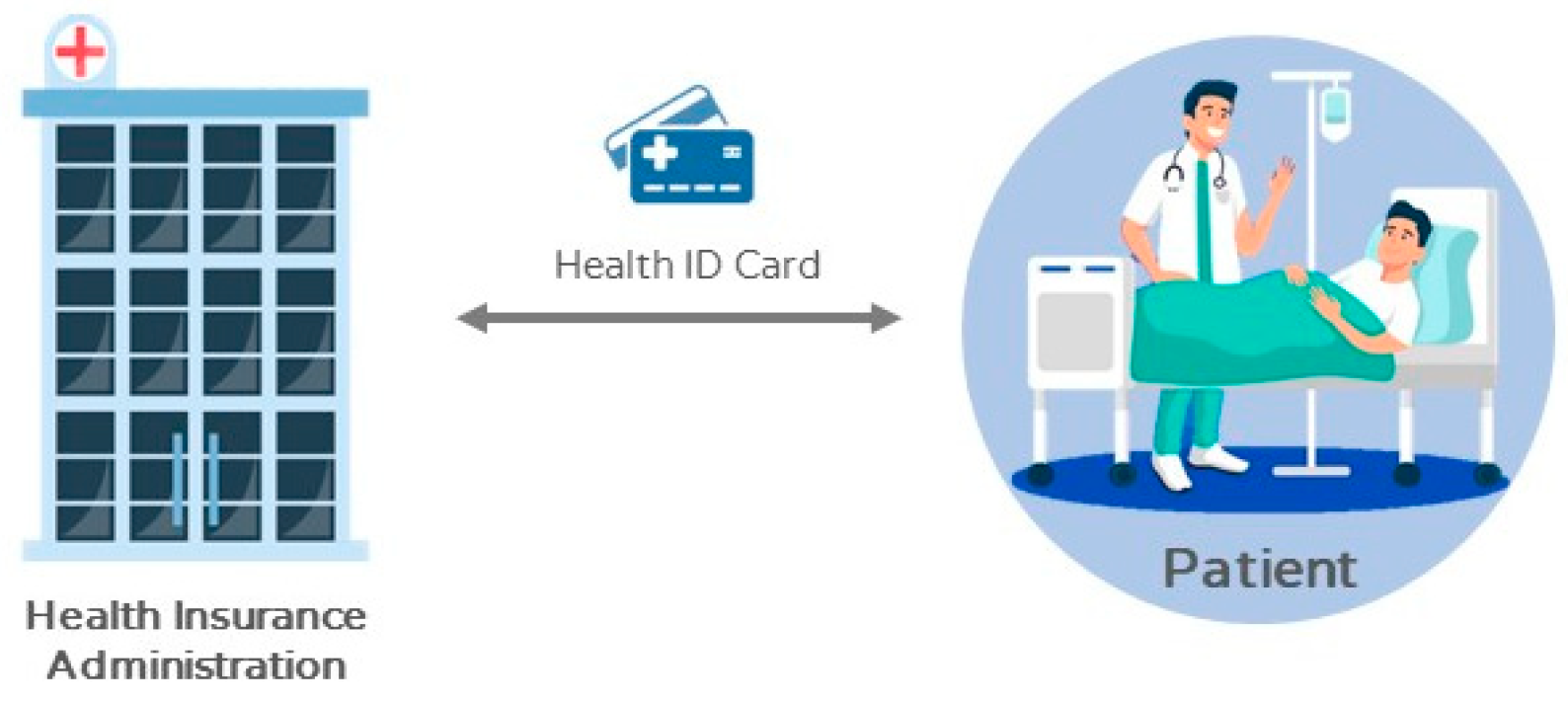
A doctor card plays a critical role in the system. A doctor card represents a doctor. The group signature key in a doctor card is required for retrieving electronic medical records in the system using process, and the signature with a doctor card is necessary for medicine collection and insurance. In this case, the doctor with the signature could be found out for medical malpractice claims. Health insurance IC cards were formally used in 2004. Past health insurance paper cards were then gradually eliminated. To cope with this trend, the type of health insurance certificates is often digital document [
10].
A health insurance IC card could be regarded as a national health insurance IC card with complete functions and multiple usages. In addition to replacing original health insurance paper cards, other data with health insurance certificates, such as children’s health booklets, maternal health booklets, and catastrophic illness cards, are also integrated into the card. In this case, a patient could simply take the health insurance IC card, regardless of identity, to see a doctor.
2.2. Electronic Medical Records
Medical records are medical business document generated in the process of various examinations, diagnoses, treatment, and care when the staff in a medical institution engaging in medical businesses, including medical records, certificate agreement, examination records, and nursing records. Due to distinct storing methods of hospitals, medical records are scattered and not easily shared and exchanged to result in bad efficiency and waste of medical resources. To improve such a situation, paper medical records are gradually developed into electronic medical records for conveniently integrating and updating data, as well as circulating in various medical institutions when necessary [
11]. Several hospitals are currently making efforts toward electronic medical records. The US Computer-Based Patient Record Institute (CPRI) describes electronic medical records as “electronically storing individual health conditions and medical care information in the life” to replace paper medical records as the major medical care records [
12].
The Institute of Medicine (IOM) further indicated that electronic medical records should be able to provide complete and accurate data, as well as clinical decision-making and medical research. The US Medical Records Institute (MRI) defined electronic medical records as the electronic information of individual health state and medical care in the life, and the development of electronic medical record system was divided into five stages, namely, automated medical record (AMR), computerized medical record (CMR), provider-based electronic medical record (EMR), and electronic health record (EHR) [
10]. The Institute of Medicine (IOM), United States National Academy of Sciences, pointed out six different data formats, including text, graphics, and images, numerical, sound, and full-motion video [
13]. An electronic medical record system, therefore, was the mechanism used to store data. IOM explained that the mechanism was the system composed of personnel, data, rules, process, processing, storing equipment, communication, and technological support to provide the acquisition, use, storage, and extraction of medical records.
The boom of information technology in past years has resulted in various cloud application services, with lots of convenient and advantages, such as concentration management, saving storage space, and convenience in sharing with other users. Nevertheless, such convenience has resulted in great problems and possible causes information loss or patients’ privacy being stolen and even abused. Hence, using electronic medical records in the cloud does involve certain risks. For example, Google Health builds its e-medical records on the cloud environment, providing users with self-management service. However, this convenience causes a big problem. Because in its privacy policy, Google Health indicates that the user can permit others (e.g., their doctors or pharmacy) to share their medical records and add the information to their medical records (e.g., test results). Although the users can withdraw the permission anytime, the previously authorized individuals or institutions may have already viewed the medical information or even kept copies of the information, which may cause the loss of information or the theft or even abuse of the patient’s privacy. When the people with administrator authority in Google can view the e-medical records, storing e-medical records in the cloud poses certain risks.
For this reason, this study store electronic medical records in the Bureau of National Health Insurance; various medical businesses are contracted by the Bureau of National Health Insurance, and the secure and efficient encryption technology is used for the transmission to protect patients’ medical records.
2.3. Digital Signature
The digital signature was originated from cryptography, functioning to provide the mechanism to sign text information and ensure the data being completely and securely transmitted to the destination [
14,
15]. It is generally used with a one-way hash function, which is a kind of mathematical algorithm that acquires an output value with constant length by inputting text information with any length. Hash function mainly functions to avoid the third-party deriving the input value from the output value [
16].
The descriptions above briefly explain the generation method of a digital signature. With a public-key system as the basis, the transmitter first uses a one-way hash function to transform electronic documents into text information with constant length, called a message digest. A personal, secret key is then used to sign the message digest to generate a digital signature. After the recipient receives the message and signature, the transmitter’s public key is used for verifying the signature integrity and confirm the message computed by hash function conforming to the content. Inconsistent content reveals the received information being tampered with. On the contrary, consistent contents show that the received message is a valid document. Accordingly, the user could confirm the integrity and security of data transmission.
- (1)
Group Signature: D. Chaum and E. van Heyst proposed the idea of group signature in 1991, as the application of digital signature. The group members, as a group, anonymously sign for the message [
17]. When there is a dispute, a specific just third-party is responsible for checking the signature and tracing the real signer. Group signature is normally used for a group announcing message. The signature is generated by any members in the group using a personal, secret key, and the verification merely requires a public group key. Logically, group signature is classified as the signature mechanism with multiple secret keys to verify a public key [
18]. As the example of medical record transmission, a patient might register different departments for the same outpatient clinic time that errors might appear in the medical record transmission process. In this case, a group signature could be used for checking the verifiability of departments and establishing the non-linkability of a signer; or, when there is a dispute, a creditable third-party could trace the signer’s identity with the secret key.
- (2)
Proxy Signature: Mambo et al. proposed proxy signature in 1996 [
19], including the operation mechanism of the original signer, proxy signer, and verifier. Under the authorization of the original signer, a proxy signer could make the decision. The authorization model is divided into authorization, partial authorization, and letter of authorization, where the letter of authorization is the most common one [
20,
21]. A letter of authorization specifies the original signer’s identification code, the proxy signer’s identification code, and the term. It could be used for collecting medicine so that disabled patients or those not being able to collect medicine could authorize an agent, with signature authorization, to collect medicine.
2.4. Electronic Medical Records System
There was already some security protocols that protect privacy within Medical Information System. In 2018, C. T. Li et al. proposed an enhanced secure protocol for cloud-based telemedical information system [
22]. It could provide user anonymity and unlinkability. Their authentication scheme included four phases: (1) Healthcare center upload phase, (2) patient data upload phase, (3) treatment phase, and (4) check-up phase. Through the security, an analysis verified that their scheme cost fewer computation costs against various known attacks. The authentication scheme for telemedical information system-based cloud environment could ensure privacy preservation. Y. Wang et al. proposed the cloud-based e-health record system in 2019 [
23]. For the centralization of a cloud-based system that exposed threats to security, they used searchable encryption and proxy-re-encryption to construct their e-health record information sharing system, based on Consortium blockchain.
The K-Anonymity mechanism was proposed to protect hospital internal information systems and electronic medical records publishing in 2018 [
24]. K. Fan et al. [
25] designed a blockchain-based medical information system, MedBlock, to manage the patients’ information. The distributed ledger of MedBlock system has an efficient access control method and secure authority. The MedBlock system can reduce the large energy consumption and network congestion. O. Enaizan et al. proposed a framework based on a multi-criteria standpoint in Malaysia. Using the Unified theory of acceptance and use of technology 2 (UTAUT2) clarifies the construction between individual, privacy, and EMR system acceptance [
26]. The research results show five factors that have a positive effect of EMR acceptance. The five factors includes: Data integrity, confidentiality, non-repudiation, facilitating conditions, and effort expectancy. With the development of information technology, Y. Cao et al. proposed a hybrid blockchain-based secure sharing scheme [
27]. They also use Hyperledger Caliper, which is a blockchain benchmark that estimates performance.
4. Function Analysis
The integrity, convenience, and security of the proposed medical system should conform to the characteristics of the mobility of medical records, urgency of emergency medical care, function of medicine collection, protection of connection function and security, and avoidance of medicine conflicts. The following descriptions would prove the system satisfying the above requirements.
Mobility of Medicine Records: Along with the popularity of mobile devices, e.g., smart cards, mobile phones, and PDAs, the advance of development technology would be able to fulfill mobile medical records when storage space, computing capability, and memory size are enhanced. In terms of the proposed IMIS, the matched national health insurance IC card would be designed as the content mentioned in the article, with the functions of signature, encryption, and decryption, as well as being able to securely store relevant medical records in the card, whose portability satisfies the mobile function. Although similar smart cards are applied to current medical systems, some complicated verifications are required for accessing relevant medical records. It is believed to present great development space in the application of electronic medical care. Smart cards similar to the one proposed in this study would be used in e-medical systems, e-patient records, and e-prescriptions to fulfill mobile medicine records.
The urgency of emergency medical care: Medical care is a skill to strive for life. Although the advance of medical care technology enhances the cure rate, it is necessary to understand a patient’s physical conditions before the treatment. However, when a patient is unconscious and is delivered to a medical institution without any alerts, various examinations are required for understanding the physical conditions. In this case, the patient’s survival rate might be reduced. It is no longer time-consuming to realize patient’s conditions. With the proposed IMIS matched with a fingerprint identification system, designed as the content in this study, it would present the functions of signature and encryption/decryption and can retrieve a patient’s medical record data to satisfy the urgency of emergency medical care and show complete protection of information. Although some simple examinations could be done, finer data would effectively enhance the cure rate. The proposed emergency medical care would be really applied to establish a new milestone.
Medicine collection: Patients are given more convenience for medicine collection, especially for physically and mentally disabled patients. Legally authorizing an agent to collect medicine could prevent loss or fraud. Particularly, with fully electronic medical systems, medicine collection does not simply give a doctor signed prescriptions to a pharmacy. It becomes an important issue to provide secure medicine collection in the network environment full of people with bad intentions or computer hackers intercepting or revising prescription data. The IMIS applies proxy signature allowing an authorized agent to collect signature prescriptions, as well as maintain the signed digital signature with confirmation and integrity, avoiding forgery, and being undeniable so that the third verification party clearly knows the legality of patients and agents. In this case, it could guarantee a patient and an agent securely and actually collecting the medicine, as well as allow medical information system to provide medicine collection.
Protection of Privacy: Regarding the protection of privacy, the IMIS would ensure the five secure connection requirements through patients’ pseudonyms and doctors’ group signature, including anonymity, coalition-resistance, linkability of patients, linkability of doctors, and non-linkability of doctors. With anonymity, the pseudonym offered by the Bureau of National Health Insurance, real name, and privacy would not be disclosed. In this case, it could ensure patients’ clinical data privacy and provide academic units for research to further discover better treatment medicine or methods. With coalition-resistance, a doctor’s and a patient’s real names and privacy would not be disclosed by the cooperation of legal users. It could prevent patients with the same symptoms from being given test medicine by a pharmaceutical factory and avoid a pharmaceutical factory monopolizing the medicine for the symptoms to further effectively apply medical resources.
With patients’ linkability, after providing a patient with a pseudonym, the Bureau of National Health Insurance, could identify the relationship between the real identity and the pseudonym of a patient. Anyone (except the outpatient doctor) could not easily acquire the information. Meanwhile, a pharmacy could merely identify, with the same pseudonym, that different medical records belong to the same patient. Thus, the proposed IMIS could satisfy patients’ linkability. In terms of a doctor’s non-linkability, the use of group signature in IMIS merely allows just the Bureau of National Health Insurance tracing a doctor’s diagnosis signature and knowing the doctor’s real identity. Other units could merely verify the legality of the signature, but not the real identity of the doctor. Such a situation satisfies a doctor’s non-linkability that a pharmacy could not know the doctor from the medical records.
In addition, personalized medicine, also known as precision medicine, is a medical model that divides people into different groups, i.e., tailored medical decisions, practices, interventions, or products for patients based on their expected response or disease risk. In personalized medicine, diagnostic tests are usually used to select the appropriate and best treatment, based on the patient’s genetic composition, or other molecular or cellular analysis backgrounds. In such a situation, it is necessary to maintain a regular connection with the patient to ensure that tailored medical decisions can be made at any time during the treatment process. In our system, the patient’s linkability is used to ensure the connection of each different alias to a specific patient, while ensuring the connectivity of the attending physician. Therefore, there are no obstacles in the medical module in this area. It can find a more unified treatment for the individuals and their genome targeted by personalized medicine to develop better drugs and provide a better diagnoses for the targeted treatments.
Privacy of Insurance Companies: Using our system, the insurance company will receive the following benefits: (1) The received diagnosis certificate and fee receipt cannot be tampered with. (2) Relevant certificates issued by non-doctors cannot be sent or counterfeited. (3) Ensure the patient’s ability to pay the expenses. The detailed descriptions are as follows: In the process of transmission, as the transmitted data is signed by the doctor (medical office) with the private key of the group and encrypted by the public key of the insurance company, it ensures the security of the data cannot be tampered with, and the signature also makes the document undeniable. In addition, because the patient’s public key certificate, PCertP, is attached to the data, it can be used to ensure that the patient can make payment for the relevant expenses. Therefore, insurance companies can get these benefits and further prevent insurance fraudulence or repetitive claims, in turn, preventing major losses.
Shared Information between the medical office and health insurance companies: The information shared by the medical office (medical unit or doctor) and health insurance companies is the patient ID, diagnosis certificate, expense receipt. When a patient needs to apply for medical insurance from an insurance company, he/she only needs to ask the medical office to convert the contents of the diagnosis and treatment into the diagnosis certificate and expense receipt required for the insurance application and attach the doctor’s group private key signature to signify the doctor’s responsibility. Together with the patient’s public key certification, PCertP, it is encrypted with the public key of the insurance company designated by the patient and sent to the insurance company, which completes the transfer of information between the two units.
Security of all phases of system: The encryption mechanism and signature mechanism employed are all security systems that already exist and are implemented today (such as RSA public key mechanism; DSA, digital signature mechanism), and their security is based on their security certification and unsolvable math problems. Therefore, during the entire process, the patient will arrive at the hospital with an insurance IC card. The patient inserts the insurance IC card into the registration machine of the hospital to register and uses the personal, secret key to sign the latest timestamp (TS) on the computer. The hospital will check the validity of the patient’s health insurance payment data (Data). Then, in the outpatient clinic, the doctor and the patient insert the physician card and insurance IC card into the reader, respectively, and the relevant information will be encrypted and transmitted with the public key of the NHI. At this time, the reader will be connected to the NHI system, and the operator of the NHI party will use the secret key and the patient’s public key to decrypt the data to analyze the correctness of the relevant medical documents. Once the verification is correct and the patient ID is confirmed, the verification result will be stored in the NHI’s database to ensure that future medical disputes can be investigated; finally, the patient’s basic information and historical medical records will be returned, and the records of the recent diagnosis and treatment in the card are displayed on the doctor’s computer screen for the doctor to diagnose the patient’s physical condition. In the medicine collection phrase, the pharmacy obtains the group signature through a private key and verifies the correctness of the prescription information sent by the doctor. This verification result will be stored in the pharmacy to ensure that in the future, should there be any medical disputes or financial disputes, the stored information can be used for dispute resolution by NHI. Next, the patient will bring the insurance IC card to the pharmacy to collect the medicine; the pharmacy will determine whether the prescription number, RX_ID, stored in the patient card matches the number transmitted by the hospital. If it is correct, the pharmacy will ask the patient to sign the number with a private key against the number to become the basis for the pharmacy to apply for subsidies for medical expenses from the NHI. Finally, the pharmacy gives the medicine to the patient and marks the prescription number as having received the medicine to complete the whole process. The above processes are all secured under the existing encryption mechanism and signature mechanism; thus, the privacy of patients and related medical institutions is guaranteed.
In terms of security of medical records collection, since the patient verification is issued by the NHI during the registration phase, this ensures that the patient is a legitimate user. When the patients go to the hospital for relevant physical examinations, the related medical records will be simultaneously written into the system. The process requires the matching of the IC card insertion of the medical staff and patients to read the private key for signature and use the NHI public.
5. Conclusions
An integrated medical information system with security policy and privacy protection, which combines e-patient records, e-prescriptions, modified smart cards, and fingerprint identification systems, and applies proxy signature and group signature, has been proposed in this study. The following conclusions are proposed.
E-Patient records could be exchanged in different medical institutions through the Bureau of National Health Insurance, and prescriptions and diagnosis certificates could be integrated and used. The use of personal electronic health records and electronic medical records could be very useful, and patients, doctors, hospitals, pharmacies, and pharmaceutical factories could adapt to this system. In addition to avoiding a pharmaceutical factory’s monopoly of medicine prices, medical institutions colluding with patients for diagnosis fees, and saving medical resources, contributing to environmental protections.
The medium of a fingerprint identification system could develop the urgency of emergency medical care. The fingerprint identification could confirm a patient’s identity and retrieve a patient’s electronic medical records saved in the Bureau of National Health Insurance for treating patients with major injuries or unconsciousness.
The functions of proxy signature and group signature could create secure verification and protection of doctors and patients. This would prevent patients from having to forgo treatment due to medical or privacy insecurity for immediate research on rare diseases and breakthroughs in medicine. Doctors, on the other hand, could make progress on the technology. There is no database of famous doctors who prescribe all the various medicines that exist within the medical field. Therefore, it might be discovered that certain medicines show better effectiveness when treating certain symptoms. It would simplify the complicated and time-consuming medical process.
The system would effectively apply and save medical resources—satisfying the mobility of medical records, presenting the function and security of medicine collection, and avoiding medical conflicts and profiteering to further acquire the maximum effectiveness with the least resources. When electronic medical care is gradually emphasized and becomes the mainstream, it is believed that the security and convenience of this system could be applicable to future medical environments.