1. Introduction
Internet of Things (IoT) devices has limited memory and processing capabilities [
1]. Hence, these constrained devices rely upon efficient routing protocols [
2] and standardized communication stack [
3]. Technological advancements in 5G [
4], intelligent 5G-based IoT [
5], IoT operating systems (OS) [
6], data-driven intelligence in wireless networks [
7], scheduling approaches for heterogeneous content-centric IoT [
8], congestion avoidance techniques in IoT using data science [
9], vehicular ad hoc networks (VANETS) [
10], Information-centric networks (ICN) [
11], reinforcement learning-based solutions for next-generation networks [
12,
13], coexistence networks [
14], IoT adaptation in agriculture [
15] and Healthcare IoT [
16] are helping to realize to connect everything and anywhere.
Internet of Multimedia Things (IoMT) devices are different from IoT devices. It requires bigger memory, higher computational power, and more power-hungry with higher bandwidth [
17].
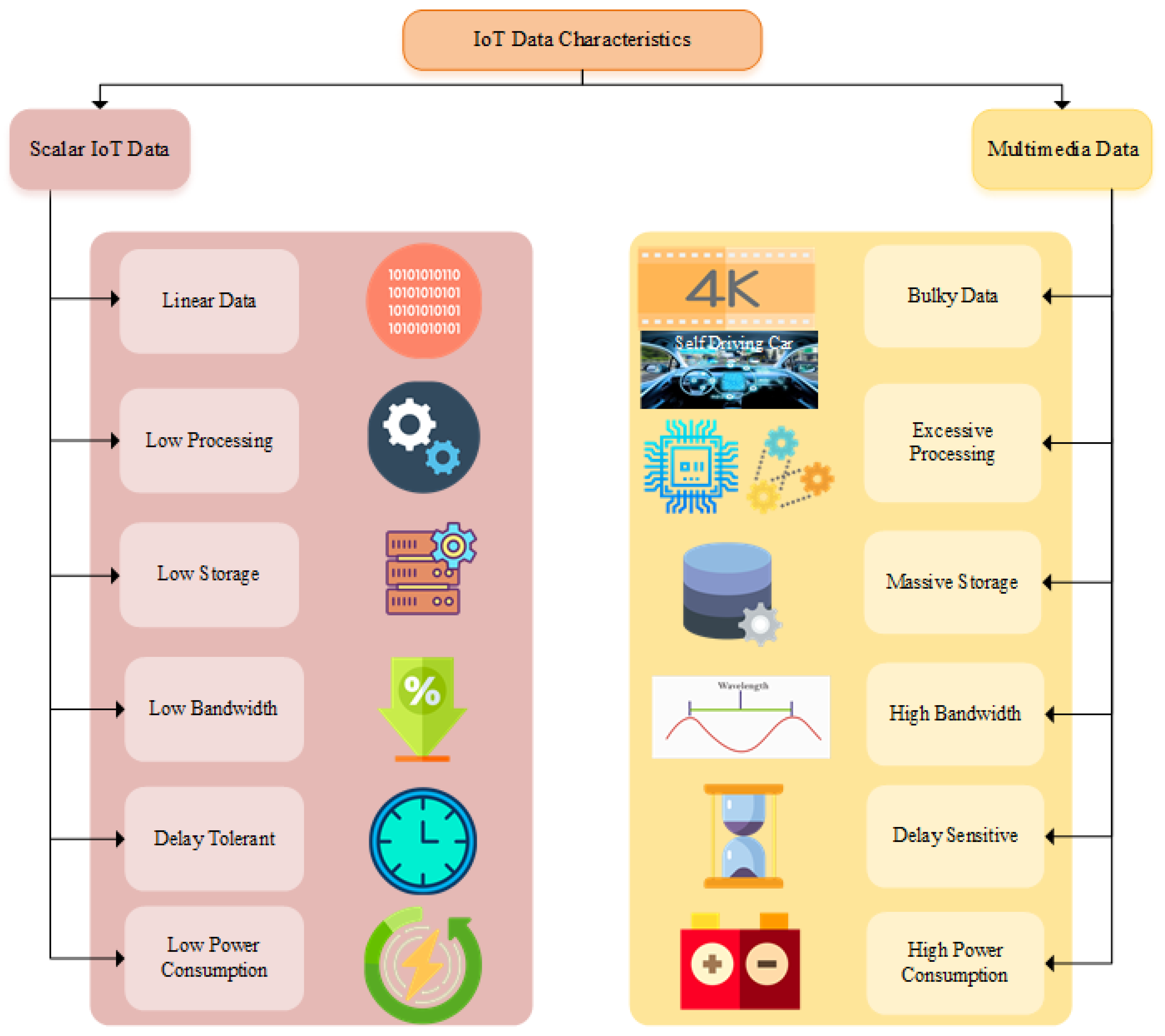
Figure 1 shows the key data characteristics of IoT and IoMT. The real-time deployment scenarios vary from industrial IoT, Smart cities, Smart hospitals, smart grid, smart agriculture, and smart homes. The main characteristic of IoMT is the timely and reliable delivery of the data. Therefore, it imposes strict quality of service (QoS) requirements and demands efficient network architecture. The users perspective of QoS is known as quality of experience (QoE). QoE can be further characterized as objective or subjective. The users Objective QoE is challenging to measure and dramatically varies according to the needs. However, service providers concern with the subjective QoE to evaluate the network mean opinion score (MOS). The multimedia data is increasing multifold. It raises new challenges to transmit, process, store and share the data. Processing requires new techniques for edge, fog and cloud devices. Further compression and decompression techniques are introduced for the storage of multimedia data. Routing protocol for low-power and lossy networks (RPL) is the standard IoT routing protocol. It needs further development by considering energy-aware, load balancing, fault tolerance, and delay aware IoMT deployment scenarios.
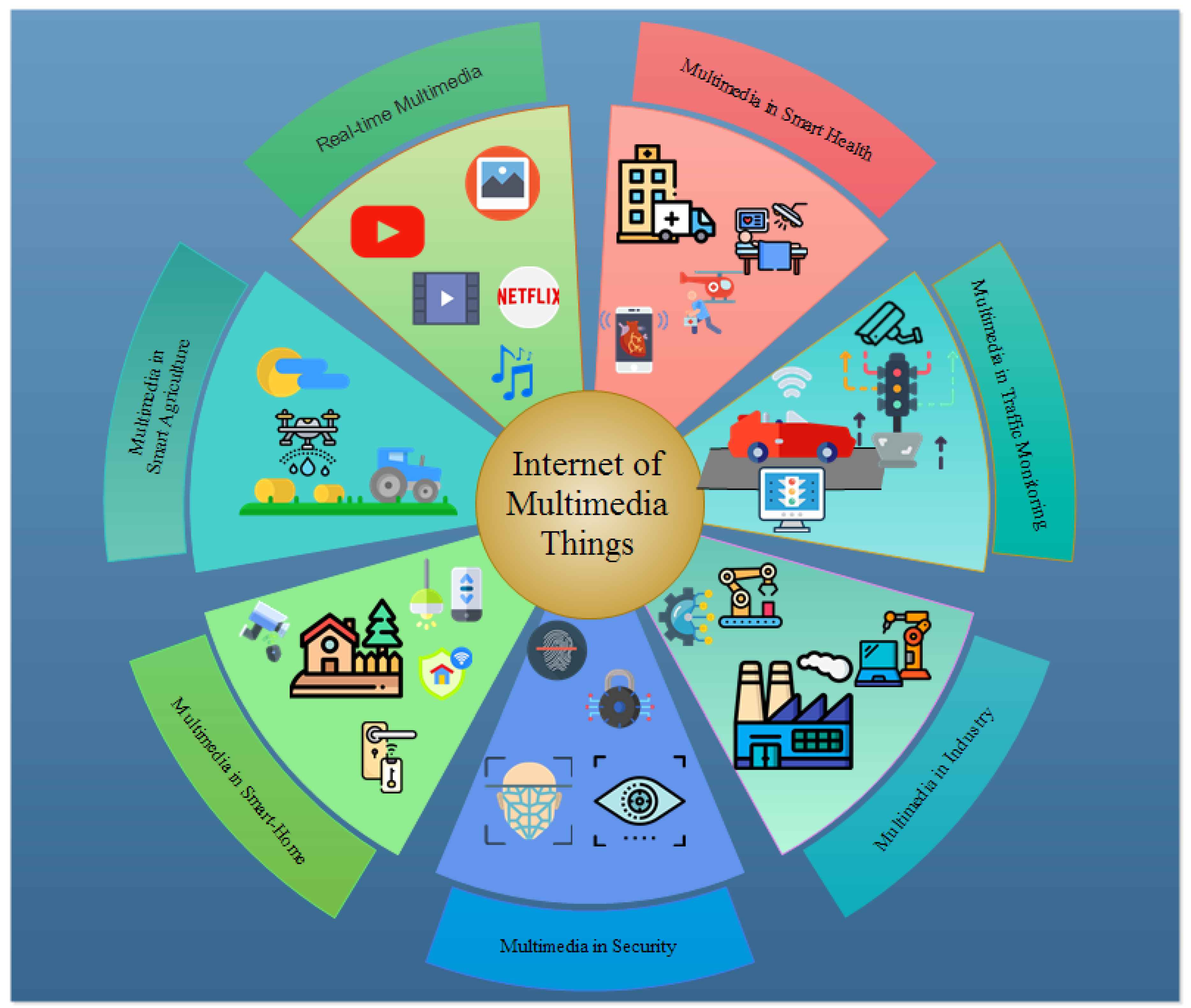
IoT characteristics support multimedia communications; however, multimedia applications are bandwidth-hungry and delay-sensitive. The rapid growth of multimedia traffic in IoT has led the way to innovating new techniques to meet its requirements. IoMT devices require higher bandwidth, bigger memory, and faster computational resources to process data. Typical communications include multipoint-to-point and multipoint-to-multipoint scenarios. Real-world multimedia applications include emergency response systems, traffic monitoring, crime inspection, smart cities, smart homes, smart hospitals, smart agriculture, surveillance systems, Internet of bodies (IoB), and Industrial IoT (IIoT). Dynamic networks, heterogeneous devices and data, strict QoS, and delay sensitivity and reliability requirements over resource-constrained IoMT pose humongous challenges for multimedia communication in IoT. Network-on-chip architecture [
18,
19] is one of the viable solution to improve the user quality of experience.
Figure 2 shows versatile IoMT applications.
The rest of the paper is organized as follows.
Section 2 provides future research directions.
Section 3 summarizes the accepted paper. Finally,
Section 4 concludes the paper.
2. Future Research Directions
Molecular communication exploits the transmission and reception of information encoded in molecules. Molecular communications have the potential of becoming the main technology for the execution of advanced medical solutions. The key research challenges in the molecular communication are the interoperability between molecular communication and the other networks, energy-efficient models and protocols for molecular communication, and implantation of reliability in the molecular communication.
Billions of resource constraint devices will be connected in the IoT. The available spectrum is far from enough to support IoT communication systems. Optimal resource allocation for critical multimedia traffic is a key challenge for IoMT. The use of artificial intelligence (machine learning, deep learning) can improve the energy-efficient resource allocation in IoMT.
Device-to-device (D2D) communication in LTE-A will establish direct communication with the device in its communication range. Potential advantages of D2D communication are increased network spectral efficiency, energy efficiency, reduced transmission delay, traffic offloaded base station, and less congestion in the cellular core network. IoMT can take the benefits of the advantages provided by D2D communication. Interference, radio resource allocation, power control, and QoE improvement for cellular users are the key research areas in D2D communication for IoMT.
Energy Efficient Operation and Protocols are the key requirement of IoMT. Many multimedia traffic sources in IoMT may rely on battery-powered sources with limited energy and/or may not be easily accessible for recharging purposes. Similar to WSNs/IoT, the energy-efficient operation, protocols design (i.e., medium access control and routing protocols), and the need to optimize the network lifetime remains a critical challenge for IoMT. Based on the specific application and deployment environment, energy-efficient protocols can be designed for IoMT.
The Internet of Multimedia Nano-Things (IoMNT) is defined as the interconnection of multimedia nano-devices with communication networks and the Internet. The potential applications of IoMNT are security, biomedical, defense, and industry. The main research challenges in IoMNT includes novel medium access control techniques, addressing schemes, neighbor discovery and routing schemes, QoS-aware cross-layer communication module and security solutions for the IoMNT.
Multimedia-oriented IoT over vehicular networks is increasing drastically. Today, vehicles have the capability of supporting real-time acquisition and transmission of the multimedia traffic generated by the built-in IoT devices. However, due to high mobility, density, and random wireless channel conditions, the performance of the delivery of multimedia contents significantly reduces in vehicular networks. Rate adaptation, multimedia delivery over heterogeneous devices, robust video encoding, scalable, and timely delivery of multimedia contents are the key research challenges in IoMT over vehicular networks.
3. A Brief Review of Articles of This Special Issue
The immense growth in multimedia traffic over the scarce licensed cellular spectrum has inspired to use unlicensed spectrum below 6 GHz for Long Term Evolution (LTE). However, Wi-Fi uses the same unlicensed band, and this gives rise to the issue of coexistence and fairness of two different technologies in the context of physical and link layer protocols. LTE in the Unlicensed (LTE-U) and LTE License Assisted Access (LTE-LAA) has been proposed in the literature for IoT system. The Third Generation Partnership (3GPP) has standardized LAA for industrial IoT. The coexistence mechanism of LAA follows Listen Before Talk (LBT), which is the same process of Wi-Fi system coexistence i.e., Carrier Sense Multiple Access (CSMA). LTE-U operates a carrier ON/OFF switch policy in duty cycles to maintain fairness in LTE and Wi-Fi transmissions. This mechanism causes spectrum inefficiency. Bajracharya et al. [
20] proposed a Machine Learning (ML)-based Adaptive Duty Cycle (ADC) and Dynamic Channel Switch (DCS) mechanism for network to access channel in dynamic network scenarios. ADC and DCS exploit Q-learning to determine the best policy to select an optimal channel and duty cycles. ADC reserve a specific number of sub-frames for Wi-Fi, whereas DCS avoids congested channels for LTE-U users. Performance evaluations are presented in comparison with the fixed duty cycle and channel occupancy time approach. Results show that their proposed method outperforms other methods in the context of fairness and throughput.
With the exponential growth of the IoT, the interaction of multiple physical devices is of extreme importance. These devices are often integrated using Radio Frequency Identification (RFID). The RFID automatically recognizes the object details by reading the physical objects. The system reader, which is equipped with a backend server, uses radio frequencies to communicate with the objects with RFID tags. It makes the practical usage of RFID very vast. Security is the most vital aspect of communication for authentication and securing private data. RFID-based security is beneficial in multiple ways, as RFID does not require a light source and line of sight scenario for communication. Hence RFID can be deployed to sensor monitoring, access control, real-time inventory, and security-aware management systems. However, due to limited computational and memory resources on an RFID tag, limited cryptographic operations can be applied. Therefore, an eavesdropper can forge and access the user’s private data. David et al. in [
21] proposed a hash-based RFID authentication mechanism for Context-Aware Sensor Management System (CASMS) to provide security to prevent attacks such as replay, man-in-the-middle, and desynchronization. Hash-based RFID authentication is the five-phase mechanism, namely pre-phase registration, reader pro-tag request and response, tag mutual session key authentication, back end server key authentication, and session key updating. Performance analysis is made based on the Packet Delivery Ratio (PDR) and End-to-End Delay (E2E). Results depict that the proposed model significantly improves PDR and E2E.
Water is the soul of life and essential to the well-being of every person, economy, and the ecosystem on Earth. More than 70% of the Earth is surface is covered by oceans, and they are critical to maintaining the weather and temperature around the globe and providing a means of transportation. However, more than 90% of oceans are unexplored even to the extent that they are still unseen by humans. IoT paved the way to explore and collect the data by connecting different types of networks underwater. Such networks are known as the Internet of Underwater Technology (IoUT) is an emerging technology to support Underwater Sensors Networks (UWSNs) for exploration of undiscovered marine resources. UWSN using communication cables and sensors and maintenance cost is very high. Therefore, underwater wireless communication is proposed. However, UWSN wireless communication is challenging due to environment and propagation losses, which include high noise, Doppler spreading, path loss, multi-path signal propagation, and high power consumption. To overcome these issues, Faheem et al. in [
22] proposed cross layered QoS Aware routing Protocol (QoSRP). The proposed scheme is composed of underwater channel detection, channel assignment, and packets forwarding. The QoSRP selects detects the high probability vacant channel and assigns the high data rate channels to an acoustic sensor node. The QoSRP also balances the traffic, avoids congestion, and data path loops to increase PDR and throughput of the system with minimum delay along the path.
Ultra Wide band (UWB) features include higher bandwidth, and it is one of the viable technologies for IoMT applications. The integration of UWB in health critical IoT applications can provide an effective and reliable solution for the monitoring of patients. Ataxia patients suffer from abnormal movement, and that severely affects walking activities. The walking activities can be classified as a normal walk, difficulty walking in a straight line, walking with heavy steps, and forward bending walking. All of these walking patterns except normal walking shows abnormality. Zilani et al. [
23] proposed a scheme to cater to this problem. They set up the testbed in an indoor environment. They collected sample walk patterns and classified it using Support Vector Machine (SVM) algorithms, namely SVM-based Sigmoid Kernel Function (SKF) and Radial Basis Function (RBF). Results show that RBF performs better than SKF. The drawback of the proposed scheme is that it is only tested for a single person. Hence, it should be extended to monitor multiple persons.
Security, privacy, and trust remain challenges in IoMT because of the openness and heterogeneity of IoMT. Access control is used to protect the confidentiality and integrity of constrained resources in IoMT services. It provides a solution to avoid any unauthorized access for multimedia applications in IoT services. However, due to increasing the number of users and multimedia services offered by the IoT platform, the access control system is becoming more and more multifaceted. Besides, access control policy evaluation reduces the performance of IoMT applications. Therefore, Meiping Liu et al. [
24] proposed an Attribute-Based Access Control (ABAC) policy retrieval method to improve the performance of access control policy evaluation in multimedia networks. To rebuild the policy decision tree, an attribute value level, and the depth index is introduced, thus, improve policy retrieval efficiency. Policy analysis is performed with a different number of rules and the increasing complexity of the policy. Results indicate that the proposed method is more efficient and scalable than the existing access control schemes.
Increasing demand for data-intensive applications is growing users’ data requirements exponentially. However, spectrum scarcity is the biggest hurdle in meeting users QoS. One of the viable solutions is to reuse and share the spectrum among the users to fulfill users demands without compromising the user’s experience. Even though unlicensed spectrums are available for free, they are already overcrowded. Different network technologies such as 5G and Wi-Fi use different spectrum access mechanisms, and sharing the spectrum among them is a trivial task. To allow fair coexistence between 5G and Wi-Fi networks operating in the same spectrum, LBT is introduced to work in parallel with the CSMA for channel access. RL techniques can be adapted to make a spectrum access mechanism to learn network conditions itself and adapt to the network changes accordingly. Consequently, the network becomes sustainable and self-adaptive. Neto et al. in [
25] proposed Q-Learning to LTE-U to adjust the duty cycle parameters to reduce coexistence interference and improve the system data rate. A saturated network scenario is considered to evaluate the proposed scheme in the ns-3 simulator. The proposed algorithm performs well in a multi-cell coexistence network scenario. Hence, it improves overall system performance by achieving a higher data rate for users and systems compared to the existing conventional mechanism.
4. Conclusions
Six papers in this SI presented state-of-the-art research trend in the area of IoMT opportunities, challenges, and solutions. The papers presented an interesting discussion and novel ideas for the readers. The guest editors would like to show appreciation to the authors and thank all the anonymous reviewers for providing constructive feedback to improve the overall quality of all the accepted papers. We would also like to thank sensors Editor in Chief Prof. Dr. Vittorio M.N. Passaro, Associate Editor in Chief of the IoT section Prof. Dr. Raffaele Bruno, and managing editor Missy Wu for the invaluable help and productive advice in finalizing this SI.
Author Contributions
Conceptualization, Y.B.Z. and M.K.A.; Writing—Original Draft Preparation, Y.B.Z.; Writing—Review & Editing, Y.B.Z., M.K.A., S.W.K.; Supervision, S.W.K. All authors have read and agreed to the published version of the manuscript.
Funding
This research received no external funding.
Acknowledgments
This research was supported in part by the Brain Korea 21 Plus Program (No. 22A20130012814) funded by the National Research Foundation of Korea (NRF), in part by the MSIT(Ministry of Science and ICT), Korea, under the ITRC(Information Technology Research Center) support program(IITP-2019-2016-0-00313) supervised by the IITP(Institute for Information & communications Technology Planning & Evaluation), and in part by Basic Science Research Program through the National Research Foundation of Korea (NRF) funded by the Ministry of Education (2018R1D1A1A09082266).
Conflicts of Interest
The authors declare no conflict of interest.
Abbreviations
The following abbreviations are used in this manuscript:
| ADC | Adaptive Duty Cycle |
| ABAC | Attribute-Based Access Control |
| CSMA | Carrier Sense Multiple Access |
| CASMS | Context-Aware Sensor Management System |
| DCS | Dynamic Channel Switch |
| E2E | End-to-End Delay |
| IoT | Internet of Things |
| IIoT | Industrial IoT |
| ICN | Information-centric networks |
| IoB | Internet of bodies |
| IoMNT | Internet of Multimedia Nano-Things |
| (IoMT) | Internet of Multimedia Things |
| IoUT | Internet of Underwater Technology |
| LBT | Listen Before Talk |
| LTE | Long Term Evolution |
| LTE-U | LTE in the Unlicensed |
| LTE-LAA | LTE License Assisted Access |
| ML | Machine Learning |
| MoS | Mean Opinion Score |
| OS | Operating Systems |
| PDR | Packet Delivery Ratio |
| QoSRP | QoS Aware routing Protocol |
| QoE | Quality of Experience |
| QoS | Quality of Service |
| RBF | Radial Basis Function |
| RFID | Radio Frequency Identification |
| RPL | Routing protocol for low-power and lossy networks |
| SKF | Sigmoid Kernel Function |
| SVM | Support Vector Machine |
| 3GPP | Third Generation Partnership |
| UWB | Ultra Wide band |
| VANETS | Vehicular Ad Hoc Networks |
References
- Zikria, Y.B.; Kim, S.W.; Hahm, O.; Afzal, M.K.; Aalsalem, M.Y. Internet of Things (IoT) Operating Systems Management: Opportunities, Challenges, and Solution. Sensors 2019, 19, 1793. [Google Scholar] [CrossRef]
- Zikria, Y.B.; Afzal, M.K.; Ishmanov, F.; Kim, S.W.; Yu, H. A survey on routing protocols supported by the Contiki Internet of things operating system. Future Gener. Comput. Syst. 2018, 82, 200–219. [Google Scholar] [CrossRef]
- Zikria, Y.B.; Yu, H.; Afzal, M.K.; Rehmani, M.H.; Hahm, O. Internet of Things (IoT): Operating System, Applications and Protocols Design, and Validation Techniques. Future Gener. Comput. Syst. 2018, 88, 699–706. [Google Scholar] [CrossRef]
- Zikria, Y.B.; Kim, S.W.; Afzal, M.K.; Wang, H.; Hahm, O.; Rehmani, M.H. 5G Mobile Services and Scenarios: Challenges and Solutions. Sustainability 2018, 10, 3626. [Google Scholar] [CrossRef]
- Afzal, M.K.; Zikria, Y.B.; Mumtaz, S.; Rayes, A.; Al-Dulaimi, A.; Guizani, M. Unlocking 5G Spectrum Potential for Intelligent IoT: Opportunities, Challenges, and Solutions. IEEE Commun. Mag. 2018, 56, 92–93. [Google Scholar] [CrossRef]
- Musaddiq, A.; Zikria, Y.B.; Hahm, O.; Yu, H.; Bashir, A.K.; Kim, S.W. A Survey on Resource Management in IoT Operating Systems. IEEE Access 2018, 6, 8459–8482. [Google Scholar] [CrossRef]
- Afzal, M.K.; Zikria, Y.B.; Ni, Q. Data-driven intelligence in wireless networks: Issues, challenges, and solution. Trans. Emerg. Tel. Tech. 2019, 30, e3722. [Google Scholar] [CrossRef]
- Al-Turjman, F.; Ever, E.; Zikria, Y.B.; Kim, S.W.; Elmahgoubi, A. SAHCI: Scheduling Approach for Heterogeneous Content-Centric IoT Applications. IEEE Access 2019, 7, 80342–80349. [Google Scholar] [CrossRef]
- Kazmi, H.S.Z.; Javaid, N.; Awais, M.; Tahir, M.; Shim, S.; Zikria, Y.B. Congestion avoidance and fault detection in WSNs using data science techniques. Trans. Emerg. Telecommun. Technol. 2019, e3756. [Google Scholar] [CrossRef]
- Rasool, I.U.; Zikria, Y.B.; Kim, S.W. A review of wireless access vehicular environment multichannel operational medium access control protocols: Quality-of-service analysis and other related issues. Int. J. Distrib. Sens. Netw. 2017, 13, 1–22. [Google Scholar] [CrossRef]
- Meng, Y.; Naeem, M.A.; Ali, R.; Zikria, Y.B.; Kim, S.W. DCS: Distributed Caching Strategy at the Edge of Vehicular Sensor Networks in Information-Centric Networking. Sensors 2019, 19, 4407. [Google Scholar] [CrossRef] [PubMed]
- Ali, R.; Shahin, N.; Zikria, Y.B.; Kim, B.; Kim, S.W. Deep Reinforcement Learning Paradigm for Performance Optimization of Channel Observation–Based MAC Protocols in Dense WLANs. IEEE Access 2018, 7, 3500–3511. [Google Scholar] [CrossRef]
- Ali, R.; Ali, N.; Zikria, Y.B.; Kim, B.; Kim, S.W. Performance optimization of QoS-supported dense WLANs using machine-learning-enabled enhanced distributed channel access (MEDCA) mechanism. Neural Comput. Appl. 2019, 0, 1–9. [Google Scholar] [CrossRef]
- Bajracharya, R.; Shrestha, R.; Zikria, Y.B.; Kim, S.W. LTE in the Unlicensed Spectrum: A Survey. IETE Tech. Rev. 2018, 35, 78–90. [Google Scholar] [CrossRef]
- Nauman, A.; Qadri, Y.A.; Amjad, M.; Zikria, Y.B.; Afzal, M.K.; Kim, S.W. Multimedia Internet of Things: A Comprehensive Survey. IEEE Access 2020, 8, 8202–8250. [Google Scholar] [CrossRef]
- Farooq, M.S.; Riaz, S.; Abid, A.; Umer, T.; Zikria, Y.B. Role of IoT Technology in Agriculture: A Systematic Literature Review. Electronics 2020, 9, 319. [Google Scholar] [CrossRef]
- Qadri, Y.A.; Nauman, A.; Zikria, Y.B.; Vasilakos, A.V.; Kim, S.W. The Future of Healthcare Internet of Things: A Survey of Emerging Technologies. IEEE Commun. Surv. Tutor. 2020. [Google Scholar] [CrossRef]
- Ibrahim, M.; Baloch, N.K.; Anjum, S.; Zikria, Y.B.; Kim, S.W. An Energy Efficient and Low Overhead Fault Mitigation Technique for Internet of Thing Edge Devices Reliable on-Chip Communication. Software: Practice and Experience. Available online: https://onlinelibrary.wiley.com/doi/pdf/10.1002/spe.2796 (accessed on 19 February 2020).
- Shafique, M.A.; Baloch, N.K.; Baig, M.I.; Hussain, F.; Zikria, Y.B.; Kim, S.W. NoCGuard: A Reliable Network-on-Chip Router Architecture. Electronics 2020, 9, 342. [Google Scholar] [CrossRef]
- Bajracharya, R.; Shrestha, R.; Kim, S.W. Q-Learning Based Fair and Efficient Coexistence of LTE in Unlicensed Band. Sensors 2019, 19, 2875. [Google Scholar] [CrossRef]
- Deebak, B.D.; Al-Turjman, F.; Mostarda, L. A Hash-Based RFID Authentication Mechanism for Context-Aware Management in IoT-Based Multimedia Systems. Sensors 2019, 19, 3821. [Google Scholar] [CrossRef]
- Faheem, M.; Butt, A.R.; Raza, B.; Alquhayz, H.; Ashraf, W.M.; Shah, B.S.; Ngadi, A.M.; Gungor, C.V. QoSRP: A Cross-Layer QoS Channel-Aware Routing Protocol for the Internet of Underwater Acoustic Sensor Networks. Sensors 2019, 19, 4762. [Google Scholar] [CrossRef] [PubMed]
- Zilani, T.A.; Al-Turjman, F.; Khan, M.B.; Zhao, N.; Yang, X. Monitoring Movements of Ataxia Patient by Using UWB Technology. Sensors 2020, 20, 931. [Google Scholar] [CrossRef] [PubMed]
- Liu, M.; Yang, C.; Li, H.; Zhang, Y. An Efficient Attribute-Based Access Control (ABAC) Policy Retrieval Method Based on Attribute and Value Levels in Multimedia Networks. Sensors 2020, 20, 1741. [Google Scholar] [CrossRef] [PubMed]
- Neto, D.M.J.; Neto, G.F.S.; Santana, M.P.; Junior, D.A.V. Multi-cell LTE-U/Wi-Fi coexistence evaluation using a reinforcement learning framework. Sensors 2020, 20, 1855. [Google Scholar] [CrossRef]
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).