A Survey of IoT Security Based on a Layered Architecture of Sensing and Data Analysis
Abstract
1. Introduction
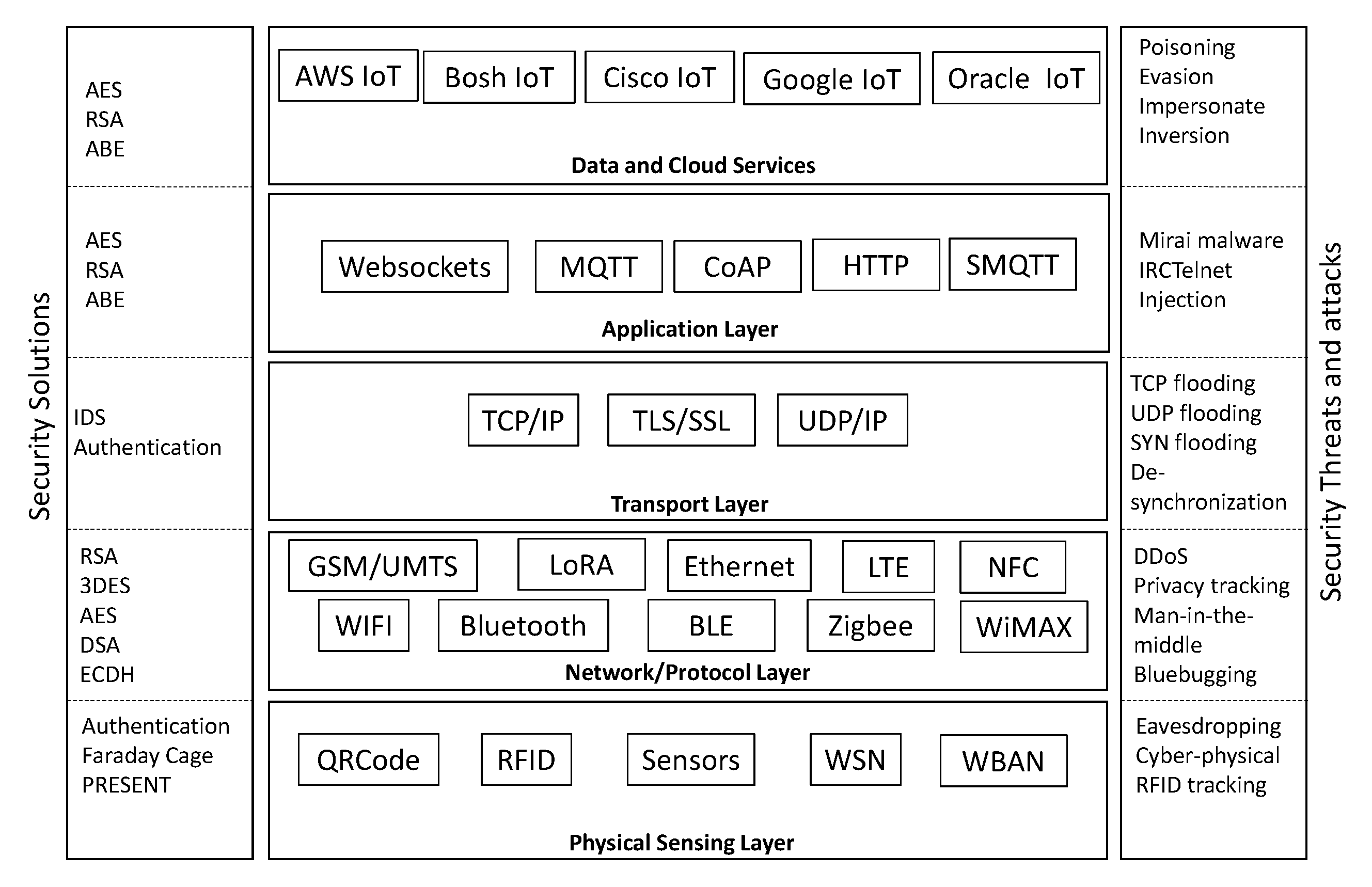
- Data and cloud services layer attacks include poisoning, evasion, impersonation, and inversion.
- Application layer attacks include Mirai malware, IPCTelnet malware, DDoS, and injection.
- Transport layer attacks include resource exhaustion, flooding, replay, DDoS attack, and amplification attacks.
- Network and protocol layer attacks include man-in-the-middle, DDoS, and replay attacks.
- Physical sensing layer attacks include eavesdropping, cyber-physical, and tracking attacks.
2. Physical Sensing Layer
2.1. Underlaying Technologies
2.2. Security Threats and Solutions
3. Network and Protocol Layer
3.1. Underlaying Technologies/Background
3.2. Security Threats and Countermeasures
- Bluejacking: This is the use of Bluetooth for sending unsolicited messages to other enabled devices. This attack exploits the Object Exchange (OBEX) protocol which is used by Bluetooth-enabled devices for exchanging data and commands [35].
- Bluesmack: This is an attack that causes denial of service to Bluetooth devices. This attack sends a Logic Link Control and Adaptation Protocol (L2CAP) ping request, which is similar to the ICMP ping attack, leading to devices being knocked out after receiving an oversized packet, which in turn leads to a DoS [38].
4. Transport Layer
4.1. Underlaying Technologies
4.2. Security Threats and Solutions
5. Application Layer
5.1. Underlaying Technologies
5.2. Security Threats and Solutions
6. Data and Cloud Services Layer
7. Open Research Issues and Future Directions
7.1. The Lack of Standardized Lightweight Encryption Algorithms for IoT Applications
7.2. Use of Machine Learning to Enhance Security in IoT
7.3. Blockchain in Smart IoT
7.4. Securing 4G/5G and beyond Applications
8. Conclusions
Funding
Conflicts of Interest
References
- Atzori, L.; Iera, A.; Morabito, G. The internet of things: A survey. Comput. Netw. 2010, 54, 2787–2805. [Google Scholar] [CrossRef]
- Whitmore, A.; Agarwal, A.; Da Xu, L. The Internet of Things—A survey of topics and trends. Inf. Syst. Front. 2015, 17, 261–274. [Google Scholar] [CrossRef]
- Asghari, P.; Rahmani, A.M.; Javadi, H.H.S. Internet of Things applications: A systematic review. Comput. Netw. 2019, 148, 241–261. [Google Scholar] [CrossRef]
- Mabkhot, M.M.; Al-Ahmari, A.M.; Salah, B.; Alkhalefah, H. Requirements of the smart factory system: A survey and perspective. Machines 2018, 6, 23. [Google Scholar] [CrossRef]
- Oueslati, N.E.; Mrabet, H.; Jemai, A.; Alhomoud, A. Comparative Study of the Common Cyber-physical Attacks in Industry 4.0. In Proceedings of the 2019 International Conference on Internet of Things, Embedded Systems and Communications (IINTEC), Tunis, Tunisia, 20–22 December 2019; pp. 1–7. [Google Scholar]
- Abrams, M.; Weiss, J. Malicious Control System Cyber Security Attack Case Study–Maroochy Water Services, Australia; The MITRE Corporation: Bedford, MA, USA, 2008. [Google Scholar]
- Maple, C. Security and privacy in the internet of things. J. Cyber Policy 2017, 2, 155–184. [Google Scholar] [CrossRef]
- Ustundag, A.; Cevikcan, E. Industry 4.0: Managing the Digital Transformation; Springer: Berlin/Heidelberg, Germany, 2017. [Google Scholar]
- Gloukhovtsev, M. IoT Security: Challenges, Solutions & Future Prospects. Available online: https://education.dellemc.com/content/dam/dell-emc/documents/en-us/2018KS_Gloukhovtsev-IoT_Security_Challenges_Solutions_and_Future_Prospects.pdf (accessed on 20 June 2020).
- Yang, Y.; Wu, L.; Yin, G.; Li, L.; Zhao, H. A survey on security and privacy issues in Internet-of-Things. IEEE Internet Things J. 2017, 4, 1250–1258. [Google Scholar] [CrossRef]
- Ammar, M.; Russello, G.; Crispo, B. Internet of Things: A survey on the security of IoT frameworks. J. Inf. Secur. Appl. 2018, 38, 8–27. [Google Scholar] [CrossRef]
- Al-Fuqaha, A.; Guizani, M.; Mohammadi, M.; Aledhari, M.; Ayyash, M. Internet of things: A survey on enabling technologies, protocols, and applications. IEEE Commun. Surv. Tutor. 2015, 17, 2347–2376. [Google Scholar] [CrossRef]
- Da Xu, L.; He, W.; Li, S. Internet of things in industries: A survey. IEEE Trans. Ind. Inform. 2014, 10, 2233–2243. [Google Scholar]
- Hammoudeh, M.; Epiphaniou, G.; Belguith, S.; Unal, D.; Adebisi, B.; Baker, T.; Kayes, A.; Watters, P. A service-oriented approach for sensing in the Internet of Things: Intelligent transportation systems and privacy use cases. IEEE Sens. J. 2020. [Google Scholar] [CrossRef]
- Suo, H.; Wan, J.; Zou, C.; Liu, J. Security in the internet of things: A review. In Proceedings of the 2012 International Conference on Computer Science and Electronics Engineering, Hangzhou, China, 23–25 March 2012; Volume 3, pp. 648–651. [Google Scholar]
- Ray, P.P. A survey on Internet of Things architectures. J. King Saud Univ. Comput. Inf. Sci. 2018, 30, 291–319. [Google Scholar]
- Butun, I.; Österberg, P.; Song, H. Security of the Internet of Things: Vulnerabilities, Attacks, and Countermeasures. IEEE Commun. Surv. Tutor. 2020, 22, 616–644. [Google Scholar] [CrossRef]
- Hussain, F.; Hussain, R.; Hassan, S.A.; Hossain, E. Machine learning in IoT security: Current solutions and future challenges. IEEE Commun. Surv. Tutor. 2020. [Google Scholar] [CrossRef]
- Khattab, A.; Jeddi, Z.; Amini, E.; Bayoumi, M. RFID security threats and basic solutions. In RFID Security; Springer: Berlin/Heidelberg, Germany, 2017; pp. 27–41. [Google Scholar]
- Chen, J.; Kher, S.; Somani, A. Distributed fault detection of wireless sensor networks. In Proceedings of the 2006 Workshop on Dependability Issues in Wireless ad hoc Networks and Sensor Networks, Los Angeles, CA, USA, 26 September 2006; ACM Press: New York, NY, USA, 2006; pp. 65–72. [Google Scholar]
- da Silva, A.P.R.; Martins, M.H.; Rocha, B.P.; Loureiro, A.A.; Ruiz, L.B.; Wong, H.C. Decentralized intrusion detection in wireless sensor networks. In Proceedings of the 1st ACM International Workshop on Quality of Service & Security in Wireless and Mobile Networks, Montreal, QC, Canada, 13 October 2005; ACM Press: New York, NY, USA, 2005; pp. 16–23. [Google Scholar]
- Wang, Y.; Wang, X.; Xie, B.; Wang, D.; Agrawal, D.P. Intrusion detection in homogeneous and heterogeneous wireless sensor networks. IEEE Trans. Mob. Comput. 2008, 7, 698–711. [Google Scholar] [CrossRef]
- Aamir, M.; Zaidi, M.A. A survey on DDoS attack and defense strategies: From traditional schemes to current techniques. Interdiscip. Inf. Sci. 2013, 19, 173–200. [Google Scholar] [CrossRef]
- Osanaiye, O.; Ogundile, O.; Aina, F.; Periola, A. Feature selection for intrusion detection system in a cluster-based heterogeneous wireless sensor network. Facta Univ. Ser. Electron. Energ. 2019, 32, 315–330. [Google Scholar] [CrossRef]
- Zou, S.; Xu, Y.; Wang, Y.; Li, Z.; Chen, S.; Hu, B. A Survey on Secure Wireless Body Area Networks. Secur. Commun. Netw. 2017, 2017, 1–9. [Google Scholar] [CrossRef]
- Belguith, S.; Kaaniche, N.; Laurent, M.; Jemai, A.; Attia, R. Phoabe: Securely outsourcing multi-authority attribute based encryption with policy hidden for cloud assisted iot. Comput. Netw. 2018, 133, 141–156. [Google Scholar] [CrossRef]
- Belguith, S.; Kaaniche, N.; Hammoudeh, M. Analysis of attribute-based cryptographic techniques and their application to protect cloud services. Trans. Emerg. Telecommun. Technol. 2019. [Google Scholar] [CrossRef]
- Kasmi, M.; Bahloul, F.; Tkitek, H. Smart home based on Internet of Things and cloud computing. In Proceedings of the 2016 7th International Conference on Sciences of Electronics, Technologies of Information and Telecommunications (SETIT), Hammamet, Tunisia, 18–20 December 2016; pp. 82–86. [Google Scholar]
- Ejaz, W.; Anpalagan, A.; Imran, M.A.; Jo, M.; Naeem, M.; Qaisar, S.B.; Wang, W. Internet of Things (IoT) in 5G wireless communications. IEEE Access 2016, 4, 10310–10314. [Google Scholar] [CrossRef]
- Madakam, S.; Lake, V.; Lake, V.; Lake, V. Internet of Things (IoT): A literature review. J. Comput. Commun. 2015, 3, 164. [Google Scholar] [CrossRef]
- Hassan, W.H. Current research on Internet of Things (IoT) security: A survey. Comput. Netw. 2019, 148, 283–294. [Google Scholar]
- Coskun, V.; Ozdenizci, B.; Ok, K. A survey on near field communication (NFC) technology. Wirel. Pers. Commun. 2013, 71, 2259–2294. [Google Scholar] [CrossRef]
- Bapat, C.; Baleri, G.; Inamdar, S.; Nimkar, A.V. Smart-lock security re-engineered using cryptography and steganography. In Proceedings of the International Symposium on Security in Computing and Communication, Manipal, India, 13–16 September 2017; Springer: Singapore, 2017; pp. 325–336. [Google Scholar]
- Vafaei, R. Encryption of 4G Mobile Broadband Systems. Available online: https://d1wqtxts1xzle7.cloudfront.net/37977538/Encryption_of_4G__mobile_broadband_.pdf?1435043247=&response-content-disposition=inline3B+filename3DEncryption_of_4G_mobile_broadband_system.pdf&Expires=1593318157&Signature=MnmQQhPUPwG2WDpoyoCvAN-lZ6QLH12S2wML3LHG9gPs5A3toNnjj60SKgXTmq~Bnb98RjoN5C5H8O8F~aACu8hu7KcBqvXaJiwtoE~rkwZWemqW7XMc-fclkKJTbSf-CFEY6vqc9FoeHmWMzBHcw4QDjgZvyKSsCtAYISPT6Vcu1bh7c4ToHumNNlVrjd37dUMOw83RCurhhbWxiIvf2R9DfVRWmBSZZTOC6gOVDsyQ77EMA7Uo7l97OKZYSGZ82xhblzPa~ye0e3Dz92tDSZGVs2zZB9Wg9GyU8ZZPasB2MNtHpOrXvoAZ3--c2FWXHpzDnwBFJIZqviQaG1RVFw__&Key-Pair-Id=APKAJLOHF5GGSLRBV4ZA (accessed on 20 June 2020).
- Mira, F.; Alsmadi, I. Review of Analysis on IoT Components, Devices and Layers Security. In Proceedings of the 2019 International Conference on Information Science and Communications Technologies (ICISCT), Tashkent, Uzbekistan, 4–6 November 2019; pp. 1–6. [Google Scholar]
- Laurie, A.; Herfurt, M.H.M. Hacking Bluetooth enabled mobile phones and beyond–Full Disclosure. In Proceedings of the 21st Chaos Communication Congress, Berliner Congress Center, Berlin, Germany, 27–29 December 2004. [Google Scholar]
- Liao, M. Bluetooth Vulnerabilities in Data Security of Mobile Phones. Available online: https://docs.lib.purdue.edu/dissertations/AAI1535052/ (accessed on 20 June 2020).
- Becker, A.; Paar, I.C. Bluetooth Security & Hacks; Ruhr-Universität Bochum: Bochum, Germany, 2007. [Google Scholar]
- Katagi, M.; Moriai, S. Lightweight Cryptography for the Internet of Things; Sony Corporation: Tokyo, Japan, 2008; pp. 7–10. [Google Scholar]
- Belguith, S.; Kaaniche, N.; Russello, G. CUPS: Secure opportunistic cloud of things framework based on attribute-based encryption scheme supporting access policy update. Secur. Priv. 2019. [Google Scholar] [CrossRef]
- Belguith, S.; Kaaniche, N.; Russello, G. Lightweight attribute-based encryption supporting access policy update for cloud assisted IoT. In Proceedings of the 15th International Joint Conference on e-Business and Telecommunications-Volume 1: SECRYPT, Porto, Portugal, 26–28 July 2018; SciTePress: Setúbal, Portugal, 2018; pp. 135–146. [Google Scholar]
- Yao, X.; Chen, Z.; Tian, Y. A lightweight attribute-based encryption scheme for the Internet of Things. Future Gener. Comput. Syst. 2015, 49, 104–112. [Google Scholar] [CrossRef]
- Saied, Y.B.; Olivereau, A.; Zeghlache, D.; Laurent, M. Lightweight collaborative key establishment scheme for the Internet of Things. Comput. Netw. 2014, 64, 273–295. [Google Scholar] [CrossRef]
- Belguith, S.; Kaaniche, N.; Mohamed, M.; Russello, G. Coop-daab: Cooperative attribute based data aggregation for internet of things applications. In OTM Confederated International Conferences “On the Move to Meaningful Internet Systems”; Springer: Berlin/Heidelberg, Germany, 2018; pp. 498–515. [Google Scholar]
- Belguith, S.; Kaaniche, N.; Mohamed, M.; Russello, G. C-ABSC: Cooperative attribute based signcryption scheme for internet of things applications. In Proceedings of the 2018 IEEE International Conference on Services Computing (SCC), San Francisco, CA, USA, 2–7 July 2018; pp. 245–248. [Google Scholar]
- Mektoubi, A.; Hassani, H.L.; Belhadaoui, H.; Rifi, M.; Zakari, A. New approach for securing communication over MQTT protocol A comparaison between RSA and Elliptic Curve. In Proceedings of the 2016 Third International Conference on Systems of Collaboration (SysCo), Casablanca, Morocco, 28–29 November 2016; pp. 1–6. [Google Scholar]
- Salman, T.; Jain, R. Networking protocols and standards for internet of things. Internet Things Data Anal. Handb. 2015, 2015, 215–238. [Google Scholar]
- Dragomir, D.; Gheorghe, L.; Costea, S.; Radovici, A. A survey on secure communication protocols for IoT systems. In Proceedings of the 2016 International Workshop on Secure Internet of Things (SIoT), Heraklion, Greece, 26–30 September 2016; pp. 47–62. [Google Scholar]
- Alhomoud, A.; Namanya, A.P.; Disso, J.P.; Awan, I. A Se/f/-healing Framework for Enterprise Networks to Combat Botnets Infections. Available online: https://repository.nauss.edu.sa/bitstream/handle/123456789/64743/A/20Self-healing/20Framework/20for/20Enterprise/20networks/20to/20combat/20Botnets/20infections.pdf?sequence=5 (accessed on 20 June 2020).
- Antonakakis, M.; April, T.; Bailey, M.; Bernhard, M.; Bursztein, E.; Cochran, J.; Durumeric, Z.; Halderman, J.A.; Invernizzi, L.; Kallitsis, M.; et al. Understanding the mirai botnet. In Proceedings of the 26th USENIX Security Symposium (USENIX Security 17), Vancouver, BC, Canada, 16–18 August 2017; pp. 1093–1110. [Google Scholar]
- Kotey, S.D.; Tchao, E.T.; Gadze, J.D. On Distributed Denial of Service Current Defense Schemes. Technologies 2019, 7, 19. [Google Scholar] [CrossRef]
- Singh, M.; Rajan, M.; Shivraj, V.; Balamuralidhar, P. Secure MQTT for Internet of Things (IoT). In Proceedings of the 2015 Fifth International Conference on Communication Systems and Network Technologies, Gwalior, India, 4–6 April 2015; pp. 746–751. [Google Scholar]
- Granjal, J.; Monteiro, E.; Silva, J.S. Security for the internet of things: A survey of existing protocols and open research issues. IEEE Commun. Surv. Tutor. 2015, 17, 1294–1312. [Google Scholar] [CrossRef]
- Rizvi, S.; Kurtz, A.; Pfeffer, J.; Rizvi, M. Securing the internet of things (IoT): A security taxonomy for IoT. In Proceedings of the 2018 17th IEEE International Conference on Trust, Security and Privacy in Computing and Communications/12th IEEE International Conference on Big Data Science and Engineering (TrustCom/BigDataSE), New York, NY, USA, 1–3 August 2018; pp. 163–168. [Google Scholar]
- Greene, S.S. Security Program and Policies: Principles and Practices; Pearson Education: London, UK, 2014. [Google Scholar]
- Iova, O.; Picco, P.; Istomin, T.; Kiraly, C. Rpl: The routing standard for the internet of things... or is it? IEEE Commun. Mag. 2016, 54, 16–22. [Google Scholar] [CrossRef]
- Tiwari, S.; Trivedi, M.C.; Mishra, K.K.; Misra, A.; Kumar, K.K. Smart Innovations in Communication and Computational Sciences: Proceedings of ICSICCS-2018; Springer: Berlin/Heidelberg, Germany, 2018; Volume 851. [Google Scholar]
- Poschmann, A.Y. Lightweight Cryptography: Cryptographic Engineering for a Pervasive World. Ph.D. Thesis, Ruhr University Bochum, Bochum, Germany, 2009. [Google Scholar]
- Shirai, T.; Shibutani, K.; Akishita, T.; Moriai, S.; Iwata, T. The 128-bit blockcipher CLEFIA. In Proceedings of the International Workshop on Fast Software Encryption, Luxembourg, 26–28 March 2007; Springer: Berlin/Heidelberg, Germany, 2007; pp. 181–195. [Google Scholar]
- Tewari, A.; Gupta, B. A lightweight mutual authentication protocol based on elliptic curve cryptography for IoT devices. Int. J. Adv. Intell. Paradig. 2017, 9, 111–121. [Google Scholar] [CrossRef]
- Odelu, V.; Das, A.K. Design of a new CP-ABE with constant-size secret keys for lightweight devices using elliptic curve cryptography. Secur. Commun. Netw. 2016, 9, 4048–4059. [Google Scholar] [CrossRef]
- Mahdavinejad, M.S.; Rezvan, M.; Barekatain, M.; Adibi, P.; Barnaghi, P.; Sheth, A.P. Machine learning for Internet of Things data analysis: A survey. Digit. Commun. Netw. 2018, 4, 161–175. [Google Scholar] [CrossRef]
- Hammoudeh, M.; Newman, R. Information extraction from sensor networks using the Watershed transform algorithm. Inf. Fusion 2015, 22, 39–49. [Google Scholar] [CrossRef]
- Derguech, W.; Bruke, E.; Curry, E. An autonomic approach to real-time predictive analytics using open data and internet of things. In Proceedings of the 2014 IEEE 11th International Conference on Ubiquitous Intelligence and Computing and 2014 IEEE 11th International Conference on Autonomic and Trusted Computing and 2014 IEEE 14th International Conference on Scalable Computing and Communications and Its Associated Workshops, Bali, Indonesia, 9–12 December 2014; pp. 204–211. [Google Scholar]
- Wu, C.H.; Ho, J.M.; Lee, D.T. Travel-time prediction with support vector regression. IEEE Trans. Intell. Transp. Syst. 2004, 5, 276–281. [Google Scholar] [CrossRef]
- Hammoudeh, M.; Newman, R.; Dennett, C.; Mount, S. Interpolation techniques for building a continuous map from discrete wireless sensor network data. Wirel. Commun. Mob. Comput. 2013, 13, 809–827. [Google Scholar] [CrossRef]
- Hammoudeh, M.; Newman, R.; Dennett, C.; Mount, S.; Aldabbas, O. Map as a service: A framework for visualising and maximising information return from multi-modalwireless sensor networks. Sensors 2015, 15, 22970–23003. [Google Scholar] [CrossRef]
- Campello, R.J.; Moulavi, D.; Sander, J. Density-based clustering based on hierarchical density estimates. In Pacific-Asia Conference on Knowledge Discovery and Data Mining; Springer: Berlin/Heidelberg, Germany, 2013; pp. 160–172. [Google Scholar]
- Wang, C.; Dong, S.; Zhao, X.; Papanastasiou, G.; Zhang, H.; Yang, G. Saliencygan: Deep learning semi-supervised salient object detection in the fog of iot. IEEE Trans. Ind. Inform. 2019, 16, 2667–2676. [Google Scholar] [CrossRef]
- Alqahtani, H.; Kavakli-Thorne, M.; Kumar, G. Applications of generative adversarial networks (gans): An updated review. In Archives of Computational Methods in Engineering; Springer: Berlin/Heidelberg, Germany, 2019; pp. 1–28. [Google Scholar]
- Peixoto, S.A.; Vasconcelos, F.F.; Guimarães, M.T.; Medeiros, A.G.; Rego, P.A.; Neto, A.V.L.; de Albuquerque, V.H.C.; Rebouças Filho, P.P. A high-efficiency energy and storage approach for IoT applications of facial recognition. Image Vis. Comput. 2020, 96, 103899. [Google Scholar] [CrossRef]
- Rajesh, S.; Paul, V.; Menon, V.G.; Khosravi, M.R. A secure and efficient lightweight symmetric encryption scheme for transfer of text files between embedded IoT devices. Symmetry 2019, 11, 293. [Google Scholar] [CrossRef]
- Yu, W.; Köse, S. A lightweight masked AES implementation for securing IoT against CPA attacks. IEEE Trans. Circuits Syst. I Regul. Pap. 2017, 64, 2934–2944. [Google Scholar] [CrossRef]
- Belguith, S.; Kaaniche, N.; Russello, G. PU-ABE: Lightweight attribute-based encryption supporting access policy update for cloud assisted IoT. In Proceedings of the 2018 IEEE 11th International Conference on Cloud Computing (CLOUD), San Francisco, CA, USA, 2–7 July 2018; pp. 924–927. [Google Scholar]
- Belguith, S.; Kaaniche, N.; Hammoudeh, M.; Dargahi, T. PROUD: Verifiable privacy-preserving outsourced attribute based signcryption supporting access policy update for cloud assisted IoT applications. Future Gener. Comput. Syst. 2019, 111, 899–918. [Google Scholar] [CrossRef]
- da Costa, K.A.; Papa, J.P.; Lisboa, C.O.; Munoz, R.; de Albuquerque, V.H.C. Internet of Things: A survey on machine learning-based intrusion detection approaches. Comput. Netw. 2019, 151, 147–157. [Google Scholar] [CrossRef]
- Doshi, R.; Apthorpe, N.; Feamster, N. Machine learning ddos detection for consumer internet of things devices. In Proceedings of the 2018 IEEE Security and Privacy Workshops (SPW), San Francisco, CA, USA, 24 May 2018; pp. 29–35. [Google Scholar]
- Carlin, A.; Hammoudeh, M.; Aldabbas, O. Defence for distributed denial of service attacks in cloud computing. Procedia Comput. Sci. 2015, 73, 490–497. [Google Scholar] [CrossRef]
- Carlin, A.; Hammoudeh, M.; Aldabbas, O. Intrusion detection and countermeasure of virtual cloud systems-state of the art and current challenges. Int. J. Adv. Comput. Sci. Appl. 2015, 6. [Google Scholar] [CrossRef]
- Zhao, S.; Li, W.; Zia, T.; Zomaya, A.Y. A dimension reduction model and classifier for anomaly-based intrusion detection in internet of things. In Proceedings of the 2017 IEEE 15th International Conference on Dependable, Autonomic and Secure Computing, 15th International Conference on Pervasive Intelligence and Computing, 3rd International Conference on Big Data Intelligence and Computing and Cyber Science and Technology Congress (DASC/PiCom/DataCom/CyberSciTech), Orlando, FL, USA, 6–10 November 2017; pp. 836–843. [Google Scholar]
- Dai, H.N.; Zheng, Z.; Zhang, Y. Blockchain for internet of things: A survey. IEEE Internet Things J. 2019, 6, 8076–8094. [Google Scholar] [CrossRef]
- Wan, J.; Li, J.; Imran, M.; Li, D. A blockchain-based solution for enhancing security and privacy in smart factory. IEEE Trans. Ind. Informat. 2019, 15, 3652–3660. [Google Scholar] [CrossRef]
- Lin, C.; He, D.; Huang, X.; Choo, K.; Vasilakos, V. BSeIn: A blockchain-based secure mutual authentication with fine grained access control system for industry 4.0. J. Netw. Comput. Appl. 2018, 116, 42–52. [Google Scholar] [CrossRef]
- Yang, Y.; Wu, L.; Yin, G.; Li, L.; Zhao, H. Blockchain Technologies for the Internet of Things: Research Issues and Challenges. IEEE Internet Things J. 2019, 6, 2188–2204. [Google Scholar]
- Kure, E.; Engelstad, P.; Maharjan, S.; Gjessing, S.; Zhang, Y. Distributed uplink offloading for IoT in 5G heterogeneous networks under private information constraints. IEEE Internet Things J. 2019, 6, 6151–6164. [Google Scholar] [CrossRef]
- Ferrag, M.; Maglaras, L.; Argyriou, A.; Kosmanos, D.; Janicke, H. Security for 4G and 5G cellular networks: A survey of existing authentication and privacy-preserving schemes. J. Netw. Comput. Appl. 2018, 101, 55–82. [Google Scholar] [CrossRef]
- Mhatli, S.; Mrabet, H.; Dayoub, I. Extensive Capacity Simulations of Massive MIMO Channels for 5G Mobile Communication System. In Proceedings of the 2019 2nd International Conference on Computer Applications and Information Security (ICCAIS), Riyadh, Saudi Arabia, 1–3 May 2019; pp. 1–6. [Google Scholar]
- Mrabet, H. Performance Investigation of New Waveforms in CRAN Architecture for 5G Communication Systems. In Proceedings of the IEEE 2020 3rd International Conference on Computer Applications and Information Security (ICCAIS), Riyadh, Saudi Arabia, 19–21 March 2020; pp. 1–5. [Google Scholar]
| Layer | Common Attack | Description | Security Countermeasures |
|---|---|---|---|
| Data and Cloud services | Poisoning | input of incorrect training data/labels to decrease the accuracy of classification/clustering process | Data sanitization. |
| Evasion | Generating an adversarial sample leading to evade system from detection spam and malware. | Retraining learning models by classifier designers with adversarial samples. | |
| Impersonate | Unauthorized access based on deep neural network DNN algorithm. | Defensive distillation on DNN. | |
| Inversion | Gathering information about ML models to compromise the data privacy. | Differential privacy (DP) technique and data encryption. | |
| Application | Mirai malware | Gain access to IoT device by using a default Telnet or SSH account | Disabling/changing default account of Telnet and SSH account. |
| IRCTelnet | Forcing Telnet port to infect LINUX operating system of IoT device. | Disabling Telnet port number. | |
| Injection | Untrusted data is sent to an interpreter as part of a command or query. | Input validation control. | |
| Transport | TCP flooding | Sending many packets through TCP protocol to stop or to reduce his activities. | A classifier based on SVM to detect and prevent DDoS TCP flooding attack. |
| UDP flooding | Sending a large number of packets through UDP protocol to stop or to reduce his activities. | A flow-based detection schema on router using a state machine and a hashing table. | |
| TCP SYN flooding | Tentative to open an externally connection without respecting to the TCP handshake procedure. | SYN-Cookies consist on coding client SYN message to change the state in the server side. | |
| TCP desynchronization | Tentative to break the packet sequence by injection a packet with a wrong sequence number. | Authentication for all packets in the TCP session. | |
| Network/protocol | Man-in-the-middle | Violate the confidentiality and integrity in data transfer. | Intrusion-detection system (IDS) and virtual private network (VPN). |
| DDoS | Making network resource unavailable for its intended use | Ingress/Egress filtering, D-WARD, Hop Count Filtering and SYN-Cookies. | |
| Replay | Manipulate the message stream and reorder the data packets. | Timeliness of Message. | |
| Physical | Eavesdropping | Infer information sent by IoT devices via network | Faraday cage. |
| Cyber-physical | Physically attacking a device | Use of fault-detection algorithm to identify the faulty nodes. | |
| RFID Tracking | to disable tags, modify their contents, or imitate them | Faraday cage. |
| Communication Protocol | Standards | Encryption Protocol | Energy Consumption | Advantages | Disadvantages |
|---|---|---|---|---|---|
| 6LoWPAN | IEEE 802.15.4 | AES | Low | Low processing | Lack of authentication |
| RPL | IETF RPL | AES | Low | Low processing | Vulnerability to many attacks |
| NFC | ISO/IEC 14443 | RSA, DSA | Low | Simplicity of deployment | Limited Range |
| Bluetooth | IEEE 802.16 | AES, ECDH | Medium/Very Low (BLE) | Low consumption | Privacy/Identity Tracking |
| Wi-Fi | IEEE 802.11i/e/g | AES | High | Mobility and efficiency | Limited reachability |
| Zigbee | IEEE 802.15.4 | AES | Low | Low-cost, low-energy devices | one-time transmission of the unprotected key |
| WiMAX | IEEE 802.16 | RSA | Medium | Supports authentication | Limited mobility |
| 3G/4G/5G | UMTS/LTE | RSA, 3DES | Medium | Portability | Battery limitation |
| OSI Layer | Protocol |
|---|---|
| Application | SMQTT |
| Session | SSL/TLS |
| Transport | TCP |
| Network | IPv4 and IPv6 |
| Data-link | Ethernet/Wi-Fi |
| Algorithm | Key Size | Execution Time | Application | |
|---|---|---|---|---|
| Symmetric | PRESENT | 64 bits block with 80/128-bit length key | 27.9 | RFID |
| CELFIA | 128 bits block with 80/128/192 bits length key | - | Used by Sony for Digital Right Management | |
| Asymmetric | RSA | 1764 Bytes | 19.33 | Authentication |
| Elliptic Curves | 1272 Bytes | 87.03 | Pervasive Computing |
| Cloud-Based IoT Framework | Confidentiality | Integrity | Access Control | Authentication | Secure Communication | Encryption Protocol |
|---|---|---|---|---|---|---|
| AWS IoT | SSL-protected, API endpoints | SSL-protected, API endpoints | Policy-based | X.509 certificates | SSL | TLS |
| Google IoT | ATLS | ATLS | Cloud IAM ACLs | ATLS RSA 2048 | HTTPS, SSL | AES, 3DESTLS/S/MIME |
| Oracle IoT | SSL | PKI: Checksums | Roles-based | PKI: X.509 certificates, Kerberos | SSL | 3DES, TSDP |
| CISCO IoT | IPsec | IPsec | Segment data based on destination | X.509 certificates | IPsec, TLS, MQTT over TLS | TLS, AES, RSA |
| Bosh IoT | WPA2 | WPA2 | No access control | SSID/Password | DTLS | LWM2M |
| Algorithm | Complexity for Prediction | Advantages | Disadvantages | IoT Applications | |
|---|---|---|---|---|---|
| Classification | KNN | O(np) | Easy to update in online setting | Unscalable to large data sets | Smart Citizen, Smart Tourism |
| Naive Bayes | O(p) | Fast and highly scalable | Strong feature independence assumptions | Smart Agriculture, Spam filtering, Text categorization | |
| SVM | O() | Good for unbalanced data | The lack of transparency of results | Real-Time Prediction: Detection of Intrusion, attacks and malware. | |
| Regression | Linear regression | O(p) | Processing under high rate | Very sensitive to outliers | Energy Applications, Market Prediction |
| SVR | O() | Useful and flexible technique | More complicated | Intelligent transportation systems, Smart Weather | |
| Clustering | K-means | O(n2) | Very fast and highly scalable | Difficult to predict the number of clusters (K-Value) | Smart Cities, Smart Home, Smart Citizen, Intelligent Transport |
| DBSCAN | O(n2) | fast and robust against outliers | Performance is sensitive to the distance metric | Smart Citizen, Smart Tourism | |
| Feed Forward Neural Network | O(n2) | Non-linearity and robustness | Longer time for training | Smart Health |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Mrabet, H.; Belguith, S.; Alhomoud, A.; Jemai, A. A Survey of IoT Security Based on a Layered Architecture of Sensing and Data Analysis. Sensors 2020, 20, 3625. https://doi.org/10.3390/s20133625
Mrabet H, Belguith S, Alhomoud A, Jemai A. A Survey of IoT Security Based on a Layered Architecture of Sensing and Data Analysis. Sensors. 2020; 20(13):3625. https://doi.org/10.3390/s20133625
Chicago/Turabian StyleMrabet, Hichem, Sana Belguith, Adeeb Alhomoud, and Abderrazak Jemai. 2020. "A Survey of IoT Security Based on a Layered Architecture of Sensing and Data Analysis" Sensors 20, no. 13: 3625. https://doi.org/10.3390/s20133625
APA StyleMrabet, H., Belguith, S., Alhomoud, A., & Jemai, A. (2020). A Survey of IoT Security Based on a Layered Architecture of Sensing and Data Analysis. Sensors, 20(13), 3625. https://doi.org/10.3390/s20133625







