1. Introduction
In recent years, the trend towards underwater environment exploration has gained significant attention due to the immense number of underwater applications such as environmental monitoring, ocean sampling, undersea exploration, assisted navigation, disaster prevention [
1,
2], mine reconnaissance, and pollution monitoring, and localization [
3,
4]. Typically, wireless sensors (nodes) are deployed in a targeted area to sense information of interest. The sensed information is then sent to surface sink(s) where it is properly interpreted [
5]. Based on the interpreted data, experts or expert systems take necessary measures subject to task completion. The underwater nodes have more costly hardware than the terrestrial ones, and need relatively high transmit power to account for the harsh underwater channel conditions [
6]. These nodes are prone to failure as they have limited battery power. Typically, the propagation delay in Underwater Wireless Sensor Networks (UWSNs) is five times larger than terrestrial sensor networks [
7], the available bandwidth is highly limited, and Global Positioning System (GPS) is not available [
8].
In addition to energy-efficient network operations, most of the underwater applications demand higher throughput and minimum end-to-end delay
. At the network layer, routing protocols play an important role in conserving node energy and improving throughput of the network. However, the uneven and drastic conditions of the ocean make the routing task highly challenging. Moreover, the lack of GPS in the underwater environment further complicates the process. In terms of location, the only available information underwater is depth of nodes. The authors in [
9] use this information to route data from source(s) at higher depth to destination/sink at lower depth. However, the intermediate nodes are heavily involved in data-forwarding. To reduce forwarding load on relaying nodes, mobile sink is introduced in [
10]. In the literature, mobile sink is also known as the courier node [
11] and Autonomous Underwater Vehicle (AUV) [
12]. Mobile sinks are equipped with high energy source and long-range communication capabilities. Mobile sinks move within the targeted network field and collect data from nodes.
In this research work, our main contributions are: the introduction of delay-intolerant routing protocol algorithm for applications such as navy battle surveillance, tsunami warnings etc.; the reduction of and maximization of throughput; mobile sink is used to further reduce nodal propagation delay and energy consumption; the adoption of varying () and data aggregation with pattern-matching technique further helps to reduce number of re-transmissions that ultimately conserve energy and enhances throughput. We use mobile sink in a three-dimensional (3-D) underwater network field to decrease the transmission distance between source and destination node. Thus, the usage of mobile sink reduces the propagation delay and enhances the throughput. Based on the availability of nodes in the vicinity of the source node, we optimize () between the source and forwarding node to reduce the number of transmissions and receptions. A reduced number of transmissions and receptions has two major benefits; minimized energy consumption and minimized nodal delays. Therefore, simulation results show that the overall proposed approach yields maximum throughput, minimal , and maximized network lifetime.
The rest of the sections are organized as follows:
Section 2 discusses the work done in this domain,
Section 3 deals with energy-consumption model,
Section 4 focuses on the calculation of optimal
, and
Section 5 discusses the proposed DIEER protocol,
Section 6 formulates network lifetime maximization and
minimization models as linear programs,
Section 7 discusses experimental results, and finally conclusions are presented in
Section 8.
4. Calculation of Optimal Radius of Depth Threshold
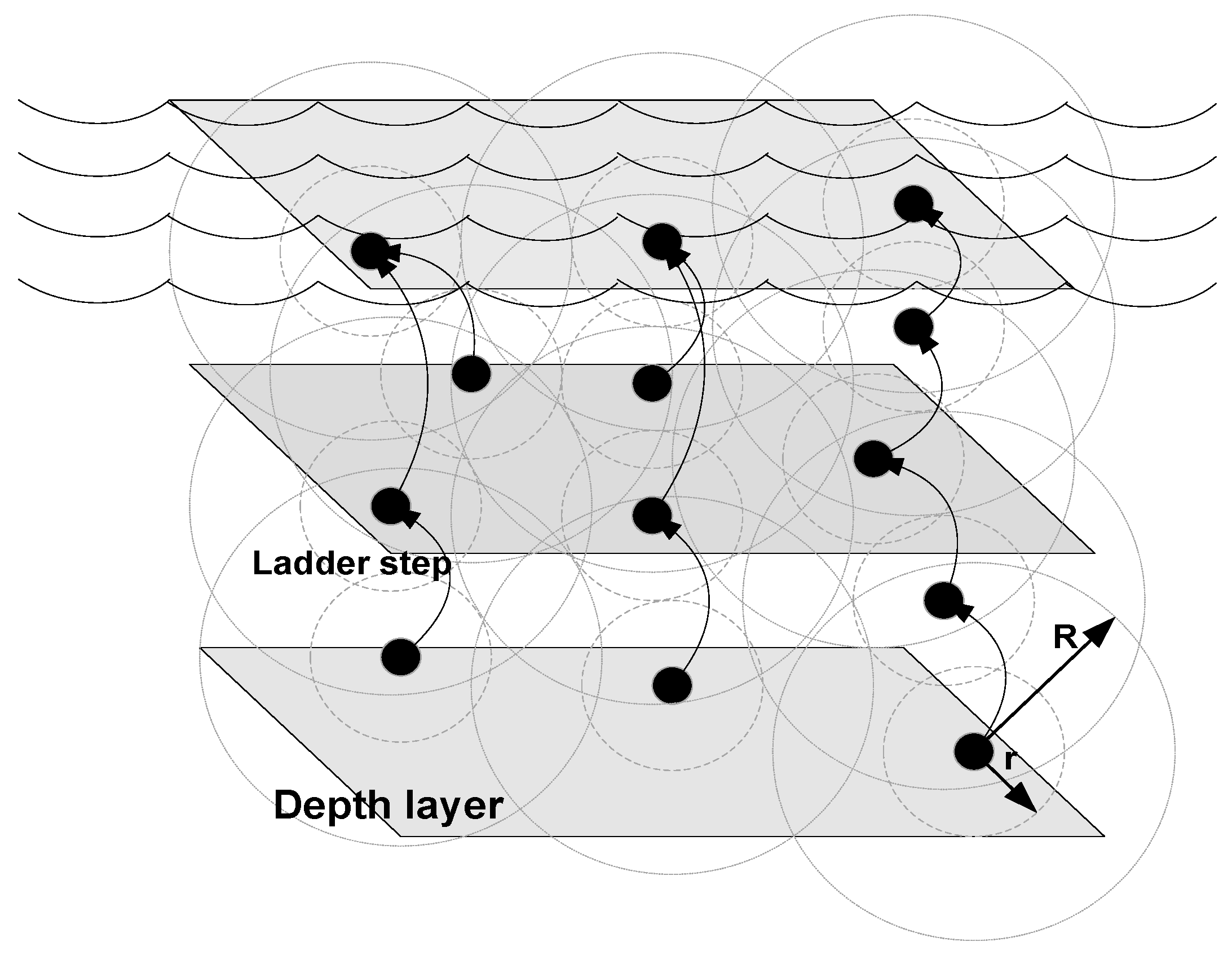
In this paper, we assume that nodes are deployed in a 3-D network field as shown in Figure 7. Data travels from nodes on the seabed towards surface sinks through nodes suspended in different layers of sea. Node placement in layers of sea are analogous to ladder steps. Each step of the ladder is considered to be a sea plane as shown in
Figure 2.
is a selection of transmission ranges for each node. There is a tradeoff between
, energy consumption, and propagation delay. Higher
means higher energy consumption with less propagation delay while lower
means less energy consumption with large propagation delay. Since each node keeps the list of alive neighbor nodes, in the beginning of the network operation
remain large. However, as node density reduces due to death of nodes,
becomes small. Therefore, large
at the network start-up consumes energy, but at the benefit of smaller propagation delay. On the other hand when sparsity of the nodes increases due to regular deaths then small
leads to reduced energy consumption. Thus, based on the above discussion, we define
as
where
R is the communication radius of the node,
is the node density of the alive forwarding nodes measured in percent and
n is the step size, which is considered to be constant. In our case we assume
. In the start of operation
, this means that
of
R. However, as the network operation evolves,
decreases say for example 20% nodes die out, and then
of
R and so on.
5. DIEER Protocol Overview
In this research work, we are motivated from [
12,
15]. The work done in [
12] can only be used for delay-tolerant applications because when AUV collects data from one 3-D zone the nodes in other 3-D zones remain in sleep mode. Thus, the AUV spends surplus time in each zone. If there are
n-zones and AUV spends
amount of time in each zone then a total delay of
will be created in one round of data collection. Therefore, this technique is inappropriate for delay-intolerant applications. It also affects throughput for an interval of time. The metric presented in [
15] is not sufficient for energy-efficient routing in the sparse and dense deployment of nodes. The selection of a forwarder node needs to be modified especially when the network becomes sparse due to the death of nodes.
Delay-Intolerant Energy-Efficient Routing (DIEER) is a greedy algorithm with optimized sink mobility that forwards the data packets from source node to destination. The forwarding node’s depth decreases as the packet travels towards the surface sinks. In DIEER, nodes make packet-forwarding decision based on defined priorities, such as the availability of mobile sink in its vicinity, and data-forwarding to minimum depth node. If the depth of the source node is and depth of its forwarder node is then otherwise forwarder node simply drops the packet.
5.1. Adaptive Depth Threshold Mechanism (ADTM)
The data packet broadcast by the source node is received by multiple nodes within
R of source node; therefore, if all eligible nodes forward the same packet, high energy consumption and high collision will occur. To reduce the transmission of same packets by multiple nodes, the number of forwarder nodes needs to be restricted. According to ADTM, each node selects a set of neighboring nodes within
R and
r. Variation in
r of
depends upon the number of alive nodes in the vicinity of the source node. If a greater number of alive nodes exist within
R of the source node, then
r of
increases and vice versa.
Figure 3 depicts the comparison of small
with optimal
. It is shown in
Figure 3 that when
is small the number of transmission(s) are increased which leads to increased energy consumption because when multiple nodes receive and transmit the same data packet the overall energy consumption increases. However, for optimal
the transmission(s) and reception(s) decrease which ultimately reduces the energy consumption.
5.2. Hold and Forward Mechanism (HFM)
In DIEER, the node forwards the data packet by using a Hold and Forward Mechanism (HFM) mechanism. HFM is depicted in
Figure 4. Each receiving node holds the data packet for a certain interval of time known as Holding Time (HT).The calculation of HT depends on the depth difference between the receiving node and the transmitting node. If the depth difference is large then the packet holding time is minimum and vice versa. HT and Depth Difference (DD) are inversely proportional to each other (
). During HT, if a node finds a mobile sink in its vicinity then the first data packet is transmitted to the mobile sink.
Figure 5a shows an elliptical path of sink mobility in which the mobile sink is in direct communication range of node
,
and
. In this case, the nodes first calculate their distance from the mobile sink, if their distance with the mobile sink is less as compared to next forwarder node then it simply transmits the data packet to the mobile sink.
If the mobile sink is not available, then the data packet is forwarded to the next hop node. For example,
in
Figure 5b is the transmitter node and
,
,
are its one-hop threshold-based neighbor. The solid line shows the transmission range of
. When
broadcasts a packet, all its neighbor nodes receive this packet. As
is at lower depth than
, it discards the packet.
and
are eligible forwarders because these are at higher depth than
. The depth of
is less than
, thus, HT of
is less than
.
5.3. Data Aggregation with Pattern Matching
A sensor node by its nature sense the environmental parameters periodically as per requirement. In data-sensitive applications, the sensing time span is very short. Therefore, nodes record plenty of redundant data of similar values. To reduce the redundancy, data aggregation is required. Several data-aggregation techniques are introduced in the literature [
31]. Pattern matching is a popular data-aggregation technique [
32]. To improve energy conservation, we use Algorithm 1 for pattern matching. Before transmitting the data packet, each node executes Algorithm 1 to generate a pattern code. Pattern codes are generated up to a predefined threshold value. If the generated code is equal to or greater than the threshold value, then data is sent as it is; otherwise, only a pattern code is embedded in the packet. The pattern-matching algorithm helps to reduce energy consumption remarkably, especially at forwarder nodes, where more than one node’s data is aggregated and forwarded.
| Algorithm 1 Data Aggregation with Pattern Matching. |
| INITIALIZATIONS |
| thresholdvalue |
| code |
| p_code = Generate_pattern_code(data,code) |
| END INITIALIZATIONS |
| int Generate_pattern_code(data,code) |
| { |
| data_matched = Compare_data_with_stored_pattern(data,code) |
| if (data_matched) then |
| return (code) |
| else |
| return () |
| end if |
| } END Generate_pattern_code |
| if (p_code ) then |
| send_data(data) |
| else |
| send_data(p_code) |
| end if |
| |
6. Network Lifetime Maximization and Minimization Models
Since energy-efficient and delay-intolerant protocol designs are our main concerns, and there are many ways/techniques of doing so. In this regard, we have exploited the network layer. However, to further improve energy efficiency of the network and to down-scale
, we present formulation via linear programming. The first objective, to maximize the network lifetime
, is as follows:
Subject to,
where
and
. Here,
provides a formal explanation about the involved processes; sensing (
), transmission (
), reception (
), and data aggregation (
). The objective function is presented in Equation (
21), i.e., to maximize the
. Constraint in Equation (
21a) states that each node is initially equipped with limited energy
upper bounded by
. Constraint in Equation (
21b) jointly considers sensing, reception, transmission, and aggregation while ensuring that these processes respect their initial levels, such that
. Our proposed DIEER protocol uses optimal
and mobile sink as tools to minimize the number of transmissions, receptions, and aggregator nodes to minimize energy-consumption cost due to these processes. Constraint in Equation (
21c) ensures flow conservation (i.e., flow through the link from node
i to node
j must respect the physical link capacity
) while routing data from source node to sink. Violation of (
21c) leads to increased contention/congestion which is directly related to both packet drop rate and
. Whenever the dropped packets are re-transmitted, the surplus energy is spent leading to decreased
. Constraint in Equation (
21d) focuses on the minimization of re-transmissions to further down-scale the energy-consumption cost. The proposed DIEER protocol implements holding time to respect constraints in Equations (
21c,d). Finally, constraint in Equation (
21e) deals with minimization of the number of hops
to maximize
. The proposed DIEER protocol efficiently uses mobile sink and optimal
to minimize
.
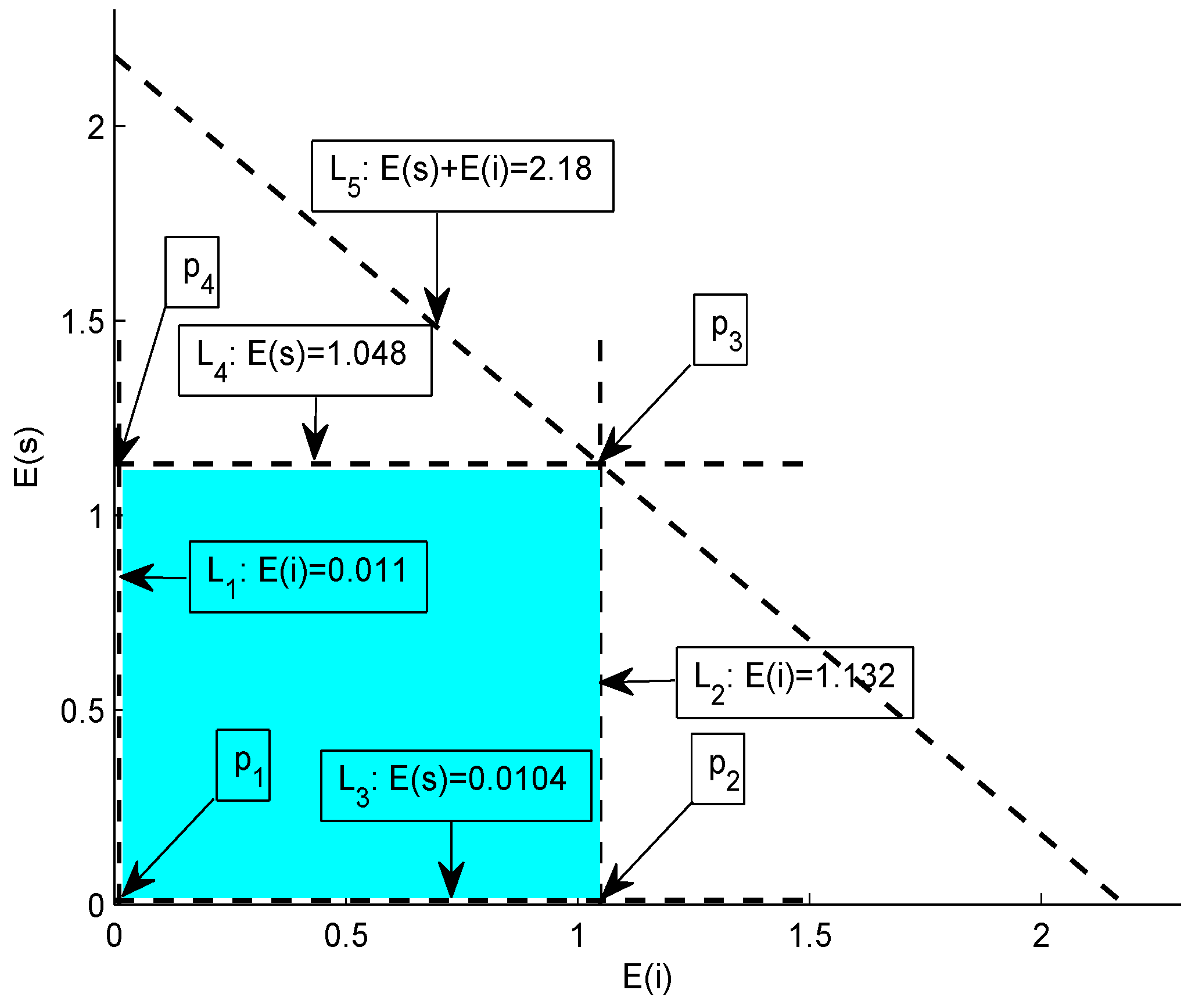
Graphical analysis: Consider a scenario in which a source node
s intends to communicate with sink via intermediate node
i such that the transmit power is
W and aggregation factor at node
i is
. Energy-consumption cost in transmission and reception is
and
, respectively. The transmit and receive power costs are for a transmission range of 100 m. If we vary the transmission range between 10–100 m, the energy-consumption costs (with units in joule) of source node and intermediate node can be modeled via the following set of equations.
Subject to the upper and lower bounds provided by Equations (24)–(26),
Figure 6 shows the intersection of five lines;
to
. These lines result in the formation of a bounded region called feasible region. This region contains the set of all possible solutions, i.e., each point that within this region represents a valid solution. Now, we test each vertex of the feasible region,
at : ,
at : ,
at : ,
and at : .
Hence, it is proved that all the valid energy-consumption costs of source and intermediate nodes for the given specifications lie within the illustrated feasible region which is colored cyan in
Figure 6.
As mentioned earlier, we aim to delay-intolerant applications. Thus, in our second objective,
minimization is formulated as follows,
where
and
Equation (
26) presents the objective function, i.e., to minimize
from source node
S to the mobile station
. Equation (
27) defines the
for the two possible cases; node(s) are involved in data routing and the intermediate node(s) are not involved in the data-forwarding. In the former case, the total
when
S communicated with
includes nodal delay at
S (i.e.,
) and
from intermediate node
j to destination
(i.e.,
). Equations (
28)–(
30) provides details about the delay contributors at
S,
j and
, respectively. Where
denotes transmission delay,
represents queuing delay,
is the re-transmission delay,
denotes reception delay and
is the data-aggregation delay. Constraint in Equation (
31a) bounds the number of nodes
between 0 and
a. If the network is dense, then relatively high number of nodes contend for channel access that leads to increased
(referred Equations (
27)–(
30)). Constraint in Equation (
31b) states that the packet sent from node
i (i.e.,
) must not exceed the packet-handling capacity
at node
j. Violation of (
31b) leads to congestion at node
j causing unbounded
. Finally, constraint in Equation (
31c) means that the arrival rate
at a given node must not exceed the departure rate
at that particular node, otherwise,
will increase if (
31b) is not violated, else
will rise.
7. Simulation Results and Analysis
This section discusses the performance analysis of our proposed protocol in comparison with Mobicast and iAMCTD. Simulation parameters are given in
Table 3. Existing MAC solutions for terrestrial WSN are not suitable for UWSN because of low propagation, high bit error rate, low bandwidth, multi-path and fading phenomena. Currently MAC solutions for UWSN are based on CSMA or CDMA protocols. However, for real implementations we assume to use UW-MAC introduced in [
33], because UW-MAC guarantees low energy consumption, high throughput and low channel access delay. UW-MAC influences CDMA properties for medium access. UM-MAC does not use a hand-shaking mechanism (RTS/CTS) therefore, reduces collision and increases channel reusability. Moreover, to further reduce the delay produced due to the back-off contention mechanism the size of the contention window (
and
) is reduced to 8 to 64 which was originally set as 32 to 1024. For simulation purposes, we assume a collision-free underwater wireless channel, therefore, interference effects in the wireless channel are ignored.
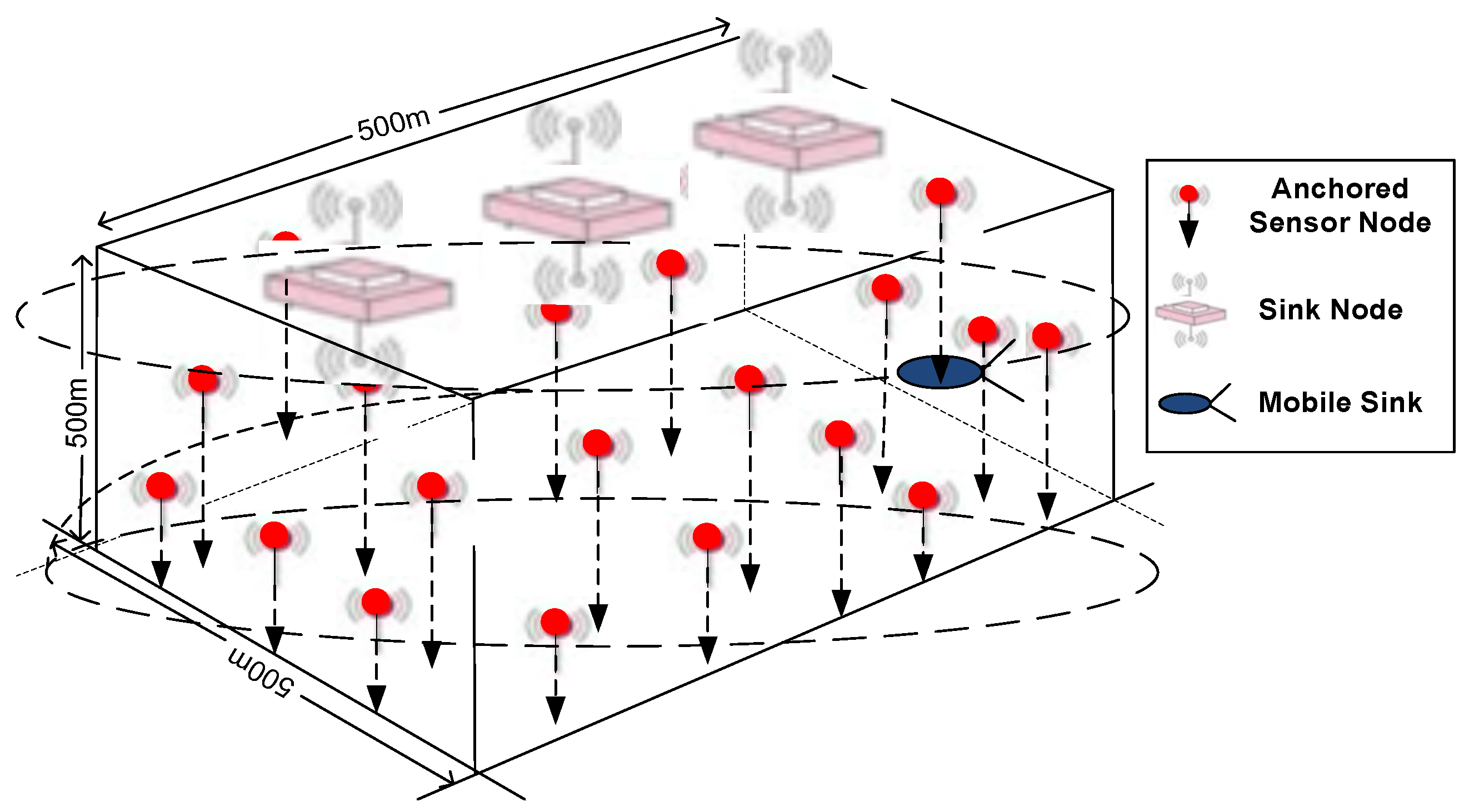
In UWSN, sensor nodes collaboratively perform an ocean column monitoring task over a 3-D target area. Therefore, in this research work, we consider the nodes are randomly deployed and are anchored with wires and floating mechanism [
34]. Sinks float on the surface of the sea having dual capability of communication with the offshore control room, mobile sink and sensor nodes. The mobile sink moves around the three-dimensional network field in elliptical spiral paths to collect data from sensor nodes and transmit it to surface sinks. An overview of the deployment strategy is shown in
Figure 7.
For simulation purposes, we used characteristics of an acoustic modem described in [
35]. According to the characteristics of the modem, it consumes 2.5 mW(milli Watt) power in stand-by mode, 5–285 mW power in listening mode, and 1.1 mW power in receive mode. For transmission mode the modem has three ranges: for 250 m range it consumes 5.5 W, for a range of 500 m modem consumes 8 W, and for 1000 m it consumes 18 W. In our simulations, we have downscaled these values for 10 m, 50 m, and 100 m ranges.
Table 3 shows the environment parameters defined for simulation and
Table 4 shows the performance metrics used for assessment of the simulation results. To simulate redundant (duplicate) data generation, we generated random data of variable lengths with 10%, 20% and 30% duplication.
7.1.
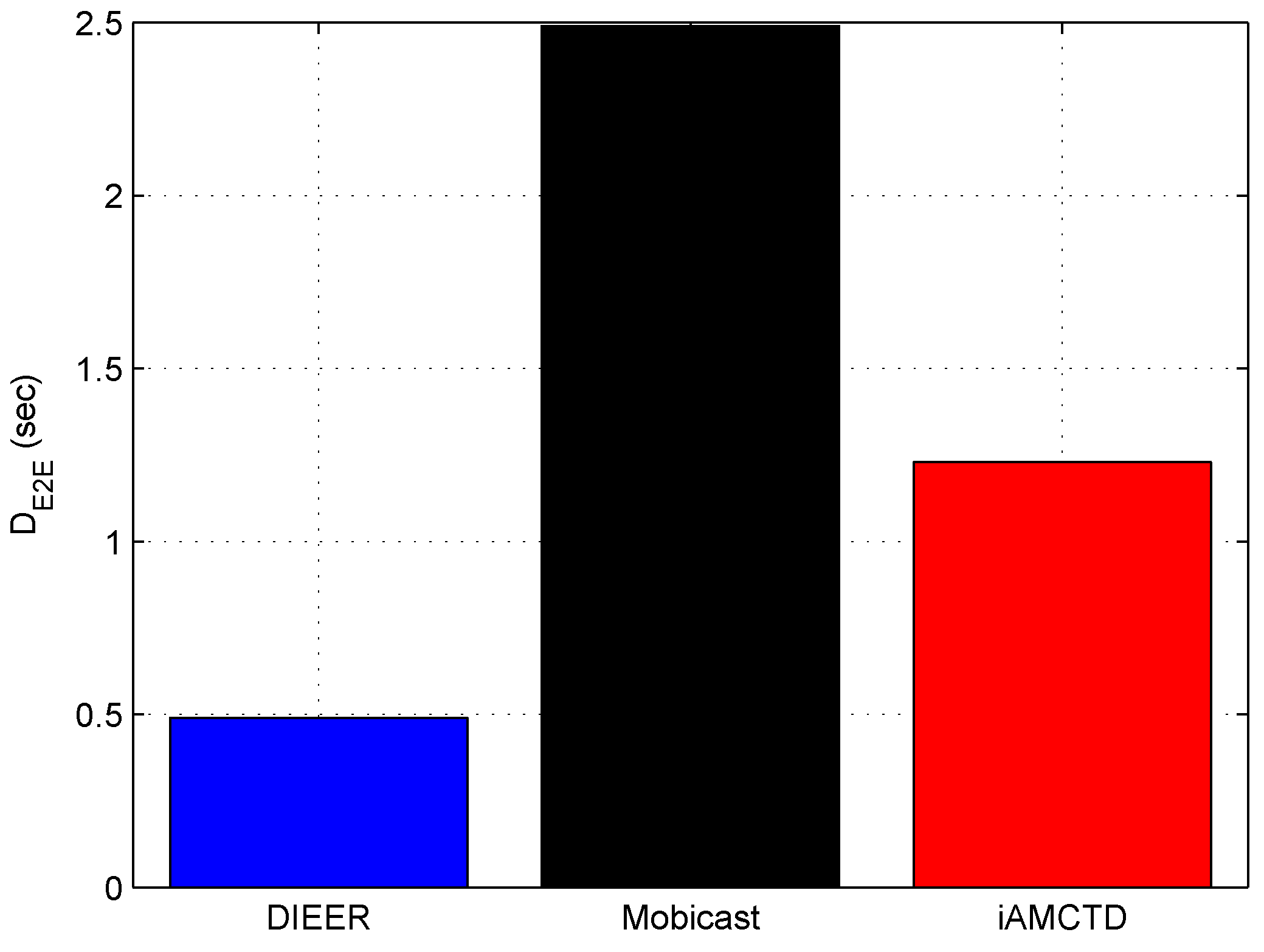
Figure 8 shows that DIEER has significantly reduced
as compared to Mobicast and iAMCTD. Among the three compared protocols, Mobicast attains the highest
. DIEER’s
is
80% reduced than Mobicast. In Mobicast, mobile sink moves on a specified path to collect data. Therefore, nodes remain in sleep mode and do not transmit data until mobile sink reaches them to collect data. Thus, a sleep–awake mechanism creates surplus
in the network. Moreover, the relatively larger travel distance and greater number of hops in Mobicast contribute in delay as well. On the other hand, iAMCTD has relatively reduced
due to courier nodes. However, the number of hops in iAMCTD are greater in number than DIEER, thereby, iAMCTD has a higher
than DIEER. To sum up, DIEER achieves the least
among the three compared protocols shown in
Figure 8 due to three reasons: (i) reduced communication distance; (ii) efficient usage of mobile sink; and (iii) reduced number of transmissions and receptions.
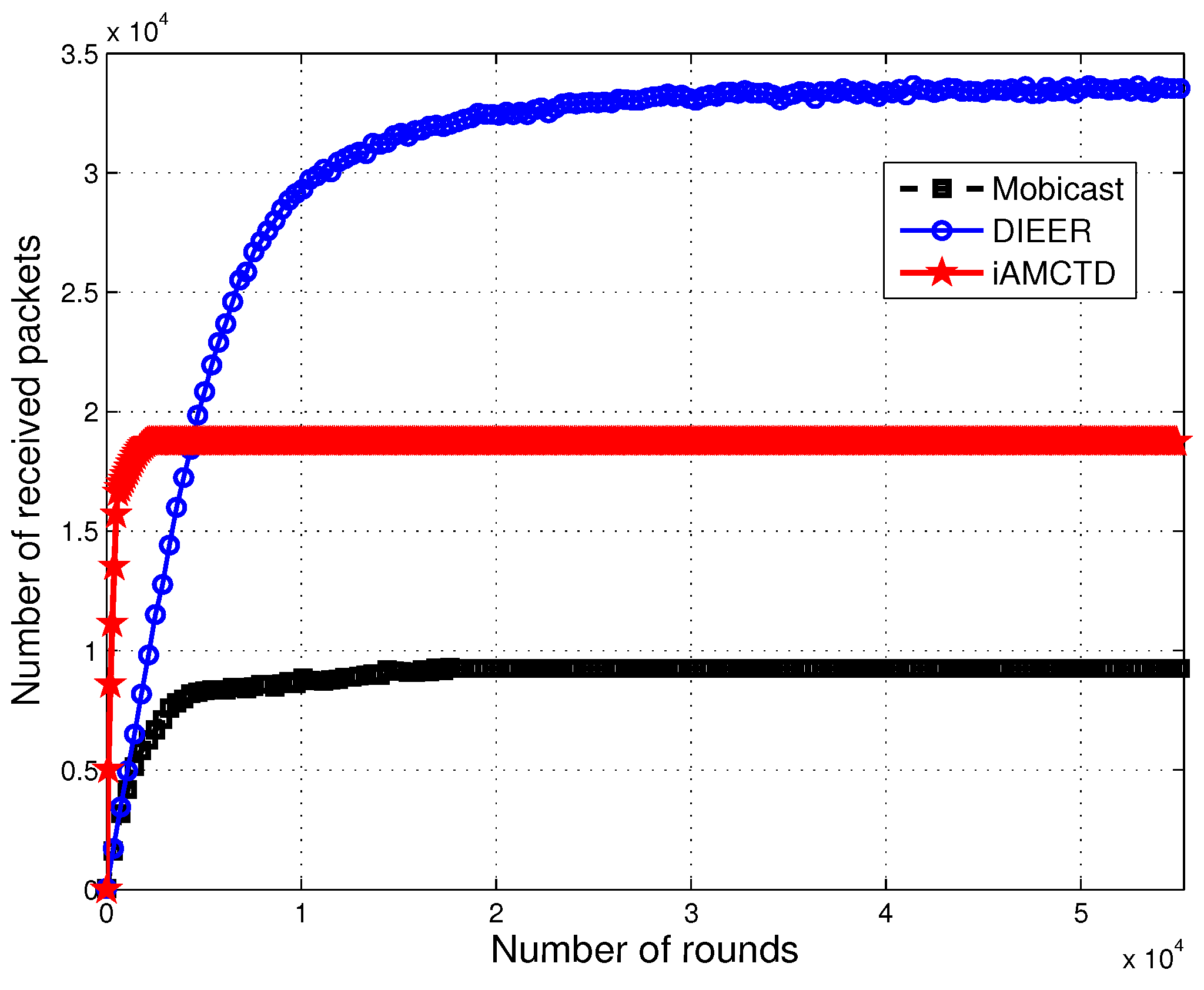
7.2. Throughput
Different techniques are proposed at physical and routing layer to maximize throughput. However, it is not always possible to successfully deliver every data packet at destination due to drastic and harsh environments of underwater. We have used the uniform random model [
36] to calculate the number of dropped packets. In DIEER, the availability of sinks has a higher probability than Mobicast. In Mobicast, mobile sink (AUV) is the only source of data forwarder to surface sink. In DIEER, mobile sink and multiple forwarder nodes (acting as sink) are the multiple sources of data-forwarding to surface sink. As there are multiple forwarder nodes, therefore, the availability of the sink has higher probability in DIEER as compared to Mobicast. DIEER adopts this design of data-forwarding to reduce the wait time of the mobile sink. However, Mobicast lags behind DIEER in this case because the mobile sink in Mobicast moves in the entire network field and collects data. So, the mobile sink at time (t) will be available in a specific zone only, while nodes of other zones are in wait state. Moreover, mobile sink of DIEER decreases the communication distance, which leads to more reliable communication. On the other hand, courier nodes of iAMCTD are advantageous in this regard as well. Thus, throughput of iAMCTD is greater than Mobicast. However, both iAMCTD and Mobicast have smaller throughput than DIEER as shown in
Figure 9.
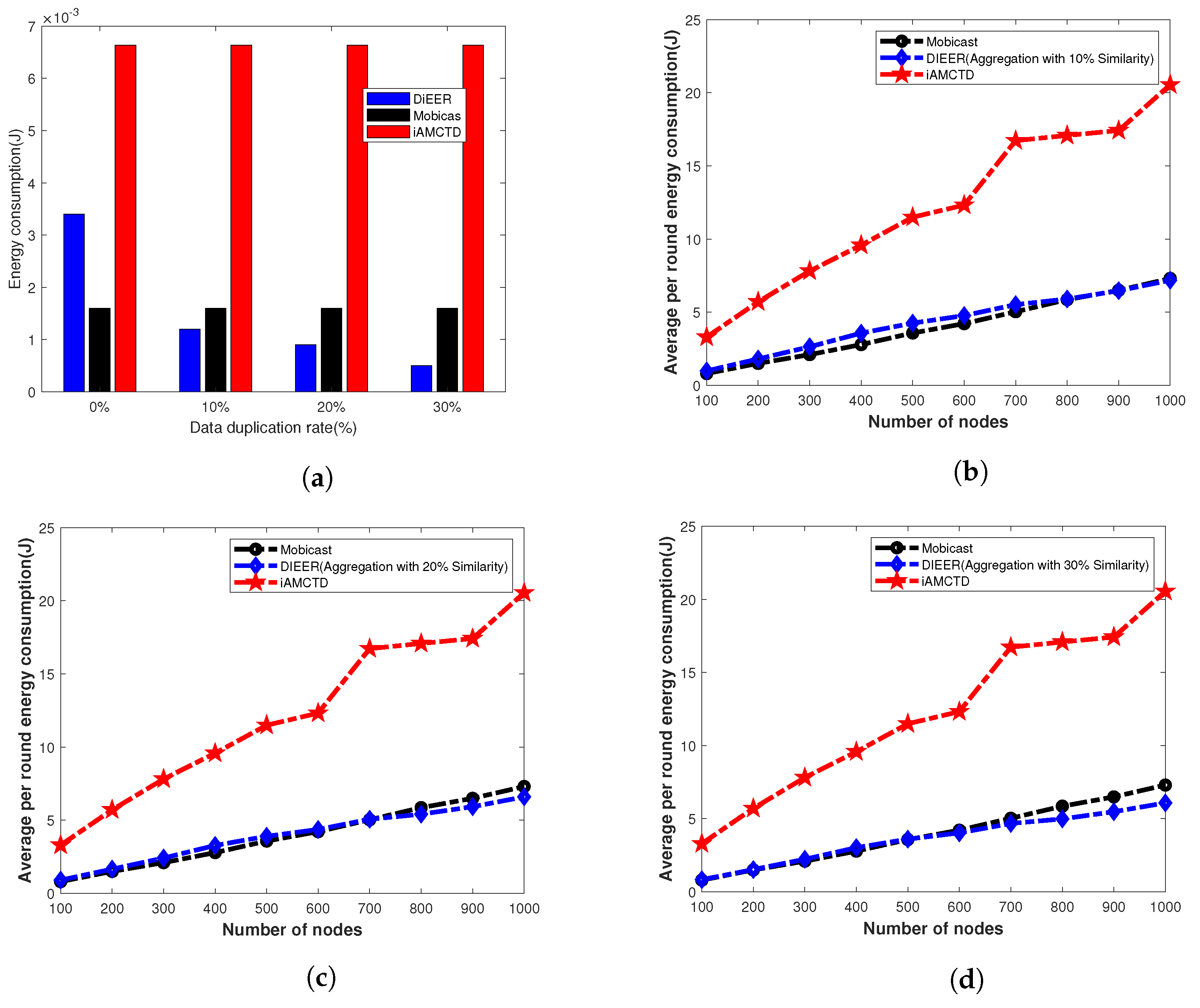
7.3. Energy Consumption
Energy consumption mainly depends upon packet size and the transmission distance between source and destination. Our protocol uses Algorithm 1 to avoid duplicate data transmission. To evaluate energy consumption of the three protocols, we run the simulations in two different scenarios. In first case, we run the simulation for fixed number of nodes and data duplication rate vary with 0%, 10%, 20% and 30% as shown in
Figure 10a. In second case, data duplication as well as number of nodes vary from 100 to 1000 as shown in
Figure 10b–d. From
Figure 10a, it is clear that energy consumption of Mobicast with 0% duplication is better than other two protocols because most of the time nodes remain in sleep mode. Nodes wake up for transmission only when AUV arrives in their transmission range. Therefore, Mobicast consumes less energy. However, as we introduce duplicate data in the simulations, the energy consumption of DIEER starts improving due to Algorithm 1, because DIEER starts suppressing duplicate data which conserves energy.
Figure 10b–d shows that energy consumption of DIEER significantly improves as the number of nodes increase.
Comparative analysis of these figures show that energy consumption of iAMCTD increases as number of nodes increase. This is because iAMCTD uses fixed for transmission and re-transmissions. Energy consumption of DIEER reduces with increase in number of nodes. Low energy cost of DIEER is because of its adoptive mechanism and suppression of duplicate data transmission. As the number of nodes increases increases, which ultimately restricts nodes to involve in re-transmission and Algorithm 1 helps to reduce packet size by just sending data pattern code for duplicate data.
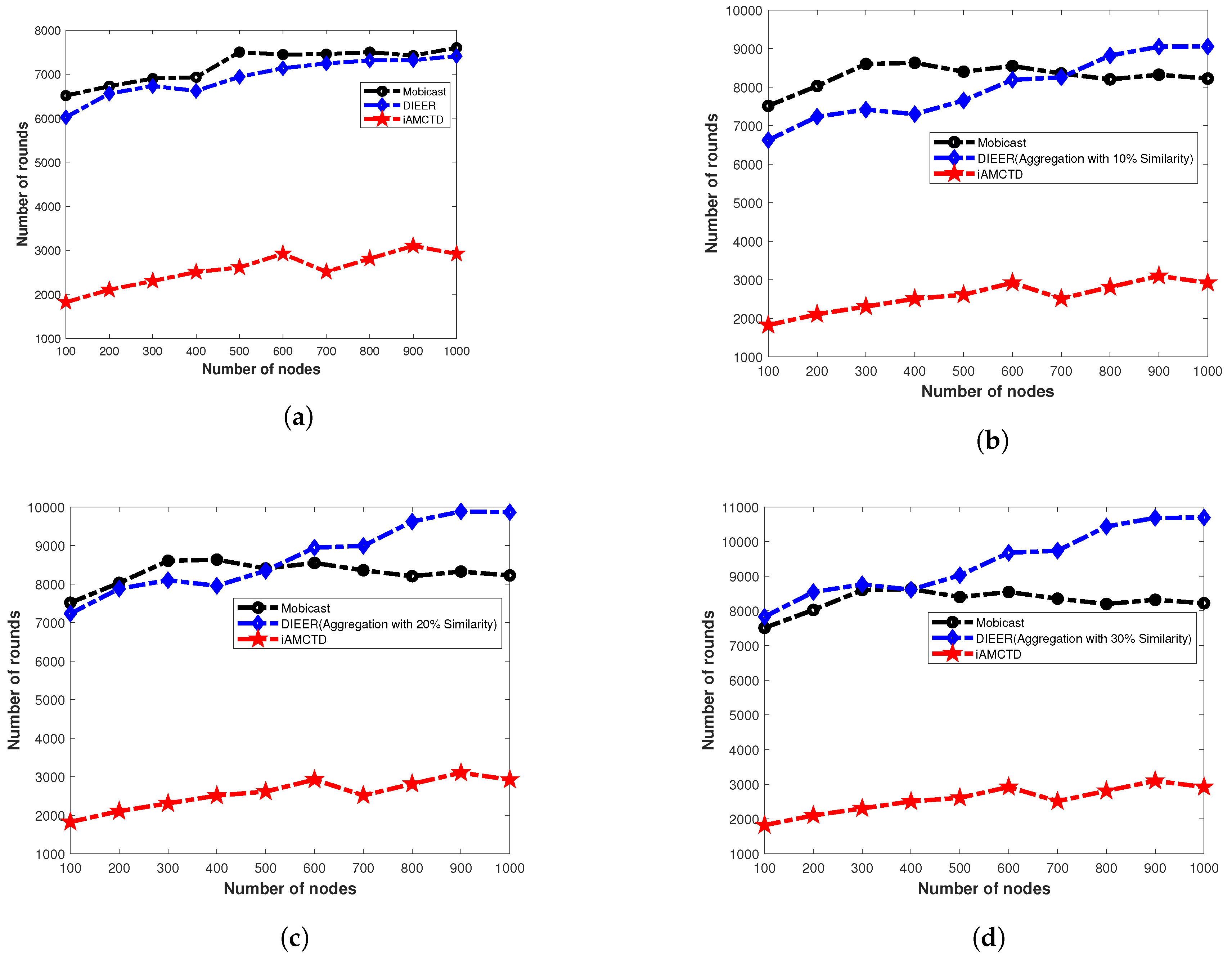
7.4. Network Lifetime
Figure 11a shows the
of three compared protocols; Mobicast, iAMCTD and DIEER with varying number of nodes and without data aggregation. In this
Figure 11a,
of Mobicast is better than DIEER and iAMCTD. However, in
Figure 11b–c as the data aggregation with pattern matching is introduced the
of DIEER improves significantly over Mobicast and iAMCTD. This is because in DIEER, nodes forward data packet by using HFM mechanism. Each receiving node holds the data packet for a certain interval of time known as HT. Calculation of HT depends on depth difference between receiving node and the transmitting node. If DD is large then HT is minimum and vice versa. HT and DD are inversely proportional to each other (
). In DIEER,
is used for the selection of forwarder nodes for re-transmission, i.e., increase/decrease of communication radius of a node. Larger radius (
) means selection of farthest node as forwarder node which reduces propagation delay (due to involvement of minimum hops) and restricts maximum nodes to involve in re-transmission additionally pattern-matching data-aggregation mechanism of DIEER reduces packet size, thus both mechanisms save overall network energy and prolong network lifetime.
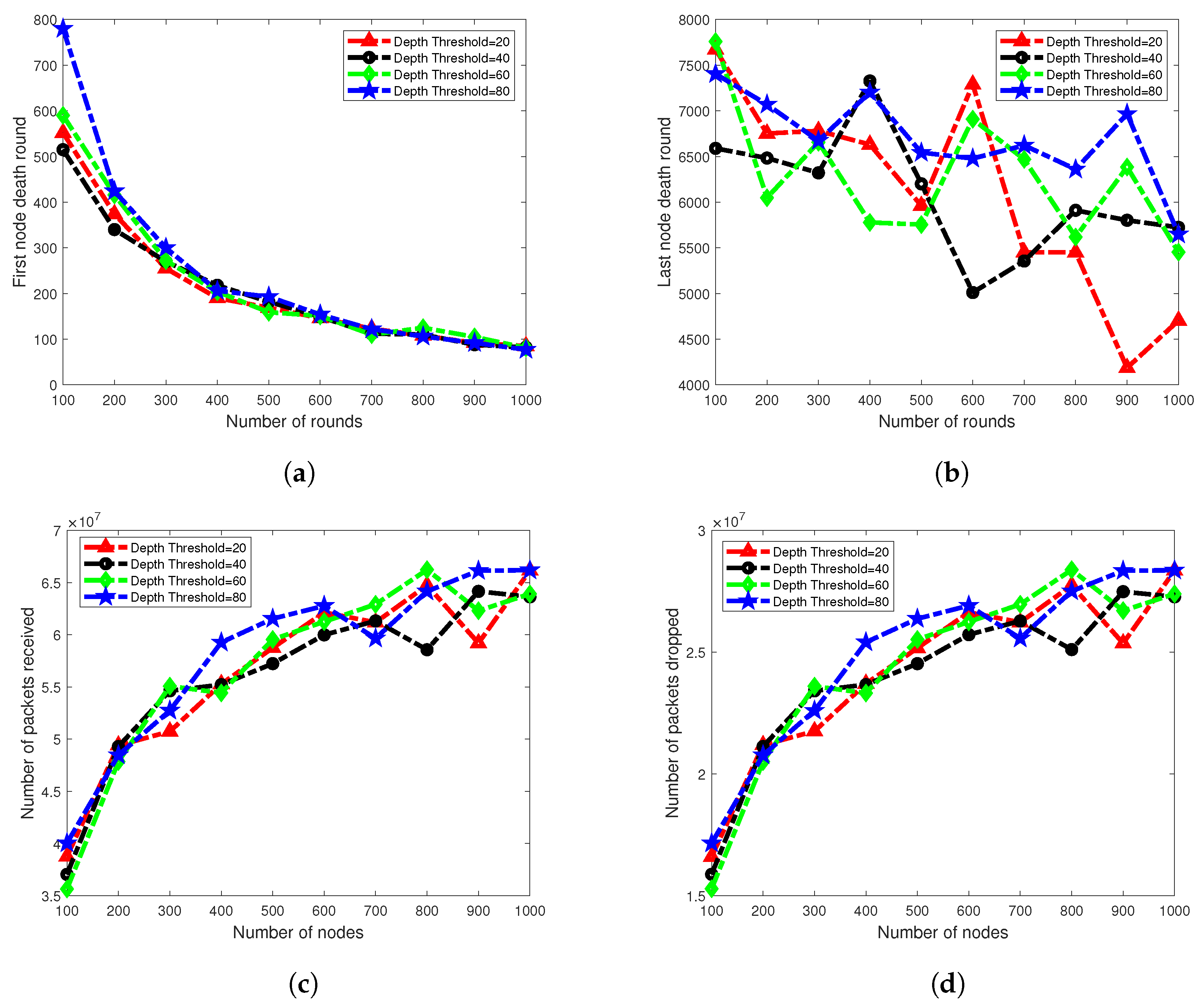
7.5. Scalability Analysis
Network scalability is an important factor for measuring the performance of the routing protocol. With the help of this metric, we can estimate the performance of a routing protocol from different perspectives for example, if number of sensor nodes in the network grows larger than how the protocol behaves in terms of throughput, delay, lifetime, etc. To measure the scalability performance of our protocol, we deploy
100 to
1000 nodes with an incremental step of
100 nodes, randomly in the network field. As in our scheme, selection of threshold radius is adaptive, therefore, to see the effect of varying threshold radius we performed simulations for
20 m,
40 m,
60 m and
80 m of radii. Rest of the simulation settings remain same as mentioned in
Table 3. In
Figure 12b, last node death round is shown against various number of nodes and
radius. Result shows that network lifetime remains stable for
. There is a little variation for
100 to
1000 nodes. However, network lifetime of
is seriously affected. It fluctuates from
6400 rounds to
4000 rounds for
100 to
1000 nodes, respectively. The main reason for reduced network lifetime is high energy consumption due to the received energy-consumption process.
Figure 12a shows the first node died time for various numbers of nodes. Result shows that the network performance decreases as the number of nodes is increased. In our scheme, the radius of the
mechanism identifies the involvement of a number of nodes in packet-forwarding. A smaller number of nodes and larger radius of threshold means a fewer number of nodes are involved in packet-forwarding, which creates fewer interference effects among nodes and less energy will be consumed in the receiving process. However, on the other hand, many nodes with small radius of
creates high energy consumption in the network, which results in rapid network instability as shown in
Figure 12b. To overcome this problem, our protocol uses ADTM.
Behavior of the graph in plots of packet received and packets dropped, shown in
Figure 12c,d, respectively, is stable. Plots of all four
types are showing an increasing trend, because a larger number of nodes are involved in the network operation; therefore, the packets received ratio is also increased. Similarly, as a greater number of packets are sent to BS, the chance of packet drops is also increased. From the scalability analysis of
and number of nodes, we conclude that our protocol is scalable to some extent for
.