Positioning Information Privacy in Intelligent Transportation Systems: An Overview and Future Perspective †
Abstract
1. Introduction
- an overview of existing privacy-related V2X solutions for infrastructure-based ITS systems;
- a modified solution for data privacy enhancement based on well-known protocol;
- a discussion of possible cybersecurity attacks on mentioned systems;
- an overview of present standardization and General Data Protection Regulation (GDPR) related activities.
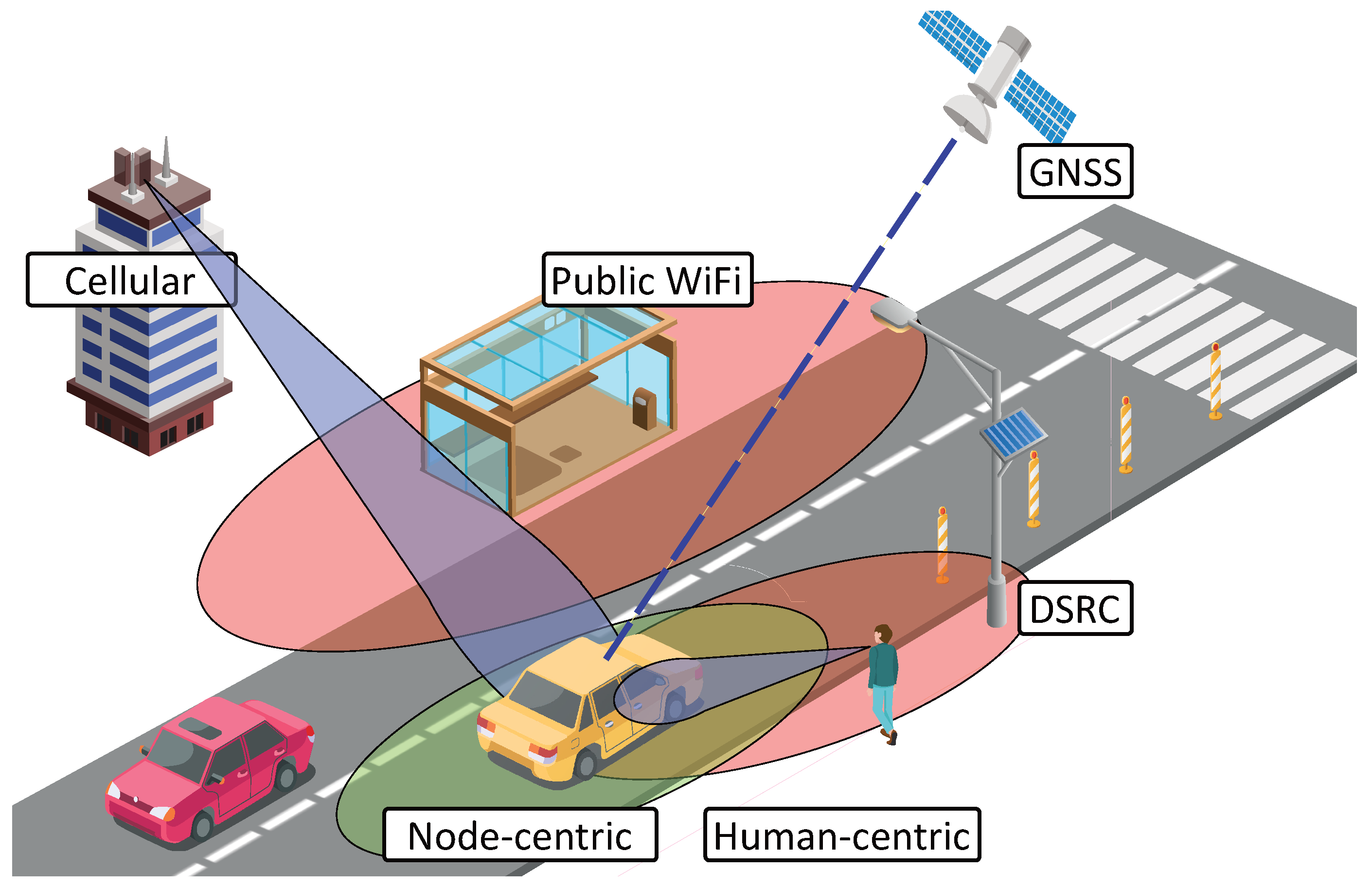
2. Solutions for Spotting of Vehicles on the Road
2.1. Global Navigation Satellite Systems
2.2. Infrastructure-Based Methods
2.3. 5G Communications as an Improvement for Positioning
2.4. Node-Centric Localization
2.5. Human-Centric Localization
2.6. Verifiable Multilateration
- Simultaneous reception: In this method, the vehicle communicates with at least three base stations in order to obtain its current coordinates. Certainly, in the real world, it is impossible to get three signals perfectly synchronized.
- Security: In the communication process, it is vital not to allow the attacker to receive the transmitted data. In [78,79] the potential cyber-attacks specific to automated vehicles are investigated. Therefore, it is necessary to provide a secure transfer of information between the station and the vehicle.
- Confidence or trustability of the access nodes: Before transmitting the information, it is required to ensure that the base station is trustworthy valid by employing mutual authentication. Some of the approaches to mutual authentication were described in [80,81]. This problem could also be addressed with conventional role-based models [82].
- Anonymity: In some situations, the base station is not supposed to obtain any information about the vehicle, neither the identification nor the location. In this paper, we show several protocols fulfilling mobile node anonymity requirement.
3. Vehicle Location Protocols Using Additional Information
- First, the ‘indirect’ distance to the static trusted nodes obtained from the known units (cellular or infrastructure units) is estimated. Mutual authentication also takes place during this phase.
- Next, the distances are utilized to estimate the location of the node through classical geometry by, for example, triangulation.
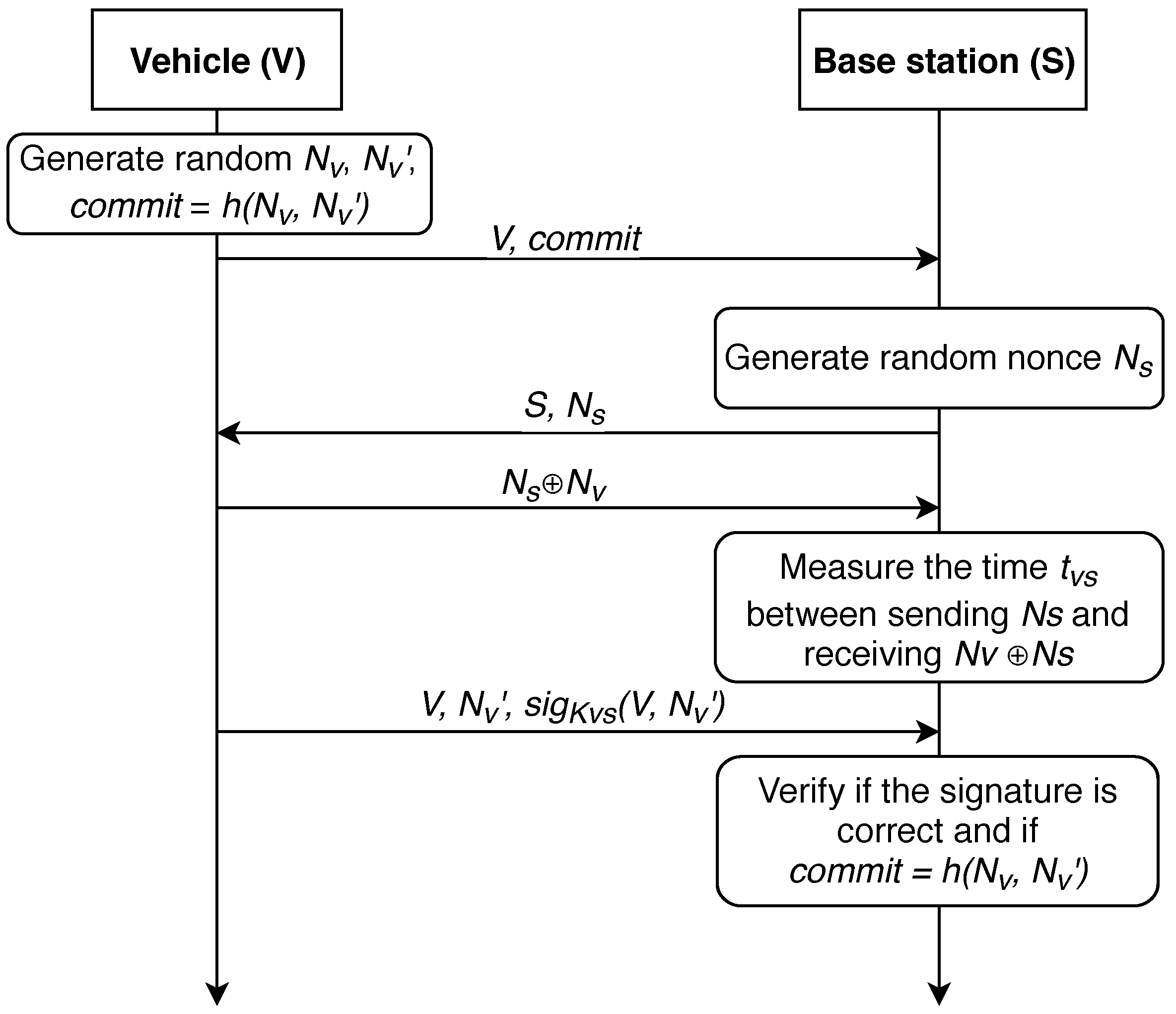
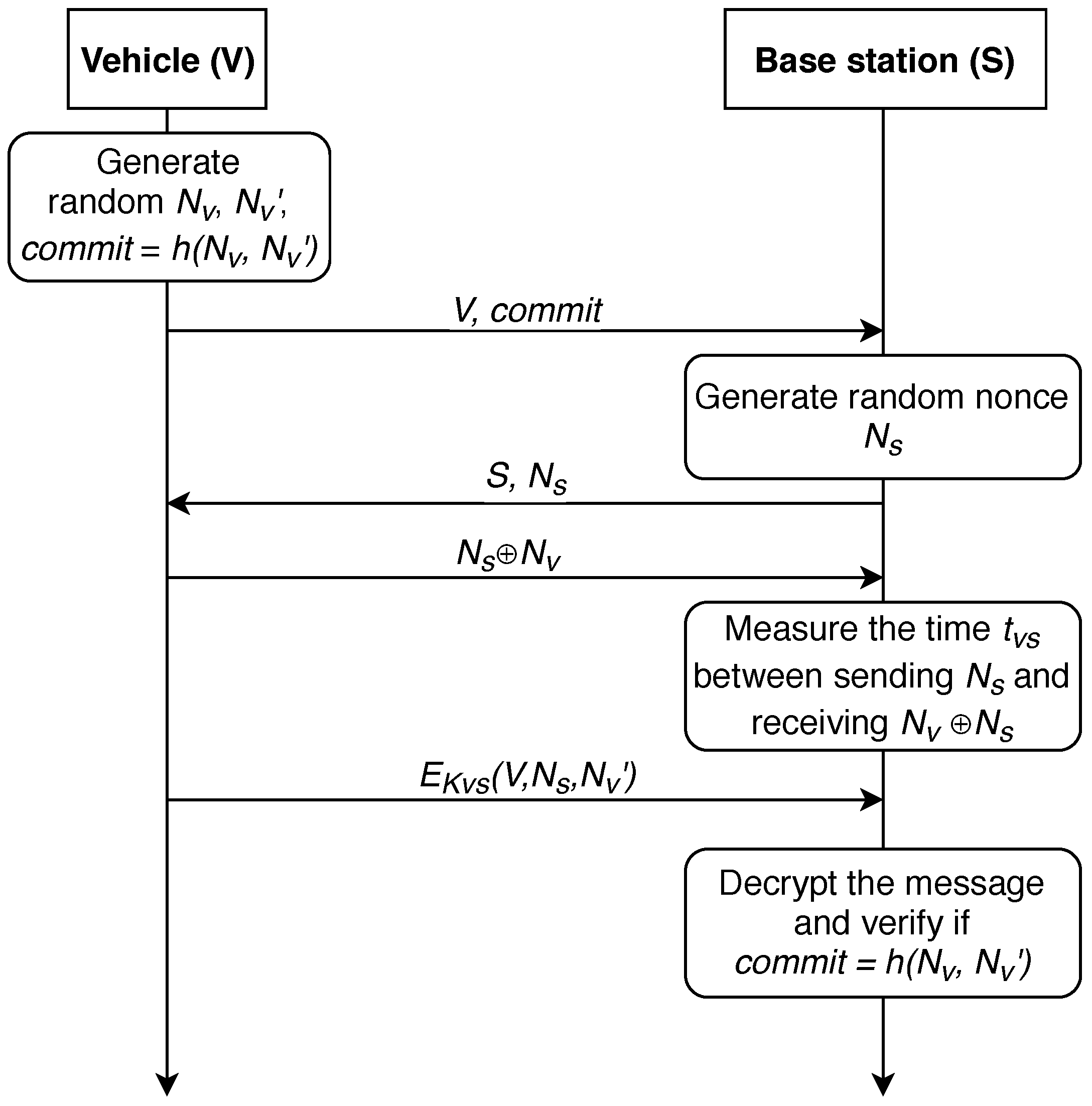
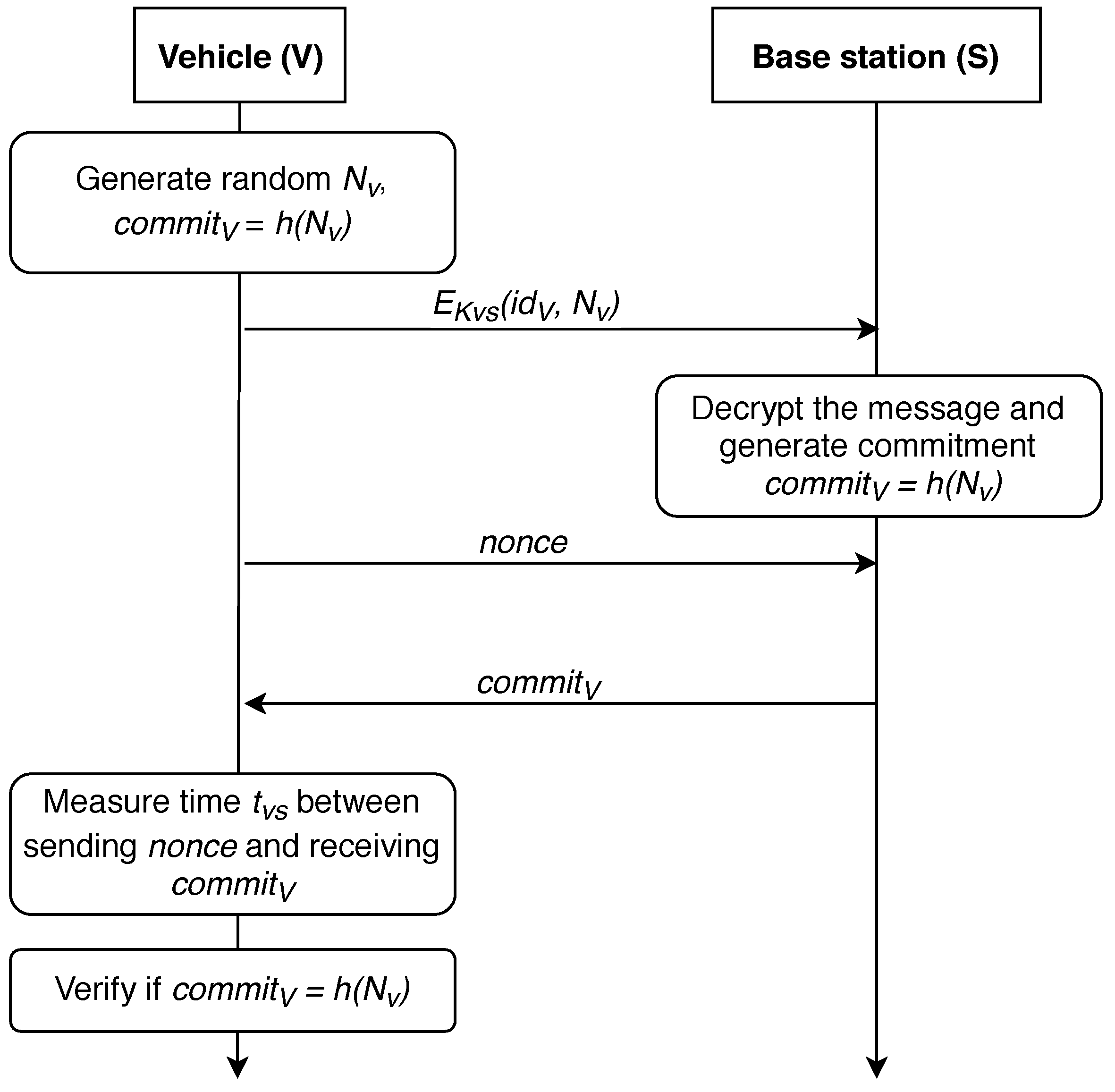
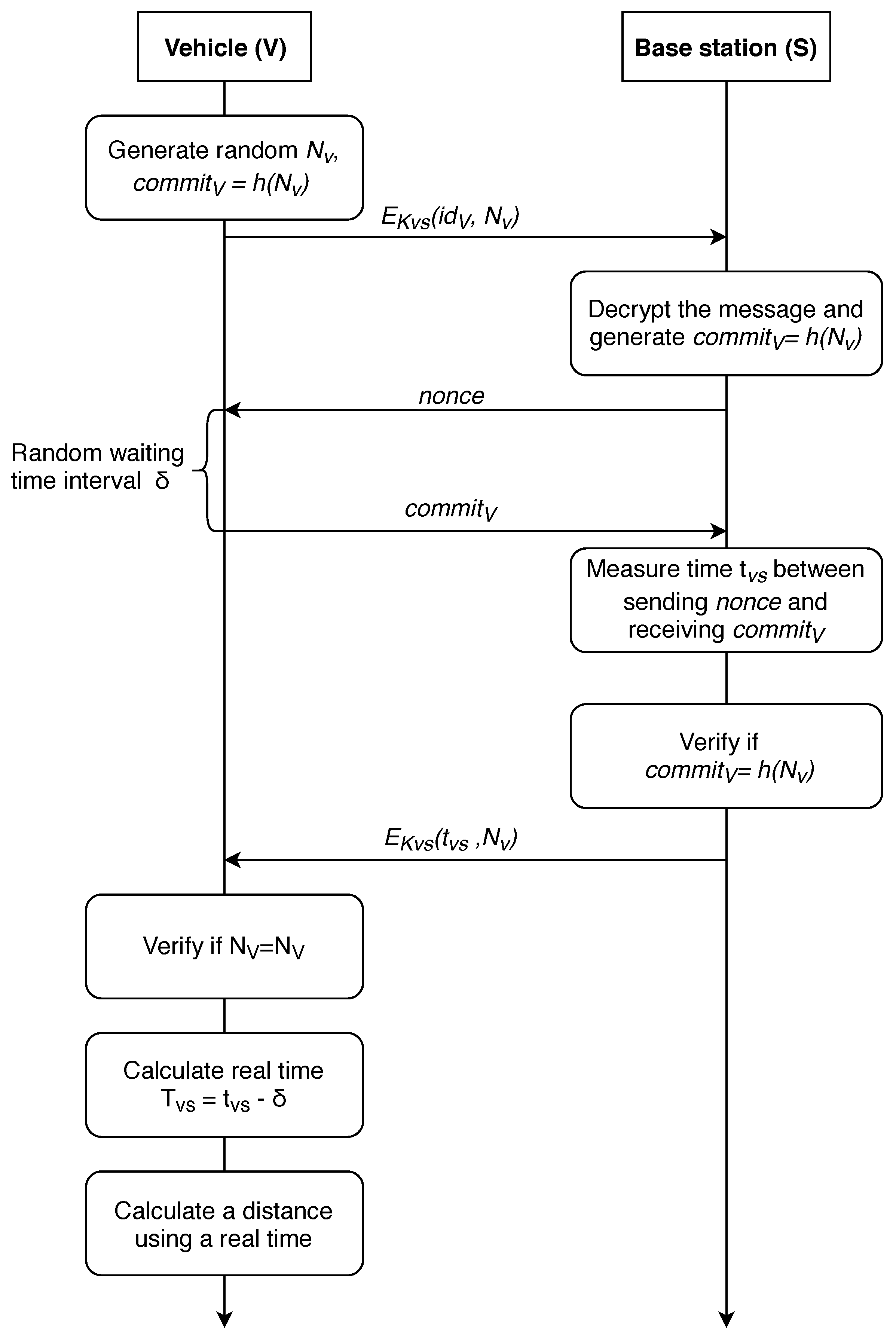
Distance Determination without Anonymity
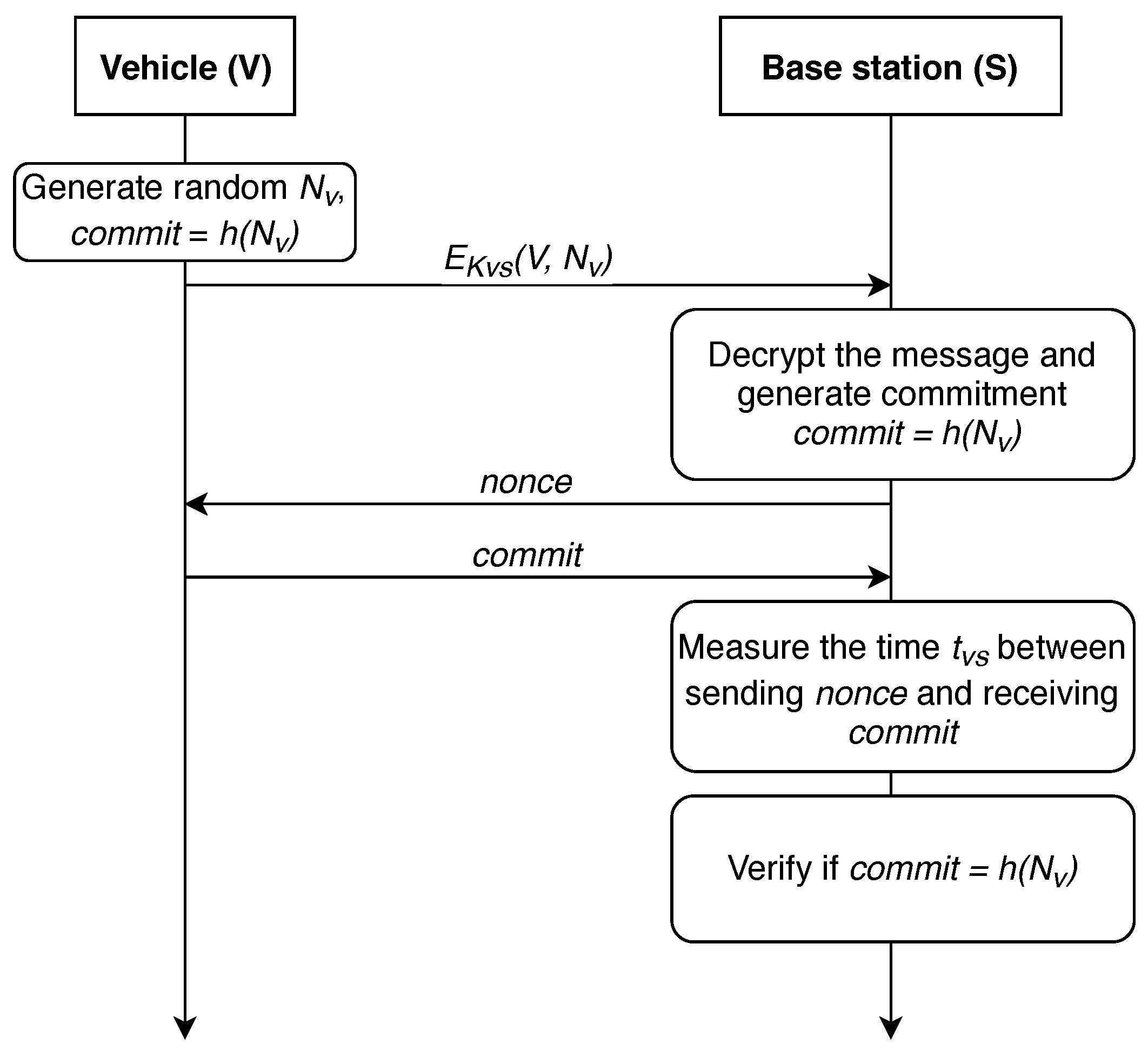
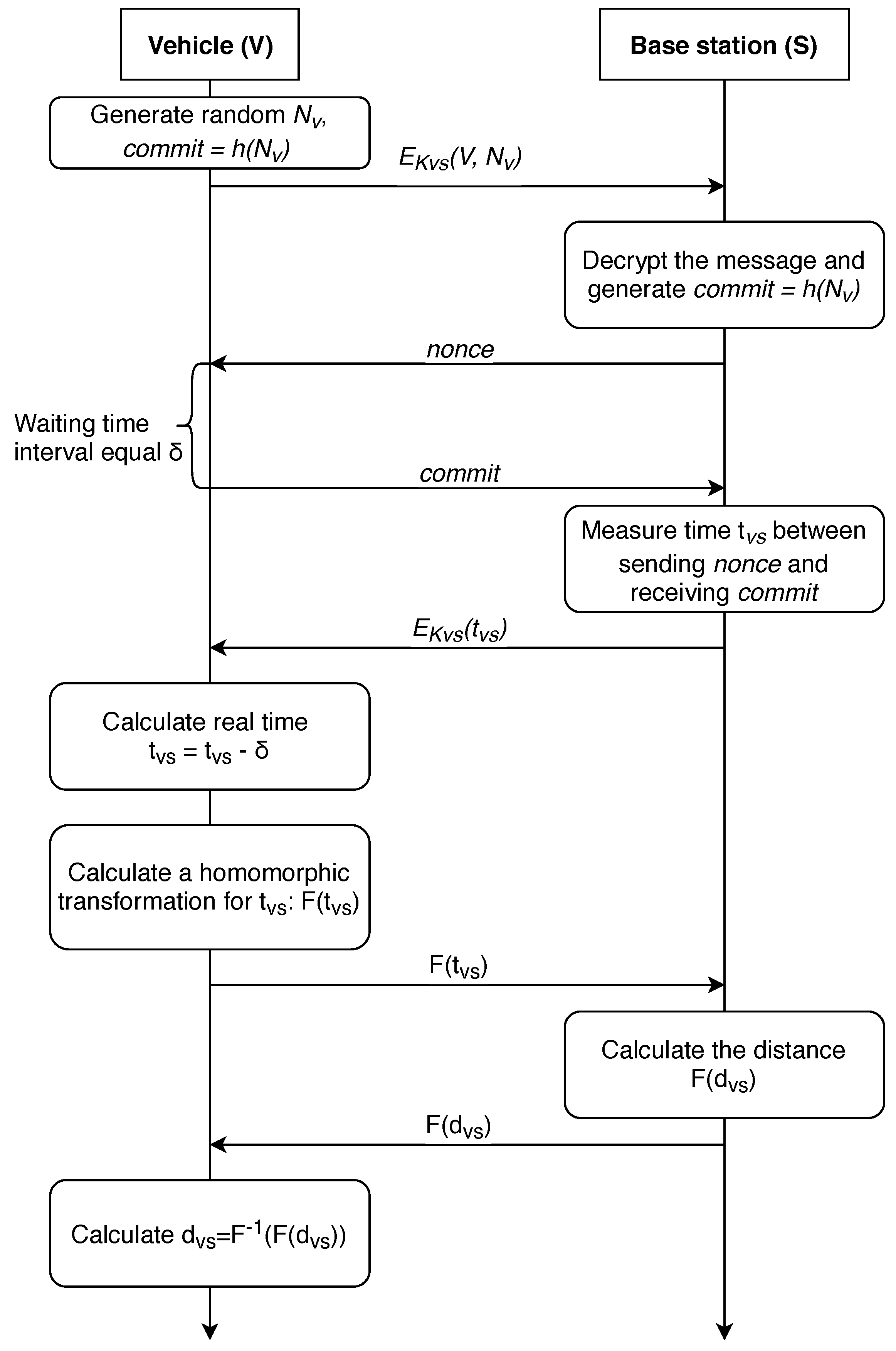
4. Location Determination with Mutual Base Station Authentication
- The distance is calculated on the side of the vehicle, all the operations are performed in a special secure computing module;
- The distance is calculated on the side of the base station, while the vehicle actions are limited to sending requests and receiving answers.
4.1. Vehicle-Centered Approach
4.2. Protocols of the Distance Determination Which Have the Property of Anonymity
5. Related Security and Privacy Threats
5.1. Security Threats
5.2. Privacy Threats
6. Discussion and Future Perspectives
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
Abbreviations
| 5G | 5th generation cellular networks |
| AOA | Angle of Arrival |
| AP | Access Point |
| BDS | BeiDou Navigation Satellite System |
| BLE | Bluetooth Low Energy |
| BSID | Base station identificator |
| CP | Cooperative positioning |
| DSRC | Dedicated Short Range Communications |
| DOS | Denial of Service Attack |
| D2D | Device-to-Device communications |
| EN | European Union |
| ETSI | European Telecommunications Institute |
| FHE | Fully homomorphic encryption |
| GNSS | Global Navigation Satellite System |
| GDPR | General Data Protection Regulation |
| GPS | Global Positioning System |
| ITS | Intelligent Transportation Systems |
| ITS-G5 | Intelligent Transport Systems operating in the 5 GHz frequency band |
| LoS | Lines of sight |
| LPWA | Low-Power Wide-Area Wireless Technology |
| LSP | Location Solution Provider |
| LIDAR | Light Detection and Ranging |
| MANET | Mobile ad hoc network |
| MEO | Medium Earth orbit |
| MITM | Man-in-the-middle attack |
| MIMO | Multiple Input Multiple Output |
| NR | New radio |
| RSS | Received signal strength |
| RSSI | Received signal strength indicator |
| TDOA | Time difference of arrival |
| TPM | Trusted Platform Module |
| TOA | Time of arrival |
| VANET | Vehicular Ad-Hoc Network |
| V2I | Vehicle-to-infrastructure paradigm |
| V2V | Vehicle-to-vehicle paradigm |
| V2X | Vehicle-to-everything paradigm |
| XOR | Exclusive OR operation |
References
- Aijaz, A.; Dohler, M.; Aghvami, A.H.; Friderikos, V.; Frodigh, M. Realizing the Tactile Internet: Haptic Communications over Next Generation 5G Cellular Networks. IEEE Wirel. Commun. 2017, 24, 82–89. [Google Scholar] [CrossRef]
- Cisco. Visual Networking Index: Global Mobile Data Traffic Forecast Update 2017–2022. 2019. Available online: https://www.cisco.com/c/en/us/solutions/collateral/service-provider/visual-networking-index-vni/white-paper-c11-738429.html (accessed on 1 April 2019).
- Menouar, H.; Guvenc, I.; Akkaya, K.; Uluagac, A.S.; Kadri, A.; Tuncer, A. UAV-enabled Intelligent Transportation Systems for the Smart City: Applications and Challenges. IEEE Commun. Mag. 2017, 55, 22–28. [Google Scholar] [CrossRef]
- Lin, D.; Kang, J.; Squicciarini, A.; Wu, Y.; Gurung, S.; Tonguz, O. MoZo: A Moving Zone Based Routing Protocol Using Pure V2V Communication in VANETs. IEEE Trans. Mob. Comput. 2017, 16, 1357–1370. [Google Scholar] [CrossRef]
- Vinel, A.; Lyamin, N.; Isachenkov, P. Modeling of V2V Communications for C-ITS Safety Applications: A CPS Perspective. IEEE Commun. Lett. 2018, 22, 1600–1603. [Google Scholar] [CrossRef]
- Zhang, F.; Xi, J.; Langari, R. Real-time Energy Management Strategy Based on Velocity Forecasts Using V2V and V2I Communications. IEEE Trans. Intell. Transp. Syst. 2017, 18, 416–430. [Google Scholar] [CrossRef]
- Dey, K.C.; Rayamajhi, A.; Chowdhury, M.; Bhavsar, P.; Martin, J. Vehicle-to-Vehicle (V2V) and Vehicle-to-Infrastructure (V2I) Communication in a Heterogeneous Wireless Network–Performance Evaluation. Transp. Res. Part C Emerg. Technol. 2016, 68, 168–184. [Google Scholar] [CrossRef]
- Lee, K.; Kim, J.; Park, Y.; Wang, H.; Hong, D. Latency of Cellular-based V2X: Perspectives on TTI-Proportional Latency and TTI-Independent Latency. IEEE Access 2017, 5, 15800–15809. [Google Scholar] [CrossRef]
- Seo, H.; Lee, K.D.; Yasukawa, S.; Peng, Y.; Sartori, P. LTE Evolution for Vehicle-to-Everything Services. IEEE Commun. Mag. 2016, 54, 22–28. [Google Scholar] [CrossRef]
- Wang, Y.; Duan, X.; Tian, D.; Chen, M.; Zhang, X. A DSRC-Based Vehicular Positioning Enhancement Using a Distributed Multiple-Model Kalman Filter. IEEE Access 2016, 4, 8338–8350. [Google Scholar] [CrossRef]
- Abboud, K.; Omar, H.A.; Zhuang, W. Interworking of DSRC and Cellular Network Technologies for V2X Communications: A Survey. IEEE Trans. Veh. Technol. 2016, 65, 9457–9470. [Google Scholar] [CrossRef]
- ETSI. Intelligent Transport Systems (ITS); Access Layer Specification for Intelligent Transport Systems Operating in the 5 GHz Frequency Band; Draft ETSI EN 302 663 V1.2.0; ETSI: Valbonne, France, 2012. [Google Scholar]
- Deinlein, T.; German, R.; Djanatliev, A. Evaluation of Single-Hop Beaconing with Congestion Control in IEEE WAVE and ETSI ITS-G5. In Proceedings of the International Conference on Measurement, Modelling and Evaluation of Computing Systems, Erlangen, Germany, 26–28 February 2018; pp. 273–282. [Google Scholar]
- FierceWireless. DSRC Mandate Moving off the Table for Automakers. 2017. Available online: https://www.fiercewireless.com/wireless/report-dsrc-mandate-moving-off-table-for-auto-makers (accessed on 1 April 2019).
- Li, J.; Cui, X.; Li, Z.; Liu, J. Method to Improve the Positioning Accuracy of Vehicular Nodes Using IEEE 802.11p Protocol. IEEE Access 2018, 6, 2834–2843. [Google Scholar] [CrossRef]
- Engadget. Most of Toyota’s Cars Will Talk to Each Other by 2025. 2017. Available online: https://www.engadget.com/2018/04/16/toyota-vehicle-to-vehicle-communications/ (accessed on 1 April 2019).
- Wang, L.; Groves, P.D.; Ziebart, M.K. Multi-Constellation GNSS Performance Evaluation for Urban Canyons Using Large Virtual Reality City Models. J. Navig. 2012, 65, 459–476. [Google Scholar] [CrossRef]
- Ometov, A.; Bezzateev, S.; Kannisto, J.; Harju, J.; Andreev, S.; Koucheryavy, Y. Facilitating the Delegation of Use for Private Devices in the Era of the Internet of Wearable Things. IEEE Internet Things J. 2017, 4, 843–854. [Google Scholar] [CrossRef]
- Bardhi, F.; Eckhardt, G.M. Access-based Consumption: The Case of Car Sharing. J. Consum. Res. 2012, 39, 881–898. [Google Scholar] [CrossRef]
- Dmitrienko, A.; Plappert, C. Secure Free-floating Car Sharing for Offline Cars. In Proceedings of the 7th ACM on Conference on Data and Application Security and Privacy, Scottsdale, AZ, USA, 22–24 March 2017; pp. 349–360. [Google Scholar]
- Cui, Y.; Ge, S.S. Autonomous Vehicle Positioning with GPS in Urban Canyon Environments. IEEE Trans. Robot. Autom. 2003, 19, 15–25. [Google Scholar]
- Wang, L.; Groves, P.D.; Ziebart, M.K. Shadow Matching: Improving Smartphone GNSS Positioning in Urban Environments. In China Satellite Navigation Conference (CSNC); Springer: Berlin/Heidelberg, Germany, 2013; pp. 613–621. [Google Scholar]
- Douglas, I.J. Improving GPS Global Navigation Accuracy for Connected Vehicles in an Urban Canyon. Ph.D. Thesis, University of Windsor, Windsor, ON, Canada, 2016. [Google Scholar]
- del Peral-Rosado, J.; Saloranta, J.; Destino, G.; López-Salcedo, J.; Seco-Granados, G. Methodology for Simulating 5G and GNSS High-Accuracy Positioning. Sensors 2018, 18, 3220. [Google Scholar] [CrossRef] [PubMed]
- Kumar, D.; Saloranta, J.; Kaleva, J.; Destino, G.; Tölli, A. Reliable Positioning and mmWave Communication via Multi-Point Connectivity. Sensors 2018, 18, 4001. [Google Scholar] [CrossRef]
- Soatti, G.; Nicoli, M.; Garcia, N.; Denis, B.; Raulefs, R.; Wymeersch, H. Implicit Cooperative Positioning in Vehicular Networks. arXiv, 2017; arXiv:1709.01282. [Google Scholar] [CrossRef]
- Han, G.; Jiang, J.; Zhang, C.; Duong, T.Q.; Guizani, M.; Karagiannidis, G.K. A Survey on Mobile Anchor Node Assisted Localization in Wireless Sensor Networks. IEEE Commun. Surv. Tutor. 2016, 18, 2220–2243. [Google Scholar] [CrossRef]
- Mahmoud, A.; Noureldin, A.; Hassanein, H.S. VANETs Positioning in Urban Environments: A Novel Cooperative Approach. In Proceedings of the 82nd Vehicular Technology Conference (VTC Fall), Boston, MA, USA, 6–9 September 2015; pp. 1–7. [Google Scholar]
- Talvitie, J.; Levanen, T.; Koivisto, M.; Pajukoski, K.; Renfors, M.; Valkama, M. Positioning of High-speed Trains Using 5G New Radio Synchronization Signals. arXiv, 2018; arXiv:1805.01830. [Google Scholar]
- Lohan, E.S.; Alén-Savikko, A.; Chen, L.; Järvinen, K.; Leppäkoski, H.; Kuusniemi, H.; Korpisaari, P. 5G Positioning: Security and Privacy Aspects. In A Comprehensive Guide to 5G Security; John Wiley & Sons Ltd.: Hoboken, NJ, USA, 2018; p. 281. [Google Scholar]
- Kalinin, M.; Krundyshev, V.; Zegzhda, P.; Belenko, V. Network Security Architectures for VANET. In Proceedings of the 10th International Conference on Security of Information and Networks, Jaipur, India, 13–15 October 2017; pp. 73–79. [Google Scholar]
- WIRED Media Group. Website Leaked Real-time Location of Most US Cell Phones to Almost Anyone. 2018. Available online: https://arstechnica.com/information-technology/2018/05/service-leaked-locations-of-us-cell-phones-for-free-no-password-required/ (accessed on 1 April 2019).
- The New York Times. Service Meant to Monitor Inmates’ Calls Could Track You, Too. 2018. Available online: https://www.nytimes.com/2018/05/10/technology/cellphone-tracking-law-enforcement.html (accessed on 1 April 2019).
- De Montjoye, Y.A.; Hidalgo, C.A.; Verleysen, M.; Blondel, V.D. Unique in the Crowd: The Privacy Bounds of Human Mobility. Sci. Rep. 2013, 3, 1376. [Google Scholar] [CrossRef] [PubMed]
- NBCUniversal Media. Your Phone May Be Tracking Your Every Move. 2017. Available online: https://www.nbclosangeles.com/news/local/Smartphone-Location-Tracking-423054644.html (accessed on 1 April 2019).
- Sui, P.; Li, X.; Bai, Y. A Study of Enhancing Privacy for Intelligent Transportation Systems: k-Correlation Privacy Model Against Moving Preference Attacks for Location Trajectory Data. IEEE Access 2017, 5, 24555–24567. [Google Scholar] [CrossRef]
- Chen, C.L.; Chiang, M.L.; Peng, C.C.; Chang, C.H.; Sui, Q.R. A Secure Mutual Authentication Scheme with Non-Repudiation for Vehicular Ad Hoc Networks. Int. J. Commun. Syst. 2017, 30, e3081. [Google Scholar] [CrossRef]
- Liu, K.; Lim, H.B.; Frazzoli, E.; Ji, H.; Lee, V.C. Improving positioning accuracy using GPS pseudorange measurements for cooperative vehicular localization. IEEE Trans. Veh. Technol. 2014, 63, 2544–2556. [Google Scholar] [CrossRef]
- Hegarty, C.J. The Global Positioning System (GPS). In Springer Handbook of Global Navigation Satellite Systems; Springer: Cham, Switzerland, 2017; pp. 197–218. [Google Scholar]
- U.S. Coast Guard Navigation Center. GPS Contallation Status. 2019. Available online: https://www.navcen.uscg.gov/?Do=constellationStatus (accessed on 1 April 2019).
- Li, X.; Ge, M.; Dai, X.; Ren, X.; Fritsche, M.; Wickert, J.; Schuh, H. Accuracy and Reliability of Multi-GNSS Real-time Precise Positioning: GPS, GLONASS, BeiDou, and Galileo. J. Geod. 2015, 89, 607–635. [Google Scholar] [CrossRef]
- Information and Analysis Center for Positioning, Navigation and Timing. GLONASS contallation Status. 2019. Available online: https://www.glonass-iac.ru/en/GLONASS/ (accessed on 1 April 2019).
- Nurmi, J.; Lohan, E.S.; Sand, S.; Hurskainen, H. GALILEO Positioning Technology; Springer: Dordrecht, The Netherlands, 2015; Volume 176. [Google Scholar]
- European GNSS Service Center. GALILEO Contallation Status. 2019. Available online: https://www.gsc-europa.eu/system-status/orbital-and-technical-parameters (accessed on 1 April 2019).
- Sun, F.; Liu, S.; Zhu, X.; Men, B. Research and Progress of Beidou Satellite Navigation System. Sci. China Inf. Sci. 2012, 55, 2899–2907. [Google Scholar] [CrossRef]
- Angrisano, A.; Gaglione, S.; Gioia, C. Performance Assessment of GPS/GLONASS Single Point Positioning in an Urban Environment. Acta Geod. Geophys. 2013, 48, 149–161. [Google Scholar] [CrossRef]
- Renfro, B.A.; Terry, A.; Boeker, N. An Analysis of Global Positioning System (GPS) Standard Positioning System (SPS) Performance for 2015; Technical Report; Space and Geophysics Laboratory, Applied Research Laboratories, The University of Texas at Austin: Austin, TX, USA, 2017. [Google Scholar]
- Specht, C.; Mania, M.; Skóra, M.; Specht, M. Accuracy of the GPS Positioning System in the Context of Increasing the Number of Satellites in the Constellation. Polish Marit. Res. 2015, 22, 9–14. [Google Scholar] [CrossRef]
- Meridian World Data, Inc. Distance Calculation. 2018. Available online: http://www.meridianworlddata.com/distance-calculation/ (accessed on 1 April 2019).
- Laitinen, E.; Lohan, E.S.; Talvitie, J.; Shrestha, S. Access Point Significance Measures in WLAN-based Location. In Proceedings of the 9th Workshop on Positioning Navigation and Communication (WPNC), Dresden, Germany, 15–16 March 2012; pp. 24–29. [Google Scholar]
- Ma, S.; Lee, H.; Cheng, H. A Positioning Accuracy Enhancement Method Based on Inter-Vehicular Communication and Self-Organizing Map. In Proceedings of the International Conference on Information and Communication Technology Convergence (ICTC), Jeju, Korea, 17–19 October 2018; pp. 748–753. [Google Scholar]
- Llorca, D.F.; Quintero, R.; Parra, I.; Sotelo, M. Recognizing Individuals in Groups in Outdoor Environments Combining Stereo Vision, RFID and BLE. Clust. Comput. 2017, 20, 769–779. [Google Scholar] [CrossRef]
- Lei, Y.; Wang, T.; Wu, J. Vehicles Relative Positioning Based on ZigBee and GPS Technology. In Proceedings of the 6th International Conference on Electronics Information and Emergency Communication (ICEIEC), Beijing, China, 17–19 June 2016; pp. 59–62. [Google Scholar]
- Sivers, M.; Fokin, G. LTE Positioning Accuracy Performance Evaluation. In Proceedings of the Conference on Smart Spaces, St. Petersburg, Russia, 26–28 August 2015; pp. 393–406. [Google Scholar]
- Koivisto, M.; Costa, M.; Hakkarainen, A.; Leppanen, K.; Valkama, M. Joint 3D Positioning and Network Synchronization in 5G Ultra-Dense Networks Using UKF and EKF. In Proceedings of the Globecom Workshops (GC Wkshps), Washington, DC, USA, 4–8 December 2016; pp. 1–7. [Google Scholar]
- Halvarsson, B.; Simonsson, A.; Elgcrona, A.; Chana, R.; Machado, P.; Asplund, H. 5G NR Testbed 3.5 GHz Coverage Results. In Proceedings of the 87th Vehicular Technology Conference (VTC Spring), Porto, Portugal, 3–6 June 2018; pp. 1–5. [Google Scholar]
- Rastorgueva-Foi, E.; Costa, M.; Koivisto, M.; Leppänen, K.; Valkama, M. User Positioning in mmW 5G Networks using Beam-RSRP Measurements and Kalman Filtering. arXiv, 2018; arXiv:1803.09478. [Google Scholar]
- Liu, Y.; Shi, X.; He, S.; Shi, Z. Prospective Positioning Architecture and Technologies in 5G Networks. IEEE Netw. 2017, 31, 115–121. [Google Scholar] [CrossRef]
- Wymeersch, H.; Seco-Granados, G.; Destino, G.; Dardari, D.; Tufvesson, F. 5G mmWave Positioning for Vehicular Networks. IEEE Wirel. Commun. 2017, 24, 80–86. [Google Scholar] [CrossRef]
- Wymeersch, H.; Garcia, N.; Kim, H.; Seco-Granados, G.; Kim, S.; Went, F.; Fröhle, M. 5G mm Wave Downlink Vehicular Positioning. In Proceedings of the Global Communications Conference (GLOBECOM), Abu Dhabi, United Arab Emirates, 9–13 December 2018; pp. 206–212. [Google Scholar]
- Kang, J.; Yu, R.; Huang, X.; Zhang, Y. Privacy-Preserved Pseudonym Scheme for Fog Computing Supported Internet of Vehicles. IEEE Trans. Intell. Transp. Syst. 2018, 19, 2627–2637. [Google Scholar] [CrossRef]
- Parker, R.; Valaee, S. Vehicle Localization in Vehicular Networks. In Proceedings of the 64th Vehicular Technology Conference (VTC), Montreal, QC, Canada, 25–28 September 2006; pp. 1–5. [Google Scholar]
- Capkun, S.; Hubaux, J.P. Secure Positioning of Wireless Devices with Application to Sensor Networks. In Proceedings of the 24th Annual Joint Conference of the IEEE Computer and Communications Societies, Miami, FL, USA, 13–17 March 2005; Volume 3, pp. 1917–1928. [Google Scholar]
- Johnson, D.B.; Maltz, D.A. Dynamic Source Routing in Ad Hoc Wireless Networks. In Mobile Computing; Springer: Boston, MA, USA, 1996; pp. 153–181. [Google Scholar]
- Kato, S.; Tsugawa, S.; Tokuda, K.; Matsui, T.; Fujii, H. Vehicle Control Algorithms for Cooperative Driving with Automated Vehicles and Intervehicle Communications. IEEE Trans. Intell. Transp. Syst. 2002, 3, 155–161. [Google Scholar] [CrossRef]
- Clark, S.; Durrant-Whyte, H. Autonomous Land Vehicle Navigation Using Millimeter Wave Radar. In Proceedings of the International Conference on Robotics and Automation, Leuven, Belgium, 16–20 May 1998; Volume 4, pp. 3697–3702. [Google Scholar]
- Yoneda, K.; Hashimoto, N.; Yanase, R.; Aldibaja, M.; Suganuma, N. Vehicle Localization Using 76GHz Omnidirectional Millimeter-Wave Radar for Winter Automated Driving. In Proceedings of the Intelligent Vehicles Symposium (IV), Changshu, China, 26–30 June 2018; pp. 971–977. [Google Scholar]
- Sánchez-Carmona, A.; Robles, S.; Borrego, C. PrivHab+: A Secure Geographic Routing Protocol for DTN. Comput. Commun. 2016, 78, 56–73. [Google Scholar] [CrossRef]
- Bou Abdo, J.; Bourgeau, T.; Demerjian, J.; Chaouchi, H. Extended Privacy in Crowdsourced Location-based Services Using Mobile Cloud Computing. Mob. Inf. Syst. 2016, 2016, 7867206. [Google Scholar] [CrossRef]
- Ometov, A.; Petrov, V.; Bezzateev, S.; Andreev, S.; Koucheryavy, Y.; Gerla, M. Challenges of Multi-Factor Authentication for Securing Advanced IoT (A-IoT) Applications. arXiv, 2019; arXiv:1901.06977. [Google Scholar] [CrossRef]
- Cui, X.; Gulliver, T.A.; Song, H.; Li, J. Real-time Positioning Based on Millimeter Wave Device to Device Communications. IEEE Access 2016, 4, 5520–5530. [Google Scholar] [CrossRef]
- Lin, X.; Andrews, J.G.; Ghosh, A.; Ratasuk, R. An Overview of 3GPP Device-to-Device Proximity Services. IEEE Commun. Mag. 2014, 52, 40–48. [Google Scholar] [CrossRef]
- Riener, A.; Ferscha, A. Supporting Implicit Human-to-Vehicle Interaction: Driver Identification from Sitting Postures. In Proceedings of the 1st Annual International Symposium on Vehicular Computing Systems (ISVCS), Dublin, Ireland, 22–24 July 2008; p. 10. [Google Scholar]
- Lu, Z.; de Winter, J.C. A Review and Framework of Control Authority Transitions in Automated Driving. Procedia Manuf. 2015, 3, 2510–2517. [Google Scholar] [CrossRef]
- Dunbar, J.; Gilbert, J.E. The Human Element in Autonomous Vehicles. In Proceedings of the International Conference on Engineering Psychology and Cognitive Ergonomics, Vancouver, BC, Canada, 9–14 July 2017; pp. 339–362. [Google Scholar]
- Campos, R.S. Evolution of Positioning Techniques in Cellular Networks, from 2G to 4G. Wirel. Commun. Mob. Comput. 2017, 2017, 2315036. [Google Scholar] [CrossRef]
- Esteves, J.S.; Carvalho, A.; Couto, C. Generalized Geometric Triangulation Algorithm for Mobile Robot Absolute Self-localization. In Proceedings of the IEEE International Symposium on Industrial Electronics, Rio de Janeiro, Brazil, 9–11 June 2003; Volume 1, pp. 346–351. [Google Scholar]
- Larson, U.E.; Nilsson, D.K. Securing Vehicles Against Cyber Attacks. In Proceedings of the 4th Annual Workshop on Cyber Security and Information Intelligence Research: Developing Strategies to Meet the Cyber Security and Information Intelligence Challenges Ahead, Oak Ridge, TN, USA, 12–14 May 2008; p. 30. [Google Scholar]
- Petit, J.; Shladover, S.E. Potential Cyberattacks on Automated Vehicles. IEEE Trans. Intell. Transp. Syst. 2015, 16, 546–556. [Google Scholar] [CrossRef]
- Dolev, S.; Krzywiecki, Ł; Panwar, N.; Segal, M. Vehicle Authentication via Monolithically Certified Public Key and Attributes. Wirel. Netw. 2016, 22, 879–896. [Google Scholar] [CrossRef]
- Zhang, C.; Lin, X.; Lu, R.; Ho, P.H. RAISE: An Efficient RSU-aided Message Authentication Scheme in Vehicular Communication Networks. In Proceedings of the International Conference on Communications, Beijing, China, 19–23 May 2008; pp. 1451–1457. [Google Scholar]
- Kalinin, M.; Krundyshev, V.; Rezedinova, E.; Zegzhda, P. Role-based Access Control for Vehicular adhoc Networks. In Proceedings of the International Black Sea Conference on Communications and Networking (BlackSeaCom), Batumi, Georgia, 4–7 June 2018; pp. 1–5. [Google Scholar]
- del Peral-Rosado, J.A.; Raulefs, R.; López-Salcedo, J.A.; Seco-Granados, G. Survey of Cellular Mobile Radio Localization Methods: From 1G to 5G. IEEE Commun. Surv. Tutor. 2018, 20, 1124–1148. [Google Scholar] [CrossRef]
- Qian, C.; Xu, H.; Li, P.; Wang, Y. Design and Implementation of Urban Vehicle Positioning System Based on RFID, GPS and LBS. In Proceedings of the Conference on Complex, Intelligent, and Software Intensive Systems, Turin, Italy, 10–13 July 2017; pp. 599–608. [Google Scholar]
- Rohani, M.; Gingras, D.; Gruyer, D. A Novel Approach for Improved Vehicular Positioning Using Cooperative Map Matching and Dynamic Base Station DGPS Concept. IEEE Trans. Intell. Transp. Syst. 2016, 17, 230–239. [Google Scholar] [CrossRef]
- Hubaux, J.P.; Capkun, S.; Luo, J. The Security and Privacy of Smart Vehicles. IEEE Secur. Priv. 2004, 2, 49–55. [Google Scholar] [CrossRef]
- Davydov, V.; Bezzateev, S. Secure Information Exchange in Defining the Location of the Vehicle. In Proceedings of the 41st International Conference on Telecommunications and Signal Processing (TSP), Athens, Greece, 4–6 July 2018; pp. 1–5. [Google Scholar]
- Brakerski, Z.; Vaikuntanathan, V. Efficient Fully Homomorphic Encryption from (Standard) LWE. SIAM J. Comput. 2014, 43, 831–871. [Google Scholar] [CrossRef]
- Rohilla, A.; Khurana, M.; Singh, L. Location Privacy using Homomorphic Encryption over Cloud. Int. J. Comput. Netw. Inf. Secur. 2017, 9, 32. [Google Scholar] [CrossRef]
- Alanwar, A.; Shoukry, Y.; Chakraborty, S.; Martin, P.; Tabuada, P.; Srivastava, M. PrOLoc: Resilient Localization with Private Observers Using Partial Homomorphic Encryption. In Proceedings of the 16th ACM/IEEE International Conference on Information Processing in Sensor Networks (IPSN), Pittsburgh, PA, USA, 18–21 April 2017; pp. 41–52. [Google Scholar]
- Rachmawati, D.; Tarigan, J.; Ginting, A. A Comparative Study of Message Digest 5 (MD5) and SHA256 Algorithm. J. Phys. Conf. Ser. 2018, 978, 012116. [Google Scholar] [CrossRef]
- Guerzhoy, M. Complexity of Aarithmetic Operations. 2018. Available online: https://www.cs.toronto.edu/~guerzhoy/180/lectures/W11/lec1/ComplArithm.html (accessed on 1 April 2019).
- Montanaro, A.; Osborne, T. On the Communication Complexity of XOR Functions. arXiv, 2009; arXiv:0909.3392. [Google Scholar]
- Armknecht, F.; Boyd, C.; Carr, C.; Gjøsteen, K.; Jäschke, A.; Reuter, C.A.; Strand, M. A Guide to Fully Homomorphic Encryption. IACR Cryptol. ePrint Arch. 2015, 2015, 1192. [Google Scholar]
- Ta, V.T.; Dvir, A.; Arie, Y. Securing Road Traffic Congestion Detection by Incorporating V2I Communications. In Proceedings of the 19th International Symposium on A World of Wireless, Mobile and Multimedia Networks (WoWMoM), Chania, Greece, 12–15 June 2018; pp. 1–6. [Google Scholar]
- Al-Kahtani, M.S. Survey on Security Attacks in Vehicular Ad hoc Networks (VANETs). In Proceedings of the 6th International Conference on Signal Processing and Communication Systems (ICSPCS), Gold Coast, QLD, Australia, 12–14 December 2012; pp. 1–9. [Google Scholar]
- Capkun, S.; Hubaux, J.P. Secure Positioning in Wireless Networks. IEEE J. Sel. Areas Commun. 2006, 24, 221–232. [Google Scholar] [CrossRef]
- Yu, B.; Xu, C.Z.; Xiao, B. Detecting Sybil Attacks in VANETs. J. Parallel Distrib. Comput. 2013, 73, 746–756. [Google Scholar] [CrossRef]
- Li, X.; Li, Z.; Han, J.; Lee, J.G. Temporal Outlier Detection in Vehicle Traffic Data. In Proceedings of the 25th International Conference on Data Engineering, Shanghai, China, 29 March–2 April 2009; pp. 1319–1322. [Google Scholar]
- Mokhtar, B.; Azab, M. Survey on Security Issues in Vehicular Ad Hoc Networks. Alex. Eng. J. 2015, 54, 1115–1126. [Google Scholar] [CrossRef]
- Mahajan, S.; Jindal, A. Security and Privacy in VANET to Reduce Authentication Overhead for Rapid Roaming Networks. Int. J. Comput. Appl. 2010, 1, 21–25. [Google Scholar] [CrossRef]
- Lin, X.; Sun, X.; Ho, P.H.; Shen, X. GSIS: A Secure and Privacy-Preserving Protocol for Vehicular Communications. IEEE Trans. Veh. Technol. 2007, 56, 3442–3456. [Google Scholar]
- Zeadally, S.; Hunt, R.; Chen, Y.S.; Irwin, A.; Hassan, A. Vehicular Ad Hoc Networks (VANETS): Status, Results, and Challenges. Telecommun. Syst. 2012, 50, 217–241. [Google Scholar] [CrossRef]
- Garip, M.T.; Gursoy, M.E.; Reiher, P.; Gerla, M. Congestion Attacks to Autonomous Cars Using Vehicular Botnets. In Proceedings of the NDSS Workshop on Security of Emerging Networking Technologies (SENT), San Diego, CA, USA, 8 February 2015. [Google Scholar]
- Smitha, A.; Pai, M.M.; Ajam, N.; Mouzna, J. An Optimized Adaptive Algorithm for Authentication of Safety Critical Messages in VANET. In Proceedings of the 8th International Conference on Communications and Networking in China (CHINACOM), Guilin, China, 14–16 August 2013; pp. 149–154. [Google Scholar]
- Alsharif, N.; Wasef, A.; Shen, X. Mitigating the Effects of Position-based Routing Attacks in Vehicular Ad Hoc Networks. In Proceedings of the International Conference on Communications (ICC), Kyoto, Japan, 5–9 June 2011; pp. 1–5. [Google Scholar]
- Erritali, M.; El Ouahidi, B. A Review and Classification of Various VANET Intrusion Detection Systems. In Proceedings of the National Security Days (JNS3), Rabat, Morocco, 26–27 April 2013; pp. 1–6. [Google Scholar]
- Sirola, P.; Joshi, A.; Purohit, K.C. An Analytical Study of Routing Attacks in Vehicular Ad-Hoc Networks (VANETs). Int. J. Comput. Sci. Eng. 2014, 3, 210–218. [Google Scholar]
- Hasrouny, H.; Samhat, A.E.; Bassil, C.; Laouiti, A. VANET Security Challenges and Solutions: A Survey. Veh. Commun. 2017, 7, 7–20. [Google Scholar] [CrossRef]
- Simic, M.N. Vehicular Ad Hoc Networks. In Proceedings of the 11th International Conference on Telecommunication in Modern Satellite, Cable and Broadcasting Services (TELSIKS), Nis, Serbia, 16–19 October 2013; Volume 2, pp. 613–618. [Google Scholar]
- Bloessl, B.; Sommer, C.; Dressier, F.; Eckhoff, D. The Scrambler Attack: A Robust Physical Layer Attack on Location Privacy in Vehicular Networks. In Proceedings of the International Conference on Computing, Networking and Communications (ICNC), Garden Grove, CA, USA, 16–19 February 2015; pp. 395–400. [Google Scholar]
- Gedik, B.; Liu, L. Protecting Location Privacy with Personalized k-anonymity: Architecture and Algorithms. IEEE Trans. Mob. Comput. 2008, 7, 1–18. [Google Scholar] [CrossRef]
- Artail, H.; Abbani, N. A Pseudonym Management System to Achieve Anonymity in Vehicular Ad Hoc Networks. IEEE Trans. Dependable Secure Comput. 2016, 13, 106–119. [Google Scholar] [CrossRef]
- Gerlach, M.; Guttler, F. Privacy in VANETs Using Changing Pseudonyms-Ideal and Real. In Proceedings of the 65th Vehicular Technology Conference, Dublin, Ireland, 22–25 April 2007; pp. 2521–2525. [Google Scholar]
- Kalinin, M.; Zegzhda, P.; Zegzhda, D.; Vasiliev, Y.; Belenko, V. Software Defined Security for Vehicular ad hoc Networks. In Proceedings of the International Conference on Information and Communication Technology Convergence (ICTC), Jeju, Korea, 19–21 Octber 2016; pp. 533–537. [Google Scholar]
- Di Maio, A.; Palattella, M.; Soua, R.; Lamorte, L.; Vilajosana, X.; Alonso-Zarate, J.; Engel, T. Enabling SDN in VANETs: What is the Impact on Security? Sensors 2016, 16, 2077. [Google Scholar] [CrossRef] [PubMed]
- European Parliament and Council of the European Union. General Data Protection Regulation (EU) 2016/679 (“GDPR”); EU Regulation; European Parliament and Council of the European Union: Brussels, Belgium, 2018. [Google Scholar]
- ETSI. Satellite Earth Stations and Systems (SES); Global Navigation Satellite System (GNSS) Receivers; Radio Equipment Operating in the 1 164 MHz to 1 300 MHz and 1 559 MHz to 1 610 MHz Frequency Bands; Harmonised Standard Covering the Essential Requirements of Article 3.2 of Directive 2014/53/EU; Draft ETSI EN 303 413 V1.1.0; ETSI: Valbonne, France, 2017. [Google Scholar]
- Di Taranto, R.; Muppirisetty, L.S.; Raulefs, R.; Slock, D.; Svensson, T.; Wymeersch, H. Location-aware Communications for 5G Networks. IEEE Signal Process. Mag. 2014, 31, 102–112. [Google Scholar] [CrossRef]
- Ahmad, I.; Kumar, T.; Liyanage, M.; Okwuibe, J.; Ylianttila, M.; Gurtov, A. 5G Security: Analysis of Threats and Solutions. In Proceedings of the Conference on Standards for Communications and Networking (CSCN), Helsinki, Finland, 18–20 September 2017; pp. 193–199. [Google Scholar]
- Huawei. 5G Security: Forward Thinking. 2015. Available online: https://www.huawei.com/minisite/5g/img/5G_Security_Whitepaper_en.pdf (accessed on 1 April 2019).

| Construct | Description |
|---|---|
| V | Target vehicle |
| S | Target base station |
| Random nonces | |
| Hashing function | |
| Unique identification number | |
| Pairwise symmetric key | |
| Signature by | |
| Distance between nodes | |
| Time between message exchange | |
| Delay in response to the base station | |
| Miscalculated time of passing the signal | |
| Homomorphic transformation |
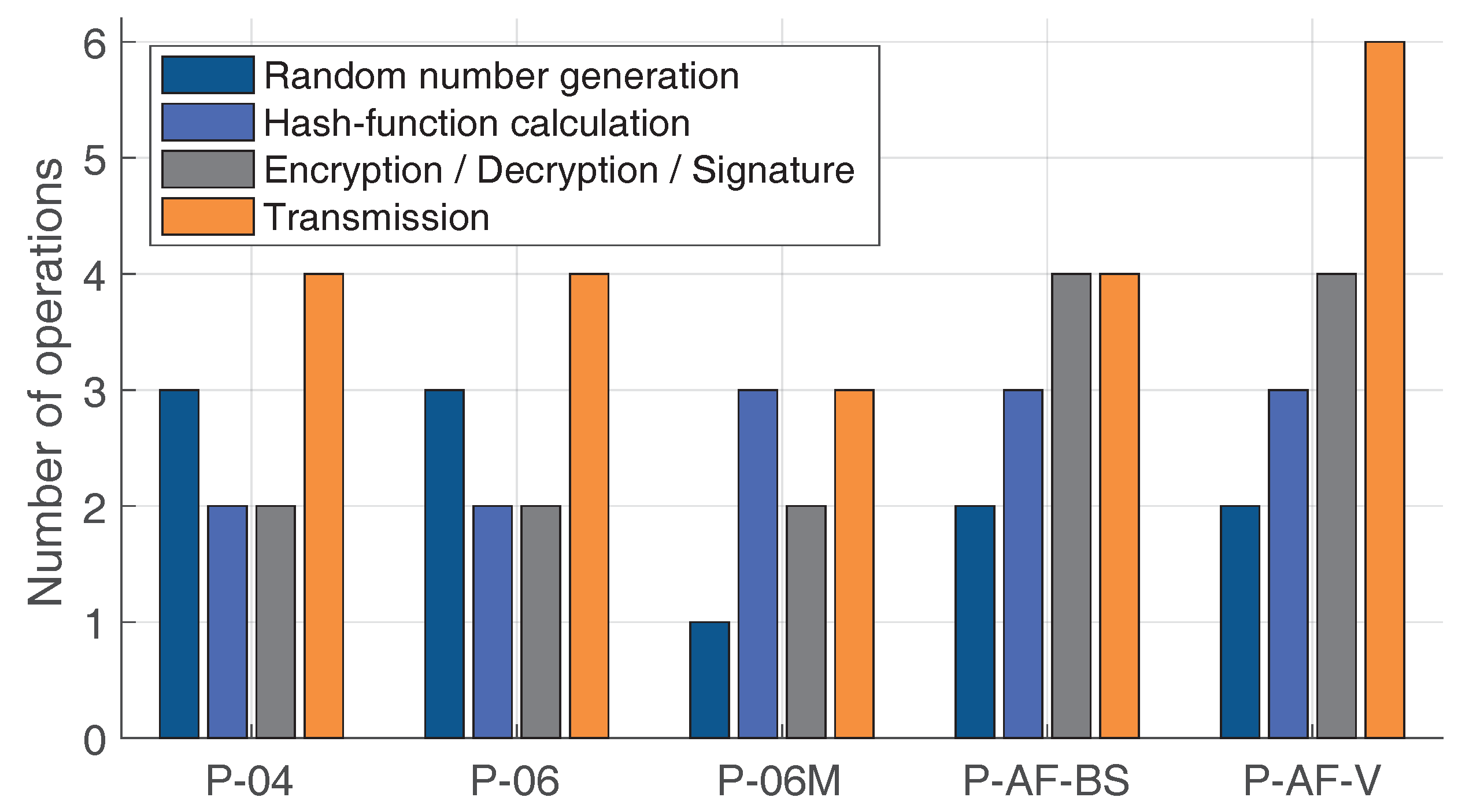
| Protocol | Storage Space | Complexity |
|---|---|---|
| Protocol-2004 (P-04) | 2 random nonces; Hash value | |
| Protocol-2006 (P-06) | 2 random nonces; Hash value; Symmetric keys | |
| Modified Protocol-2006 (P-06-M) | Random nonce; Hash value; Symmetric keys | |
| BS-based anonymity-focused protocol (P-AF-BS) | Random nonce; Hash value; Symmetric keys; Interval sigma | |
| Vehicle-based anonymity-focused protocol (P-AF-V) | Random nonce; Hash value; Symmetric keys; Interval sigma |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ometov, A.; Bezzateev, S.; Davydov, V.; Shchesniak, A.; Masek, P.; Lohan, E.S.; Koucheryavy, Y. Positioning Information Privacy in Intelligent Transportation Systems: An Overview and Future Perspective. Sensors 2019, 19, 1603. https://doi.org/10.3390/s19071603
Ometov A, Bezzateev S, Davydov V, Shchesniak A, Masek P, Lohan ES, Koucheryavy Y. Positioning Information Privacy in Intelligent Transportation Systems: An Overview and Future Perspective. Sensors. 2019; 19(7):1603. https://doi.org/10.3390/s19071603
Chicago/Turabian StyleOmetov, Aleksandr, Sergey Bezzateev, Vadim Davydov, Anna Shchesniak, Pavel Masek, Elena Simona Lohan, and Yevgeni Koucheryavy. 2019. "Positioning Information Privacy in Intelligent Transportation Systems: An Overview and Future Perspective" Sensors 19, no. 7: 1603. https://doi.org/10.3390/s19071603
APA StyleOmetov, A., Bezzateev, S., Davydov, V., Shchesniak, A., Masek, P., Lohan, E. S., & Koucheryavy, Y. (2019). Positioning Information Privacy in Intelligent Transportation Systems: An Overview and Future Perspective. Sensors, 19(7), 1603. https://doi.org/10.3390/s19071603









