Tell the Device Password: Smart Device Wi-Fi Connection Based on Audio Waves
Abstract
:1. Introduction
- Audio wave transmission is not based on 802.11 or some other standards. Service providers can freely design the format their audio packets. It means that credentials are not necessarily stored in meta-data area. Independent packet design also means that we reduce space waste to some extent, and the format of packet can be not public to all, which means encryption can be more secret.
- It is much more difficult to eavesdrop audio waves than Wi-Fi packets. Loudness and noise will interfere with attackers efficiently when they try to conduct attack actions in a secure distance, which is usually not near the device.
- Audio wave transmission has higher efficiency than SmartCfg. It is fast to generate the encoded audio waves and broadcast them. Receiving and decoding also take very little time. Therefore, network connection can be completed very quickly.
- Most devices are already equipped with audio components, which means deploying this new configuration solution would be very simple.
2. Background and Related Work
2.1. Wi-Fi Configuration of Smart Devices
2.2. Audio Wave Transmission in IoT
2.3. Present Configuration Methods
SmartCfg
- Although SmartCfg has three different storing schemes, it is still easy for attackers to detect which scheme the app is using because of the obvious features of these three schemes. The reason is that 802.11 packets have designed format. The positions of all meta data are public to all. As a result, SmartCfg is not secure enough congenitally.
- Wi-Fi packet is easy to be eavesdropped as 802.11 packets have various frequency bands. To make sure the configuration progresses properly, the devices need to sniff all frequency bands in turn and the user’s app should send the same packets many times to ensure that no packet is lost, which increases the possibility that packets are captured by attackers.
- According to the second disadvantage, it is hard for the devices to capture the correct packet quickly because they have to sniff all frequency bands one by one. That is, SmartCfg is not efficient enough.
2.4. Other Possible Techniques
2.4.1. Bluetooth Low Energy
2.4.2. Wi-Fi Direct
3. Audio Wave Based Credential Transmission
3.1. Overview
3.2. Scheme Design
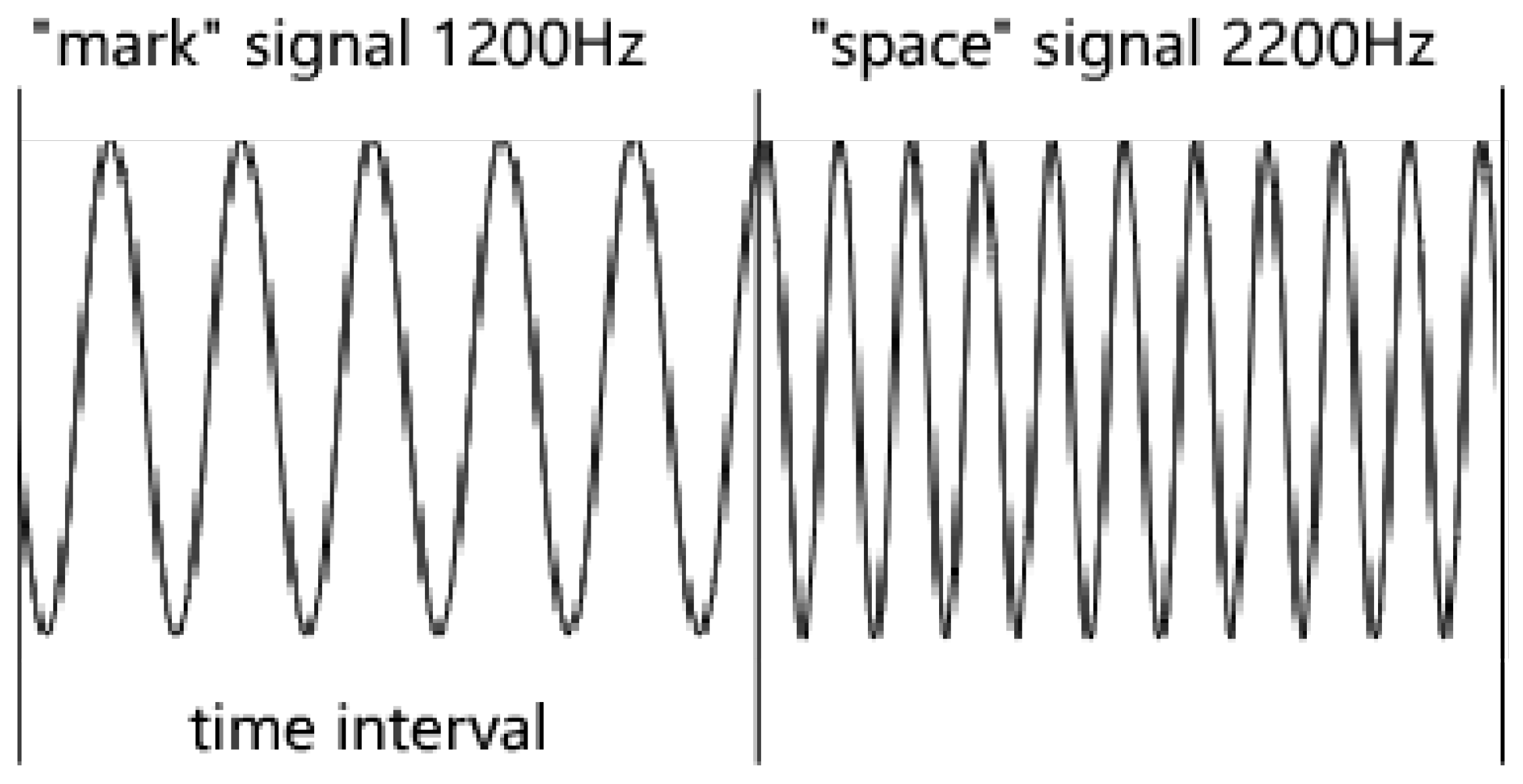
3.2.1. Modulation
- It transmits fewer bits than other methods, which provides higher efficiency.
- It has high resistance to noise due to narrow receiver bandwidth per tone.
- It can hardly be affected by ionospheric effects such as Doppler, fading and multi-path.
- The error rate of MFSK family reduces as the number of tones is increased, and 16 tones is most suitable.
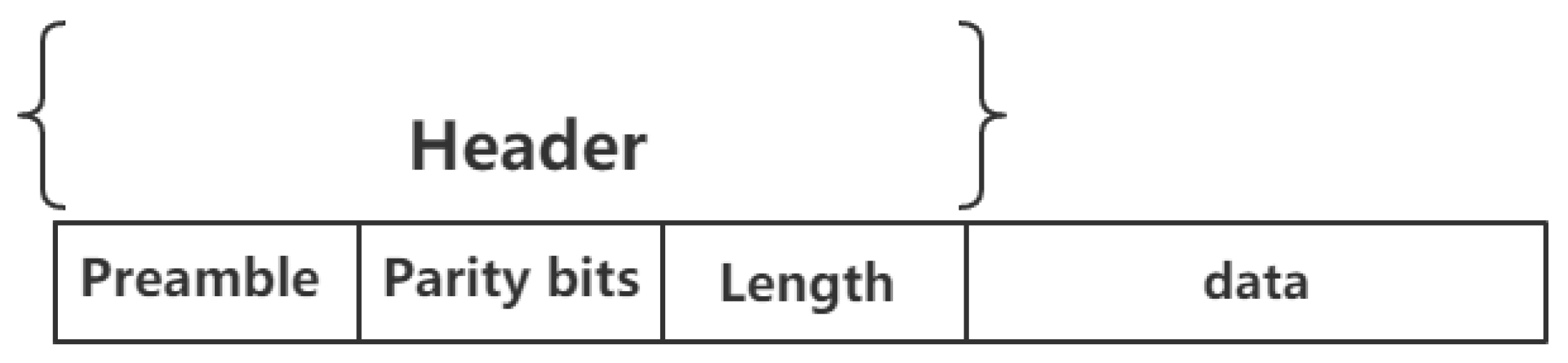
3.2.2. Packet Format
3.3. Work Process
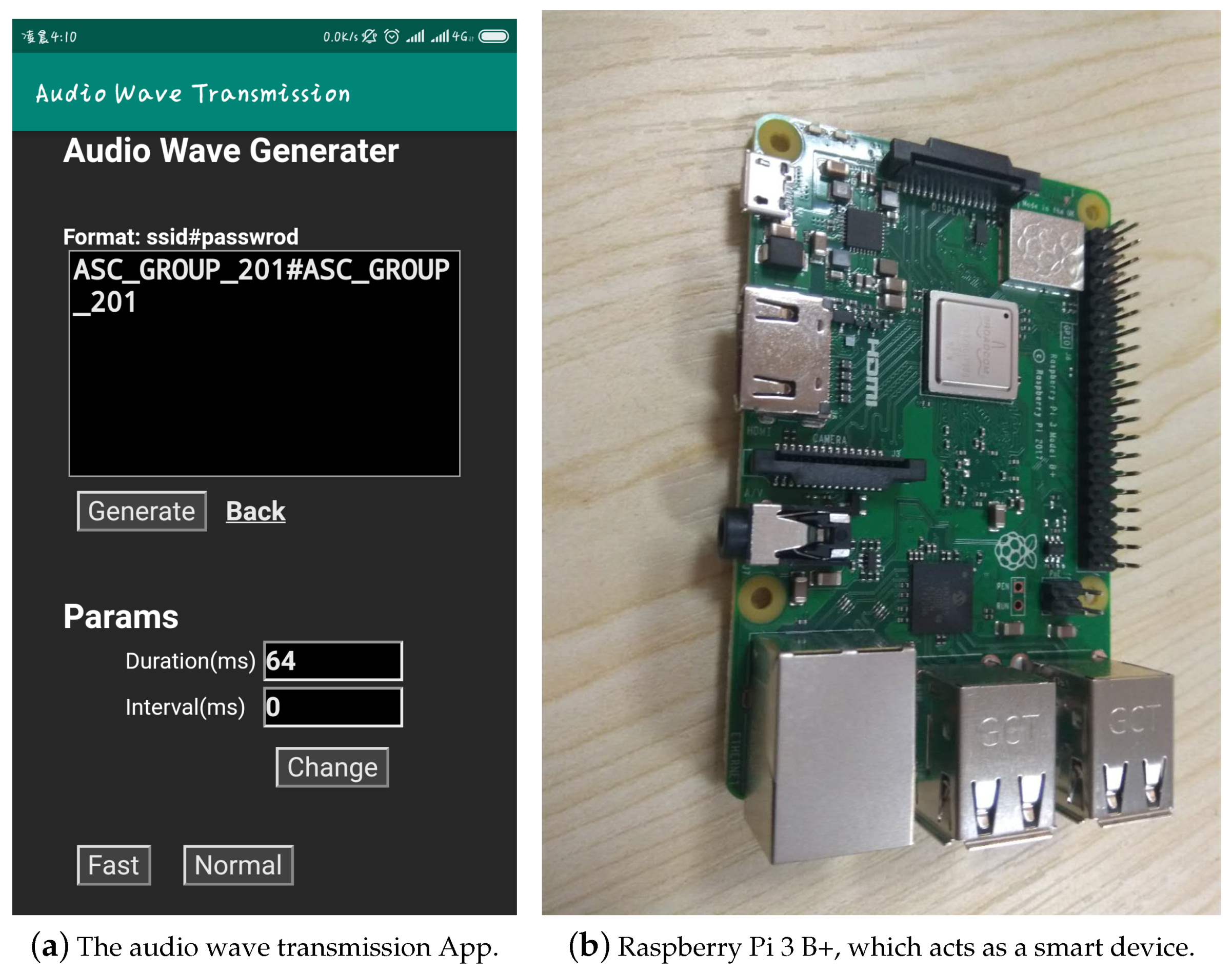
3.3.1. Signal Generation
3.3.2. Signal Receiving
3.4. Encryption
- Use a secure hash function H, and use the as the key to do the encryption, such as SHA256. This method is the fastest and can deal with most situations. However, once the hash function used is found by attackers, it becomes very vulnerable.
- Use ECDH (Elliptic Curve Diffie-Hellman) to do the key-exchange [28]. This method is secure but it need the manufacturer to implement PKI (Public key infrastructure) on each of its devices, which increases the cost. In addition, the speed of ECDH is not fast enough.
- Use password-authenticated key exchange (PAKE) to establish a secure cryptographic key, such as J-PAKE (Password Authenticated Key Exchange by Juggling) [29], which is a fast PAKE protocol providing two or more parties to establish private and authenticated communication solely without PKI based on their shared (low-entropy) secret. In this method, the cryptographic key is computed before the configuration process. This method takes a little time to do the PAKE process but is very secure.
3.5. Summary
4. Experimental Evaluation
4.1. Environment and Settings
4.2. Results
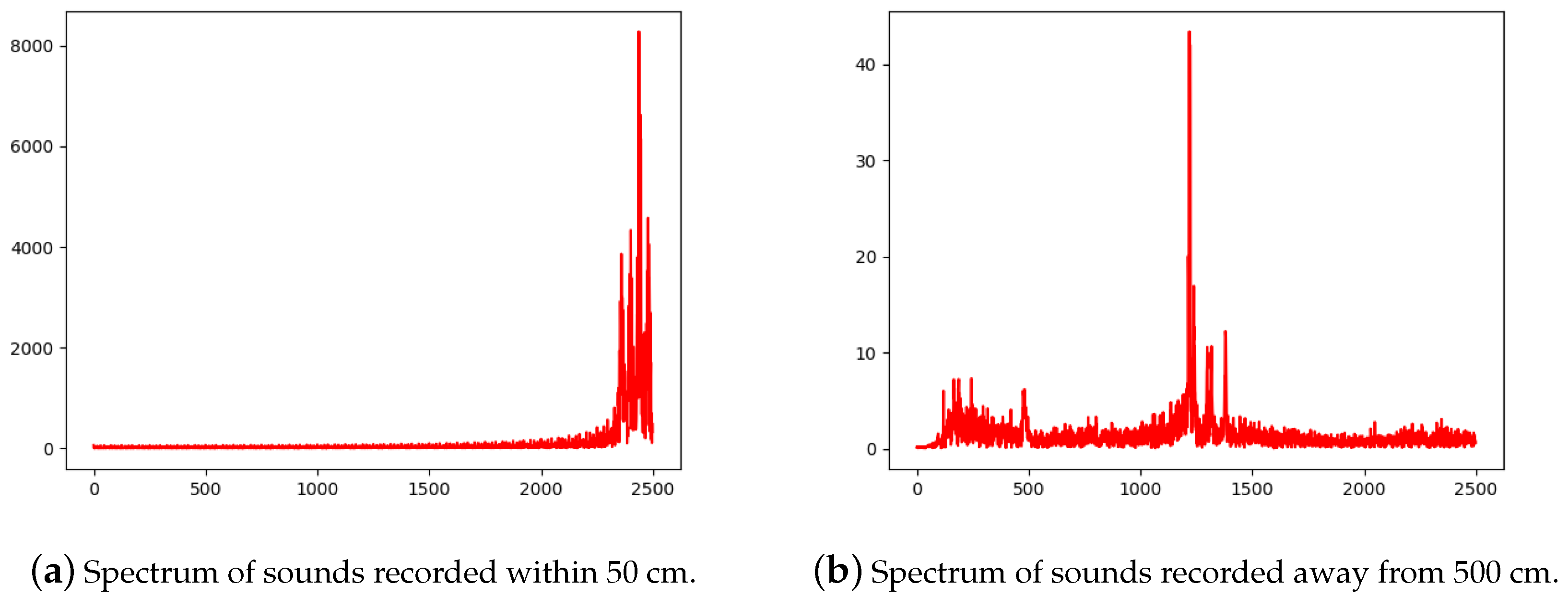
4.2.1. Security Analysis
4.2.2. Speed Analysis
4.3. Summary
5. Discussions
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Zhang, Z.; Cho, M.C.Y.; Wang, C.; Hsu, C.; Chen, C.; Shieh, S. IoT Security: Ongoing Challenges and Research Opportunities. In Proceedings of the 2014 IEEE 7th International Conference on Service-Oriented Computing and Applications, Matsue, Japan, 17–19 November 2014; pp. 230–234. [Google Scholar] [CrossRef]
- Li, C.; Cai, Q.; Li, J.; Liu, H.; Zhang, Y.; Gu, D.; Yu, Y. Passwords in the Air: Harvesting Wi-Fi Credentials from SmartCfg Provisioning. In Proceedings of the 11th ACM Conference on Security Privacy in Wireless and Mobile Networks, Stockholm, Sweden, 18–20 June 2018; pp. 1–11. [Google Scholar] [CrossRef]
- Smarthome—Home Automation Systems, Products, Kits, Hubs. Available online: http://www.smarthome.com (accessed on 14 June 2018).
- Wang, W.; Yang, L.; Zhang, Q. Resonance-Based Secure Pairing for Wearables. IEEE Trans. Mob. Comput. 2018, 17, 2607–2618. [Google Scholar] [CrossRef]
- Liang, X.; Yun, T.; Peterson, R.; Kotz, D. LightTouch: Securely connecting wearables to ambient displays with user intent. In Proceedings of the IEEE INFOCOM 2017—IEEE Conference on Computer Communications, Atlanta, GA, USA, 1–4 May 2017. [Google Scholar] [CrossRef]
- CC3200 SmartConfig Provisioning. Available online: http://processors.wiki.ti.com/index.php/CC3200_SmartConfig_Provisioning?keyMatch=smartconfig&tisearch=Search-EN-Everything (accessed on 10 June 2018).
- Li, H.; Zhu, H.; Ma, D. Demographic Information Inference through Meta-Data Analysis of Wi-Fi Traffic. IEEE Trans. Mob. Comput. 2018, 17, 1033–1047. [Google Scholar] [CrossRef]
- Liu, H.; Li, C.; Jin, X.; Li, J.; Zhang, Y.; Gu, D. Smart Solution, Poor Protection: An Empirical Study of Security and Privacy Issues in Developing and Deploying Smart Home Devices. In Proceedings of the 2017 Workshop on Internet of Things Security and Privacy, Dallas, TX, USA, 30 October–3 November 2017. [Google Scholar] [CrossRef]
- Ghose, N.; Lazos, L.; Li, M. HELP: Helper-Enabled In-Band Device Pairing Resistant Against Signal Cancellation. In Proceedings of the 26th USENIX Security Symposium (USENIX Security 17), Vancouver, BC, Canada, 16–18 August 2017; pp. 433–450. [Google Scholar]
- Wu, Y.; Chen, B.; Zhao, Z.; Cheng, Y. Attack and Countermeasure on Interlock-Based Device Pairing Schemes. IEEE Trans. Inf. Forensics Secur. 2018, 13, 745–757. [Google Scholar] [CrossRef]
- Wright, J.; Cache, J. Hacking Exposed Wireless: Wireless Security Secrets & Solutions, 3rd ed.; McGraw-Hill Education Group: New York, NY, USA, 2015. [Google Scholar]
- Liao, C.; Shuai, H.; Wang, L. Eavesdropping prevention for heterogeneous Internet of Things systems. In Proceedings of the 2018 15th IEEE Annual Consumer Communications Networking Conference (CCNC), Las Vegas, NV, USA, 12–15 January 2018; pp. 1–2. [Google Scholar] [CrossRef]
- Xu, Q.; Ren, P.; Song, H.; Du, Q. Security Enhancement for IoT Communications Exposed to Eavesdroppers With Uncertain Locations. IEEE Access 2016, 4, 2840–2853. [Google Scholar] [CrossRef]
- Geneiatakis, D.; Kounelis, I.; Neisse, R.; Nai-Fovino, I.; Steri, G.; Baldini, G. Security and privacy issues for an IoT based smart home. In Proceedings of the 2017 40th International Convention on Information and Communication Technology, Electronics and Microelectronics (MIPRO), Opatija, Croatia, 22–26 May 2017; pp. 1292–1297. [Google Scholar] [CrossRef]
- Ho, G.; Leung, D.; Mishra, P.; Hosseini, A.; Song, D.; Wagner, D. Smart Locks: Lessons for Securing Commodity Internet of Things Devices. In Proceedings of the 11th ACM on Asia Conference on Computer and Communications Security, Xi’an, China, 30 May–3 June 2016. [Google Scholar] [CrossRef]
- Jewell, M.O.; Costanza, E.; Kittley-Davies, J. Connecting the Things to the Internet: An Evaluation of Four Configuration Strategies for Wi-fi Devices with Minimal User Interfaces. In Proceedings of the 2015 ACM International Joint Conference on Pervasive and Ubiquitous Computing, Osaka, Japan, 7–11 September 2015. [Google Scholar] [CrossRef]
- Kamruzzaman, J.; Wang, G.; Karmakar, G.; Ahmad, I.; Bhuiyan, M.Z.A. Acoustic sensor networks in the Internet of Things applications. Future Gener. Comput. Syst. 2018, 86, 1167–1169. [Google Scholar] [CrossRef]
- Sound Wave Payment. Available online: https://docs.open.alipay.com/140/104622/ (accessed on 12 September 2018).
- Vacher, M.; Istrate, D.; Portet, F.; Joubert, T.; Chevalier, T.; Smidtas, S.; Meillon, B.; Lecouteux, B.; Sehili, M.; Chahuara, P.; et al. The sweet-home project: Audio technology in smart homes to improve well-being and reliance. In Proceedings of the 2011 Annual International Conference of the IEEE Engineering in Medicine and Biology Society, Boston, MA, USA, 30 August–3 September 2011. [Google Scholar] [CrossRef]
- Cueva-Sánchez, Y.; Castro-Paredes, H.; Barrientos-Padilla, A.; Shiguihara-Juárez, P. Comparative Analysis of Technologies for Audio Data Transmission. In Proceedings of the 2018 IEEE Sciences and Humanities International Research Conference (SHIRCON), Lima, Peru, 20–22 November 2018. [Google Scholar] [CrossRef]
- SmartConfig Technology Comparison. Available online: https://blog.csdn.net/flyingcys/article/details/49283273 (accessed on 12 June 2018).
- Texas Instruments. Simplelink Wi-Fi Smartconfig Technology. Available online: http://www.ti.com/tool/smartConfig?keyMatch=smart20config&tisearch=Search-EN-Everything (accessed on 14 June 2018).
- The Attack Vector “BlueBorne” Exposes Almost Every Connected Device. Available online: https://armis.com/blueborne/ (accessed on 25 June 2018).
- Biham, E.; Neumann, L. Breaking the Bluetooth Pairing–Fixed Coordinate Invalid Curve Attack. Available online: http://www.cs.technion.ac.il/~biham/BT/bt-fixed-coordinate-invalid-curve-attack.pdf (accessed on 14 June 2018).
- Shen, W.; Yin, B.; Cao, X.; Cai, L.X.; Cheng, Y. Secure device-to-device communications over WiFi direct. IEEE Netw. 2016, 30, 4–9. [Google Scholar] [CrossRef]
- MFSK16. Available online: https://www.qsl.net/zl1bpu/MFSK/M16.htm. (accessed on 12 September 2018).
- Bell 202 Interface Specification for Transmission of Binary Data by Frequency Manipulation FSK. Available online: http://www.softelectro.ru/bell202_en.html. (accessed on 24 June 2018).
- Barker, E.; Johnson, D.; Smid, M. Recommendation for Pair-Wise Key Establishment Schemes Using Discrete Logarithm Cryptography; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2006.
- Hao, F.; Ryan, P. J-PAKE: Authenticated Key Exchange without PKI. In Transactions on Computational Science XI: Special Issue on Security in Computing, Part II; Gavrilova, M.L., Tan, C.J.K., Moreno, E.D., Eds.; Springer: Berlin/Heidelberg, Germany, 2010; pp. 192–206. [Google Scholar] [CrossRef]
- Karapanos, N.; Marforio, C.; Soriente, C.; Capkun, S. Sound-Proof: Usable Two-Factor Authentication Based on Ambient Sound. In Proceedings of the 24th USENIX Security Symposium (USENIX Security 15), Washington, DC, USA, 12–14 August 2015; pp. 483–498. [Google Scholar]
- Wang, W.; Yang, L.; Zhang, Q. Touch-and-guard: Secure Pairing Through Hand Resonance. In Proceedings of the 2016 ACM International Joint Conference on Pervasive and Ubiquitous Computing, Heidelberg, Germany, 12–16 September 2016. [Google Scholar] [CrossRef]
- Zhang, G.; Yan, C.; Ji, X.; Zhang, T.; Zhang, T.; Xu, W. DolphinAttack: Inaudible Voice Commands. In Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security, Dallas, TX, USA, 30 October–3 November 2017. [Google Scholar] [CrossRef]
- Genkin, D.; Shamir, A.; Tromer, E. Acoustic Cryptanalysis. J. Cryptol. 2017, 30, 392–443. [Google Scholar] [CrossRef]
- Genkin, D.; Pattani, M.; Schuster, R.; Tromer, E. Synesthesia: Detecting Screen Content via Remote Acoustic Side Channels. arXiv, 2018; arXiv:1809.02629. [Google Scholar]


| Manufacturer | Technique |
|---|---|
| TI | SmartConfig |
| MTK | SmartConnection |
| Marvell | EasyConnect |
| Reltek | SimpleConfig |
| Espressif | SmartConfig |
| AirKiss |
| Tone (Hz) | Bits |
|---|---|
| 1200 | 0000 |
| 1240 | 0001 |
| 1280 | 0011 |
| 1320 | 0010 |
| 1360 | 0110 |
| 1400 | 0111 |
| 1440 | 0101 |
| 1480 | 0100 |
| 1520 | 1100 |
| 1560 | 1101 |
| 1600 | 1111 |
| 1640 | 1110 |
| 1680 | 1010 |
| 1720 | 1011 |
| 1760 | 1001 |
| 1800 | 1000 |
| Normal Loudness | Relatively Loud | |
|---|---|---|
| 10 cm | 100% | 100% |
| 30 cm | 93.3% | 100% |
| 50 cm | 72.5% | 96.2% |
| 100 cm | 9.45% | 42.6% |
| Normal Loudness | Relatively Loud | |
|---|---|---|
| 10 cm | 2.6 | 2.8 |
| 30 cm | 2.8 | 2.6 |
| 50 cm | 9.3 | 4.5 |
| 100 cm | 95.2 | 64.2 |
| Distance | Time Spent |
|---|---|
| 10 cm | 6.58 |
| 30 cm | 6.19 |
| 50 cm | 8.12 |
| 100 cm | 8.57 |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Liu, L.; Han, Z.; Fang, L.; Ma, Z. Tell the Device Password: Smart Device Wi-Fi Connection Based on Audio Waves. Sensors 2019, 19, 618. https://doi.org/10.3390/s19030618
Liu L, Han Z, Fang L, Ma Z. Tell the Device Password: Smart Device Wi-Fi Connection Based on Audio Waves. Sensors. 2019; 19(3):618. https://doi.org/10.3390/s19030618
Chicago/Turabian StyleLiu, Liang, Zhaoyang Han, Liming Fang, and Zuchao Ma. 2019. "Tell the Device Password: Smart Device Wi-Fi Connection Based on Audio Waves" Sensors 19, no. 3: 618. https://doi.org/10.3390/s19030618
APA StyleLiu, L., Han, Z., Fang, L., & Ma, Z. (2019). Tell the Device Password: Smart Device Wi-Fi Connection Based on Audio Waves. Sensors, 19(3), 618. https://doi.org/10.3390/s19030618






