A Multi-Server Two-Factor Authentication Scheme with Un-Traceability Using Elliptic Curve Cryptography
Abstract
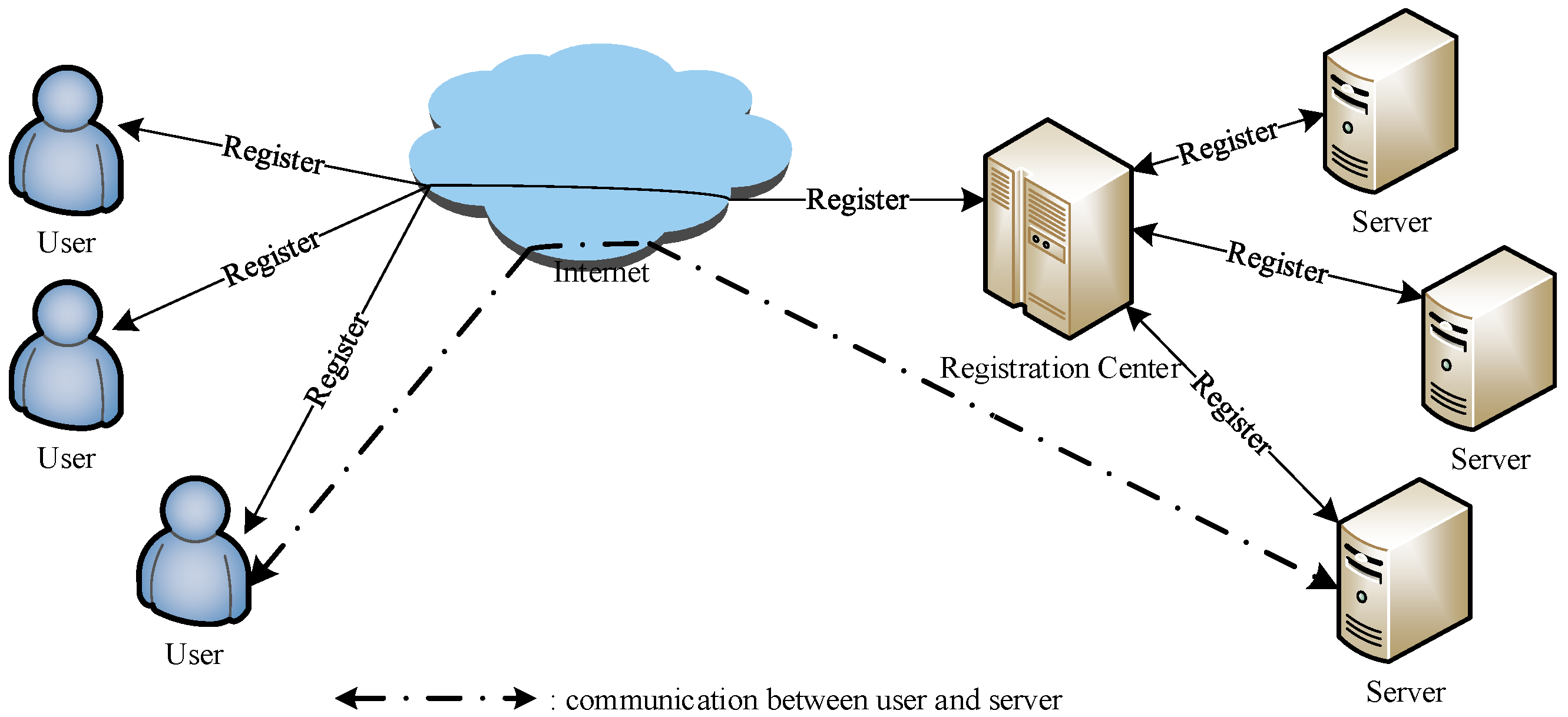
1. Introduction
1.1. Contributions
1.2. Outline of This Paper
2. Preliminary
2.1. Collision-Resistant One-Way Hash Function
- Given , it is difficult to determine the input within polynomial time.
- It is difficult to determine such that , where .
- It is difficult to uncover a pair , such that and could hold.
2.2. Intractable Problems in ECC
- ECDLP: The elliptic curve discrete-logarithm problem over elliptic curve refers to computing from for given .
- ECCDHP: The elliptic curve computational Diffie–Hellman problem over elliptic curve refers to computing , given points .
2.3. Adversary Model
- is able to intercept, block, delete, modify, and resend the message contents through an open channel.
- Because identity and password have low entropy, can enlist all pairs of simultaneously from within polynomial time, where and refer to the space of passwords and identities in and , respectively.
- can either acquire of the via malicious device or reveal the information from , but is not permitted to use both methods together.
- can acquire a server’s private key while evaluating forward secrecy or key-compromise user impersonation attack.
- has the ability to reveal all parameters of the smart card when assessing stolen smart-card attack, offline password guessing attack, impersonation attack, forward secrecy, etc.
3. Brief Review of Amin et al.’s Proposal
3.1. Initialization
3.2. Registration
- enters an identity and password . Subsequently, randomly picks up a number r and calculates . Afterwards, transmits the registration request message to S via secure medium.
- Upon receiving the request message from the new user , S calculates , , and . Afterwards, S stores the contents in a new card and sends to .
- Once obtaining , stores u into .
3.3. Login and Authentication
- To start the session with the S, inserts into a card reader and inputs their login details, including and . Subsequently, calculates , and . Afterwards, it verifies the value of . In case of invalid values, the session is ended. Otherwise, randomly chooses a number , the current time stamp , and calculates and . Next, transmits the login request message to S.
- Upon receiving the login request from , S verifies the time stamp corresponding to the current time stamp . In the case of valid time stamp , it continues to execute the following steps. Otherwise, it aborts the session. Afterwards, S decrypts to obtain and then checks whether and . Afterwards, S checks . After finishing this verification, S randomly selects a number and computes . Finally, S transmits the respond message to via public channel.
- Once receiving the response message from S, checks the validity of . After finishing the verification, checks whether and verifies . If it holds, accepts the response message. Finally, S and calculate the session key:
4. Limitations of Amin et al.’s Scheme
4.1. User Un-Traceability
4.2. Offline Password Guessing Attack
- From the password dictionary space , the adversary randomly chooses the password , and picks up the identity from the identity dictionary space .
- calculates .
- calculates .
- calculates .
- To check the correctness of and , examines whether , where belongs to of .
- If the aforementioned equality holds, ’s guess results as successful. Otherwise, repeats Steps 1–5 until it obtains the correct password and identity of .
4.3. Lacks of Perfect Forward Secrecy
- The adversary computes to obtain .
- computes .
- computes .
- computes .
4.4. Key-Compromise User Impersonation Attack
- computes , and subsequently calculates and .
- obtains the login request message of , randomly selects a number , and computes Afterwards, transmits the forged request message to S.
- Upon receiving the forged message, obviously S can verify it successfully. Thus, S randomly provokes a number , and computes and . Finally, S sends to .
- Upon receiving the response from S, calculates . Finally, the server S believes that is the common session key between a legitimate user and itself. However, in actual terms, acts as .
5. Review of Srinivas et al.’s Scheme
5.1. Initialization
5.2. Registration Process
5.2.1. Server Registration
5.2.2. User Registration
5.3. Login and Authentication
- inserts into a card reader and inputs and . checks , and . Afterwards, randomly generates a number a, chooses the current time stamp , and calculates and . Subsequently, transmits the login request message to .
- receives the request message from , figures out , and checks . terminates the login request if the expression does not hold. Apart from that, a random number b and calculates . Afterwards, picks the current time stamp and computes and . Finally, sends the response message to .
- On receiving the response message, figures out , and Subsequently, checks and terminates this login request if the expression does not hold. Otherwise, calculates and transmits it to through a public channel.
- Upon acquiring , computes and checks . After successful accomplishment of all steps, and believe that they have the common session key .
5.4. Password Updation Stage
6. Limitations of Srinivas et al.’s Protocol
6.1. Offline Password Guessing Attack
- From the password dictionary space , the adversary chooses the password , and picks up the identity from the identity dictionary space .
- computes .
- computes .
- computes .
- computes .
- verifies whether , where is acquired from smart card of .
- If it holds, then and is the correct identity and password pair. Otherwise, repeats Steps 1–6 until it obtains the correct identity and password of .
6.2. Lack of User Un-Traceability
6.3. Key-Compromise User Impersonation Attack
- intercepts the login request message of , and calculates .
- randomly selects a number to compute . Afterwards, sends the forged login request message to .
- Obviously, the forged message can pass the verification of . Thus, randomly chooses a number to compute . Subsequently, chooses the current time stamp to compute and . Finally, sends the response message to .
- On receiving the response message, figures out Subsequently, calculates and transmits it to through a public channel.
- receives , computes , and checks whether . After finishing all steps successfully, believes that it holds the common session key with . Actually, however, plays as . Thus, successfully impersonated to under the condition that the long-term private key of the server was leaked.
7. The Improved Scheme
7.1. Initialization
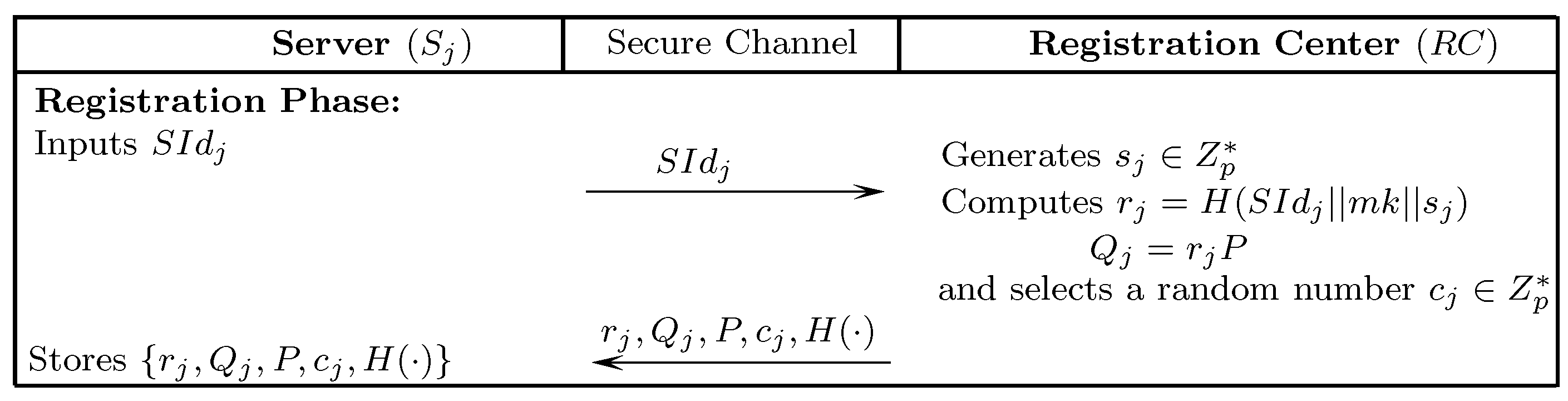
7.2. Server Registration
- chooses an identity and transmits it to via a secure-medium.
- receives the registration message, randomly generates a number , and computes Subsequently, randomly generates a number for . Finally, sends to through secure-medium.
- stores in its database.
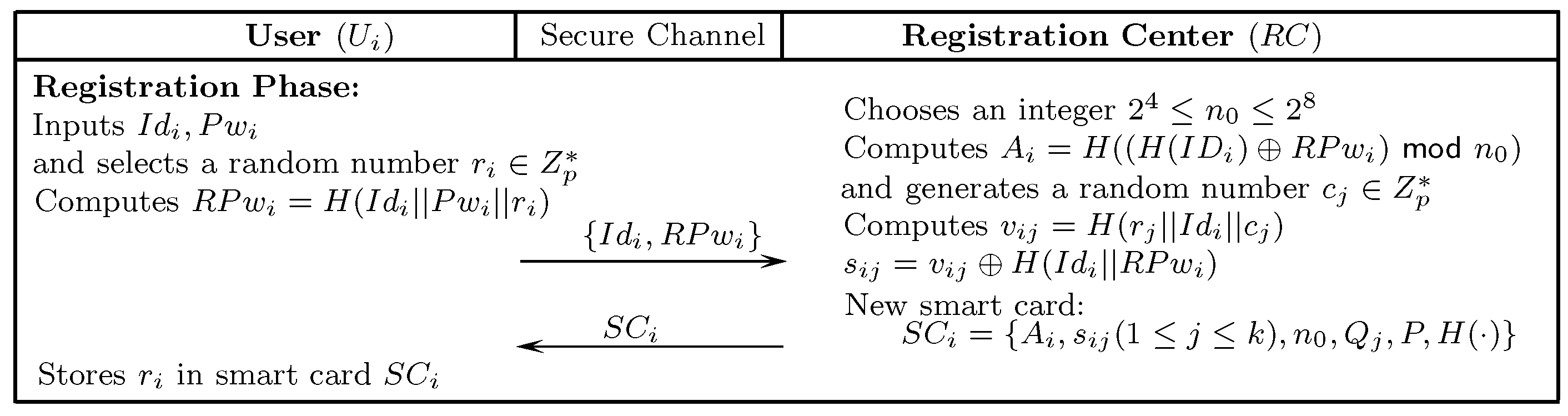
7.3. User Registration
- selects , , and randomly generates a number to compute . Afterwards, transmits the registration request message to through a secure medium.
- Upon receiving the registration message, randomly generates numbers , and computes the following: , where . Afterwards, inserts , into a new . and sends it to through secure-medium.
- stores in .
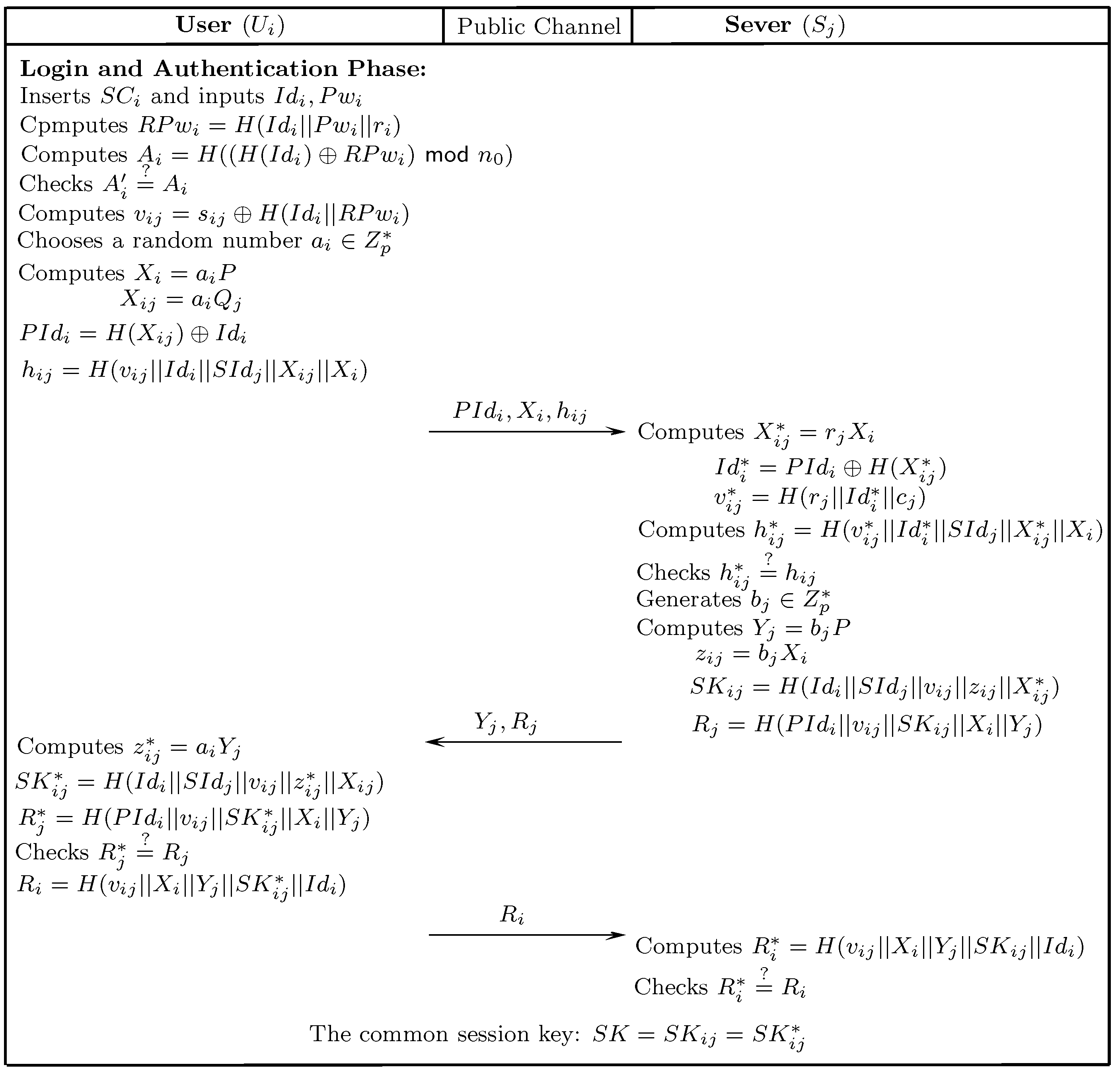
7.4. Login and Mutual Authentication
- inserts into a card reader and inputs , . computes , and subsequently calculates . Afterwards, inspects the correctness of while comparing it with the value of sorted in . If , and are validated. Otherwise, the session is expired. continues to compute and randomly selects a number to calculate the following: Finally, transmits the request to via an open channel.
- After receiving , calculates , and Afterwards, computes Then, verifies . In the case of invalidation, terminates the session and sets the counter . keeps suspending the card until registers again if N surpasses some threshold mark (e.g., 8). Otherwise, randomly selects a number to compute , and Finally, sends the response message to via open channel.
- Upon receiving the respond message , computes , and Subsequently, checks whether . The session is aborted if these are not equal, . Otherwise, is authenticated by and accepts . Afterwards, computes Finally, transmits the challenge message to through an open channel.
- Upon receiving the challenge message from , computes and verifies whether . If these are equal, then is authenticated successfully.
7.5. Password Updation
- inserts the into a card reader and inputs , current password , and password to be updated .
- computes and Afterwards, checks whether . In case of inequality, refuses to update the password.
- Apart from that, randomly selects a number to compute Subsequently, computes Finally, replaces with , respectively.
8. Security Inspection
8.1. User Un-Traceability and Anonymity
8.2. Stolen Smart-Card Attack
8.3. Offline Password Guessing Attack
8.4. Privileged Insider Attack
8.5. Key-Compromise User Impersonation Attack
8.6. Server Impersonation Attack
8.7. Replay Attack
8.8. Known Key Security
8.9. Mutual Authentication
8.10. Man-in-the-Middle Attack
8.11. Denial-of-Service Attack
8.12. Perfect Forward Secrecy
9. BAN-Logic Proof
9.1. Idealized Scheme
- Message 1.
- : ,
- Message 2.
- : , .
9.2. Security Objectives
- Objective 1.
- Objective 2.
- Objective 3.
- Objective 4.
9.3. Initiative Premises
- IP 1.
- .
- IP 2.
- .
- IP 3.
- .
- IP 4.
- .
- IP 5.
- .
- IP 6.
- .
- IP 7.
- .
- IP 8.
- .
9.4. Proof Procedure
- Step 1.
- From Message 2, it shows the following:
- Step 2.
- From Step 1, IP 5, and the message-meaning rule, it illustrates the following:
- Step 3.
- From IP 1 and the freshness conjuncatenation rule, the following can be inferred:
- Step 4.
- From Steps 2 and 3, the freshness rule, and the nonce verification rule, we obtain the following:
- Step 5.
- From Step 4 and the believe rule, we deduce the first objective as follows:
- Step 6.
- From Objective 1, IP 7, and the jurisdiction rule, we accomplish the second objective as follows:
- Step 7.
- From Message 1, it indicates the following:
- Step 8.
- From Step 7, IP 6, and the message meaning rule, the following can be inferred:
- Step 9.
- From IP 2 and the freshness conjuncatenation rule, the following can be obtained:
- Step 10.
- From Steps 8 and 9, the freshness rule, and the nonce-verification rule, we determine the following:
- Step 11.
- From Step 10 and the believe rule, the third objective can be achieved as follows:
- Step 12.
- From Objective 3, IP 8, and the jurisdiction rule, the fourth objective is accomplished as follows:
10. Performance Comparison
11. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Lamport, L. Password authentication with insecure communication. Commun. ACM 1981, 24, 770–772. [Google Scholar] [CrossRef]
- Franks, J.; Hallam-Baker, P.; Hostetler, J.; Lawrence, S.; Leach, P.; Luotonen, A. HTTP Authentication: Basic and Digest Access Authentication. IETF RFC 1999, 2617, 1–34. [Google Scholar]
- Yang, C.; Wang, R.; Liu, W. Secure authentication scheme for session initiation protocol. Comput. Secur. 2005, 24, 381–386. [Google Scholar] [CrossRef]
- Khan, M.K. Fingerprint Biometric-based Self-Authentication and Deniable Authentication Schemes for the Electronic World. IETE Tech. Rev. 2009, 26, 191–195. [Google Scholar] [CrossRef]
- Farash, M.S.; Chaudhry, S.A.; Heydari, M.; Sadough, S.M.S.; Kumari, S.; Khan, M.K. A lightweight anonymous authentication scheme for consumer roaming in ubiquitous networks with provable security. Int. J. Commun. Syst. 2017, 30, e3019. [Google Scholar] [CrossRef]
- Arkko, J.; Torvinen, V.; Camarillo, G.; Niemi, A.; Haukka, T. Security Mechanism Agreement for SIP Sessions; IETF Internet Draft: Fremont, CA, USA, 2002. [Google Scholar]
- Arshad, R.; Ikram, N. Elliptic curve cryptography based mutual authentication scheme for session initiation protocol. Multimed. Tools Appl. 2013, 66, 165–178. [Google Scholar] [CrossRef]
- Chaudhry, S.A.; Khan, I.; Irshad, A.; Ashraf, M.U.; Khan, M.K.; Ahmad, H.F. A provably secure anonymous authentication scheme for session initiation protocol. Secur. Commun. Netw. 2016. [Google Scholar] [CrossRef]
- Chaudhry, S.A.; Naqvi, H.; Shon, T.; Sher, M.; Farash, M.S. Cryptanalysis and Improvement of an Improved Two Factor Authentication Protocol for Telecare Medical Information Systems. J. Med. Syst. 2015, 39, 66. [Google Scholar] [CrossRef] [PubMed]
- Farash, M.S.; Attari, M.A. An Enhanced authenticated key agreement for session initiation protocol. Inf. Technol. Control 2013, 42, 333–342. [Google Scholar] [CrossRef]
- He, D. An efficient remote user authentication and key agreement protocol for mobile client-server environment from pairings. Ad Hoc Netw. 2012, 10, 1009–1016. [Google Scholar] [CrossRef]
- He, D.; Chen, J.; Chen, Y. A secure mutual authentication scheme for session initiation protocol using elliptic curve cryptography. Secur. Commun. Netw. 2012, 5, 1423–1429. [Google Scholar] [CrossRef]
- Islam, S.; Khan, M. Cryptanalysis and improvement of authentication and key agreement protocols for telecare medicine information systems. J. Med. Syst. 2014, 38. [Google Scholar] [CrossRef] [PubMed]
- Kumari, S.; Karuppiah, M.; Das, A.K.; Li, X.; Wu, F.; Gupta, V. Design of a secure anonymity-preserving authentication scheme for session initiation protocol using elliptic curve cryptography. J. Ambient Intell. Hum. Comput. 2017. [Google Scholar] [CrossRef]
- Qiu, S.; Xu, G.; Ahmad, H.; Wang, L. A Robust Mutual Authentication Scheme Based on Elliptic Curve Cryptography for Telecare Medical Information Systems. IEEE Access 2018, 6, 7452–7463. [Google Scholar] [CrossRef]
- Shen, C.; Nahum, E.; Schulzrinne, H.; Wright, C.P. The impact of TLS on SIP server performance: Measurement and modeling. IEEE/ACM Trans. Netw. 2012, 20, 1217–1230. [Google Scholar] [CrossRef]
- Thomas, M. SIP Security Requirements; Work In Progress; IETF Internet Draft: Fremont, CA, USA, 2001. [Google Scholar]
- Wang, D.; He, D.; Wang, P.; Chu, C. Anonymous two-factor authentication in distributed systems: Certain goals are beyond attainment. IEEE Trans. Depend. Secur. Comput. 2015, 12, 428–442. [Google Scholar] [CrossRef]
- Xie, Q. A new authenticated key agreement for session initiation protocol. Int. J. Commun. Syst. 2012, 25, 47–54. [Google Scholar] [CrossRef]
- Zhang, Z.; Qi, Q.; Kumar, N.; Chilamkurti, N.; Jeong, H.J. A secure authentication scheme with anonymity for session initiation protocol using elliptic curve cryptography. Multimed. Tools Appl. 2015, 74, 3477–3488. [Google Scholar] [CrossRef]
- Qiu, S.; Xu, G.; Ahmad, H.; Guo, Y. An enhanced password authentication scheme for session initiation protocol with perfect-forward-secrecy. PLoS ONE 2018, 13, e0194072. [Google Scholar] [CrossRef] [PubMed]
- Qiu, S.; Xu, G.; Guo, Y.; Zhang, M. Cryptanalysis and improvement of 2 mutual authentication schemes for Session Initiation Protocol. Int. J. Commun. Syst. 2018, 31, e3568. [Google Scholar] [CrossRef]
- Awasthi, A.K.; Srivastava, K.; Mittal, R.C. An improved timestamp-based remote user authentication scheme. Comput. Electr. Eng. 2011, 37, 869–874. [Google Scholar] [CrossRef]
- Jau-Ji, S.; Lin, C.-W.; Hwang, M.-S. Security enhancement for the timestamp-based password authentication scheme using smart cards. Comput. Secur. 2003, 22, 591–595. [Google Scholar]
- Huang, H.-F.; Chang, H.-W.; Yu, P.-K. Enhancement of Timestamp-based User Authentication Scheme with Smart Card. Int. J. Netw. Secur. 2014, 16, 463–467. [Google Scholar]
- Amin, R.; Maitra, T.; Giri, D.; Srivastava, P.D. Cryptanalysis and Improvement of an RSA Based Remote User Authentication Scheme Using Smart Card. Wirel. Pers. Commun. 2017, 96, 4629–4659. [Google Scholar] [CrossRef]
- Pippal, R.S.; Jaidhar, C.D.; Tapaswi, S. Robust Smart Card Authentication Scheme for Multi-server Architecture. Wirel. Pers. Commun. 2013, 72, 729–745. [Google Scholar] [CrossRef]
- Li, X.; Niu, J.; Kumari, S.; Liao, J.; Liang, W. An Enhancement of a Smart Card Authentication Scheme for Multi-server Architecture. Wirel. Pers. Commun. 2015, 80, 175–192. [Google Scholar] [CrossRef]
- Srinivas, J.; Mukhopadhyay, S.; Mishra, D. A Self-Verifiable Password Based Authentication Scheme for Multi-Server Architecture Using Smart Card. Wirel. Pers. Commun. 2017, 96, 6273–6297. [Google Scholar] [CrossRef]
- He, D.; Kumar, N.; Chilamkurti, N. A secure temporal-credential-based mutual authentication and key agreement scheme with pseudo identity for wireless sensor networks. Inf. Sci. Int. J. 2015, 321, 263–277. [Google Scholar] [CrossRef]
- Chang, I.; Lee, T.; Lin, T.; Liu, C. Enhanced two-factor authentication and key agreement using dynamic identities in wireless sensor networks. Sensors 2015, 15, 29841–29854. [Google Scholar] [CrossRef] [PubMed]
- Hsiu-Lien, Y.; Chen, T.H.; Liu, P.C.; Tai-Hoo, K.; Wei, H.W. A secured authentication protocol for wireless sensor networks using elliptic curves cryptography. Sensors 2011, 11, 4767–4779. [Google Scholar]
- Choi, Y.; Lee, D.; Kim, J.; Nam, J.; Won, D. Security enhanced user authentication protocol for wireless sensor networks using elliptic curves cryptography. Sensors 2014, 14, 10081–10106. [Google Scholar] [CrossRef] [PubMed]
- Shi, W.; Gong, P. A new user authentication protocol for wireless sensor networks using elliptic curves cryptography. Int. J. Distrib. Sens. Netw. 2013, 2013, 51–59. [Google Scholar] [CrossRef]
- Jiang, Q.; Ma, J.; Lu, X.; Tian, Y. An efficient two-factor user authentication scheme with unlinkability for wireless sensor networks. Peer-to-Peer Netw. Appl. 2015, 8, 1070–1081. [Google Scholar] [CrossRef]
- Jung, J.; Moon, J.; Lee, D.; Won, D. Efficient and security enhanced anonymous authentication with key agreement scheme in wireless sensor networks. Sensors 2017, 17, 644. [Google Scholar] [CrossRef] [PubMed]
- Park, Y.; Park, Y. Three-factor user authentication and key agreement using elliptic curve cryptosystem in wireless sensor networks. Sensors 2016, 16, 2123. [Google Scholar] [CrossRef] [PubMed]
- Wang, D.; Li, W.; Wang, P. Measuring Two-Factor Authentication Schemes for Real-Time Data Access in Industrial Wireless Sensor Networks. IEEE Trans. Ind. Inform. 2018. [Google Scholar] [CrossRef]
- Wang, D.; Wang, P. On the Anonymity of Two-Factor Authentication Schemes for Wireless Sensor Networks: Attacks, Principle and Solutions. Comput. Netw. 2014, 73, 41–57. [Google Scholar] [CrossRef]
- Wang, D.; Wang, P. Understanding security failures of two-factor authentication schemes for real-time applications in hierarchical wireless sensor networks. Ad Hoc Netw. 2014, 20, 1–15. [Google Scholar] [CrossRef]
- Menezes, A.J. Elliptic Curve Public Key Cryptosystems; Kluwer Academic Publishers: Boston, MA, USA, 1993. [Google Scholar]
- Wang, D.; Wang, P. Two birds with one stone: Two-factor authentication with security beyond conventional bound. IEEE Trans. Depend. Secur. Comput. 2016. [Google Scholar] [CrossRef]
- Kocher, P.; Jaffe, J.; Jun, B. Differential power analysis. Adv. Cryptol. 1999, 1666, 388–397. [Google Scholar]
- Eisenbarth, T.; Kasper, T.; Moradi, A.; Paar, C.; Salmasizadeh, M.; Shalmani, M.T. On the power of power analysis in the. real world: A complete break of the KeeLoq code hopping scheme. In Advances in Cryptology-CRYPTO; Lecture Notes in Computer Science; Springer: Berlin, Germany, 2008; Volume 5157, pp. 203–220. [Google Scholar]
- Messerges, T.S.; Dabbish, E.A.; Sloan, R.H. Examining smart-card security under the threat of power analysis attacks. IEEE Trans. Comput. 2002, 51, 541–552. [Google Scholar] [CrossRef]
- Castiglione, A.; De Santis, A.; Castiglione, A.; Palmieri, F. An Efficient and Transparent One-Time Authentication Protocol with Non-interactive Key Scheduling and Update. AINA 2014, 351–358. [Google Scholar] [CrossRef]
- Wang, D.; Wang, N.; Wang, P.; Qing, S. Preserving privacy for free: Efficient and provably secure two-factor authentication scheme with user anonymity. Inf. Sci. 2015, 321, 162–178. [Google Scholar] [CrossRef]
- Wang, D.; Zhang, Z.; Wang, P. Targeted online password guessing: An underestimated threat. Proc. ACM CCS 2016, 16, 1242–1254. [Google Scholar]
- Wang, D.; Wang, P. On the implications of Zipf’s law in passwords. In Proceedings of the 21st European Symposium on Research in Computer Security, Heraklion, Greece, 26–30 September 2016; pp. 11–131. [Google Scholar]
- Wang, D.; Cheng, H.; Wang, P.; Huang, X.; Jian, G. Zipf’s Law in Passwords. IEEE Trans. Inform. Forensics Secur. 2017, 12, 2776–2791. [Google Scholar] [CrossRef]
- Syverson, P.F.; Cervesato, I. The Logic of Authentication Protocols; FOSAD: Bertinoro, Italy, 2000; pp. 63–136. [Google Scholar]
- Burrow, M.; Abadi, M.; Needham, R.M. A logic of authentication. ACM Trans. Comput. Syst. 1990, 8, 18–36. [Google Scholar] [CrossRef]
- Arshad, H.; Nikooghadam, M. An efficient and secure authentication and key agreement scheme for session initiation protocol using ECC. Multimed. Tools Appl. 2014, 75, 1–17. [Google Scholar] [CrossRef]
- Kilinc, H.; Yanik, T. A survey of SIP authentication and key agreement schemes. IEEE Commun. Surv. Tutor. 2013. [Google Scholar] [CrossRef]
| Symbol | Description | Symbol | Description |
|---|---|---|---|
| Registration center | Server | ||
| User | Smart card of | ||
| Identification of user | Password belonging to user | ||
| Random numbers of | p | Large prime | |
| Public key of | Private key of | ||
| Random number of | ⊕ | The bitwise XOR operation | |
| The string concatenation operation | One-way hash function | ||
| The malicious adversary | Session key belonging to and |
| Symbol | Description |
|---|---|
| A has trust on X | |
| A acquires/observes X | |
| A sends X X (or A once called) | |
| A regulates X | |
| X is fresh | |
| A and B utilize shared key K for communication | |
| use K as key to compute hash values of X and Y | |
| X is exclusive or-ed with K |
| Rule | Description |
|---|---|
| , |
| Symbol | ||||
|---|---|---|---|---|
| Time | ms | ms | ms | ms |
| Schemes | Awasthi et al. [23] | Huang et al. [25] | Amin et al. [26] | Pippal et al. [27] | Li et al. [28] | Srinivas et al. [29] | Proposed Scheme | |
|---|---|---|---|---|---|---|---|---|
| Features | ||||||||
| No | No | No | No | No | No | Yes | ||
| No | No | No | No | No | No | Yes | ||
| No | No | No | No | No | No | Yes | ||
| No | No | Yes | No | No | Yes | Yes | ||
| No | No | No | No | No | No | Yes | ||
| No | Yes | Yes | No | No | Yes | Yes | ||
| Yes | Yes | Yes | Yes | Yes | Yes | Yes | ||
| N/A | N/A | Yes | Yes | Yes | Yes | Yes | ||
| Yes | Yes | Yes | Yes | Yes | Yes | Yes | ||
| No | Yes | Yes | No | No | Yes | Yes | ||
| No | No | Yes | No | No | Yes | Yes | ||
| N/A | N/A | No | Yes | Yes | Yes | Yes | ||
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Xu, G.; Qiu, S.; Ahmad, H.; Xu, G.; Guo, Y.; Zhang, M.; Xu, H. A Multi-Server Two-Factor Authentication Scheme with Un-Traceability Using Elliptic Curve Cryptography. Sensors 2018, 18, 2394. https://doi.org/10.3390/s18072394
Xu G, Qiu S, Ahmad H, Xu G, Guo Y, Zhang M, Xu H. A Multi-Server Two-Factor Authentication Scheme with Un-Traceability Using Elliptic Curve Cryptography. Sensors. 2018; 18(7):2394. https://doi.org/10.3390/s18072394
Chicago/Turabian StyleXu, Guosheng, Shuming Qiu, Haseeb Ahmad, Guoai Xu, Yanhui Guo, Miao Zhang, and Hong Xu. 2018. "A Multi-Server Two-Factor Authentication Scheme with Un-Traceability Using Elliptic Curve Cryptography" Sensors 18, no. 7: 2394. https://doi.org/10.3390/s18072394
APA StyleXu, G., Qiu, S., Ahmad, H., Xu, G., Guo, Y., Zhang, M., & Xu, H. (2018). A Multi-Server Two-Factor Authentication Scheme with Un-Traceability Using Elliptic Curve Cryptography. Sensors, 18(7), 2394. https://doi.org/10.3390/s18072394





