Performance Evaluation of Relay Selection Schemes in Beacon-Assisted Dual-Hop Cognitive Radio Wireless Sensor Networks under Impact of Hardware Noises
Abstract
1. Introduction
1.1. Motivations
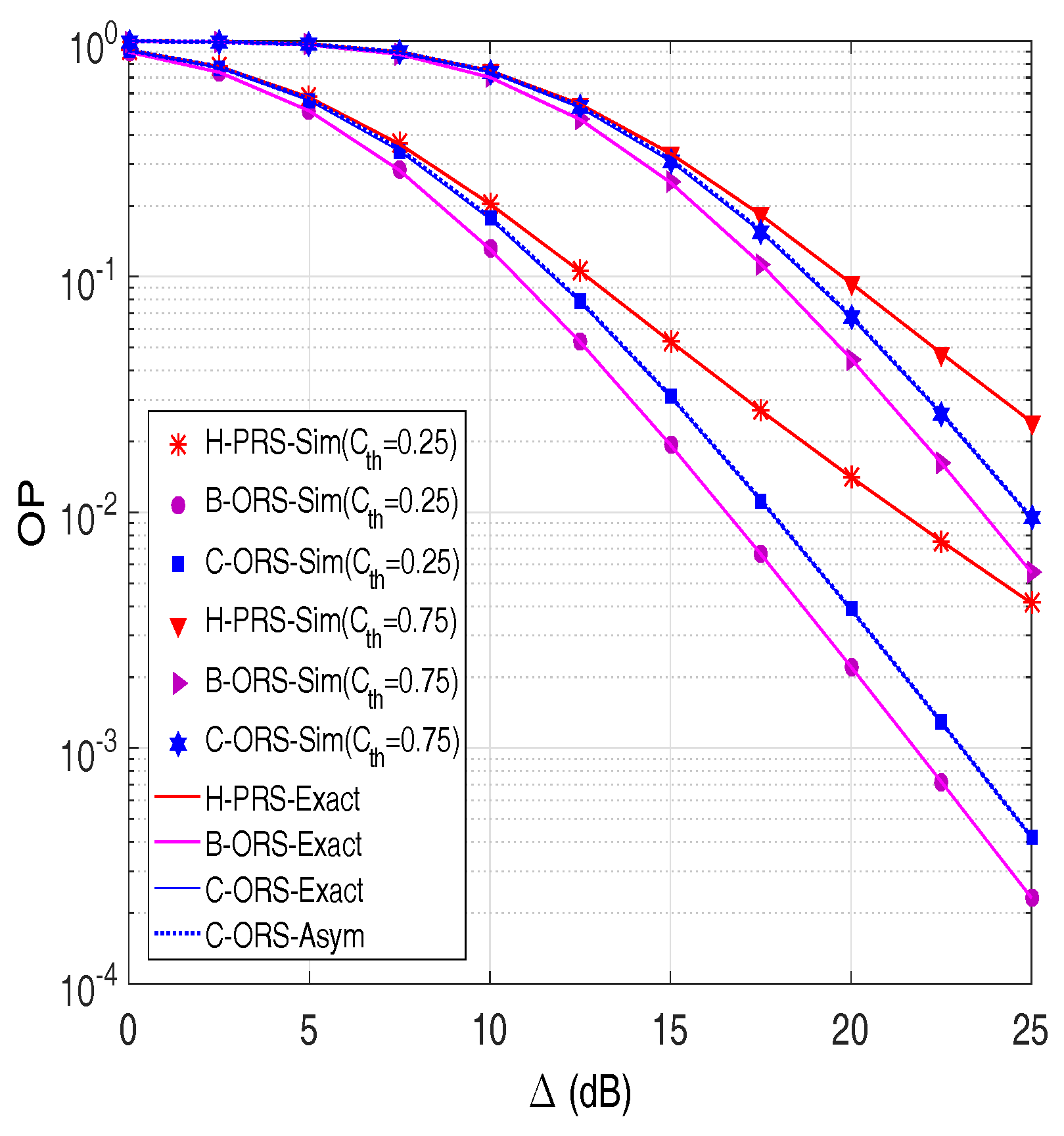
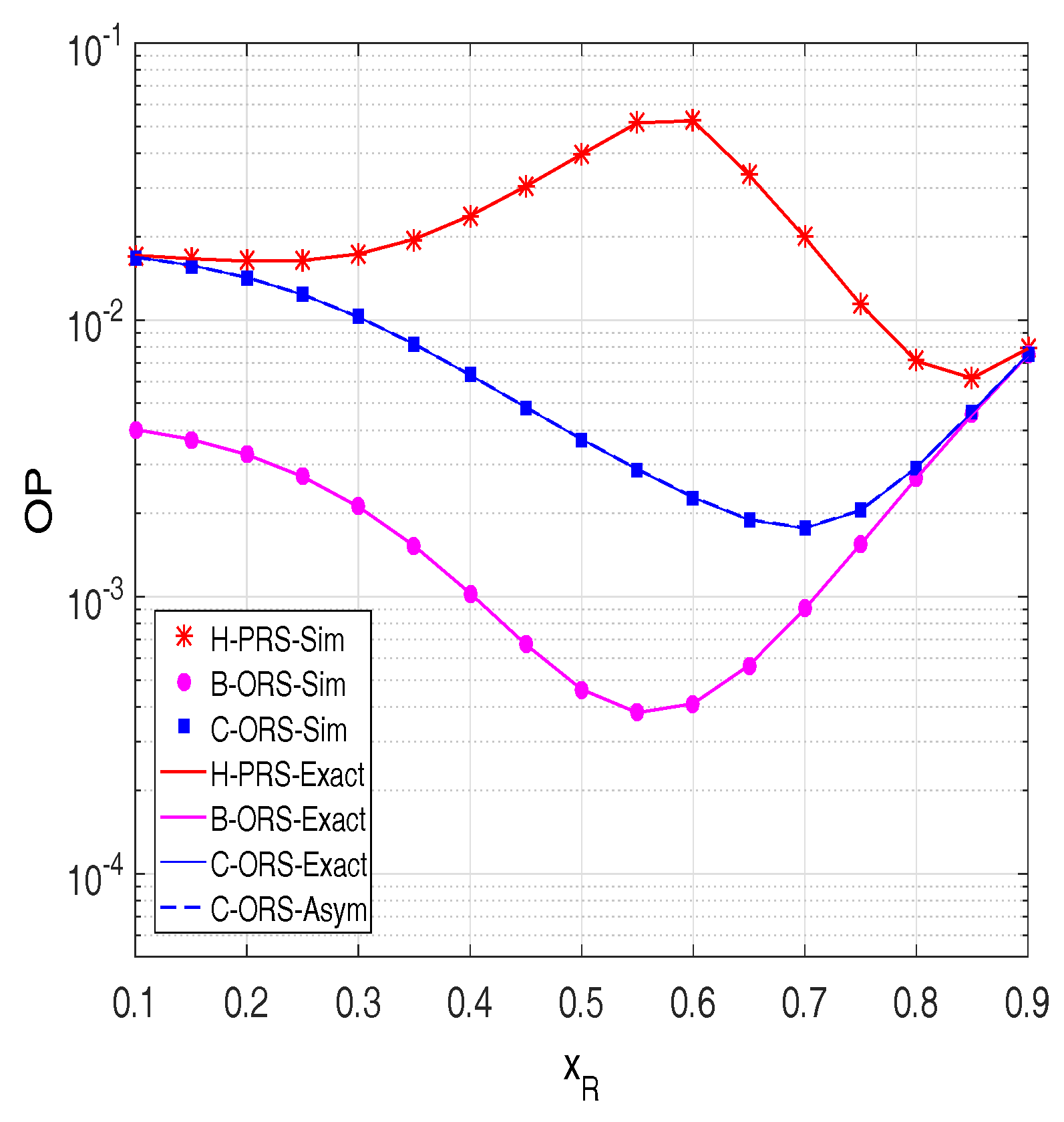
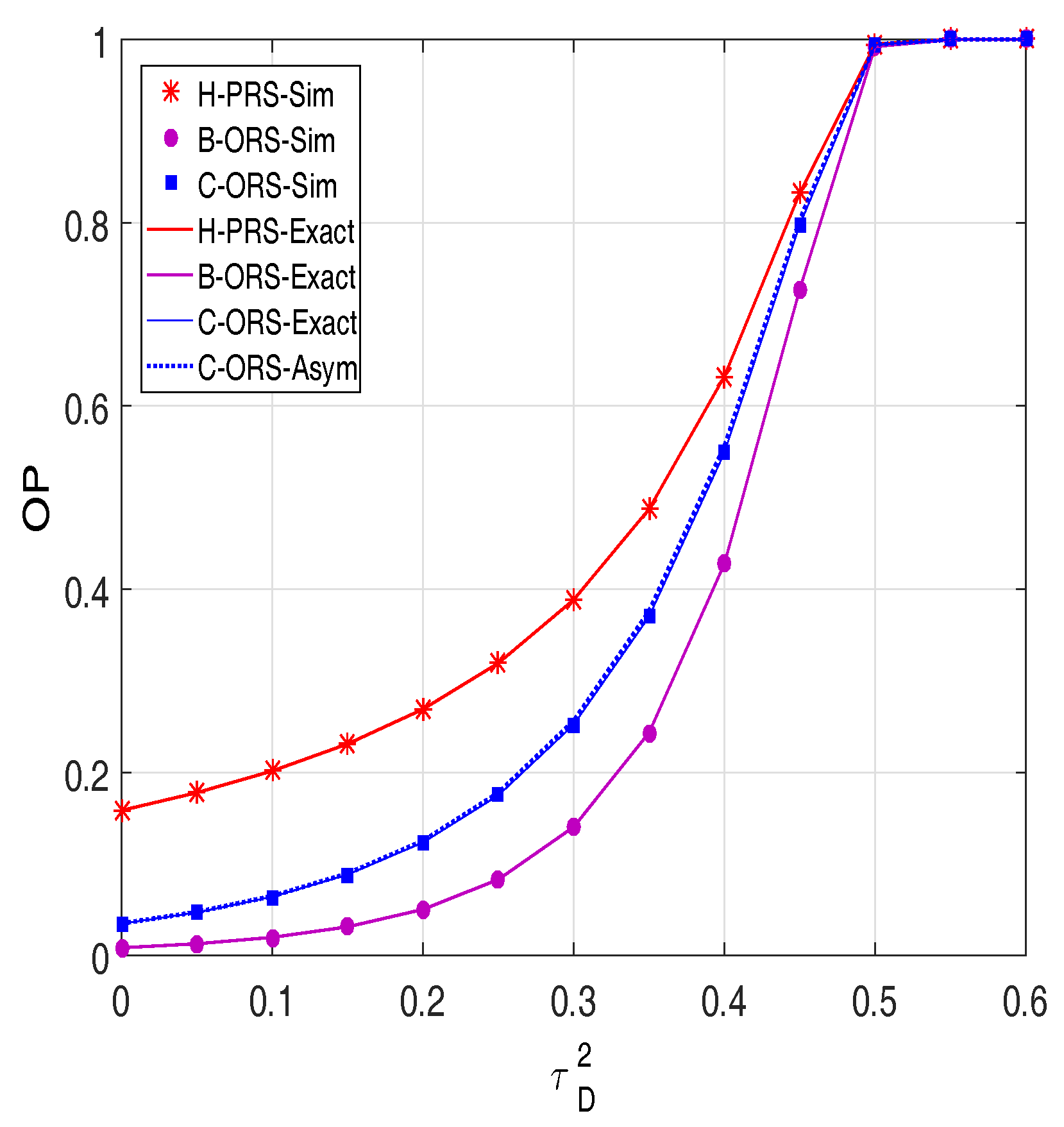
1.2. Contributions
- Three dual-hop DF cooperative relaying protocols are proposed. In H-PRS, the best relay can be selected by using the CSIs of the first or second hop. On the other hand, C-ORS and B-ORS select a relay that has the highest e2e channel gain and the highest e2e SNRs, respectively, to convey the data transmission from secondary source to secondary destination.
- It is noteworthy that the PB-assisted cooperative CR relaying systems using H-PRS, B-ORS, or C-ORS have their own mathematical analysis challenges since the energy harvested from the beacon and the interference constraint of the primary users (PUs) affect the transmit power of the secondary source and relays. Moreover, due to the correlation between SNRs of the first and second hop, the analysis of the performance in the C-ORS scheme becomes much more challenging, compared with that in the H-PRS and B-ORS schemes.
- Assuming independently and identically distributed (i.i.d.) Rayleigh fading environment, exact closed-form expressions and asymptotic analysis of OP and TP for H-PRS, B-ORS and C-ORS are derived. Monte Carlo simulations are performed to validate our derivations.
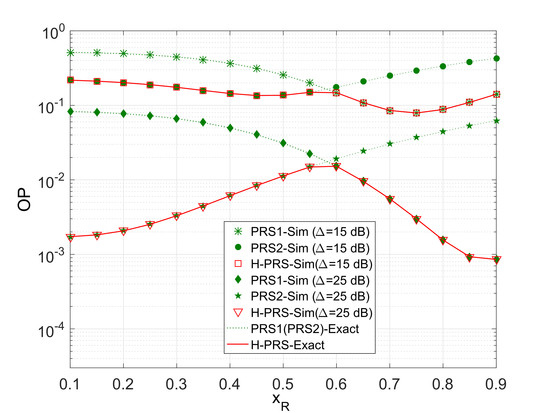
2. System Model
2.1. Hardware Impairments
2.2. Energy Harvesting Phase
2.3. Transmit Power Formulation
2.4. Relay Selection Methods
2.4.1. Hybrid Partial Relay Selection (H-PRS)
2.4.2. Best Opportunistic Relay Selection (B-ORS)
2.4.3. Conventional Opportunistic Relay Selection (C-ORS)
3. Performance Evaluation
3.1. Outage Probability
- Case 1:
- Case 2:Similarly, we obtainNow, with and , the following are respectively obtained:
3.2. Throughput
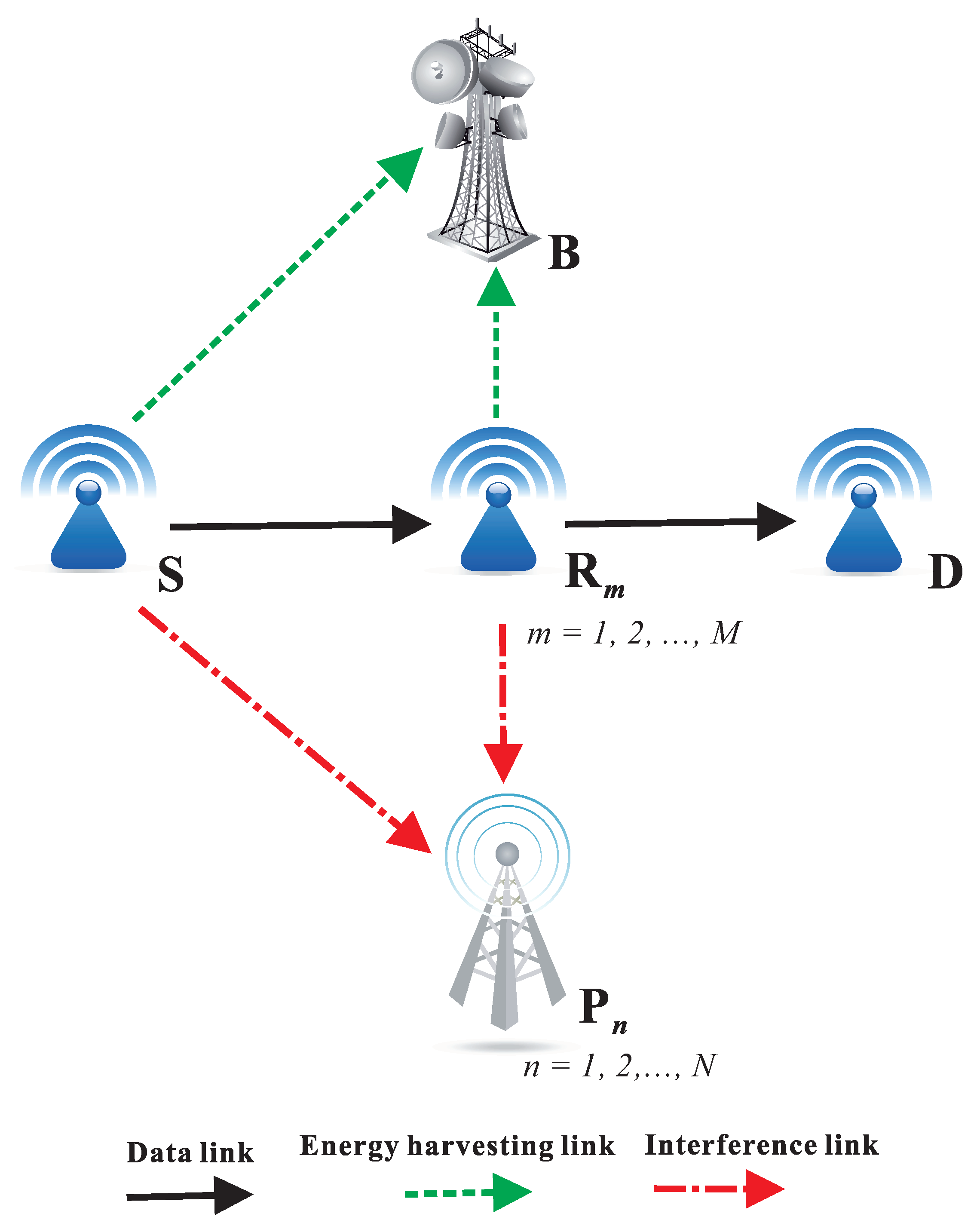
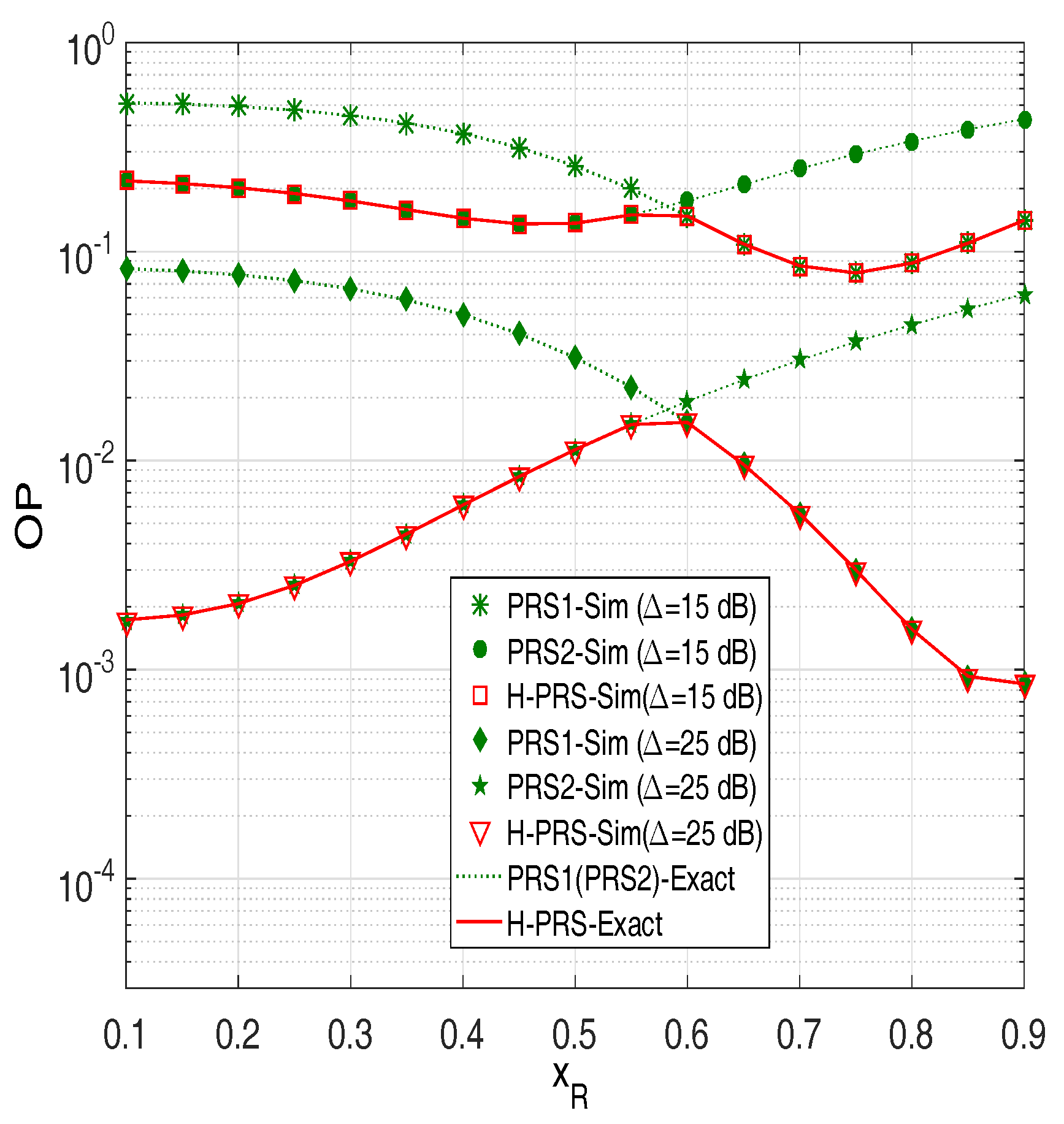
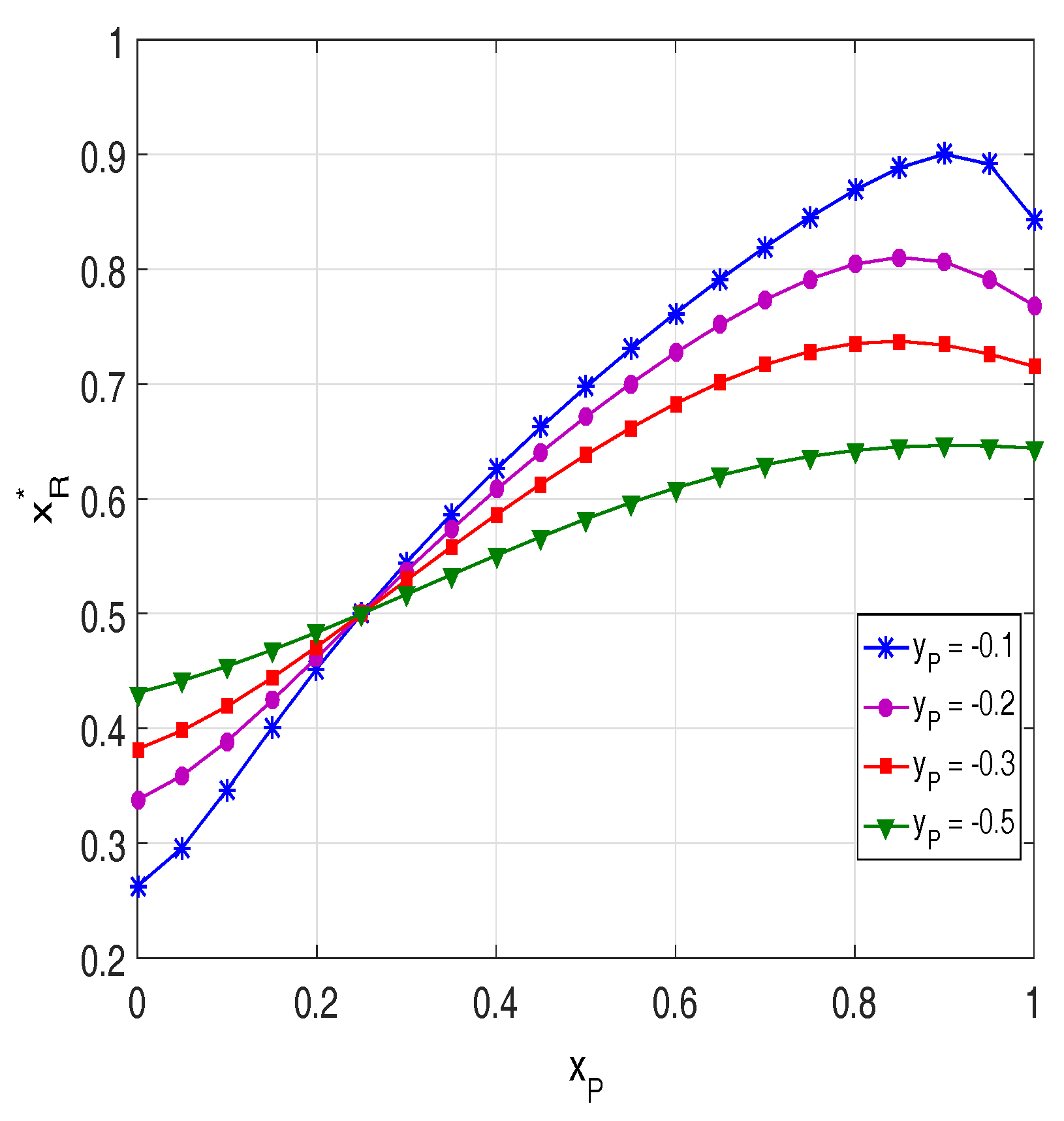
4. Simulation Results
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Lin, H.; Bai, D.; Gao, D.; Liu, Y. Maximum data collection rate routing protocol based on topology control for rechargeable wireless sensor networks. Sensors 2016, 16, 1201. [Google Scholar] [CrossRef] [PubMed]
- Wang, Z.; Zeng, P.; Zhou, M.; Li, D.; Wang, J. Cluster-based maximum consensus time synchronization for industrial wireless sensor networks. Sensors 2017, 17, 141. [Google Scholar] [CrossRef] [PubMed]
- Jiang, L.; Tian, H.; Xing, Z.; Wang, K.; Zhang, K.; Maharjan, S.; Gjessing, S.; Zhang, Y. Social-aware energy harvesting device-to-device communications in 5G networks. IEEE Wirel. Commun. 2016, 23, 20–27. [Google Scholar] [CrossRef]
- Yadav, A.; Goonewardena, M.; Ajib, W.; Dobre, O.A.; Elbiaze, H. Energy management for energy harvesting wireless sensors with adaptive retransmission. IEEE Trans. Commun. 2017, 65, 5487–5498. [Google Scholar] [CrossRef]
- Paradiso, J.A.; Starner, T. Energy scavenging for mobile and wireless electronics. IEEE Pervasive Comput. 2005, 4, 18–27. [Google Scholar] [CrossRef]
- Raghunathan, V.; Ganeriwal, S.; Srivastava, M. Emerging techniques for long lived wireless sensor networks. IEEE Commun. Mag. 2006, 44, 108–114. [Google Scholar] [CrossRef]
- Hieu, T.D.; Dung, L.T.; Kim, B.S. Stability-aware geographic routing in energy harvesting wireless sensor networks. Sensors 2016, 16, 696. [Google Scholar] [CrossRef] [PubMed]
- Varshney, L.R. Transporting Information and Energy Simultaneously. In Proceedings of the IEEE International Symposium on Information Theory (ISIT), Toronto, ON, Canada, 6–11 July 2008; pp. 1612–1616. [Google Scholar]
- Zhang, R.; Ho, C.K. MIMO broadcasting for simultaneous wireless information and power transfer. IEEE Trans. Wirel. Commun. 2013, 12, 1989–2001. [Google Scholar] [CrossRef]
- Zhou, X.; Zhang, R.; Ho, C.K. Wireless information and power transfer: architecture design and rate-energy trade-off. IEEE Trans. Commun. 2013, 61, 4754–4767. [Google Scholar] [CrossRef]
- Nasir, A.A.; Zhou, X.; Durrani, S.; Kennedy, R.A. Relaying protocols for wireless energy harvesting and information processing. IEEE Trans. Wirel. Commun. 2013, 12, 3622–3636. [Google Scholar] [CrossRef]
- Shi, Q.; Liu, L.; Xu, W.; Zhang, R. Joint transmit beamforming and receive power splitting for MISO SWIPT systems. IEEE Trans. Wirel. Commun. 2014, 13, 3269–3280. [Google Scholar] [CrossRef]
- Krikidis, I. Simultaneous information and energy transfer in large scale networks with/without relaying. IEEE Trans. Commun. 2014, 62, 900–912. [Google Scholar] [CrossRef]
- Huang, K.; Lau, V.K.N. Enabling wireless power transfer in cellular networks: Architecture, modeling and deployment. IEEE Trans. Wirel. Commun. 2014, 13, 902–912. [Google Scholar] [CrossRef]
- Le, N.P. Throughput analysis of power-beacon assisted energy harvesting wireless systems over non-identical Nakagami-m fading channels. IEEE Commun. Lett. 2018, 22, 840–843. [Google Scholar] [CrossRef]
- Liu, Y.; Wang, L.; Zaidi, S.A.R.; Elkashlan, M.; Duong, T.Q. Secure D2D communication in large-scale cognitive cellular networks: A wireless power transfer model. IEEE Trans. Commun. 2016, 64, 329–342. [Google Scholar] [CrossRef]
- Doan, T.X.; Hoang, T.M.; Duong, T.Q.; Ngo, H.Q. Energy harvesting-based D2D communications in the presence of interference and ambient RF sources. IEEE Access 2017, 5, 5224–5234. [Google Scholar] [CrossRef]
- Tehrani, M.N.; Uysal, M.; Yanikomeroglu, H. Device-to-device communication in 5G cellular networks: Challenges, solutions, and future directions. IEEE Commun. Mag. 2014, 52, 86–92. [Google Scholar] [CrossRef]
- Van, N.T.; Duy, T.T.; Hanh, T.; Bao, V.N.Q. Outage Analysis of Energy-Harvesting Based Multihop Cognitive Relay Networks with Multiple Primary Receivers and Multiple Power Beacons. In Proceedings of the International Symposium on Antennas and Propagation (ISAP), Phuket, Thailand, 30 October–2 November 2017; pp. 1–2. [Google Scholar]
- Van, N.T.; Do, T.N.; Bao, V.N.Q.; An, B. Performance analysis of wireless energy harvesting multihop cluster-based networks over Nakgami-m fading channels. IEEE Access 2018, 6, 3068–3084. [Google Scholar] [CrossRef]
- Hieu, T.D.; Duy, T.T.; Choi, S.G. Performance Enhancement for Harvest-to-Transmit Cognitive Multi-Hop Networks with Best Path Selection Method Under Presence of Eavesdropper. In Proceedings of the IEEE 20th International Conference on Advanced Communication Technology (ICACT), Chuncheon-si, Gangwon-do, Korea, 11–14 February 2018; pp. 323–328. [Google Scholar]
- Hieu, T.D.; Duy, T.T.; Kim, B.S. Performance enhancement for multi-hop harvest-to-transmit WSNs with path-selection methods in presence of eavesdroppers and hardware noises. IEEE Sens. J. 2018, 18, 5173–5186. [Google Scholar] [CrossRef]
- Mitola, J.; Maguire, G.Q. Cognitive radio: Making software radios more personal. IEEE Pers. Commun. 1999, 6, 13–18. [Google Scholar] [CrossRef]
- Kong, F.; Cho, J.; Lee, B. Optimizing spectrum sensing time with adaptive sensing interval for energy-efficient CRSNs. IEEE Sens. J. 2017, 17, 7578–7588. [Google Scholar] [CrossRef]
- Dung, L.T.; Hieu, T.D.; Choi, S.G.; Kim, B.S.; An, B. Impact of beamforming on the path connectivity in cognitive radio ad-hoc networks. Sensors 2017, 17, 690. [Google Scholar] [CrossRef] [PubMed]
- Joshi, G.P.; Nam, S.Y.; Kim, S.W. Cognitive radio wireless sensor networks: Applications, challenges and research trends. Sensors 2013, 13, 11196–11228. [Google Scholar] [CrossRef] [PubMed]
- Wu, Y.; Cardei, M. Multi-channel and cognitive radio approaches for wireless sensor networks. Comput. Commun. 2016, 94, 30–45. [Google Scholar] [CrossRef]
- Guo, Y.; Kang, G.; Zhang, N.; Zhou, W.; Zhang, P. Outage performance of relay-assisted cognitive-radio system under spectrum sharing constraints. Electron. Lett. 2010, 46, 182–183. [Google Scholar] [CrossRef]
- Lee, J.; Wang, H.; Andrews, J.G.; Hong, D. Outage probability of cognitive relay networks with interference constraints. IEEE Trans. Wirel. Commun. 2011, 10, 390–395. [Google Scholar] [CrossRef]
- Laneman, J.N.; Tse, D.N.; Wornell, G.W. Cooperative diversity in wireless networks: Efficient protocols and outage behavior. IEEE Trans. Inf. Theory 2004, 50, 3062–3080. [Google Scholar] [CrossRef]
- Bletsas, A.; Khisti, A.; Reed, D.P.; Lippman, A. A simple cooperative diversity method based on network path selection. IEEE J. Sel. Areas Commun. 2006, 24, 659–672. [Google Scholar] [CrossRef]
- Dongyang, X.; Pinyi, R.; Qinghe, D.; Li, S. Joint dynamic clustering and user scheduling for downlink cloud radio access network with limited feedback. China Commun. 2015, 12, 147–159. [Google Scholar]
- Dongyang, X.; Du, Q.; Ren, P.; Sun, L.; Zhao, W.; Hu, Z. AF-Based CSI Feedback for User Selection in Multi-User MIMO Systems. In Proceedings of the IEEE Global Communication Conference (GLOBECOM), San Diego, CA, USA, 8–12 December 2015; pp. 1–6. [Google Scholar]
- Tourki, K.; Yang, H.C.; Alouini, M.S. Accurate outage analysis of incremental decode-and-forward opportunistic relaying. IEEE Trans. Wirel. Commun. 2011, 10, 1021–1025. [Google Scholar] [CrossRef]
- Krikidis, I.; Thompson, J.; McLaughlin, S.; Goertz, N. Amplify-and-forward with partial relay selection. IEEE Commun. Lett. 2008, 12, 235–237. [Google Scholar] [CrossRef]
- Ding, H.; Ge, J.; da Costa, D.B.; Jiang, Z. Diversity and coding gains of fixed-gain amplify-and-forward with partial relay selection in Nakagami-m fading. IEEE Commun. Lett. 2010, 14, 734–736. [Google Scholar] [CrossRef]
- Duy, T.T.; Kong, H.Y. Performance analysis of incremental amplify-and-forward relaying protocols with nth best partial relay selection under interference constraint. Wirel. Pers. Commun. 2013, 71, 2741–2757. [Google Scholar] [CrossRef]
- Fredj, K.B.; Aissa, S. Performance of amplify-and-forward systems with partial relay selection under spectrum-sharing constraints. IEEE Trans. Wirel. Commun. 2012, 11, 500–504. [Google Scholar] [CrossRef]
- Sharma, P.K.; Upadhyay, P.K. Cognitive relaying with transceiver hardware impairments under interference constraints. IEEE Commun. Lett. 2016, 20, 820–823. [Google Scholar] [CrossRef]
- Tourki, K.; Qaraqe, K.A.; Alouini, M.-S. Outage analysis for underlay cognitive networks using incremental regenerative relaying. IEEE Trans. Veh. Technol. 2013, 62, 721–734. [Google Scholar] [CrossRef]
- Hakim, H.; Boujemaa, H.; Ajib, W. Performance comparison between adaptive and fixed transmit power in underlay cognitive radio networks. IEEE Trans. Commun. 2013, 61, 4836–4846. [Google Scholar] [CrossRef]
- Hoang, D.T.; Niyato, D.; Wang, P.; Kim, D.I. Opportunistic channel access and RF energy harvesting in cognitive radio networks. IEEE J. Sel. Areas Commun. 2014, 32, 2039–2052. [Google Scholar] [CrossRef]
- Hoang, D.T.; Niyato, D.; Wang, P.; Kim, D.I. Performance analysis of wireless energy harvesting cognitive radio networks under smart jamming attacks. IEEE Trans. Cogn. Commun. Netw. 2015, 1, 200–216. [Google Scholar] [CrossRef]
- Nguyen, D.K.; Jayakody, D.N.K.; Chatzinotas, S.; Thompson, J.S.; Li, J. Wireless energy harvesting assisted two-way cognitive relay networks: Protocol design and performance analysis. IEEE Access 2017, 5, 21447–21460. [Google Scholar] [CrossRef]
- Xu, C.; Zheng, M.; Liang, W.; Yu, H.; Liang, Y.C. Outage performance of underlay multihop cognitive relay networks with energy harvesting. IEEE Commun. Lett. 2016, 20, 1148–1151. [Google Scholar] [CrossRef]
- Xu, C.; Zheng, M.; Liang, W.; Yu, H.; Liang, Y.C. End-to-end throughput maximization for underlay multi-hop cognitive radio networks with RF energy harvesting. IEEE Trans. Wirel. Commun. 2017, 16, 3561–3572. [Google Scholar] [CrossRef]
- Mokhtar, M.; Gomaa, A.; Al-Dhahir, N. OFDM AF relaying under I/Q imbalance: Performance analysis and baseband compensation. IEEE Trans. Commun. 2013, 61, 1304–1313. [Google Scholar] [CrossRef]
- Bjornson, E.; Matthaiou, M.; Debbah, M. A new look at dual-hop relaying: Performance limits with hardware impairments. IEEE Trans. Commun. 2013, 61, 4512–4525. [Google Scholar] [CrossRef]
- Duy, T.T.; Duong, T.Q.; da Costa, D.B.; Bao, V.N.Q.; Elkashlan, M. Proactive relay selection with joint impact of hardware impairment and co-channel interference. IEEE Trans. Commun. 2015, 63, 1594–1606. [Google Scholar] [CrossRef]
- Peng, C.; Li, F.; Liu, H. Wireless energy harvesting two-way relay networks with hardware impairments. Sensors 2017, 17, 2604. [Google Scholar] [CrossRef] [PubMed]
- Zhang, C.; Ge, J.; Li, J.; Gong, F.; Ji, Y.; Farah, M.A. Energy efficiency and spectral efficiency trade-off for asymmetric two-way AF relaying with statistical CSI. IEEE Trans. Veh. Technol. 2016, 65, 2833–2839. [Google Scholar] [CrossRef]
- Choi, J. Joint rate and power allocation for NOMA with statistical CSI. IEEE Trans. Commun. 2017, 65, 4519–4528. [Google Scholar] [CrossRef]
- Gradshten, I.S.; Ryzhik, I.M. Table of Integrals, Series and Products, 7th ed.; Academic Press: San Diego, CA, USA, 2007. [Google Scholar]


© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Hieu, T.D.; Duy, T.T.; Dung, L.T.; Choi, S.G. Performance Evaluation of Relay Selection Schemes in Beacon-Assisted Dual-Hop Cognitive Radio Wireless Sensor Networks under Impact of Hardware Noises. Sensors 2018, 18, 1843. https://doi.org/10.3390/s18061843
Hieu TD, Duy TT, Dung LT, Choi SG. Performance Evaluation of Relay Selection Schemes in Beacon-Assisted Dual-Hop Cognitive Radio Wireless Sensor Networks under Impact of Hardware Noises. Sensors. 2018; 18(6):1843. https://doi.org/10.3390/s18061843
Chicago/Turabian StyleHieu, Tran Dinh, Tran Trung Duy, Le The Dung, and Seong Gon Choi. 2018. "Performance Evaluation of Relay Selection Schemes in Beacon-Assisted Dual-Hop Cognitive Radio Wireless Sensor Networks under Impact of Hardware Noises" Sensors 18, no. 6: 1843. https://doi.org/10.3390/s18061843
APA StyleHieu, T. D., Duy, T. T., Dung, L. T., & Choi, S. G. (2018). Performance Evaluation of Relay Selection Schemes in Beacon-Assisted Dual-Hop Cognitive Radio Wireless Sensor Networks under Impact of Hardware Noises. Sensors, 18(6), 1843. https://doi.org/10.3390/s18061843