1. Introduction
Underwater sensor networks (UWSNs) have great potential in many areas, mainly in environmental monitoring, with applications in the fields of oceanography, defense and security, and fisheries, which include pollution control, the gathering of scientific data, or intruder’s surveillance. Image transmission from remote sites is the most envisaged capability of UWSNs [
1,
2,
3]. One important case is monitoring the behavior of river-fed sediment plumes in estuaries and deltas [
4], because of their influence on water quality and the environment.
UWSNs are long-overdue to reduce the cost of traditional monitoring methods, like campaigns of CTD (Conductivity-Temperature-Depth) and turbidity measurements on board ships. These measurement campaigns are also affected by bad weather, e.g., storms, which are frequently the reason for the campaigns. Furthermore, the data gathered and sent by the network can be available near real time in an on land data center for later processing.
Nowadays, using optical wireless communications for the underwater medium is only possible up to a few meters [
5], and even less if radiofrequency waves are used instead, while acoustic waves can reach distances in the range of kilometers. Therefore, the communication channel chosen in this work is the underwater acoustic channel (UAC), which has several important limitations: the low propagation speed of the acoustic waves, the limited available bandwidth, the high absorption, and the frequency-selective fading. The former causes underwater communications to suffer from a high latency, while the others only allow for transmission with a limited signaling rate. Special care must be taken in time scheduling to achieve a reasonable throughput in the network operation. In this paper, we cope with the latency so that it will not play against throughput.
The first step to achieve a high throughput must be to employ a time-efficient MAC layer. In this work, the Time-Division Multiple Access (TDMA) operation has been adopted, since it is the most time-efficient technique [
6]. Nevertheless, TDMA requires good scheduling to organize the node transmissions. We exploit the large propagation delay to choose the best scheduling, as we will see later in
Section 2.
Many TDMA techniques have already been presented and assessed in the literature when concerning the MAC layer in UWSNs [
7]. A recent paper that also provides an exhaustive survey of the different TDMA variants in this type of networks is [
8]. For example, the protocol named the Acoustic Communication network for Monitoring of Environment (ACMENet) [
9], divides sensor nodes into two types: master and slave nodes, similar to protocol SBMAC [
10]. In these protocols, propagation delays are measured and the resulting values are used to avoid packet collisions. Although slave nodes in the ACMENet protocol have a simple design, the master node is complex and can be a problem when the network size grows. In [
11], protocol ST-MAC is designed to overcome the spatial-temporal uncertainty in the TDMA-based MAC scheduling, improving the throughput by means of resolving a conflict graph.
Spatial TDMA (STDMA) was proposed as early as 1985 [
12]. The idea is that two hop links of the network that are far enough apart, i.e., do not interfere each other, can be operating simultaneously. Scheduling is of paramount importance in STDMA networks. Luque-Nieto, et al. [
4] present optimal STDMA scheduling for linear networks where the sink node collects a single packet from every node in one frame. The problem of finding the shortest frame is addressed as a bin packing problem. However, no propagation delay was considered. The long propagation delay of the acoustic waves allows the nodes to overlap their transmissions in time without collisions. The idea of exploiting the time overlapping of travelling waves to increase the throughput in TDMA networks has been already proposed [
6,
13,
14]. It has been successfully applied to several topologies, like a grid mesh of sensors [
15] or in a linear network [
16], by means of dynamic linear programming. Nevertheless, these methods, based on a sequential decision problem slot by slot, are far from easy to implement in networks with a medium/large number of nodes. A new function to obtain a figure of merit of the vector of the states, denoted reward in [
13], must be optimized by iteration for each network size. In these networks, the main drawback is the need to ascertain an efficient and simple algorithm to determine the optimal schedule with low complexity. In the case of a regular spaced linear network, another approach to find an optimal schedule is to analyze the constraints to avoid collisions within the dual space-time domain (location of nodes and time slots) in a geometric 2D lattice chart [
17]. We now show in this work that it is possible to use the 2D space-time lattice to find the best possible schedule (optimal) for a linear network.
A key issue in UWSN is the energy consumed by the nodes. In [
18], a procedure to avoid retransmissions is pointed out by means of transmitting duplicate data through different paths of the network (routing). Nevertheless, this topic is not the focus of the present work. Another key point in UWSNs is the physical topology. We consider a static monitoring network with fixed nodes anchored to the seabed, which is a realistic assumption for a monitoring or surveillance UWSN [
16]. According to the number of nodes, and the area to cover for sensing, we can find the formation ranging from simple isolated linear networks (called string or chain networks) up to clusters of subnetworks linked through special nodes acting as master nodes. In this work, we have chosen a simple case, the multi-hop string network, but under the worst operation conditions: the sink node is located at one end of the string. This fact may create a bottleneck that needs to be overcome. As a consequence, multi-hop TDMA network scheduling has two components: 1) A time schedule to assign transmission slots to nodes and 2) a packet service policy to determine the origin of the packet to be transmitted in a particular time slot. In this paper, scheduling is proposed so that the network performance is optimal in terms of throughput and fairness. In order to obtain the packet end-to-end delay, two services policies are compared: FIFO and Round-Robin.
Probabilistic wireless networks can be modeled and analyzed using process calculus [
19,
20] describes a compositional theory for networks with static topology assuming that communication between nodes is reliable, and applies the theory to routing protocols. Merro, et al. [
21] defines a well-formed network as a network which is node-unique, connected, exposure-consistent, and transmission-consistent. Bugliesi, et al. [
22] describes a framework for the analysis of mobile ad-hoc networks (MANET) and proposes the evaluation of communication interference based on preorders; this work also models the concept of a scheduler in wireless networks. The analysis is carried out for well-formed networks in which active receivers are in the range of exactly one transmitter and transmitters sense the channel beforehand. A similar probabilistic approach is used in [
23] to address connectivity and energy consumption in mobile wireless sensor networks.
Networks like the one analyzed in this work can be modelled as an open Jackson network using queueing theory. Each node is considered a service station that receives as input the packets from the previous node plus its own generated packets [
24]. In our network, however, we can simplify those more general approaches as nodes generate traffic in a deterministic way, and we use spatial TDMA multiplexing [
12] with fixed scheduling. This means that the arrival times at each node are deterministic, as well as the instants of the generation of packets in each node. Thus, we can see our network as a special case of the previous analysis frameworks. These assumptions model a deployable monitoring network where information is sent periodically towards a central facility. Our aim is to identify the schedule and policy that maximize the amount of information that can be received under a fairness constraint.
The rest of the paper is organized as follows.
Section 2 introduces the network model including the operation of the nodes and the collision constraints involved. Then, time scheduling and some related points are addressed, especially the optimal scheduling. A new graphic method to find the optimal scheduling is presented.
Section 3 analyses the network performance for the two service policies considered: FIFO and Round-Robin. Firstly, numerical results for throughput are presented. Secondly, end-to-end packet delay is measured and improved by establishing specific initial conditions. Thirdly, the mean queue length of the nodes is calculated. Finally, concerning the fairness behavior, a discussion about the delivered packet distribution to the Gateway node is presented.
2. Network Model and Operation
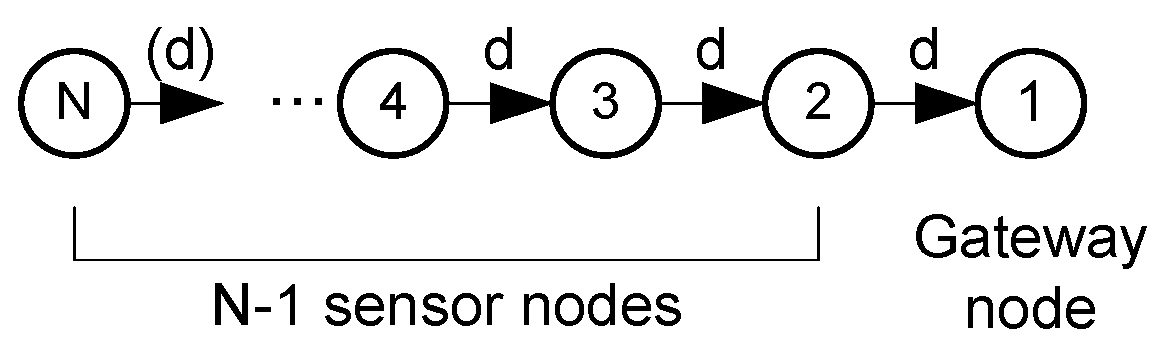
The string network under study is shown in
Figure 1. There are two kinds of nodes: the sensor nodes (numbered from 2 to
) and a single sink node (the Gateway, numbered 1) located at the network edge. The seabed is neither flat nor smooth. Therefore, nodes may not be equally spaced. Nevertheless, the analysis will begin considering that the nodes are equally spaced in terms of the distance
d between each of them and eventually, in
Section 2.2.3, we will consider the general case of unequally spaced nodes.
The sensor nodes provide fixed size data packets (e.g., with environmental measurements) and the Gateway node collects all the packets to forward them to a data center normally located on the water surface or on land, for later processing. The nodes will use a unicast service, so the packets of a node will be routed to the next node toward the Gateway (path in
Figure 1). This multi-hop routing technique has the advantage of saving energy, an important issue in UWSNs.
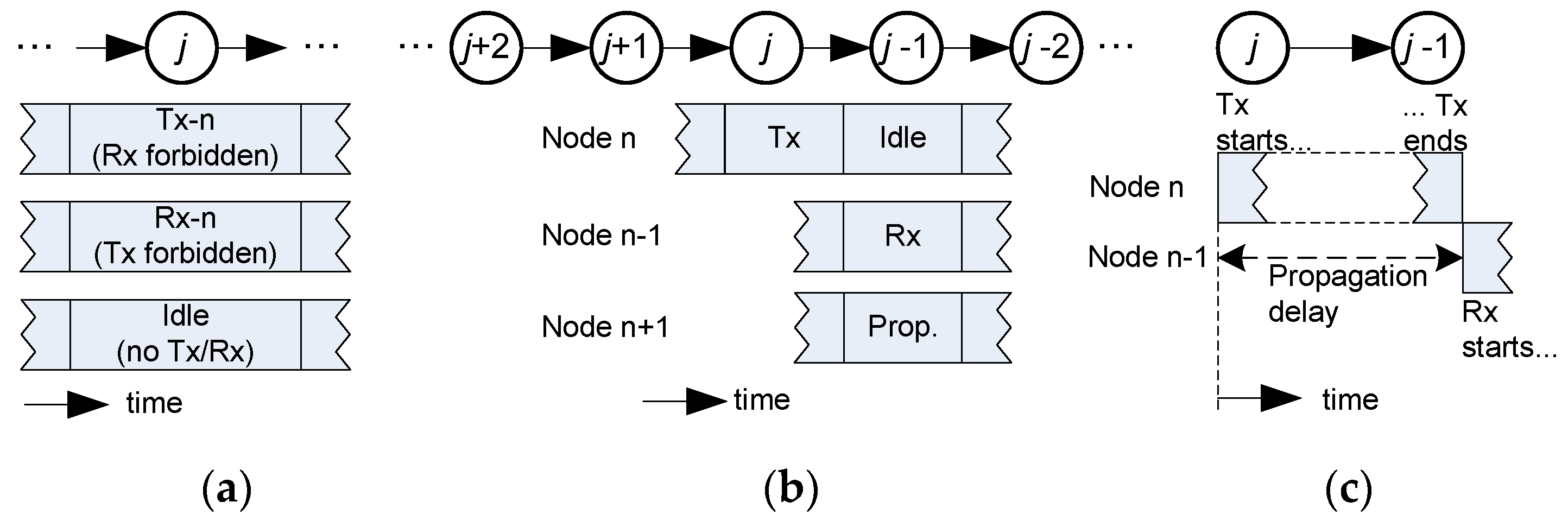
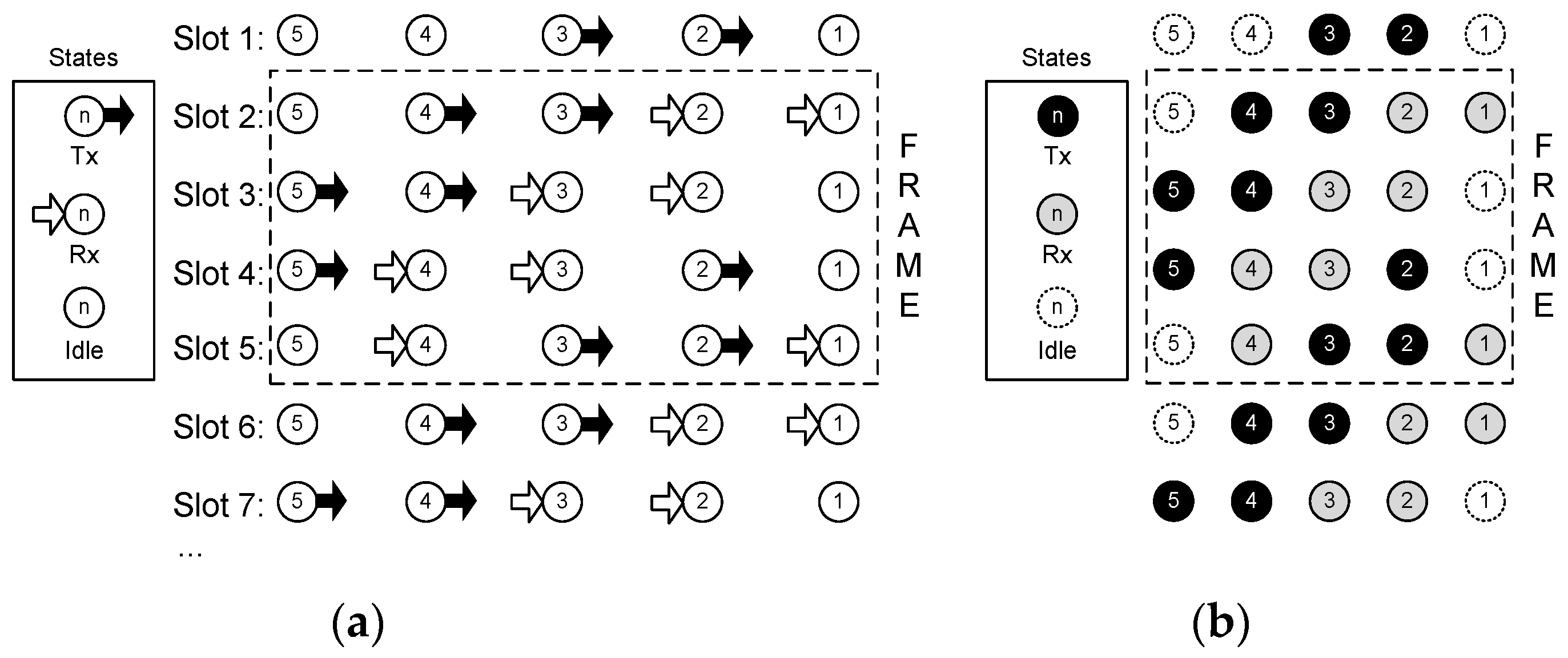
Concerning the communication technique employed, the following considerations are assumed: (i) one-way operation; (ii) non-directive transducers (projectors and hydrophones) with a power range adjusted to a single-hop distance; and (iii) a transmission time, the so-called time slot, equal to the propagation delay to reach the neighbor node. These starting conditions are pointed out in
Figure 2. Because of (i), a sensor node can be in one of three states: transmission, reception, or idle. Condition (ii) allows the acoustic wave to travel in all directions from a transmitting node, reaching every neighbor node in its transmission range, and causing interference. Due to the power control applied to the acoustic modem, it is possible to establish a hop-by-hop relayed operation with simultaneous transmissions from nodes far enough from each other, because the acoustic power received from farther than two hops will be negligible. Power control is currently a mature technology, widely used in wireless systems. Nodes transmit the power strictly needed to reach their respective destination, which substantiates the assumption of negligible interference at the second hop. Condition (iii) ensures that the time slot available to transmit is full of data, and will enhance the throughput obtained.
2.1. Collision Constraints
Let us consider that node
j has to transmit in time slot
t. If the transmission range is one hop (distance
d in
Figure 1), there are three constraints to avoid interference: (i) node
cannot transmit in the previous slot
; (ii) the destination node
cannot transmit in slot
, when it expects to receive the data from node
j; and (iii) nodes
and
cannot transmit simultaneously. The reasons for these constraints are discussed in
Figure 3 with the help of a graphic sketch. Besides that, since the network has a finite size, there are two obvious rules for nodes at both ends: the Gateway (node 1) never transmits to another node in the network, and node
never receives data from another node. These conditions will be considered in
Section 2.2.2 to find valid schedules.
2.2. Time Schedule
Time scheduling in a TDMA network concerns how to assign time slots to nodes for transmission. If the assignment is periodic, the shortest complete set of slots without repetition is the so-called frame. In a TDMA network, a schedule is a periodic sequence of time slots (frame), where every time slot can be assigned to a set of nodes. Due to the constraints mentioned in the previous Section, transmission is not possible during all the time slots in a frame. A first goal in scheduling is to make as many transmissions as possible within a frame to increase the throughput in the network, while keeping the frame as short as possible, avoiding the collisions already mentioned.
2.2.1. Definitions
A schedule can be represented by a matrix
[
19], where element
denotes the state of node
j during time slot
:
when node
will be planned to transmit to node
, and
when node
will be planned to receive from node
. Finally,
means node
is in an idle state.
A schedule has a period T if it repeats every T time slots: . In essence, TDMA has a periodic operation, so our interest will be focused on periodic schedules. Period T is the frame length. We denote by the matrix that represents the schedule in a period.
A perfect schedule is a matrix
with no zero entries (no node has an idle state in the frame). A schedule is called optimal in case of providing maximum throughput. In [
19], it is shown that every network has an optimal schedule that is periodic, so the periodicity is an important feature to search for the optimal schedule. Since it is impossible to find a perfect schedule for a linear array of
nodes [
19], our goal is to find an optimal periodic schedule containing the largest number of transmissions or, which is the same, the smallest number of idle states.
The average throughput
of a periodic schedule
can be calculated as the number of either transmissions or receptions in one frame divided by the frame length [
19,
25]:
where
is the indicator function with value 1 if the logical expression
is true and 0 otherwise.
The constraints shown in
Figure 3 can be mathematically expressed for any discrete time
t as follows:
Equations (2) and (3) mean that a node can only transmit to its down-stream neighbor, Equation (4) states that nodes and cannot transmit simultaneously, and Equations (5) and (6) set the boundary conditions for a finite network: Equation (5) means that the Gateway (node 1) either collects packets from node 2 or remains idle, and Equation (6) means that the upper-stream node never receives packets from other nodes. It is important to note that positive values represent nodes in a transmission state, negative values represent nodes in a reception state, and zero means idle. Since a transmission is always associated with a reception, there will be as many positive valued elements as negative ones.
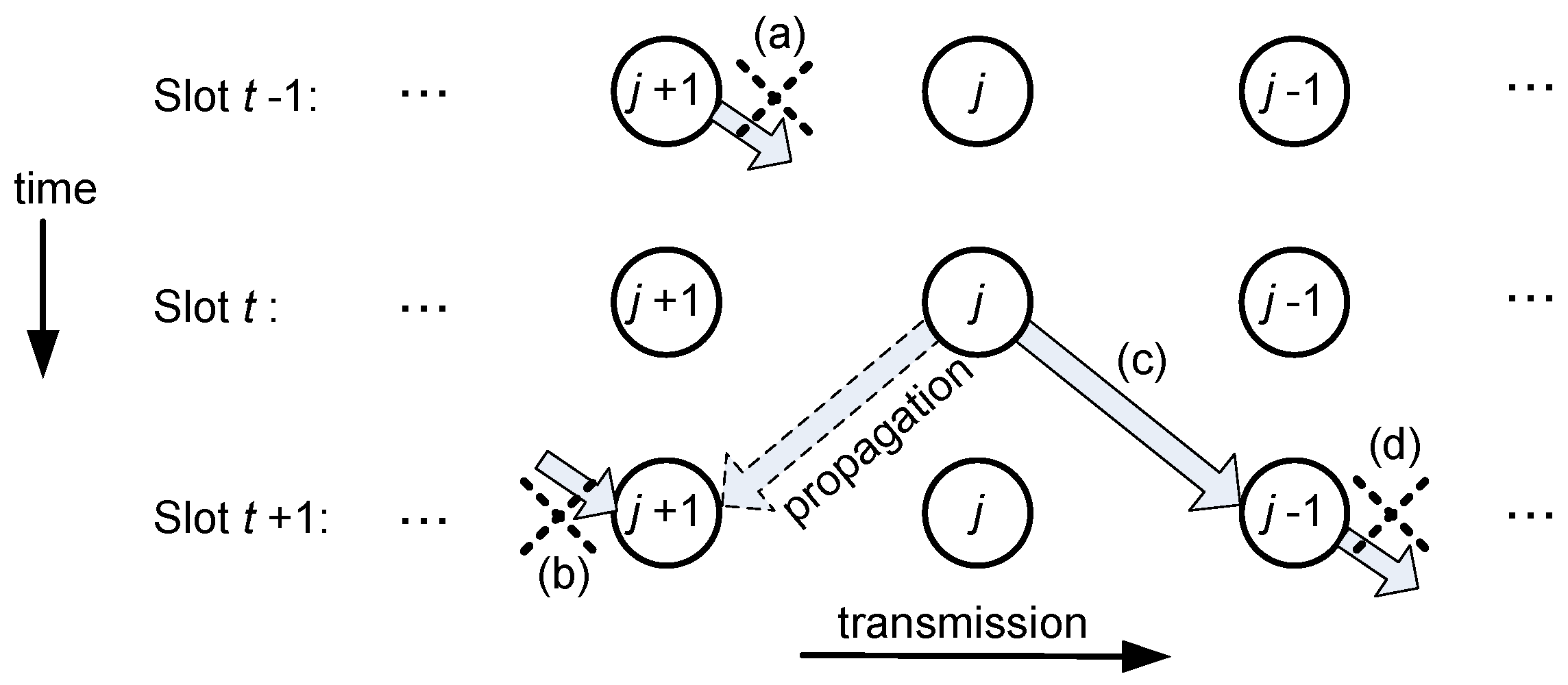
2.2.2. Space-Time Analysis
In order to find a simple algorithm that in turn finds the optimal schedule of the string network, we start analysing a small network. Later on, in
Section 3.1, the limitation on the packet generation rate of every node for queue stability will be established. The optimal schedules found for network sizes
2, 3, and 4 nodes are shown in
Figure 4. The procedure to obtain the optimal schedule consists of applying Equations (2)–(6) to the nodes, trying to minimize the number of idle states, and looking for a periodic operation. It can be noted that for
4, slots 6 and 2 are equal, and the same will happen with 7-3, 8-4, and so on. Therefore, for
N = 4, the frame length is
T = 4. In this schedule, there are only four nodes in an idle state during the whole frame, achieving the busiest operation possible for this network topology.
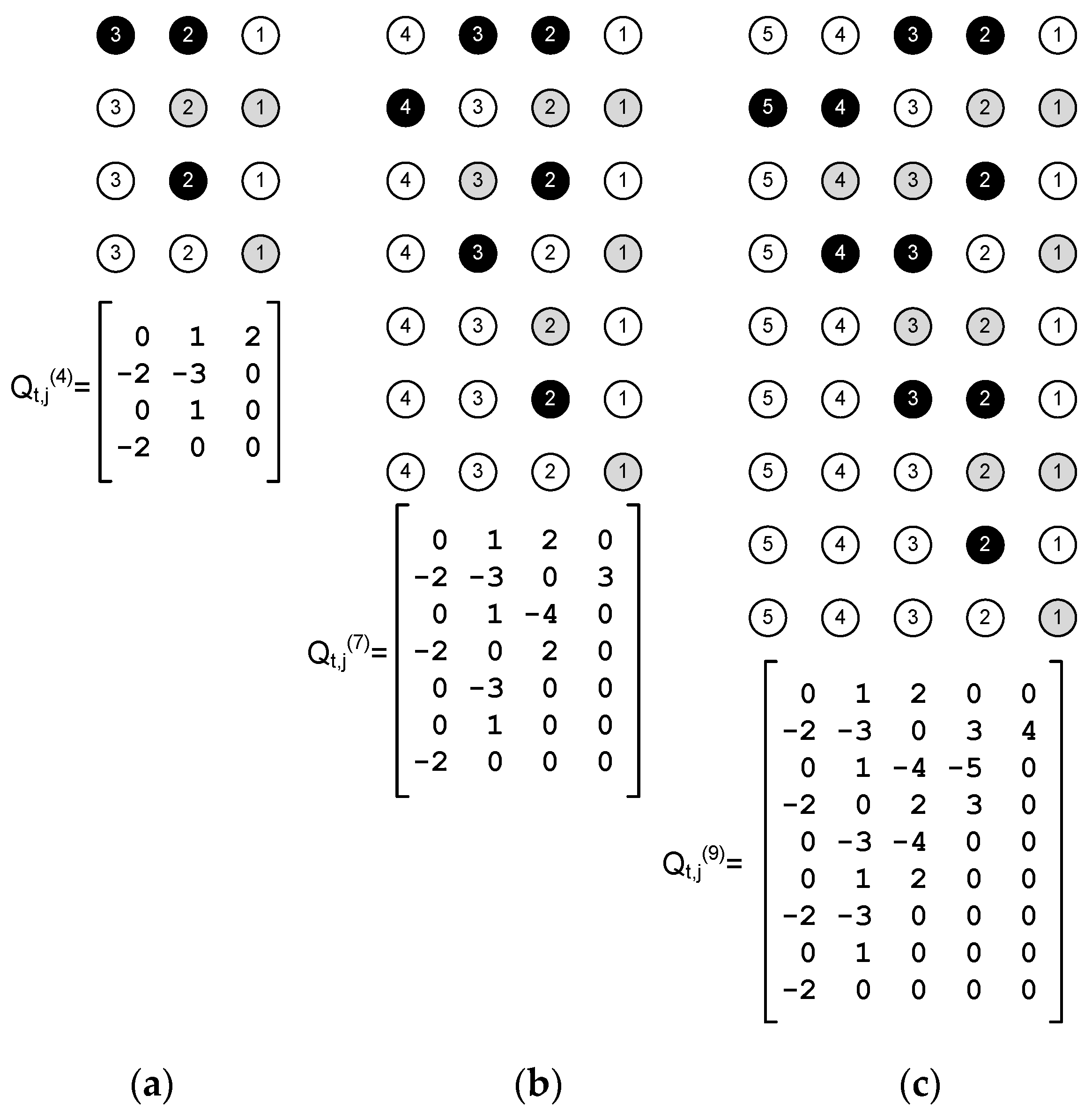
The optimal schedule found for
(see
Figure 4) has a period of
T = 4. It happens that the optimal frame length is also
T = 4 for
N > 4. The method to obtain
can be extended to any network size, because of the regularity of the network structure (hop distance and conditions of the edge nodes). First, we must define a set of four column vectors
for each node
j of the network,
:
where the superscript ‘ stands for transpose. Note that, in this case,
represents column vectors, i.e.,
is the column index of matrix
. It is easy to see that two elements of each vector Equations (7)–(10) will always be negative. These elements represent nodes in a reception state.
Finally, the optimal schedule for a string network of
nodes, which we denote by
, is obtained using vectors Equations (7)–(10) in the columns of the
Q matrix corresponding to the node number in the subscript
j of each vector
, and the superscript
i = j modulo 4. That is, the optimal schedule is:
where, in the last vector
, the negative elements must be replaced by zero because node
N never receives from another node and, instead, it will remain in the idle state. For example,
Figure 5 shows the optimal schedule for a string network of size
, which is given by:
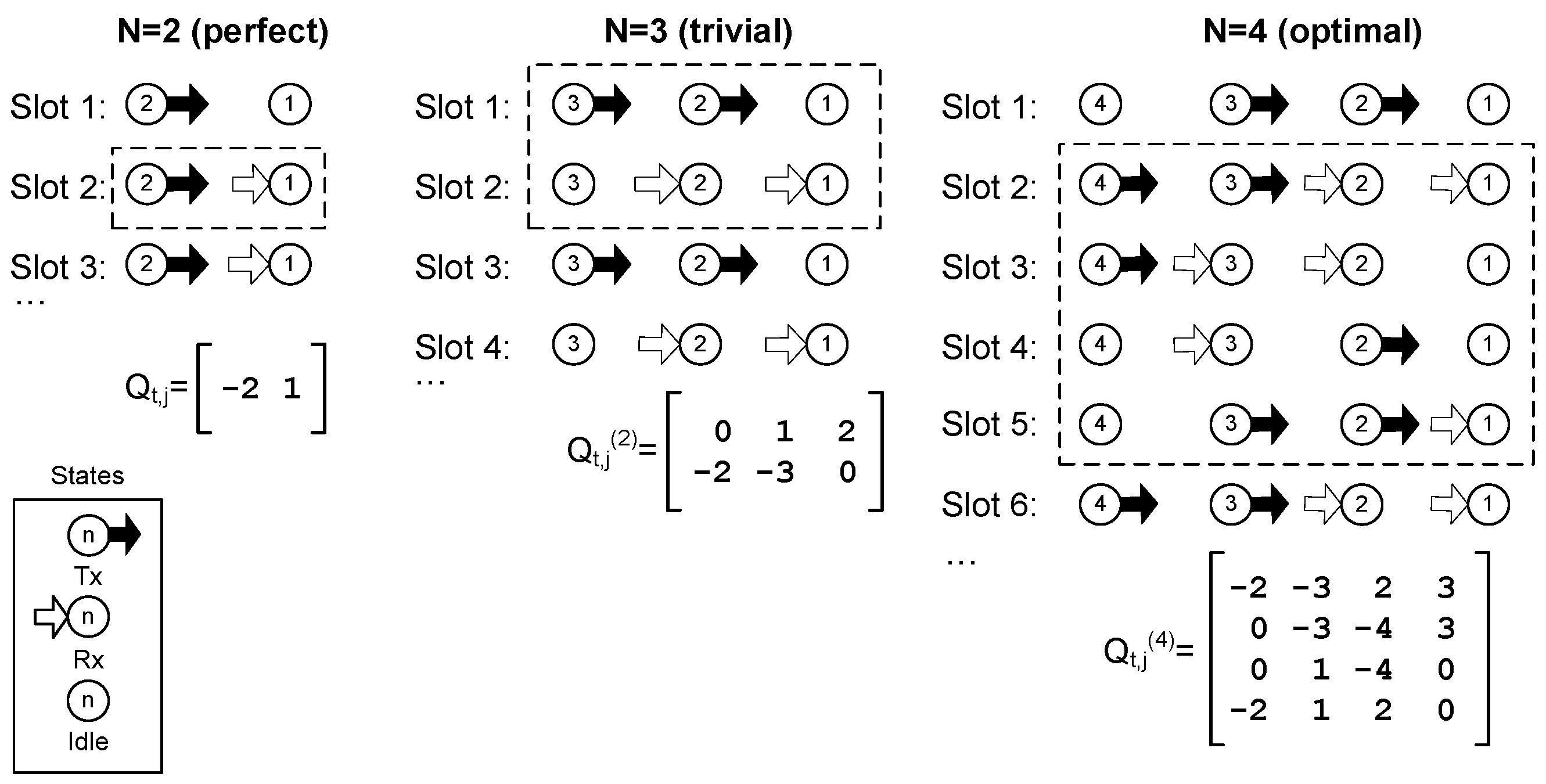
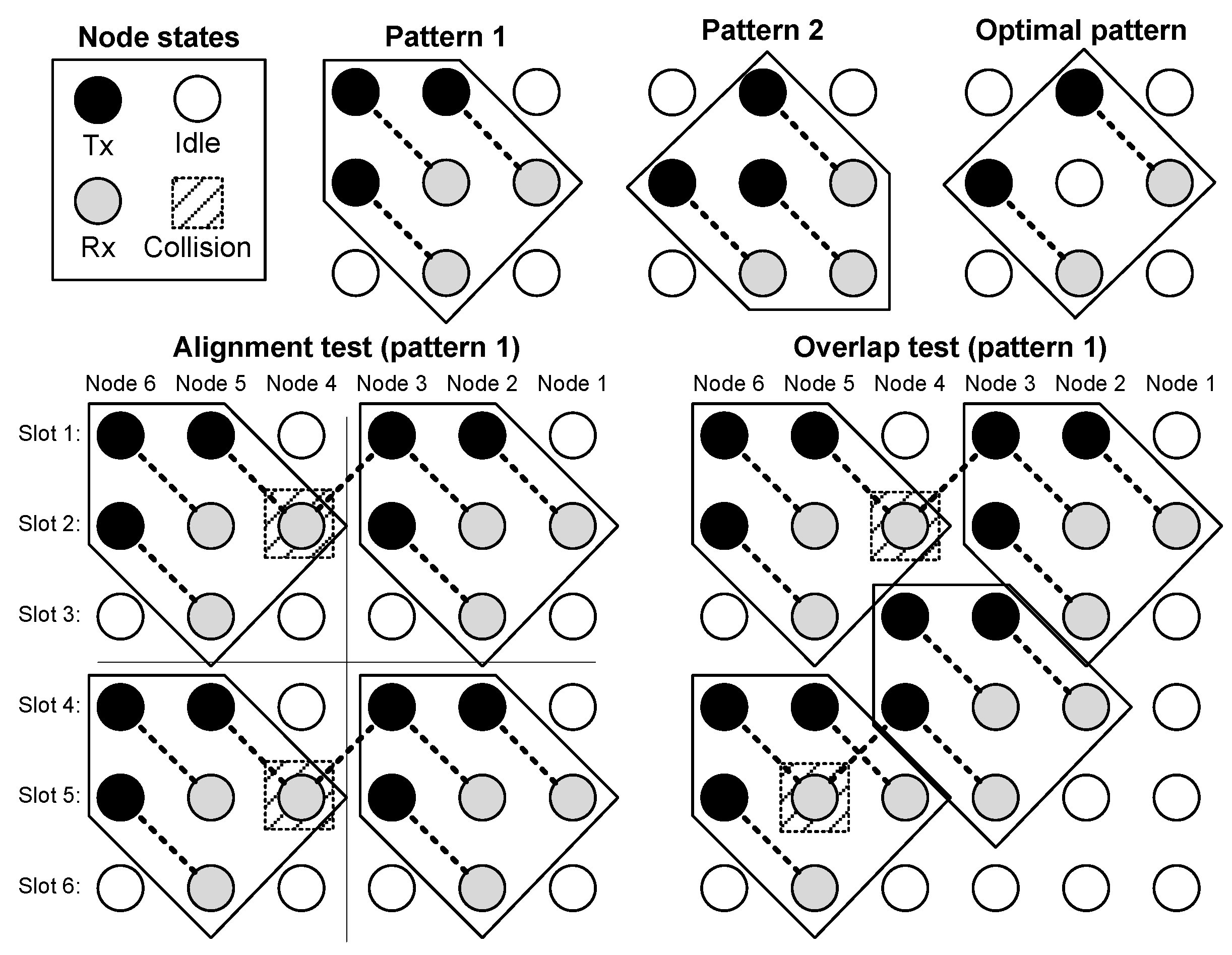
A geometric interpretation can be given to find and to prove this optimal schedule. Let us imagine a 2D space-time lattice, where the node number is in the
-axis and the time slot number is in the
-axis. The problem can be formulated as to set the state (Tx/Rx/Idle) of every node in that 2D space-time lattice, with two constraints: minimize the number of idle states and be periodic in time. We call the pattern the set of states that is repeated in space and time. A final consideration concerns the size of the pattern: the minimum size is
, because
is trivial, and does not lead to a valid solution when it is repeated within the 2D lattice. The proposed procedure to find the best scheduling includes three steps. In the first step, called pattern selection, a reduced state pattern (time slots × nodes with Tx/Rx assigned states), which fulfils Equations (2)–(4), is found, so that it includes as many Tx/Rx states as possible. Once the pattern is found, in the second step, called alignment, the pattern is repeated in the 2D space-time lattice. If collisions arise, the pattern is discarded. When the alignment provides a collision-free schedule, in the third step, called overlap, the Tx/Rx part of a pattern is moved to fill as many idle states as possible and then, again, a check for collisions is carried out, as shown in the lower right corner of
Figure 6. In the steps of alignment and overlap, the found schedule must fulfill conditions Equations (2)–(6).
Figure 6 shows examples of three candidate
patterns, which fulfill constraints Equations (2)–(4), but only one of them passes both alignment and overlap tests without collisions. When repeated by overlapping in the whole 2D lattice, this candidate pattern turns into the optimal schedule presented in Equation (11). For the sake of brevity, the alignment and overlap tests have only been included in
Figure 6 for pattern 1, but the procedure is similar for the other two patterns (2 and the optimal case).
2.2.3. Unequally Spaced Nodes
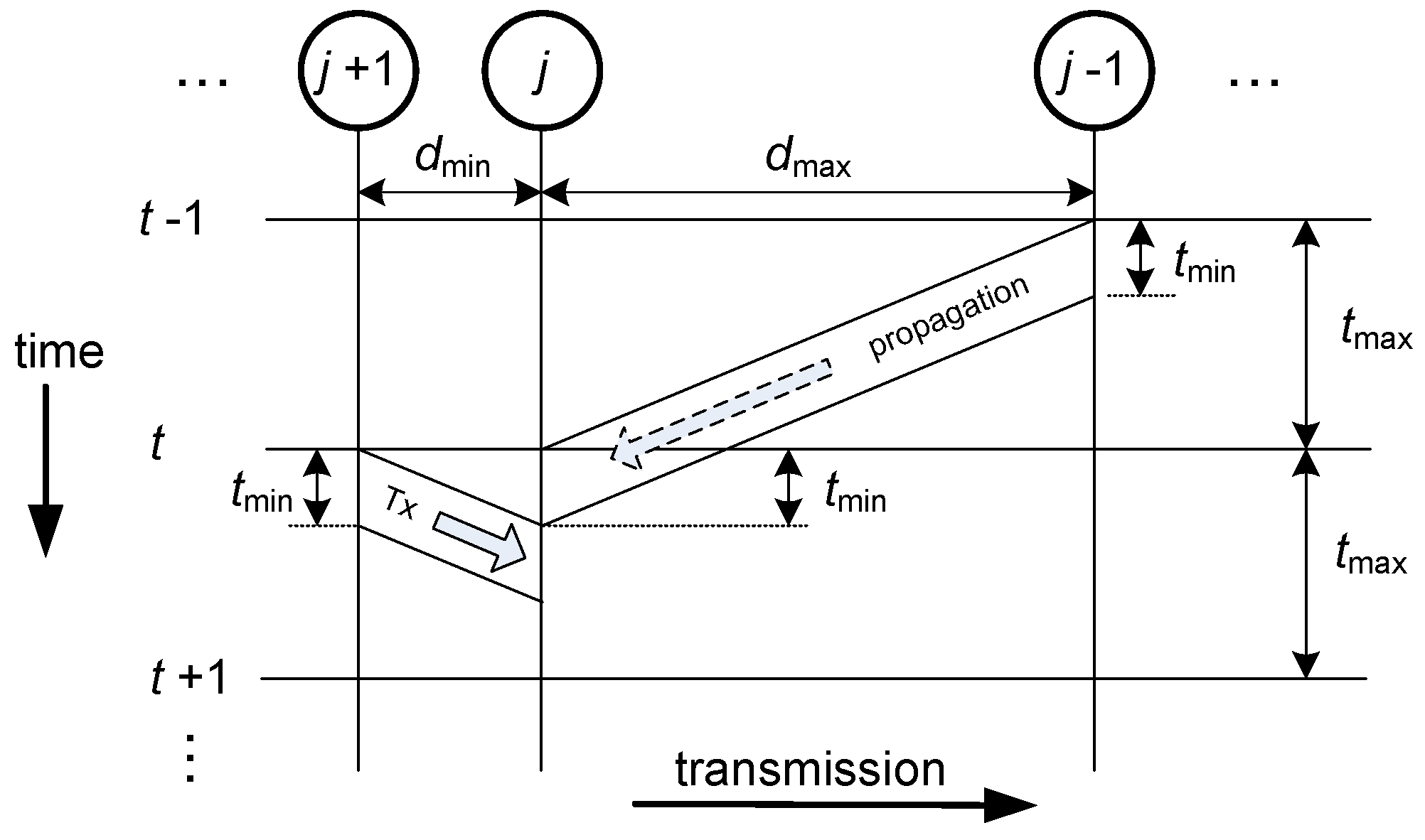
Let us consider now the general case of unequally spaced nodes. To make sure that there will be no interference, in this scenario, the transmission time, which is given by the packet size, cannot be equal to the time slot. To avoid interference, two constraints must be met. First, the time slot must be set so that the longest propagation time is considered; this way, all transmissions will reach their destinations before the end of the second time slot after their start. Second, the packet size must be adjusted to the shortest propagation time; this way, no transmission will reach its destination node before the end of any other possible interference in that node.
These ideas are depicted in
Figure 7, where the worst case of the shortest and longest links being adjacent is shown. We denote
to be the propagation time of the shortest link, and
the propagation time of the longest link. The link distances are, respectively,
and
. In this general case, scheduling is obtained using the proposed method. The throughput will decrease by a factor of
compared to the results for the equidistant network.
3. Results: Network Performance
The performance of the network will be evaluated in four aspects: throughput, end-to-end delay, queue length, and fairness. Closed-form expressions are given for throughput. In case of packet end-to-end delay, we present simulation results. Furthermore, by evaluating different initial conditions, we show that it is possible to reduce the average delay in the network; numerical results are given to prove the statement. The lengths of the queues are determined by simulations. Finally, we have calculated the Gini index to assess the fairness behavior of the network. Simulation results of the Gini index for both throughput and packet delay are shown.
3.1. Throughput
The number of transmissions or receptions in a frame is the number of positive or negative elements of Equation (11). With the proposed method, Equation (11) can be easily built for any N and realize that this number is
. A more rigorous explanation is based on counting the negative valued elements (receptions) in Equation (11). Since there are two negative elements in each Equations (7)–(10), and the right end column of the matrix has no negative values, in a string network with
nodes, the optimal scheduling in Equation (11) will have
transmissions/receptions in the frame. Since the period is four time slots, the theoretical average throughput (1) is given by:
The throughput in Equation (13) is close to the throughput of the perfect schedule, which has a value of
, impossible to obtain in a linear network, as discussed above. The difference is
per cent: the larger
, the smaller the relative difference between the throughputs of both schedules. Obviously, since a node cannot transmit and receive simultaneously, the upper bound of the throughput is
We denote
to be the packet generation rate of node
j and consider equal offered traffic by all sensor nodes. In order to achieve this upper bound, the packet generation rate of the
j node,
, can be calculated as:
For comparison purposes, we can consider a simple fair schedule where every sensor node only transmits one self-generated packet to the Gateway in a frame (
Figure 8). The frame length of this scheduling is given by:
Equation (15) is obtained by inspection of the graphics shown in
Figure 8, up to
. Due to the regularity of the network structure, it is also true for larger networks. A packet generated in node
j will be relayed
times to reach the Gateway. Therefore, the total number of transmissions in one frame is:
The average throughput is the number of transmissions in a frame divided by the frame length. Using Equations (15) and (16) we obtain:
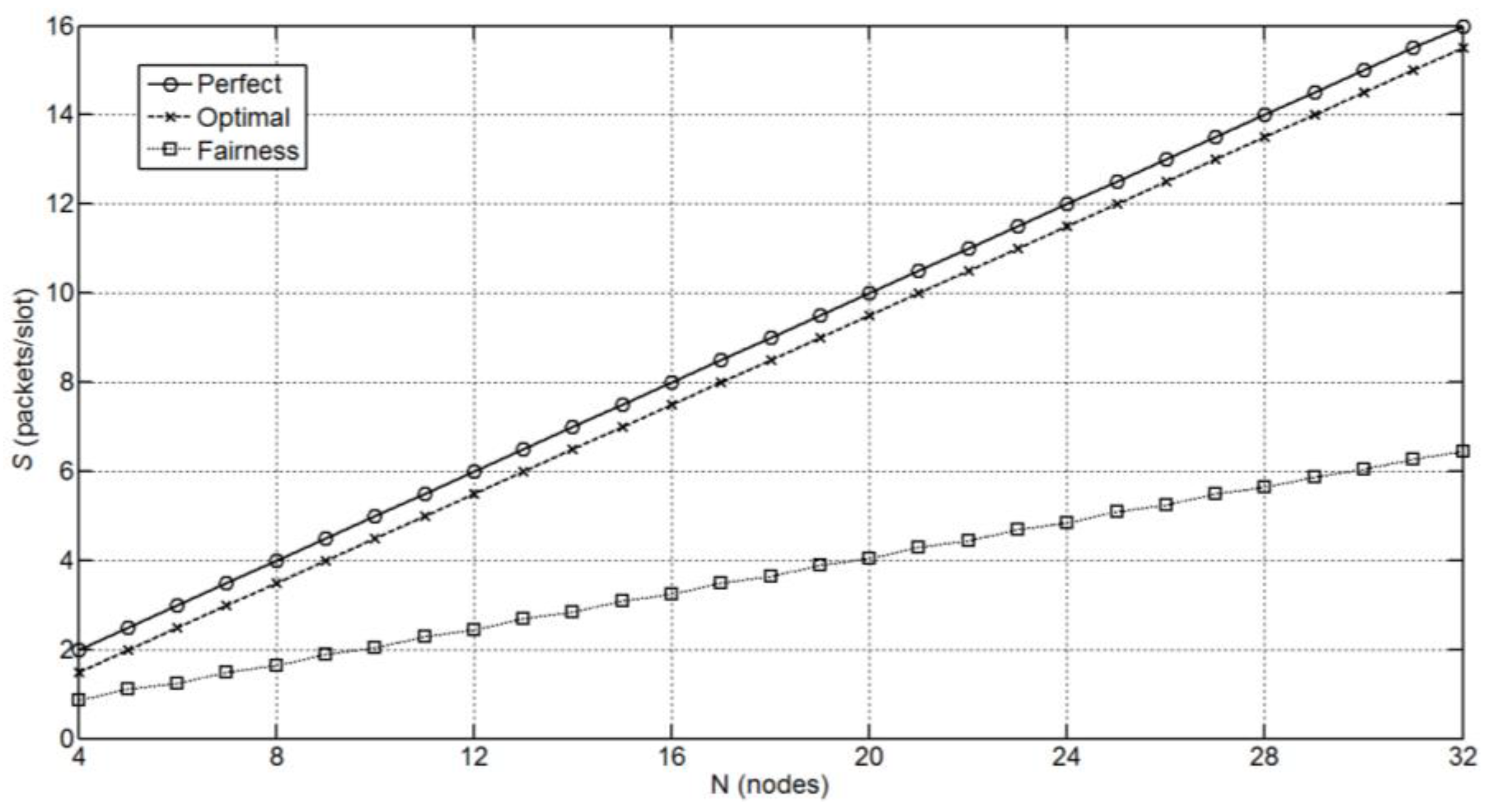
Figure 9 compares the throughput results of both optimal and simple fair schedules and the perfect schedule, showing that the optimal is the non-perfect schedule with the highest average throughput in the network. The reason not to achieve the throughput of the perfect schedule lies in the border effect: the last node never receives data from another node.
3.2. Delay
One of the most important parameters of the performance of a multi-hop network is the delay of the packets delivered by the nodes to the Gateway, which should be as low as possible. In order to compute the delay, the network has been simulated with a Matlab©-based proprietary discrete events simulator. Two measures have been considered: the maximum and the average end-to-end delay
, defined by:
with
being the total number of packets delivered,
the amount of packets delivered from node
j, and
the end-to-end delay of the
-th packet from node
.
In a transmission state, the service policy of the node has to choose which packet to transmit: its own generated packet or a packet from another node (relayed packets). As seen in
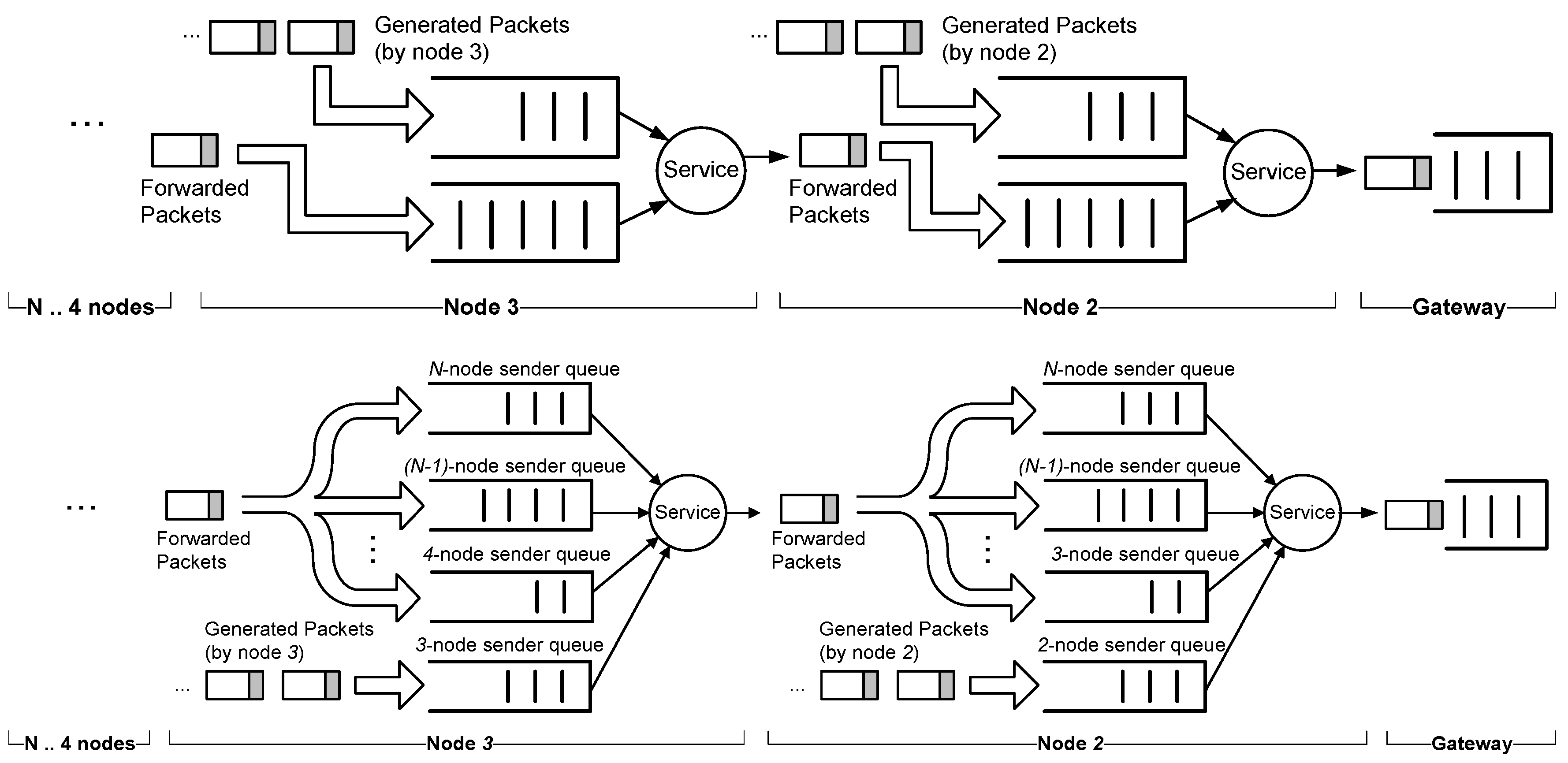
Figure 10, several strategies for the service can be implemented independently of the scheduling scheme adopted. In order to measure the packet delay, we have considered two strategies: FIFO and Round-Robin. In the case of FIFO policy, we need to include two queues, one for the packets received from the up-stream nodes and another one for the self-generated packets. For the sake of clarity, we will denote the former to be the queue and the latter to be the buffer. For the buffer, we will assume the packet rate in Equation (14).
In the case of Round-Robin policy, node j has different queues that store packets coming from the up-stream nodes (nodes to ) and the buffer for its own generated packets. In every transmission slot, a different queue is selected by rotation to send a packet. If the selected queue is empty, the next queue in the sequence is chosen. If none of them have packets, it will be the turn of node j, which will send a packet from its buffer.
Both policies, FIFO and Round-Robin, are examples of polling systems. Systems with several queues attended by a single server based on a pre-scheduled rule belong to the family of vacation queues with a gated operation and a time limited service (one single time slot) [
26,
27]. However, since the transmissions are scheduled, the arrivals process is deterministic and can be studied without resorting to queueing theory. Both delays are shown in
Table 1 for a set of network sizes varying from
to
. It can be seen that the delays are almost equal in both cases. The FIFO service policy is then preferable for large
N because of an easier implementation since there are only two queues per node. Last but not least, the initial conditions different from perfect synchronism, i.e., all the nodes start the counter to transmit from their own buffer simultaneously, can slightly affect the delay shown in
Table 1.
A significant improvement can be obtained when initial conditions are taken into account in the FIFO service policy. In every Tx-slot, a counter is increased and when it reaches a preset threshold, a packet of the buffer is transmitted and the counter will be reset. This means that in FIFO, the packet is transmitted in that slot, while in Round-Robin, the new packet is stored in the buffer, waiting for its turn to be transmitted. In both cases, if the threshold is set to a different value, the offered traffic of the node will also be different.
At this point, it is convenient to define a set of variables for the Tx-slot counter W:
- :
Tx-slots elapsed for the node j (jin the slot t since the last reset;
- :
preset threshold for (when a new packet is generated in slot t and );
- :
initial value for the counter of the node n ();
- :
vector containing values for all nodes: .
The trivial case is to impose that
when the network operation starts. However, testing for different values for every node, it is possible to obtain a lower average delay in the FIFO case, as can be seen in
Table 2. In this table, two cases have been shown for the
vector for three network sizes and different packet rates: the cases shown in
Table 2 are the best and the worst average delay of all possible cases (permutations). For example, when using an initial vector of
in the case of
and uniform packet rate of
, the maximum end-to-end delay is reduced to 13 slots, far from the case of 21 slots when using
. In this particular case, this is a reduction of 38%, a very important benefit for delay in the continuous operation of the string network proposed.
The number of packets delivered to the Gateway from every node is shown in the last column of
Table 2. It can be seen that the two above mentioned
vectors significantly reduce the delay with minimal impact on that number of packets. Similar results for the case of Round-Robin service policy can be observed in
Table 3.
Finally, if the maximum delay is the main design objective,
Table 4 shows again a similar comparison between both policies, suggesting that the service policy hardly affects the end-to-end delay. This effect can be easily observed in
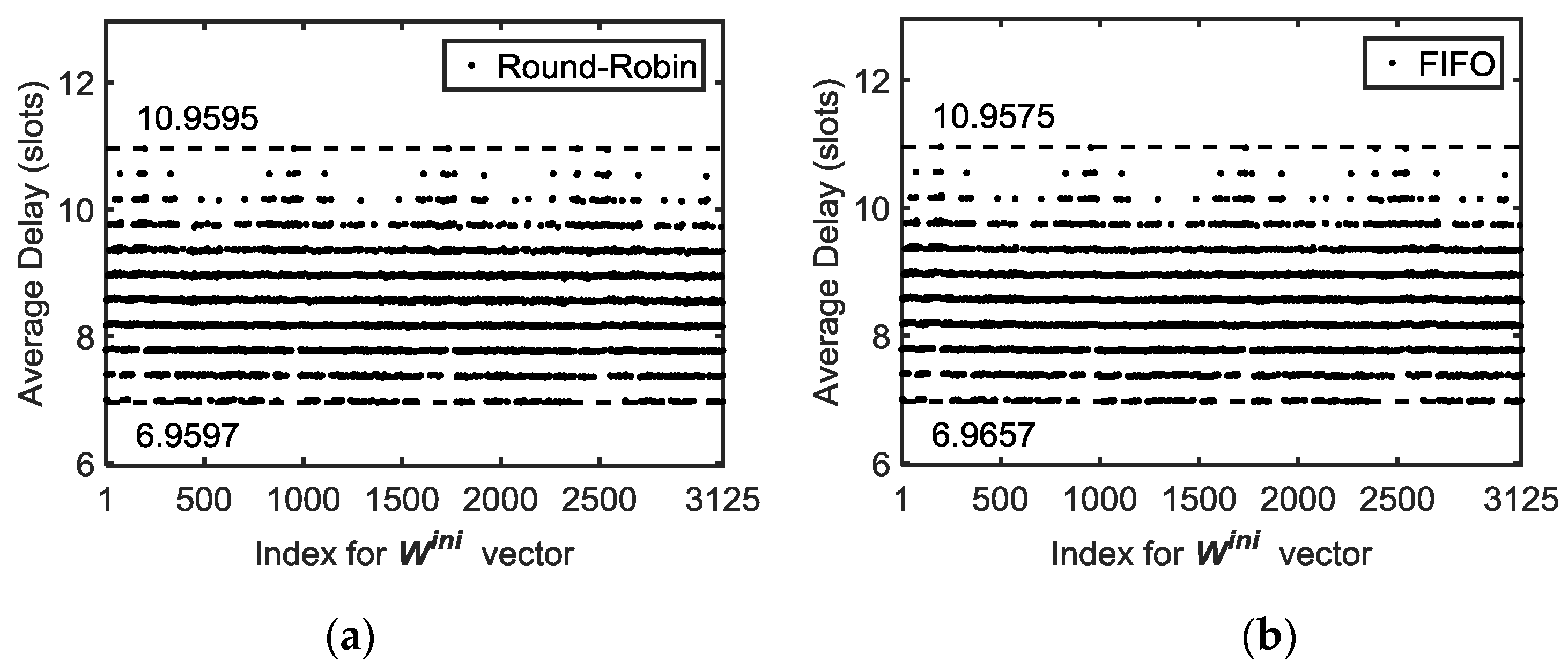
Figure 11, where it can be seen how the service policy has a minimal effect on the bounds (min/max) of average end-to-end delay. In order to represent the simulation results for all the possible
(permutations), an index vector has been used to name every different
vector. This index is equal to the position of the vector
in an ascending sorted list of all the permutations, i.e., index=1 for
, index=2 for
and so on, up to index = 3125 (5
5 different vectors) for
.
3.3. Queue Lengths
From the implementation point of view, it is very interesting to estimate the queue size needed to store packets in a node. The mean queue length
is calculated as the overall sum of packets stored in the queues in all the time slots divided by the simulation time and the number of nodes (excluding the Gateway), that is:
with
being the number of packets stored in the queue of node
after time slot
, and
the duration of the simulation. The results for both cases of Round-Robin and FIFO policies yield
independently of
and the operation time
considered.
Regarding the maximum length of the queue, it is easy to see that there is an upper bound equal to the number of time slots that the node remains in a non-transmission state (i.e., receiving or idle) plus one (own packet generated). For the scheduling matrix in Equation (11), the maximum queue length is three packets because the maximum time between transmission slots is 2.
3.4. Fairness
Throughput and fairness are usually in conflict. On one hand, the highest throughput is obtained with a greedy schedule. On the other hand, a fair schedule yields a poor throughput. When all node locations are equally important in terms of data acquisition, transmission fairness [
28] is a scheduling objective. In this analysis, fairness means that all nodes transmit the same amount of their own data in the long-term, regardless of their distance to the sink node. Previous works by other authors deal with fair scheduling in STDMA networks. Wang et al. proposed a scheduling algorithm [
29], but they emphasized adaptive scheduling instead of the shortest frame. Concerning UWSNs, Diamant and Lutz proposed STDMA protocol for ad hoc UWSNs where fairness was considered [
30] but not uniformly achieved. Xiao et al. also presented an algorithm to find optimal fair scheduling for linear topology in TDMA networks [
31], but the duration of the frame (called cycle in their paper) is greater than our frame length (four slots) and dependent of the network size
, i.e., for a
network, their frame length is six slots, and 12 slots in the case of
. Besides that, the end-to-end delay is higher than the present case, as we have seen in
Section 3.2.
In general, a multi-hop TDMA network does not exhibit fair behavior. In our case, the optimal scheduling jointly with the packet generation rate in (14) guarantees a fair operation in the network, maintaining the number of packets delivered to the Gateway from every node. Moreover, the packet generation rate in (14) defines the maximum traffic load that a node can offer to the network, and fulfils the condition of queue stability:
It is interesting to note that Equation (20) lets us adjust the traffic per node in the network to maintain a stable behavior in the long-term, and it is not imperative that if node j is farther than node from the Gateway, should happen to avoid bottlenecks.
In order to measure the differences between the average packet delays of the different nodes, a commonly used figure of merit of inequality is the Gini index [
32]. Originally used in economics to show imbalances of income distribution [
33], the Gini index has spread to many disciplines because of its simplicity, e.g., in demography (population studies) [
34], medicinal chemistry [
35], or even for improving the resources distribution in packet networks [
36]. The Gini index
can be calculated from [
37]:
with
being the number of nodes,
the average delay of the packets generated at node
j and delivered to the Gateway, and
the arithmetic mean of
(
). Index
takes values in [0,1]. Zero means a homogenous distribution or fairness, which means no difference, i.e., the average delays that the packets suffer from in terms of the different nodes would be the same. On the other hand, a value 1 for
means that there is a node with such a high average delay that the delays of the rest of nodes are negligible (usually called greedy behavior).
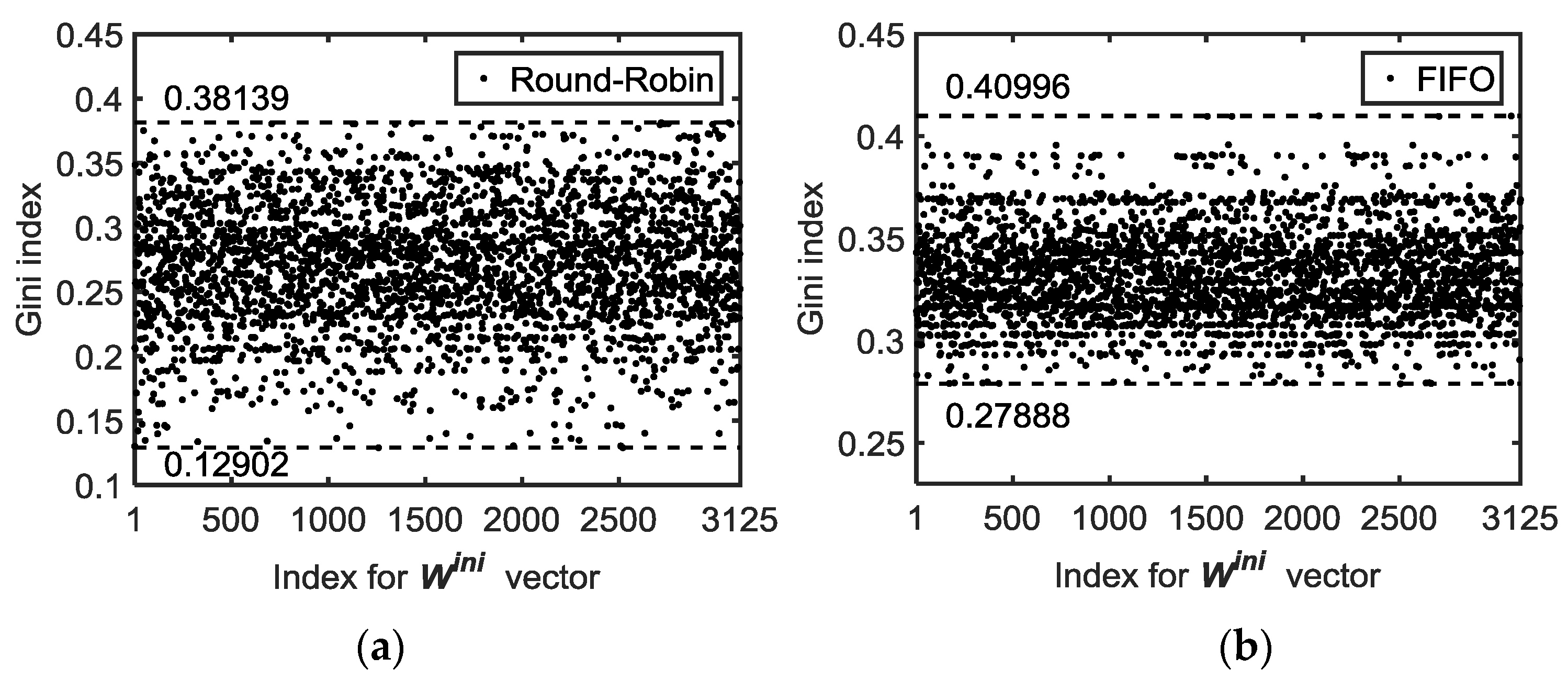
The simulation results for all possible
(permutations) are presented in
Figure 12 for a network with six nodes. In order to look for the bounds of the Gini index of the delay,
Table 5 shows the minimum (fairest case) and maximum values for different network sizes under the same generated traffic conditions as those in
Table 4.
When we observe
Figure 12 and the results in
Table 5, we realize that in, general, the Round Robin service policy is fairer, i.e., has a smaller Gini index. In all cases, however, a task-force analysis has to be carried out to find the best
vector that achieves the sought objective, e.g., minimize the average delay, the maximum delay, or the Gini index.