Suppression Attack Against Multicast Protocol in Low Power and Lossy Networks: Analysis and Defenses
Abstract
1. Introduction
- We significantly extend our previous work [13], and analyze the suppression attack with a preliminary result in MPL-based LLNs. This is the first in-depth work that investigates the performance impact of suppression attack in MPL-based LLNs.
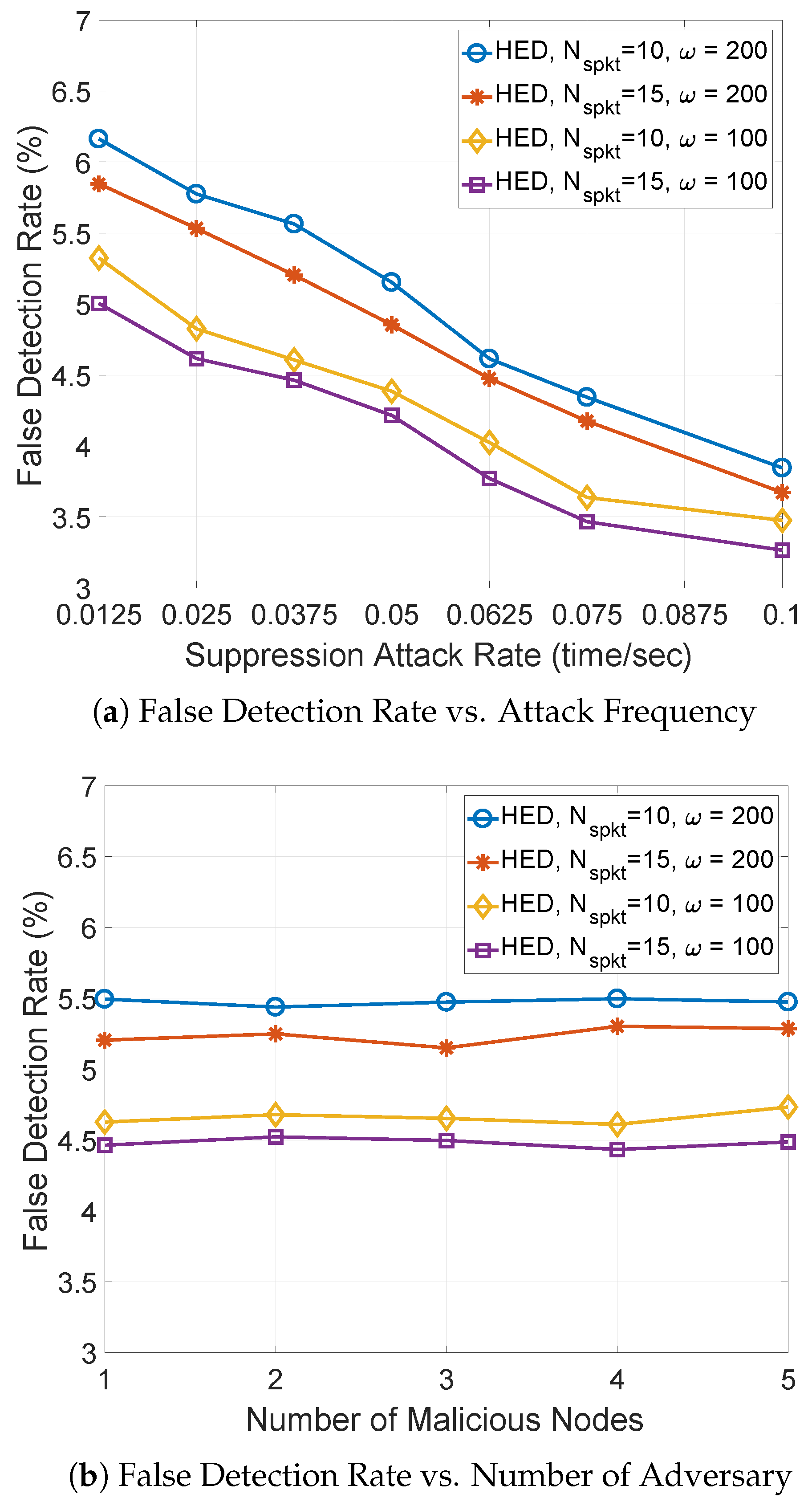
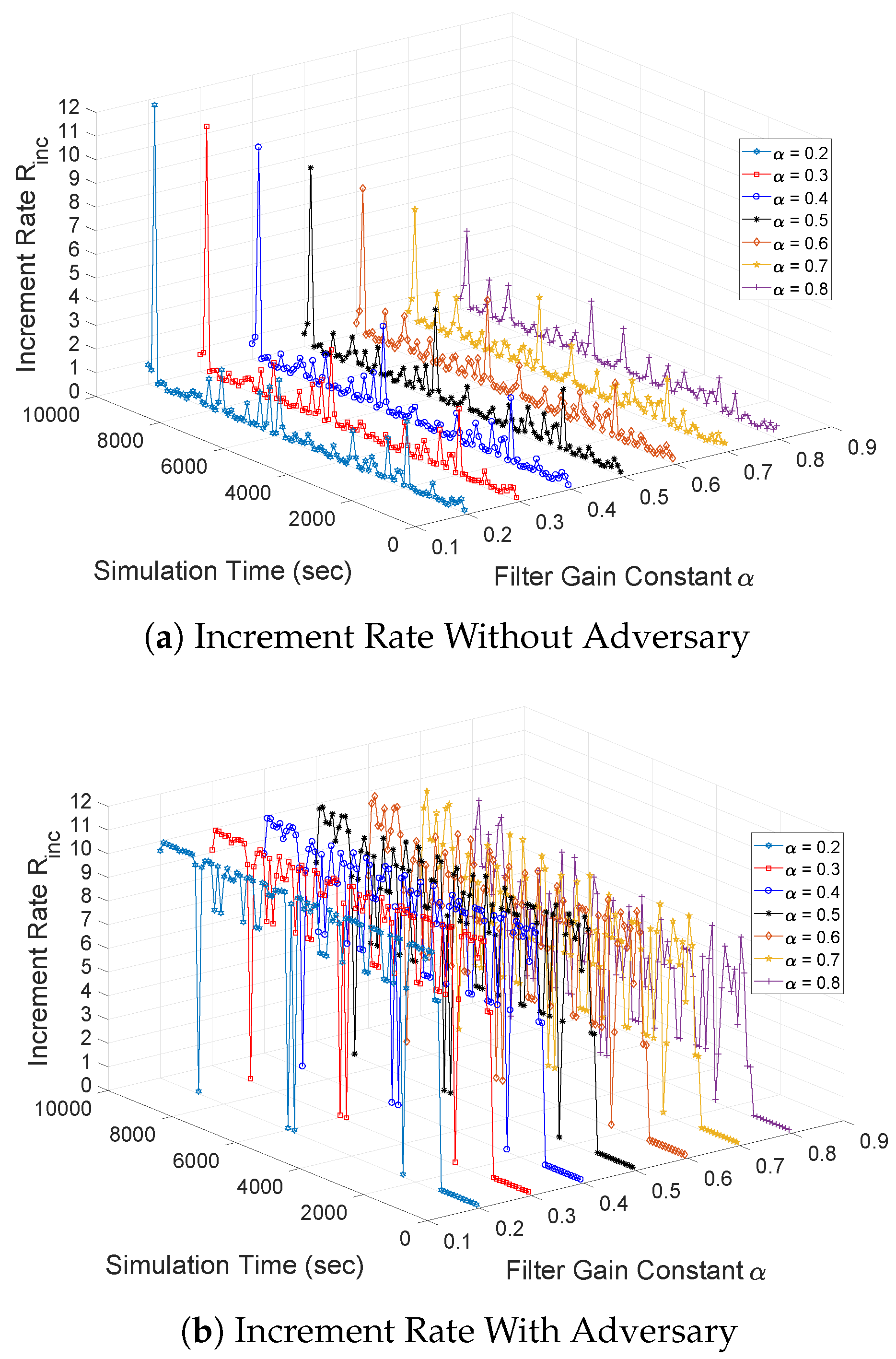
- We propose a heuristic-based detection scheme, called HED, to efficiently mitigate the suppression attack in MPL-based LLNs. In the HED, each node maintains an increment rate of the minimum sequence number in the Seed Set, and compares the recent increment of sequence numbers within a time period with the heuristically calculated increment threshold of sequence numbers to detect potential malicious node.
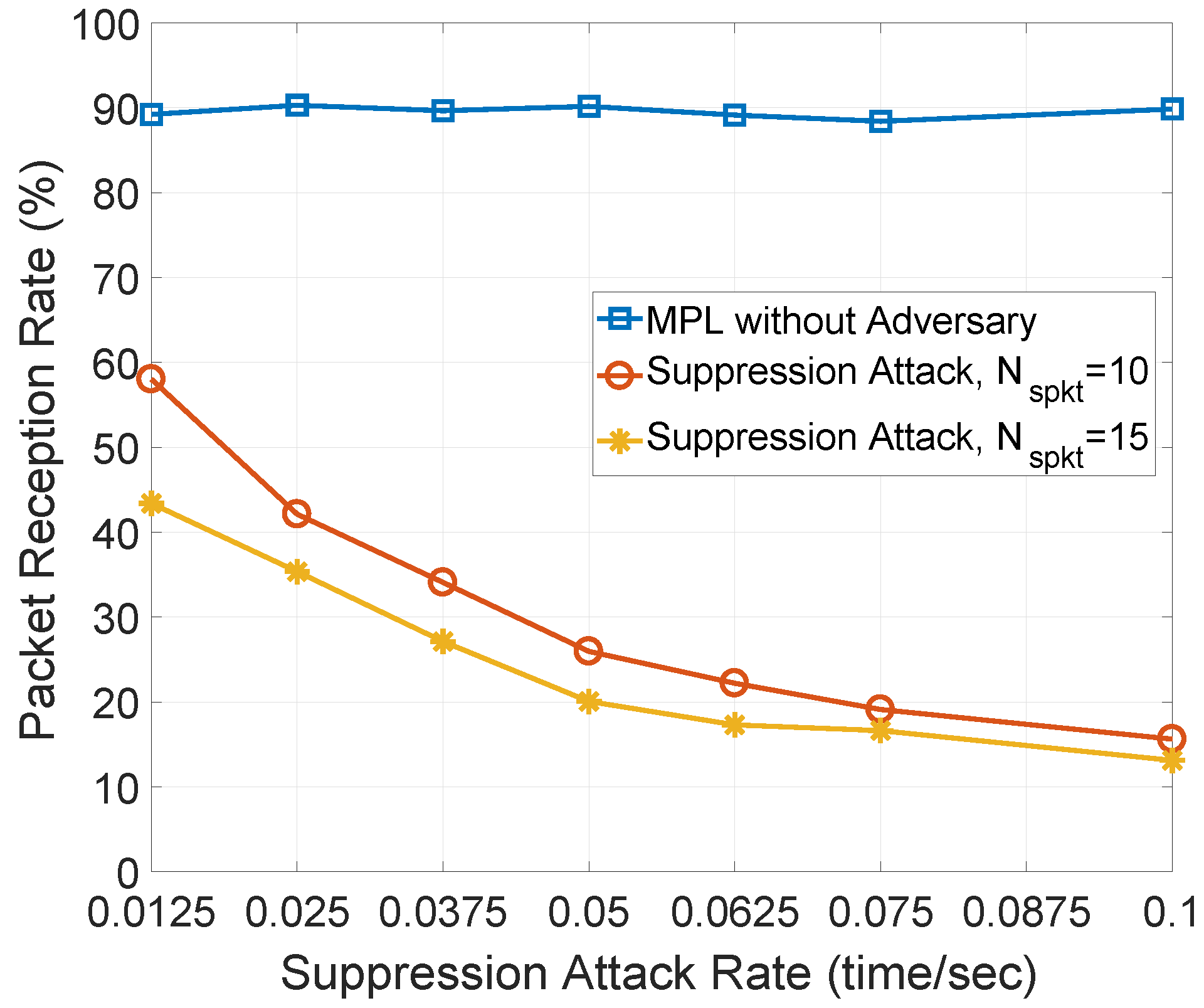
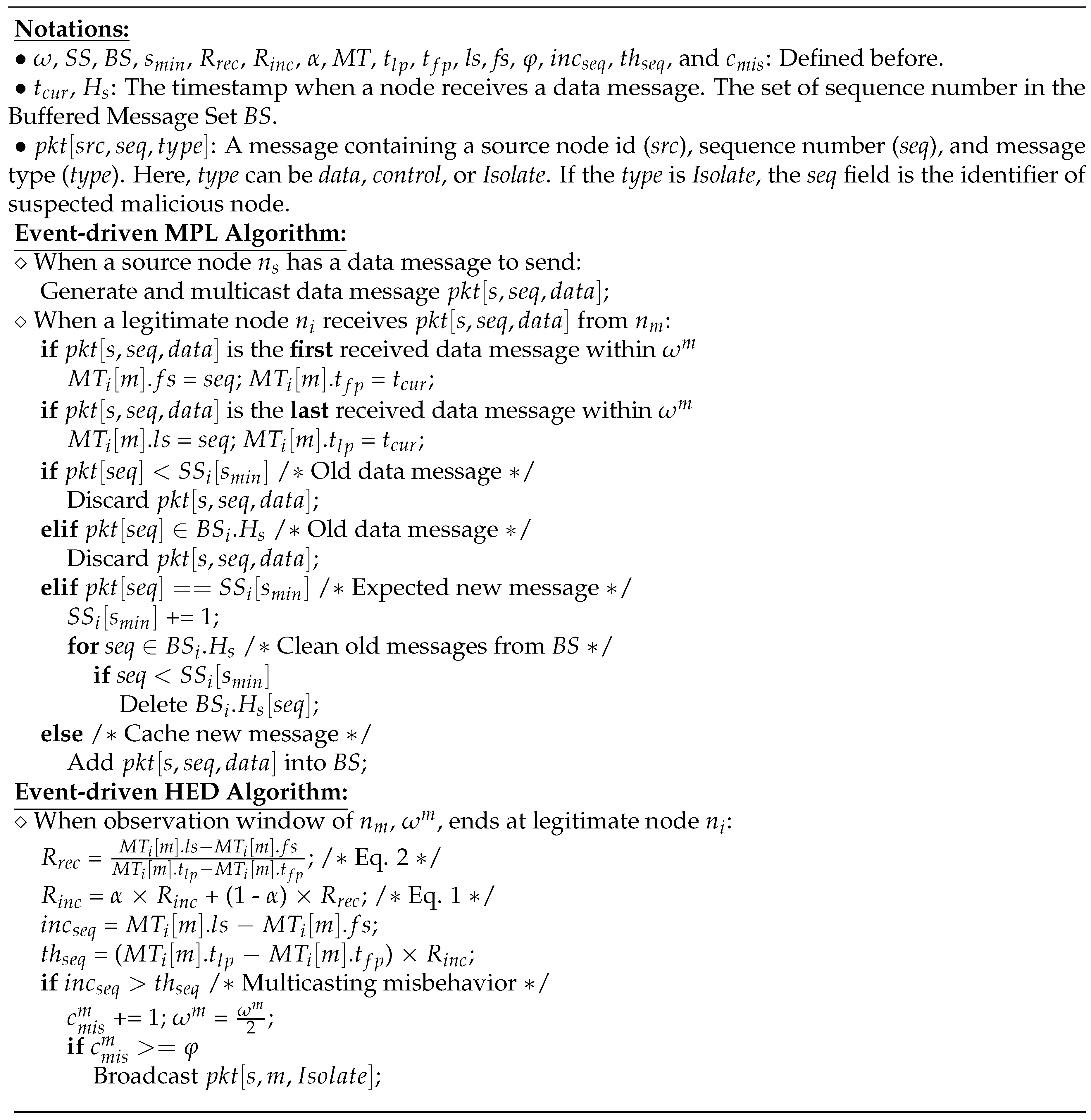
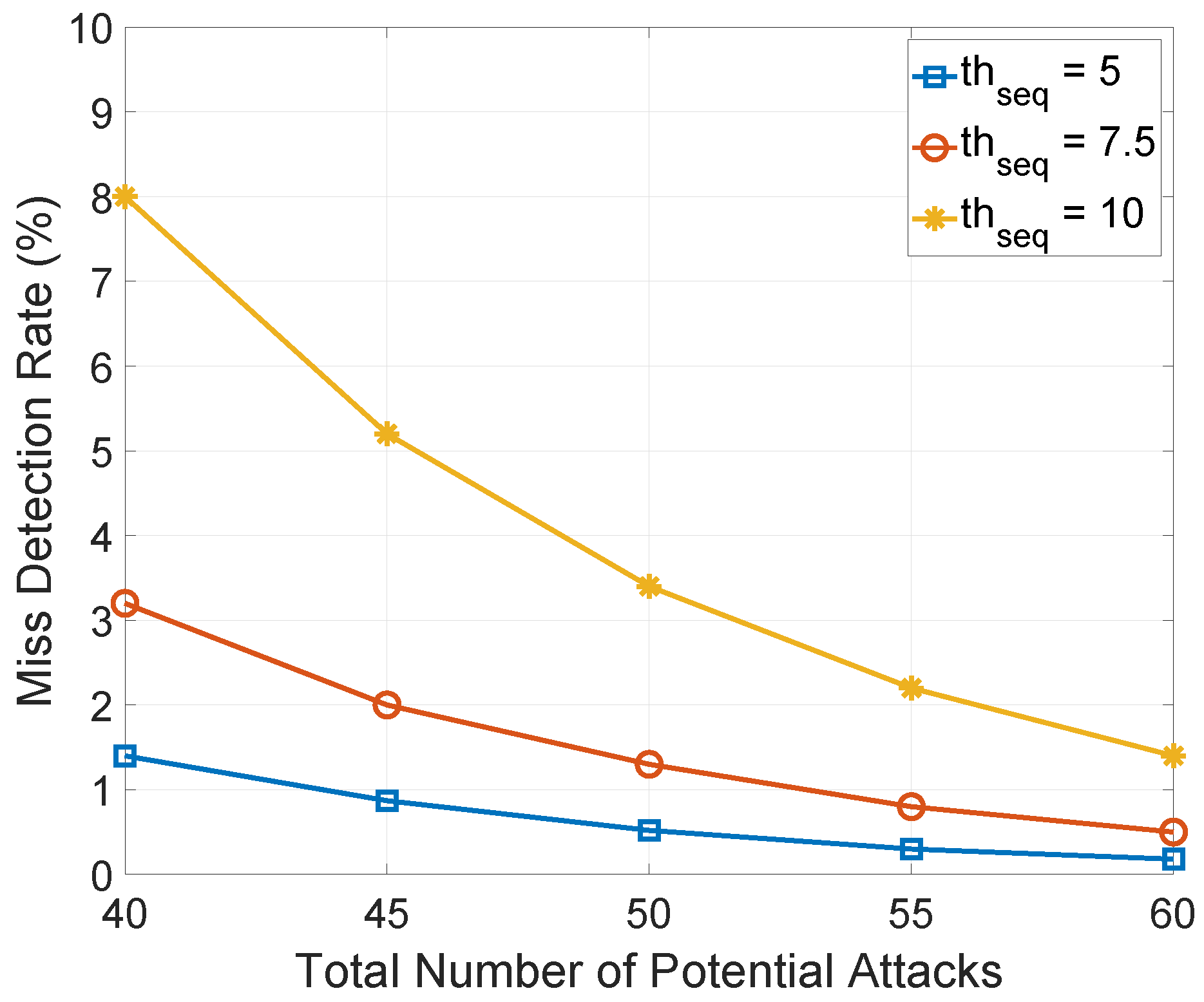
- We propose a simple analytical model of the HED and show its numerical result in terms of miss detection rate. We also revisit and implement the original MPL with and without adversary for performance comparison. In addition, the original MPL without adversary will be used as the upper bound of packet reception rate.
2. Related Work
2.1. Wireless Ad Hoc Networks
2.2. Low Power and Lossy Networks
2.3. Internet of Things
3. Countermeasure to Suppression Attack
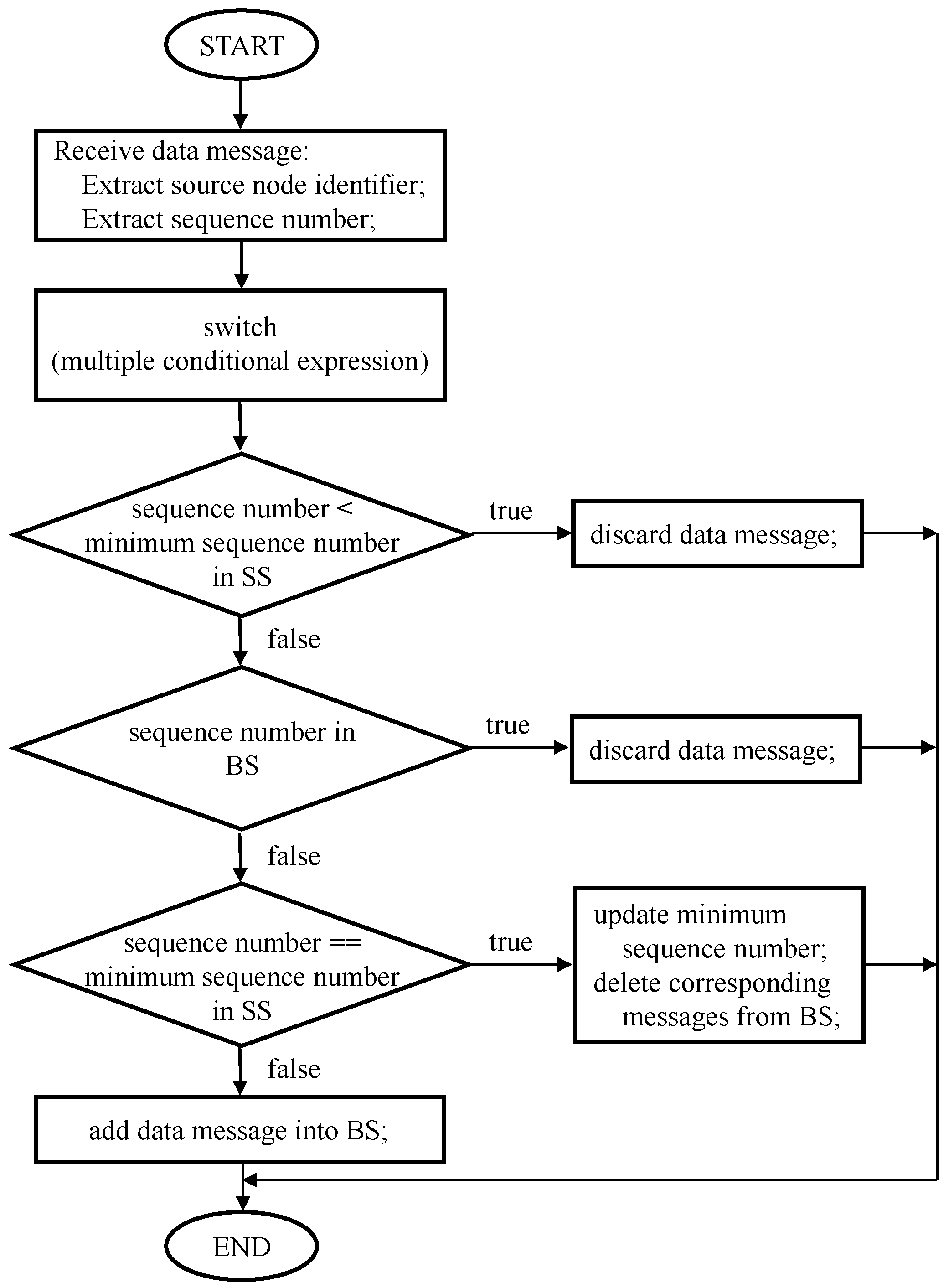
3.1. Overview of Multicast Protocol
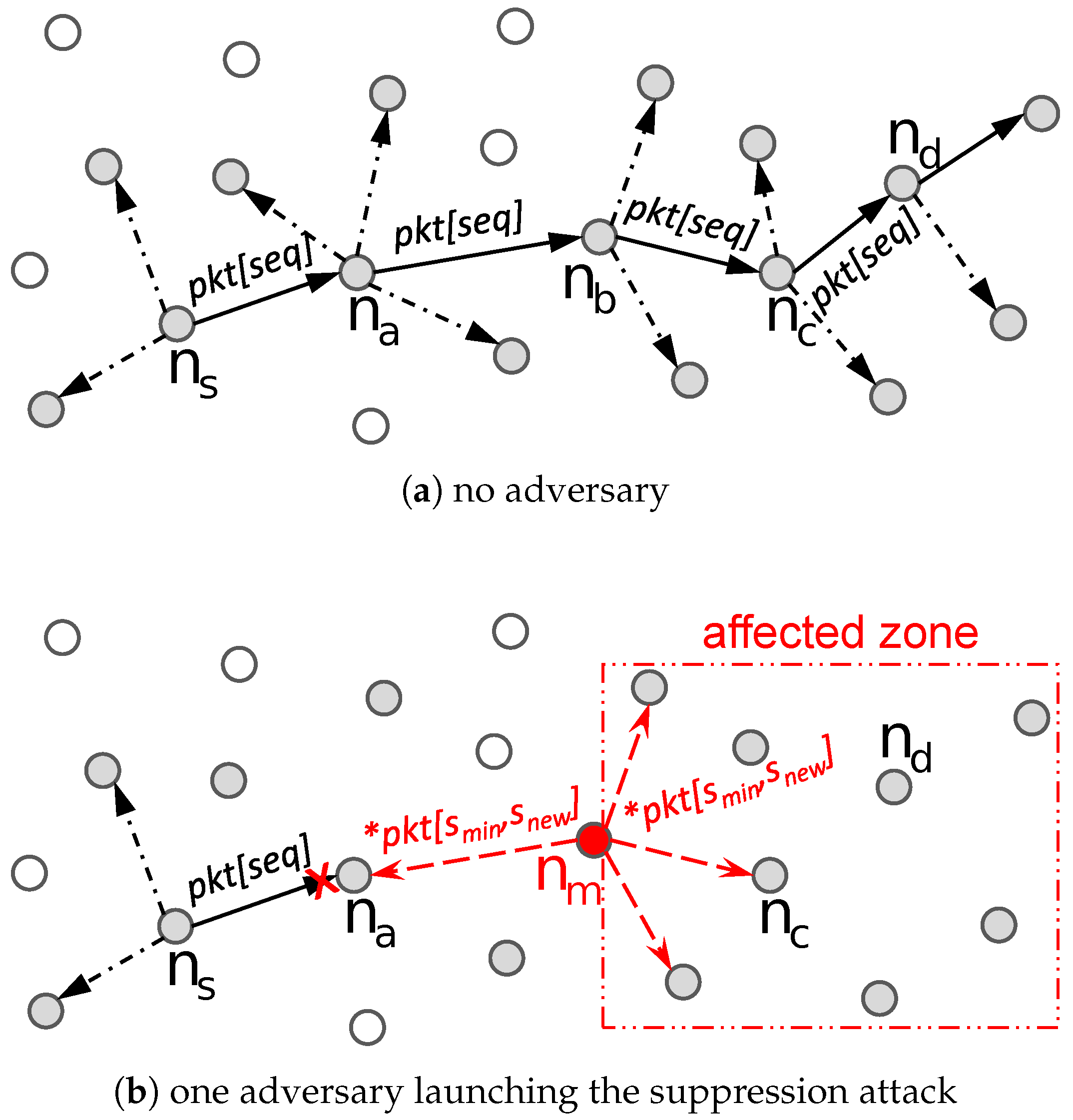
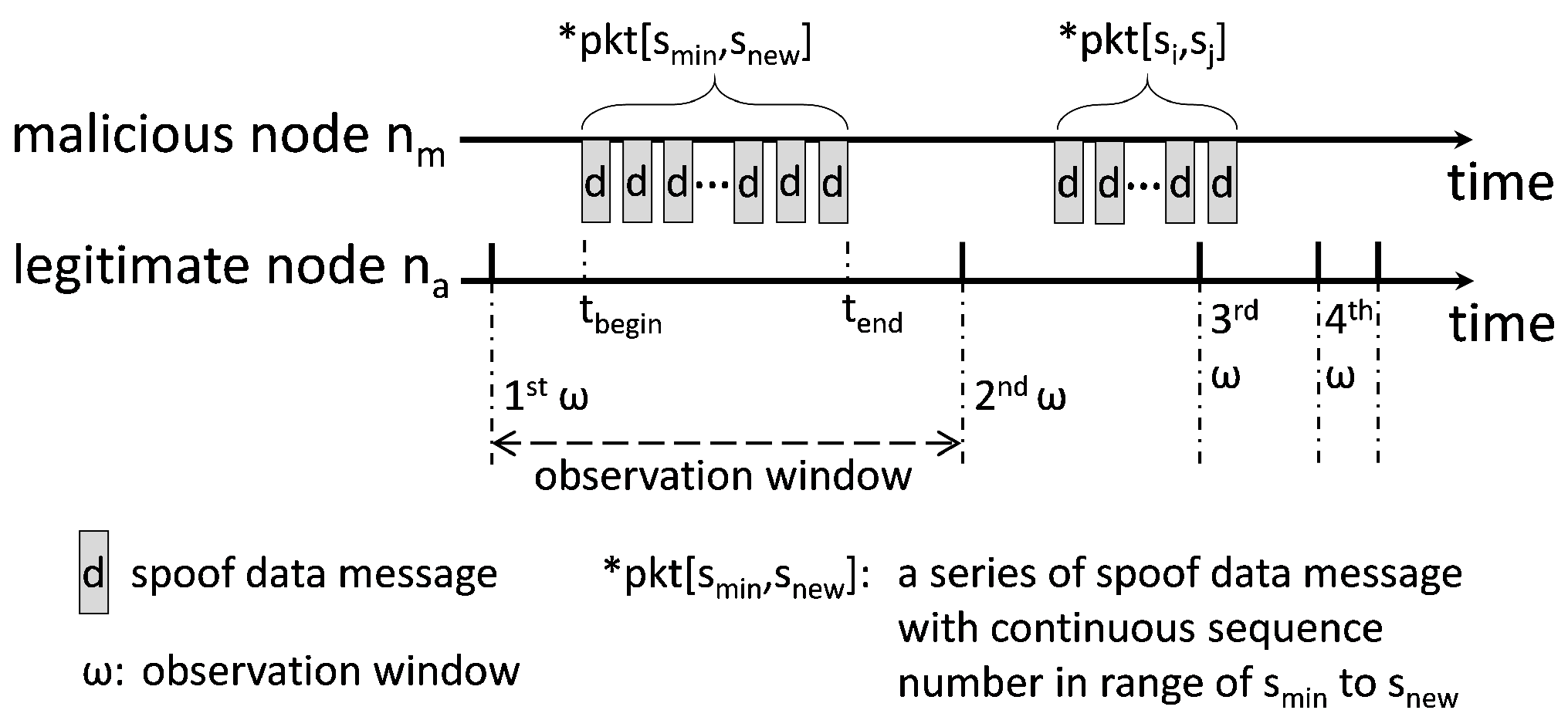
3.2. Analysis of Suppression Attack
3.3. HED: Heuristic-Based Detection Scheme
4. Analysis of the Proposed Countermeasure
5. Performance Evaluation
5.1. Simulation Testbed
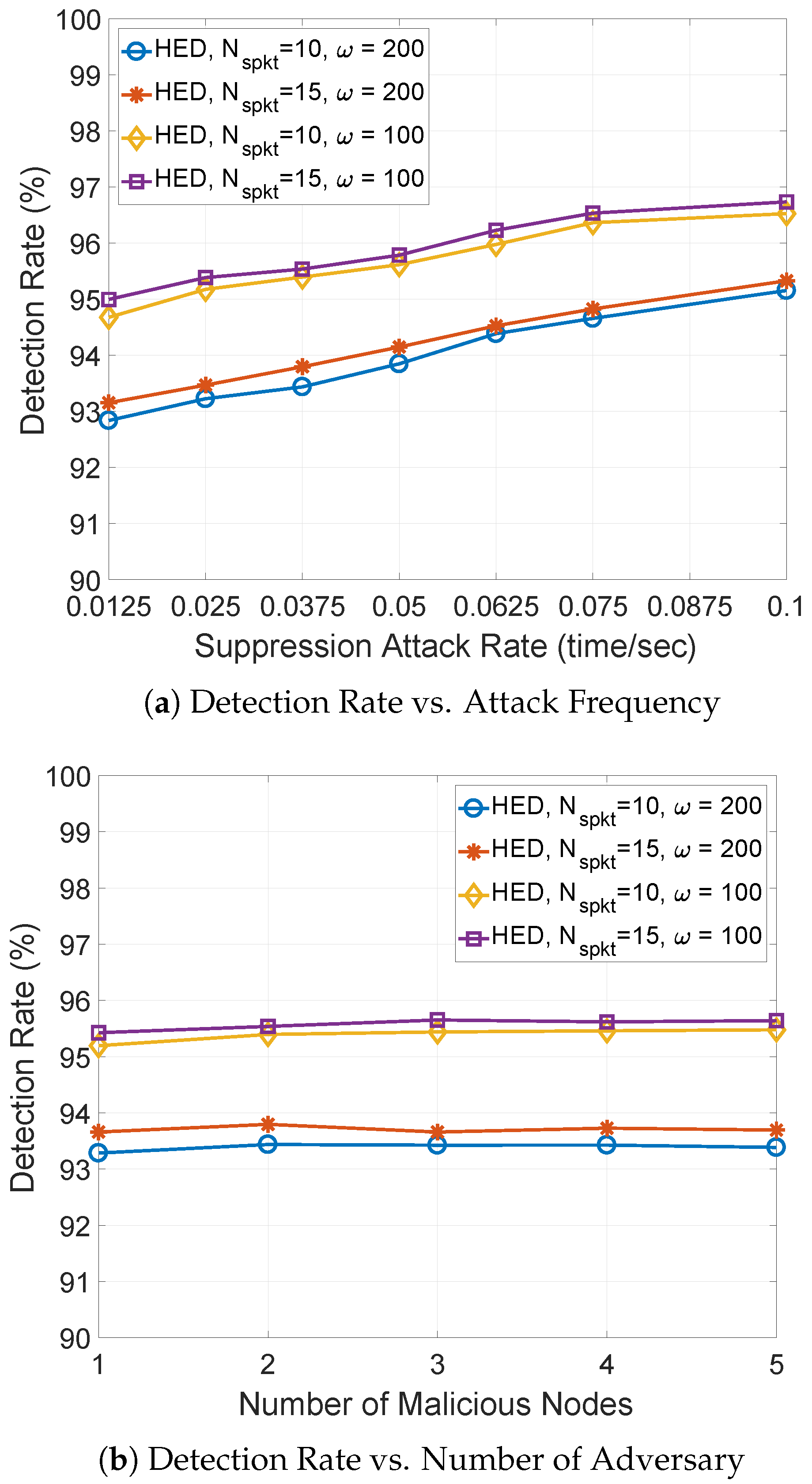
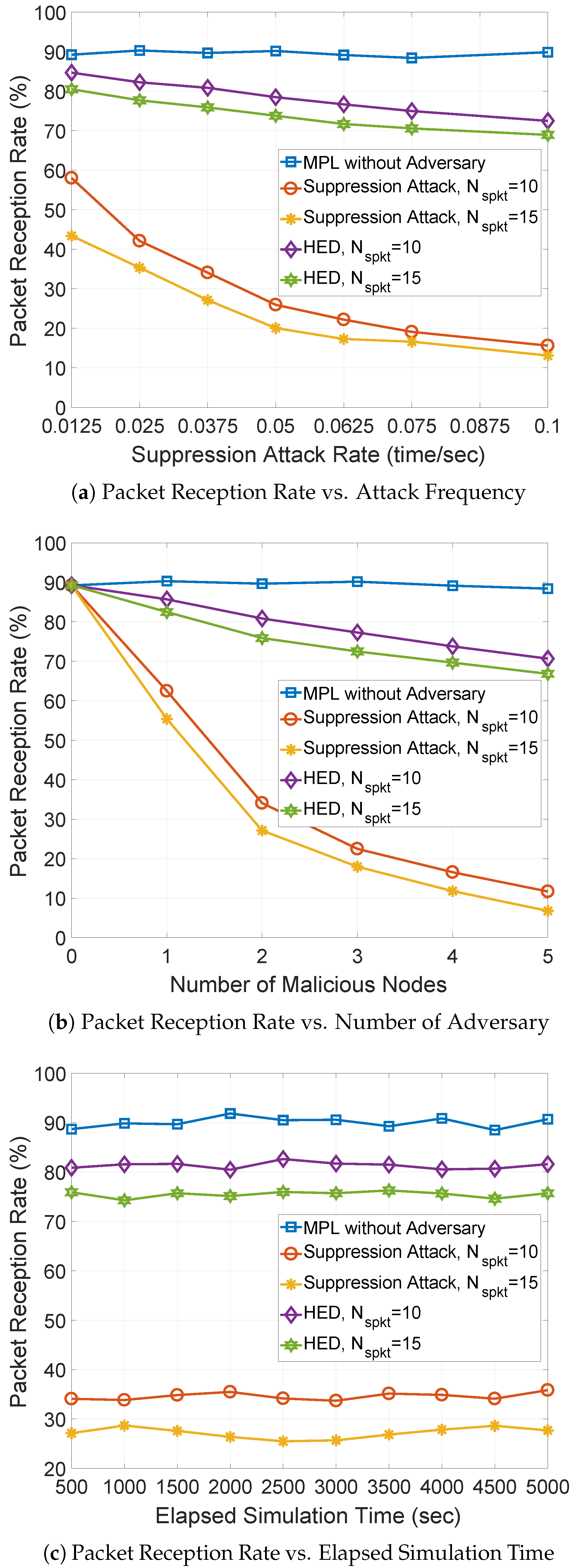
5.2. Simulation Results and Analysis
6. Discussion
7. Concluding Remarks
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Palattella, M.; Dohler, M.; Grieco, A.; Rizzo, G.; Torsner, J.; Engel, T.; Ladid, L. Internet of Things in the 5G Era: Enablers, Architecture, and Business Models. IEEE J. Sel. Areas Commun. 2016, 34, 510–527. [Google Scholar] [CrossRef]
- Gartner Says 8.4 Billion Connected “Things” Will Be in Use in 2017, Up 31 Percent From 2016. 2017. Available online: https://www.gartner.com/en/newsroom/press-releases/2017-02-07-gartner-says-8-billion-connected-things-will-be-in-use-in-2017-up-31-percent-from-2016 (accessed on 26 September 2018).
- Al-Fuqaha, A.; Guizani, M.; Mohammadi, M.; Aledhari, M.; Ayyash, M. Internet of Things: A Survey on Enabling Technologies, Protocols, and Applications. IEEE Commun. Surv. Tutor. 2015, 17, 2347–2376. [Google Scholar] [CrossRef]
- Hui, J.; Kelsey, R. Multicast Protocol for Low-Power and Lossy Networks (MPL). RFC Stand. 7731. 2016. Available online: https://www.rfc-editor.org/info/rfc7731 (accessed on 26 September 2018).
- Kim, H.; Ko, J.; Culler, D.; Paek, J. Challenging the IPv6 Routing Protocol for Low-Power and Lossy Networks (RPL): A Survey. IEEE Commun. Surv. Tutor. 2017, 19, 2502–2525. [Google Scholar] [CrossRef]
- IEEE Standards Association. 802.15.4-2011—IEEE Standard for Local and Metropolitan Area Networks—Part 15.4: Low-Rate Wireless Personal Area Networks (LR-WPANs); IEEE Standards Association: Piscataway, NJ, USA, 2011. [Google Scholar]
- Cisco Connected Grid Security for Field Area Network. January 2012. Available online: https://www.cisco.com/c/dam/en_us/solutions/industries/docs/energy/C11-696279-00_cgs_fan_white_paper.pdf (accessed on 26 September 2018).
- Challa, S.; Wazid, M.; Das, A.; Kumar, N.; Reddy, A.; Yoon, E.; Yoo, K. Secure Signature-Based Authenticated Key Establishment Scheme for Future IoT Applications. IEEE Access 2017, 5, 3028–3043. [Google Scholar] [CrossRef]
- Sehgal, A.; Perelman, V.; Kuryla, S.; Schonwalder, J. Management of Resource Constrained Devices in the Internet of Things. IEEE Commun. Mag. 2012, 50, 144–149. [Google Scholar] [CrossRef]
- Sehgal, A.; Mayzaud, A.; Badonnel, R.; Chrisment, I.; Schnwlder, J. Addressing DODAG Inconsistency Attacks in RPL Networks. In Proceedings of the Global Information Infrastructure and Networking Symposium (GIIS), Montreal, QC, Canada, 15–19 September 2014; pp. 1–8. [Google Scholar]
- Tsao, T.; Alexander, R.; Dohler, M.; Daza, V.; Lozano, A.; Richardson, M. A Security Threat Analysis for the Routing Protocol for Low-Power and Lossy Networks (RPLs). RFC Stand. 7416. 2015. Available online: https://www.rfc-editor.org/info/rfc7416 (accessed on 26 September 2018). [CrossRef]
- Pelechrinis, K.; Iliofotou, M.; Krishnamurthy, S. Denial of Service Attacks in Wireless Networks: The Case of Jammers. IEEE Commun. Surv. Tutor. 2011, 13, 245–257. [Google Scholar] [CrossRef]
- Pu, C.; Zhou, X.; Lim, S. Mitigating Suppression Attack in Multicast Protocol for Low Power and Lossy Networks. In Proceedings of the IEEE 43rd Conference on Local Computer NetworksLCN, Chicago, IL, USA, 1–4 October 2018. [Google Scholar]
- Varga, A. OMNeT++. 2014. Available online: http://www.omnetpp.org/ (accessed on 15 March 2018).
- Pu, C.; Lim, S. Spy vs. Spy: Camouflage-based Active Detection in Energy Harvesting Motivated Networks. In Proceedings of the IEEE Military Communications Conference (MILCOM), Tampa, FL, USA, 26–28 October 2015; pp. 903–908. [Google Scholar]
- Pu, C.; Lim, S.; Jung, B.; Chae, J. EYES: Mitigating Forwarding Misbehavior in Energy Harvesting Motivated Networks. Elsevier Comput. Commun. 2018, 124, 17–30. [Google Scholar] [CrossRef]
- Pu, C.; Lim, S.; Byungkwan, J.; Manki, M. Mitigating Stealthy Collision Attack in Energy Harvesting Motivated Networks. In Proceedings of the IEEE Military Communications Conference (MILCOM), Baltimore, MD, USA, 23–25 October 2017; pp. 575–580. [Google Scholar]
- Pu, C.; Lim, S. A Light-Weight Countermeasure to Forwarding Misbehavior in Wireless Sensor Networks: Design, Analysis, and Evaluation. IEEE Syst. J. 2016, 12, 834–842. [Google Scholar] [CrossRef]
- Cui, B.; Yang, S. NRE: Suppress Selective Forwarding Attacks in Wireless Sensor Networks. In Proceedings of the IEEE Conference on Communications and Network Security, San Francisco, CA, USA, 29–31 October 2014; pp. 229–237. [Google Scholar]
- Pu, C.; Lim, S.; Jinseok, C.; Byungkwan, J. Active Detection in Mitigating Routing Misbehavior for MANETs. Wirel. Netw. 2017. [Google Scholar] [CrossRef]
- Yang, X.; Lin, J.; Yu, W.; Moulema, P.; Fu, X.; Zhao, W. A Novel En-Route Filtering Scheme Against False Data Injection Attacks in Cyber-Physical Networked Systems. IEEE Trans. Comput. 2015, 64, 4–18. [Google Scholar] [CrossRef]
- Zou, Y.; Zhu, J.; Wang, X.; Hanzo, L. A Survey on Wireless Security: Technical Challenges, Recent Advances, and Future Trends. Proc. IEEE 2016, 104, 1727–1765. [Google Scholar] [CrossRef]
- Dvir, A.; Holczer, T.; Buttyan, L. VeRA-Version Number and Rank Authentication in RPL. In Proceedings of the IEEE Eighth International Conference on Mobile Ad-Hoc and Sensor Systems, Valencia, Spain, 17–22 October 2011; pp. 709–714. [Google Scholar]
- Winter, T.; Thubert, P. RPL: IPv6 Routing Protocol for Low-Power and Lossy Networks. RFC Stand. 6550. 2012. Available online: https://www.rfc-editor.org/info/rfc6550 (accessed on 26 September 2018).
- Le, A.; Loo, J.; Lasebae, A.; Vinel, A.; Chen, Y.; Chai, M. The Impact of Rank Attack on Network Topology of Routing Protocol for Low-Power and Lossy Networks. IEEE Sens. J. 2013, 11, 3685–3692. [Google Scholar] [CrossRef]
- Heo, J.; Kim, J.; Bahk, S.; Paek, J. Dodge-Jam: Anti-Jamming Technique for Low-Power and Lossy Wireless Networks. In Proceedings of the 14th Annual IEEE International Conference on Sensing, Communication, and Networking (SECON), San Diego, CA, USA, 12–14 June 2017; pp. 1–9. [Google Scholar]
- Perazzo, P.; Vallati, C.; Anastasi, G.; Dini, G. DIO Suppression Attack Against Routing in the Internet of Things. IEEE Commun. Lett. 2017, 21, 2524–2527. [Google Scholar] [CrossRef]
- Pu, C.; Hajjar, S. Mitigating Forwarding Misbehaviors in RPL-based Low Power and Lossy Networks. In Proceedings of the 15th IEEE Annual Consumer Communications & Networking Conference (CCNC), Las Vegas, NV, USA, 12–15 January 2018; pp. 1–6. [Google Scholar]
- Pu, C. Mitigating DAO Inconsistency Attack in RPL-based Low Power and Lossy Networks. In Proceedings of the IEEE 8th Annual Computing and Communication Workshop and Conference (CCWC), Las Vegas, NV, USA, 8–10 January 2018; pp. 570–574. [Google Scholar]
- Pu, C.; Song, T. Hatchetman Attack: A Denial of Service Attack Against Routing in Low Power and Lossy Networks. In Proceedings of the 5th IEEE International Conference on Cyber Security and Cloud Computing (CSCloud)/2018 4th IEEE International Conference on Edge Computing and Scalable Cloud (EdgeCom), Shanghai, China, 22–24 June 2018; pp. 12–17. [Google Scholar]
- Raza, S.; Wallgren, L.; Voigt, T. SVELTE: Real-time intrusion detection in the Internet of Things. Ad Hoc Netw. 2013, 11, 2661–2674. [Google Scholar] [CrossRef]
- Beigi-Mohammadi, N.; Misic, J.; Khazaei, H.; Misic, V.B. An Intrusion Detection System for Smart Grid Neighborhood Area Network. In Proceedings of the IEEE International Conference on Communications (ICC), Sydney, NSW, Australia, 10–14 June 2014; pp. 4125–4130. [Google Scholar]
- Hummen, R.; Hiller, J.; Wirtz, H.; Henze, M.; Shafagh, H.; Wehrle, K. 6LoWPAN Fragmentation Attacks and Mitigation Mechanisms. In Proceedings of the Sixth ACM Conference on Security and Privacy in Wireless and Mobile Networks, Budapest, Hungary, 17–19 April 2013; pp. 55–66. [Google Scholar]
- Sajjad, S.M.; Yousaf, M. Security analysis of IEEE 802.15. 4 MAC in the context of Internet of Things (IoT). In Proceedings of the Conference on Information Assurance and Cyber Security (CIACS), Rawalpindi, Pakistan, June 2014; pp. 9–14. [Google Scholar]
- Kasinathan, P.; Pastrone, C.; Spirito, M.A.; Vinkovits, M. Denial-of-Service detection in 6LoWPAN based Internet of Things. In Proceedings of the IEEE 9th International Conference on Wireless and Mobile Computing, Networking and Communications (WiMob), Lyon, France, 7–9 October 2013; pp. 600–607. [Google Scholar]
- Rghioui, A.; Khannous, A.; Bouhorma, M. Denial-of-Service attacks on 6LoWPAN-RPL networks: Threats and an intrusion detection system proposition. J. Adv. Comput. Sci. Technol. 2014, 3, 143–152. [Google Scholar] [CrossRef]
- Levis, P.; Clausen, T. The Trickle Algorithm. RFC Stand. 6206. 2011. Available online: https://www.rfc-editor.org/info/rfc6206 (accessed on 26 September 2018).
- Zhao, J. On Resilience and Connectivity of Secure Wireless Sensor Networks Under Node Capture Attacks. IEEE Trans. Inf. Forensics Secur. 2017, 12, 557–571. [Google Scholar] [CrossRef]
- Abdallah, A.; Shen, X. Efficient Prevention Technique for False Data Injection Attack in Smart Grid. In Proceedings of the IEEE International Conference on Communications (ICC), Kuala Lumpur, Malaysia, 22–27 May 2016; pp. 1–6. [Google Scholar]
- Boulis, A. Castalia. 2014. Available online: http://castalia.forge.nicta.com.au (accessed on 15 February 2018).
- Marti, S.; Giuli, T.J.; Lai, K.; Baker, M. Mitigating routing misbehavior in mobile ad hoc networks. In Proceedings of the 6th Annual International Conference on Mobile Computing and Networking, Boston, MA, USA, 6–11 August 2000; pp. 255–265. [Google Scholar]
- Shila, D.M.; Yu, C.; Anjali, T. Mitigating Selective Forwarding Attacks with a Channel-Aware Approach in WMNs. IEEE Trans. on Wirel. Commun. 2010, 9, 1661–1675. [Google Scholar] [CrossRef]
| Parameter | Value |
|---|---|
| Network Area | 150 × 150 m2 |
| Number of Nodes | 51 |
| Communication Range | 30 m |
| Packet Injection Rate | 0.1 packet/s |
| Packet Size | 40 bytes |
| Radio Data Rate | 250 Kbps |
| Channel Error Rate | 10% |
| Number of Malicious Nodes | 1 to 5 |
| Suppression Attack Rate | 0.0125 to 0.1 time/s |
| Number of Spoof Data Messages | 10 and 15 |
| Simulation Time | 10,000 s |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Pu, C.; Zhou, X. Suppression Attack Against Multicast Protocol in Low Power and Lossy Networks: Analysis and Defenses. Sensors 2018, 18, 3236. https://doi.org/10.3390/s18103236
Pu C, Zhou X. Suppression Attack Against Multicast Protocol in Low Power and Lossy Networks: Analysis and Defenses. Sensors. 2018; 18(10):3236. https://doi.org/10.3390/s18103236
Chicago/Turabian StylePu, Cong, and Xitong Zhou. 2018. "Suppression Attack Against Multicast Protocol in Low Power and Lossy Networks: Analysis and Defenses" Sensors 18, no. 10: 3236. https://doi.org/10.3390/s18103236
APA StylePu, C., & Zhou, X. (2018). Suppression Attack Against Multicast Protocol in Low Power and Lossy Networks: Analysis and Defenses. Sensors, 18(10), 3236. https://doi.org/10.3390/s18103236




